Manufacturing Cybersecurity Presented by Jean Lehman Jules DAlessandro

Manufacturing Cybersecurity Presented by Jean Lehman, Jules D’Alessandro, Carl Benevento, & Rick Norberg
Agenda • Introductions from Congressman Jim Langevin • Current Cybersecurity Challenges • Ramifications of Cyber Attacks • What is good cybersecurity in 2021? • Q&A
Congressman Jim Langevin • Introductions from Congressman Jim Langevin General remarks • What is currently happening at the federal and local level? • Legislation • Funding • Possibilities • Future •
Current Cybersecurity Challenges
What is Cybersecurity? Prevention of damage to Protection of Restoration of • Confidentiality • Integrity • Availability nvlpubs. nist. gov/nistpubs/ir/2016/NIST. IR. 7621 r 1. pdf
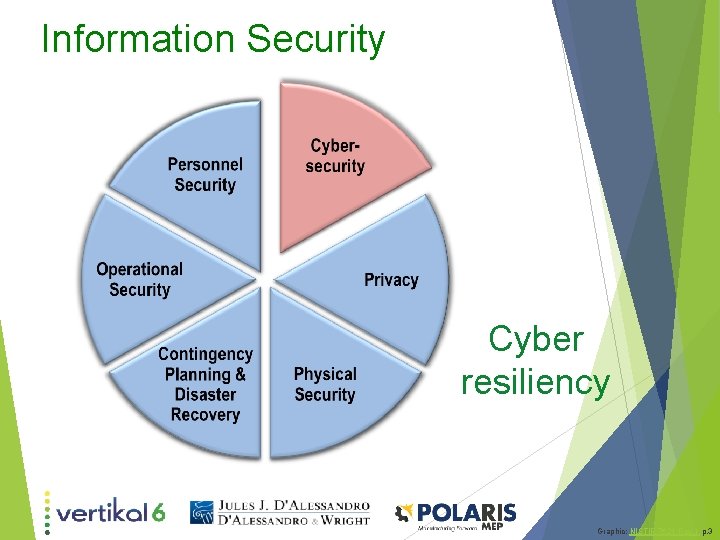
Information Security Cyber resiliency Graphic: NISTIR 7621 Rev. 1 p. 3

The Challenge How to protect your operations and information Understand your risks Manage your risks Shutterstock ID 226966702 By Onur Kocamaz Graphic by Elio Reichert is licensed under CC By 4. 0
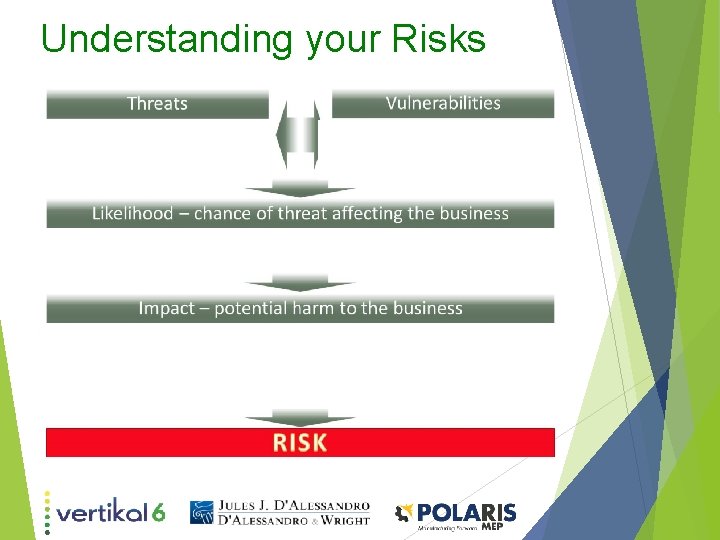
Understanding your Risks
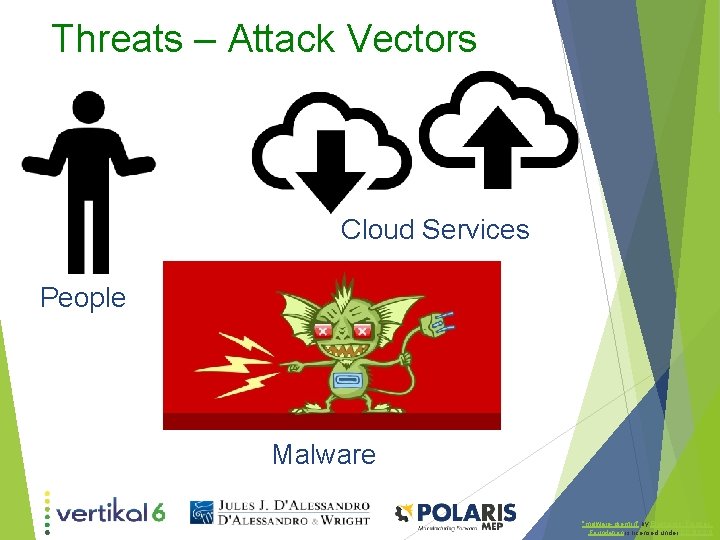
Threats – Attack Vectors Cloud Services People Malware "malware-gremlin" by Electronic_Frontier_ Foundation is licensed under CC BY 2. 0

Manage Your Risks • Inventory • • Identify and prioritize information and assets Protect and mitigate risk • Apply Security Principles and Controls

