Mashup Security by Compilation Tamara Rezk These slides
Mashup Security by Compilation Tamara Rezk These slides discuss joint work with Zhengqin Luo and Jose Santos February 22 nd , 2013
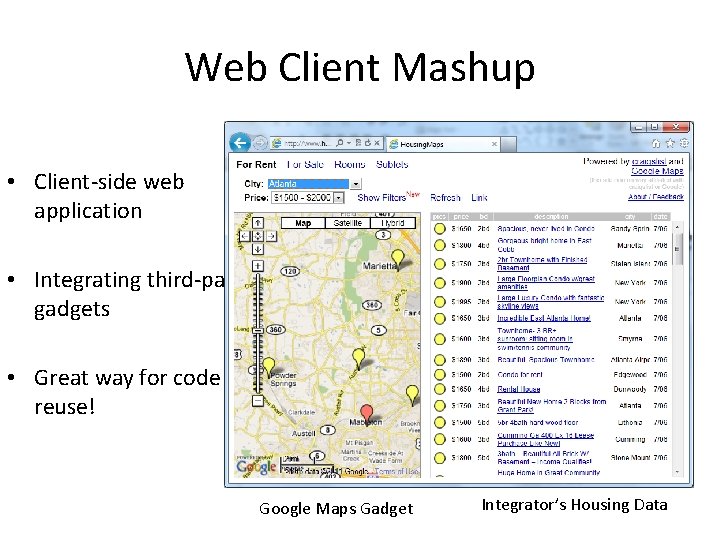
Web Client Mashup • Client-side web application • Integrating third-party gadgets • Great way for code reuse! Google Maps Gadget Integrator’s Housing Data
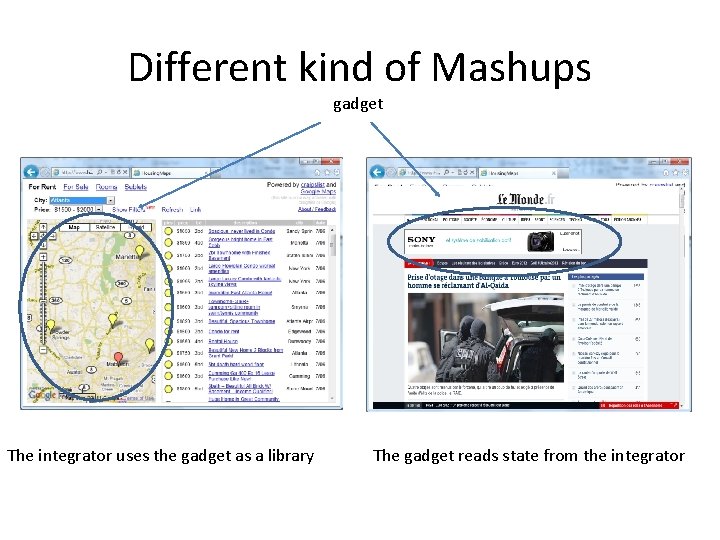
Different kind of Mashups gadget The integrator uses the gadget as a library The gadget reads state from the integrator
Programming model • Mashups written in HTML + Javascript; • Two ways to include external gadgets: – Using script tag – Using frame tag
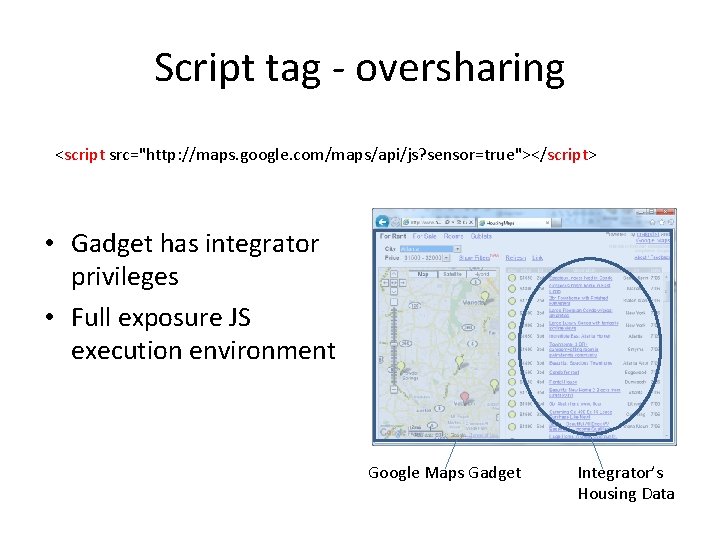
Script tag - oversharing <script src="http: //maps. google. com/maps/api/js? sensor=true"></script> • Gadget has integrator privileges • Full exposure JS execution environment Google Maps Gadget Integrator’s Housing Data
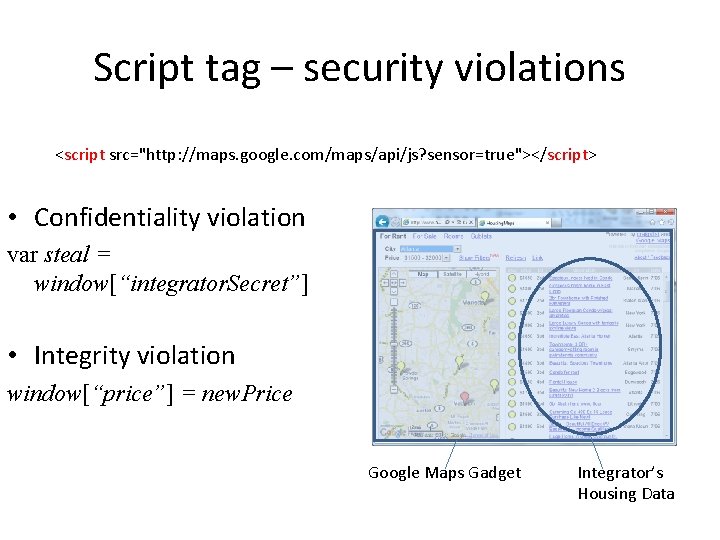
Script tag – security violations <script src="http: //maps. google. com/maps/api/js? sensor=true"></script> • Confidentiality violation var steal = window[“integrator. Secret”] • Integrity violation window[“price”] = new. Price Google Maps Gadget Integrator’s Housing Data
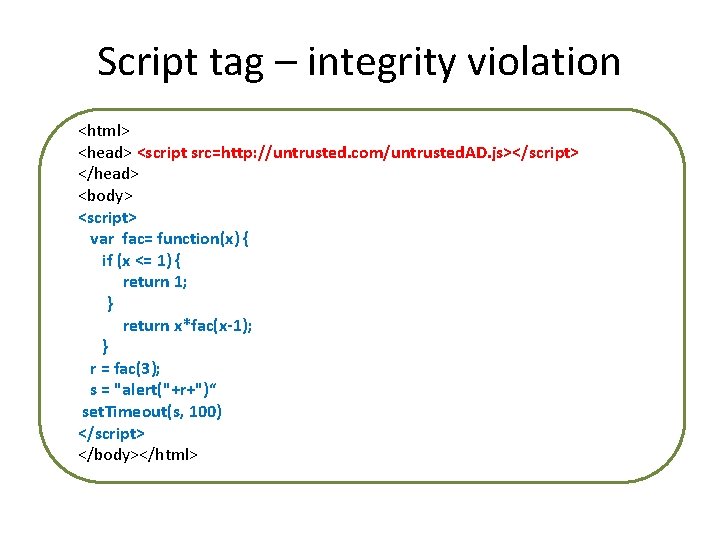
