Memory management Linux Memory Management Total memory available
Memory management
Linux Memory Management • Total memory available for processes = real memory + paging space - 1 MB. • First megabyte of real memory is used for kernel program and kernel data -> not for applications. – A bz. Image kernel might use more than 1 MB. • Rest is used for processes. • Pages in real memory will be paged out to disk if necessary. • Unused real memory will be used for disk caching. • The maximum amount of usable memory (on intel -32) is 4 GB (if kernel supports it)
Example: Lightly Loaded System • On a lightly loaded system – All processes will fit in real memory – Real memory will be left which will be used to cache data on disk to reduce data access time
Example: Heavily Loaded System • On a heavily loaded system – less often used process will be swapped out to disk ( paging space) – Only most often used processes will be in memory • Linux uses a very efficient and effective, but non-tunable algorithm to decide whether to give up caching space or to swap out processes if real memory becomes full.
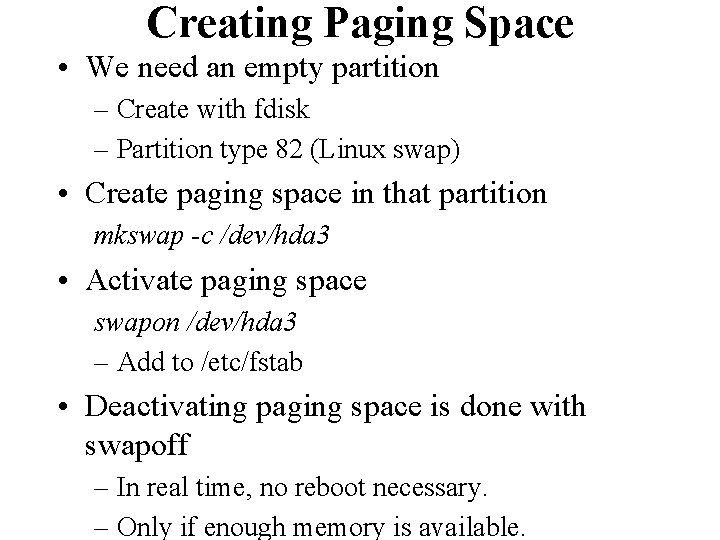
Creating Paging Space • We need an empty partition – Create with fdisk – Partition type 82 (Linux swap) • Create paging space in that partition mkswap -c /dev/hda 3 • Activate paging space swapon /dev/hda 3 – Add to /etc/fstab • Deactivating paging space is done with swapoff – In real time, no reboot necessary. – Only if enough memory is available.
Creating Paging Space • Paging can also be done to a file (less efficient) – Create a large file and use it as if it were a partition

Useful Commands • top : displays memory, CPU process statistics continuously • uptime : displays system uptime + load • free : displays memory statistics • ps : displays processes • sync : flushes the cache to disk • xload : graphically displays system load
Backup & Restore
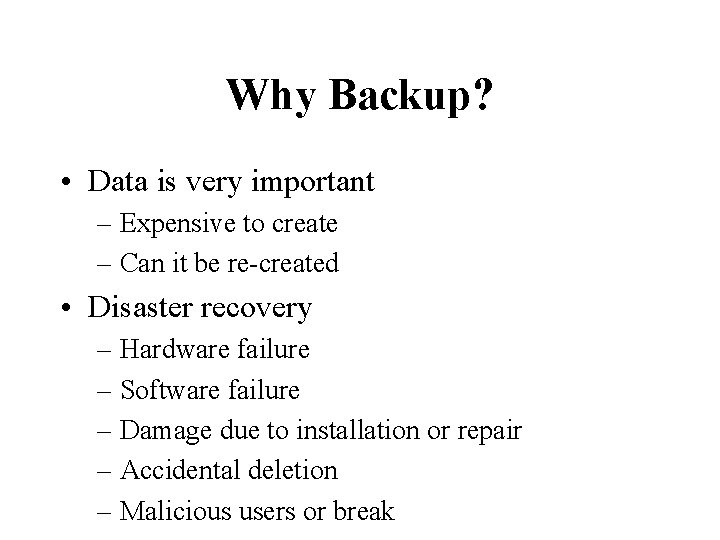
Why Backup? • Data is very important – Expensive to create – Can it be re-created • Disaster recovery – Hardware failure – Software failure – Damage due to installation or repair – Accidental deletion – Malicious users or break
Why Backup? (Cont’d) • Long-term archive • System Administration – Transfer of data between systems – Reorganizing file system – Defragmentation – Checkpoint before and after an upgrade
Why Restore? • • • Recover files Compare versions of files Recover system after disaster Restore archived data Shrink file systems