Manage Your Risks Graphic: NISTIR 7621 Rev. 1 p. 7

Regulations – Federal (just a few…) FAR Federal Acquisition Regulations Basic Safeguarding of Covered Contractor Information Systems DFARS Defense Federal Acquisition Regulation Supplement Safeguarding Covered Defense Information and Cyber Incident Reporting Interim Rule: 252. 204 -7019 , 252. 204 -7020, 252. 204 -7021 ITAR/EAR International Traffic in Arms / Export Administration
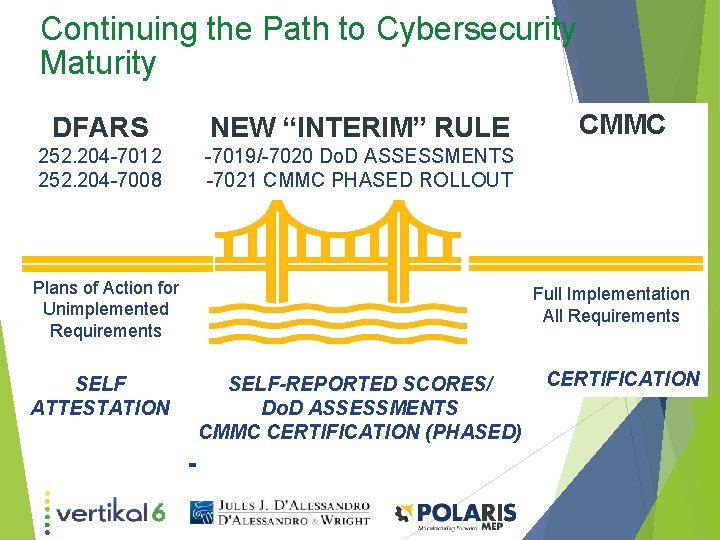
Continuing the Path to Cybersecurity Maturity DFARS NEW “INTERIM” RULE 252. 204 -7012 252. 204 -7008 -7019/-7020 Do. D ASSESSMENTS -7021 CMMC PHASED ROLLOUT Plans of Action for Unimplemented Requirements SELF ATTESTATION CMMC Full Implementation All Requirements SELF-REPORTED SCORES/ Do. D ASSESSMENTS CMMC CERTIFICATION (PHASED) CERTIFICATION

Other Regulations & Industry Standards PII – Personally Identifiable Information HIPAA – Health Insurance Portability & Accountability Act General Data Protection Regulation (EU) California Consumer Privacy Act SOX – publicly traded companies Industry Standards – FDA, Automotive, Aerospace Customer-specified requirements
Cybersecurity system risk • Industry 4. 0 – increased use of robotics, artificial intelligence, machine learning • Data integrity issues/modification of customer specification prior to manufacturing. • Cyber-physical damage to manufacturing facilities and end products. • Health and safety of employees • Loss of productivity due to down time. • Malware imbedded in supply chain that impacts integrity of manufacturing process
