Microsoft Security Response Center Presented by Fan Chiang
Microsoft Security Response Center Presented by Fan Chiang, Chun-Wei(范姜竣韋) 2020/11/4 NTUIM 1

Microsoft Security Response Center Agenda • • • Background Case Current Problem MSRC Microsoft Security Response Center Security Vulnerability Problem Solving Process ▫ Workarounds ▫ Service Packs ▫ Patches 4 phases of patch developing 2020/11/4 • Follow-up • Question NTUIM 2
Microsoft Security Response Center Background • According to a 2000 study of IDC : Data security budget in 2003 had risen to 14. 8 billion from 6. 2 billion in 1999 Microsoft Security Response Center • Of all the technologies, the Internet has proven to be the greatest threat to data security. Because of three reasons : 2020/11/4 ▫ Scope ▫ Anonymity ▫ Reproducibility NTUIM 3
Microsoft Security Response Center 2020/11/4 NTUIM 4
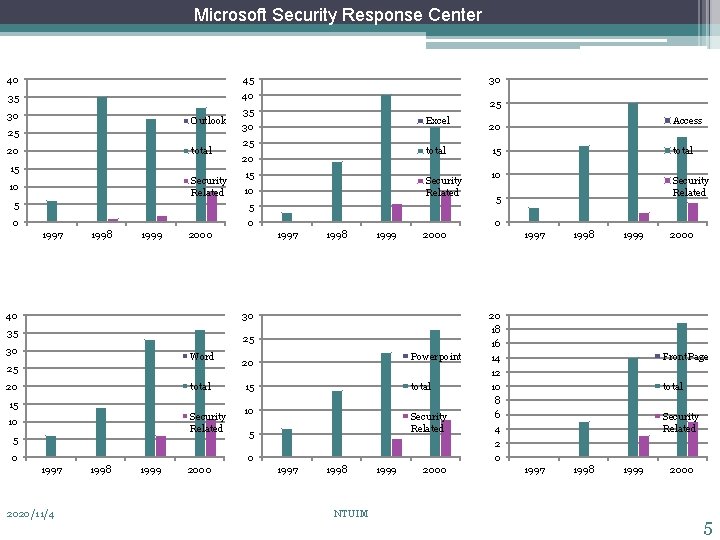
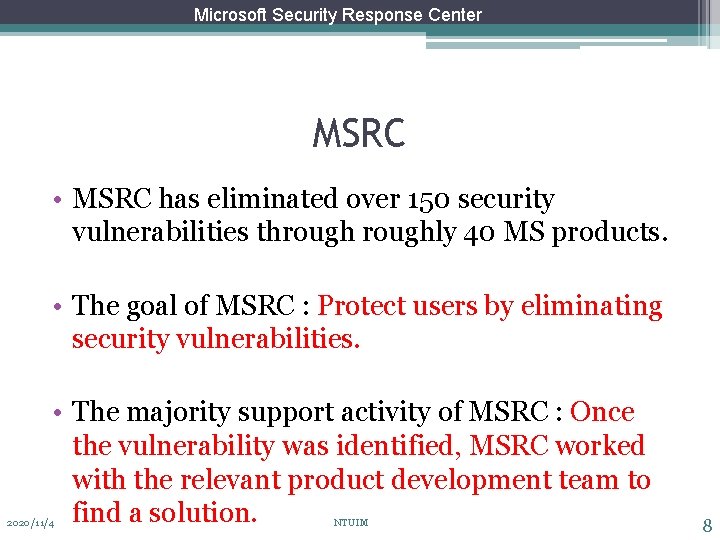
Microsoft Security Response Center 40 45 35 40 30 35 Outlook 25 20 total 15 Security Related 10 5 30 25 Excel 30 25 total 20 15 Security Related 10 5 0 1998 1999 2000 40 1997 1998 1999 25 30 Word 25 20 total 15 Security Related 10 5 0 Powerpoint 20 15 total 10 Security Related 5 0 1997 2020/11/4 1998 1999 2000 total 10 Security Related 5 1997 1998 NTUIM 1999 1997 2000 30 35 15 0 0 1997 Access 20 2000 1998 1999 20 18 16 14 12 10 8 6 4 2 0 2000 Front. Page total Security Related 1997 1998 1999 2000 5

Microsoft Security Response Center Case • Security program manager of MSRC Scott Culp v. s. Cy. BER Paladin(Cy. P) Microsoft Security Response Center • Security Vulnerability of MS IIS(version 4. 0、5. 0) “Canonicalization Error” • Cy. P planned to post his findings publicly “within few days. ” 2020/11/4 NTUIM 6
Microsoft Security Response Center Current Problem • Contact the IIS development team and get them on their situation. Microsoft Security Response Center • Legitimize the security vulnerability. 2020/11/4 NTUIM 7
Microsoft Security Response Center MSRC • MSRC has eliminated over 150 security vulnerabilities throughly 40 MS products. Microsoft Security Response Center • The goal of MSRC : Protect users by eliminating security vulnerabilities. • The majority support activity of MSRC : Once the vulnerability was identified, MSRC worked with the relevant product development team to find a solution. 2020/11/4 NTUIM 8
Microsoft Security Response Center MSRC (con’t) • Forms and types of vulnerabilities : ▫ Virus、worms、incorrectly-configured systems, password written on sticky pads. Microsoft Security Response Center • Security vulnerability definition of MS : ▫ As a flaw in a product that makes it infeasible even when using the product properly - to prevent attackers from usurping privileges on the user’s system, regulating its operation, compromising data on it or assuming ungranted trust. 2020/11/4 NTUIM 9
Microsoft Security Response Center Security Vulnerability Problem Solving Process • Step 1 : Obtain information about possible security problems. Microsoft Security Response Center • Step 2 : Perform Initial Triage. ▫ - Working with customer to gather more information on the problem ▫ - Testing reported configuration ▫ - Informing the user about patches or workarounds already release • Step 3 : Involve Product Team. 2020/11/4 NTUIM 10
Microsoft Security Response Center Security Vulnerability Problem Solving Process (con’t) • Step 4 : Devise Solution Alternatives. ▫ ▫ - Server-side fixes - Workarounds - Service Packs - Patches Microsoft Security Response Center • Step 5 : Implement Solutions. • Step 6 : Press Response 2020/11/4 NTUIM 11
