Message Authentication Code July 2011 Message Authentication Problem
Message Authentication Code July 2011
Message Authentication Problem Message Authentication is concerned with: How to detect changes by adversary to message? Ancient solution : protecting the integrity of a message validating identity of originator sign and seal More technique: break to message part and authenticator part (“tag”) How to do this digitally? Create a tag t(M) and send tag securely
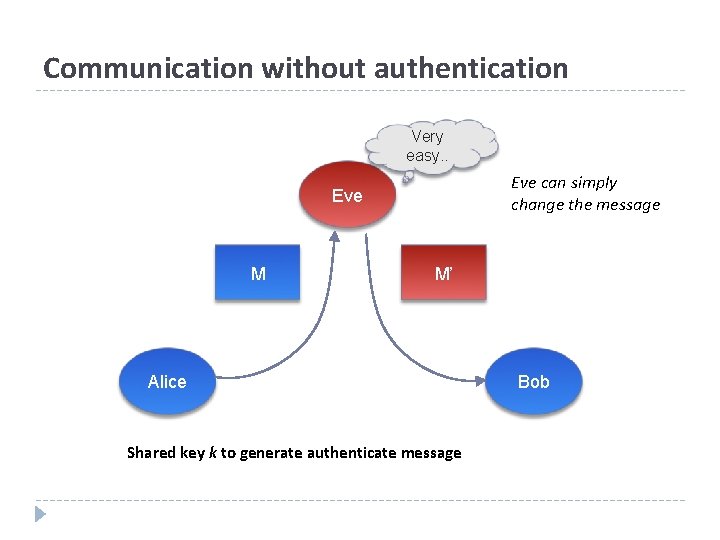
Communication without authentication Very easy. . Eve can simply change the message Eve M M’ Alice Shared key k to generate authenticate message Bob
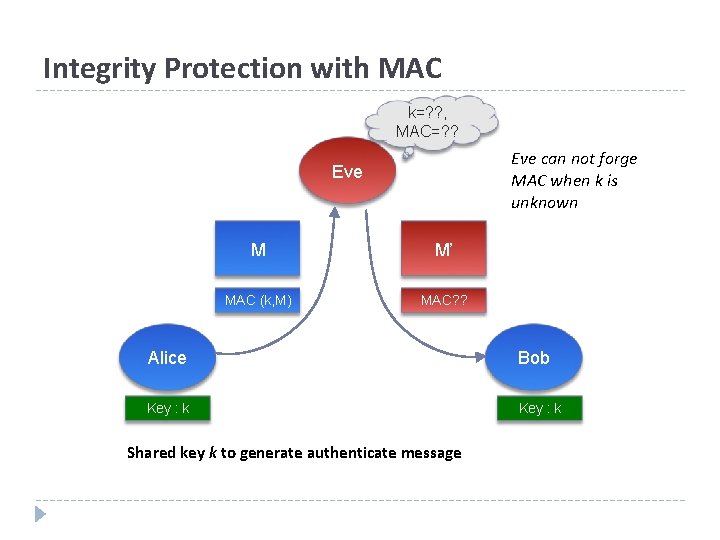
Integrity Protection with MAC k=? ? , MAC=? ? Eve can not forge MAC when k is unknown Eve M M’ MAC (k, M) MAC? ? Alice Bob Key : k Shared key k to generate authenticate message
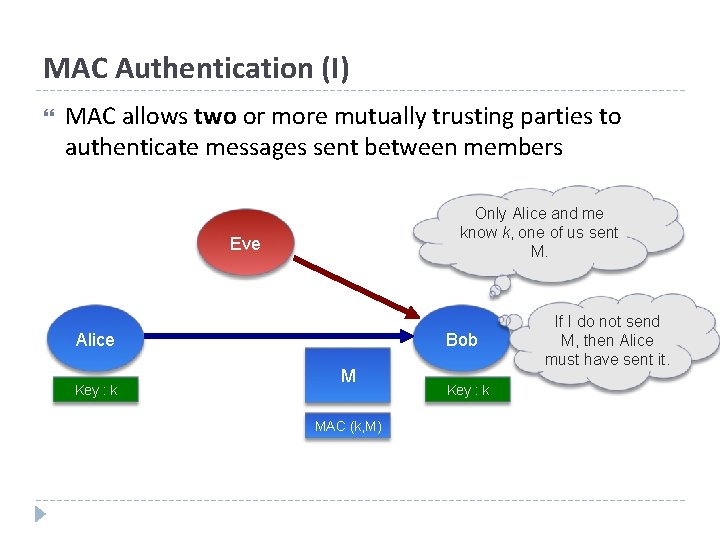
MAC Authentication (I) MAC allows two or more mutually trusting parties to authenticate messages sent between members Only Alice and me know k, one of us sent M. Eve Alice Key : k Bob M MAC (k, M) Key : k If I do not send M, then Alice must have sent it.
