Measuring DNSSEC Geoff Huston George Michaelson APNICLabs February
Measuring DNSSEC Geoff Huston & George Michaelson APNICLabs February 2012
What is DNSSEC? lide s e e on n) io vers (th • DNSSEC adds digital signatures to the responses generated by authoritative servers for a zone • A validating DNS resolver can use this signature to verify that the response has not been altered or tampered with in any way • DNSSEC uses the key used to sign the root of the DNS as its Trust Anchor • Signature Validation in DNSSEC establishes a sequence of overlapping digital signatures from the Trust Anchor to the signature being verified • DNSSEC uses some new RRs to contain digital signatures, public keys and key hashes
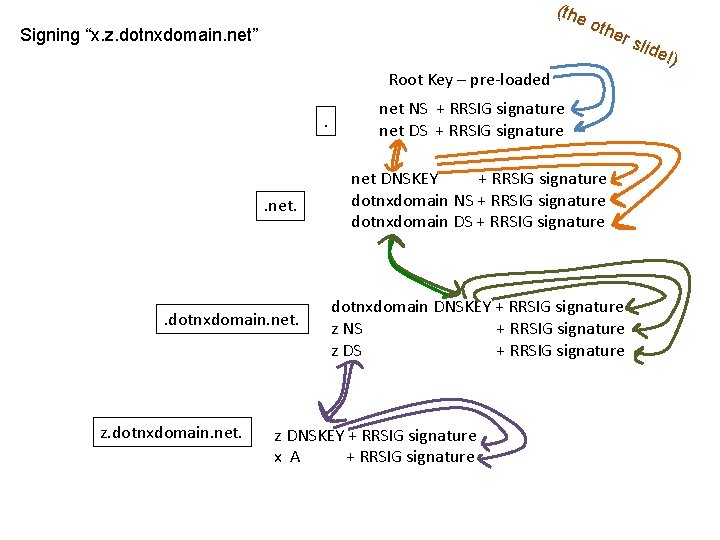
(the Signing “x. z. dotnxdomain. net” oth er s Root Key – pre-loaded. . net. . dotnxdomain. net. z. dotnxdomain. net NS + RRSIG signature net DNSKEY + RRSIG signature dotnxdomain NS + RRSIG signature dotnxdomain DNSKEY + RRSIG signature z NS + RRSIG signature z DNSKEY + RRSIG signature x A + RRSIG signature lide !)
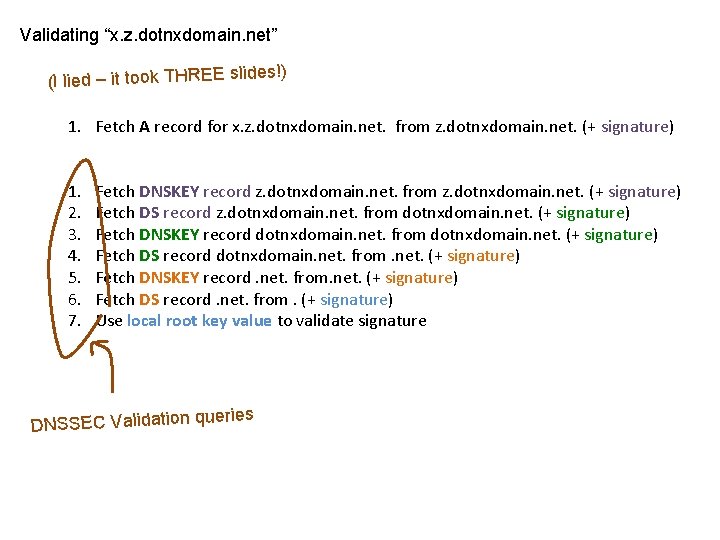
Validating “x. z. dotnxdomain. net” (I lied – it took THREE slid es!) 1. Fetch A record for x. z. dotnxdomain. net. from z. dotnxdomain. net. (+ signature) 1. 2. 3. 4. 5. 6. 7. Fetch DNSKEY record z. dotnxdomain. net. from z. dotnxdomain. net. (+ signature) Fetch DS record z. dotnxdomain. net. from dotnxdomain. net. (+ signature) Fetch DNSKEY record dotnxdomain. net. from dotnxdomain. net. (+ signature) Fetch DS record dotnxdomain. net. from. net. (+ signature) Fetch DNSKEY record. net. from. net. (+ signature) Fetch DS record. net. from. (+ signature) Use local root key value to validate signature ueries DNSSEC Validation q
What are the questions? 1. What proportion of DNS resolvers are DNSSEC-capable? 2. What proportion of users are using DNSSECvalidating DNS resolvers? 3. Where are these users? 4. How long does DNSSEC validation take for a client?
The Experiment • Use code embedded in an online ad to retrieve a set of URLs • Embed the unique id generation and the ad control in flash code: – Retrieve three URLs, all with a unique domain name: • one from a DNSSEC-signed domain, validly signed, • one from a DNSSEC-signed domain with an invalid DS record, and • one from a non-DNSSEC domain) – Use a 10 second timer to POST results to the server (to distinguish between incomplete and completed test runs) • Enrol an online advertisement network to display the ad • The underlying code and the retrieval of the image is executed as part of the ad display function – No user click-through is required! (or wanted!)
