Microsoft Forefront Identity Manager 2010 Henk Den Baes
Microsoft Forefront Identity Manager 2010 Henk Den Baes Technology advisor Microsoft Belux
Agenda • • • What is identity? Microsoft’s Identity and Access Strategy Business Ready Security − The business challenges − How Forefront Identity Manager (FIM) 2010 addresses the challenges − Scenarios Summary Resources
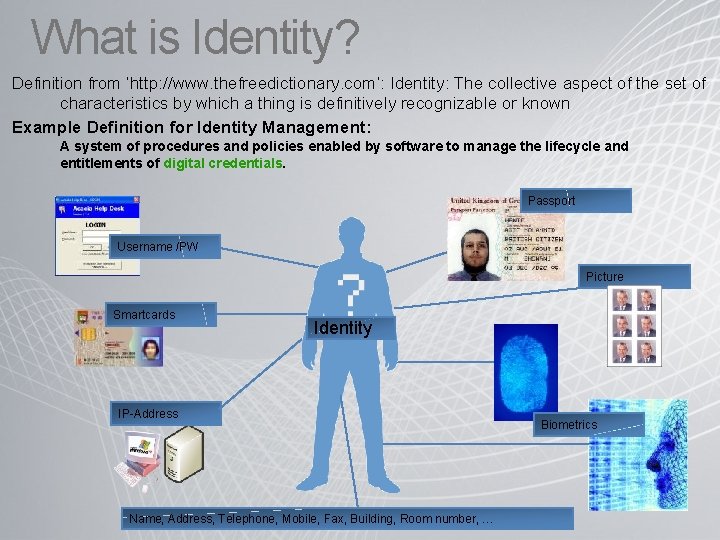
What is Identity? Definition from ‘http: //www. thefreedictionary. com’: Identity: The collective aspect of the set of characteristics by which a thing is definitively recognizable or known Example Definition for Identity Management: A system of procedures and policies enabled by software to manage the lifecycle and entitlements of digital credentials. Passport Username /PW Picture Smartcards Identity IP-Address Name, Address, Telephone, Mobile, Fax, Building, Room number, … Biometrics
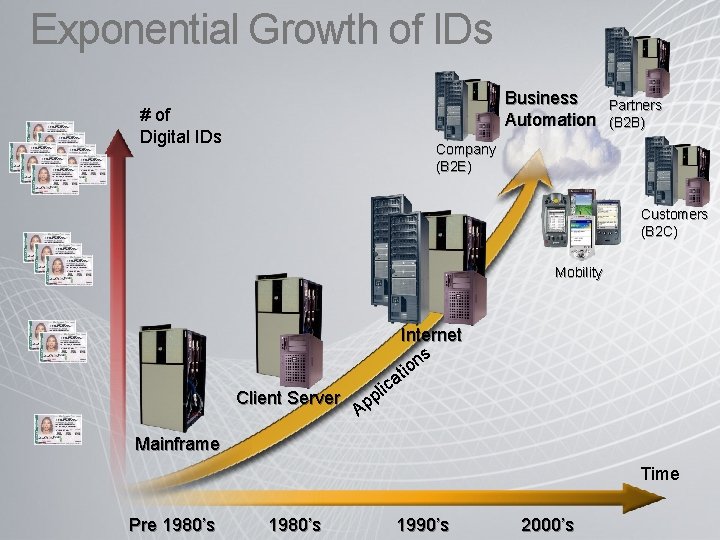
Exponential Growth of IDs Business Automation # of Digital IDs Partners (B 2 B) Company (B 2 E) Customers (B 2 C) Mobility Client Server Internet ns it o ica l p p A Mainframe Time Pre 1980’s 1990’s 2000’s
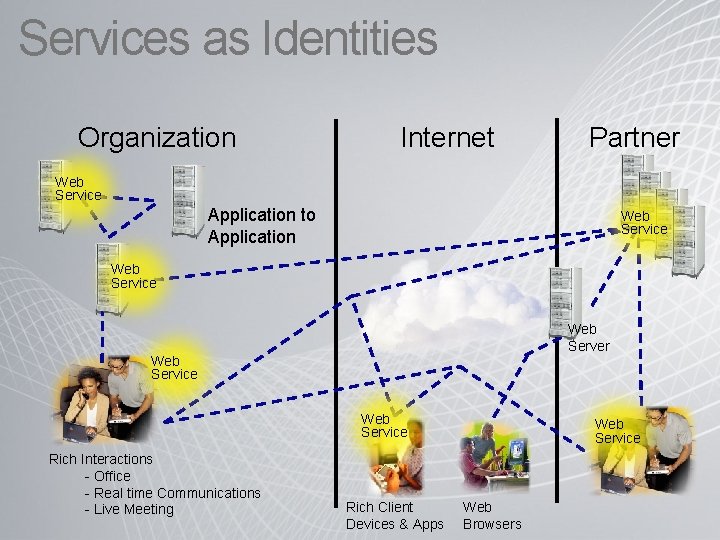
Services as Identities Organization Internet Partner Web Service Application to Application Web Service Web Server Web Service Rich Interactions - Office - Real time Communications - Live Meeting Rich Client Devices & Apps Web Service Web Browsers
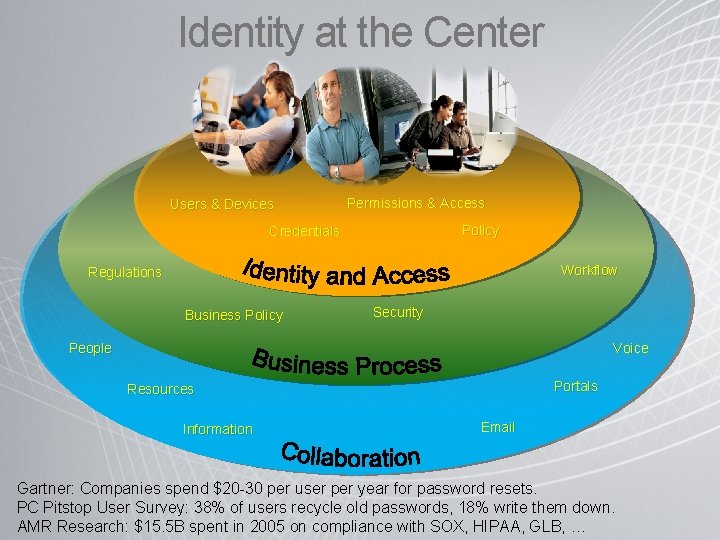
Identity at the Center Users & Devices Permissions & Access Policy Credentials Workflow Regulations Business Policy Security Voice People Portals Resources Information Email Gartner: Companies spend $20 -30 per user per year for password resets. PC Pitstop User Survey: 38% of users recycle old passwords, 18% write them down. AMR Research: $15. 5 B spent in 2005 on compliance with SOX, HIPAA, GLB, …