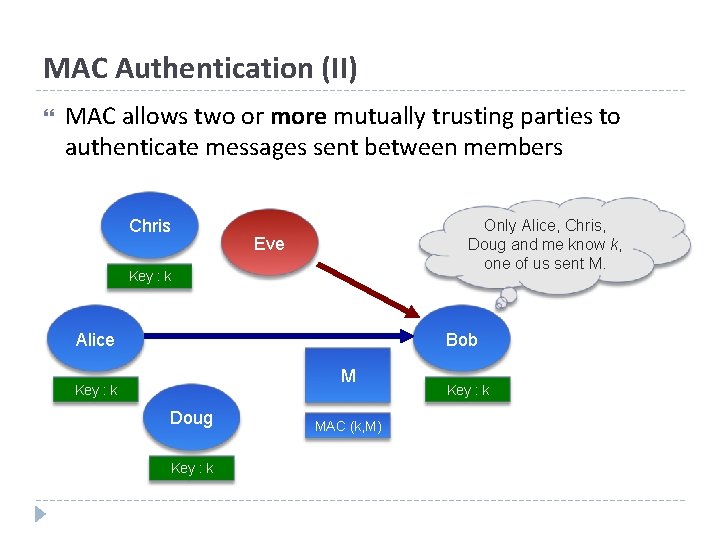
MAC Authentication (II) MAC allows two or more mutually trusting parties to authenticate messages sent between members Chris Only Alice, Chris, Doug and me know k, one of us sent M. Eve Key : k Alice Bob M Key : k Doug Key : k MAC (k, M) Key : k
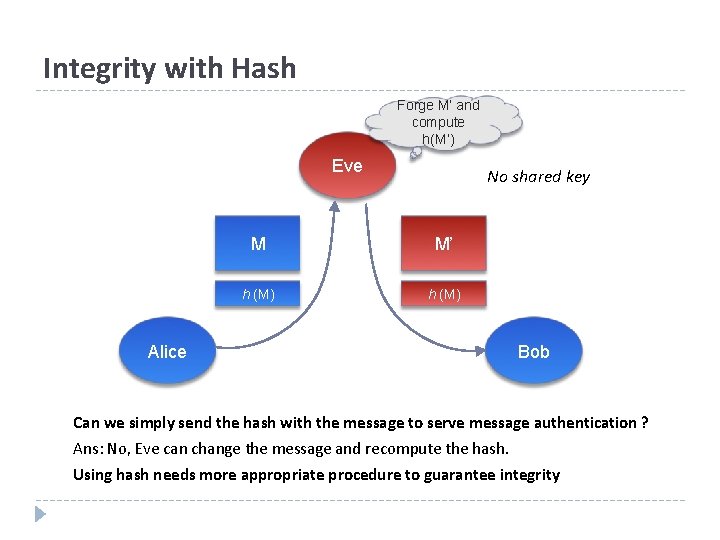
Integrity with Hash Forge M’ and compute h(M’) Eve No shared key M M’ h (M) Alice Bob Can we simply send the hash with the message to serve message authentication ? Ans: No, Eve can change the message and recompute the hash. Using hash needs more appropriate procedure to guarantee integrity
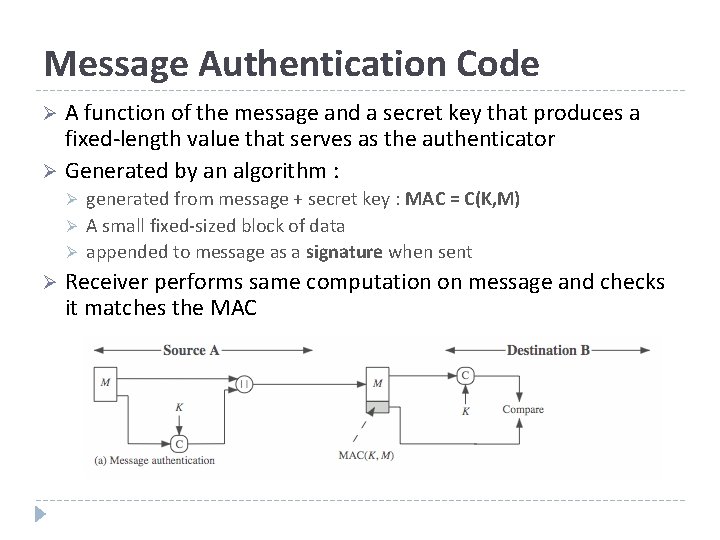
Message Authentication Code A function of the message and a secret key that produces a fixed-length value that serves as the authenticator Ø Generated by an algorithm : Ø Ø Ø generated from message + secret key : MAC = C(K, M) A small fixed-sized block of data appended to message as a signature when sent Receiver performs same computation on message and checks it matches the MAC
MAC and Encryption Ø As shown the MAC provides authentication Ø But encryption can also provides authentication! Ø Why use a MAC? l l sometimes only authentication is needed sometimes need authentication to persist longer than the encryption (eg. archival use) Ø Note that a MAC is not a digital signature
