Maxcsysware com tw Sysware Corporation 2003 Sysware Corporation

- Slides: 93
網路安全的探討及防範 精誠資訊 錢宜中 Maxc@sysware. com. tw Sysware Corporation. 2003
網路安全的範圍---防火牆 Sysware Corporation. 2003
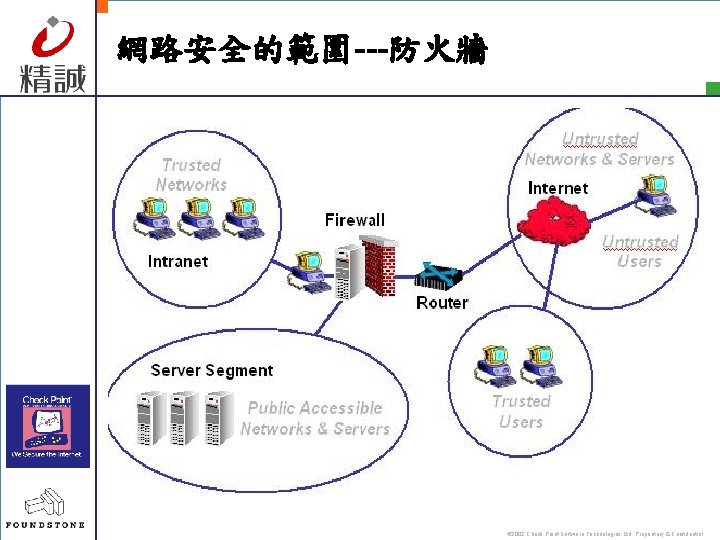
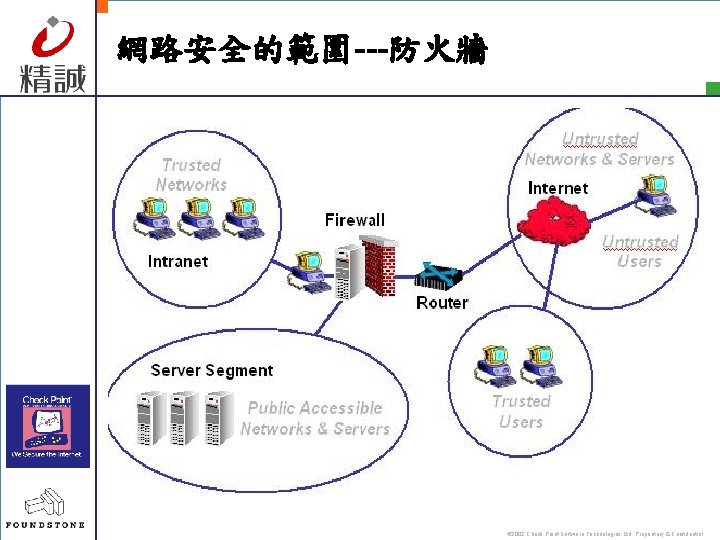
網路安全的範圍---防火牆 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
防火牆的世代種類 § 封包過濾防火牆-Packet filtering Firewall § 代理伺服器(應用層)防火牆-Proxy ( Application Layer)Firewall § 狀態檢驗式防火牆-Stateful Inspection Firewall © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
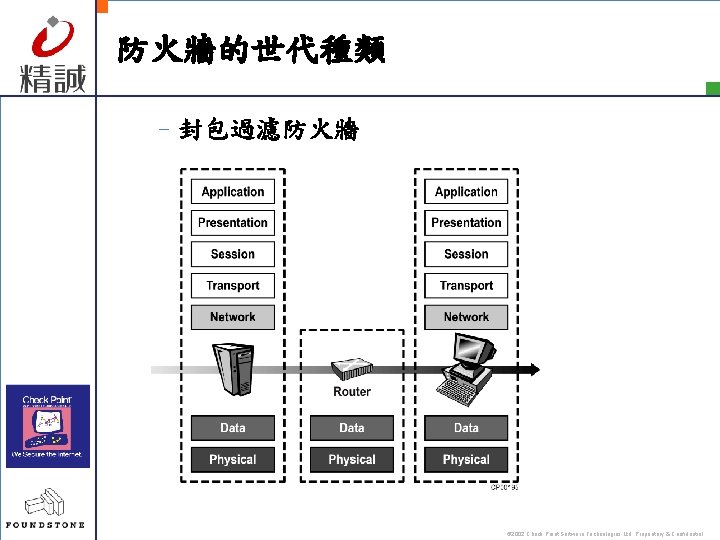
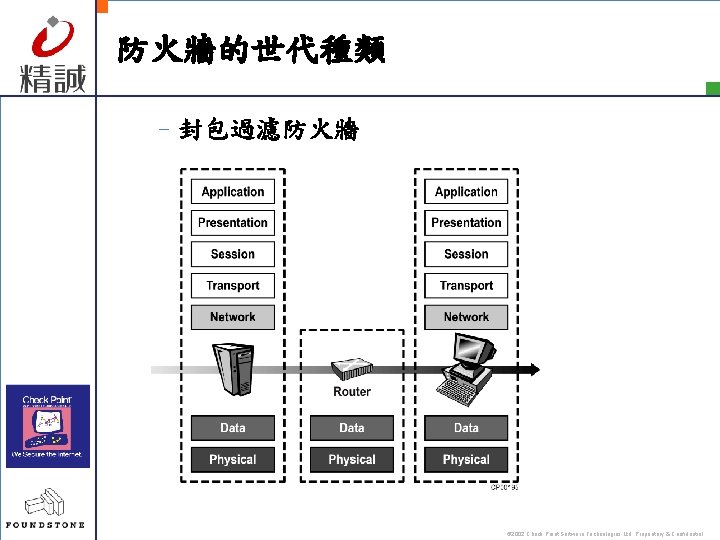
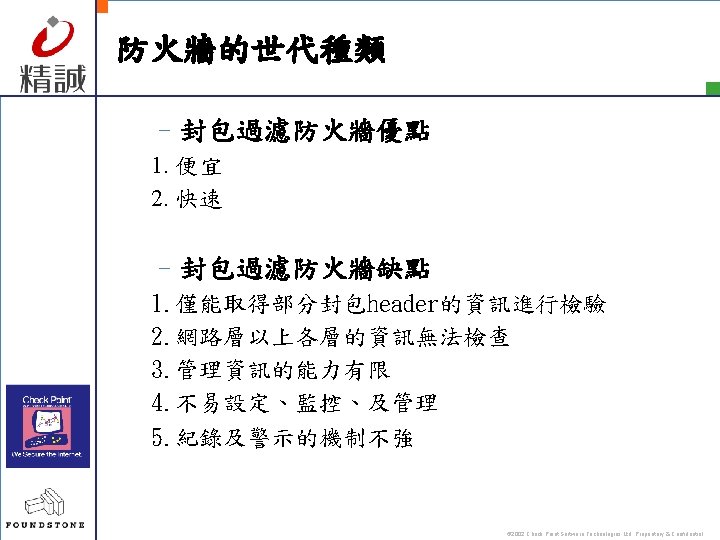
防火牆的世代種類 –封包過濾防火牆 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
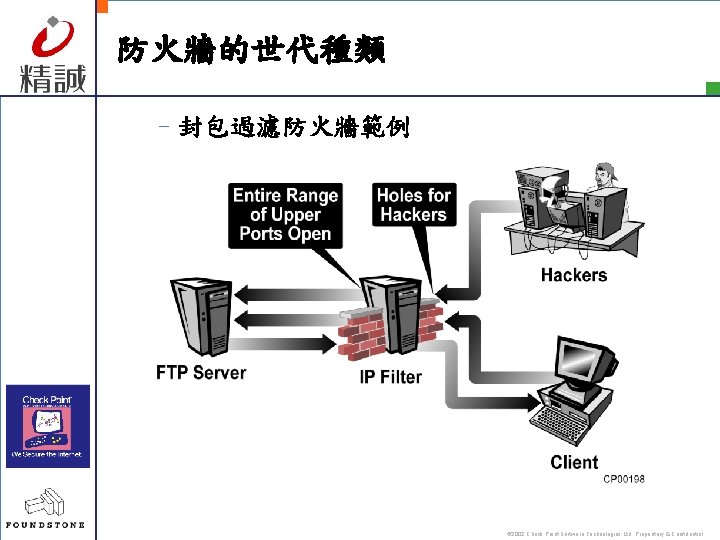
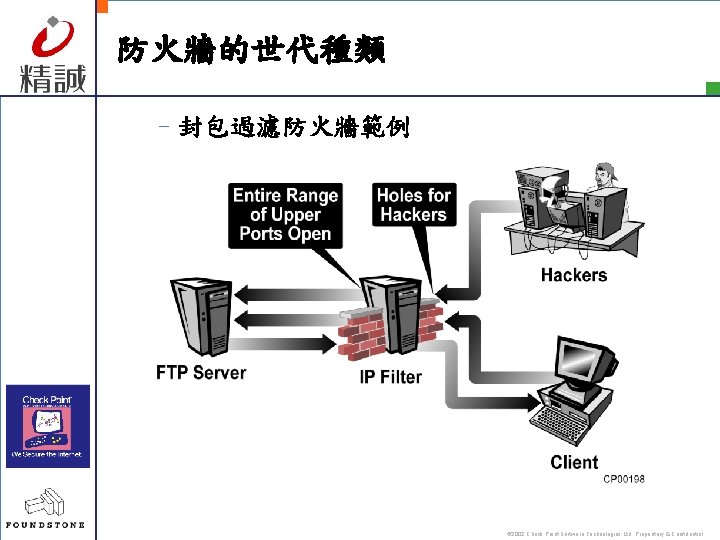
防火牆的世代種類 –封包過濾防火牆範例 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
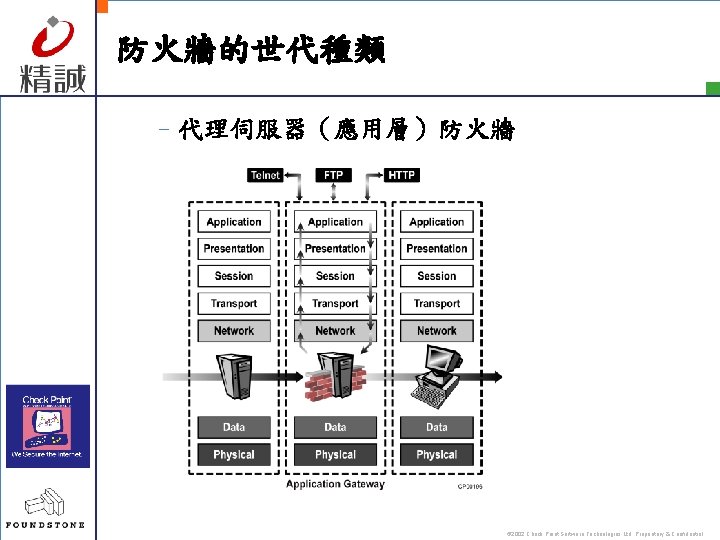
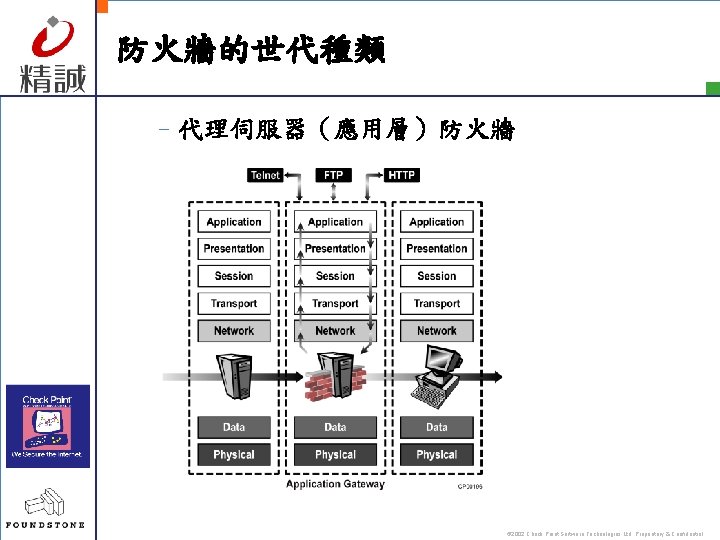
防火牆的世代種類 –代理伺服器(應用層)防火牆 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
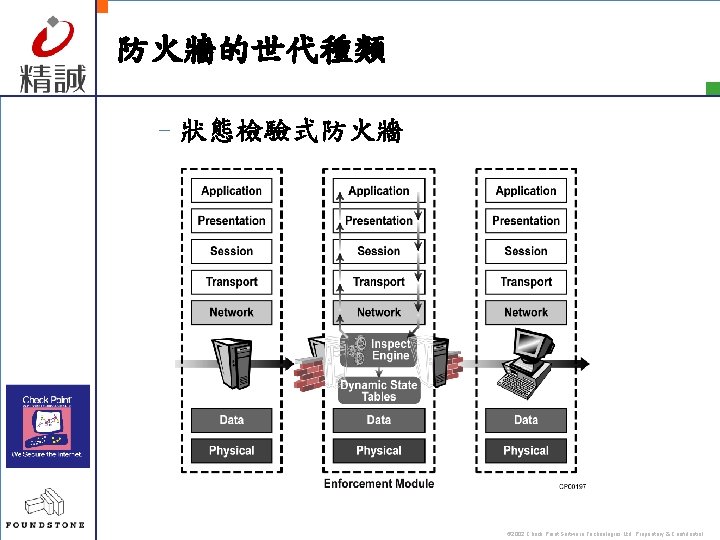
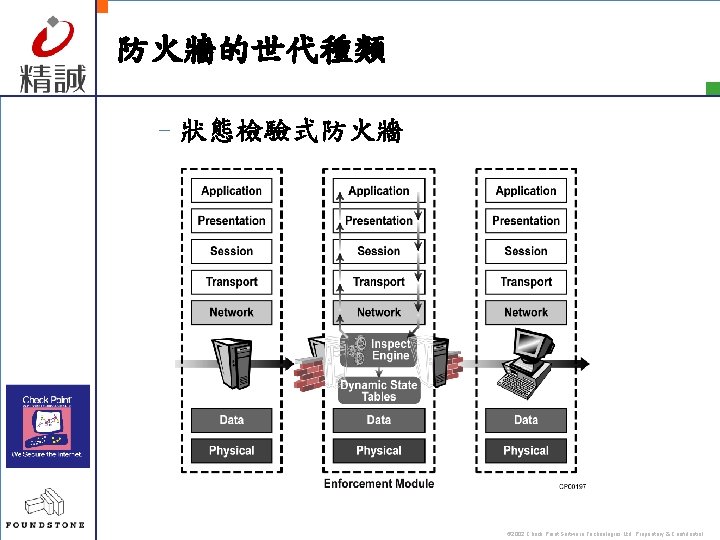
防火牆的世代種類 –狀態檢驗式防火牆 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
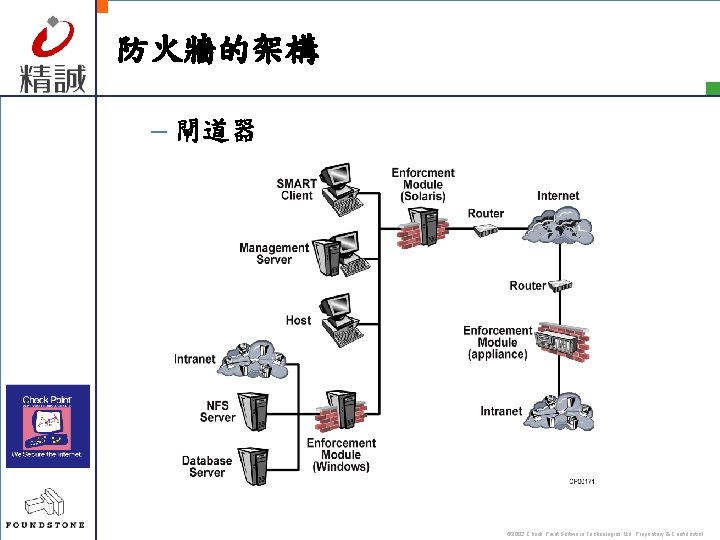
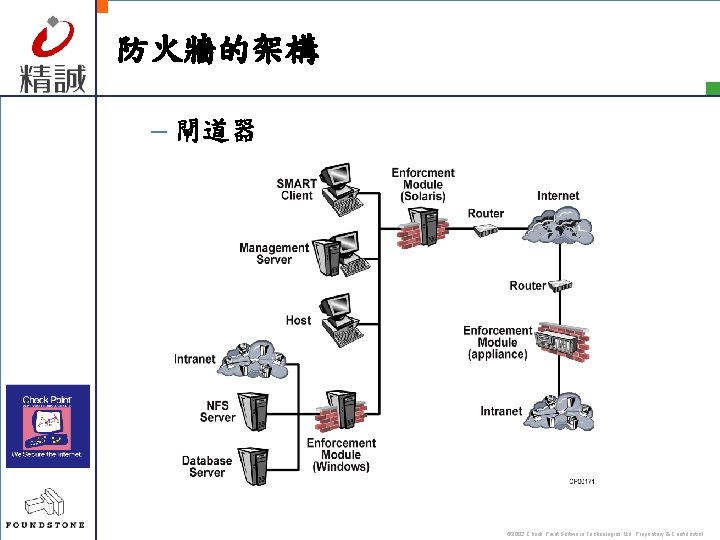
防火牆的架構 – 閘道器 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
