Microsoft Certified Trainer MCT BCS Chartered IT Professional


Microsoft Certified Trainer (MCT) BCS Chartered IT Professional (CITP) Microsoft Business Value Planning (MBVP) Certified Information Systems Auditor (CISA) Certified Information Systems Security Professional (CISSP) Microsoft Certified Information Technology Professional (MCITP) Strategic Business Planning & Audit • • Insititute of Information Security Professionals (IISP) Information Security Audit and Control Association (ISACA) International Information Systems Security Certification Consortium (ISC)2 Cloud Security Alliance—UK and Ireland • Euro. Cloud • Voices for Innovation • Microsoft Partner Advisory Council • Microsoft Executive Partner Board • IAMCP UK and International Board Member


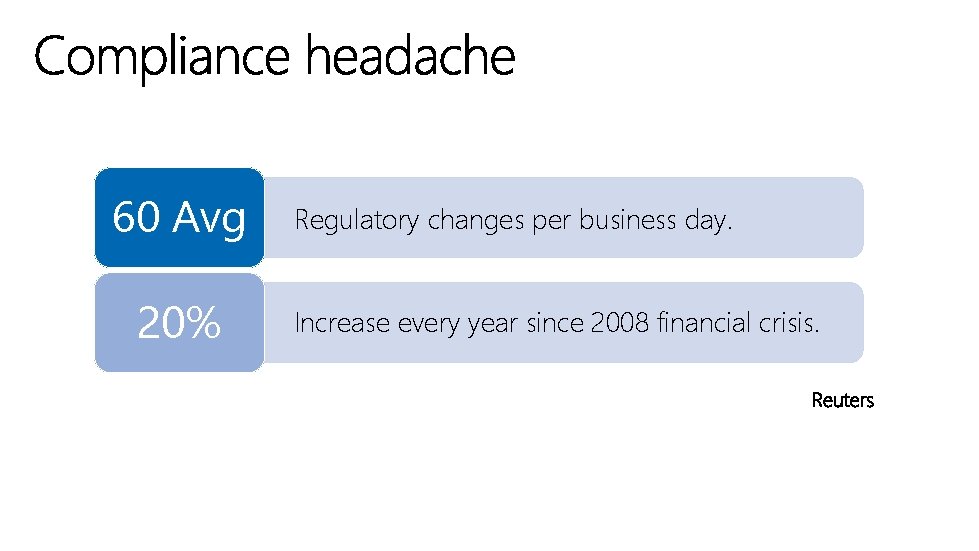
60 Avg 20% Regulatory changes per business day. Increase every year since 2008 financial crisis.