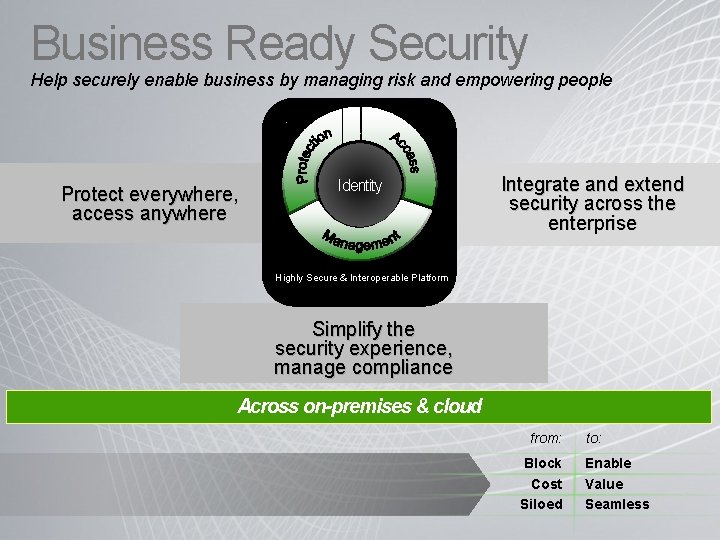
Business Ready Security Help securely enable business by managing risk and empowering people Protect everywhere, access anywhere Identity Integrate and extend security across the enterprise Highly Secure & Interoperable Platform Simplify the security experience, manage compliance Across on-premises & cloud from: Block Cost Siloed to: Enable Value Seamless
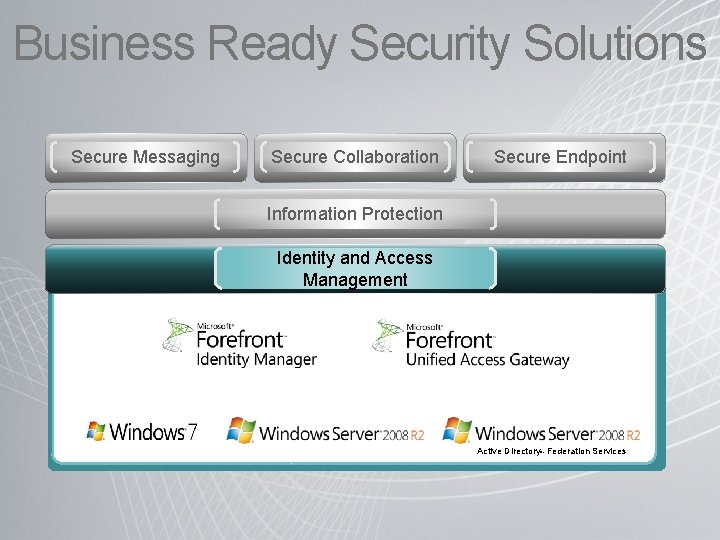
Business Ready Security Solutions Secure Messaging Secure Collaboration Secure Endpoint Information Protection Identity and Access Management Active Directory Federation Services ® ®
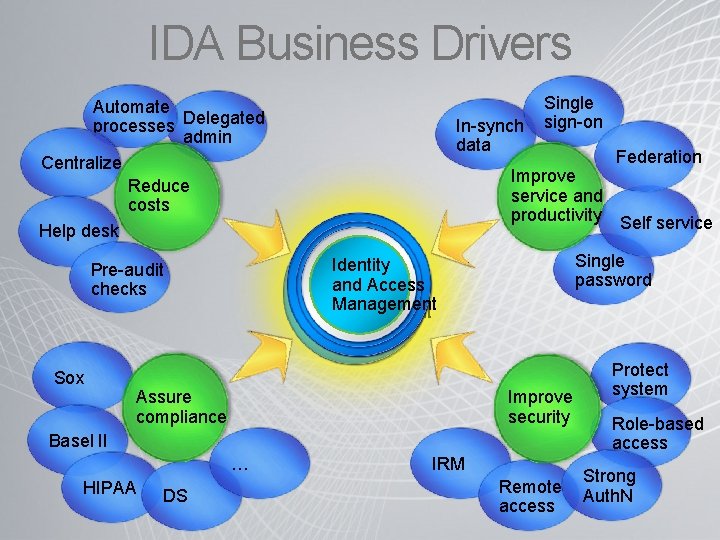
IDA Business Drivers Automate processes Delegated admin Centralize Reduce costs Help desk Single password Improve security Assure compliance Basel II … HIPAA DS Federation Improve service and productivity Self service Identity and. Access and Management Pre-audit checks Sox In-synch data Single sign-on IRM Remote access Protect system Role-based access Strong Auth. N
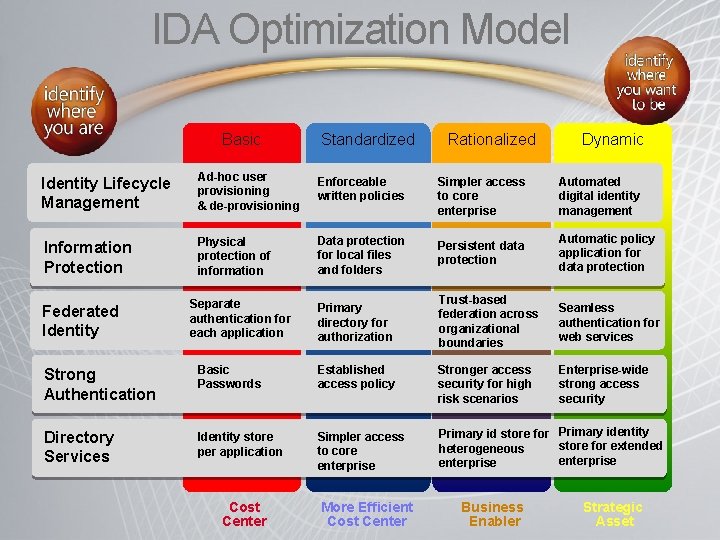
IDA Optimization Model Basic Standardized Rationalized Dynamic Identity Lifecycle Management Ad-hoc user provisioning & de-provisioning Enforceable written policies Simpler access to core enterprise Automated digital identity management Information Protection Physical protection of information Data protection for local files and folders Persistent data protection Automatic policy application for data protection Primary directory for authorization Trust-based federation across organizational boundaries Seamless authentication for web services Enterprise-wide strong access security Federated Identity Separate authentication for each application Strong Authentication Basic Passwords Established access policy Stronger access security for high risk scenarios Directory Services Identity store per application Simpler access to core enterprise Primary id store for Primary identity store for extended heterogeneous enterprise Cost Center More Efficient Cost Center Business Enabler Strategic Asset
