Mapping and Comparing Encrypted Numbers Vladimir Kolesnikov Joint
Mapping and Comparing Encrypted Numbers Vladimir Kolesnikov Joint work with Ian F. Blake University of Toronto
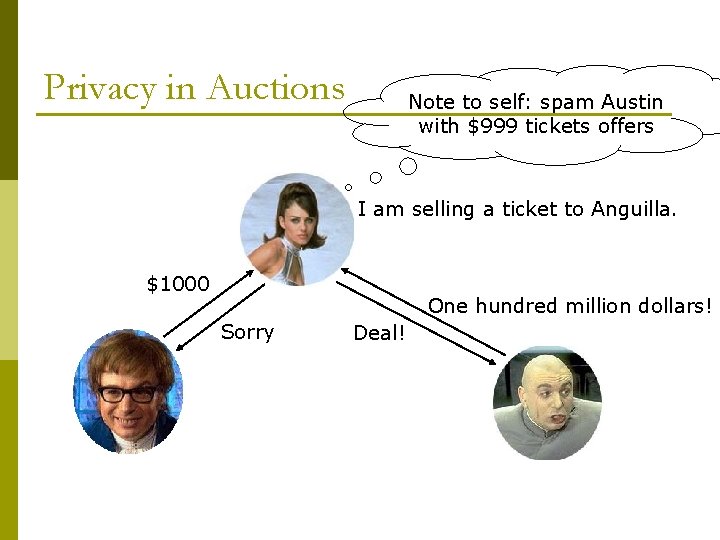
Privacy in Auctions Note to self: spam Austin with $999 tickets offers I am selling a ticket to Anguilla. $1000 One hundred million dollars! Sorry Deal!
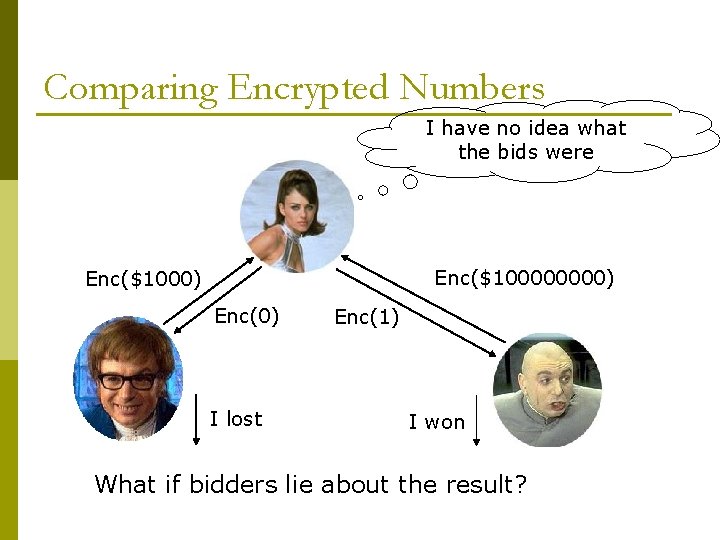
Comparing Encrypted Numbers I have no idea what the bids were Enc($10000) Enc($1000) Enc(0) I lost Enc(1) I won What if bidders lie about the result?