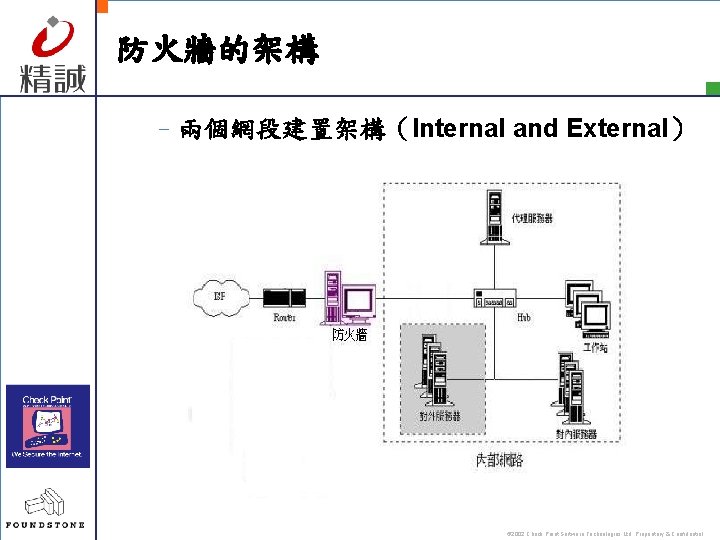
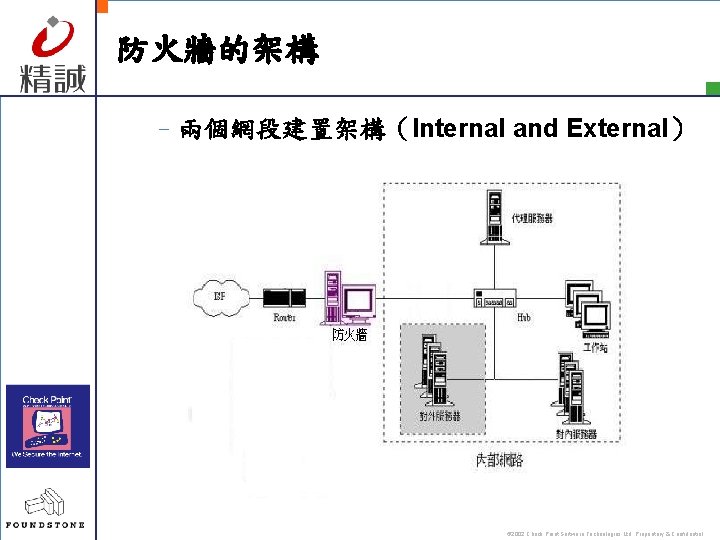
防火牆的架構 –兩個網段建置架構(Internal and External) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
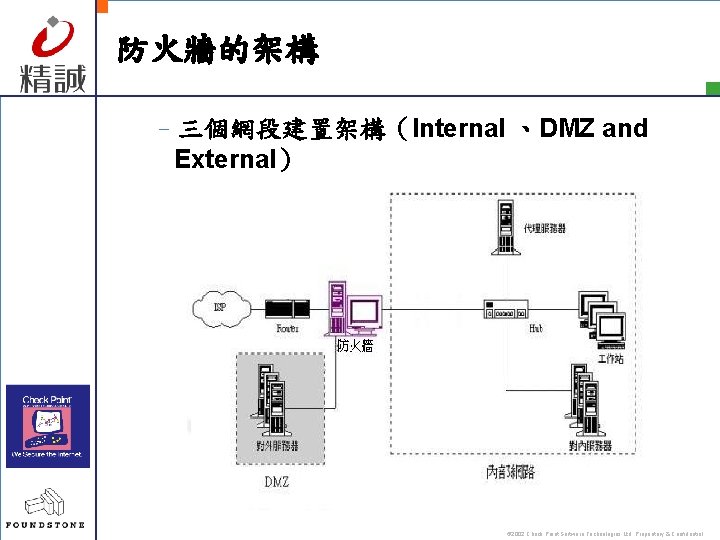
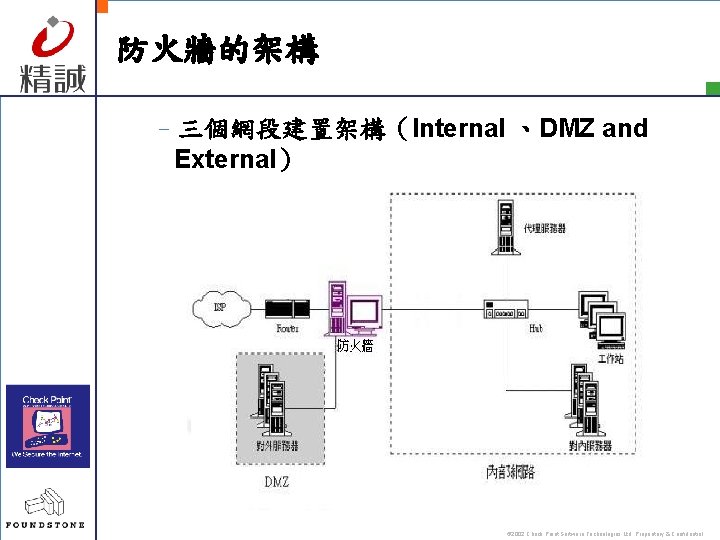
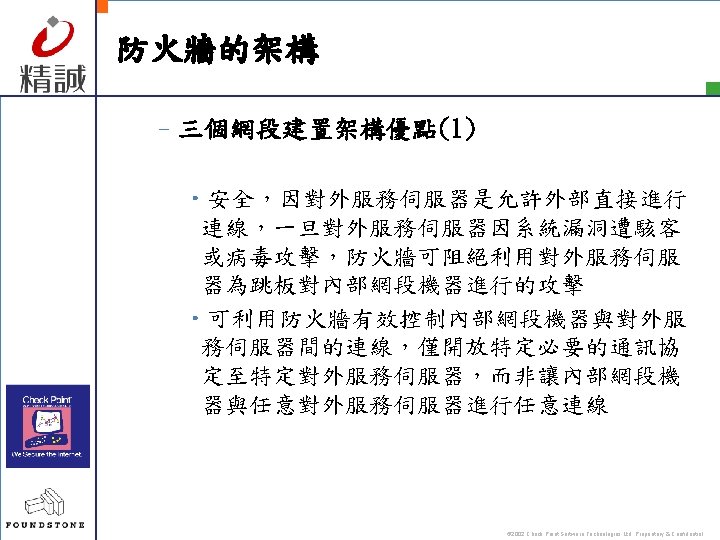
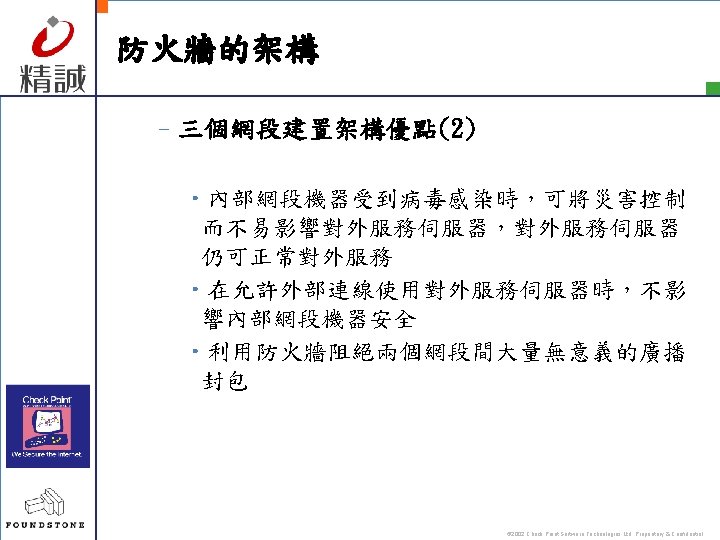
防火牆的架構 –三個網段建置架構(Internal 、DMZ and External) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
安全政策(Security Policy) –安全政策的制定種類 • 內定值是‘拒絕’ • 內定值是‘允許’ © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
Questions? © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
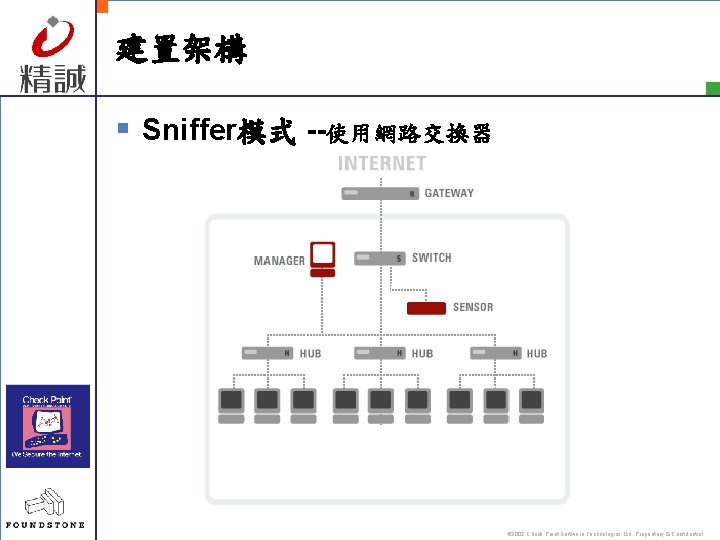
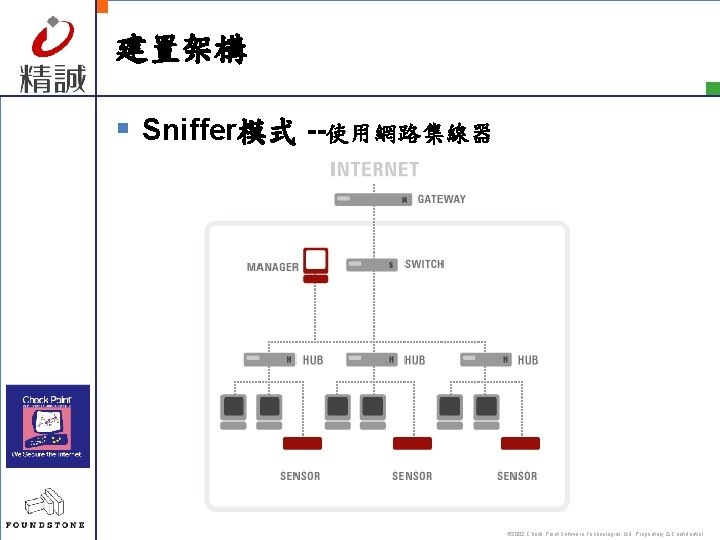
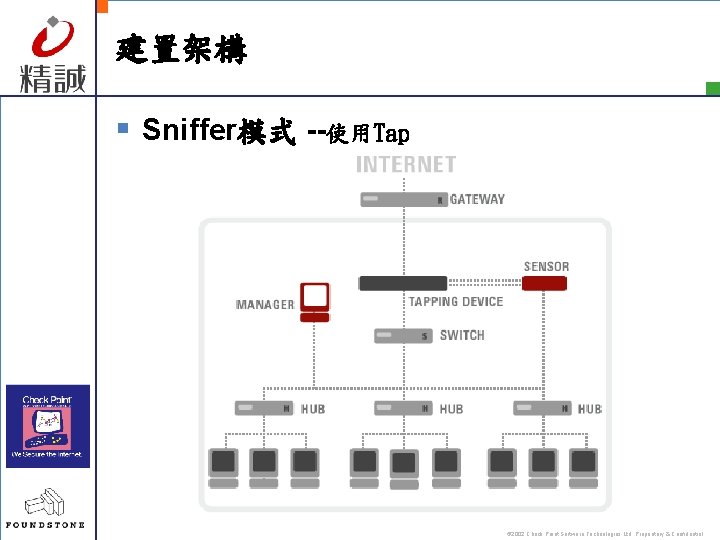
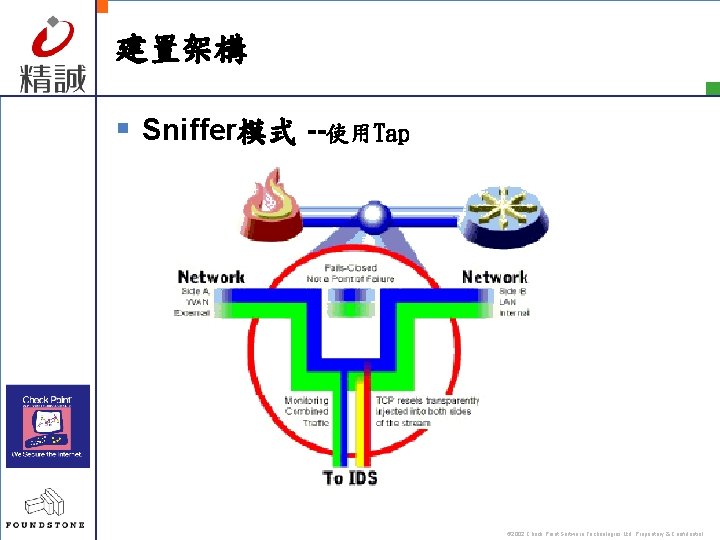
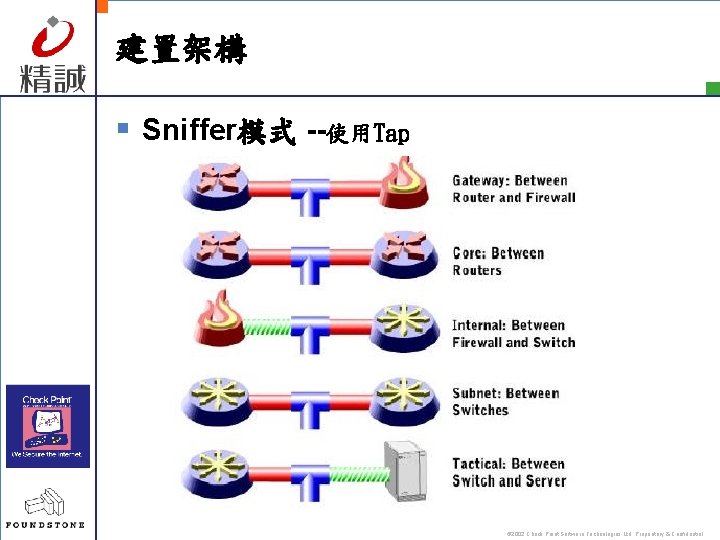
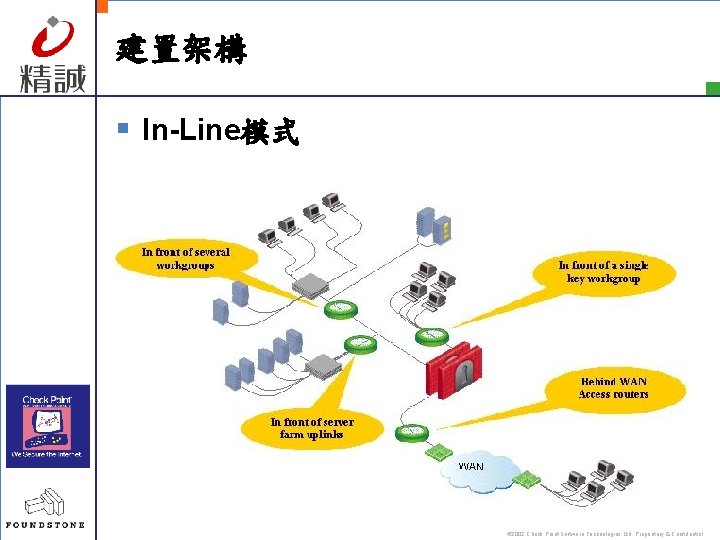
建置架構 § Sniffer模式 --使用網路交換器 --使用網路集線器 --使用 Tap § In-Line模式 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
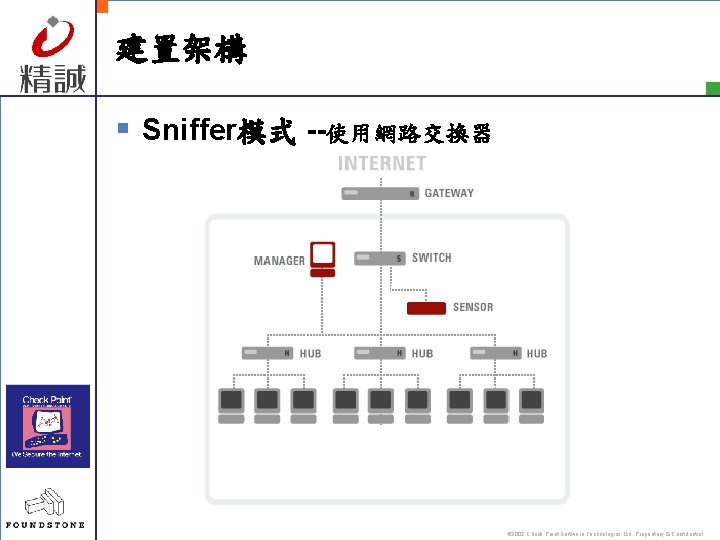
建置架構 § Sniffer模式 --使用網路交換器 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
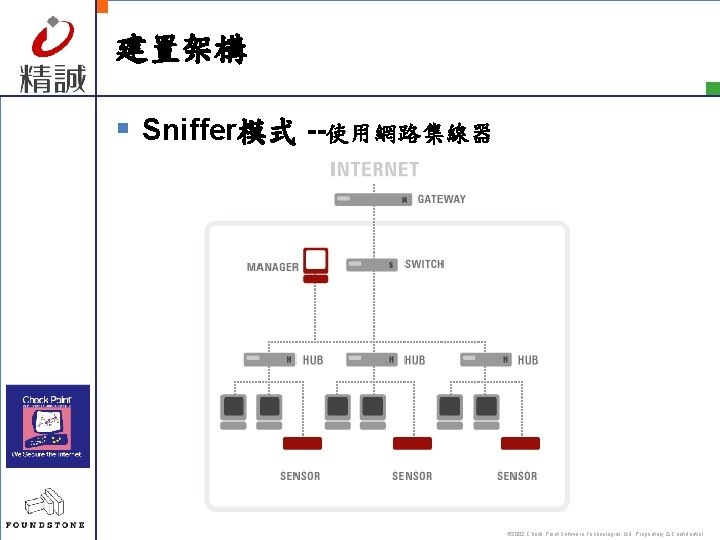
建置架構 § Sniffer模式 --使用網路集線器 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
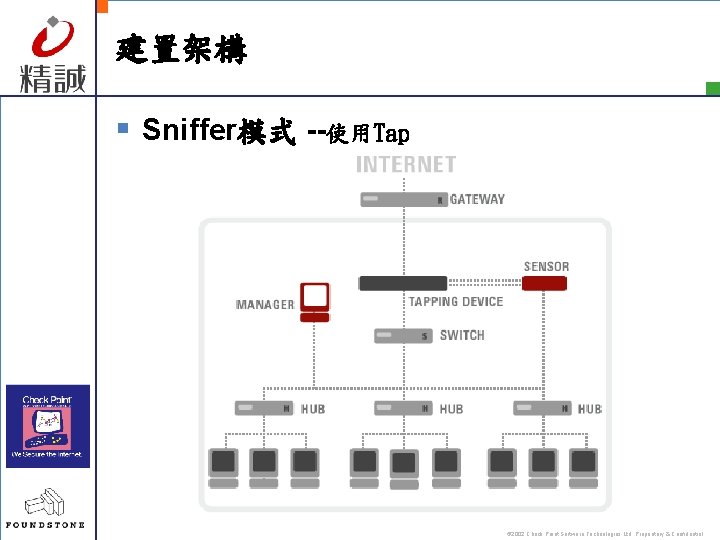
建置架構 § Sniffer模式 --使用Tap © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