Script tag – integrity violation <html> <head> <script src=http: //untrusted. com/untrusted. AD. js></script> </head> <body> <script> var fac= function(x) { if (x <= 1) { return 1; } return x*fac(x-1); } r = fac(3); s = "alert("+r+")“ set. Timeout(s, 100) </script> </body></html>
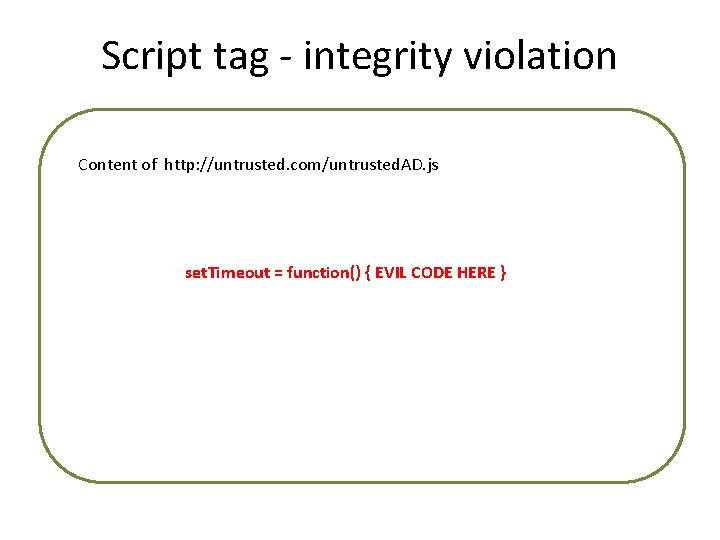
Script tag - integrity violation Content of http: //untrusted. com/untrusted. AD. js set. Timeout = function() { EVIL CODE HERE }
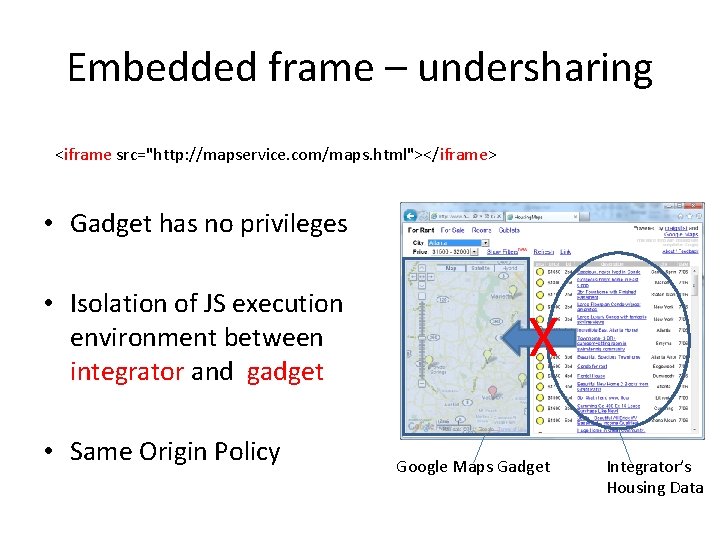
Embedded frame – undersharing <iframe src="http: //mapservice. com/maps. html"></iframe> • Gadget has no privileges • Same Origin Policy X • Isolation of JS execution environment between integrator and gadget Google Maps Gadget Integrator’s Housing Data
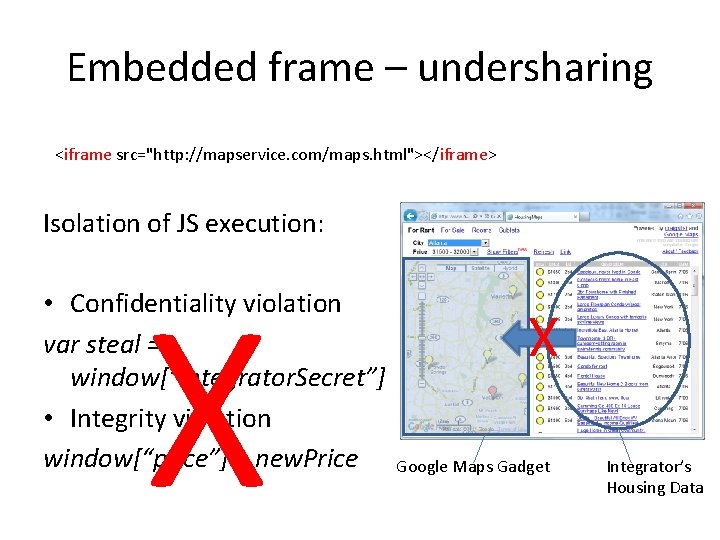
Embedded frame – undersharing <iframe src="http: //mapservice. com/maps. html"></iframe> Isolation of JS execution: X X • Confidentiality violation var steal = window[“integrator. Secret”] • Integrity violation window[“price”] = new. Price Google Maps Gadget Integrator’s Housing Data
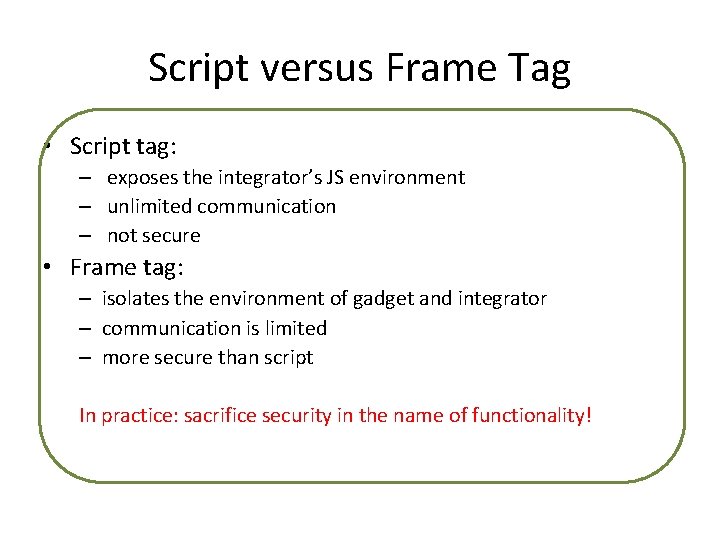
Script versus Frame Tag • Script tag: – exposes the integrator’s JS environment – unlimited communication – not secure • Frame tag: – isolates the environment of gadget and integrator – communication is limited – more secure than script In practice: sacrifice security in the name of functionality!
