Managing Multiuser Databases DAVID M KROENKES DATABASE PROCESSING

Managing Multiuser Databases DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 1
Database Administration • All large and small databases need database administration • Data administration refers to a function concerning all of an organization’s data assets • Database administration (DBA) refers to a person or office specific to a single database and its applications DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 2
DBA Tasks • • Managing database structure Controlling concurrent processing Managing processing rights and responsibilities Developing database security Providing for database recovery Managing the DBMS Maintaining the data repository DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 3
Managing Database Structure • DBA’s tasks: – Participate in database and application development • Assist in requirements stage and data model creation • Play an active role in database design and creation – Facilitate changes to database structure • • • Seek community-wide solutions Assess impact on all users Provide configuration control forum Be prepared for problems after changes are made Maintain documentation DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 4
Concurrency Control • Concurrency control ensures that one user’s work does not inappropriately influence another user’s work – No single concurrency control technique is ideal for all circumstances • Guaranteed repeatability, or latest info? – Trade-offs need to be made between level of protection and throughput • Strict protection or multi-user performance? DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 5
Atomic Transactions • A transaction, or logical unit of work (LUW), is a series of actions taken against the database that occurs as an atomic unit – Either all actions in a transaction occur or none of them do • Command Start Transaction begins a transaction – Not in Oracle – Start Transaction is automatic with any SQL data manipulation. • Command Commit or Rollback ends a transaction – Until Commit or Rollback, changes will usually not be visible to others, and locks will be maintained. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 6
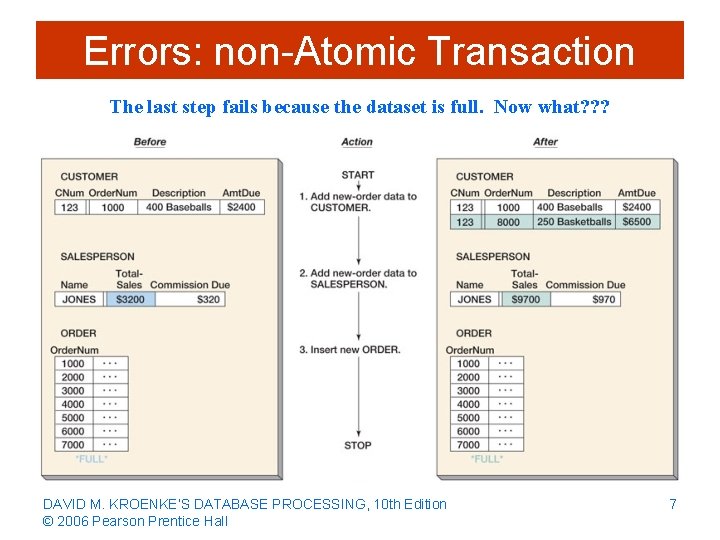
Errors: non-Atomic Transaction The last step fails because the dataset is full. Now what? ? ? DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 7
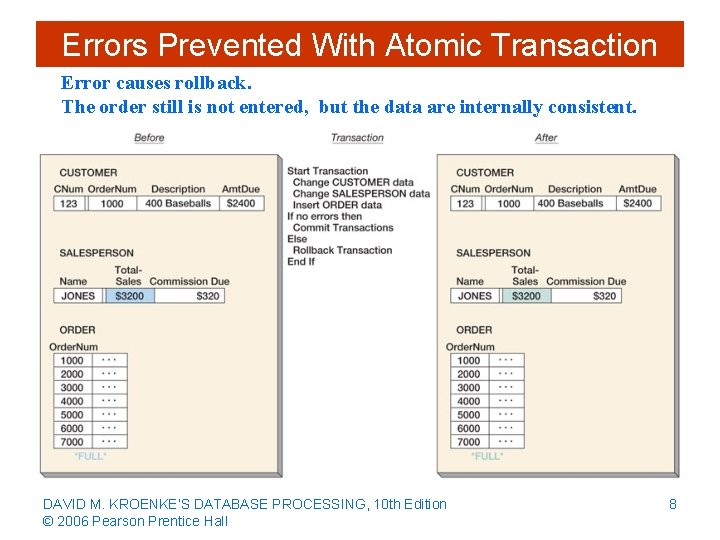
Errors Prevented With Atomic Transaction Error causes rollback. The order still is not entered, but the data are internally consistent. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 8
Concurrent Transaction • Concurrent transactions refer to two or more transactions that appear to users as they are being processed against a database at the same time • In reality, CPU can execute only one instruction at a time – Transactions are interleaved meaning that the operating system quickly switches CPU services among tasks so that some portion of each of them is carried out in a given interval • Concurrency problems: – lost updates and – inconsistent reads DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 9