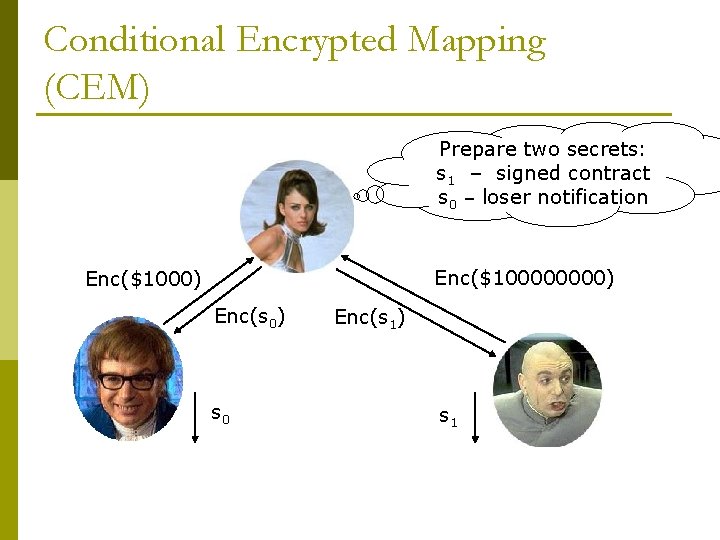
Conditional Encrypted Mapping (CEM) Prepare two secrets: s 1 – signed contract s 0 – loser notification Enc($10000) Enc($1000) Enc(s 0) s 0 Enc(s 1) s 1
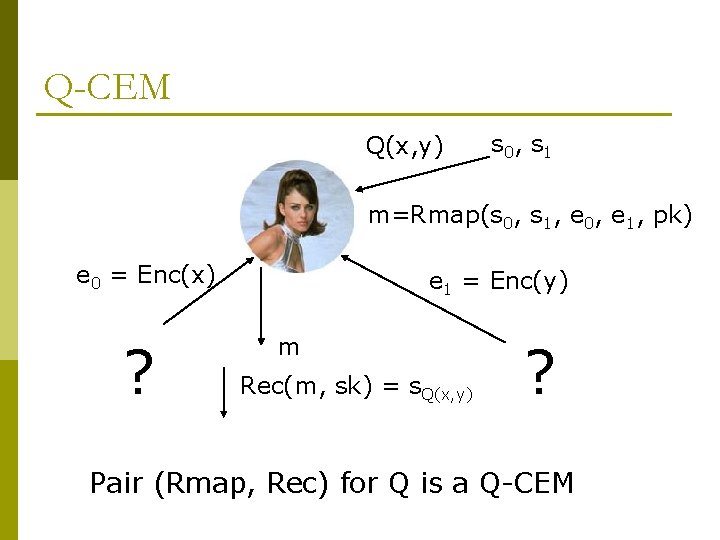
Q-CEM Q(x, y) s 0, s 1 m=Rmap(s 0, s 1, e 0, e 1, pk) e 0 = Enc(x) ? e 1 = Enc(y) m Rec(m, sk) = s. Q(x, y) ? Pair (Rmap, Rec) for Q is a Q-CEM
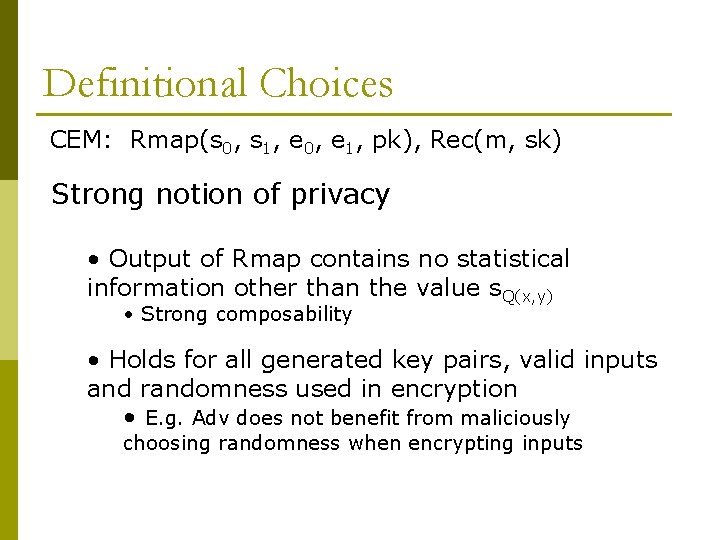
Definitional Choices CEM: Rmap(s 0, s 1, e 0, e 1, pk), Rec(m, sk) Strong notion of privacy • Output of Rmap contains no statistical information other than the value s. Q(x, y) • Strong composability • Holds for all generated key pairs, valid inputs and randomness used in encryption • E. g. Adv does not benefit from maliciously choosing randomness when encrypting inputs
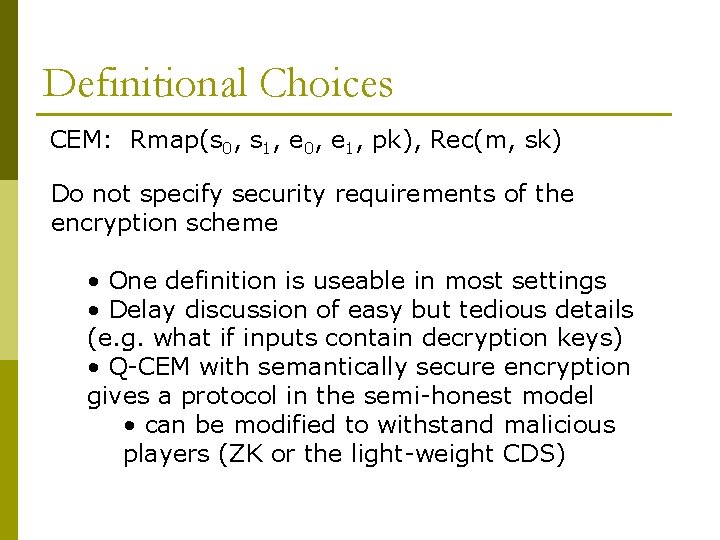
Definitional Choices CEM: Rmap(s 0, s 1, e 0, e 1, pk), Rec(m, sk) Do not specify security requirements of the encryption scheme • One definition is useable in most settings • Delay discussion of easy but tedious details (e. g. what if inputs contain decryption keys) • Q-CEM with semantically secure encryption gives a protocol in the semi-honest model • can be modified to withstand malicious players (ZK or the light-weight CDS)