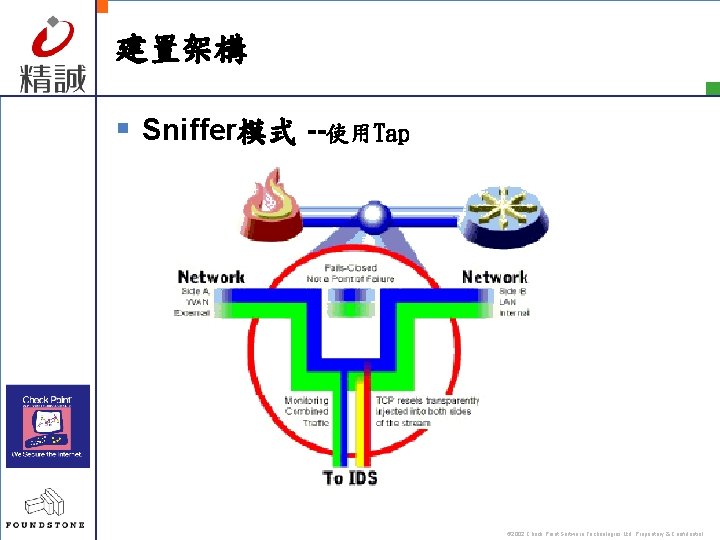
建置架構 § Sniffer模式 --使用Tap © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
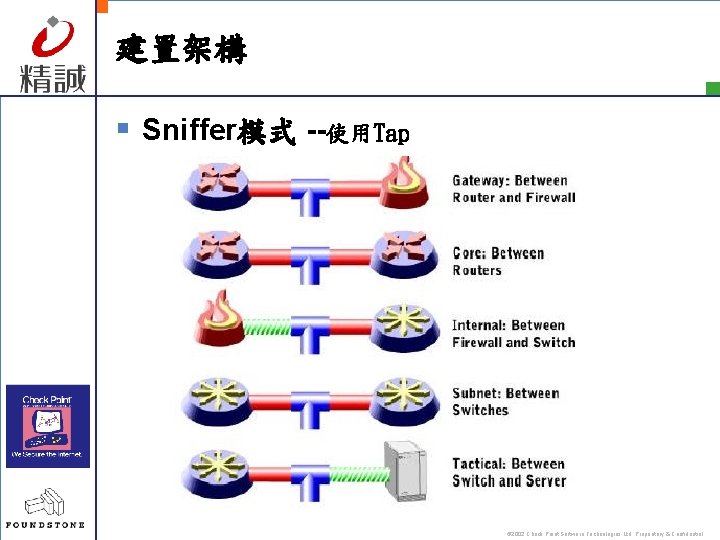
建置架構 § Sniffer模式 --使用Tap © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
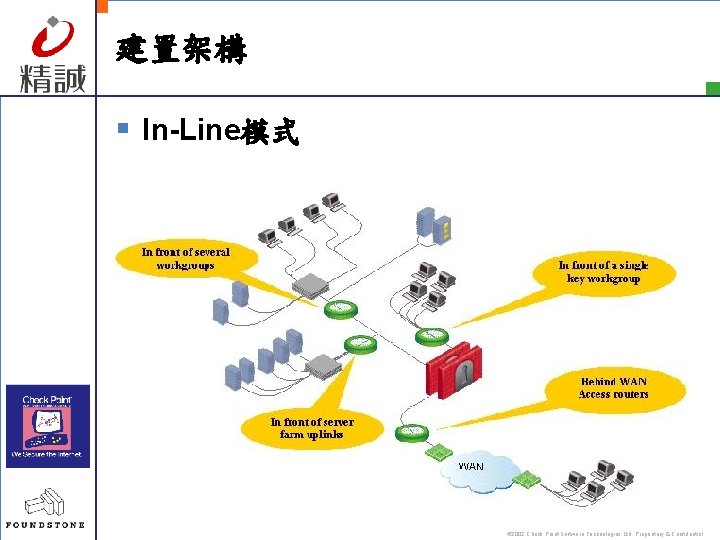
建置架構 § In-Line模式 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
偵測運作原理 § 特徵比對(signature match) § 通訊協定異常偵測 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
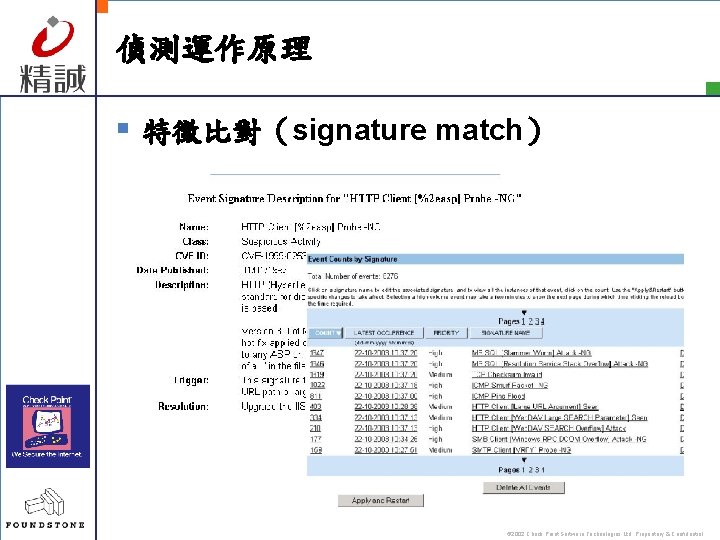
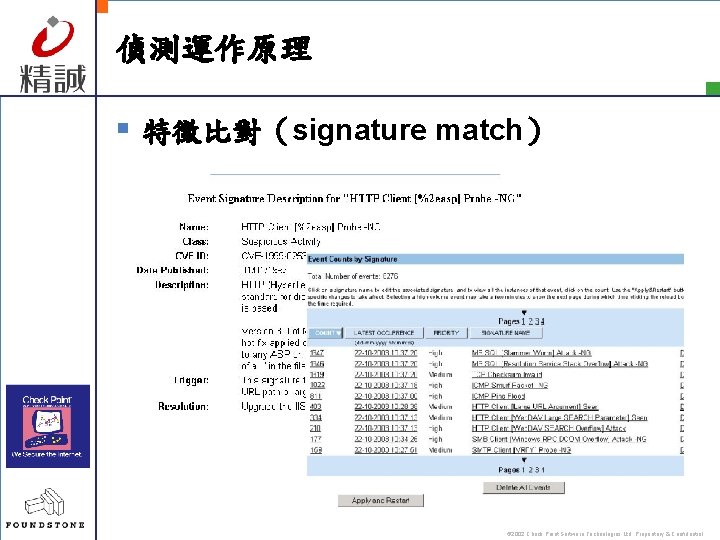
偵測運作原理 § 特徵比對(signature match) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
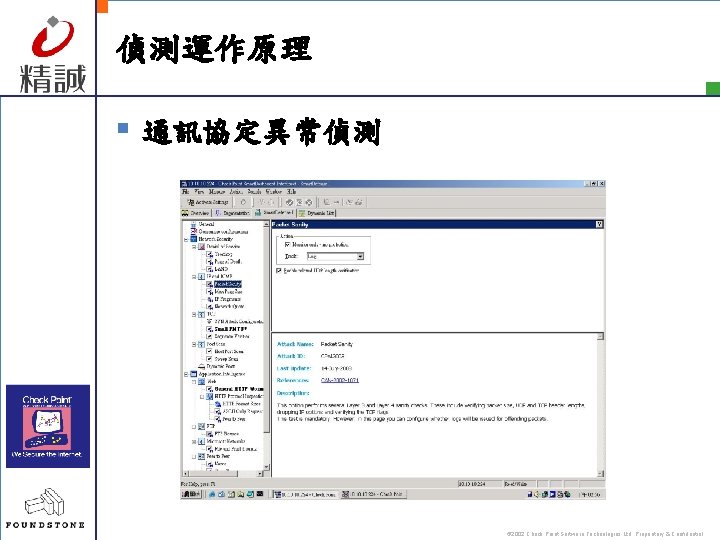
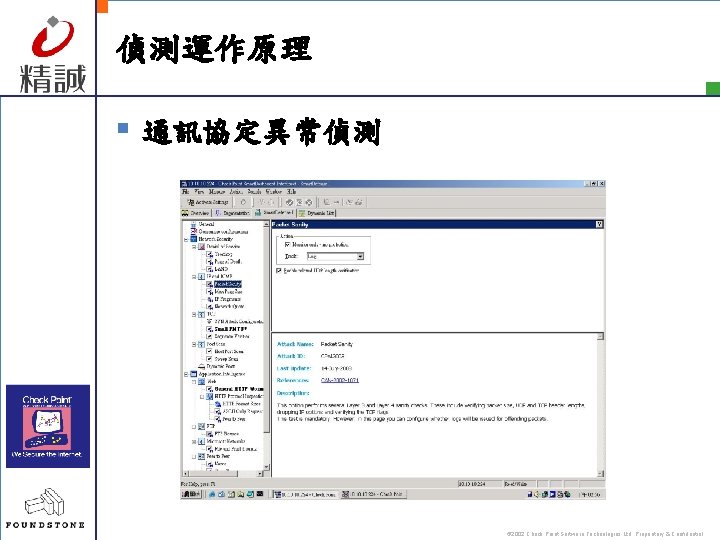
偵測運作原理 § 通訊協定異常偵測 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
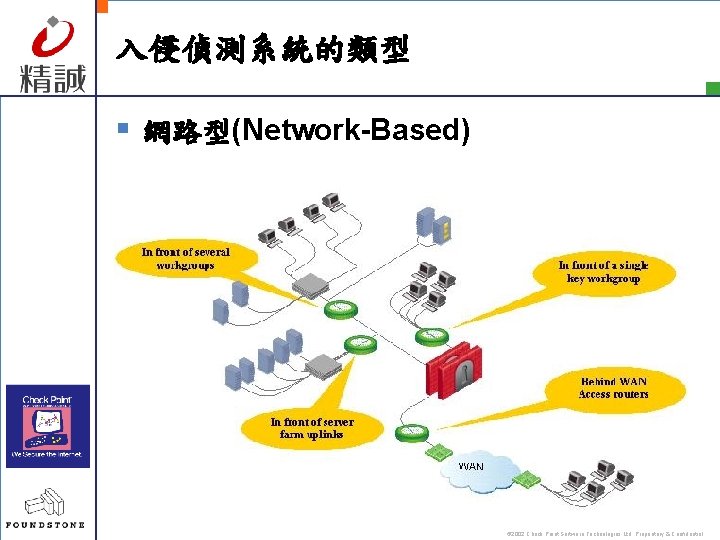
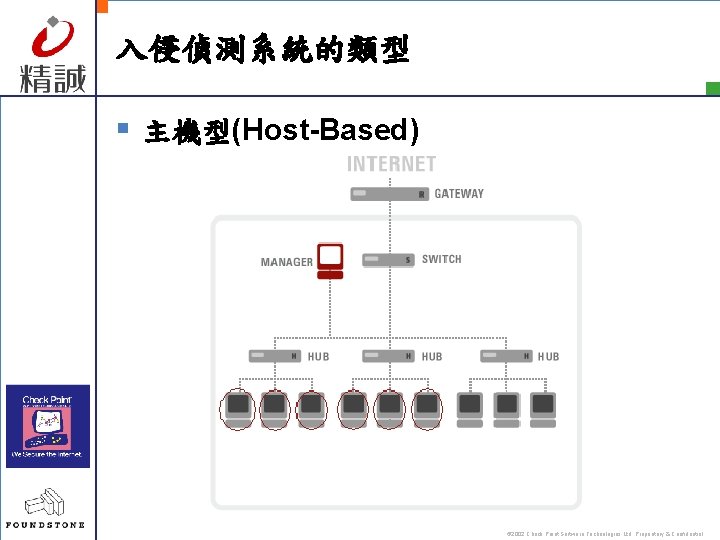
入侵偵測系統的類型 § 網路型(Network-Based) § 主機型(Host-Based) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
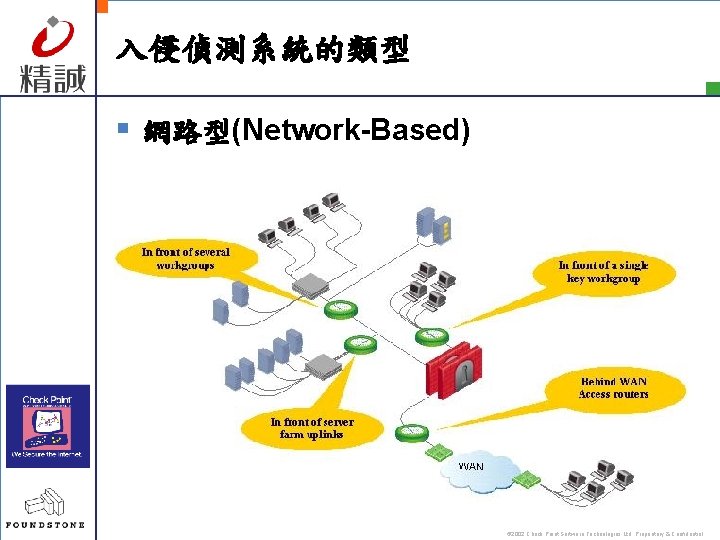
入侵偵測系統的類型 § 網路型(Network-Based) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
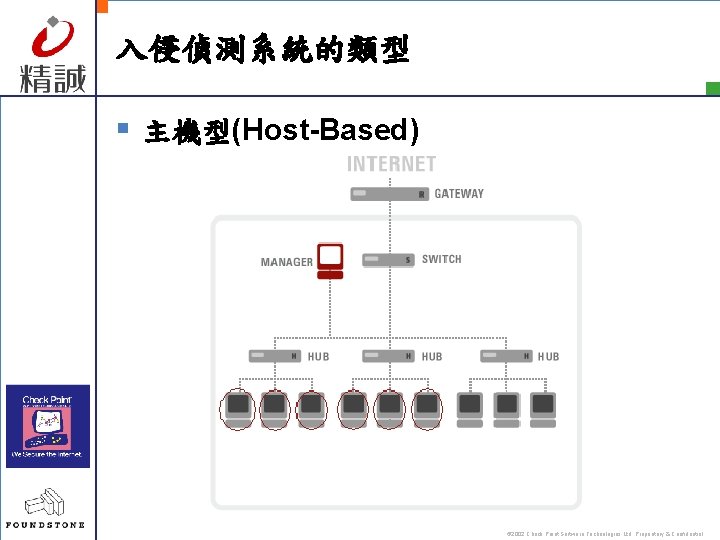
入侵偵測系統的類型 § 主機型(Host-Based) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
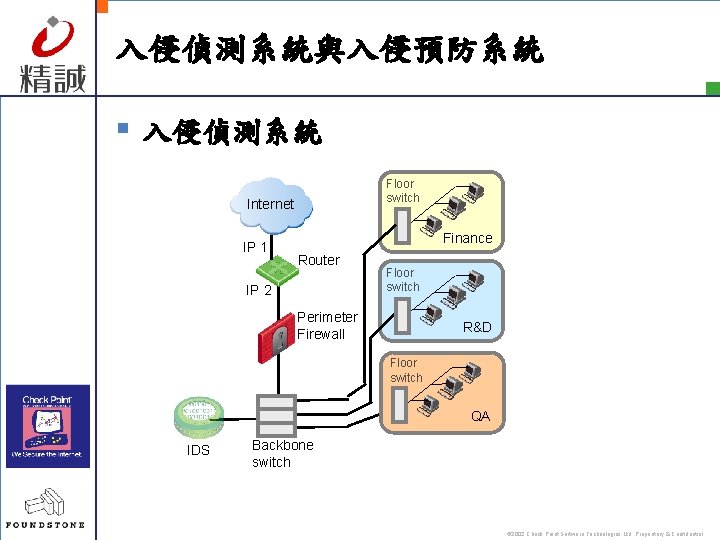
入侵偵測系統與入侵預防系統 § 入侵偵測系統 § 入侵預防系統 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