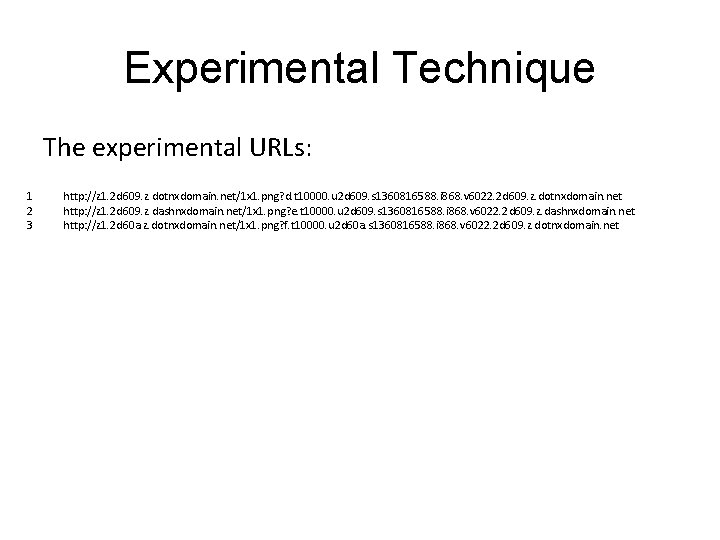
Experimental Technique The experimental URLs: 1 2 3 http: //z 1. 2 d 609. z. dotnxdomain. net/1 x 1. png? d. t 10000. u 2 d 609. s 1360816588. i 868. v 6022. 2 d 609. z. dotnxdomain. net http: //z 1. 2 d 609. z. dashnxdomain. net/1 x 1. png? e. t 10000. u 2 d 609. s 1360816588. i 868. v 6022. 2 d 609. z. dashnxdomain. net http: //z 1. 2 d 60 a. z. dotnxdomain. net/1 x 1. png? f. t 10000. u 2 d 60 a. s 1360816588. i 868. v 6022. 2 d 609. z. dotnxdomain. net
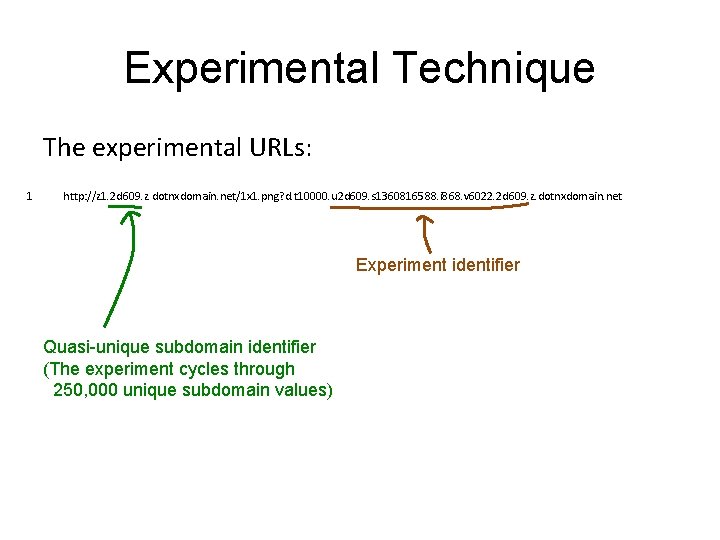
Experimental Technique The experimental URLs: 1 http: //z 1. 2 d 609. z. dotnxdomain. net/1 x 1. png? d. t 10000. u 2 d 609. s 1360816588. i 868. v 6022. 2 d 609. z. dotnxdomain. net Experiment identifier Quasi-unique subdomain identifier (The experiment cycles through 250, 000 unique subdomain values)
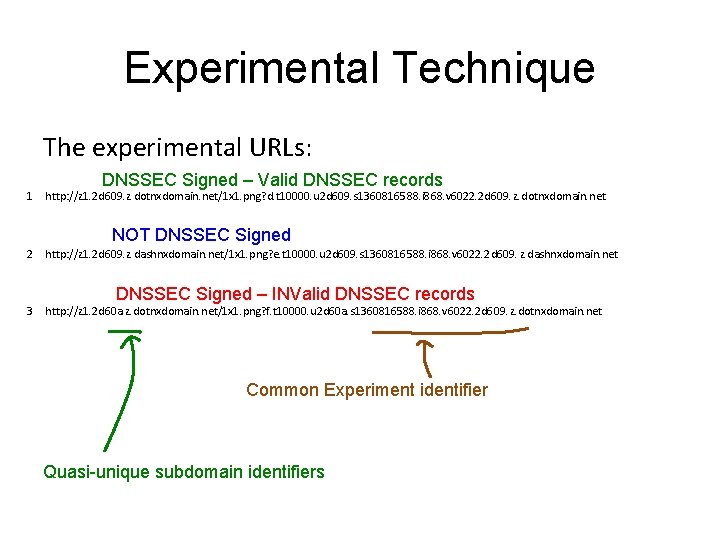
Experimental Technique The experimental URLs: DNSSEC Signed – Valid DNSSEC records 1 http: //z 1. 2 d 609. z. dotnxdomain. net/1 x 1. png? d. t 10000. u 2 d 609. s 1360816588. i 868. v 6022. 2 d 609. z. dotnxdomain. net NOT DNSSEC Signed 2 http: //z 1. 2 d 609. z. dashnxdomain. net/1 x 1. png? e. t 10000. u 2 d 609. s 1360816588. i 868. v 6022. 2 d 609. z. dashnxdomain. net DNSSEC Signed – INValid DNSSEC records 3 http: //z 1. 2 d 60 a. z. dotnxdomain. net/1 x 1. png? f. t 10000. u 2 d 60 a. s 1360816588. i 868. v 6022. 2 d 609. z. dotnxdomain. net Common Experiment identifier Quasi-unique subdomain identifiers
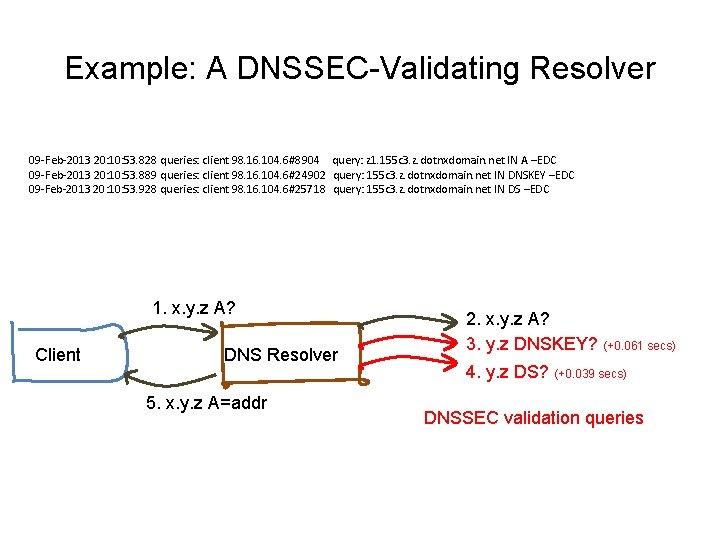
Example: A DNSSEC-Validating Resolver 09 -Feb-2013 20: 10: 53. 828 queries: client 98. 16. 104. 6#8904 query: z 1. 155 c 3. z. dotnxdomain. net IN A –EDC 09 -Feb-2013 20: 10: 53. 889 queries: client 98. 16. 104. 6#24902 query: 155 c 3. z. dotnxdomain. net IN DNSKEY –EDC 09 -Feb-2013 20: 10: 53. 928 queries: client 98. 16. 104. 6#25718 query: 155 c 3. z. dotnxdomain. net IN DS –EDC 1. x. y. z A? Client DNS Resolver 5. x. y. z A=addr 2. x. y. z A? 3. y. z DNSKEY? (+0. 061 secs) 4. y. z DS? (+0. 039 secs) DNSSEC validation queries
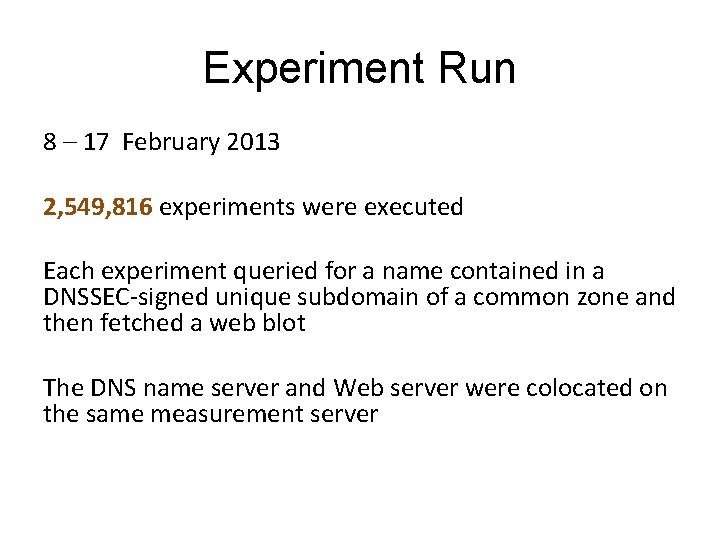
Experiment Run 8 – 17 February 2013 2, 549, 816 experiments were executed Each experiment queried for a name contained in a DNSSEC-signed unique subdomain of a common zone and then fetched a web blot The DNS name server and Web server were colocated on the same measurement server
DNS Resolvers • How many unique IP addresses queried for experiment domains in dotnxdomain. net? • How many of these DNS resolvers also queried for the DNSKEY RR of dotnxdomain. net?