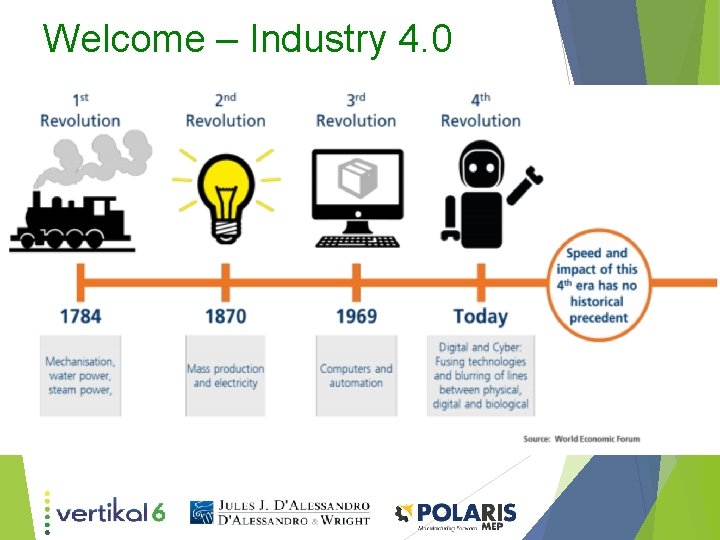
Welcome – Industry 4. 0
Data Integrity Issues • Risks in data integrity can occur when manufacturers do not take steps to confirm data accuracy or completeness or when they assume quality systems are robust. • Failure to maintain data integrity compromises a company’s ability to demonstrate the safety and efficacy of its products.
Cyber-physical damage • Breach of the supply chain cause issues in the production of products among many stages of the manufacturing process. • HVAC and other system exploitation can also cause damage to materials (especially temperature sensitive ones. • SCADA system exploitation
Safety and productivity • Exploitation of systems can impact the safety protocols inherent in those systems causing undue risk to employees • System failure can result as a direct or indirect consequence of exploitation • Direct – Compromised system ceases to function or cannot function correctly • Indirect – Software exploitation (especially malware) causes downtime to remove and remediate.
Imbedded Malware • This has been seen time and time again in the news as of late. • It not only impacts the integrity directly but can also cause loss of faith from consumers and suppliers. • This will continue to be one of the major challenges of systems in the 21 st century.