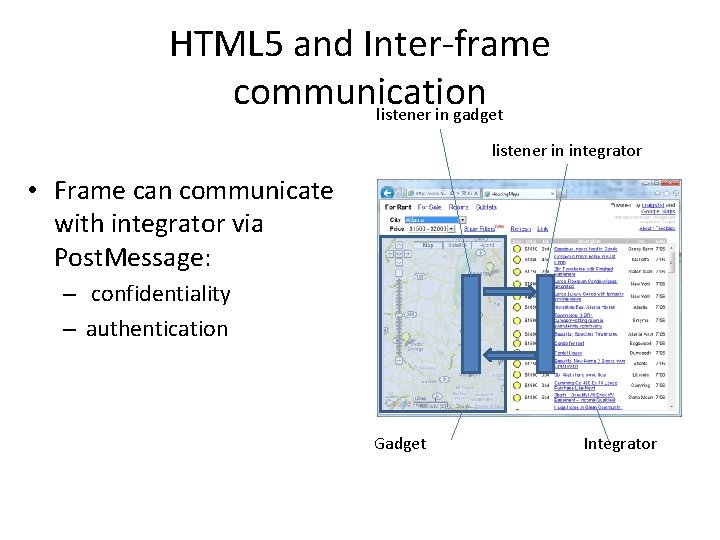
HTML 5 and Inter-frame communication listener in gadget listener in integrator • Frame can communicate with integrator via Post. Message: – confidentiality – authentication Gadget Integrator
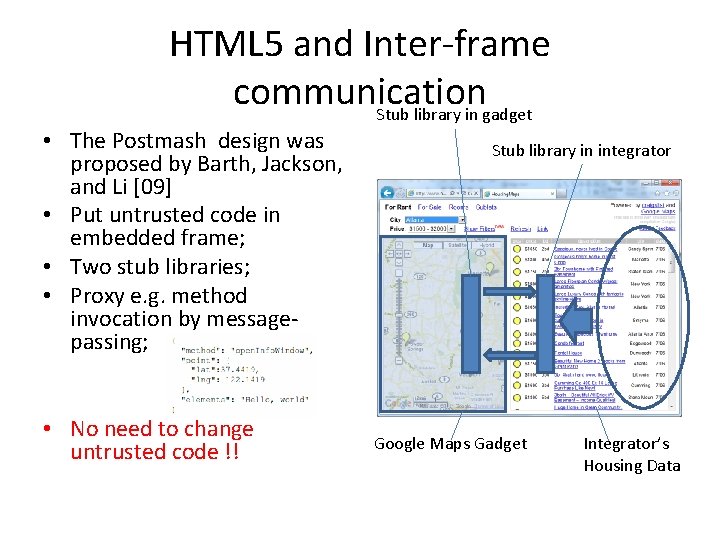
HTML 5 and Inter-frame communication Stub library in gadget • The Postmash design was proposed by Barth, Jackson, and Li [09] • Put untrusted code in embedded frame; • Two stub libraries; • Proxy e. g. method invocation by messagepassing; • No need to change untrusted code !! Stub library in integrator Google Maps Gadget Integrator’s Housing Data
Postmash • How to transform an insecure mashup to a mashup following the Postmash design? – Manually writing two stub libraries (gadget dependent); – Manually rewriting of integrators’ code; • Our proposal : automate it and characterize the security property that it enforces: Mashic Compiler [CSF’ 12]
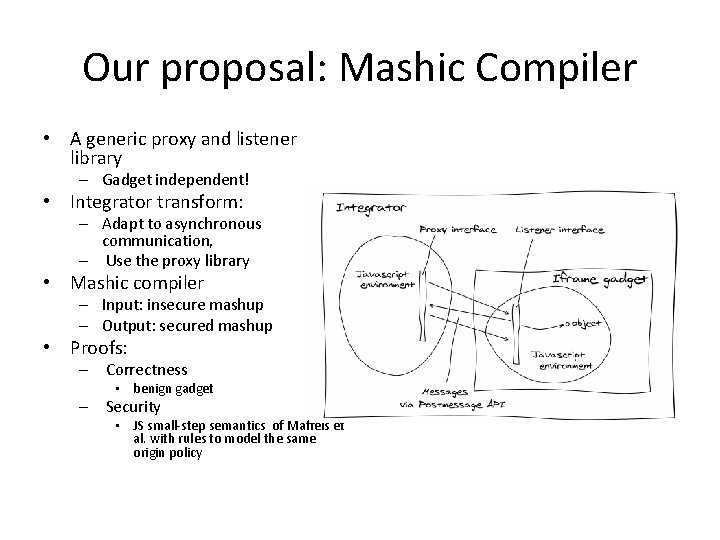
Our proposal: Mashic Compiler • A generic proxy and listener library – Gadget independent! • Integrator transform: – Adapt to asynchronous communication, – Use the proxy library • Mashic compiler – Input: insecure mashup – Output: secured mashup • Proofs: – Correctness • benign gadget – Security • JS small-step semantics of Maffeis et al. with rules to model the same origin policy
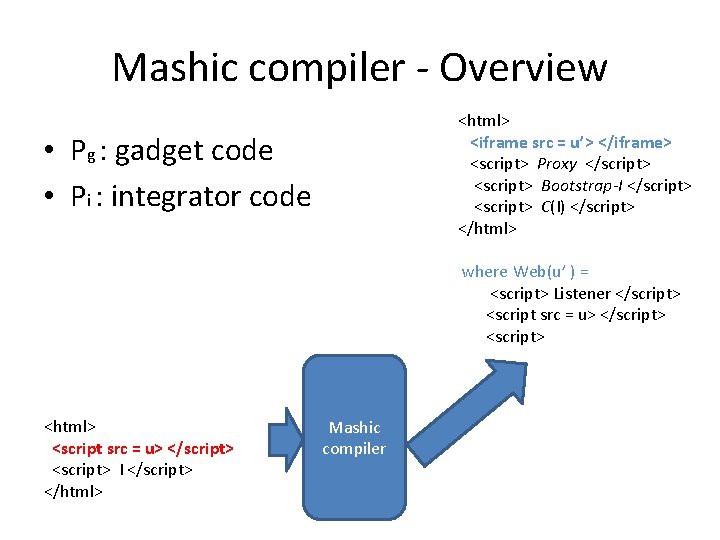
Mashic compiler - Overview <html> <iframe src = u’> </iframe> <script> Proxy </script> <script> Bootstrap-I </script> <script> C(I) </script> </html> • Pg : gadget code • Pi : integrator code where Web(u’ ) = <script> Listener </script> <script src = u> </script> <html> <script src = u> </script> <script> I </script> </html> Mashic compiler
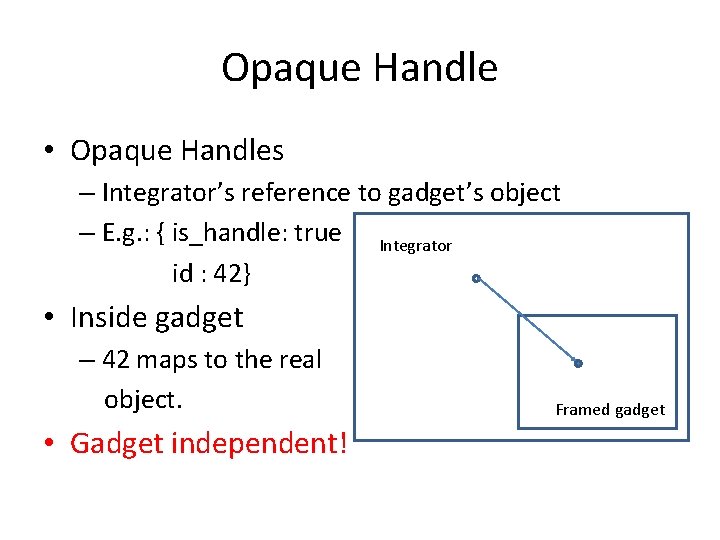