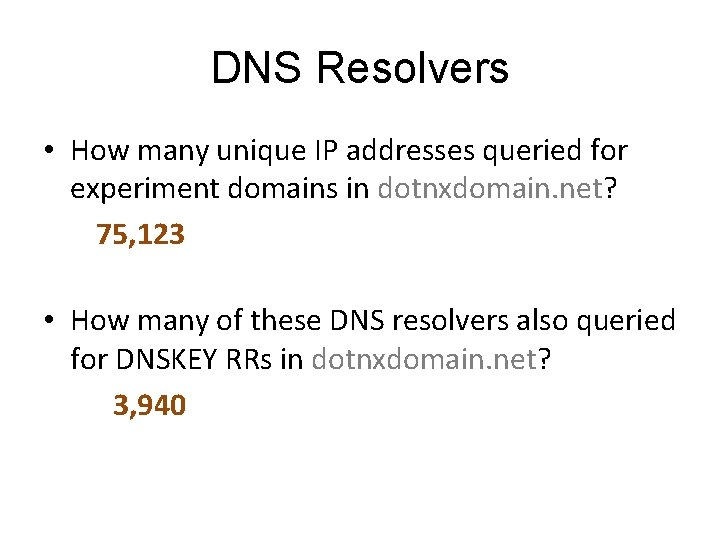
DNS Resolvers • How many unique IP addresses queried for experiment domains in dotnxdomain. net? 75, 123 • How many of these DNS resolvers also queried for DNSKEY RRs in dotnxdomain. net? 3, 940
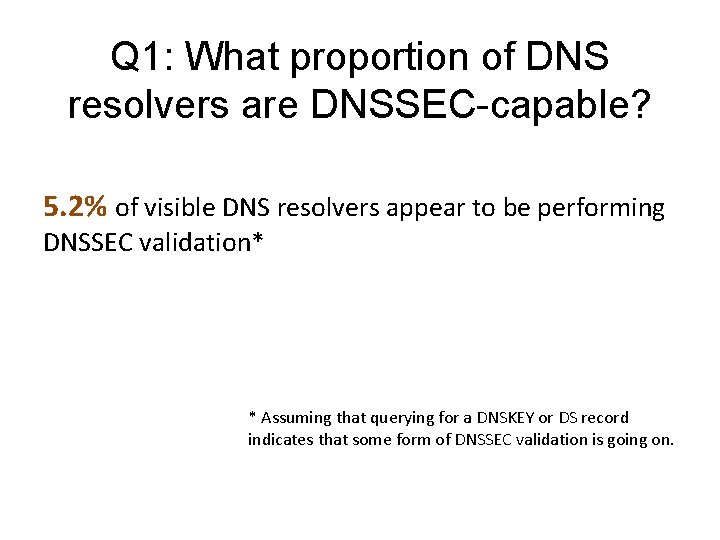
Q 1: What proportion of DNS resolvers are DNSSEC-capable? 5. 2% of visible DNS resolvers appear to be performing DNSSEC validation* * Assuming that querying for a DNSKEY or DS record indicates that some form of DNSSEC validation is going on.
A simple view of the DNS Client DNS Resolver Server
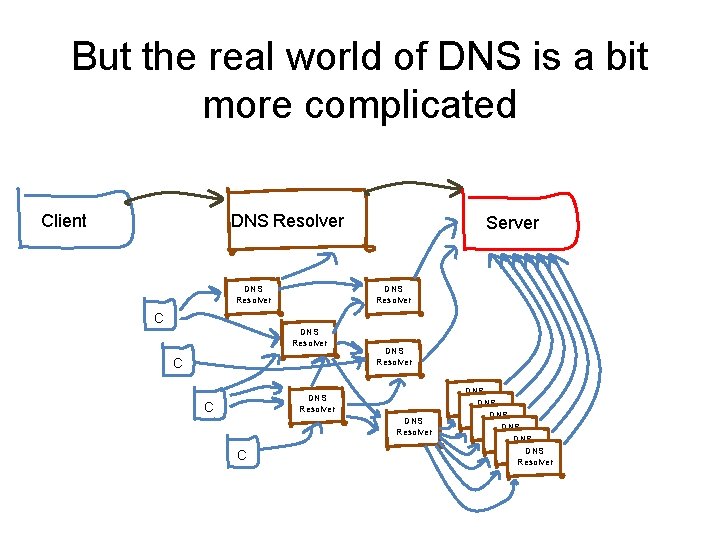
But the real world of DNS is a bit more complicated Client DNS Resolver Server DNS Resolver C DNS Resolver DNS Resolver
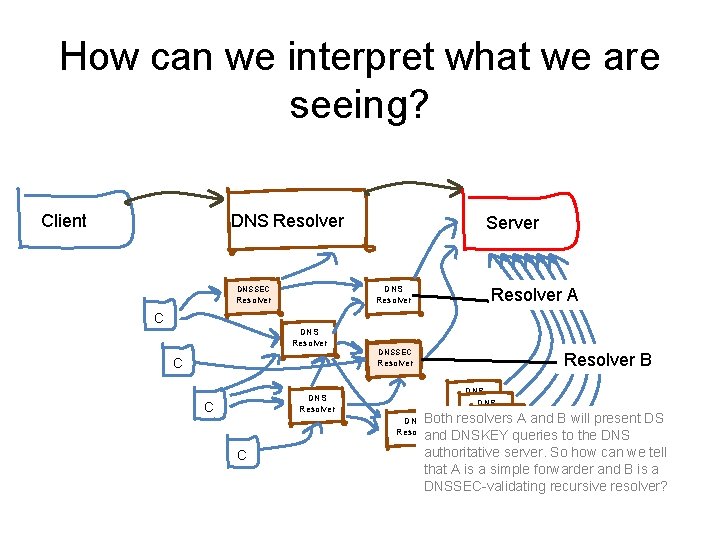
How can we interpret what we are seeing? Client DNS Resolver DNSSEC Resolver Server DNS Resolver A C DNS Resolver C C DNSSEC Resolver B DNS Resolver DNS Both resolvers A and B will present DS Resolver DNS Resolver and DNSKEY queries to the DNS Resolver DNS authoritative server. So how can we tell Resolver that A is a simple forwarder and B is a DNSSEC-validating recursive resolver?
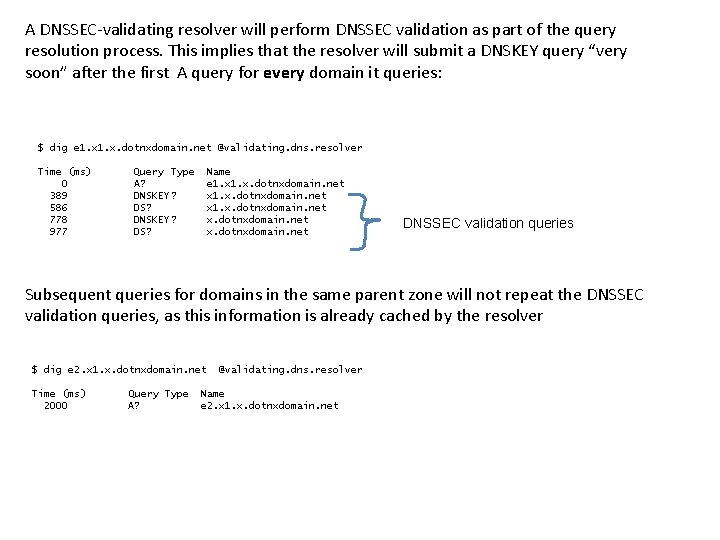
A DNSSEC-validating resolver will perform DNSSEC validation as part of the query resolution process. This implies that the resolver will submit a DNSKEY query “very soon” after the first A query for every domain it queries: $ dig e 1. x. dotnxdomain. net @validating. dns. resolver Time (ms) 0 389 586 778 977 Query Type A? DNSKEY? DS? Name e 1. x. dotnxdomain. net x. dotnxdomain. net DNSSEC validation queries Subsequent queries for domains in the same parent zone will not repeat the DNSSEC validation queries, as this information is already cached by the resolver $ dig e 2. x 1. x. dotnxdomain. net Time (ms) 2000 Query Type A? @validating. dns. resolver Name e 2. x 1. x. dotnxdomain. net
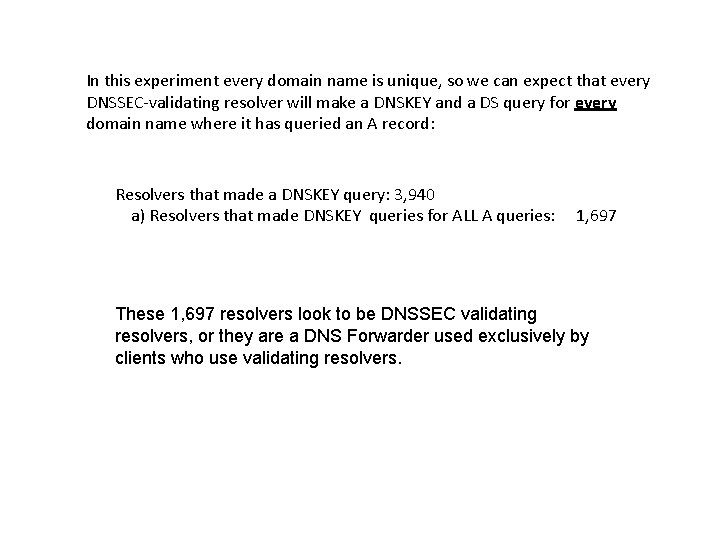
In this experiment every domain name is unique, so we can expect that every DNSSEC-validating resolver will make a DNSKEY and a DS query for every domain name where it has queried an A record: Resolvers that made a DNSKEY query: 3, 940 a) Resolvers that made DNSKEY queries for ALL A queries: 1, 697 These 1, 697 resolvers look to be DNSSEC validating resolvers, or they are a DNS Forwarder used exclusively by clients who use validating resolvers.