MAC Properties Ø A MAC is a cryptographic checksum l l l MAC = CK(M) condenses a variable-length message M using a secret key K to a fixed-sized authenticator Ø A many-to-one function l l potentially many messages have same MAC but finding these needs to be very difficult
Keyed Hash Functions as MACs Ø Want a MAC based on a hash function l l because hash functions are generally faster crypto hash function code is widely available Ø Need a hashing Ø including a key along with message But hashing is internally has no key! Ø Original proposal: Keyed. Hash = Hash(Key|Message) l some weaknesses were found with this Ø Eventually led to development of HMAC
HMAC Ø Hash-based Message Authentication Code Ø Developed by Mihir Bellare, Ran Canetti, and Hugo Krawczyk in 1996 Ø Specified as Internet standard RFC 2104 Ø Use cryptographic hash function in combination with a secret key Ø Any hash function can be used l l eg. MD 5, SHA-1, RIPEMD-160, Whirlpool HMAC-MD 5, HMAC-SHA 1, HMAC-RIPEND-160, HMACWhirlpool Ø HMAC-SHA 1 and HMAC-MD 5 are used within the IPsec and TLS protocols
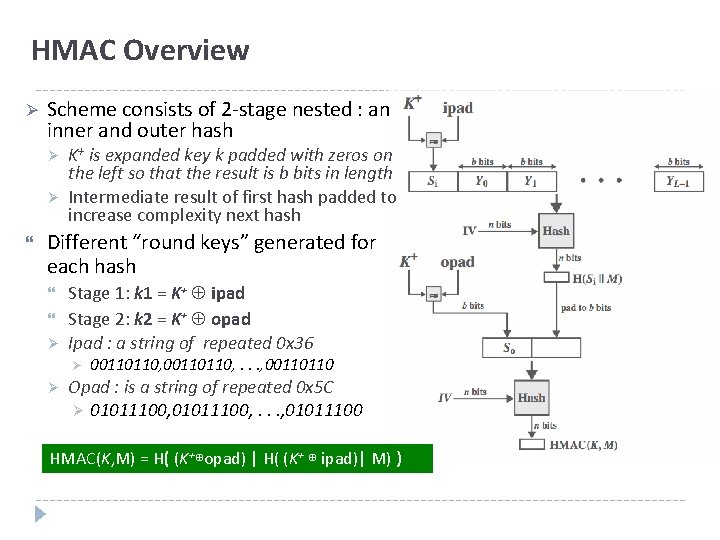
HMAC Overview Ø Scheme consists of 2 -stage nested : an inner and outer hash Ø Ø K+ is expanded key k padded with zeros on the left so that the result is b bits in length Intermediate result of first hash padded to increase complexity next hash Different “round keys” generated for each hash Ø Stage 1: k 1 = K+ ipad Stage 2: k 2 = K+ opad Ipad : a string of repeated 0 x 36 Ø Ø 00110110, . . . , 00110110 Opad : is a string of repeated 0 x 5 C Ø 01011100, . . . , 01011100 HMAC(K, M) = H( (K+⊕opad) | H( (K+ ⊕ ipad)| M) )