Opaque Handle • Opaque Handles – Integrator’s reference to gadget’s object – E. g. : { is_handle: true Integrator id : 42} • Inside gadget – 42 maps to the real object. • Gadget independent! Framed gadget
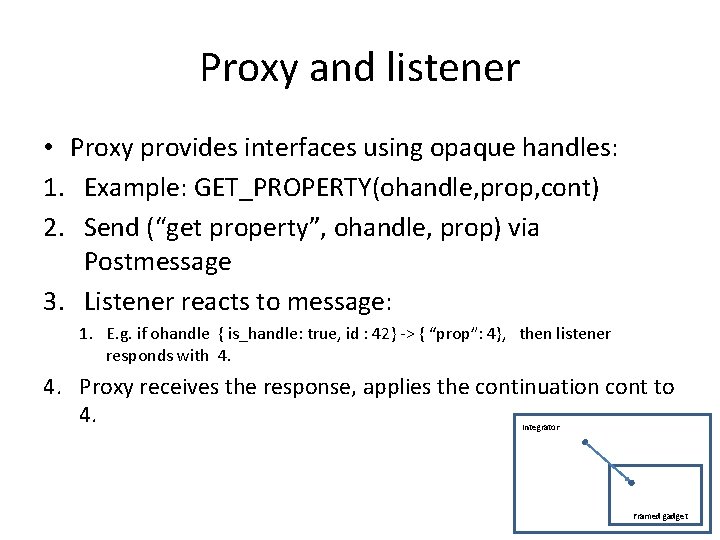
Proxy and listener • Proxy provides interfaces using opaque handles: 1. Example: GET_PROPERTY(ohandle, prop, cont) 2. Send (“get property”, ohandle, prop) via Postmessage 3. Listener reacts to message: 1. E. g. if ohandle { is_handle: true, id : 42} -> { “prop”: 4}, then listener responds with 4. Proxy receives the response, applies the continuation cont to 4. Integrator Framed gadget
A minimal set of Proxy Interfaces • GET_GLOBAL_REF – Get global property • CALL_METHOD – Call a method • CALL_FUNCTION – Call a function • ASSIGN_PROPERTY – Property assignment • General enough to encode most real-world mashups!!
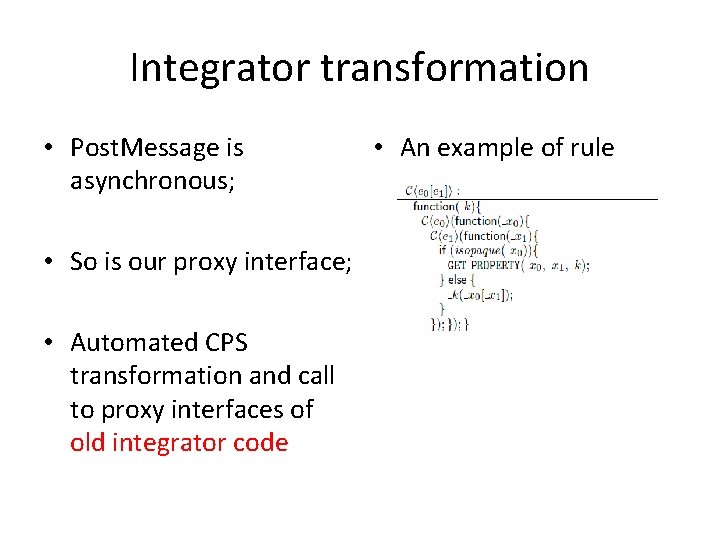
Integrator transformation • Post. Message is asynchronous; • So is our proxy interface; • Automated CPS transformation and call to proxy interfaces of old integrator code • An example of rule
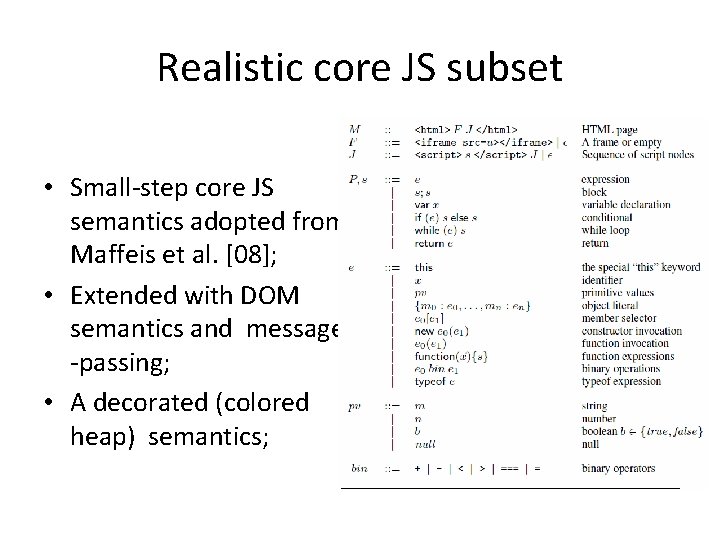
Realistic core JS subset • Small-step core JS semantics adopted from Maffeis et al. [08]; • Extended with DOM semantics and message -passing; • A decorated (colored heap) semantics;
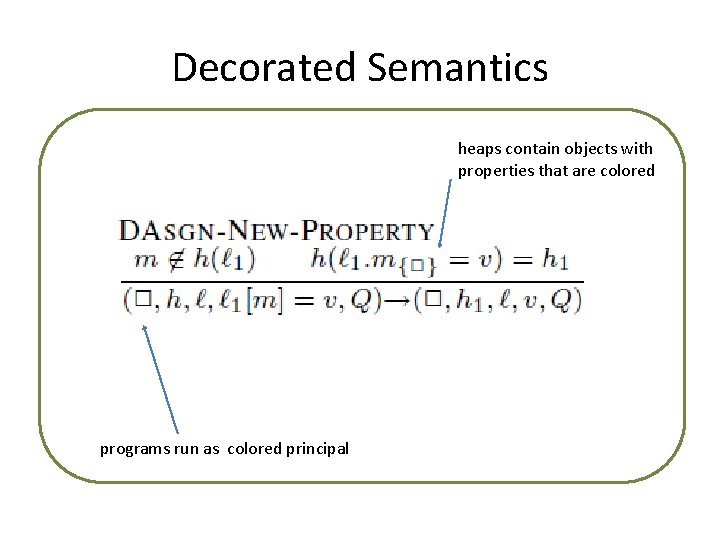
Decorated Semantics heaps contain objects with properties that are colored programs run as colored principal
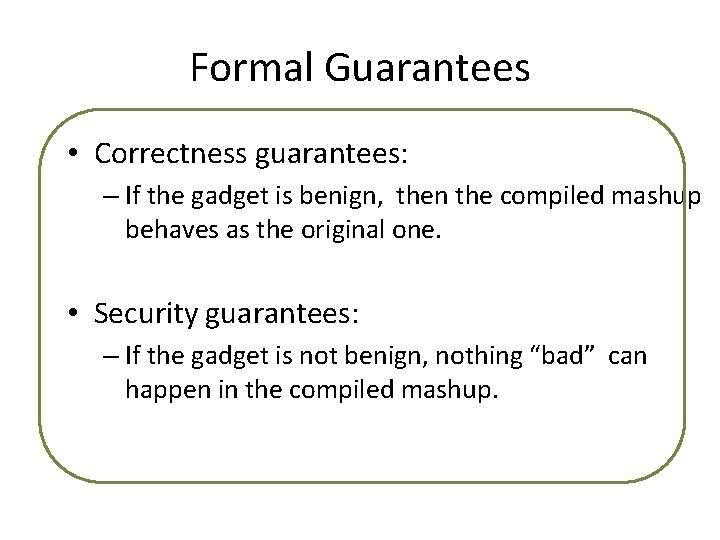
Formal Guarantees • Correctness guarantees: – If the gadget is benign, then the compiled mashup behaves as the original one. • Security guarantees: – If the gadget is not benign, nothing “bad” can happen in the compiled mashup.