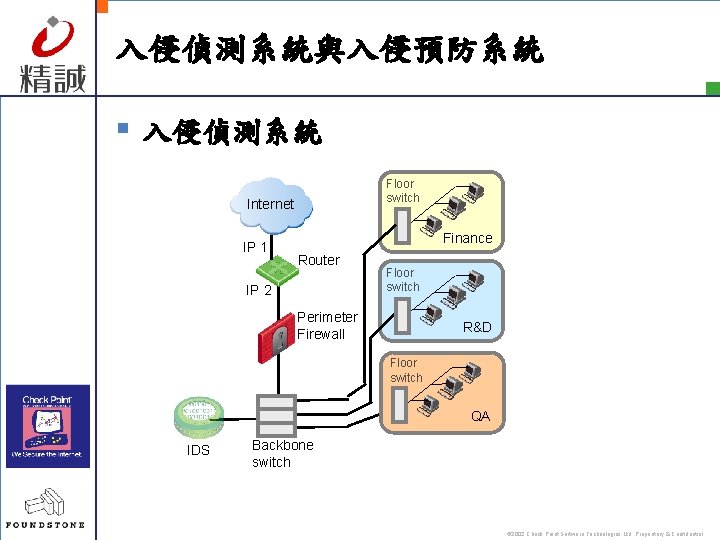
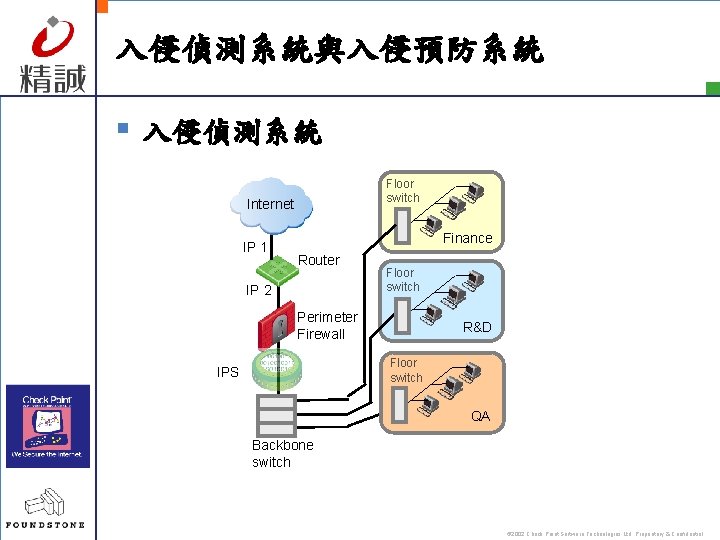
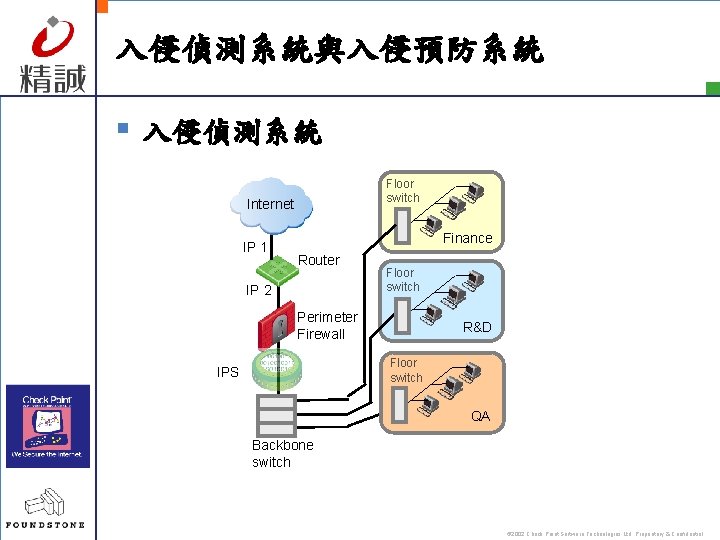
入侵偵測系統與入侵預防系統 § 入侵偵測系統 Floor switch Internet IP 1 Finance Router IP 2 Floor switch Perimeter Firewall R&D Floor switch QA IDS Backbone switch © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
入侵偵測系統與入侵預防系統 § 入侵偵測系統 Floor switch Internet IP 1 Finance Router IP 2 Floor switch Perimeter Firewall R&D Floor switch IPS QA Backbone switch © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
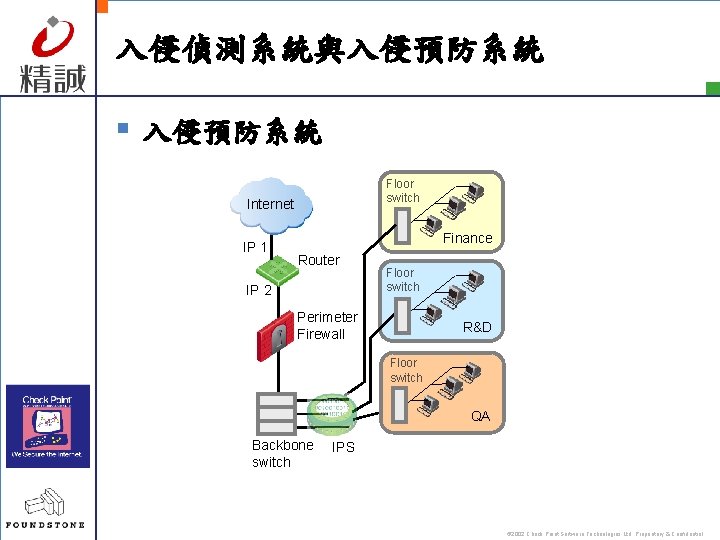
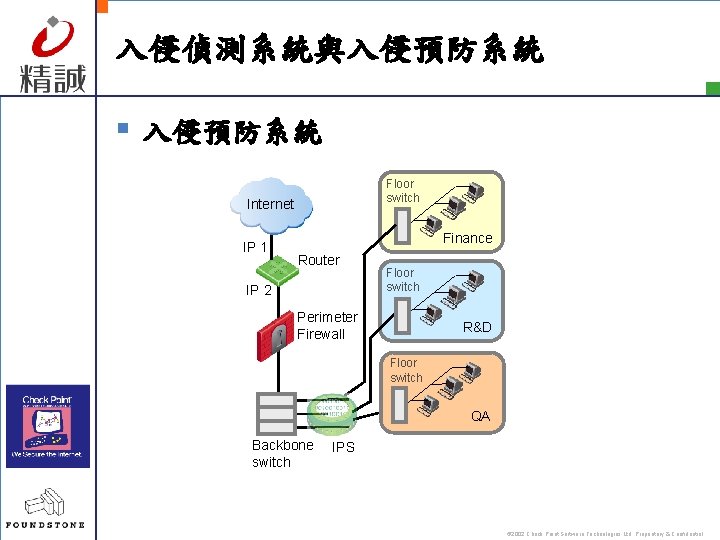
入侵偵測系統與入侵預防系統 § 入侵預防系統 Floor switch Internet IP 1 Finance Router IP 2 Floor switch Perimeter Firewall R&D Floor switch QA Backbone switch IPS © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
Question? © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
防範網路駭客攻擊---弱點評估 Sysware Corporation. 2003
弱點評估 § Introduction © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
弱點及威脅分析 § 軟體本身之漏洞 – Buffers overflow 、Unexpected combinations 、 Unhandleded input § 系統之設定問題 – Default configurations 、Lazy administrators、 Hole creation、Trust relationships § 監看未經加密的流量 § 設計的瑕疵 – TCP/IP protocol © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
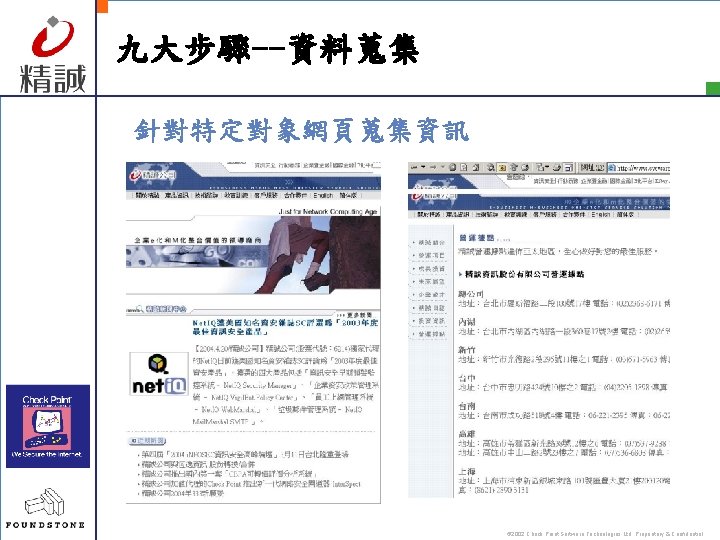
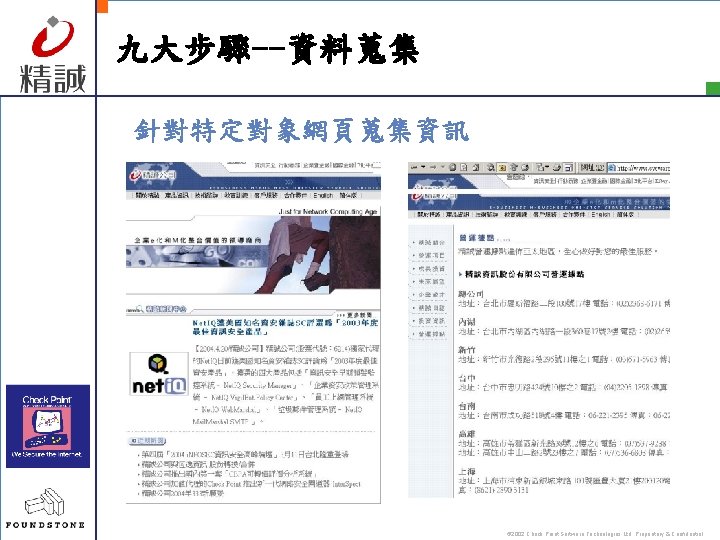