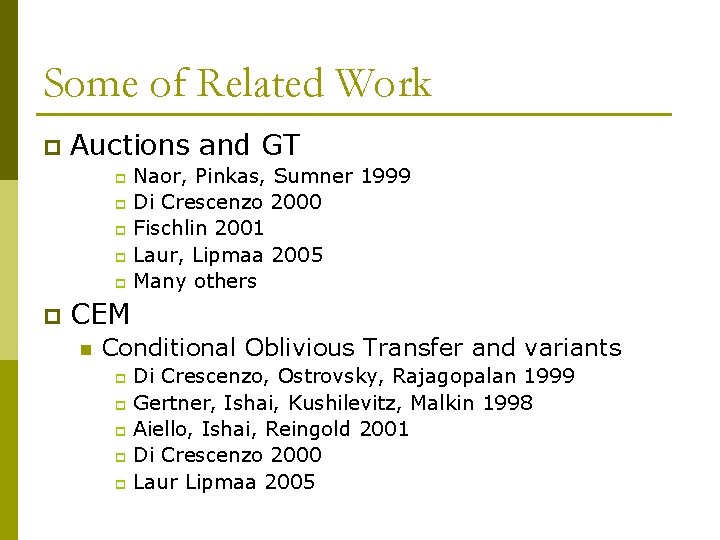
Some of Related Work p Auctions and GT Naor, Pinkas, Sumner 1999 p Di Crescenzo 2000 p Fischlin 2001 p Laur, Lipmaa 2005 p Many others p p CEM n Conditional Oblivious Transfer and variants Di Crescenzo, Ostrovsky, Rajagopalan 1999 p Gertner, Ishai, Kushilevitz, Malkin 1998 p Aiello, Ishai, Reingold 2001 p Di Crescenzo 2000 p Laur Lipmaa 2005 p
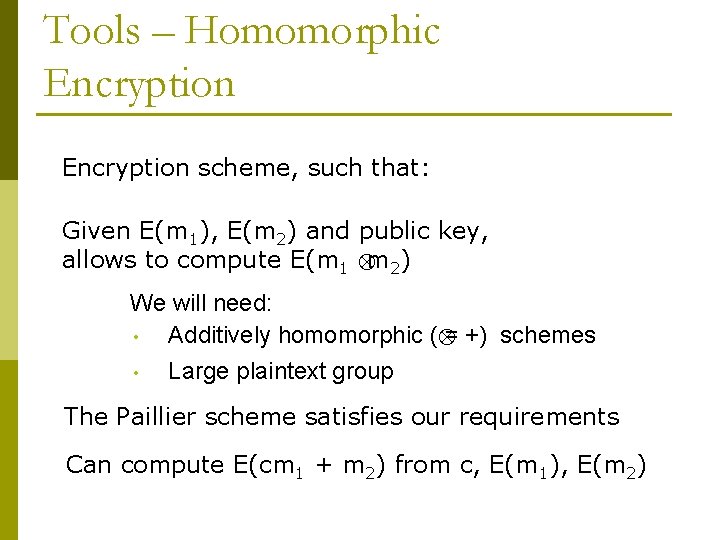
Tools – Homomorphic Encryption scheme, such that: Given E(m 1), E(m 2) and public key, allows to compute E(m 1 m 2) We will need: • Additively homomorphic ( = +) schemes • Large plaintext group The Paillier scheme satisfies our requirements Can compute E(cm 1 + m 2) from c, E(m 1), E(m 2)
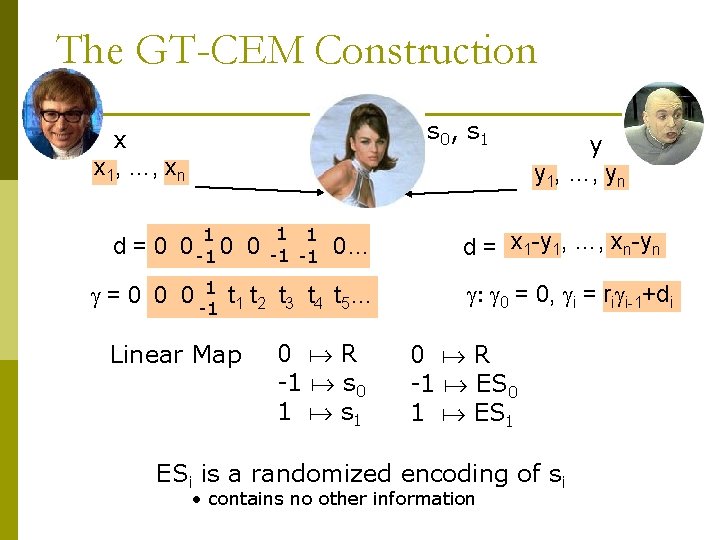
The GT-CEM Construction s 0, s 1 x x 1, …, xn 1 d = 0 0 -1 0 0 =0 0 0 1 t t -1 1 2 Linear Map 1 1 -1 -1 0… t 3 t 4 t 5… 0 R -1 s 0 1 s 1 y y 1, …, yn d = x 1 -y 1, …, xn-yn : 0 = 0, i = ri i-1+di 0 R -1 ES 0 1 ES 1 ESi is a randomized encoding of si • contains no other information