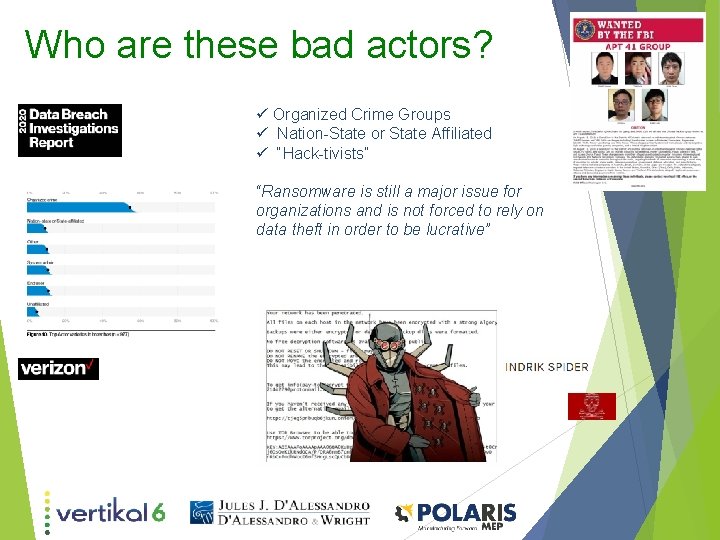
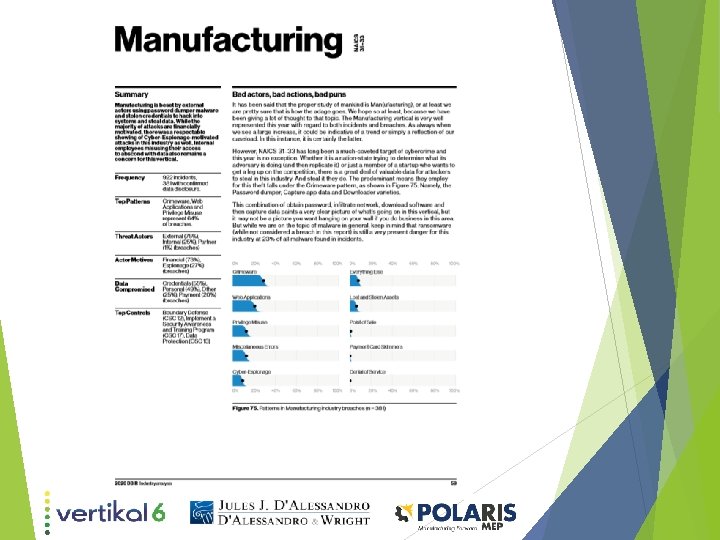
Who are these bad actors? ü Organized Crime Groups ü Nation-State or State Affiliated ü “Hack-tivists” “Ransomware is still a major issue for organizations and is not forced to rely on data theft in order to be lucrative”
Hacking Consequences • Financial • Damages to the brand • Employee morale • Customer confidence • Bad press • Fines • Forensic Examinations • Legal Defense & settlements • Loss of payment card privileges • Time, resources for remediation & repair
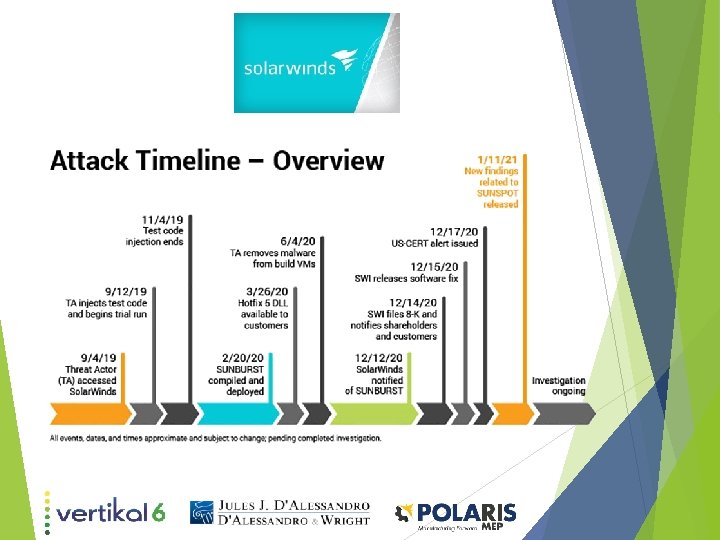
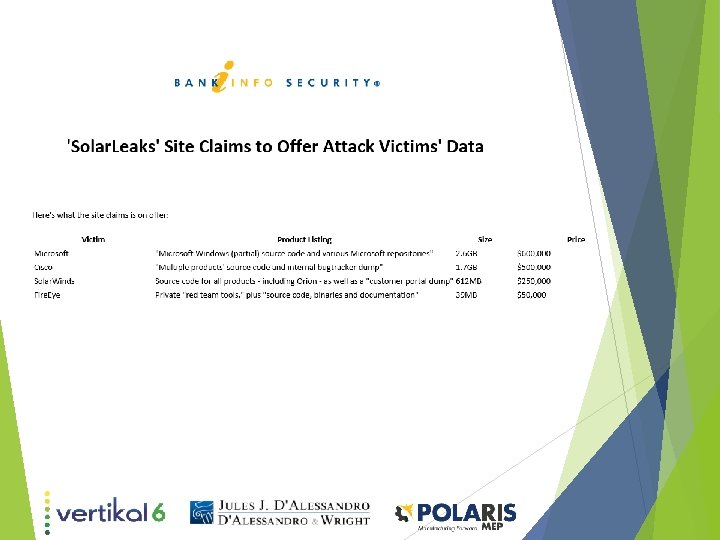
Solarwinds: What happened?
• Texas based software manufacturer that provides network monitoring applications. Global footprint. • September of 2019 attackers successfully hacked the company’s Microsoft Visual Studio development tools and added a “back door” into the company’s software builds. • The backdoor, dubbed "Sunburst, " was added to the company's Orion network monitoring software beginning in March 2020. Up to 18, 000 customers installed and ran the Trojanized software. • Attackers then used the backdoor to target a subset of customers, perhaps numbering in the hundreds, for secondstage attacks, which could have led to data exfiltration, eavesdropping - including email inbox access - and follow-on attacks against business partners.