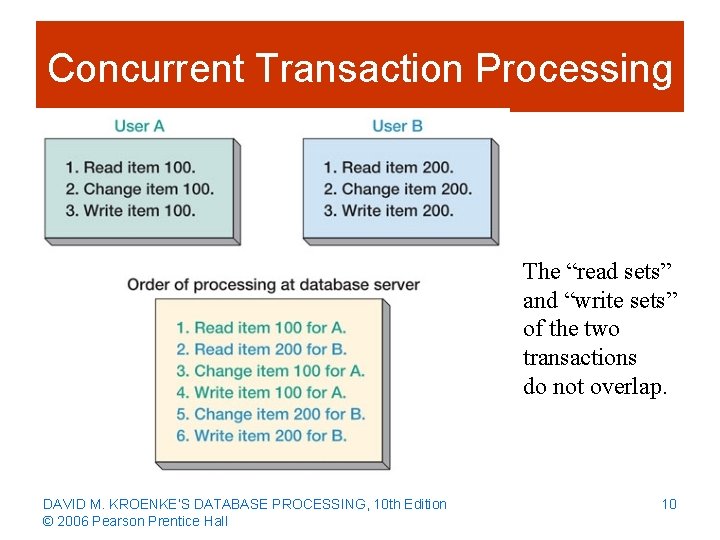
Concurrent Transaction Processing The “read sets” and “write sets” of the two transactions do not overlap. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 10
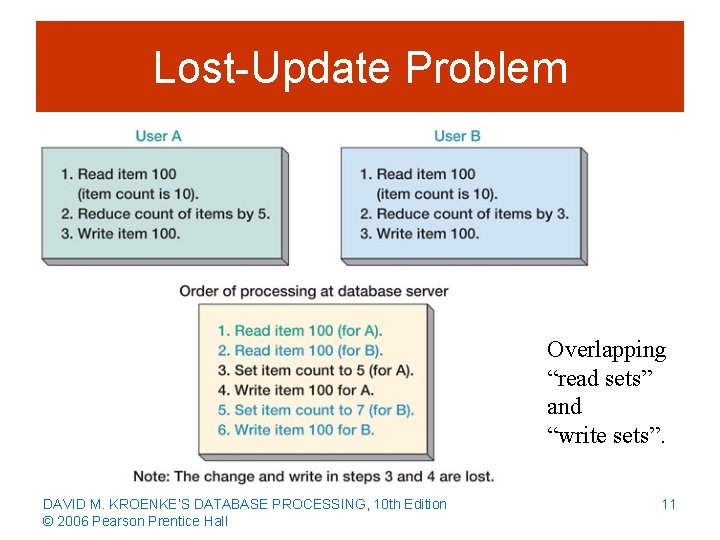
Lost-Update Problem Overlapping “read sets” and “write sets”. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 11
Resource Locking • Resource locking prevents multiple applications from obtaining copies of the same record when the record is about to be changed DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 12
Lock Terminology • Implicit locks are locks placed by the DBMS • Explicit locks are issued by the application program • Lock granularity refers to size of a locked resource – Rows, page, table, and database level – Large granularity is easy to manage but frequently causes conflicts • Types of lock – An exclusive lock prohibits other users from reading the locked resource – A shared lock allows other users to read the locked resource, but not update it DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 13
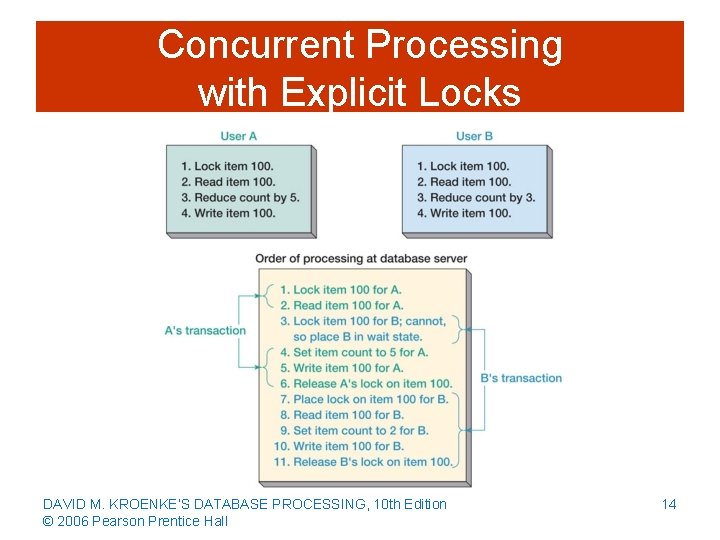
Concurrent Processing with Explicit Locks DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 14
![Manual Locks in Oracle SELECT FROM WHERE FOR UPDATE OF [NOWAIT]; <column names> <table Manual Locks in Oracle SELECT FROM WHERE FOR UPDATE OF [NOWAIT]; <column names> <table](http://slidetodoc.com/presentation_image_h2/9c4a8e1093a253f821d7f3ecf014a012/image-15.jpg)
Manual Locks in Oracle SELECT FROM WHERE FOR UPDATE OF [NOWAIT]; <column names> <table names> <condition> <column names> Lock all qualifying rows until the transaction is committed. NOWAIT option says, “Return immediately if another lock is already in place. ” Make changes quickly and COMMIT as soon as possible. 15
Serializable Transactions • Serializable transactions refer to two transactions that run concurrently and generate results that are consistent with the results that would have occurred if they had run separately • Two-phased locking is one of the techniques used to achieve serializability DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 16
Two-phased Locking • Two-phased locking -- guarantees serializability (but limits concurrency, and still allows deadlock & starvation) – Transactions are allowed to obtain locks as necessary (growing phase) – Once the first lock is released (shrinking phase), no other lock can be obtained • “Rigorous 2 PL”: a special case of 2 PL – Locks are obtained throughout the transaction – No lock is released until the COMMIT or ROLLBACK command is issued – This strategy is more restrictive but easier to implement than two-phased locking DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 17