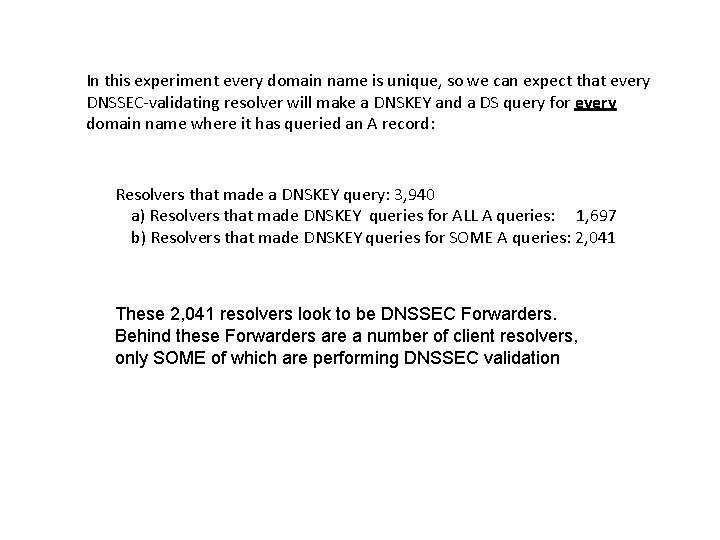
In this experiment every domain name is unique, so we can expect that every DNSSEC-validating resolver will make a DNSKEY and a DS query for every domain name where it has queried an A record: Resolvers that made a DNSKEY query: 3, 940 a) Resolvers that made DNSKEY queries for ALL A queries: 1, 697 b) Resolvers that made DNSKEY queries for SOME A queries: 2, 041 These 2, 041 resolvers look to be DNSSEC Forwarders. Behind these Forwarders are a number of client resolvers, only SOME of which are performing DNSSEC validation
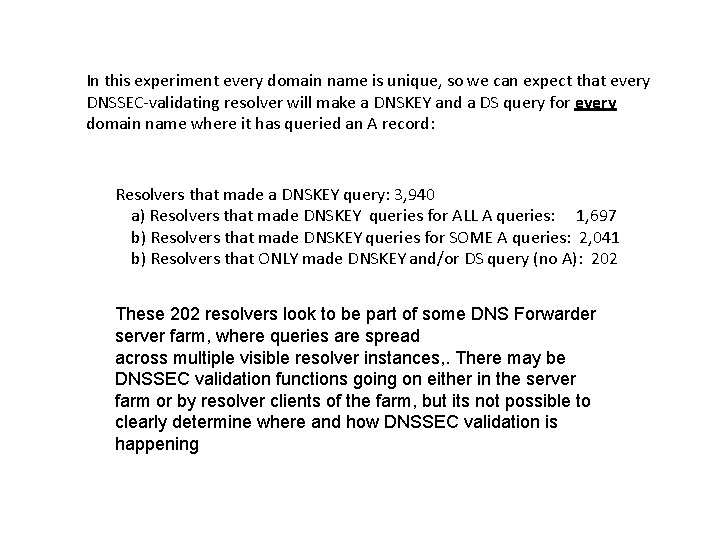
In this experiment every domain name is unique, so we can expect that every DNSSEC-validating resolver will make a DNSKEY and a DS query for every domain name where it has queried an A record: Resolvers that made a DNSKEY query: 3, 940 a) Resolvers that made DNSKEY queries for ALL A queries: 1, 697 b) Resolvers that made DNSKEY queries for SOME A queries: 2, 041 b) Resolvers that ONLY made DNSKEY and/or DS query (no A): 202 These 202 resolvers look to be part of some DNS Forwarder server farm, where queries are spread across multiple visible resolver instances, . There may be DNSSEC validation functions going on either in the server farm or by resolver clients of the farm, but its not possible to clearly determine where and how DNSSEC validation is happening
Spot the Difference. . . How can we tell the difference between a DNSSEC-capable DNS Recursive Resolver and a DNS Forwarder? Count only those resolvers who issue DS and DNSKEY queries following a query for the A record of the DNS name all of the time.
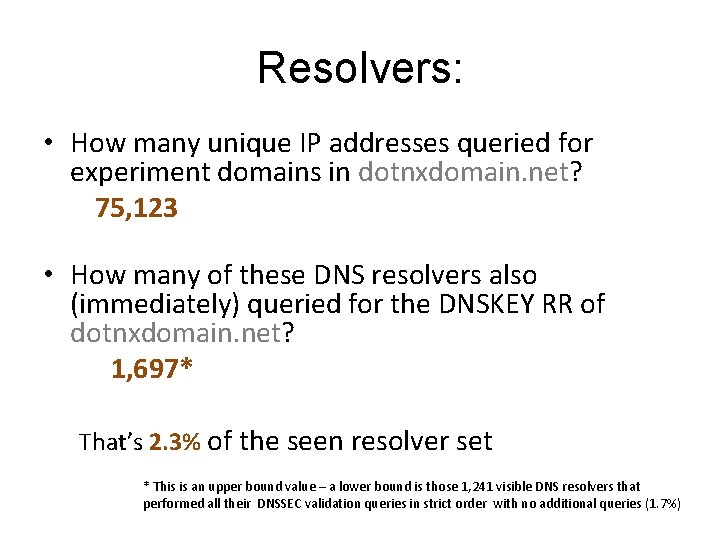
Resolvers: • How many unique IP addresses queried for experiment domains in dotnxdomain. net? 75, 123 • How many of these DNS resolvers also (immediately) queried for the DNSKEY RR of dotnxdomain. net? 1, 697* That’s 2. 3% of the seen resolver set * This is an upper bound value – a lower bound is those 1, 241 visible DNS resolvers that performed all their DNSSEC validation queries in strict order with no additional queries (1. 7%)
Who does DNSSEC Validation? We see both large-scale resolvers used by many clients (such as Google’s Open DNS resolvers) and small-scale resolvers used by a single client Is DNSSEC validation more prevalent in large or small resolvers?