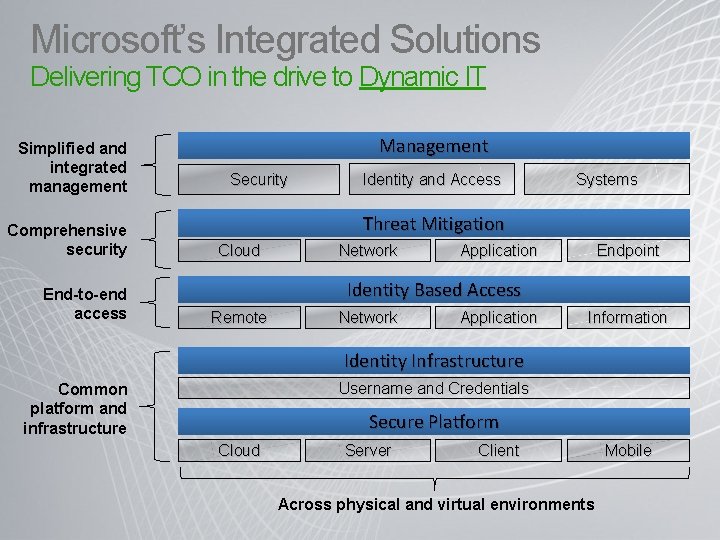
Microsoft’s Integrated Solutions Delivering TCO in the drive to Dynamic IT Simplified and integrated management Comprehensive security End-to-end access Management Security Identity and Access Systems Threat Mitigation Cloud Network Application Endpoint Identity Based Access Remote Network Application Information Identity Infrastructure Username and Credentials Common platform and infrastructure Secure Platform Cloud Server Client Across physical and virtual environments Mobile
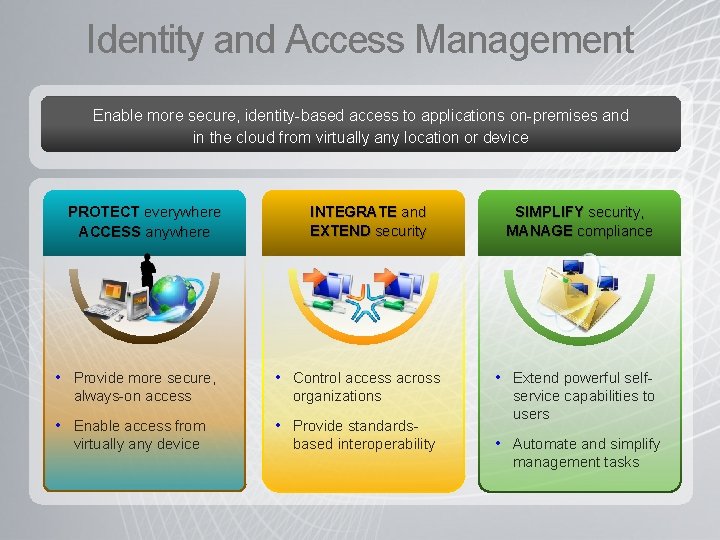
Identity and Access Management Enable more secure, identity-based access to applications on-premises and in the cloud from virtually any location or device PROTECT everywhere ACCESS anywhere • Provide more secure, always-on access • Enable access from virtually any device INTEGRATE and EXTEND security • Control access across organizations • Provide standardsbased interoperability SIMPLIFY security, MANAGE compliance • Extend powerful selfservice capabilities to users • Automate and simplify management tasks
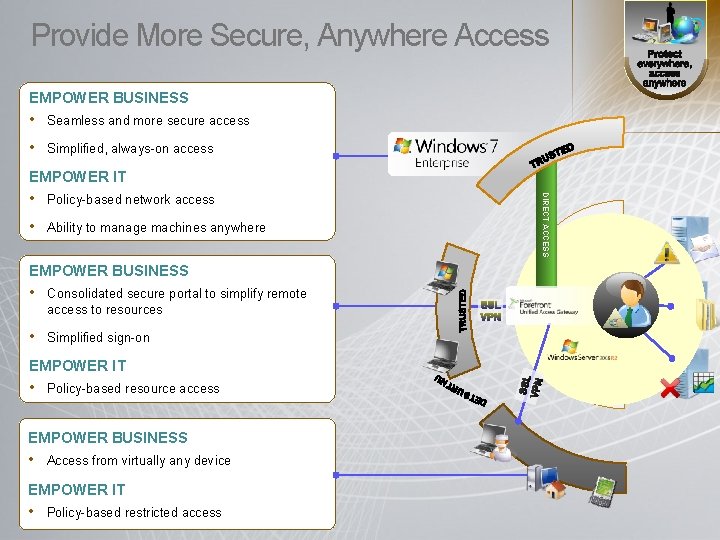
Provide More Secure, Anywhere Access EMPOWER BUSINESS • Seamless and more secure access • Simplified, always-on access EMPOWER IT • Ability to manage machines anywhere EMPOWER BUSINESS • Consolidated secure portal to simplify remote access to resources • Simplified sign-on EMPOWER IT • Policy-based resource access EMPOWER BUSINESS • Access from virtually any device EMPOWER IT • Policy-based restricted access DIRECT ACCESS • Policy-based network access
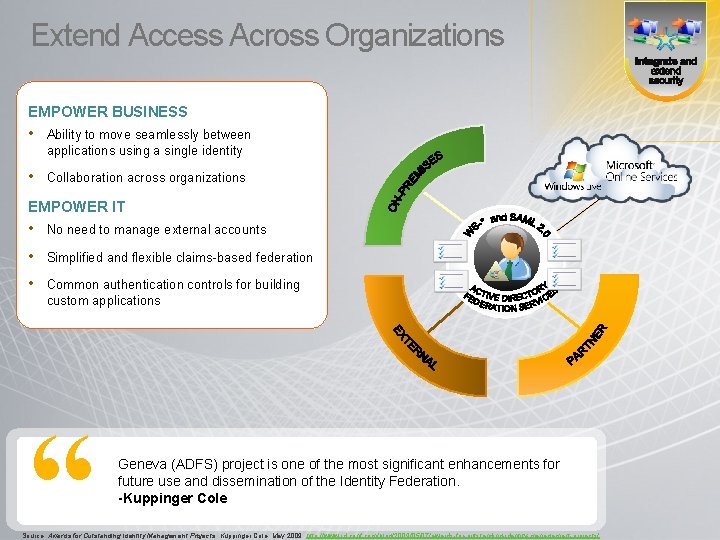