Deadlock • • Deadlock, or the deadly embrace, occurs when two transactions are each waiting on a resource that the other transaction holds Preventing deadlock 1. Require users to issue all lock requests at one time • Called “Conservative 2 PL” or “Static 2 PL” 2. Require all application programs to lock resources in the same order • Breaking deadlock – Almost every DBMS has algorithms for detecting deadlock – When deadlock occurs, the DBMS aborts one of the transactions, and rolls back partially completed work • “Victim selected…” (one of my favorite error messages…) 18
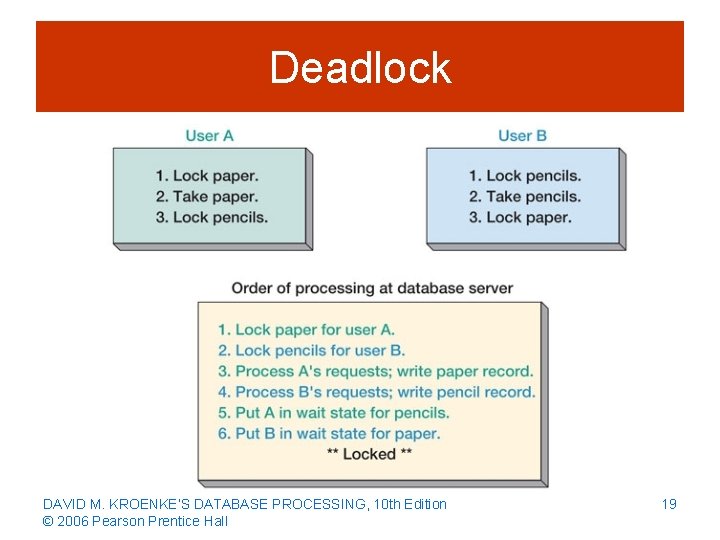
Deadlock DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 19
Optimistic versus Pessimistic Locking • Optimistic locking assumes that no transaction conflict will occur: – DBMS processes a transaction; checks whether conflict occurred: • If not, the transaction is finished • If so, the transaction is repeated until there is no conflict • Pessimistic locking assumes that conflict will occur: – Locks are issued before a transaction is processed, and then the locks are released • Optimistic locking is preferred for the Internet and for many intranet applications (usually better multi-user performance) – Go to pessimistic locking in the face of performance problems with optimistic locking (too much conflict). DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 20
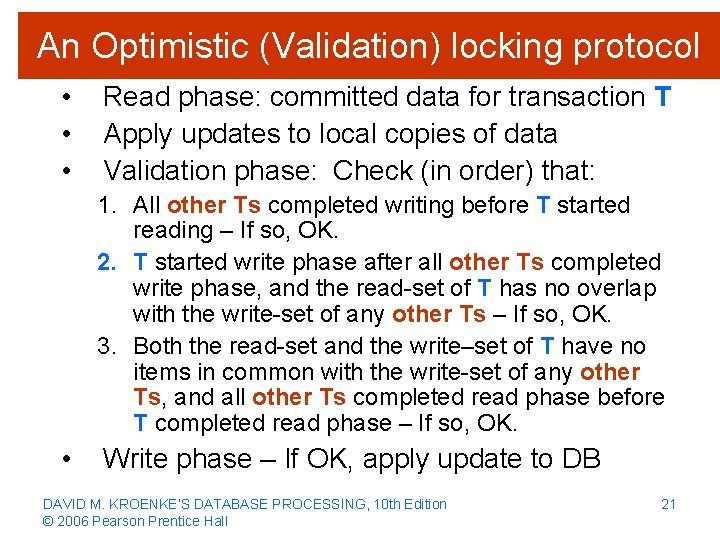
An Optimistic (Validation) locking protocol • • • Read phase: committed data for transaction T Apply updates to local copies of data Validation phase: Check (in order) that: 1. All other Ts completed writing before T started reading – If so, OK. 2. T started write phase after all other Ts completed write phase, and the read-set of T has no overlap with the write-set of any other Ts – If so, OK. 3. Both the read-set and the write–set of T have no items in common with the write-set of any other Ts, and all other Ts completed read phase before T completed read phase – If so, OK. • Write phase – If OK, apply update to DB DAVID M. KROENKE’S DATABASE PROCESSING, Edition Think what the DBMS 10 th is tracking!!! © 2006 Pearson Prentice Hall 21 Elmasri & Navathe, 2000
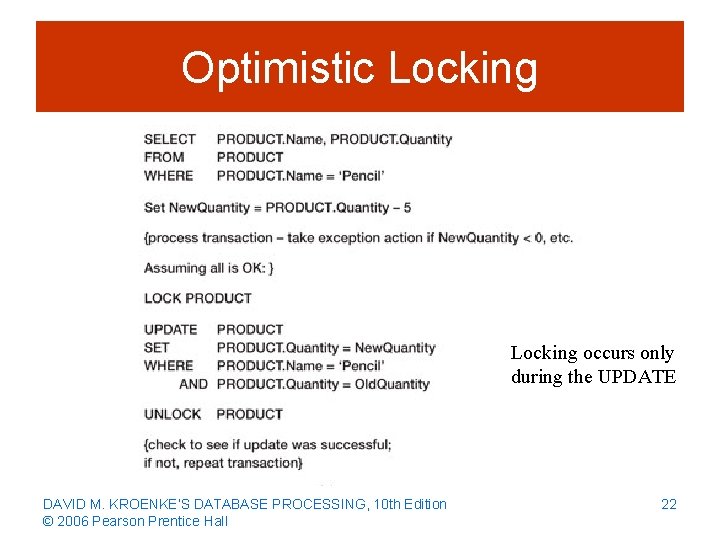
Optimistic Locking occurs only during the UPDATE DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 22
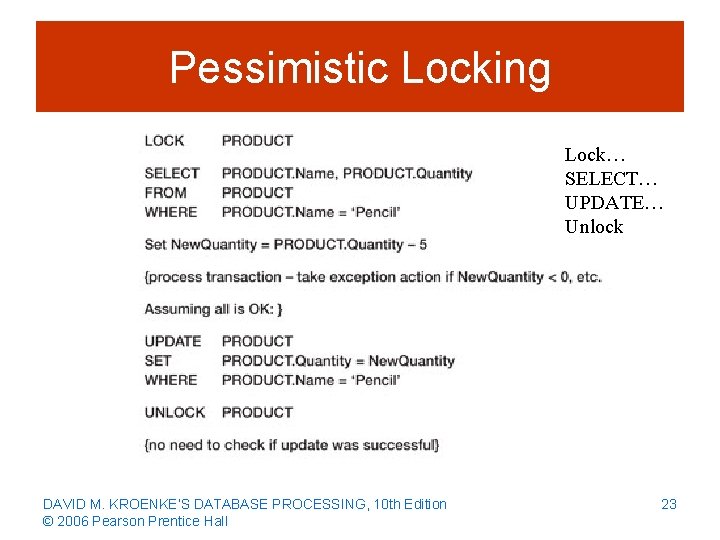
Pessimistic Locking Lock… SELECT… UPDATE… Unlock DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 23
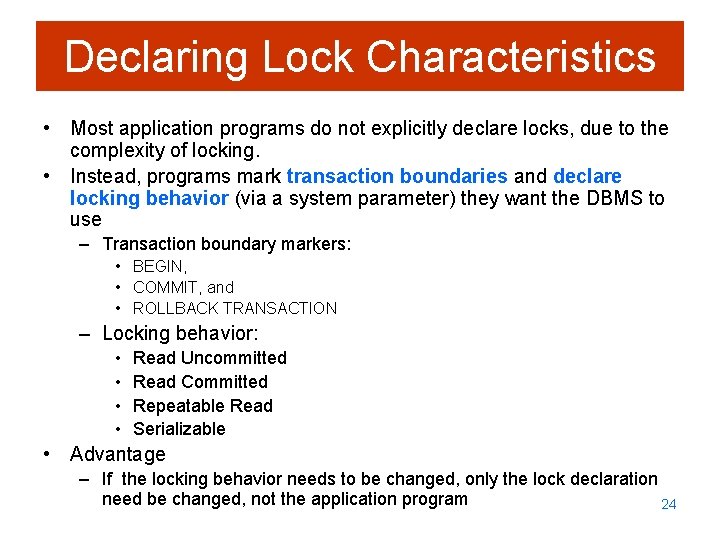
Declaring Lock Characteristics • Most application programs do not explicitly declare locks, due to the complexity of locking. • Instead, programs mark transaction boundaries and declare locking behavior (via a system parameter) they want the DBMS to use – Transaction boundary markers: • BEGIN, • COMMIT, and • ROLLBACK TRANSACTION – Locking behavior: • • Read Uncommitted Read Committed Repeatable Read Serializable • Advantage – If the locking behavior needs to be changed, only the lock declaration need be changed, not the application program 24