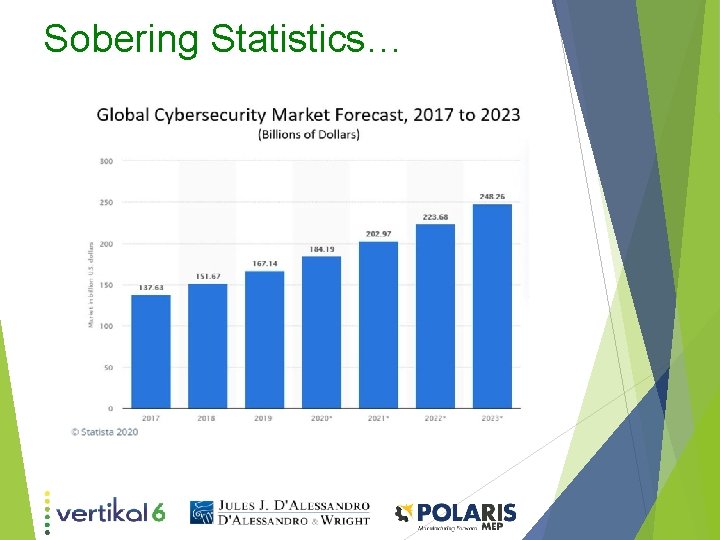
Sobering Statistics…
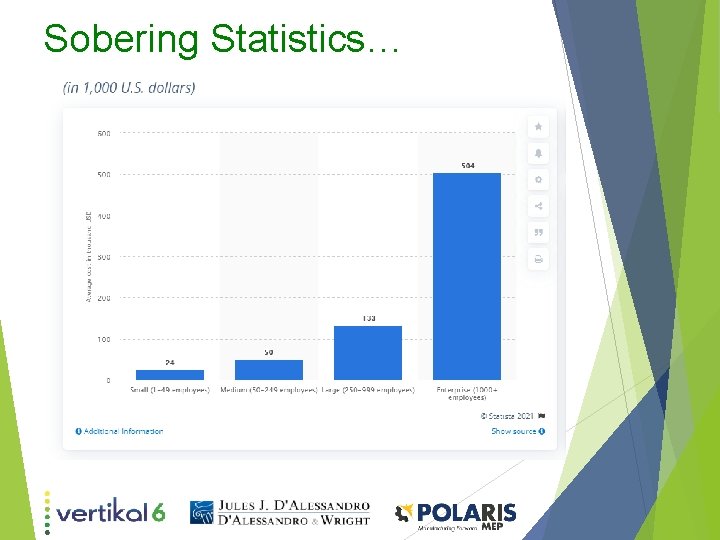
Sobering Statistics…
Ramifications of Cyberattacks
Legal Specific Ramifications of Cyberattacks There are few if any absolutes in the law
Legal Specific Ramifications of Cyberattacks However, some statements that you will absolutely never hear as to the legal ramifications of a cyber attack or breach are…
Legal Specific Ramifications of Cyberattacks “Wow, those legal costs were so much less than we thought they would be!”
Legal Specific Ramifications of Cyberattacks “I can’t believe how quickly that lawsuit was resolved, done and over!”
Legal Specific Ramifications of Cyberattacks The short as well as long term legal costs associated with a cyber event range from staggering to catastrophic!
Legal Specific Ramifications of Cyberattacks The consequences of cyberattacks continue to grow, with digital incidents now costing businesses of all sizes $200, 000 on average, according to insurance carrier Hiscox. 60% go out of business within 6 months of being victimized. https: //www. cnbc. com/2019/10/13/cyberattacks-cost-small-companies-200 k-putting-many-out-of-business. html
Legal Specific Ramifications of Cyberattacks Unfortunately, many small businesses (“SMB’s”)still hold the mindset that hackers are solely focused on targeting the bigger enterprise players, such as large well-known brands, and therefore believe their organizations are just too small for such a robust investment. But, the reality is quite different. https: //www. cnbc. com/2019/10/13/cyberattacks-cost-small-companies-200 k-putting-many-out-of-business. html
Legal Specific Ramifications of Cyberattacks According to recent research conducted by Hiscox, the proportion of SMB businesses that reported a cyber attack has jumped from 40% to 55% in the last year, while at the same time more organizations admitted that they aren’t fully prepared for a security breach. https: //www. cnbc. com/2019/10/13/cyberattacks-cost-small-companies-200 k-putting-many-out-of-business. html
Legal Specific Ramifications of Cyberattacks • Contract losses • Liability for breaches • Direct and indirect Financial loss • Regulatory fines and penalties • Insurance • Loss of reliability, integrity of products and company reputation. • Client damage/loss of client
Legal Specific Ramifications of Cyberattacks Breach of Contract is the number one result of failing to adequately and fully prepare for a security breach.