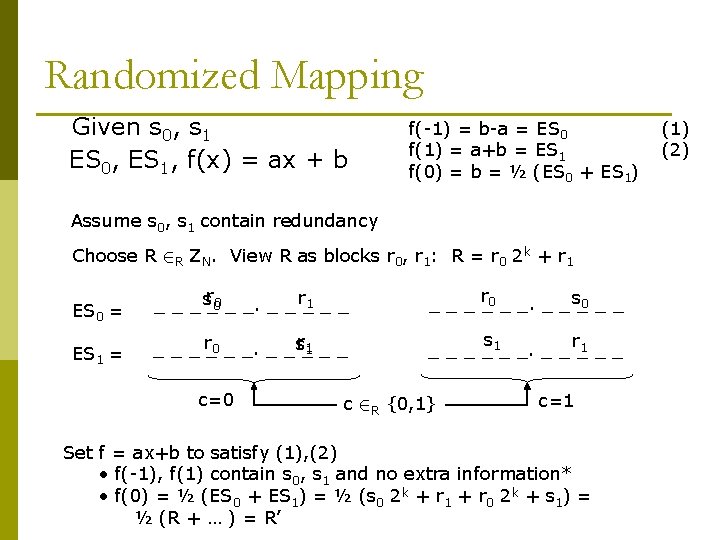
Randomized Mapping Given s 0, s 1 ES 0, ES 1, f(x) = ax + b f(-1) = b-a = ES 0 f(1) = a+b = ES 1 f(0) = b = ½ (ES 0 + ES 1) Assume s 0, s 1 contain redundancy Choose R 2 R ZN. View R as blocks r 0, r 1: R = r 0 2 k + r 1 ES 0 = _ _ _ sr_00 _ _ r_1 _ _ _ r_0 _ _ s_0 _ _ ES 1 = _ _ _ r_0 _ _ sr_1 _ _ s _ _1_ _. _ _ r_1 _ _ c=0 c 2 R {0, 1} c=1 Set f = ax+b to satisfy (1), (2) • f(-1), f(1) contain s 0, s 1 and no extra information* • f(0) = ½ (ES 0 + ES 1) = ½ (s 0 2 k + r 1 + r 0 2 k + s 1) = ½ (R + … ) = R’ (1) (2)
Resource Comparison Orders of magnitude improvement over GM-based schemes Performance similar to previous Paillier-based COT schemes c-bit secrets are transferred based on comparison of n-bit numbers. l and are the correctness and security parameter
Conclusions General and convenient definition of CEM p CEM for any NC 1 predicate p GT-CEM Constructions p n n p Simple and composable Especially efficient for transferring larger secrets ( e. g. ¼ 500 -1000 bits ) Applications to auctions, etc
- Slides: 13