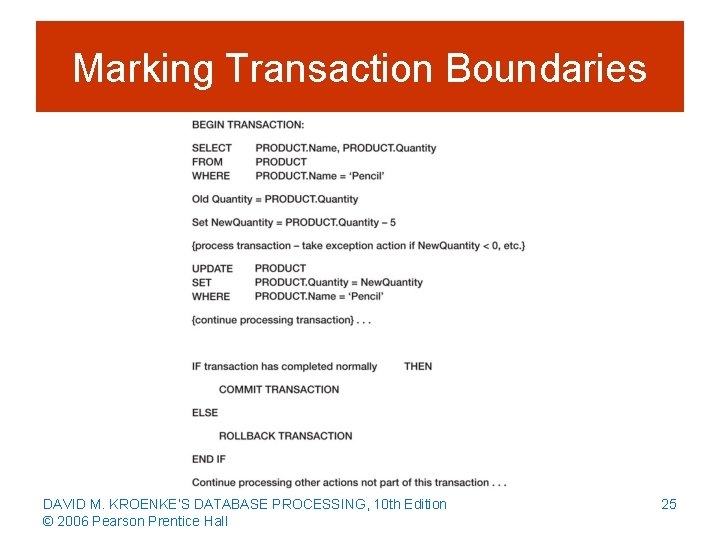
Marking Transaction Boundaries DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 25
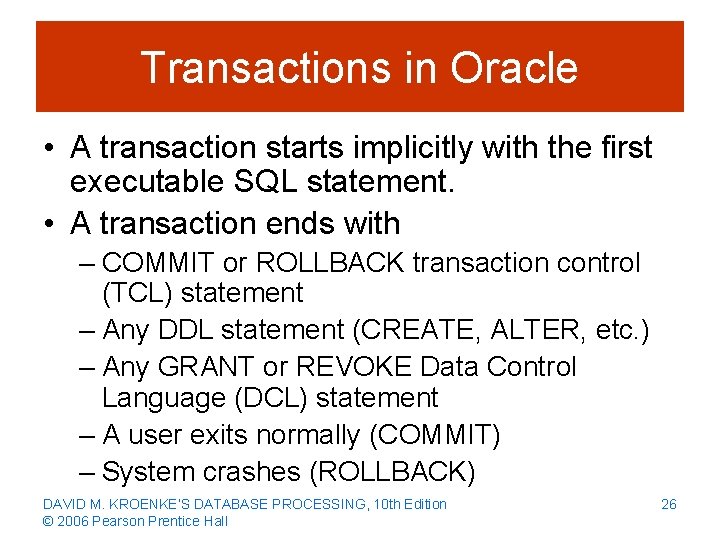
Transactions in Oracle • A transaction starts implicitly with the first executable SQL statement. • A transaction ends with – COMMIT or ROLLBACK transaction control (TCL) statement – Any DDL statement (CREATE, ALTER, etc. ) – Any GRANT or REVOKE Data Control Language (DCL) statement – A user exits normally (COMMIT) – System crashes (ROLLBACK) DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 26
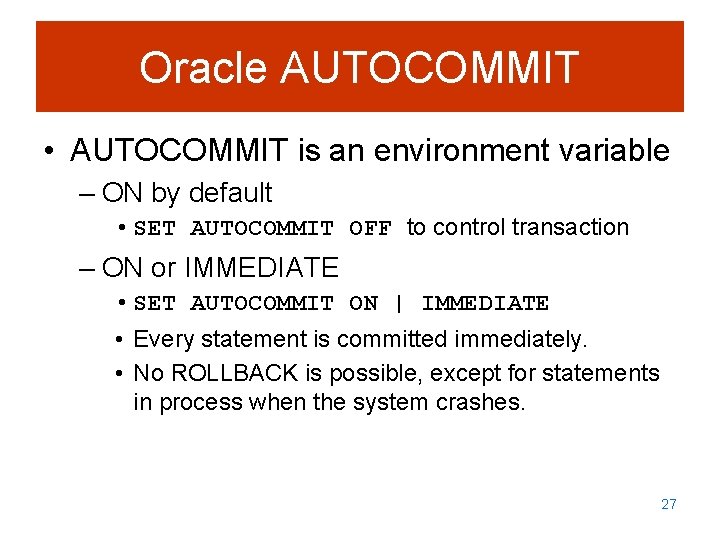
Oracle AUTOCOMMIT • AUTOCOMMIT is an environment variable – ON by default • SET AUTOCOMMIT OFF to control transaction – ON or IMMEDIATE • SET AUTOCOMMIT ON | IMMEDIATE • Every statement is committed immediately. • No ROLLBACK is possible, except for statements in process when the system crashes. 27
ACID Transactions • Acronym ACID transaction is one that is Atomic, Consistent, Isolated, and Durable • Atomic means either all or none of the database actions occur • Durable means database committed changes are permanent DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 28
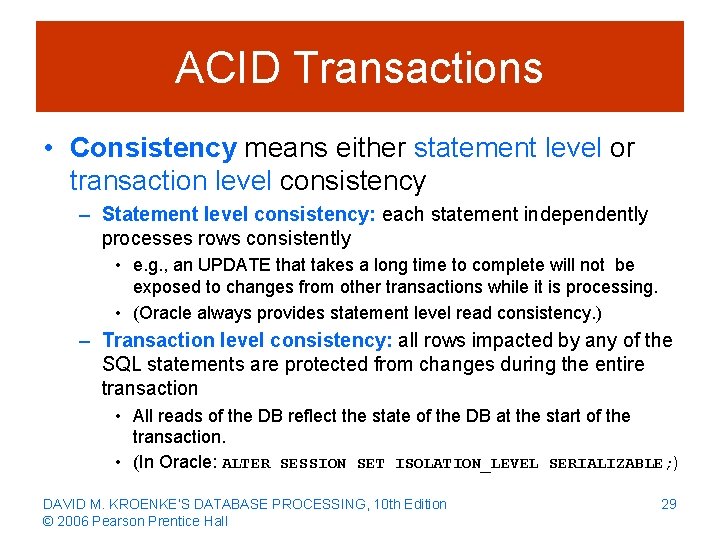
ACID Transactions • Consistency means either statement level or transaction level consistency – Statement level consistency: each statement independently processes rows consistently • e. g. , an UPDATE that takes a long time to complete will not be exposed to changes from other transactions while it is processing. • (Oracle always provides statement level read consistency. ) – Transaction level consistency: all rows impacted by any of the SQL statements are protected from changes during the entire transaction • All reads of the DB reflect the state of the DB at the start of the transaction. • (In Oracle: ALTER SESSION SET ISOLATION_LEVEL SERIALIZABLE; ) DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 29
ACID Transactions • Isolation means application programmers are able to declare the type of isolation level and to have the DBMS manage locks so as to achieve that level of isolation • SQL-92 defines four transaction isolation levels: – – Read uncommitted Read committed Repeatable read Serializable DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 30
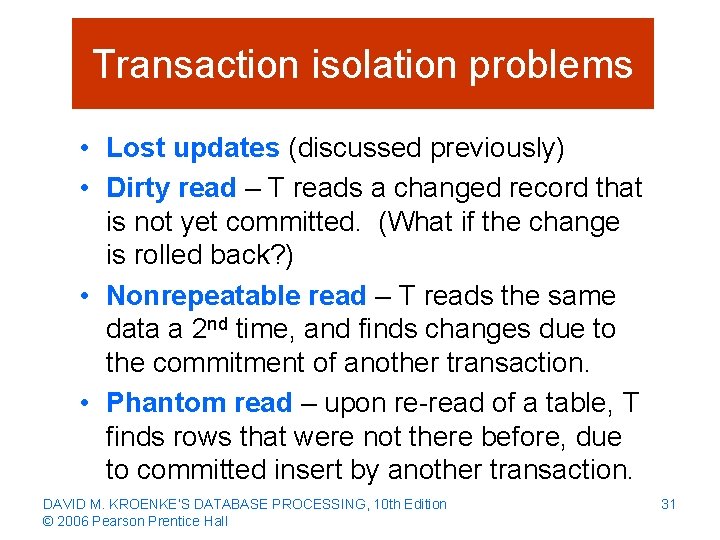
Transaction isolation problems • Lost updates (discussed previously) • Dirty read – T reads a changed record that is not yet committed. (What if the change is rolled back? ) • Nonrepeatable read – T reads the same data a 2 nd time, and finds changes due to the commitment of another transaction. • Phantom read – upon re-read of a table, T finds rows that were not there before, due to committed insert by another transaction. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 31
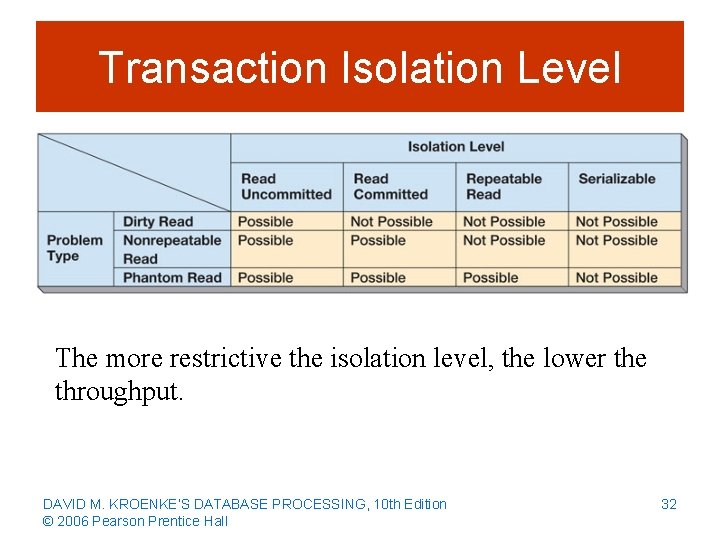
Transaction Isolation Level The more restrictive the isolation level, the lower the throughput. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 32