“Small-scale” Resolvers Look at those resolvers that are associated with 10 or fewer clients How many “small” resolvers were seen: 54, 014 How many perform DNSSEC validation: 1, 226 What’s the DNSSEC-active proportion of these resolvers: 2. 3%
“Larger” Resolvers: Look at those resolvers that are associated with more than 10 clients How many “big” resolvers were seen: How many perform DNSSEC validation: 19, 935 399 What’s the DNSSEC-validating proportion of these resolvers: 2. 0%
“Infrastructure” Resolvers: Look at those resolvers that are associated with more than 1, 000 clients How many “very big” resolvers were seen: 1, 241 How many perform DNSSEC validation: 0 What’s the DNSSEC-validating proportion of these resolvers: 0. 0%
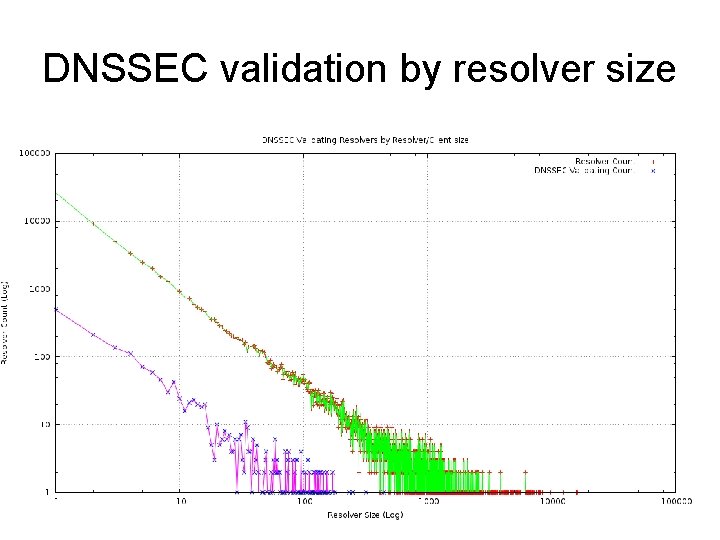
DNSSEC validation by resolver size
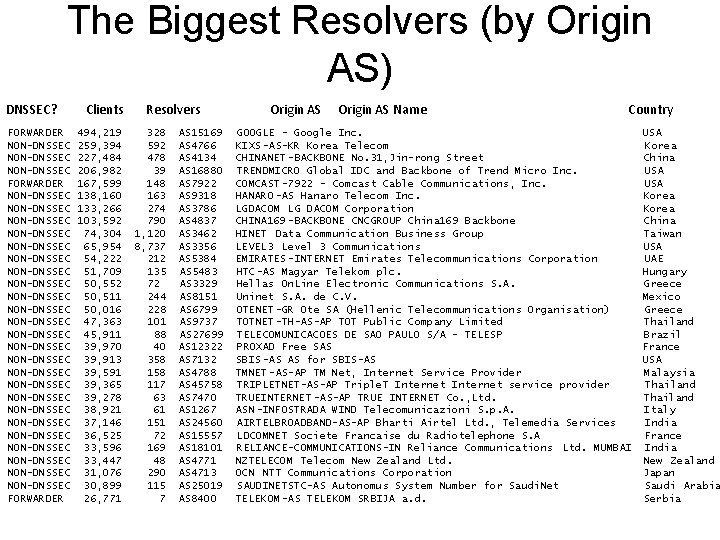
The Biggest Resolvers (by Origin AS) DNSSEC? FORWARDER NON-DNSSEC NON-DNSSEC NON-DNSSEC NON-DNSSEC NON-DNSSEC NON-DNSSEC NON-DNSSEC FORWARDER Clients 494, 219 259, 394 227, 484 206, 982 167, 599 138, 160 133, 266 103, 592 74, 304 65, 954 54, 222 51, 709 50, 552 50, 511 50, 016 47, 363 45, 911 39, 970 39, 913 39, 591 39, 365 39, 278 38, 921 37, 146 36, 525 33, 596 33, 447 31, 076 30, 899 26, 771 Resolvers 328 592 478 39 148 163 274 790 1, 120 8, 737 212 135 72 244 228 101 88 40 358 117 63 61 151 72 169 48 290 115 7 AS 15169 AS 4766 AS 4134 AS 16880 AS 7922 AS 9318 AS 3786 AS 4837 AS 3462 AS 3356 AS 5384 AS 5483 AS 3329 AS 8151 AS 6799 AS 9737 AS 27699 AS 12322 AS 7132 AS 4788 AS 45758 AS 7470 AS 1267 AS 24560 AS 15557 AS 18101 AS 4771 AS 4713 AS 25019 AS 8400 Origin AS Name Country GOOGLE - Google Inc. USA KIXS -AS-KR Korea Telecom Korea CHINANET -BACKBONE No. 31, Jin-rong Street China TRENDMICRO Global IDC and Backbone of Trend Micro Inc. USA COMCAST -7922 - Comcast Cable Communications, Inc. USA HANARO -AS Hanaro Telecom Inc. Korea LGDACOM LG DACOM Corporation Korea CHINA 169 -BACKBONE CNCGROUP China 169 Backbone China HINET Data Communication Business Group Taiwan LEVEL 3 Level 3 Communications USA EMIRATES -INTERNET Emirates Telecommunications Corporation UAE HTC-AS Magyar Telekom plc. Hungary Hellas On. Line Electronic Communications S. A. Greece Uninet S. A. de C. V. Mexico OTENET-GR Ote SA (Hellenic Telecommunications Organisation) Greece TOTNET-TH-AS-AP TOT Public Company Limited Thailand TELECOMUNICACOES DE SAO PAULO S/A - TELESP Brazil PROXAD Free SAS France SBIS -AS AS for SBIS-AS USA TMNET -AS-AP TM Net, Internet Service Provider Malaysia TRIPLETNET-AS-AP Triple. T Internet service provider Thailand TRUEINTERNET -AS-AP TRUE INTERNET Co. , Ltd. Thailand ASN -INFOSTRADA WIND Telecomunicazioni S. p. A. Italy AIRTELBROADBAND-AS-AP Bharti Airtel Ltd. , Telemedia Services India LDCOMNET Societe Francaise du Radiotelephone S. A France RELIANCE-COMMUNICATIONS-IN Reliance Communications Ltd. MUMBAI India NZTELECOM Telecom New Zealand Ltd. New Zealand OCN NTT Communications Corporation Japan SAUDINETSTC-AS Autonomus System Number for Saudi. Net Saudi Arabia TELEKOM -AS TELEKOM SRBIJA a. d. Serbia
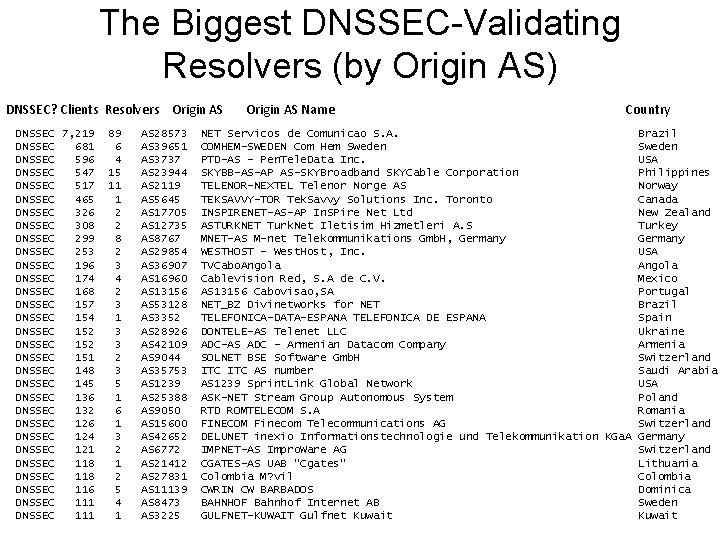
The Biggest DNSSEC-Validating Resolvers (by Origin AS) DNSSEC? Clients Resolvers Origin AS DNSSEC 7, 219 DNSSEC 681 DNSSEC 596 DNSSEC 547 DNSSEC 517 DNSSEC 465 DNSSEC 326 DNSSEC 308 DNSSEC 299 DNSSEC 253 DNSSEC 196 DNSSEC 174 DNSSEC 168 DNSSEC 157 DNSSEC 154 DNSSEC 152 DNSSEC 151 DNSSEC 148 DNSSEC 145 DNSSEC 136 DNSSEC 132 DNSSEC 126 DNSSEC 124 DNSSEC 121 DNSSEC 118 DNSSEC 116 DNSSEC 111 89 6 4 15 11 1 2 2 8 2 3 4 2 3 1 3 3 2 3 5 1 6 1 3 2 1 2 5 4 1 AS 28573 AS 39651 AS 3737 AS 23944 AS 2119 AS 5645 AS 17705 AS 12735 AS 8767 AS 29854 AS 36907 AS 16960 AS 13156 AS 53128 AS 3352 AS 28926 AS 42109 AS 9044 AS 35753 AS 1239 AS 25388 AS 9050 AS 15600 AS 42652 AS 6772 AS 21412 AS 27831 AS 11139 AS 8473 AS 3225 Origin AS Name Country NET Servicos de Comunicao S. A. Brazil COMHEM-SWEDEN Com Hem Sweden PTD-AS - Pen. Tele. Data Inc. USA SKYBB-AS-AP AS-SKYBroadband SKYCable Corporation Philippines TELENOR-NEXTEL Telenor Norge AS Norway TEKSAVVY-TOR Tek. Savvy Solutions Inc. Toronto Canada INSPIRENET-AS-AP In. SPire Net Ltd New Zealand ASTURKNET Turk. Net Iletisim Hizmetleri A. S Turkey MNET-AS M-net Telekommunikations Gmb. H, Germany WESTHOST - West. Host, Inc. USA TVCabo. Angola Cablevision Red, S. A de C. V. Mexico AS 13156 Cabovisao, SA Portugal NET_BZ Divinetworks for NET Brazil TELEFONICA-DATA-ESPANA TELEFONICA DE ESPANA Spain DONTELE-AS Telenet LLC Ukraine ADC-AS ADC - Armenian Datacom Company Armenia SOLNET BSE Software Gmb. H Switzerland ITC AS number Saudi Arabia AS 1239 Sprint. Link Global Network USA ASK-NET Stream Group Autonomous System Poland RTD ROMTELECOM S. A Romania FINECOM Finecom Telecommunications AG Switzerland DELUNET inexio Informationstechnologie und Telekommunikation KGa. A Germany IMPNET-AS Impro. Ware AG Switzerland CGATES-AS UAB "Cgates" Lithuania Colombia M? vil Colombia CWRIN CW BARBADOS Dominica BAHNHOF Bahnhof Internet AB Sweden GULFNET-KUWAIT Gulfnet Kuwait
Now lets look at Clients: • How many unique experiment identifiers completed DNS queries for objects named in the experiment? • How many clients exclusively used DNSSECvalidating resolvers?