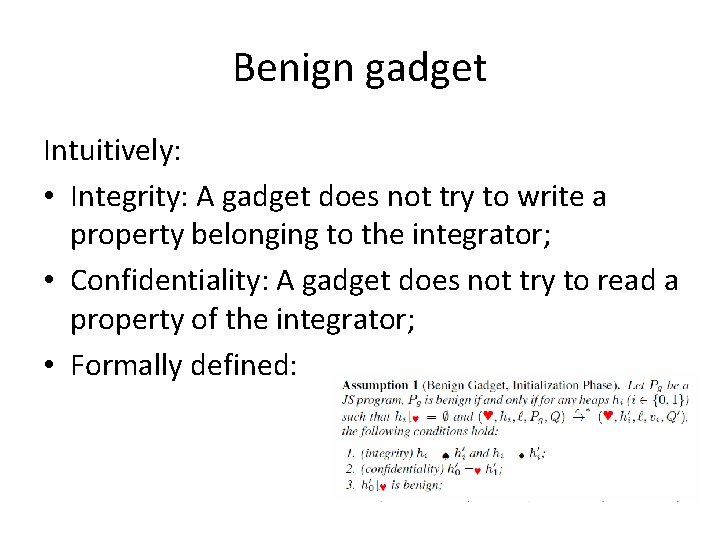
Benign gadget Intuitively: • Integrity: A gadget does not try to write a property belonging to the integrator; • Confidentiality: A gadget does not try to read a property of the integrator; • Formally defined:
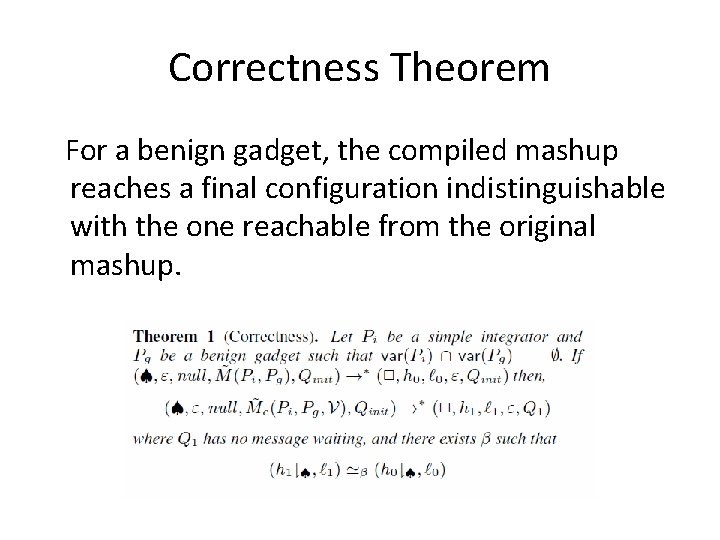
Correctness Theorem For a benign gadget, the compiled mashup reaches a final configuration indistinguishable with the one reachable from the original mashup.
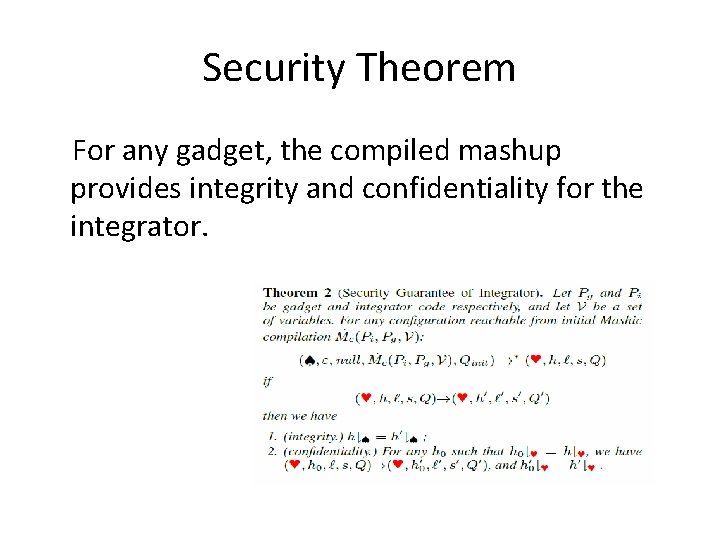
Security Theorem For any gadget, the compiled mashup provides integrity and confidentiality for the integrator.