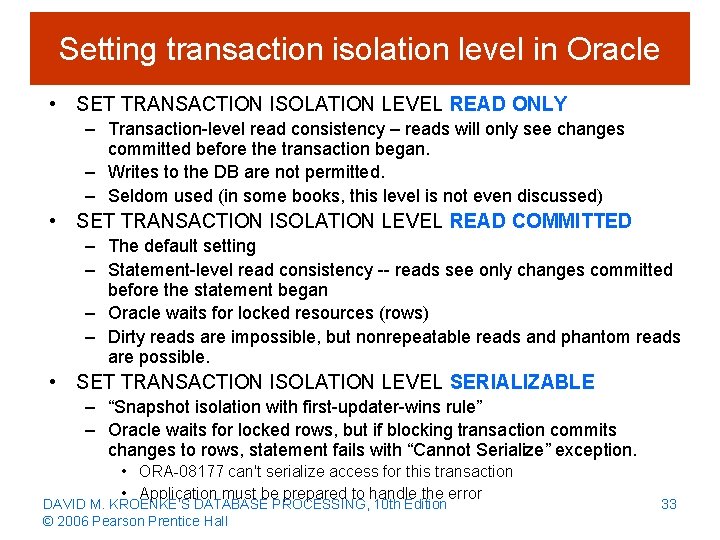
Setting transaction isolation level in Oracle • SET TRANSACTION ISOLATION LEVEL READ ONLY – Transaction-level read consistency – reads will only see changes committed before the transaction began. – Writes to the DB are not permitted. – Seldom used (in some books, this level is not even discussed) • SET TRANSACTION ISOLATION LEVEL READ COMMITTED – The default setting – Statement-level read consistency -- reads see only changes committed before the statement began – Oracle waits for locked resources (rows) – Dirty reads are impossible, but nonrepeatable reads and phantom reads are possible. • SET TRANSACTION ISOLATION LEVEL SERIALIZABLE – “Snapshot isolation with first-updater-wins rule” – Oracle waits for locked rows, but if blocking transaction commits changes to rows, statement fails with “Cannot Serialize” exception. • ORA-08177 can't serialize access for this transaction • Application must be prepared to handle the error DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 33
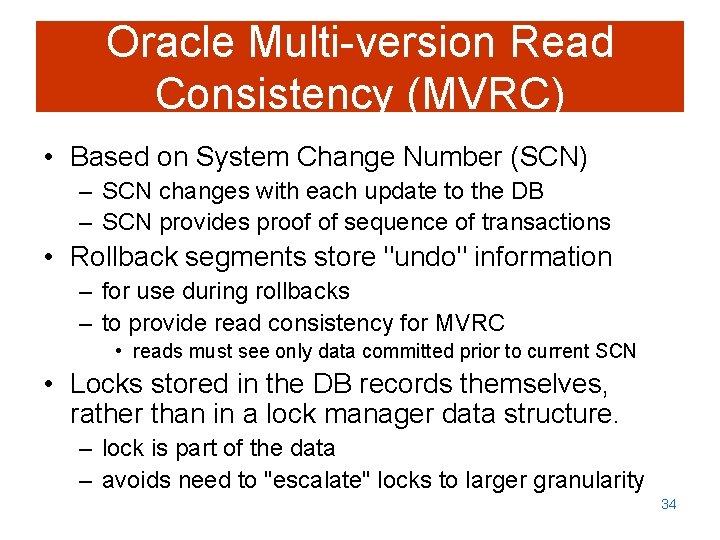
Oracle Multi-version Read Consistency (MVRC) • Based on System Change Number (SCN) – SCN changes with each update to the DB – SCN provides proof of sequence of transactions • Rollback segments store "undo" information – for use during rollbacks – to provide read consistency for MVRC • reads must see only data committed prior to current SCN • Locks stored in the DB records themselves, rather than in a lock manager data structure. – lock is part of the data – avoids need to "escalate" locks to larger granularity 34
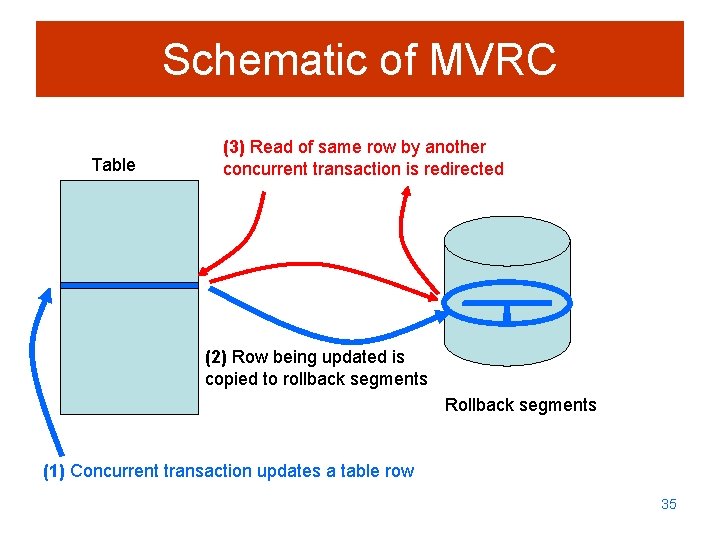
Schematic of MVRC Table (3) Read of same row by another concurrent transaction is redirected (2) Row being updated is copied to rollback segments Rollback segments (1) Concurrent transaction updates a table row 35
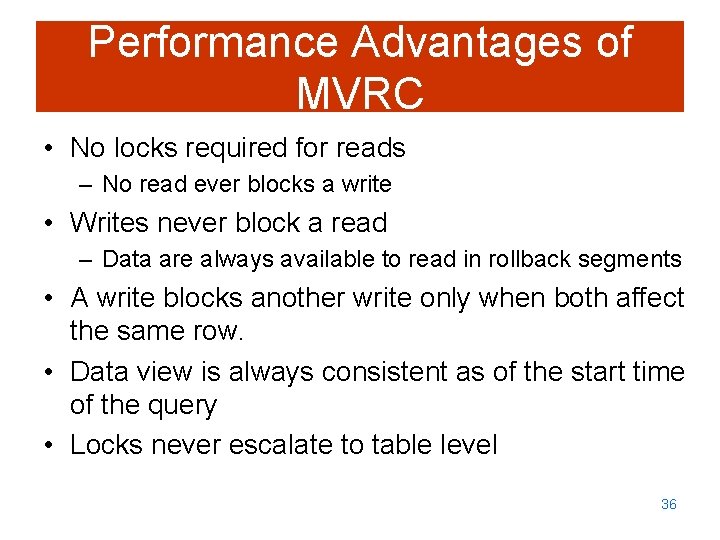
Performance Advantages of MVRC • No locks required for reads – No read ever blocks a write • Writes never block a read – Data are always available to read in rollback segments • A write blocks another write only when both affect the same row. • Data view is always consistent as of the start time of the query • Locks never escalate to table level 36
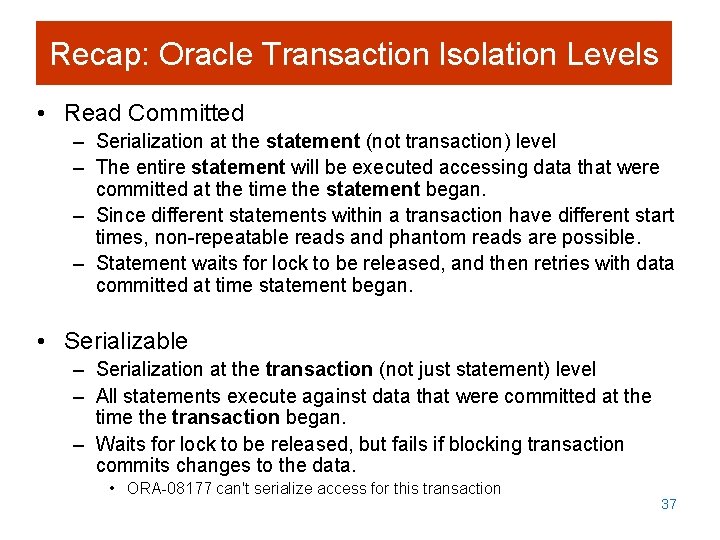
Recap: Oracle Transaction Isolation Levels • Read Committed – Serialization at the statement (not transaction) level – The entire statement will be executed accessing data that were committed at the time the statement began. – Since different statements within a transaction have different start times, non-repeatable reads and phantom reads are possible. – Statement waits for lock to be released, and then retries with data committed at time statement began. • Serializable – Serialization at the transaction (not just statement) level – All statements execute against data that were committed at the time the transaction began. – Waits for lock to be released, but fails if blocking transaction commits changes to the data. • ORA-08177 can't serialize access for this transaction 37