Extend Access Across Organizations EMPOWER BUSINESS • Ability to move seamlessly between applications using a single identity • Collaboration across organizations EMPOWER IT • No need to manage external accounts • Simplified and flexible claims-based federation • Common authentication controls for building custom applications “ Geneva (ADFS) project is one of the most significant enhancements for future use and dissemination of the Identity Federation. -Kuppinger Cole Source: Awards for Outstanding Identity Management Projects. Kuppinger Cole, May 2009. http: //www. id-conf. com/blog/2009/05/07/awards-for-outstanding-identity-management-projects/
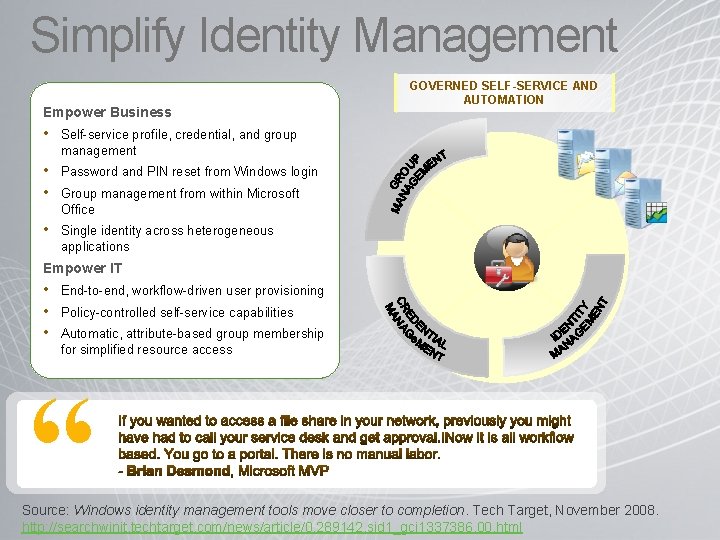
Simplify Identity Management Empower Business GOVERNED SELF-SERVICE AND AUTOMATION • Self-service profile, credential, and group management • Password and PIN reset from Windows login • Group management from within Microsoft Office • Single identity across heterogeneous applications Empower IT • End-to-end, workflow-driven user provisioning • Policy-controlled self-service capabilities • Automatic, attribute-based group membership for simplified resource access “ Source: Windows identity management tools move closer to completion. Tech Target, November 2008. http: //searchwinit. techtarget. com/news/article/0, 289142, sid 1_gci 1337386, 00. html
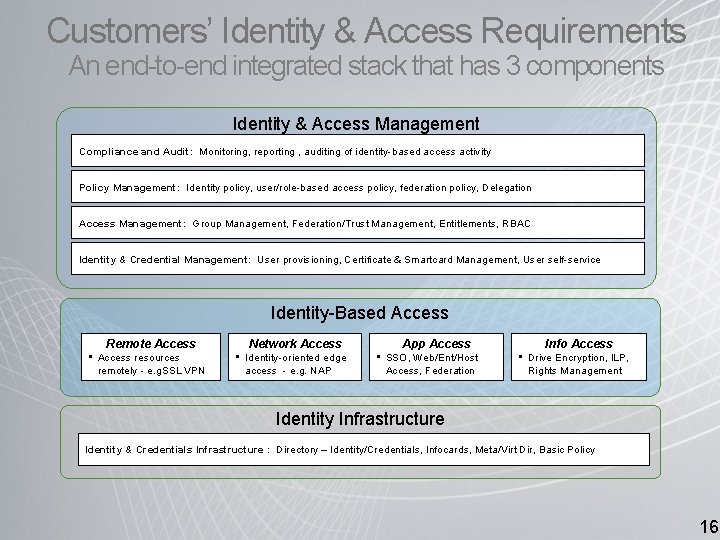
Customers’ Identity & Access Requirements An end-to-end integrated stack that has 3 components Identity & Access Management Compliance and Audit: Monitoring, reporting , auditing of identity-based access activity Policy Management: Identity policy, user/role-based access policy, federation policy, Delegation Access Management: Group Management, Federation/Trust Management, Entitlements, RBAC Identity & Credential Management: User provisioning, Certificate & Smartcard Management, User self-service Identity-Based Access Remote Access • Access resources remotely - e. g. SSL VPN Network Access • Identity-oriented edge access - e. g. NAP App Access • SSO, Web/Ent/Host Access, Federation Info Access • Drive Encryption, ILP, Rights Management Identity Infrastructure Identity & Credentials Infrastructure : Directory – Identity/Credentials, Infocards, Meta/Virt Dir, Basic Policy 16