Clients: • How many unique experiment identifiers completed DNS queries for objects named in the experiment? 2, 549, 816 • How many clients exclusively used DNSSECvalidating resolvers when resolving the domain name with invalid DNSSEC credentials? 77, 021 (3. 0%)
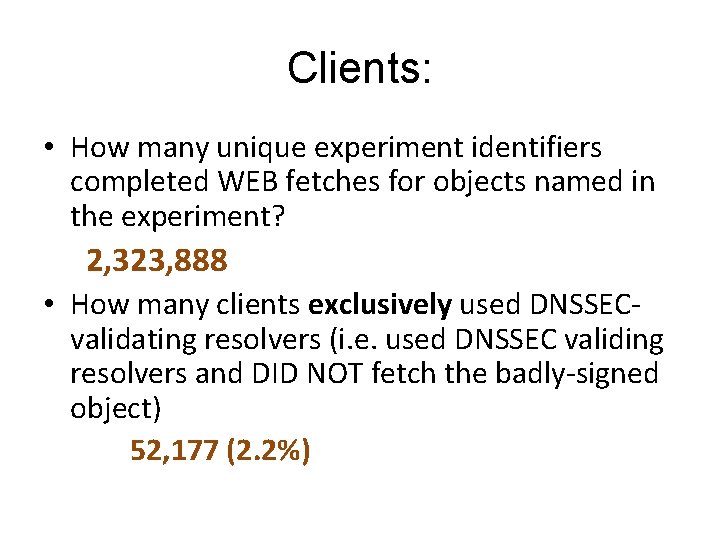
Clients: • How many unique experiment identifiers completed WEB fetches for objects named in the experiment? 2, 323, 888 • How many clients exclusively used DNSSECvalidating resolvers (i. e. used DNSSEC validing resolvers and DID NOT fetch the badly-signed object) 52, 177 (2. 2%)
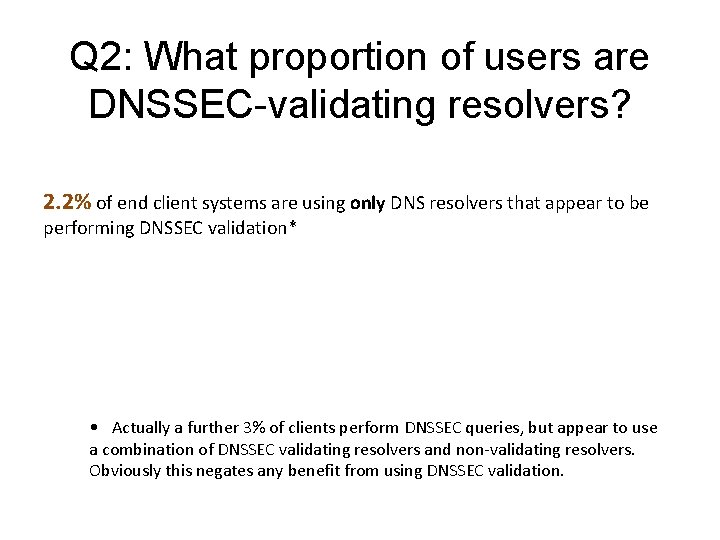
Q 2: What proportion of users are DNSSEC-validating resolvers? 2. 2% of end client systems are using only DNS resolvers that appear to be performing DNSSEC validation* • Actually a further 3% of clients perform DNSSEC queries, but appear to use a combination of DNSSEC validating resolvers and non-validating resolvers. Obviously this negates any benefit from using DNSSEC validation.
Q 3: Where can we find DNSSECvalidating clients?
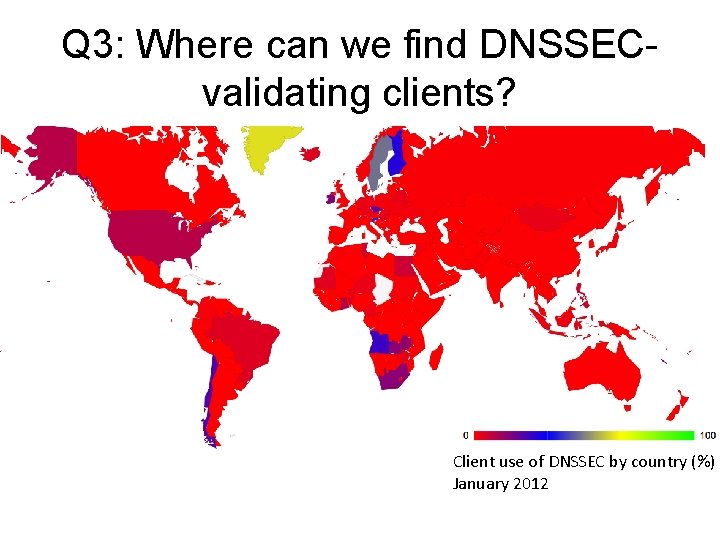
Q 3: Where can we find DNSSECvalidating clients? Client use of DNSSEC by country (%) January 2012
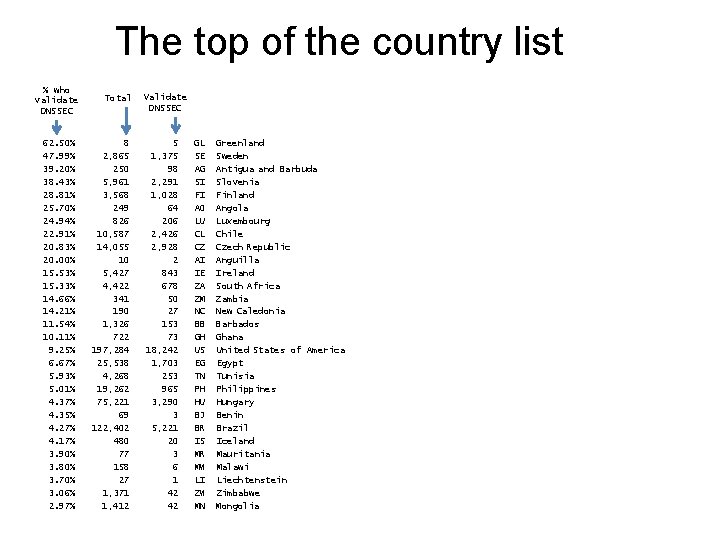
The top of the country list % who validate DNSSEC 62. 50% 47. 99% 39. 20% 38. 43% 28. 81% 25. 70% 24. 94% 22. 91% 20. 83% 20. 00% 15. 53% 15. 33% 14. 66% 14. 21% 11. 54% 10. 11% 9. 25% 6. 67% 5. 93% 5. 01% 4. 37% 4. 35% 4. 27% 4. 17% 3. 90% 3. 80% 3. 70% 3. 06% 2. 97% Total 8 2, 865 250 5, 961 3, 568 249 826 10, 587 14, 055 10 5, 427 4, 422 341 190 1, 326 722 197, 284 25, 538 4, 268 19, 262 75, 221 69 122, 402 480 77 158 27 1, 371 1, 412 Validate DNSSEC 5 1, 375 98 2, 291 1, 028 64 206 2, 426 2, 928 2 843 678 50 27 153 73 18, 242 1, 703 253 965 3, 290 3 5, 221 20 3 6 1 42 42 GL SE AG SI FI AO LU CL CZ AI IE ZA ZM NC BB GH US EG TN PH HU BJ BR IS MR MW LI ZW MN Greenland Sweden Antigua and Barbuda Slovenia Finland Angola Luxembourg Chile Czech Republic Anguilla Ireland South Africa Zambia New Caledonia Barbados Ghana United States of America Egypt Tunisia Philippines Hungary Benin Brazil Iceland Mauritania Malawi Liechtenstein Zimbabwe Mongolia
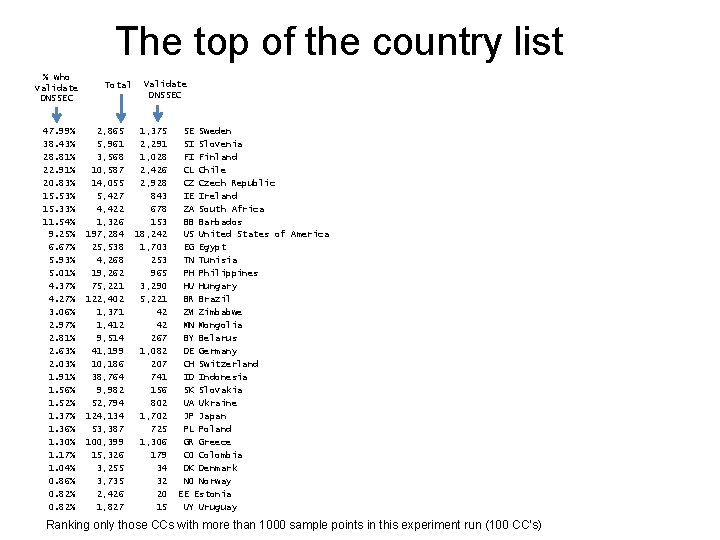
The top of the country list % who validate DNSSEC 47. 99% 38. 43% 28. 81% 22. 91% 20. 83% 15. 53% 15. 33% 11. 54% 9. 25% 6. 67% 5. 93% 5. 01% 4. 37% 4. 27% 3. 06% 2. 97% 2. 81% 2. 63% 2. 03% 1. 91% 1. 56% 1. 52% 1. 37% 1. 36% 1. 30% 1. 17% 1. 04% 0. 86% 0. 82% Total 2, 865 5, 961 3, 568 10, 587 14, 055 5, 427 4, 422 1, 326 197, 284 25, 538 4, 268 19, 262 75, 221 122, 402 1, 371 1, 412 9, 514 41, 199 10, 186 38, 764 9, 982 52, 794 124, 134 53, 387 100, 399 15, 326 3, 255 3, 735 2, 426 1, 827 Validate DNSSEC 1, 375 2, 291 1, 028 2, 426 2, 928 843 678 153 18, 242 1, 703 253 965 3, 290 5, 221 42 42 267 1, 082 207 741 156 802 1, 702 725 1, 306 179 34 32 20 15 SE Sweden SI Slovenia FI Finland CL Chile CZ Czech Republic IE Ireland ZA South Africa BB Barbados US United States of America EG Egypt TN Tunisia PH Philippines HU Hungary BR Brazil ZW Zimbabwe MN Mongolia BY Belarus DE Germany CH Switzerland ID Indonesia SK Slovakia UA Ukraine JP Japan PL Poland GR Greece CO Colombia DK Denmark NO Norway EE Estonia UY Uruguay Ranking only those CCs with more than 1000 sample points in this experiment run (100 CC’s)