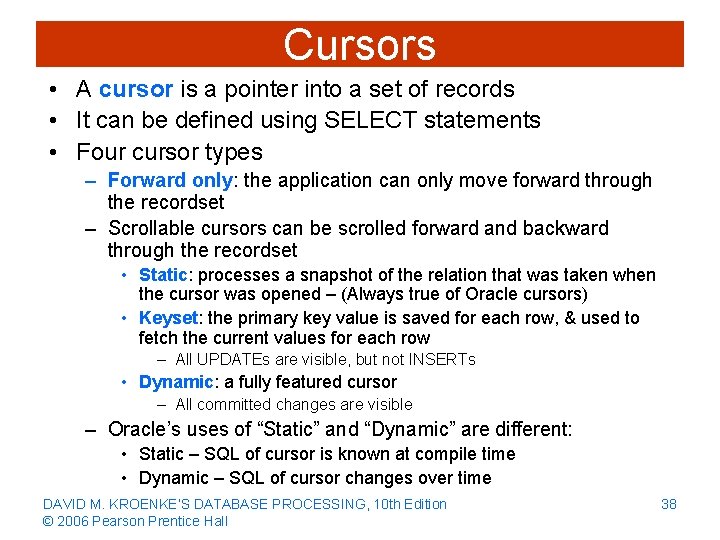
Cursors • A cursor is a pointer into a set of records • It can be defined using SELECT statements • Four cursor types – Forward only: the application can only move forward through the recordset – Scrollable cursors can be scrolled forward and backward through the recordset • Static: processes a snapshot of the relation that was taken when the cursor was opened – (Always true of Oracle cursors) • Keyset: the primary key value is saved for each row, & used to fetch the current values for each row – All UPDATEs are visible, but not INSERTs • Dynamic: a fully featured cursor – All committed changes are visible – Oracle’s uses of “Static” and “Dynamic” are different: • Static – SQL of cursor is known at compile time • Dynamic – SQL of cursor changes over time DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 38
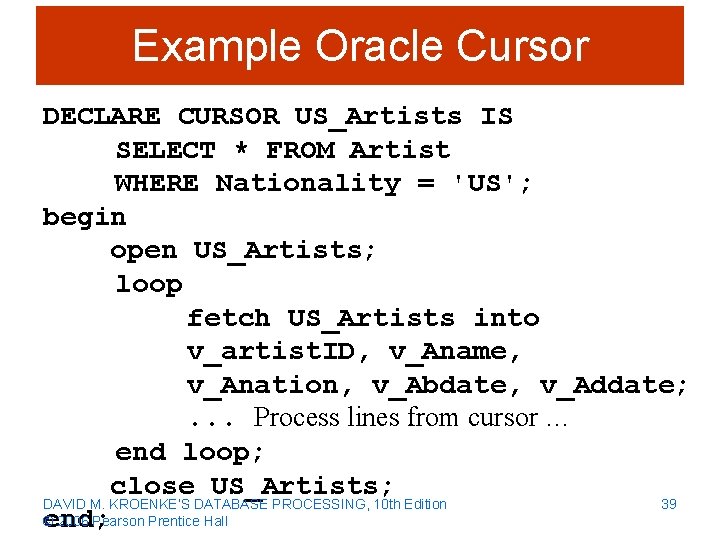
Example Oracle Cursor DECLARE CURSOR US_Artists IS SELECT * FROM Artist WHERE Nationality = 'US'; begin open US_Artists; loop fetch US_Artists into v_artist. ID, v_Aname, v_Anation, v_Abdate, v_Addate; . . . Process lines from cursor … end loop; close US_Artists; 39 DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall end;
Database Security • Database security ensures that only authorized users can perform authorized activities at authorized times • Developing database security – Determine users’ processing rights and responsibilities – Enforce security requirements using security features from both DBMS and application programs DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 40
DBMS Security • DBMS products provide security facilities • They limit certain actions on certain objects to certain users or groups (also called roles) • Almost all DBMS products use some form of user name and password security DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 41
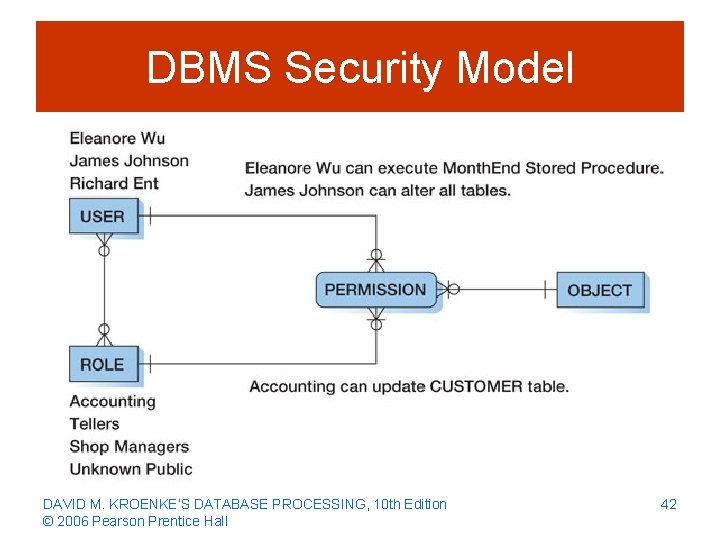
DBMS Security Model DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 42
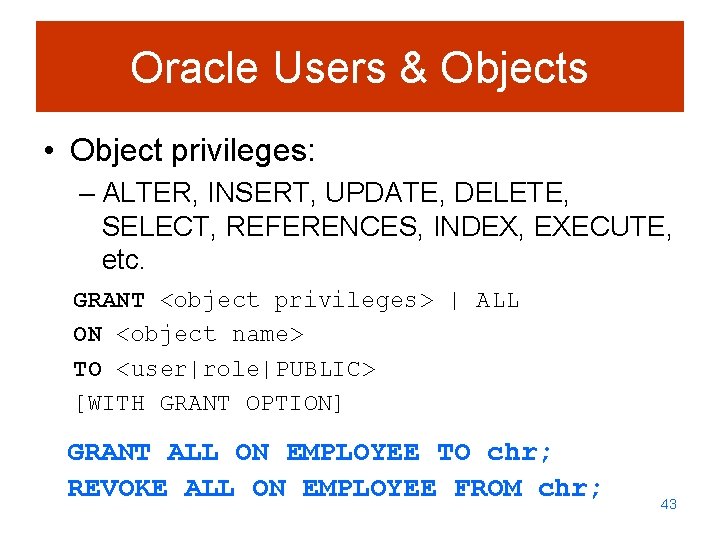
Oracle Users & Objects • Object privileges: – ALTER, INSERT, UPDATE, DELETE, SELECT, REFERENCES, INDEX, EXECUTE, etc. GRANT <object privileges> | ALL ON <object name> TO <user|role|PUBLIC> [WITH GRANT OPTION] GRANT ALL ON EMPLOYEE TO chr; REVOKE ALL ON EMPLOYEE FROM chr; 43
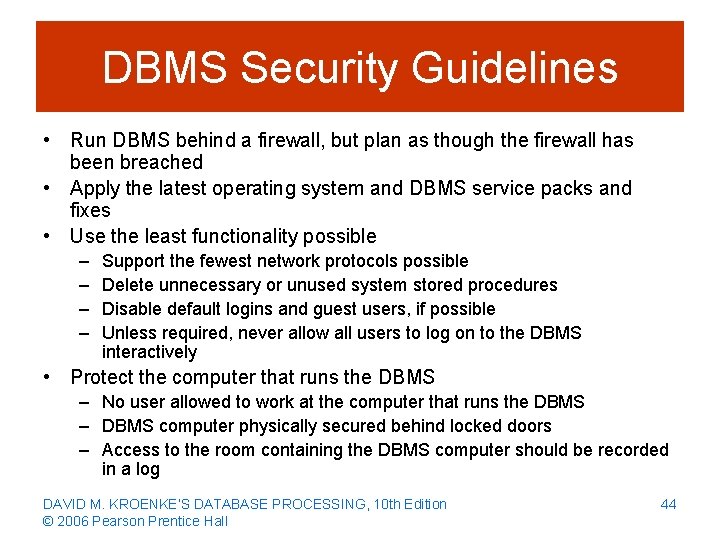
DBMS Security Guidelines • Run DBMS behind a firewall, but plan as though the firewall has been breached • Apply the latest operating system and DBMS service packs and fixes • Use the least functionality possible – – Support the fewest network protocols possible Delete unnecessary or unused system stored procedures Disable default logins and guest users, if possible Unless required, never allow all users to log on to the DBMS interactively • Protect the computer that runs the DBMS – No user allowed to work at the computer that runs the DBMS – DBMS computer physically secured behind locked doors – Access to the room containing the DBMS computer should be recorded in a log DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 44