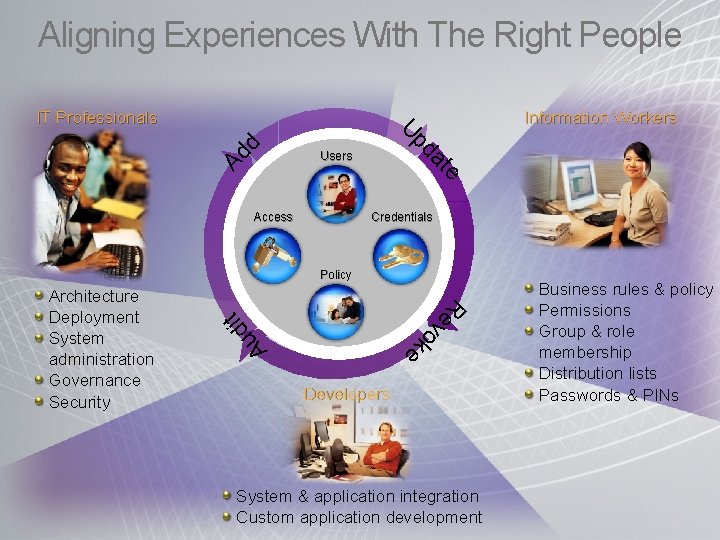
Aligning Experiences With The Right People Information Workers Users Access e at Ad pd U d IT Professionals Credentials Policy t di R e v Au o k e Architecture Deployment System administration Governance Security Developers System & application integration Custom application development Business rules & policy Permissions Group & role membership Distribution lists Passwords & PINs
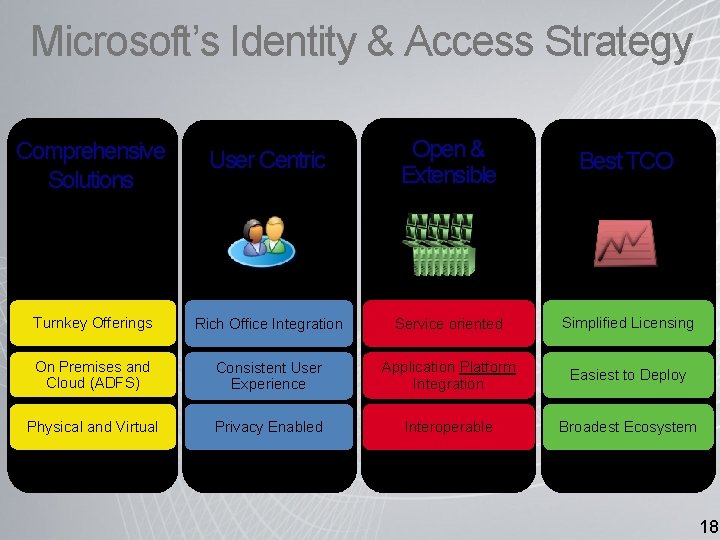
Microsoft’s Identity & Access Strategy Comprehensive Solutions User Centric Open & Extensible Best TCO Turnkey Offerings Rich Office Integration Service oriented Simplified Licensing On Premises and Cloud (ADFS) Consistent User Experience Application Platform Integration Easiest to Deploy Physical and Virtual Privacy Enabled Interoperable Broadest Ecosystem 18
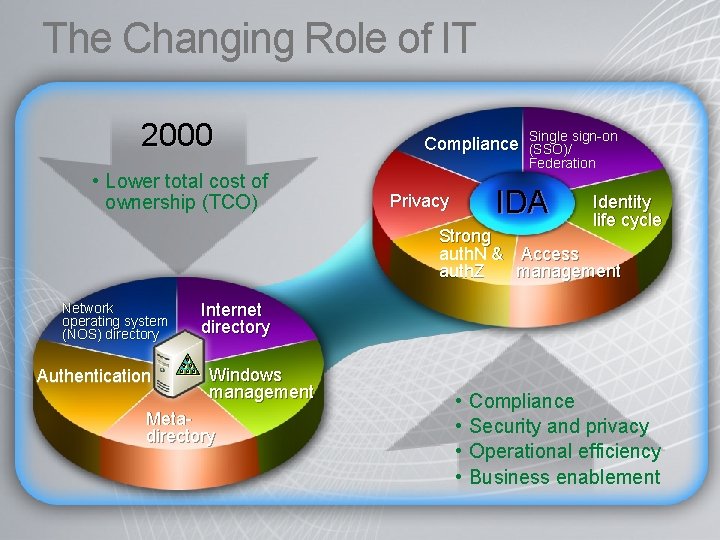
The Changing Role of IT 2000 • Lower total cost of ownership (TCO) Compliance Single sign-on (SSO)/ Federation IDA Privacy Identity life cycle Strong auth. N & Access auth. Z management Network operating system (NOS) directory Authentication Internet directory Windows management Metadirectory • • Compliance Security and privacy Operational efficiency Business enablement
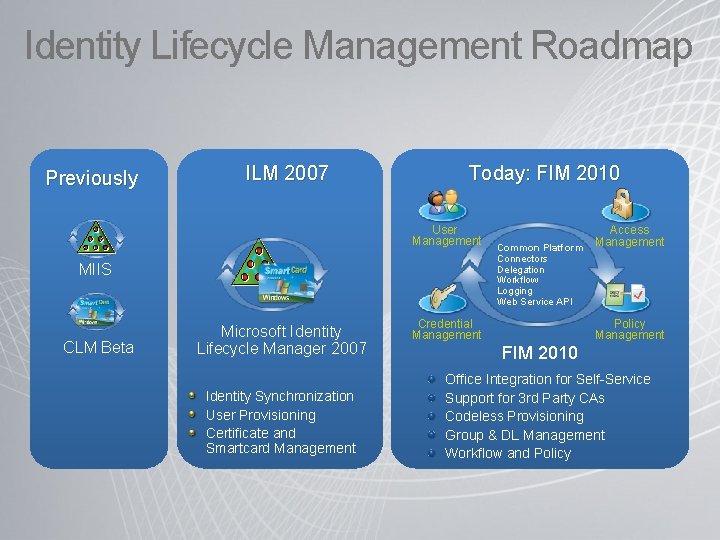
Identity Lifecycle Management Roadmap Previously ILM 2007 Today: FIM 2010 User Management Connectors Delegation Workflow Logging Web Service API MIIS CLM Beta Access Management Common Platform Microsoft Identity Lifecycle Manager 2007 Identity Synchronization User Provisioning Certificate and Smartcard Management Credential Management Policy Management FIM 2010 Office Integration for Self-Service Support for 3 rd Party CAs Codeless Provisioning Group & DL Management Workflow and Policy