It’s in the name! But its not in practice. . . Data Environment


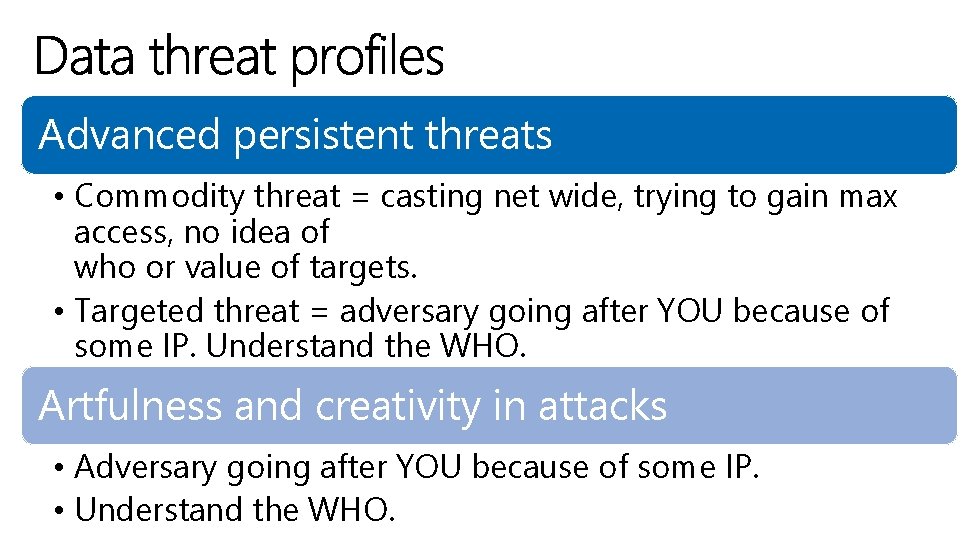
Advanced persistent threats • Commodity threat = casting net wide, trying to gain max access, no idea of who or value of targets. • Targeted threat = adversary going after YOU because of some IP. Understand the WHO. Artfulness and creativity in attacks • Adversary going after YOU because of some IP. • Understand the WHO.
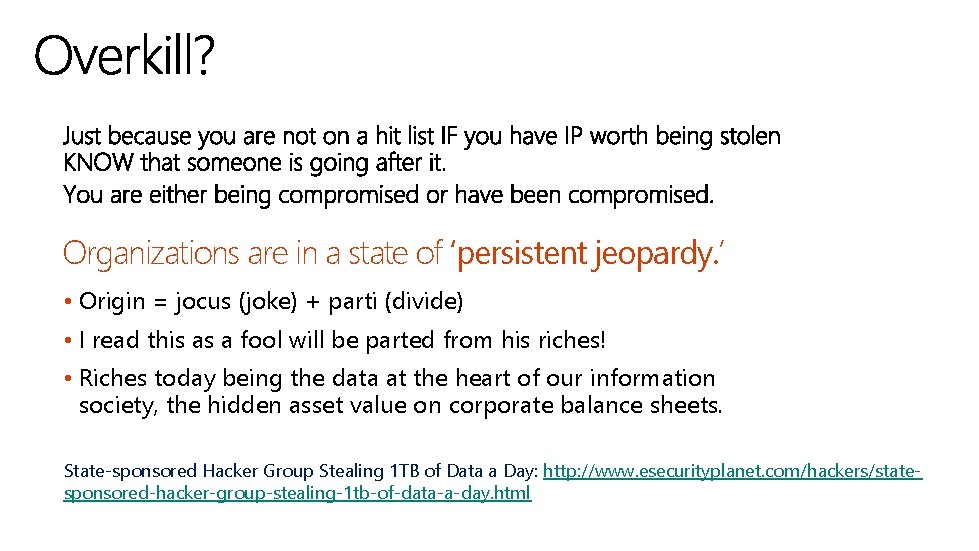
Organizations are in a state of ‘persistent jeopardy. ’ • Origin = jocus (joke) + parti (divide) • I read this as a fool will be parted from his riches! • Riches today being the data at the heart of our information society, the hidden asset value on corporate balance sheets. State-sponsored Hacker Group Stealing 1 TB of Data a Day: http: //www. esecurityplanet. com/hackers/statesponsored-hacker-group-stealing-1 tb-of-data-a-day. html

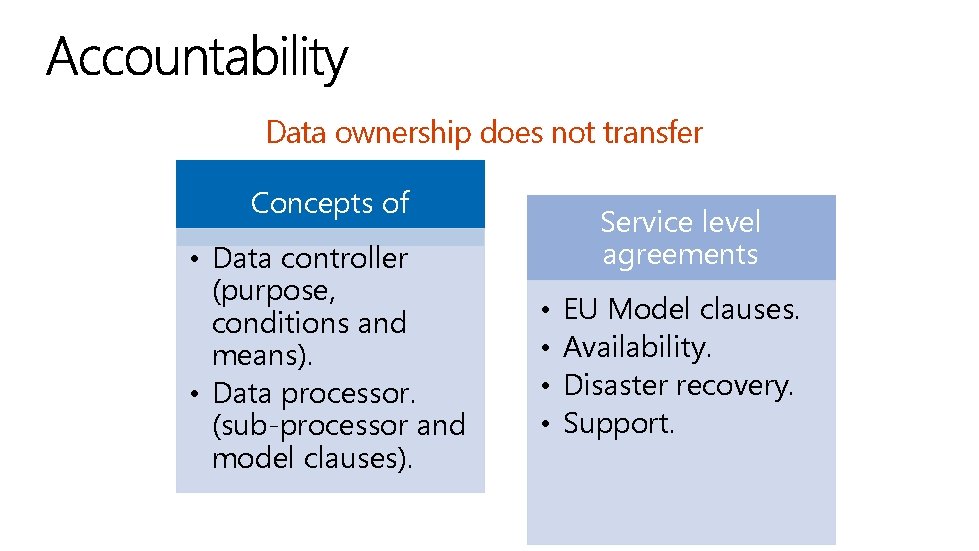
Responsibility Data ownership does not transfer Concepts of • Data controller (purpose, conditions and means). • Data processor. (sub-processor and model clauses). Service level agreements • • EU Model clauses. Availability. Disaster recovery. Support.