九大步驟--資料蒐集 針對特定對象網頁蒐集資訊 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
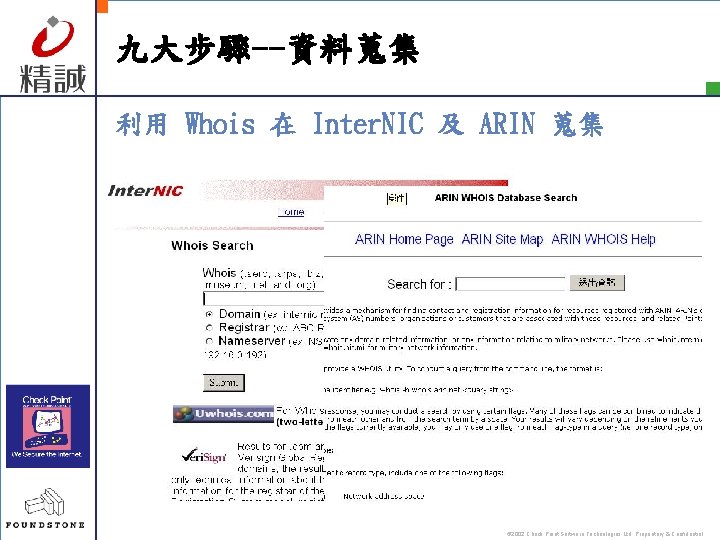
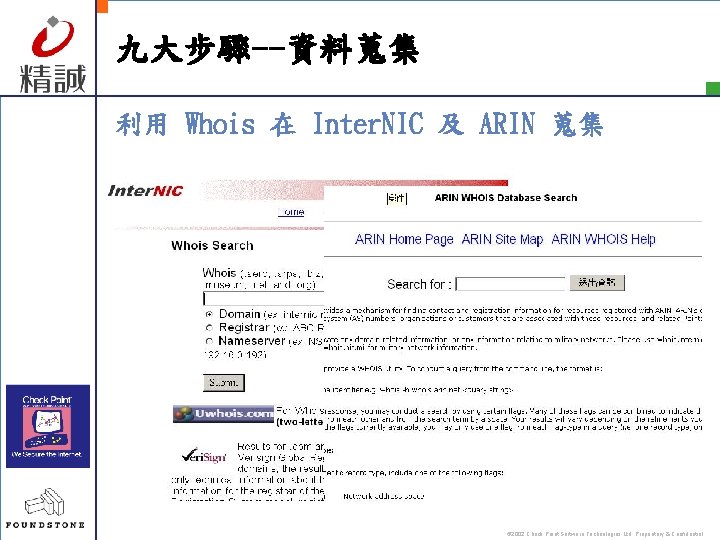
九大步驟--資料蒐集 利用 Whois 在 Inter. NIC 及 ARIN 蒐集 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
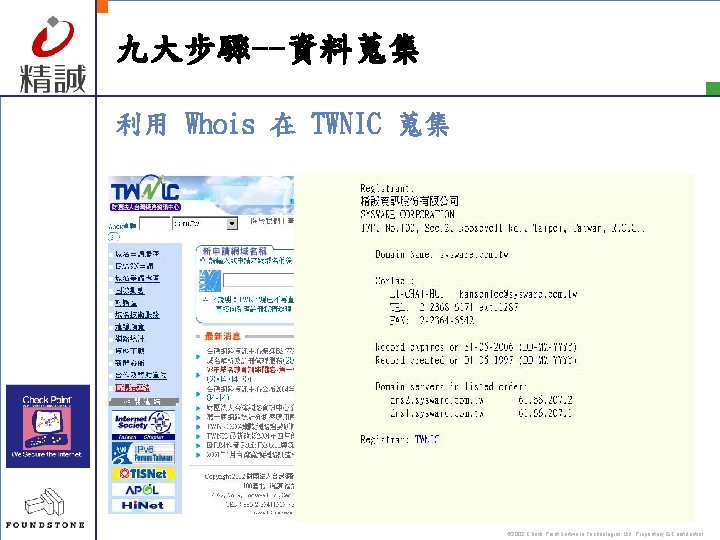
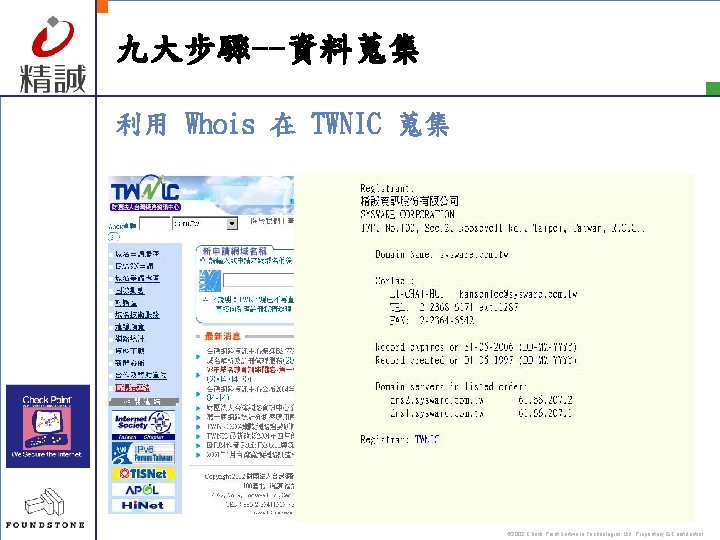
九大步驟--資料蒐集 利用 Whois 在 TWNIC 蒐集 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--資料蒐集 § DNS zone transfer § nslookup § A record : IP; HINFO record : OS type © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
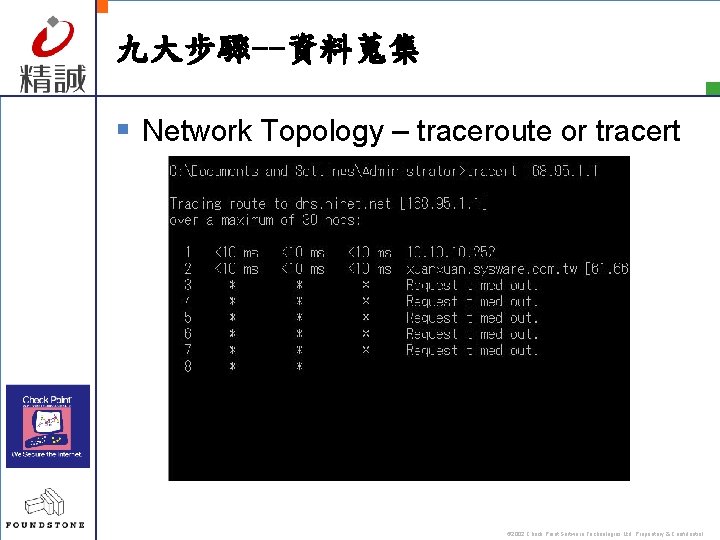
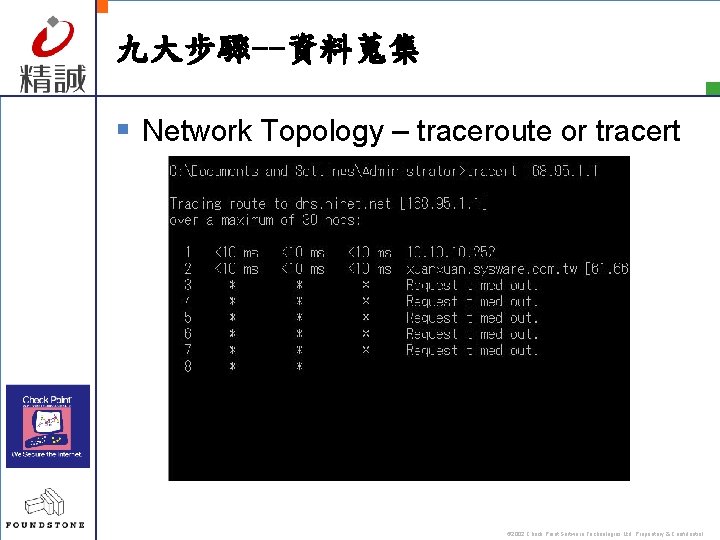
九大步驟--資料蒐集 § Network Topology – traceroute or tracert © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § ping: gping and fping $gping 203. 74. 128. 1 254 | fping -a § nmap $nmap –sp 192. 168. 1. 0/24 § Icmpenum: icmp echo, icmp time stamp request, and icmp info $icmpenum –i 2 –c 192. 168. 1. 0 192. 168. 1. 1 is up 192. 168. 1. 5 is up © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § § § Strobe Udp_scan netcat nmap Net. Scan Tool Pro 2000 Super. Scan © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
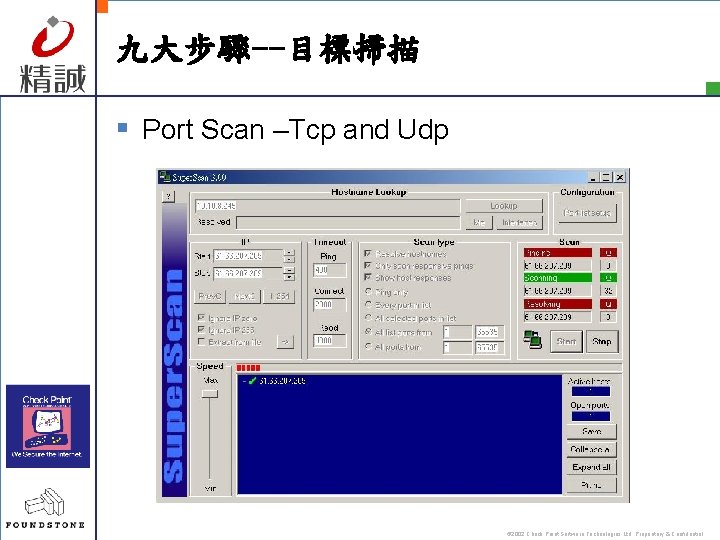
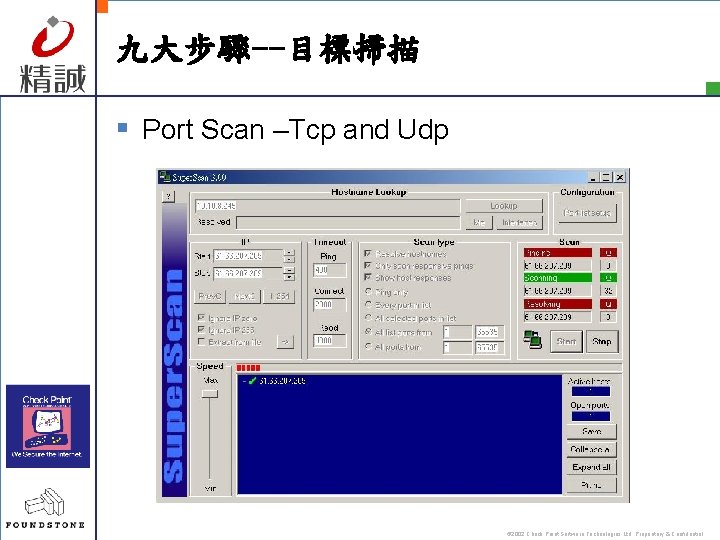