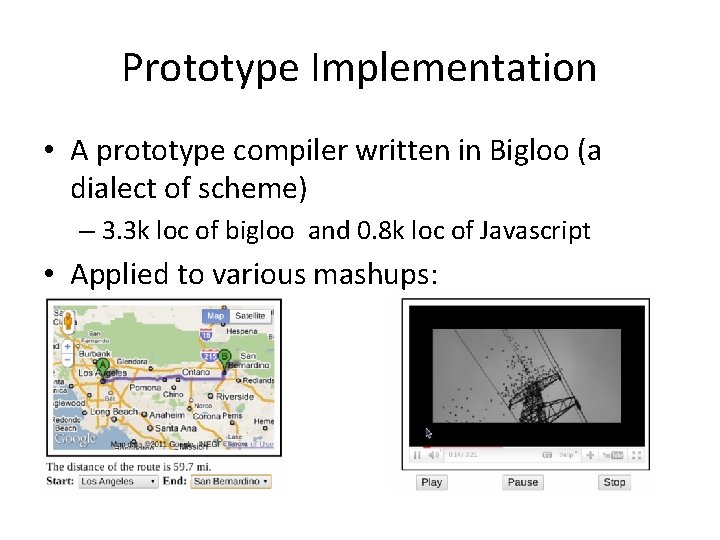
Prototype Implementation • A prototype compiler written in Bigloo (a dialect of scheme) – 3. 3 k loc of bigloo and 0. 8 k loc of Javascript • Applied to various mashups:
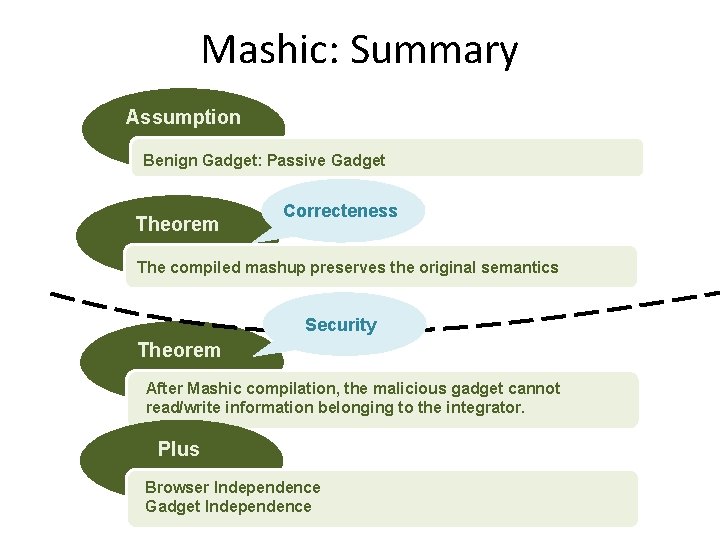
Mashic: Summary Assumption Benign Gadget: Passive Gadget Theorem Correcteness The compiled mashup preserves the original semantics Security Theorem After Mashic compilation, the malicious gadget cannot read/write information belonging to the integrator. Plus Browser Independence Gadget Independence
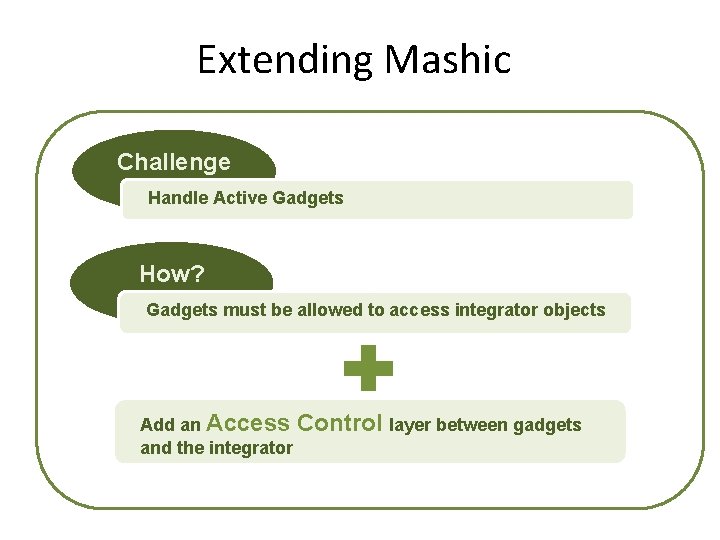
Extending Mashic Challenge Handle Active Gadgets How? Gadgets must be allowed to access integrator objects Add an Access Control layer between gadgets and the integrator
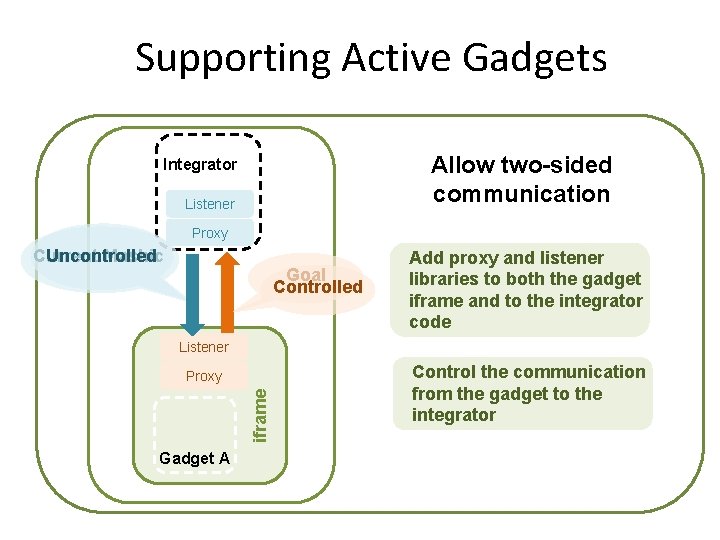
Supporting Active Gadgets Integrator. js Integrator Allow two-sided communication Listener Proxy Goal Controlled Add proxy and listener libraries to both the gadget iframe and to the integrator code Listener Proxy iframe Page. html Current Uncontrolled Mashic Gadget A Control the communication from the gadget to the integrator
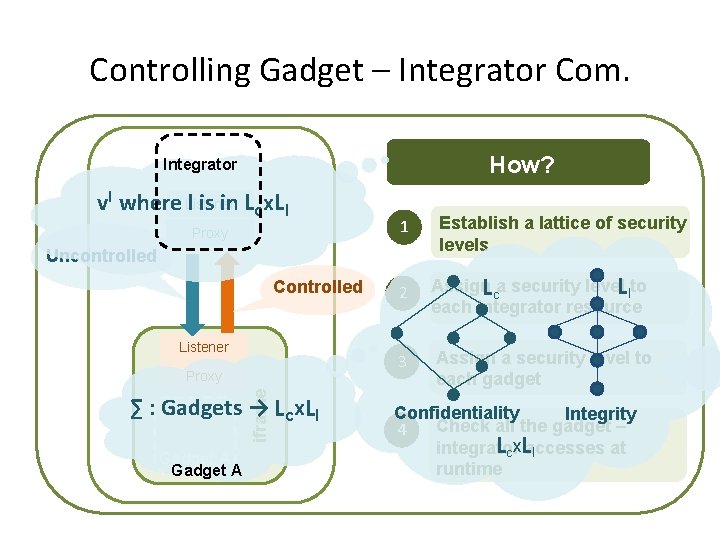
Controlling Gadget – Integrator Com. Integrator. js Integrator How? vl where Listener l is in Lcx. LI Proxy 1 Controlled Listener Proxy iframe Page. html Uncontrolled ∑ : Gadgets → Lcx. LI Gadget A Establish a lattice of security levels 2 Assign. Lca security level. LIto each integrator resource 3 Assign a security level to each gadget Confidentiality Integrity Check all the gadget – 4 Lcx. Laccesses integrator at I runtime
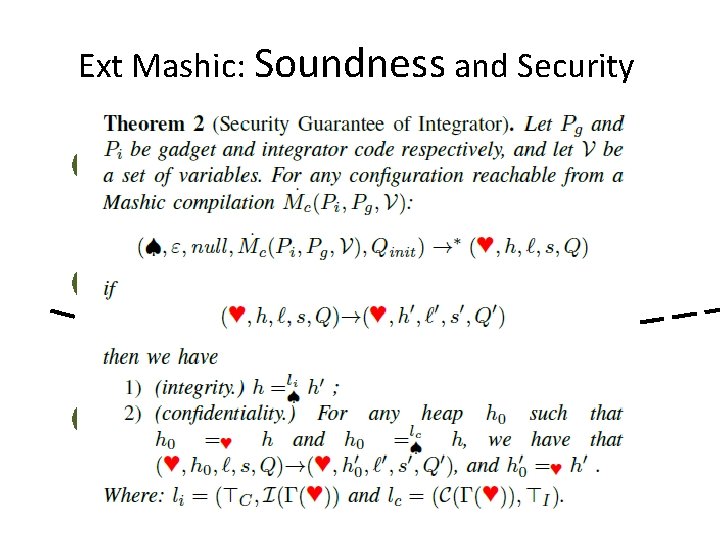
Ext Mashic: Soundness and Security Assumption Benign Gadget: A gadget that only tries to access integrator information compatible with its security level Theorem Correcteness The compiled mashup preserves the original semantics Theorem Security After Mashic compilation, the malicious gadget can only read/write integrator information compatible with its security level.