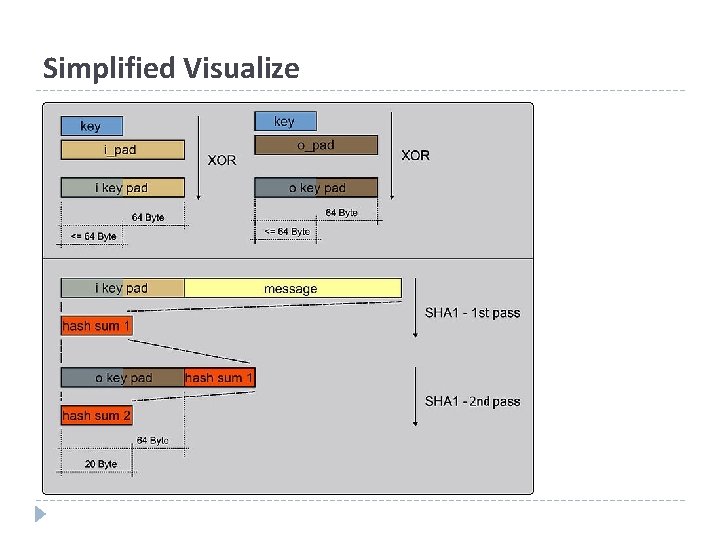
Simplified Visualize
CMAC (Cipher-based MAC) “Hashless” MAC Uses an encryption algorithm (DES, AES, etc. ) to generate MAC Based on same idea as cipher block chaining Compresses result to size of single block (unlike encryption
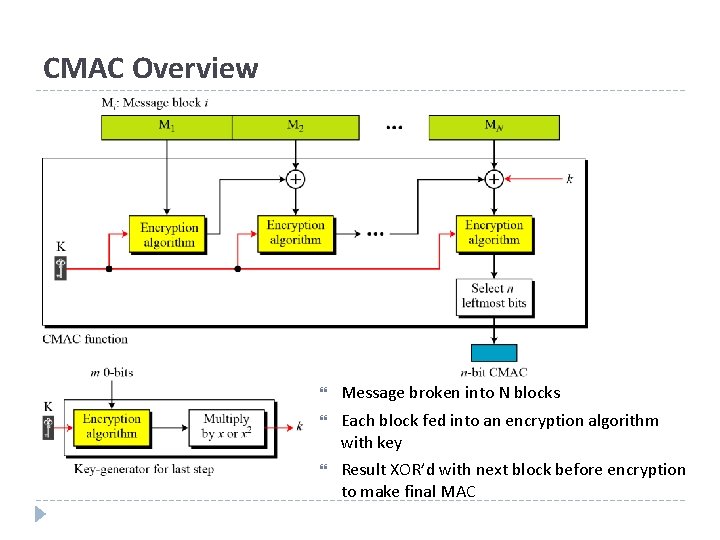
CMAC Overview Message broken into N blocks Each block fed into an encryption algorithm with key Result XOR’d with next block before encryption to make final MAC
CMAC Facts Advantages: Can use existing encryption functions Encryption functions have properties that resist preimage and collision attacks Ciphertext designed to appear like “random noise” – good approximation of random oracle model Most exhibit strong avalanche effect – minor change in message gives great change in resulting MAC Disadvantage: 17 Encryption algorithms (particularly when chained) can be much slower than hash algorithms
Summary Ø A Hash is used to guarantee the integrity of data, a MAC guarantees integrity AND authentication Ø A Hash take a single input – a message and produces a message digest Ø A MAC algorithm takes two inputs -- a message and a secret key -- and produces a MAC Ø A HMAC algorithm is simply a specific type of MAC algorithm that uses a hash algorithm internally to generate the MAC Ø A CMAC algorithm is a specific type of MAC algorithm that uses a block cipher internally to generate the MAC
- Slides: 18