Microsoft certification status: CERTIFICATION MARKET REGION
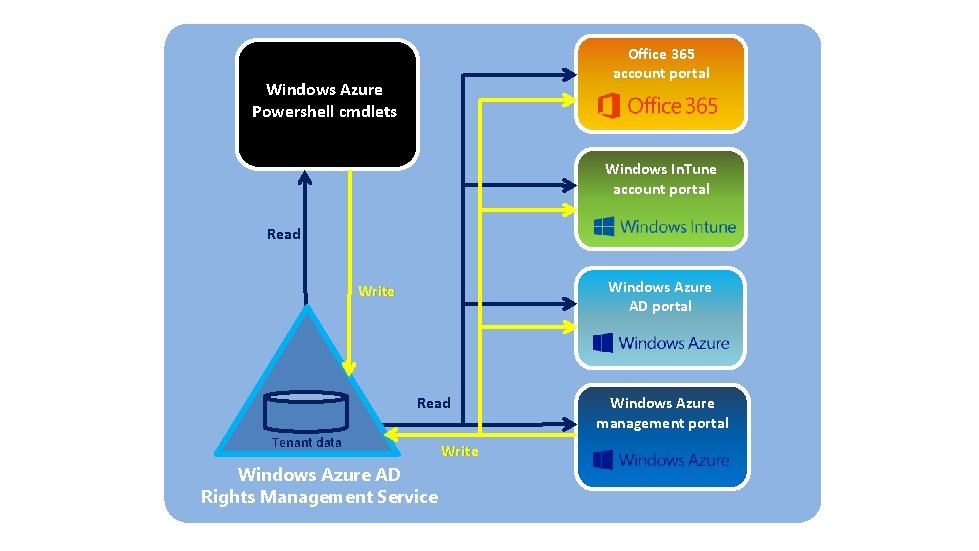
Office 365 account portal Windows Azure Powershell cmdlets Windows In. Tune account portal Read Windows Azure AD portal Write Read Tenant data Windows Azure AD Rights Management Service Write Windows Azure management portal