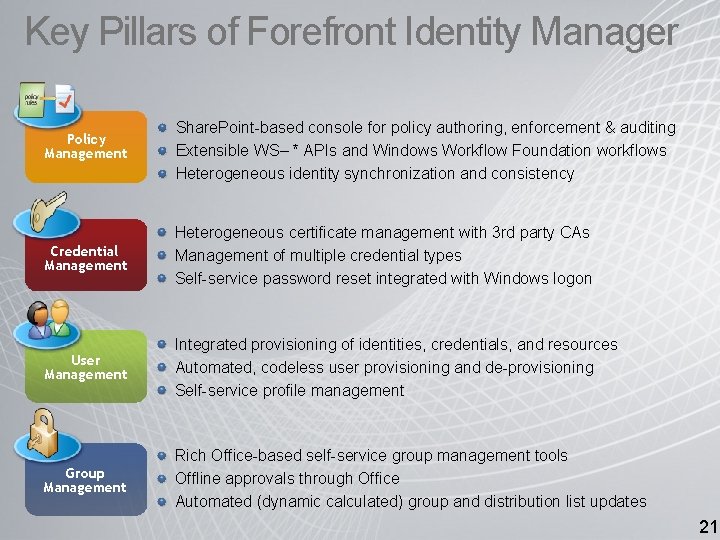
Key Pillars of Forefront Identity Manager Policy Management Share. Point-based console for policy authoring, enforcement & auditing Extensible WS– * APIs and Windows Workflow Foundation workflows Heterogeneous identity synchronization and consistency Credential Management Heterogeneous certificate management with 3 rd party CAs Management of multiple credential types Self-service password reset integrated with Windows logon User Management Integrated provisioning of identities, credentials, and resources Automated, codeless user provisioning and de-provisioning Self-service profile management Group Management Rich Office-based self-service group management tools Offline approvals through Office Automated (dynamic calculated) group and distribution list updates 21
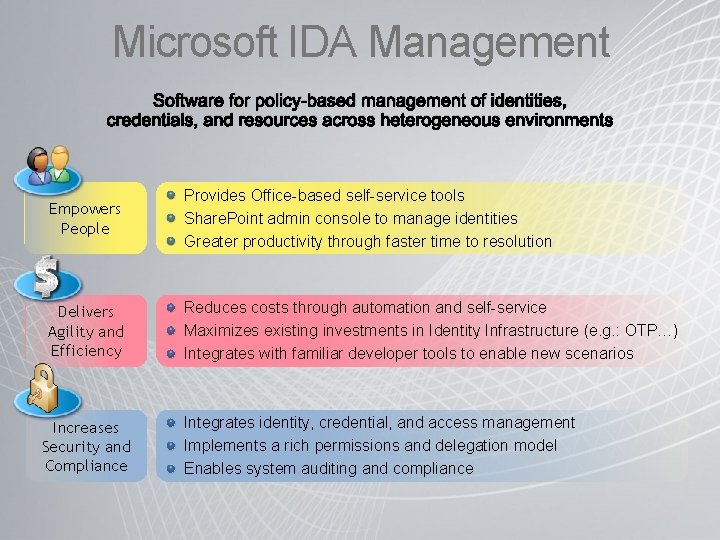
Microsoft IDA Management Software for policy-based management of identities, credentials, and resources across heterogeneous environments Empowers People Provides Office-based self-service tools Share. Point admin console to manage identities Greater productivity through faster time to resolution Delivers Agility and Efficiency Reduces costs through automation and self-service Maximizes existing investments in Identity Infrastructure (e. g. : OTP…) Integrates with familiar developer tools to enable new scenarios Increases Security and Compliance Integrates identity, credential, and access management Implements a rich permissions and delegation model Enables system auditing and compliance
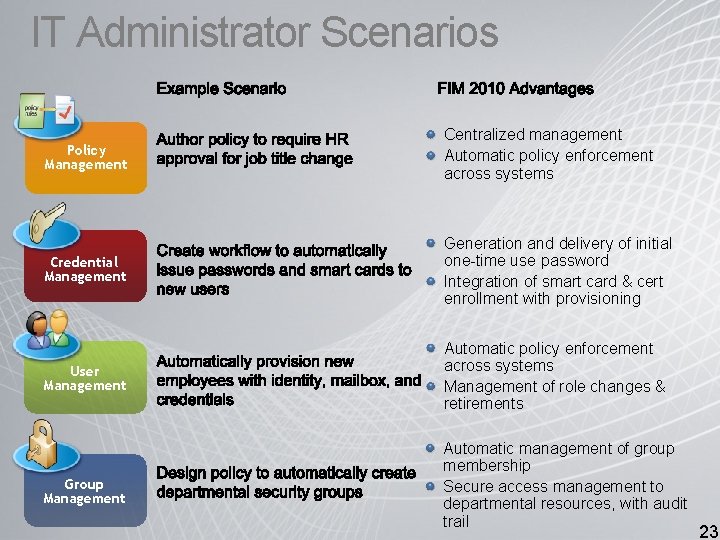