Information Flow control needed for the integrator code! (and only the integrator code)
Information Flow Control needed • Separation of the gadget using iframe : no need to analyze gadget code • Existing work on dynamic monitors (browser dependent): • Hedin and Sabelfeld, 12 • Austin and Flanagan, 09, 10, 12 • Inlining of dynamic security monitors (browser independent) : • Sabelfeld et al ‘’ 10 • Chudnov and Naumann’ 10
![Information Flow Control Labeling in Java. Script LI Lc var o = {}; o[f()] Information Flow Control Labeling in Java. Script LI Lc var o = {}; o[f()]](http://slidetodoc.com/presentation_image_h2/887768d3261f2a67a654b715a8bfa721/image-35.jpg)
Information Flow Control Labeling in Java. Script LI Lc var o = {}; o[f()] = 1 Confidentiality f() is a function that returns a dynamically computed string Integrity Lcx. LI In the final memory o has a new property unknown before execution! Static labeling is not always possible.
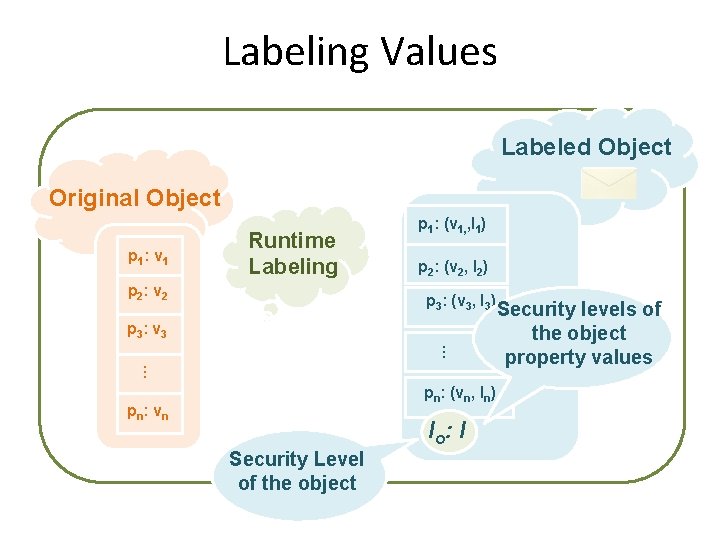
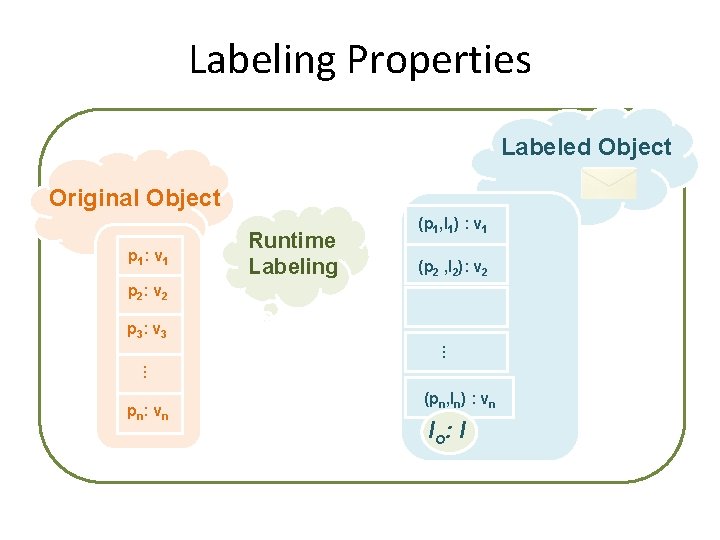
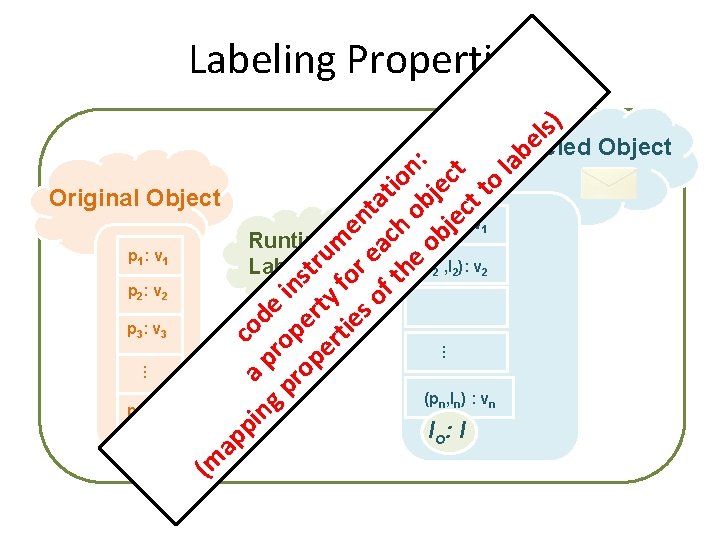
Labeling Values Labeled Object Original Object p 1: v 1 Runtime Labeling p 2: v 2 p 1: (v 1, , l 1) p 2: (v 2, l 2) p 3: (v 3, l 3) p 3: v 3 … … pn: (vn, ln) pn : vn Security Level of the object l o: l Security levels of the object property values
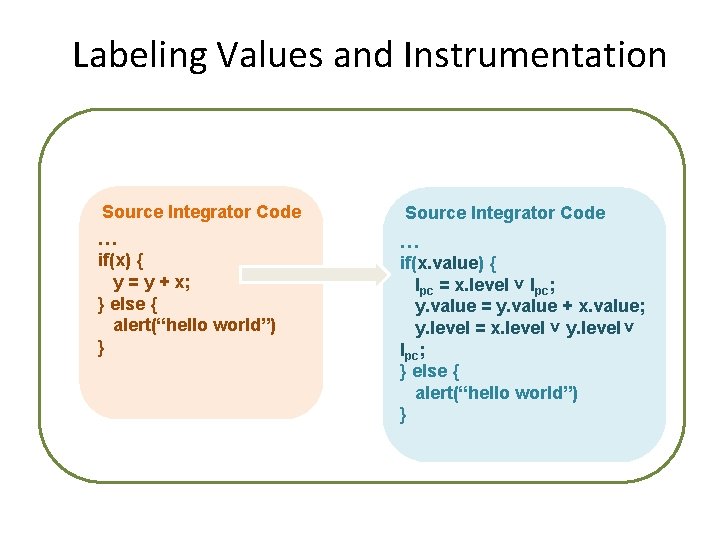
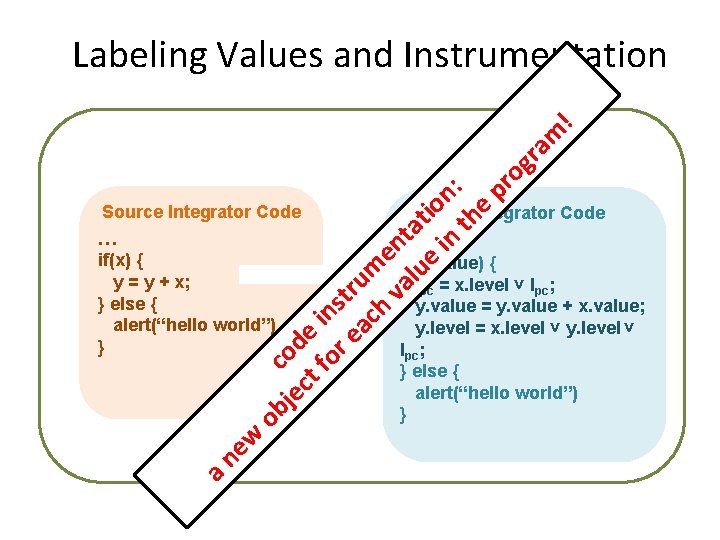
Labeling Values and Instrumentation Source Integrator Code … if(x) { y = y + x; } else { alert(“hello world”) } Source Integrator Code … if(x. value) { lpc = x. level ˅ lpc; y. value = y. value + x. value; y. level = x. level ˅ y. level ˅ lpc; } else { alert(“hello world”) }
je cod ct e fo ins r e tr ac um h va ent lu at e io in n: th e pr og ra m ! Labeling Values and Instrumentation a ne w ob Source Integrator Code … if(x) { y = y + x; } else { alert(“hello world”) } Source Integrator Code … if(x. value) { lpc = x. level ˅ lpc; y. value = y. value + x. value; y. level = x. level ˅ y. level ˅ lpc; } else { alert(“hello world”) }