Microsoft Security Response Center Security Vulnerability Problem Solving Process - Step 4 • Workarounds : Provide the user with a alternative method of using the product that prevents a vulnerability from being exploited. Microsoft Security Response Center • Service Packs : A scheduled, periodic software update that corrected a large number of bugs, including security vulnerabilities. • Patches : Used when the vulnerability needs to be fixed immediately. 2020/11/4 NTUIM 12
Microsoft Security Response Center 4 phases of patch developing • Phase 1 : Create a “Private build, ” and Undergo initial testing. Microsoft Security Response Center • Phase 2 : Proceed to “War Team”. They challenge the developer to show that the “Private build” is necessary and the engineering solution is correct. 2020/11/4 NTUIM 13
Microsoft Security Response Center 4 phases of patch developing (con’t) • Phase 3 : Formal testing and Conduct full compatibility testing. Microsoft Security Response Center • Phase 4 : Develop installer package of each version of the affected product. And then the packages are signed (by MS) and retested. 2020/11/4 NTUIM 14
Microsoft Security Response Center Security Vulnerability Problem Solving Process (con’t) • Step 4 : Devise Solution Alternatives. ▫ - Workarounds ▫ - Service Packs ▫ - Patches Microsoft Security Response Center • Step 5 : Implement Solutions. ▫ Build bulletin and knowledge base, then Release the patches or workarounds. • Step 6 : Press Response 2020/11/4 NTUIM 15
Microsoft Security Response Center Follow-Up (B) • Good news : The IIS development team knew that this security problem was solved by a already released patch months ago. Microsoft Security Response Center • Bad news : Due to the issue was complex, affected few users and some mitigating factors, few customers had installed the corresponding patch. 2020/11/4 NTUIM 16
Microsoft Security Response Center Canonicalization Error • Security Vulnerability of MS IIS(version 4. 0、 5. 0) “Canonicalization Error” Microsoft Security Response Center ▫ c: dirtest. dat, and. . test. dat might all refer to the same file like c: dirtest. dat. ▫ c: inetpubwwwroottest 1test 2test. asp ▫ www. microsoft. com/windowsnt/information/test. asp (VIRTUAL) ▫ www. microsoft. com/test 1/test 2/test. asp (PHYSICAL) 2020/11/4 NTUIM 17
Microsoft Security Response Center Follow-Up (B) (con’t) • First, release the information as quickly as possible, in case malicious users were already compromising web sites. Microsoft Security Response Center • Second, and equally important, once the bulletin was released, the whole world needed to be informed as quickly as possible. Otherwise hackers would start attacking the stragglers. 2020/11/4 NTUIM 18
Microsoft Security Response Center Follow-Up (C) • MSRC decided to keep the security vulnerability problem under wraps over the weekend. Microsoft Security Response Center • MSRC asked TAMs to support the patch installation on customers’ machines. 2020/11/4 NTUIM 19
Microsoft Security Response Center Question • How could Culp solve this security problem before the attacker compromising Web sites running MS IIS ? Microsoft Security Response Center • Whether take a calculated risk and wait an extra day in order to prepare the patch in multiple languages? 2020/11/4 NTUIM 20
- Slides: 20