IT Administrator Scenarios Example Scenario FIM 2010 Advantages Policy Management Centralized management Automatic policy enforcement across systems Credential Management Generation and delivery of initial one-time use password Integration of smart card & cert enrollment with provisioning User Management Automatic policy enforcement across systems Management of role changes & retirements Group Management Automatic management of group membership Secure access management to departmental resources, with audit trail 23
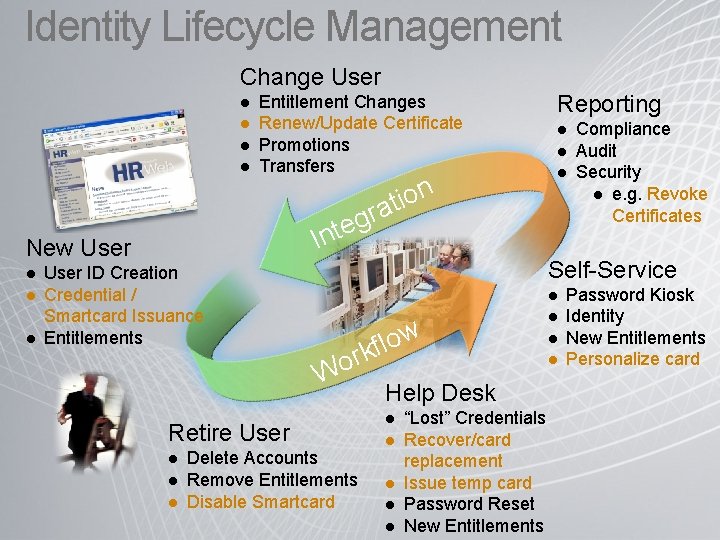
Identity Lifecycle Management Change User l l Entitlement Changes Renew/Update Certificate Promotions Transfers l l l r g te In New User l n o i at Reporting User ID Creation Credential / Smartcard Issuance Entitlements Self-Service l w o l f rk Wo Retire User l l l Compliance Audit Security l e. g. Revoke Certificates Delete Accounts Remove Entitlements Disable Smartcard Help Desk l l l “Lost” Credentials Recover/card replacement Issue temp card Password Reset New Entitlements l l l Password Kiosk Identity New Entitlements Personalize card
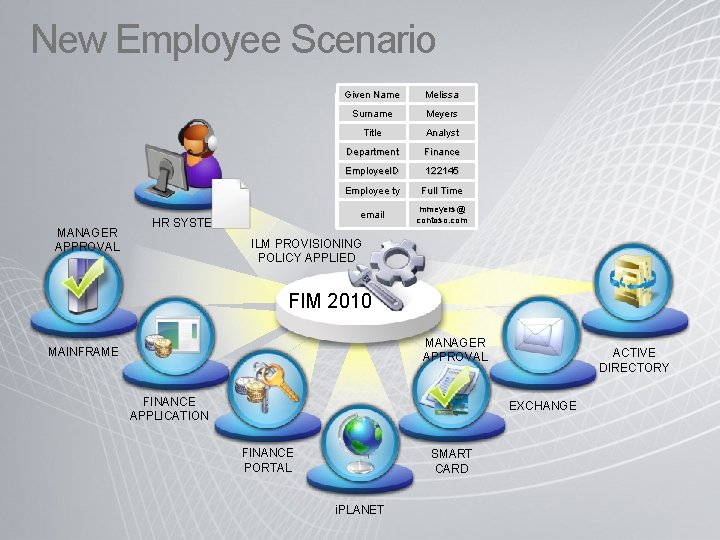
New Employee Scenario MANAGER APPROVAL Given Name Surname Title Department Employee. ID Employee ty email HR SYSTEM Melissa Meyers Analyst Finance 122145 Full Time mmeyers@ contoso. com ILM PROVISIONING POLICY APPLIED FIM 2010 MANAGER APPROVAL MAINFRAME FINANCE APPLICATION ACTIVE DIRECTORY EXCHANGE FINANCE PORTAL SMART CARD i. PLANET
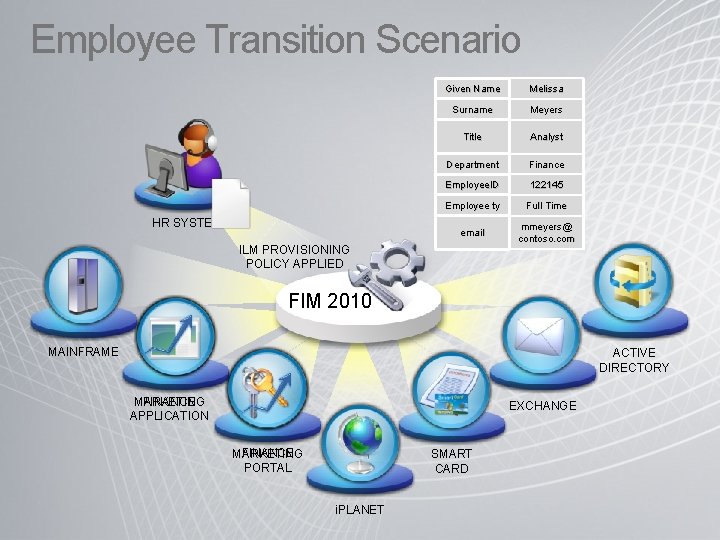
Employee Transition Scenario Given Name Melissa Surname Meyers Department Employee. ID Group Analyst Marketing Manager Finance Marketing 122145 Employee ty ty Full Time email mmeyers@ contoso. com Title HR SYSTEM ILM PROVISIONING POLICY APPLIED FIM 2010 MAINFRAME ACTIVE DIRECTORY FINANCE MARKETING APPLICATION EXCHANGE FINANCE MARKETING PORTAL SMART CARD i. PLANET
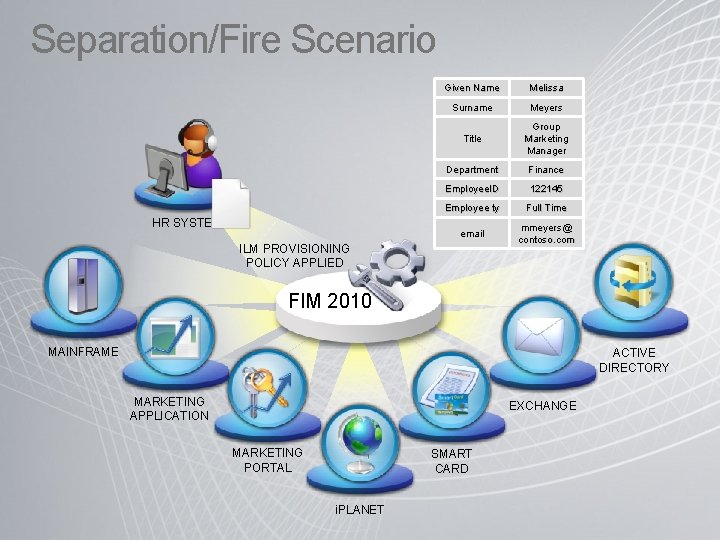