Legal Specific Ramifications of Cyberattacks Who is liable for breach of contract when you fail to adequately and fully prepare for a security breach? YOU ARE!!!
Legal Specific Ramifications of Cyberattacks The customer that entered into a contract with you, assumed that your business was prepared for a security breach and otherwise cyber compliant. They never assumed that you did nothing prepare for a cyber event. If they knew that, they would never have entered into a contract with you.
Legal Specific Ramifications of Cyberattacks Business customers and their lawyers are getting more savvy and are now adding language to contracts that requires industry standard cyber compliance as well as proof thereof. It is the difference of getting the contract or not!
Legal Specific Ramifications of Cyberattacks – Immediate costs • Customer breach notifications • Post breach customer protection • Regulatory compliance fines • Public relations/crisis communications • Attorney fees and litigation • Technical investigations • Loss of customer trust • Disruption of normal business operations • Immediate financial losses
Legal Specific Ramifications of Cyberattacks – Long Term costs • Increase in insurance premiums • Operational disruptions • Lost value in customer relationships • Value of lost contract revenue • Devaluation of trade name • Loss of intellectual property • Loss of future business contracts and relationships
Legal Specific Ramifications of Cyberattacks – Other costs Even the TV lawyers are jumping on the cyber liability lawsuit band wagon!
Legal Specific Ramifications of Cyberattacks – Other costs Individual as well as Class Action Lawsuits are on the rise alleging that companies are negligent for failing to adequately prepare for a security breach.
Legal Specific Ramifications of Cyberattacks – Other costs In negligence Lawsuits, the sky is the limit!
Legal Specific Ramifications of Cyberattacks – Other costs Damages sought include actual damages, consequential damages, punitive damages and attorneys' fees
Legal Specific Ramifications of Cyberattacks – Other costs While your Cyber insurance carrier should respond to these types of suits, we are also seeing a rise in insurance companies issuing reservation of rights letters where the insured’s conduct in preparing for a cyber attack is questioned for the purpose of denying coverage.
Legal Specific Ramifications of Cyberattacks – Other costs An insurance company can be successful in denying a claim if the insured, in its application for coverage, stated that certain cyber protections were in place when in fact they were not.
Legal Specific Ramifications of Cyberattacks A recent insurance lawsuit highlights the risk: A policyholder faced a lawsuit arising out of the release of electronic medical records caused by a third-party vendor. It turned to its cyber insurer, Columbia Casualty, for coverage. Although Columbia Casualty funded an ensuing settlement under reservation of rights, it turned around and sued its policyholder for recoupment, alleging that among other omissions, Cottage failed to: • "continuously implement the procedures and risk controls identified in its application"; • "regularly check and maintain security patches on its systems"; or • "enhance risk controls". Columbia Cas. Co. v. Cottage Healthcare Sys. , No. 2: 15 -cv-03432 (C. D. Cal. ).
Hackers try to contaminate Florida town’s water supply through computer breach The hackers remotely gained access to a software program, named Team. Viewer, on the computer of an employee. Team. Viewer is used for remote support and is currently on 2. 5 billion devices worldwide.
Hackers try to contaminate Florida town’s water supply through computer breach • The hackers remotely gained access to a software program, named Team. Viewer, on the computer of an employee. Team. Viewer is used for remote support and is currently on 2. 5 billion devices worldwide. • The hackers then increased the amount of sodium hydroxide, also known as lye, being distributed into the water supply. The chemical is typically used in small amounts to control the acidity of water, but at higher levels is dangerous to consume. Sodium hydroxide poisoning – Extensive damage to the mouth, throat, eyes, lungs, esophagus, nose, and stomach are possible. The longterm outcome depends on the extent of this damage. Damage to the esophagus and stomach continues to occur for several weeks after the poison was swallowed. Death may occur as long as a month later. Let that sink in – These are very bad actors who don’t care who they hurt.