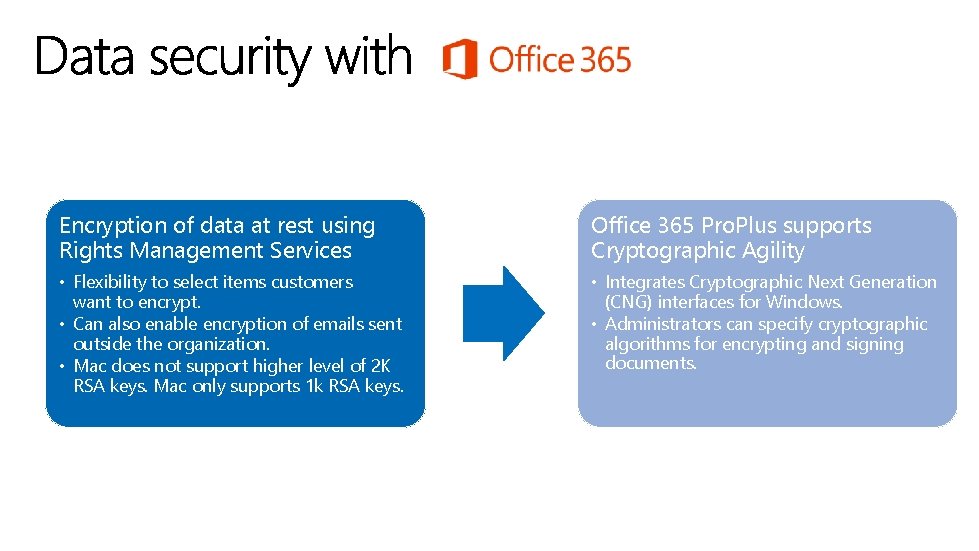
Encryption of data at rest using Rights Management Services Office 365 Pro. Plus supports Cryptographic Agility • Flexibility to select items customers want to encrypt. • Can also enable encryption of emails sent outside the organization. • Mac does not support higher level of 2 K RSA keys. Mac only supports 1 k RSA keys. • Integrates Cryptographic Next Generation (CNG) interfaces for Windows. • Administrators can specify cryptographic algorithms for encrypting and signing documents.
Litéra Corp Litéra offers a comprehensive suite of document lifecycle management solutions: § creation, § comparison, § collaboration, § cleaning § control software
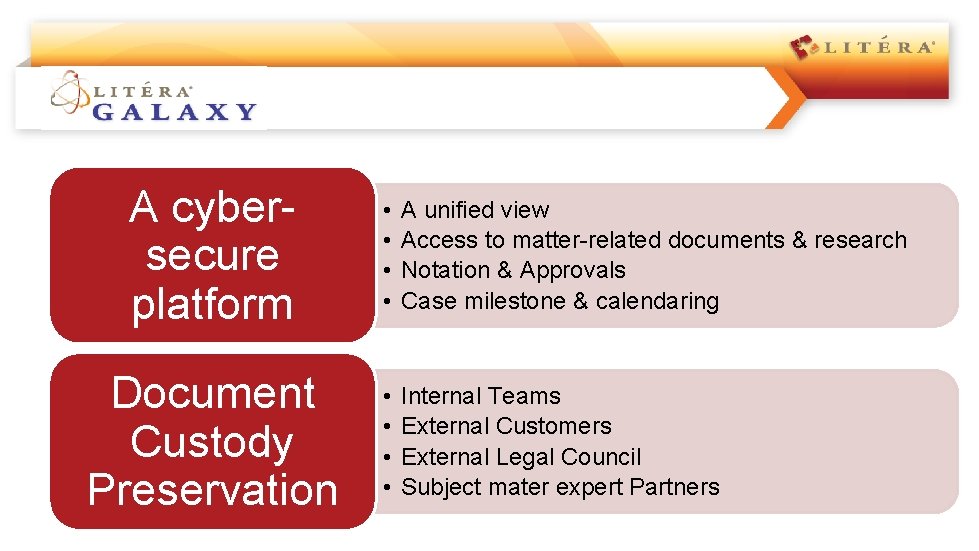
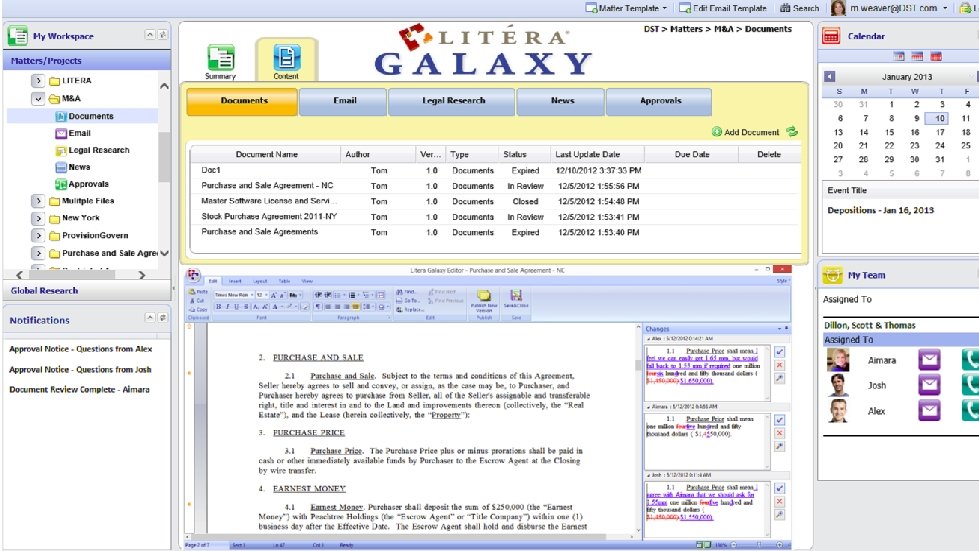
A cybersecure platform • • A unified view Access to matter-related documents & research Notation & Approvals Case milestone & calendaring Document Custody Preservation • • Internal Teams External Customers External Legal Council Subject mater expert Partners
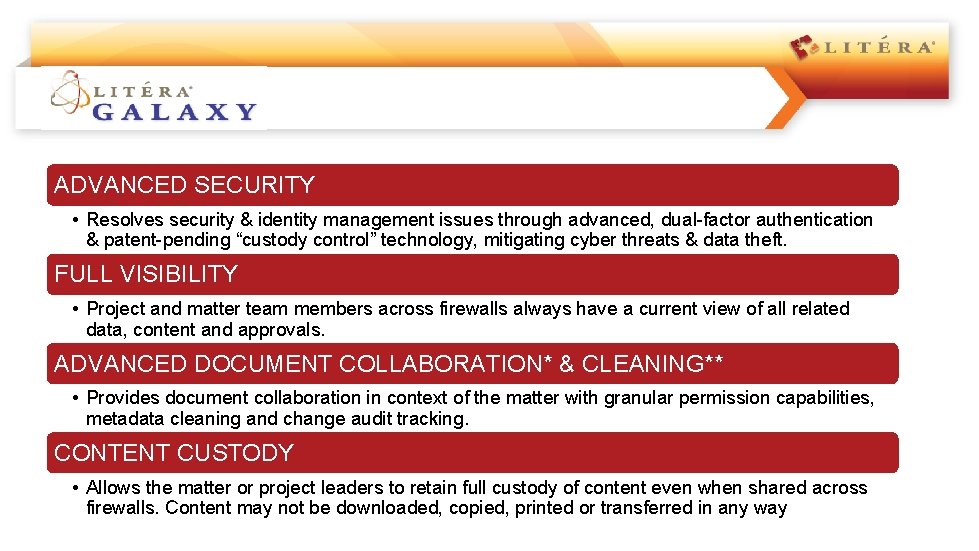