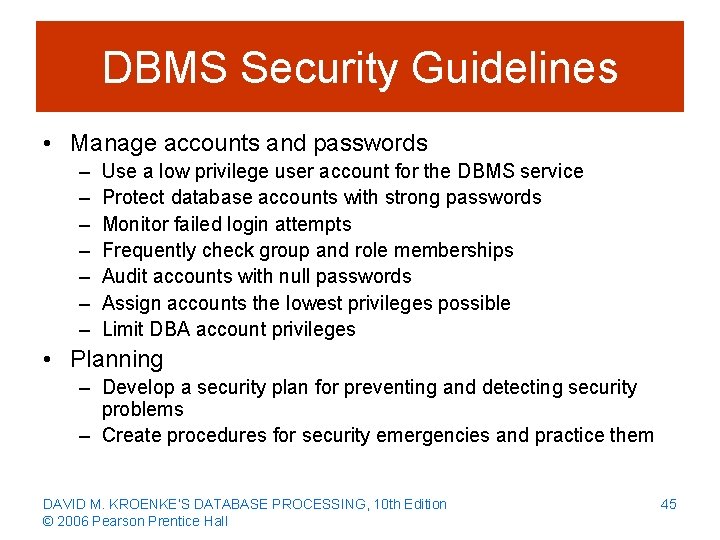
DBMS Security Guidelines • Manage accounts and passwords – – – – Use a low privilege user account for the DBMS service Protect database accounts with strong passwords Monitor failed login attempts Frequently check group and role memberships Audit accounts with null passwords Assign accounts the lowest privileges possible Limit DBA account privileges • Planning – Develop a security plan for preventing and detecting security problems – Create procedures for security emergencies and practice them DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 45
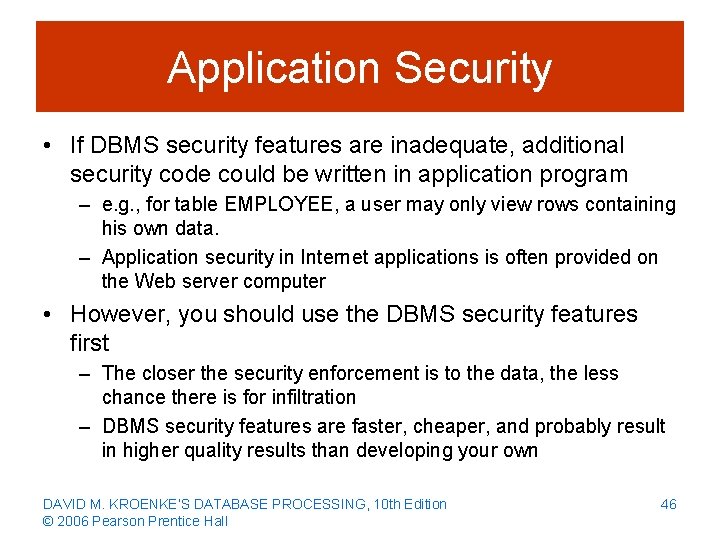
Application Security • If DBMS security features are inadequate, additional security code could be written in application program – e. g. , for table EMPLOYEE, a user may only view rows containing his own data. – Application security in Internet applications is often provided on the Web server computer • However, you should use the DBMS security features first – The closer the security enforcement is to the data, the less chance there is for infiltration – DBMS security features are faster, cheaper, and probably result in higher quality results than developing your own DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 46
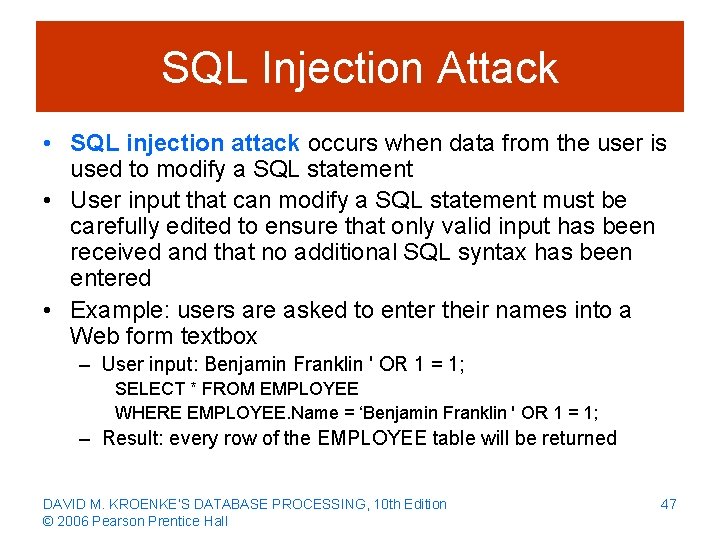
SQL Injection Attack • SQL injection attack occurs when data from the user is used to modify a SQL statement • User input that can modify a SQL statement must be carefully edited to ensure that only valid input has been received and that no additional SQL syntax has been entered • Example: users are asked to enter their names into a Web form textbox – User input: Benjamin Franklin ' OR 1 = 1; SELECT * FROM EMPLOYEE WHERE EMPLOYEE. Name = ‘Benjamin Franklin ' OR 1 = 1; – Result: every row of the EMPLOYEE table will be returned DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 47
Database Recovery • In the event of system failure, that database must be restored to a usable state as soon as possible • Two recovery techniques: – Recovery via reprocessing – Recovery via rollback/rollforward DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 48
Recovery via Reprocessing • Recovery via reprocessing: the database goes back to a known point (database save) and reprocesses the workload from there • Unfeasible strategy because – The recovered system may never catch up if the computer is heavily scheduled – Changing the order of asynchronous events, although concurrent transactions, may cause different results (e. g. , the last window seat goes to someone different upon reprocessing) DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 49
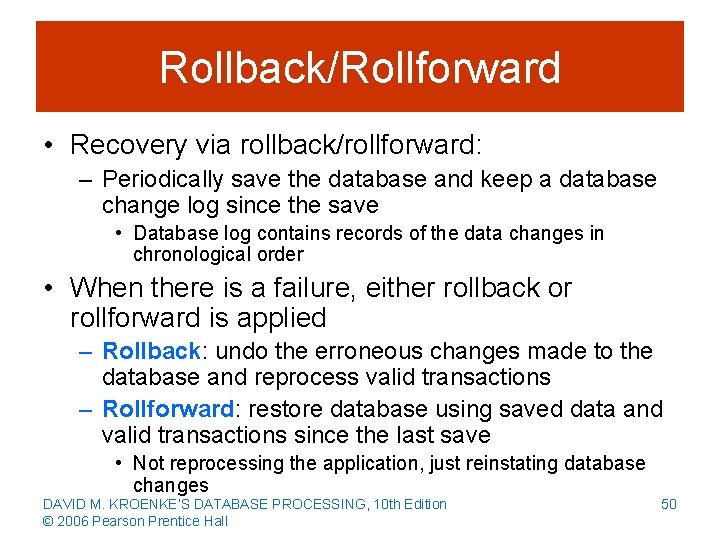