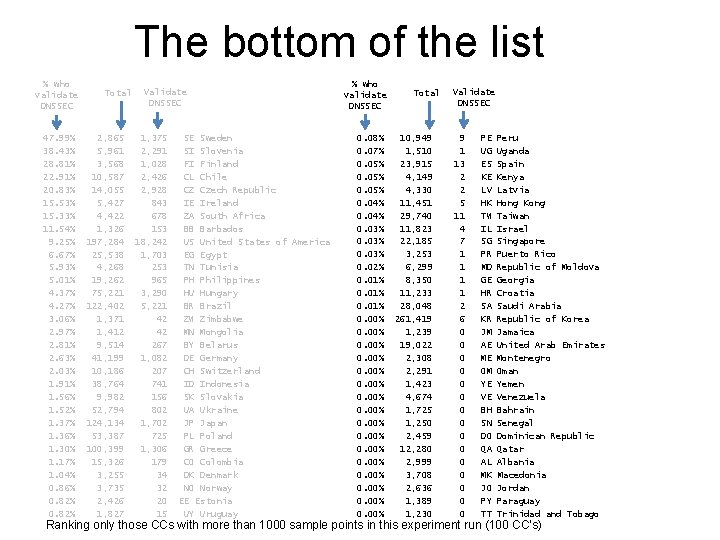
The bottom of the list % who validate DNSSEC 47. 99% 38. 43% 28. 81% 22. 91% 20. 83% 15. 53% 15. 33% 11. 54% 9. 25% 6. 67% 5. 93% 5. 01% 4. 37% 4. 27% 3. 06% 2. 97% 2. 81% 2. 63% 2. 03% 1. 91% 1. 56% 1. 52% 1. 37% 1. 36% 1. 30% 1. 17% 1. 04% 0. 86% 0. 82% Total 2, 865 5, 961 3, 568 10, 587 14, 055 5, 427 4, 422 1, 326 197, 284 25, 538 4, 268 19, 262 75, 221 122, 402 1, 371 1, 412 9, 514 41, 199 10, 186 38, 764 9, 982 52, 794 124, 134 53, 387 100, 399 15, 326 3, 255 3, 735 2, 426 1, 827 Validate DNSSEC 1, 375 2, 291 1, 028 2, 426 2, 928 843 678 153 18, 242 1, 703 253 965 3, 290 5, 221 42 42 267 1, 082 207 741 156 802 1, 702 725 1, 306 179 34 32 20 15 SE Sweden SI Slovenia FI Finland CL Chile CZ Czech Republic IE Ireland ZA South Africa BB Barbados US United States of America EG Egypt TN Tunisia PH Philippines HU Hungary BR Brazil ZW Zimbabwe MN Mongolia BY Belarus DE Germany CH Switzerland ID Indonesia SK Slovakia UA Ukraine JP Japan PL Poland GR Greece CO Colombia DK Denmark NO Norway EE Estonia UY Uruguay % who validate DNSSEC 0. 08% 0. 07% 0. 05% 0. 04% 0. 03% 0. 02% 0. 01% 0. 00% 0. 00% Total 10, 949 1, 510 23, 915 4, 149 4, 330 11, 451 29, 740 11, 823 22, 185 3, 253 6, 299 8, 350 11, 233 28, 048 261, 419 1, 239 19, 022 2, 308 2, 291 1, 423 4, 674 1, 725 1, 250 2, 459 12, 280 2, 999 3, 708 2, 636 1, 389 1, 230 Validate DNSSEC 9 1 13 2 2 5 11 4 7 1 1 2 6 0 0 0 0 PE UG ES KE LV HK TW IL SG PR MD GE HR SA KR JM AE ME OM YE VE BH SN DO QA AL MK JO PY TT Peru Uganda Spain Kenya Latvia Hong Kong Taiwan Israel Singapore Puerto Rico Republic of Moldova Georgia Croatia Saudi Arabia Republic of Korea Jamaica United Arab Emirates Montenegro Oman Yemen Venezuela Bahrain Senegal Dominican Republic Qatar Albania Macedonia Jordan Paraguay Trinidad and Tobago Ranking only those CCs with more than 1000 sample points in this experiment run (100 CC’s)
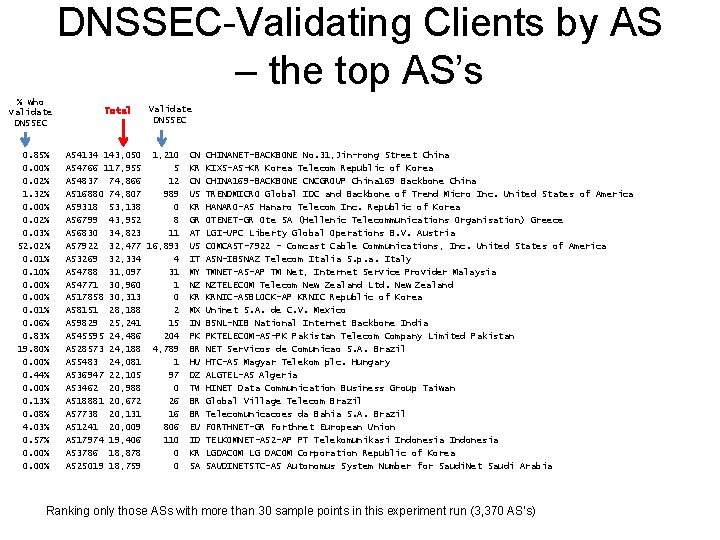
DNSSEC-Validating Clients by AS – the top AS’s % who validate DNSSEC 0. 85% 0. 00% 0. 02% 1. 32% 0. 00% 0. 02% 0. 03% 52. 02% 0. 01% 0. 10% 0. 00% 0. 01% 0. 06% 0. 83% 19. 80% 0. 00% 0. 44% 0. 00% 0. 13% 0. 08% 4. 03% 0. 57% 0. 00% Total Validate DNSSEC AS 4134 143, 050 1, 210 AS 4766 117, 955 5 AS 4837 74, 866 12 AS 16880 74, 807 989 AS 9318 53, 138 0 AS 6799 43, 952 8 AS 6830 34, 823 11 AS 7922 32, 477 16, 893 AS 3269 32, 334 4 AS 4788 31, 097 31 AS 4771 30, 960 1 AS 17858 30, 313 0 AS 8151 28, 188 2 AS 9829 25, 241 15 AS 45595 24, 486 204 AS 28573 24, 188 4, 789 AS 5483 24, 081 1 AS 36947 22, 105 97 AS 3462 20, 988 0 AS 18881 20, 672 26 AS 7738 20, 131 16 AS 1241 20, 009 806 AS 17974 19, 406 110 AS 3786 18, 878 0 AS 25019 18, 759 0 CN KR CN US KR GR AT US IT MY NZ KR MX IN PK BR HU DZ TW BR BR EU ID KR SA CHINANET-BACKBONE No. 31, Jin-rong Street China KIXS-AS-KR Korea Telecom Republic of Korea CHINA 169 -BACKBONE CNCGROUP China 169 Backbone China TRENDMICRO Global IDC and Backbone of Trend Micro Inc. United States of America HANARO-AS Hanaro Telecom Inc. Republic of Korea OTENET-GR Ote SA (Hellenic Telecommunications Organisation) Greece LGI-UPC Liberty Global Operations B. V. Austria COMCAST-7922 - Comcast Cable