九大步驟--目標掃描 § Port Scan –Tcp and Udp © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § 作業系統偵查 – 主動性 – 被動性 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § 主動性作業系統偵查 – FIN 封包試探, ISN辨識, 監視“Don’t fragment bit”, 追蹤TCP initial window size, ACK value, icmp 錯 誤訊息, TOS(type of service), 重複封包分割處理, TCP選項 – nmap – queso © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § 被動性作業系統偵查 – TTL, Window Size, DF, TOS – snort – siphon © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--目標掃描 § 社交 程 – 詐騙手段 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential

九大步驟--弱點刺探 § Win NT/2000 § 目標 – CIFS/SMB – Net. BIOS § 具 – Win Resource Kit – Null Session – others © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--弱點刺探 § Null Session – – net use \x. xIPS$ “ “ /u: ” “ Block TCP/UDP 135 -139 Disable Net. BIOS Over Restrict. Anonymous • HKey_LOCAL_MACHINESYSTEMCurrent. C ontril. SetControlLSA • MMC -> 本機原則 ->安全性選項 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--弱點刺探 § 網路資源與分享 – 找出網域, 節點, 及服務 – Net view, nbtstat, nbtscan, nltest, Legion, … – Epdump, getmac, netdom, netviewx, enum, … © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--弱點刺探 § 使用者與群組 – nbtstat, nbtscan, enum – sid 2 user, user 2 sid • security identifier • rid: 500, 501, 1000 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--弱點刺探 § 應用程式與標誌 – telnet, netcat © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--取得初步權限 § 密碼猜測 – 空的密碼 • NTIS – admin, test, password, …. . – 字典攻擊法 • Legion, Net. BIOS Audition Tool, … © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--取得初步權限 § 網路監聽密碼雜湊 – Chanllege/Response – Lanman hash – Tools: L 0 pht. Crack, John © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--取得初步權限 § 緩衝區溢位攻擊 – 針對 IIS 及 Outlook © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
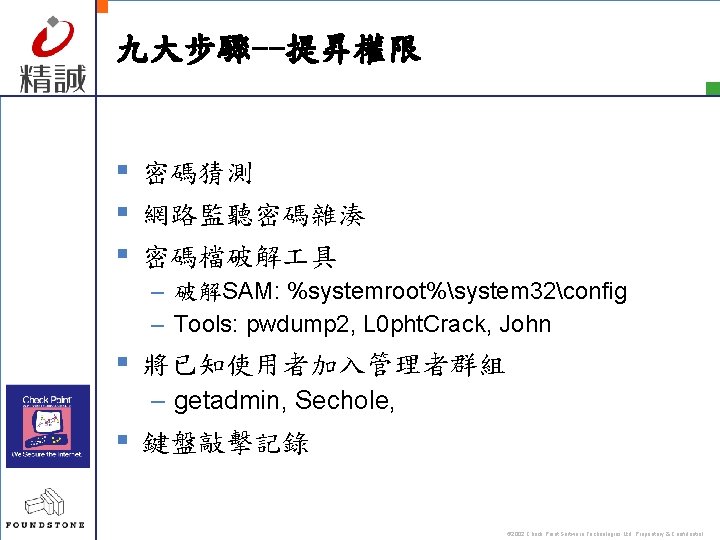
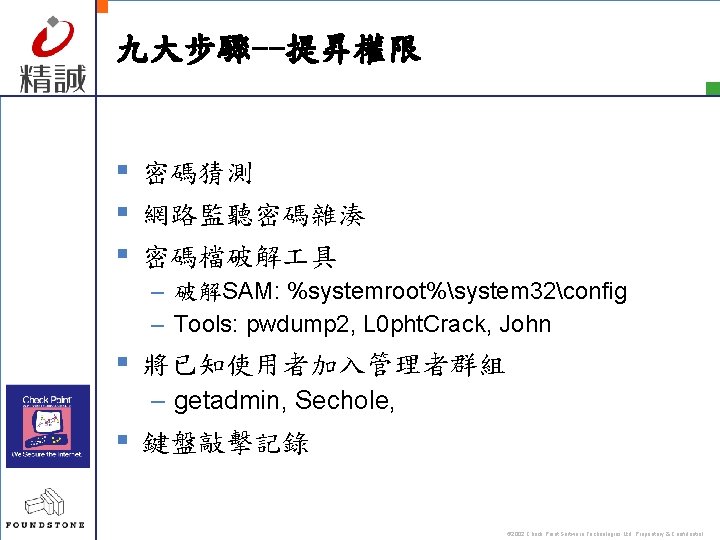
九大步驟--提昇權限 § 密碼猜測 § 網路監聽密碼雜湊 § 密碼檔破解 具 – 破解SAM: %systemroot%system 32config – Tools: pwdump 2, L 0 pht. Crack, John § 將已知使用者加入管理者群組 – getadmin, Sechole, § 鍵盤敲擊記錄 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--建立後門 § 啟動的操控 – HKLMSOFTWAREMicrosoftWindowsCurrent. V ersion, – Run, Run. Once. Ex, Run. Services § 遠端控制 – Telnet service © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
九大步驟--消滅證據 § 關閉稽核 § 清除記錄 –elsave § 隱藏檔案 –Attrib –隱藏至NTFS file streaming © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
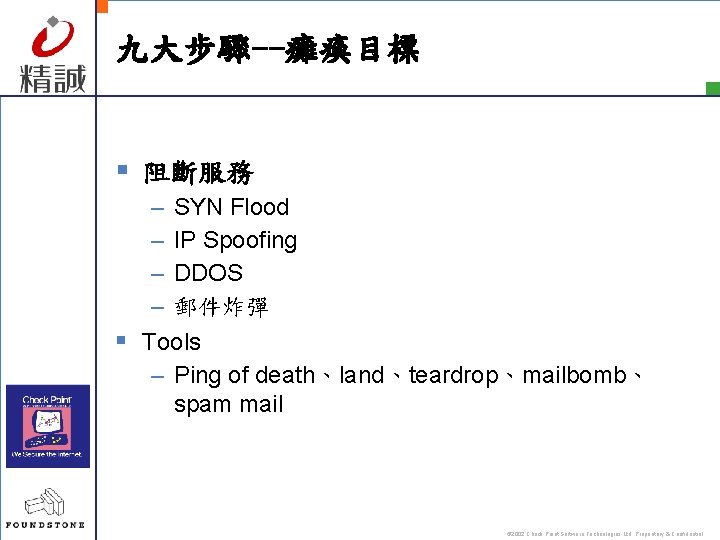
九大步驟--癱瘓目標 § 阻斷服務 – SYN Flood – IP Spoofing – DDOS – 郵件炸彈 § Tools – Ping of death、land、teardrop、mailbomb、 spam mail © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
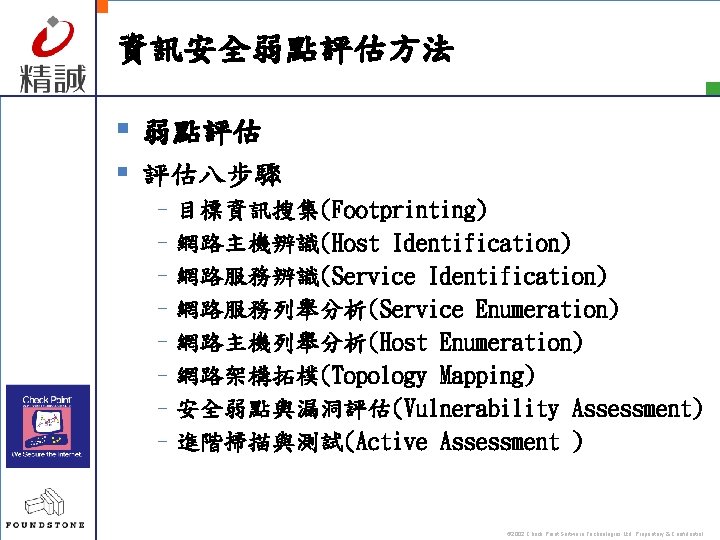
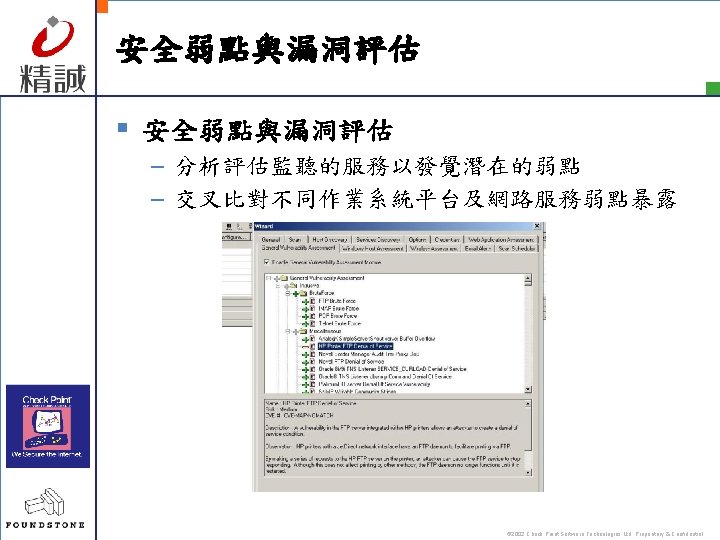
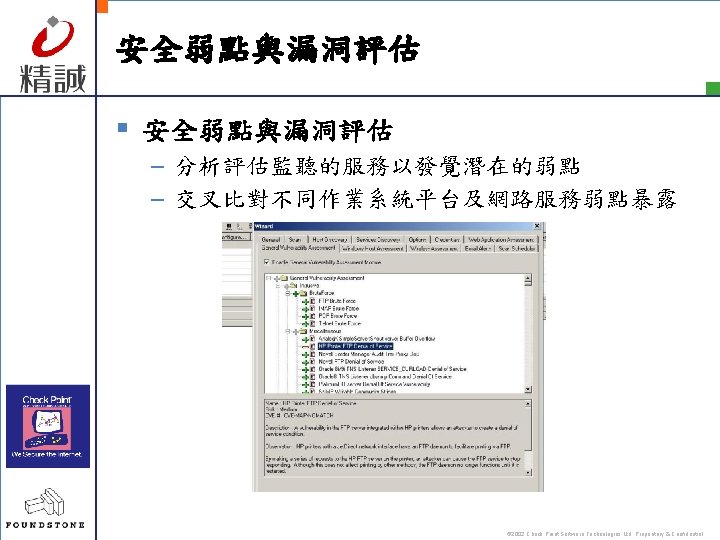