Labeling Properties Labeled Object Original Object p 1: v 1 Runtime Labeling (p 1, l 1) : v 1 (p 2 , l 2): v 2 p 2: v 2 p 3: v 3 … … pn : vn (pn, ln) : vn l o: l
s) Labeling Properties co a ng p de pr rop in op er str er ty um tie fo e s o r e nt f t ach atio he o n ob bje : je ct ct to la be l Labeled Object Original Object p 1: v 1 p 2: v 2 p 3: v 3 Runtime Labeling (p 1, l 1) : v 1 (p 2 , l 2): v 2 … pi (pn, ln) : vn (m ap … pn : vn l o: l
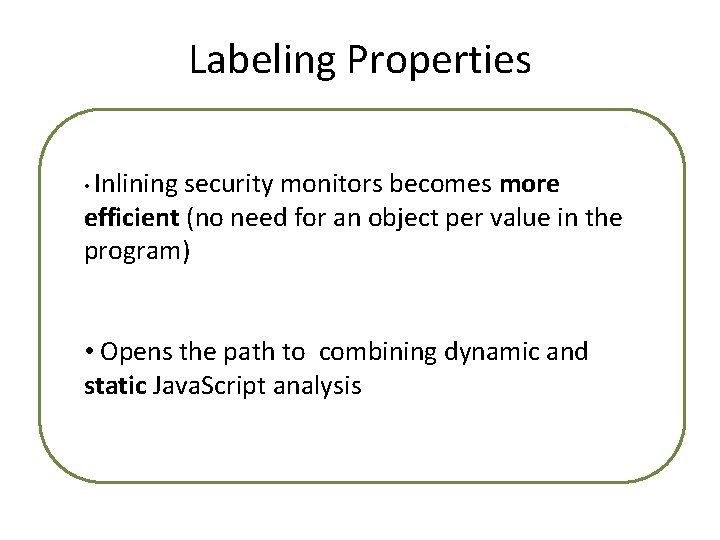
Labeling Properties • Inlining security monitors becomes more efficient (no need for an object per value in the program) • Opens the path to combining dynamic and static Java. Script analysis
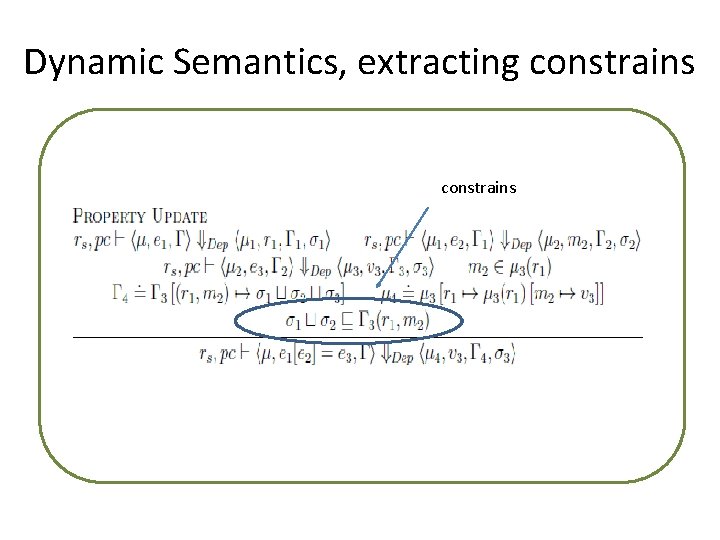
Dynamic Semantics, extracting constrains
Conclusions Mashic Compiler: – assumption: gadgets used as libraries – correctness under assumption – security guarantees based on SOP, characterized as IF where everything in the integrator is treated as top security level – compilation: gadget and browser independent!
Conclusions Mashic Compiler Extension: – assumption: two way communication with AC – correctness under assumption – security guarantees based on information flow security – compilation: • IF analysis for the integrator using code instrumentation • gadget independence regarding IF analysis • browser independence
Open Questions • IF analysis for the integrator using code instrumentation: – Combining with static analysis? If part of the code is in a static typable subset [Maffeis 2010] then type check and instrument the rest. • Gadget independence regarding IF analysis: – Still have to adapt to asynchrony of Post. Message … what’s a good solution to this? shadow pages? [Adjail 2010] • Making the web ad business model secure and practical?
- Slides: 45