ADVANCED SECURITY • Resolves security & identity management issues through advanced, dual-factor authentication & patent-pending “custody control” technology, mitigating cyber threats & data theft. FULL VISIBILITY • Project and matter team members across firewalls always have a current view of all related data, content and approvals. ADVANCED DOCUMENT COLLABORATION* & CLEANING** • Provides document collaboration in context of the matter with granular permission capabilities, metadata cleaning and change audit tracking. CONTENT CUSTODY • Allows the matter or project leaders to retain full custody of content even when shared across firewalls. Content may not be downloaded, copied, printed or transferred in any way
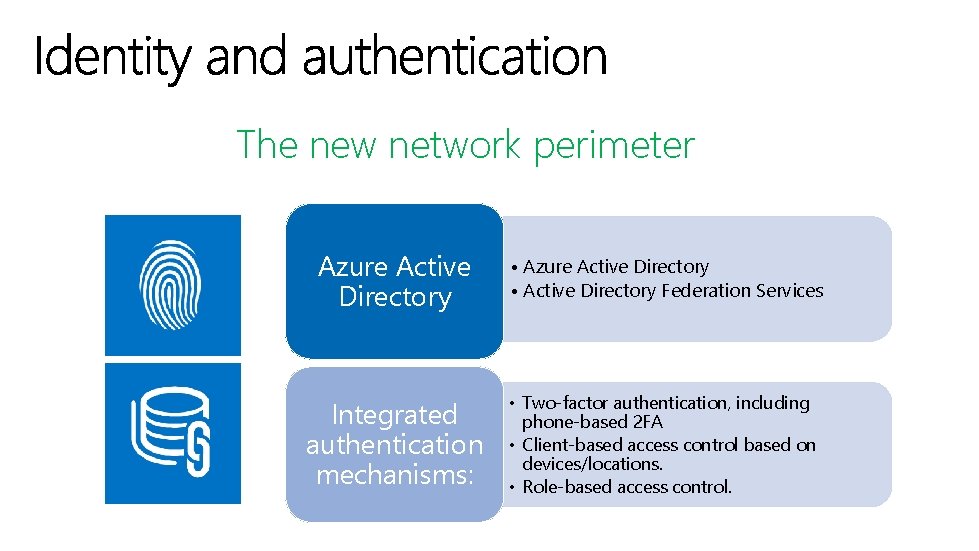
The new network perimeter Azure Active Directory • Azure Active Directory • Active Directory Federation Services Integrated authentication mechanisms: • Two-factor authentication, including phone-based 2 FA • Client-based access control based on devices/locations. • Role-based access control.

Neither is your current IT Same traditional IT security rules apply. New set of skills – IT & business. Game changer: • Access to cheap IT. • Access to Enterprise IT. • Access to professional support resources. Easier to be secure and compliant.



http: //www. windowsazure. com/en-us/support/trust-center/ http: //trust. office 365. com
- Slides: 34