資訊安全弱點評估方法 § 弱點評估 § 評估八步驟 –目標資訊搜集(Footprinting) –網路主機辨識(Host Identification) –網路服務辨識(Service Identification) –網路服務列舉分析(Service Enumeration) –網路主機列舉分析(Host Enumeration) –網路架構拓樸(Topology Mapping) –安全弱點與漏洞評估(Vulnerability Assessment) –進階掃描與測試(Active Assessment ) © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
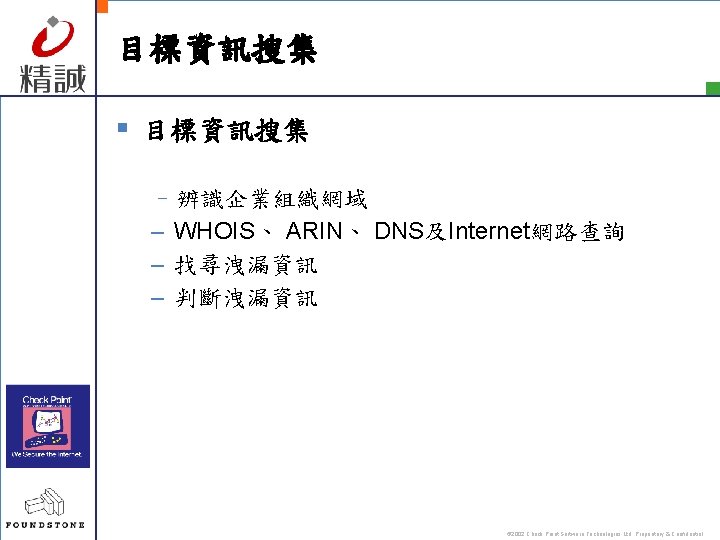
目標資訊搜集 § 目標資訊搜集 –辨識企業組織網域 – WHOIS、 ARIN、 DNS及Internet網路查詢 – 找尋洩漏資訊 – 判斷洩漏資訊 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
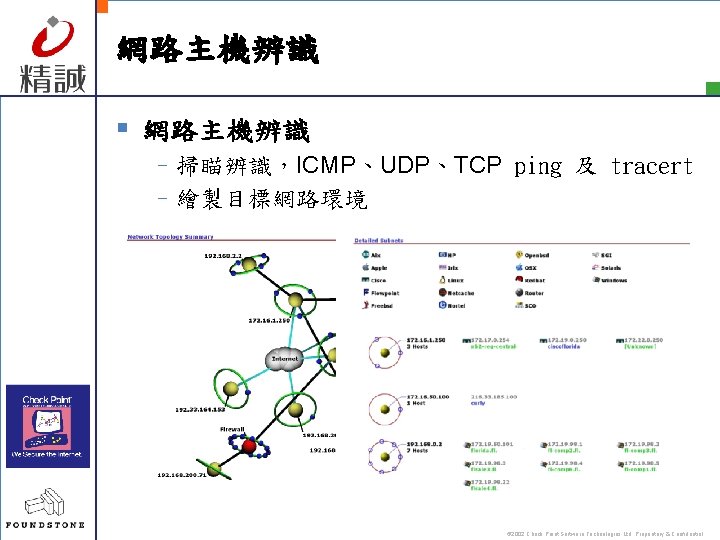
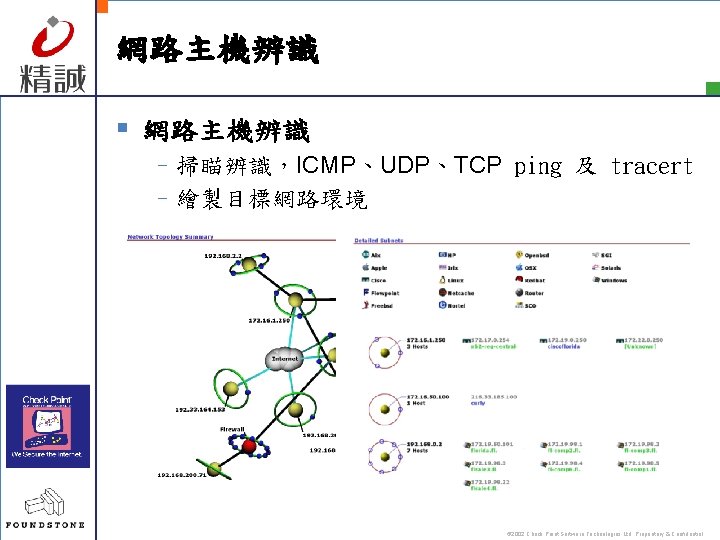
網路主機辨識 § 網路主機辨識 –掃瞄辨識,ICMP、UDP、TCP ping 及 tracert –繪製目標網路環境 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
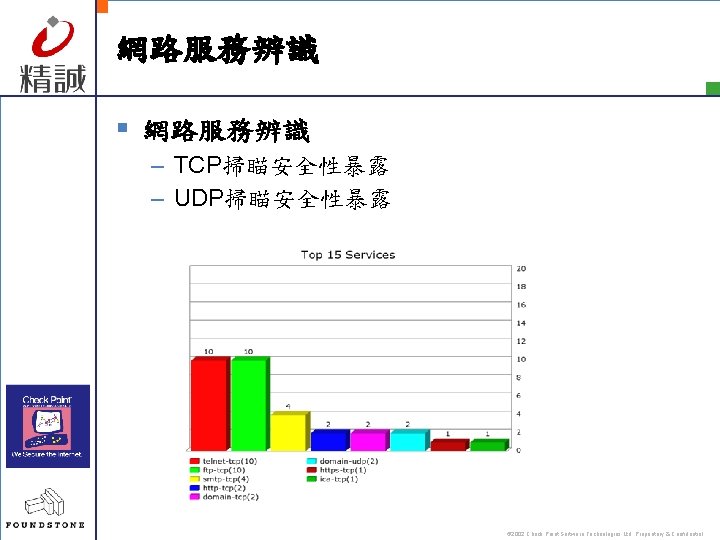
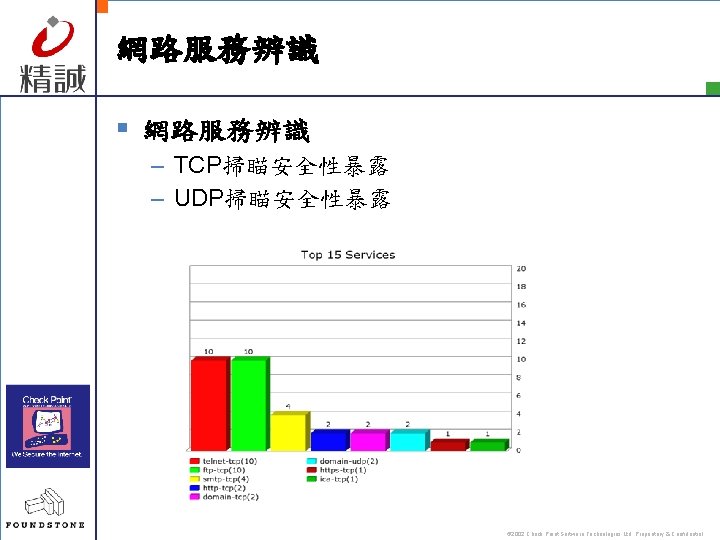
網路服務辨識 § 網路服務辨識 – TCP掃瞄安全性暴露 – UDP掃瞄安全性暴露 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
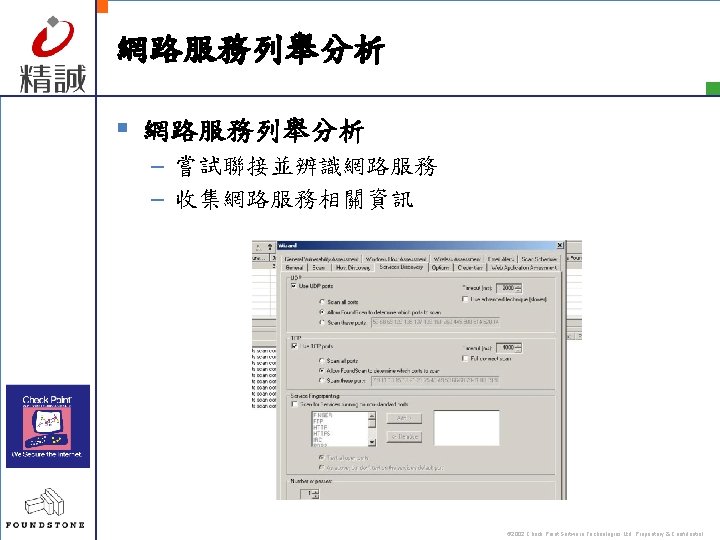
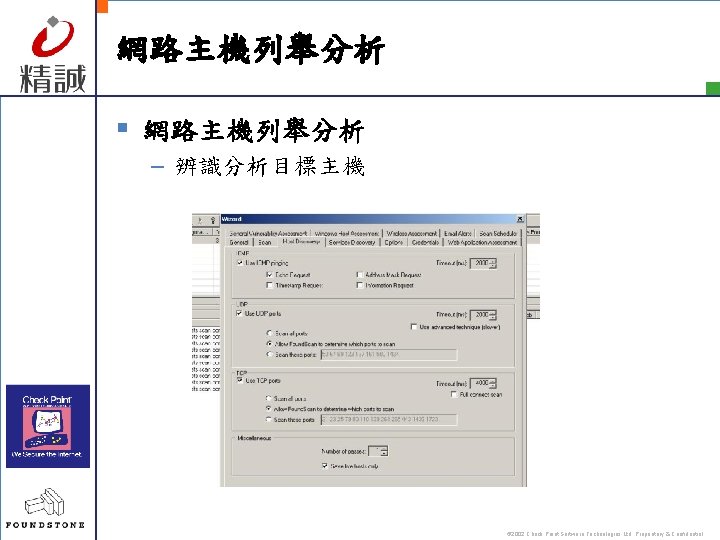
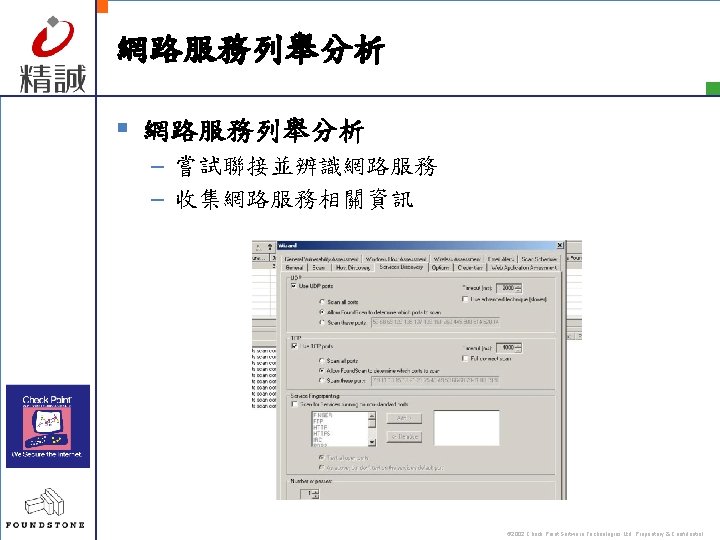
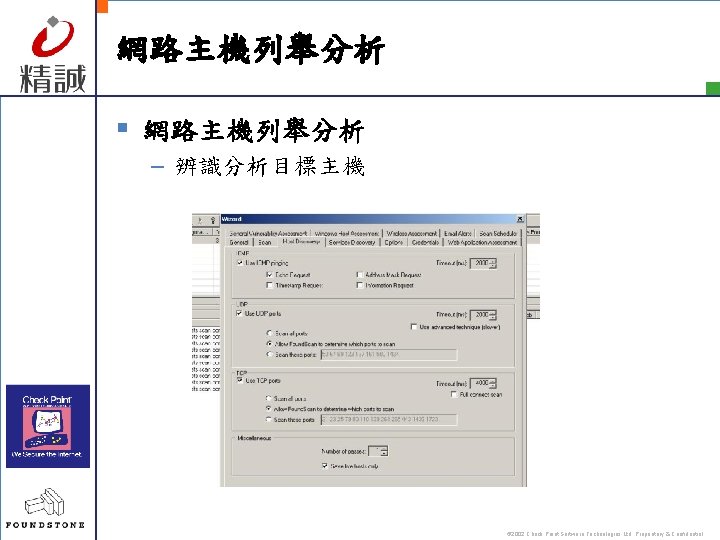
網路主機列舉分析 § 網路主機列舉分析 – 辨識分析目標主機 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
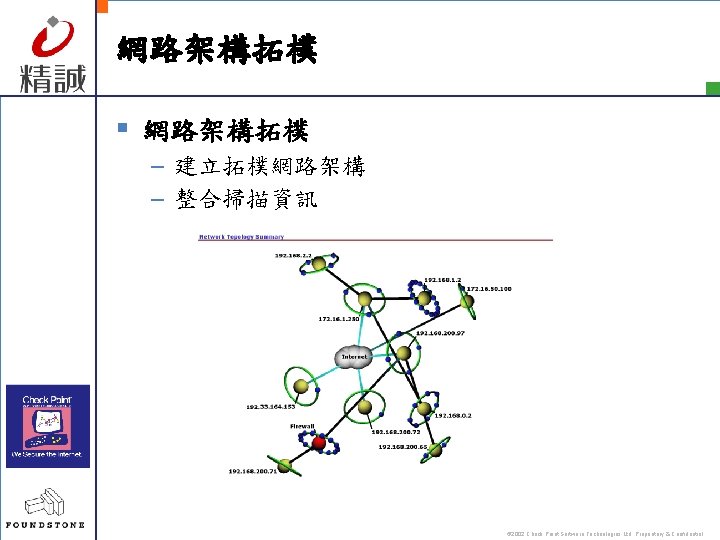
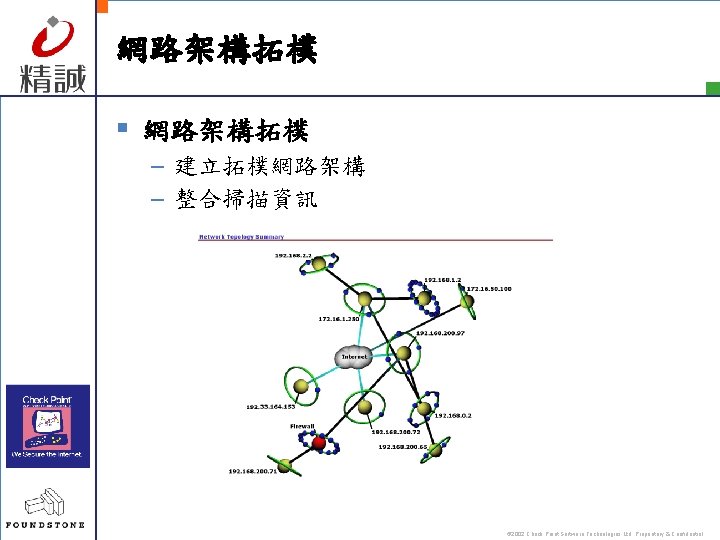
網路架構拓樸 § 網路架構拓樸 – 建立拓樸網路架構 – 整合掃描資訊 © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential
THANK YOU! § Questions? © 2002 Check Point Software Technologies Ltd. Proprietary & Confidential