Rollback/Rollforward • Recovery via rollback/rollforward: – Periodically save the database and keep a database change log since the save • Database log contains records of the data changes in chronological order • When there is a failure, either rollback or rollforward is applied – Rollback: undo the erroneous changes made to the database and reprocess valid transactions – Rollforward: restore database using saved data and valid transactions since the last save • Not reprocessing the application, just reinstating database changes DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 50
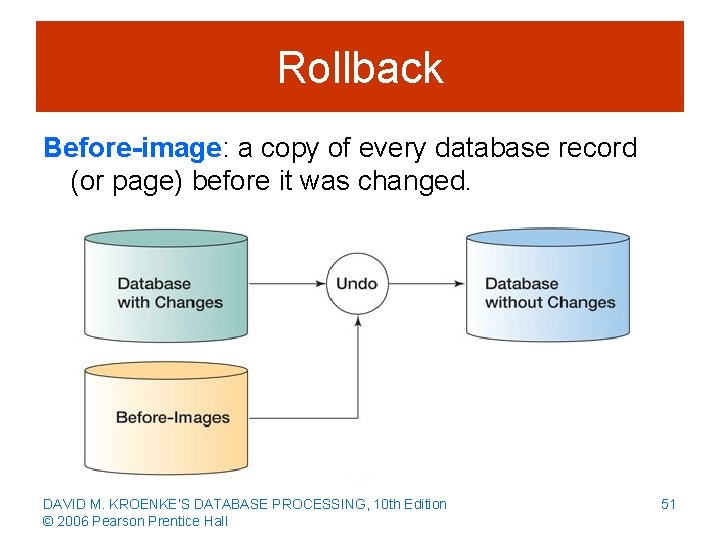
Rollback Before-image: a copy of every database record (or page) before it was changed. DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 51
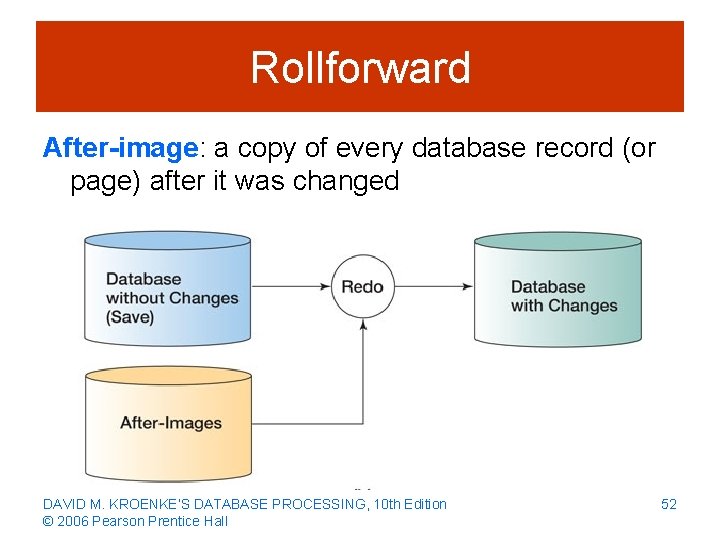
Rollforward After-image: a copy of every database record (or page) after it was changed DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 52
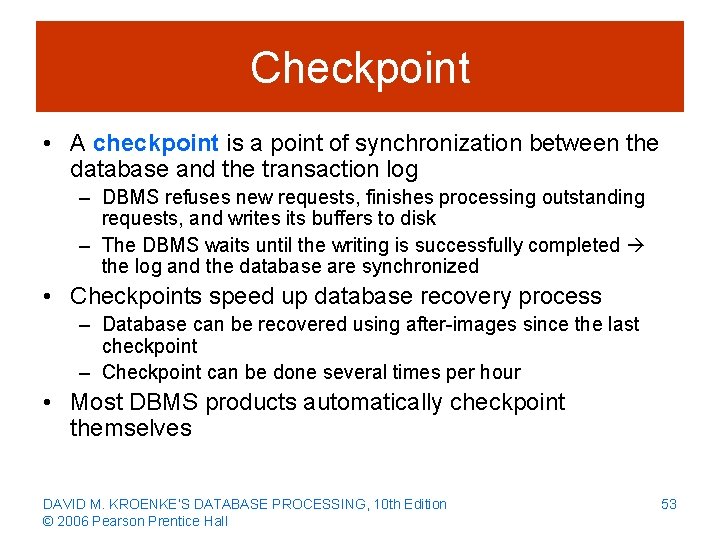
Checkpoint • A checkpoint is a point of synchronization between the database and the transaction log – DBMS refuses new requests, finishes processing outstanding requests, and writes its buffers to disk – The DBMS waits until the writing is successfully completed the log and the database are synchronized • Checkpoints speed up database recovery process – Database can be recovered using after-images since the last checkpoint – Checkpoint can be done several times per hour • Most DBMS products automatically checkpoint themselves DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 53
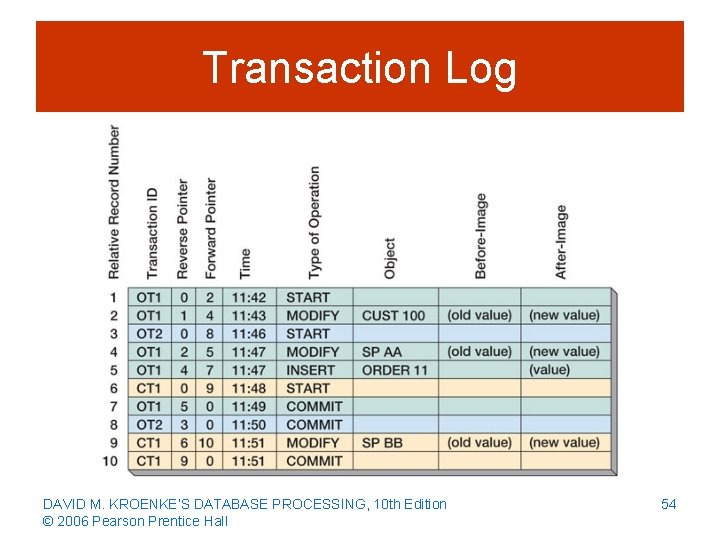
Transaction Log DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 54
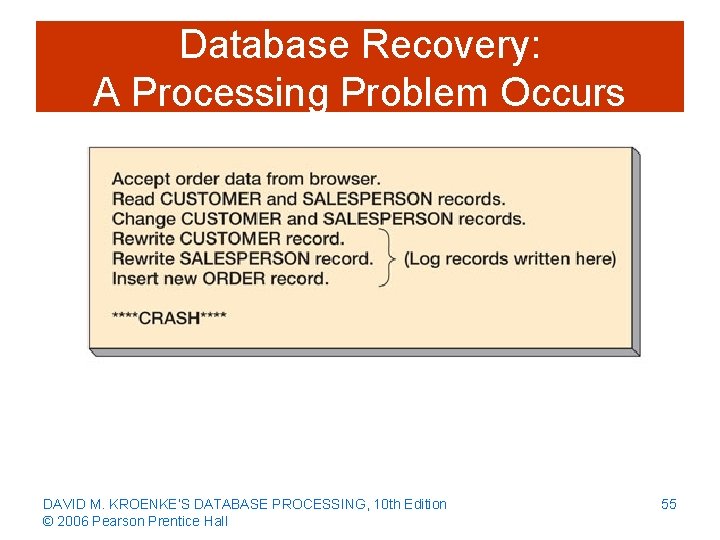
Database Recovery: A Processing Problem Occurs DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 55
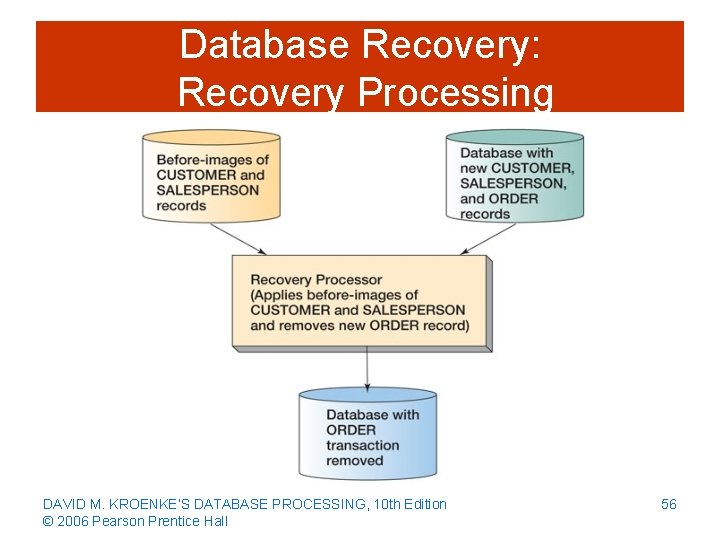
Database Recovery: Recovery Processing DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 56
Managing the DBMS • DBA’s Responsibilities – Generate database application performance reports – Investigate user performance complaints – Assess need for changes in database structure or application design – Modify database structure • e. g. , surrogate keys, use of views – Evaluate and implement new DBMS features – Tune the DBMS • e. g. , locking strategy, indexing DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 57
Maintaining the Data Repository • DBA is responsible for maintaining the data repository • Data repositories are collections of metadata about users, databases, and its applications • The repository may be – Virtual as it is composed of metadata from many different sources: DBMS, code libraries, Web page generation and editing tools, etc. – An integrated product from a CASE tool vendor or from other companies • The best repositories are active and they are part of the system development process DAVID M. KROENKE’S DATABASE PROCESSING, 10 th Edition © 2006 Pearson Prentice Hall 58
- Slides: 58