Separation/Fire Scenario HR SYSTEM Given Name Melissa Surname Meyers Title Group Marketing Manager Department Finance Employee. ID 122145 Employee ty Terminated Full Time email mmeyers@ contoso. com ILM PROVISIONING POLICY APPLIED FIM 2010 MAINFRAME ACTIVE DIRECTORY MARKETING APPLICATION EXCHANGE MARKETING PORTAL SMART CARD i. PLANET
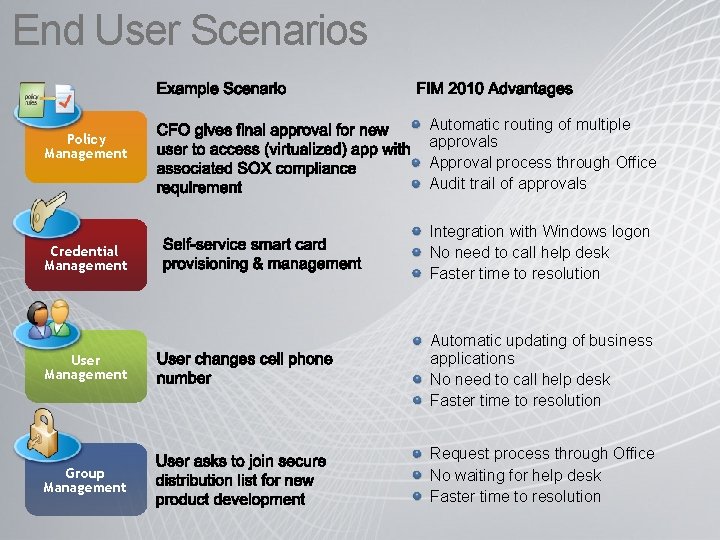
End User Scenarios Example Scenario Policy Management FIM 2010 Advantages Automatic routing of multiple approvals Approval process through Office Audit trail of approvals Credential Management Integration with Windows logon No need to call help desk Faster time to resolution User Management Automatic updating of business applications No need to call help desk Faster time to resolution Group Management Request process through Office No waiting for help desk Faster time to resolution
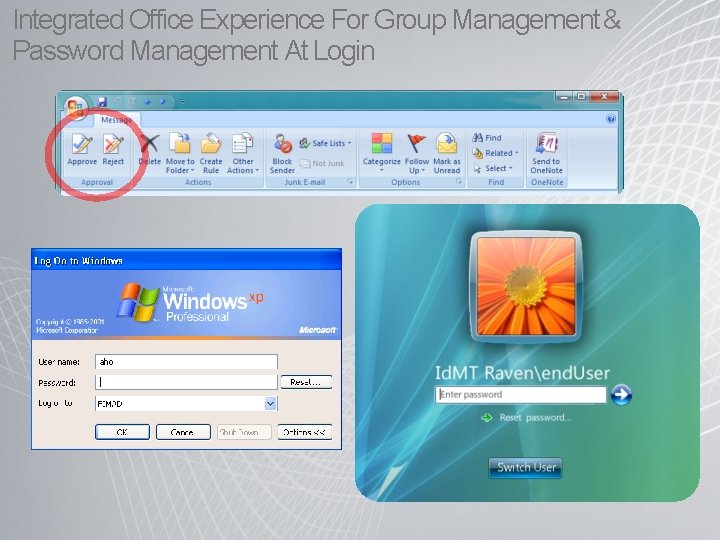
Integrated Office Experience For Group Management & Password Management At Login
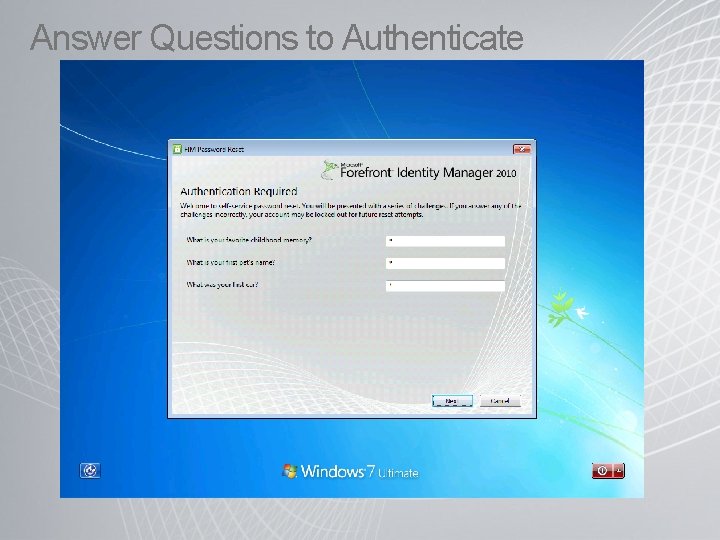
Answer Questions to Authenticate
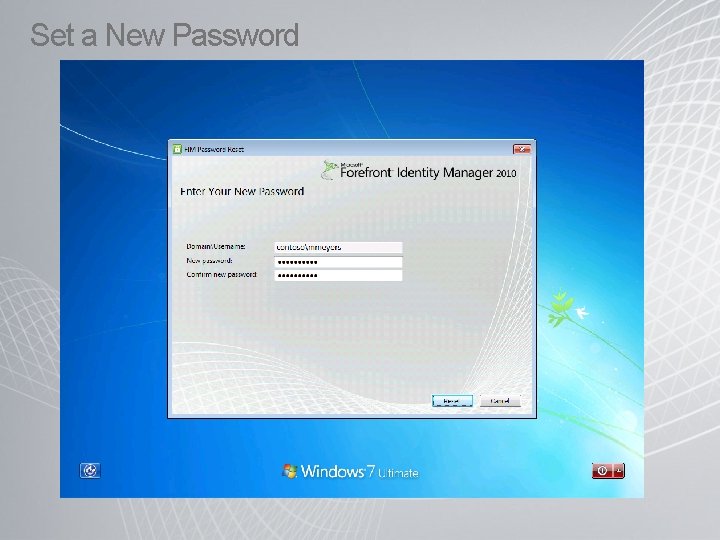
Set a New Password
Summary Identity is core to the people-driven business Today the identity life cycle management burden is on IT Microsoft’s approach: Align experiences with the right people Lowers cost Empowers people Provides IT with control with less effort How we get there ILM 2007: Brings together metadirectory, certificate management, and provisioning across Windows and enterprise systems FIM 2010: Extends ILM 2007 with new solutions to manage users, credentials, access, and policy using the tools that IT, users, and developers are most familiar with
Resources Learn more about Identity Lifecycle Manager • FIM 2010 Product Page: http: //www. microsoft. com/fim ILM 2007 Product Page: www. microsoft. com/ILM 2007 Learn About Microsoft Identity and Access (IDA) • IDA Solutions Home Page: www. microsoft. com/IDA • IDA Partners: www. microsoft. com/IDA
© 2008 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.
- Slides: 34