Communications, Inc. United States of America ASN-IBSNAZ Telecom Italia S. p. a. Italy TMNET-AS-AP TM Net, Internet Service Provider Malaysia NZTELECOM Telecom New Zealand Ltd. New Zealand KRNIC-ASBLOCK-AP KRNIC Republic of Korea Uninet S. A. de C. V. Mexico BSNL-NIB National Internet Backbone India PKTELECOM-AS-PK Pakistan Telecom Company Limited Pakistan NET Servicos de Comunicao S. A. Brazil HTC-AS Magyar Telekom plc. Hungary ALGTEL-AS Algeria HINET Data Communication Business Group Taiwan Global Village Telecom Brazil Telecomunicacoes da Bahia S. A. Brazil FORTHNET-GR Forthnet European Union TELKOMNET-AS 2 -AP PT Telekomunikasi Indonesia LGDACOM LG DACOM Corporation Republic of Korea SAUDINETSTC-AS Autonomus System Number for Saudi. Net Saudi Arabia Ranking only those ASs with more than 30 sample points in this experiment run (3, 370 AS’s)
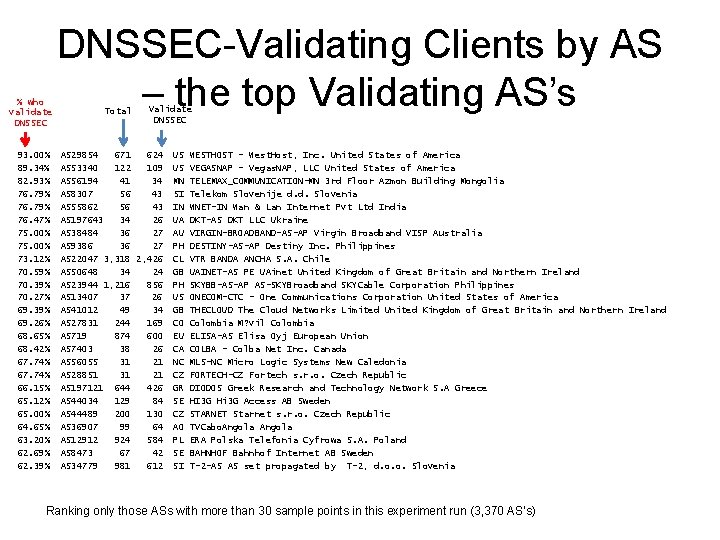
% who validate DNSSEC 93. 00% 89. 34% 82. 93% 76. 79% 76. 47% 75. 00% 73. 12% 70. 59% 70. 39% 70. 27% 69. 39% 69. 26% 68. 65% 68. 42% 67. 74% 66. 15% 65. 12% 65. 00% 64. 65% 63. 20% 62. 69% 62. 39% DNSSEC-Validating Clients by AS – the top Validating AS’s Total Validate DNSSEC AS 29854 671 624 AS 53340 122 109 AS 56194 41 34 AS 8307 56 43 AS 55862 56 43 AS 197643 34 26 AS 38484 36 27 AS 9386 36 27 AS 22047 3, 318 2, 426 AS 50648 34 24 AS 23944 1, 216 856 AS 13407 37 26 AS 41012 49 34 AS 27831 244 169 AS 719 874 600 AS 7403 38 26 AS 56055 31 21 AS 28851 31 21 AS 197121 644 426 AS 44034 129 84 AS 44489 200 130 AS 36907 99 64 AS 12912 924 584 AS 8473 67 42 AS 34779 981 612 US US MN SI IN UA AU PH CL GB PH US GB CO EU CA NC CZ GR SE CZ AO PL SE SI WESTHOST - West. Host, Inc. United States of America VEGASNAP - Vegas. NAP, LLC United States of America TELEMAX_COMMUNICATION-MN 3 rd Floor Azmon Building Mongolia Telekom Slovenije d. d. Slovenia WNET-IN Wan & Lan Internet Pvt Ltd India DKT-AS DKT LLC Ukraine VIRGIN-BROADBAND-AS-AP Virgin Broadband VISP Australia DESTINY-AS-AP Destiny Inc. Philippines VTR BANDA ANCHA S. A. Chile UAINET-AS PE UAinet United Kingdom of Great Britain and Northern Ireland SKYBB-AS-AP AS-SKYBroadband SKYCable Corporation Philippines ONECOM-CTC - One Communications Corporation United States of America THECLOUD The Cloud Networks Limited United Kingdom of Great Britain and Northern Ireland Colombia M? vil Colombia ELISA-AS Elisa Oyj European Union COLBA - Colba Net Inc. Canada MLS-NC Micro Logic Systems New Caledonia FORTECH-CZ Fortech s. r. o. Czech Republic DIODOS Greek Research and Technology Network S. A Greece HI 3 G Hi 3 G Access AB Sweden STARNET Starnet s. r. o. Czech Republic TVCabo. Angola ERA Polska Telefonia Cyfrowa S. A. Poland BAHNHOF Bahnhof Internet AB Sweden T-2 -AS AS set propagated by T-2, d. o. o. Slovenia Ranking only those ASs with more than 30 sample points in this experiment run (3, 370 AS’s)
And finally. . . The “Mad Resolver” prize goes to the resolver: 161. 185. 154. 2 who successfully queried for the same A RR from our server for a total of 190 times despite establishing that the DNSSEC signature was invalid after the first query! Second prize to 82. 212. 62. 37, who queried the DNSKEY record for a domain 178 times Never take NO for an answer! Thanks guys! Great achievement!
Thank you!
- Slides: 43