Three Types of Backup • System backup – Preserves system directories and files • Full backup – Preserves all user data and configuration files • Incremental backup – Records changes since last full backup or last incremental backup – very fast, but takes more time to restore – must be used carefully – Needs more tapes
Backup Strategy (1) Normal Working System • System Backup -> Full Backup -> Incremental Backup ->. . . • Note: Each organisation has its own special considerations concerning data to take into account.
Backup Strategy (1) • In practice you would want to exclude certain directories from the backup process. Some of the directories being – /tmp – /var/tmp – /usr/tmp • Not backing up these directories saves space on the archives
Backup Strategy (1) • Do not backup /proc even if it exists on your system. The /proc filesystem is not a disk file system but is a way for the kernel to provide you with information about the operating system and system memory. You cannot restore it later.

Backup Strategy (2) • Back up everything which has changed since last system backup: – All user data – All changed system files – All changed application files • Do not back up: – Unchanged application files – Software quickly loaded from tape
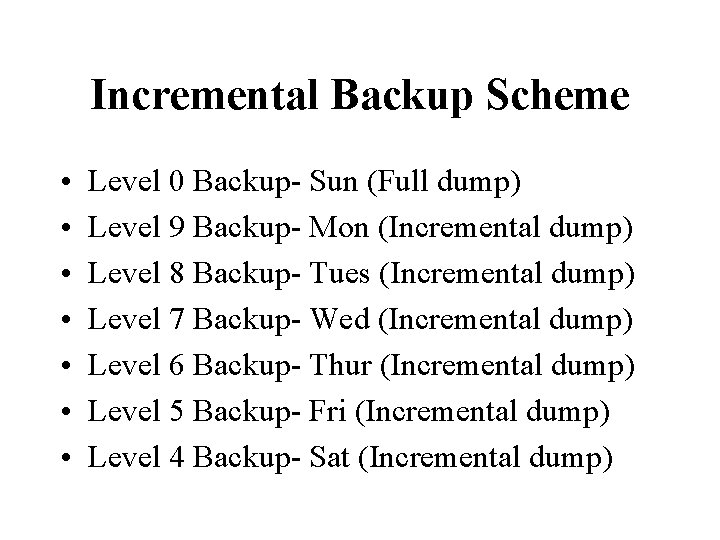
Incremental Backup Scheme • • Level 0 Backup- Sun (Full dump) Level 9 Backup- Mon (Incremental dump) Level 8 Backup- Tues (Incremental dump) Level 7 Backup- Wed (Incremental dump) Level 6 Backup- Thur (Incremental dump) Level 5 Backup- Fri (Incremental dump) Level 4 Backup- Sat (Incremental dump)
Backup Devices • • • Tape drive CD-ROM Hard disk Diskette drive ZIP drive Network
Backup Commands • tar – Widely available – Excellent for transferring data between platforms – Beware of empty directories (-d option) • cpio – Widely available – Difficulties with many symbolic links
Backup Commands • dd – Not a real backup command – Copies are exact images – Can be used for conversions
tar command • Traditional UNIX tape archive command – Performs backup and restore • Backup with tar: tar cvf <device> [files | dir] tar cvf /dev/fd 0 /home tar cvf /mnt/hda 8/filename. tar /home
![tar command • Restore with tar: tar -xvf device [files|dir] tar -xvf /dev/fd 0 tar command • Restore with tar: tar -xvf device [files|dir] tar -xvf /dev/fd 0](http://slidetodoc.com/presentation_image_h/acb33407e26f9a3bd9af14b782fe48bb/image-22.jpg)
tar command • Restore with tar: tar -xvf device [files|dir] tar -xvf /dev/fd 0 "/home/ j*" • List contents of a tar backup: tar -tvf <device>

cpio Command • Common UNIX backup command • Backup with cpio: cpio -ov <files> > <device> find /home | cpio -ov > /dev /fd 0
![cpio Command • Restore with cpio: cpio -iv[-dum] [files] < <device> cpio -ivdum " cpio Command • Restore with cpio: cpio -iv[-dum] [files] < <device> cpio -ivdum "](http://slidetodoc.com/presentation_image_h/acb33407e26f9a3bd9af14b782fe48bb/image-24.jpg)
cpio Command • Restore with cpio: cpio -iv[-dum] [files] < <device> cpio -ivdum " /home/ j*" < /dev/fd 0 • List contents of a cpio backups: cpio -itv < <device> cpio itv < /dev/fd 0
dd Command • Not a real backup command • Converts and copies files – dd reads the infile parameter, does the specified conversions – Copies the converted data to the outfile parameter
dd Command • Examples: – Makes a backup of /etc/passwd dd if = /etc/passwd of = /dev /rfd 0 – Displays the long list of the current directory in uppercase ls -l | dd conv = ucase
- Slides: 26