Hackers try to contaminate Florida town’s water supply through computer breach • The liability that could result from the failure to prevent a breach like this would be an entity ending event for your organization. • You would also have to live with the catastrophic injury and possible death of hundreds perhaps thousands of people of all ages.
What is good cybersecurity in 2021?
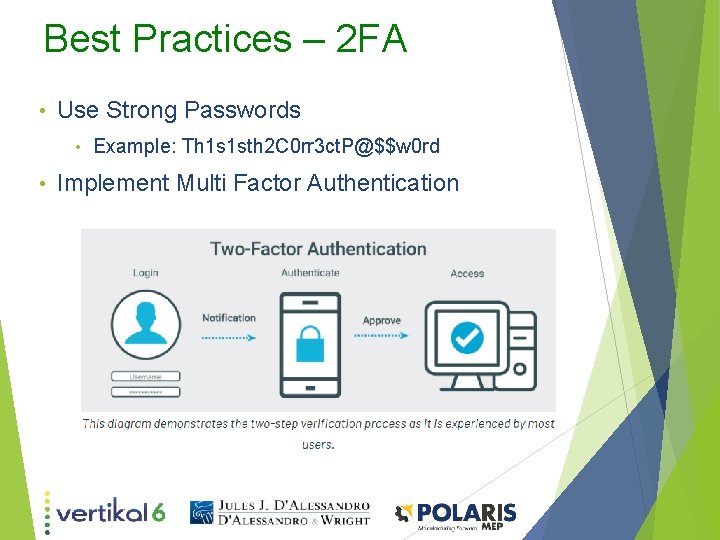
Best Practices – 2 FA • Use Strong Passwords • • Example: Th 1 s 1 sth 2 C 0 rr 3 ct. P@$$w 0 rd Implement Multi Factor Authentication
Best Practices – Issues • Tested Backups – Systems and Timeframes • Disaster recovery and continuity plan • Incident response plan - checklist
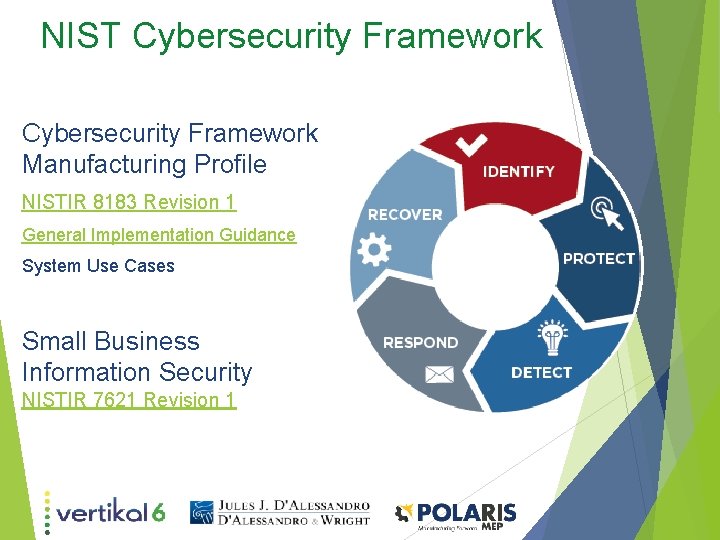
NIST Cybersecurity Framework Manufacturing Profile NISTIR 8183 Revision 1 General Implementation Guidance System Use Cases Small Business Information Security NISTIR 7621 Revision 1
How do I protect my organization ? 1 – Security Awareness Training 2 – Risk Assessment 3 – Policy Review & Development 4 – Penetration Testing 5 - Incident Response Plan 6 – Adopt a Framework
Legal Risks and Insurance Assessment “By understanding your risks, you can know where to focus your efforts. While you can never completely eliminate your risks, the goal of your information security program should be to provide reasonable assurance that you have made informed decisions related to the security of your information”… “make a reasonable effort when trying to understand threats, vulnerabilities, potential impact and likelihood. ” (Paulsen & Toth, 2016, NISTIR 7621 Rev 1 p. 12) NIST’s Interagency Report on Small Business Information Security

Thank You For Attending Johna Krushnowski Jean Lehman Johna@vertikal 6. com JLehman@polarismep. org 401. 825. 4412 401. 542. 4402 Jules D’Alessandro Jules@dwlawri. com 401. 353. 0440
- Slides: 64