Managing Information Security at Navy Federal John Myers








- Slides: 19
Managing Information Security at Navy Federal John Myers Vice President, Cybersecurity Navy Federal Credit Union October 4, 2019 1
Agenda Understanding Threat Trends, Threat Drivers & Challenges Managing Information Security at Navy Federal Pursuing Careers in Information Security 2

Understanding Threat Trends, Threat Drivers & Challenges 3

Understanding Threat Trends, Threat Drivers & Challenges • • • Application vulnerabilities Credential stuffing Increased insider threat across industry Trends • • • Transactional fraud Extortion PII exposure Sabotage Misusing asset resources Intellectual property theft Access brokering Hacktivism Thrill seeking Drivers • • • Legacy systems Cloud Supply chain Balancing security with business objectives Proactive versus reactive operations Legacy organizational cultures Challenges 4
Managing Information Security at Navy Federal 5
Who We Are: Navy Federal Credit Union • Our mission is to always put members first • Our most important asset is member trust • As a member-owned, not-for-profit credit union, we are honored to serve those who serve • We’re the largest credit union in the world, serving more than 8. 6 million members • We have $106. 1 billion in assets and a workforce of more than 18, 000 employees, including more than 7, 000 in Pensacola • We manage more than 330 branches in 100+ locations, including 26 international locations 6

How We Work Together Chief Security Officer Chief Information Security Officer Vice President, Information Security Governance Vice President, Cybersecurity 7

How Cybersecurity Operations Has Grown 1 VP 1 AVP 5 managers and 6 supervisors 10 FTEs 45 FTEs 24 x 7 coverage through oncall/MSSP support 12 contractors and 5 interns In-house 24 x 7 x 365 operations Q 4 2016 Q 4 2019 8

Who We Are: Cybersecurity Operations Center Incident Response Engineering Insider Trust Vulnerability Assessment Threat Intelligence 9
Who We Are: Incident Response Provides 24 x 7 x 365 network defense monitoring and response capabilities to protect Navy Federal employees, members, systems and data from advanced persistent threats • Ensures the security and confidentiality of member information • Prevents unauthorized access to and use of member information • Protects against anticipated threats or hazards to the security and integrity of member information 10
Who We Are: Vulnerability Assessment Identify Analyze Communicate Track . . . vulnerabilities affecting the credit union 11

Who We Are: Threat Intelligence Supports Security and the enterprise with risk-based decision making using actionable intelligence analysis and reporting on external cyber threats • • The Intelligence Cycle Threats: Hackers, cyber criminals, nation states Capabilities: Phishing, malware, credential attacks, ransomware, malicious apps 12
Who We Are: Insider Trust Deter Detect Investigate Mitigate. . . behavior by current or former employees, contractors or vendors who may introduce risk or cause harm to NFCU information, data or resources 13
Who We Are: Engineering Design Deploy Maintain . . . all cybersecurity solutions in direct support of the Cybersecurity Operations Center’s mission 14
Successes • • • Cultivating relationships Implementing an intelligence-driven defense strategy Growing our insider trust and digital forensics programs Managing vulnerabilities and identifying network weaknesses Remediating potential phishing emails Promoting/expanding education and training across the credit union 15

Pursuing Careers in Information Security 16
Pursuing Careers in Information Security • Be constantly curious; always ask why • • • Learn creative problem solving Look for internships or co-op programs Learn to code and learn scripting languages Learn to write well and write from the perspective of the business Seek out additional education and certifications • • Diversify your skill set Certs (CISSP, CEH, GCTI, Comp. TIA A+, etc. ) 17
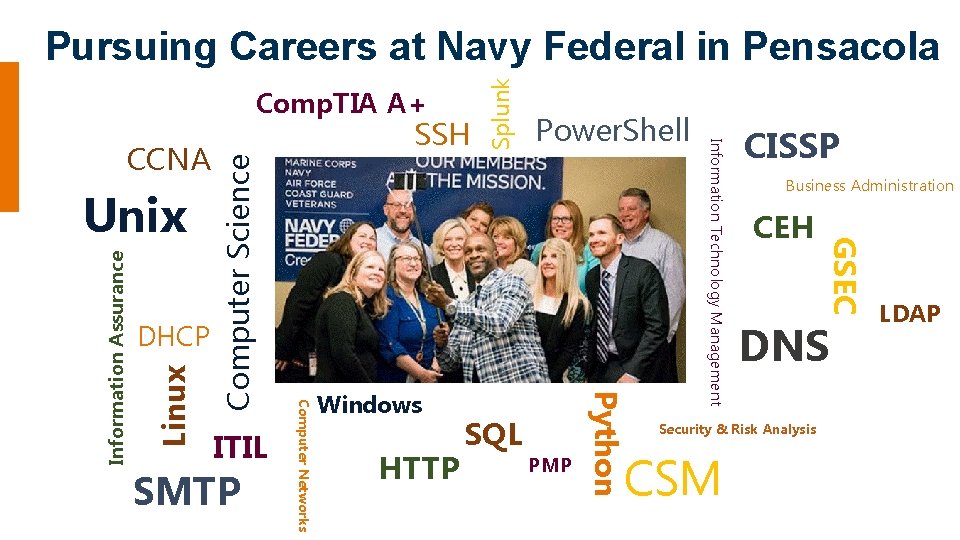
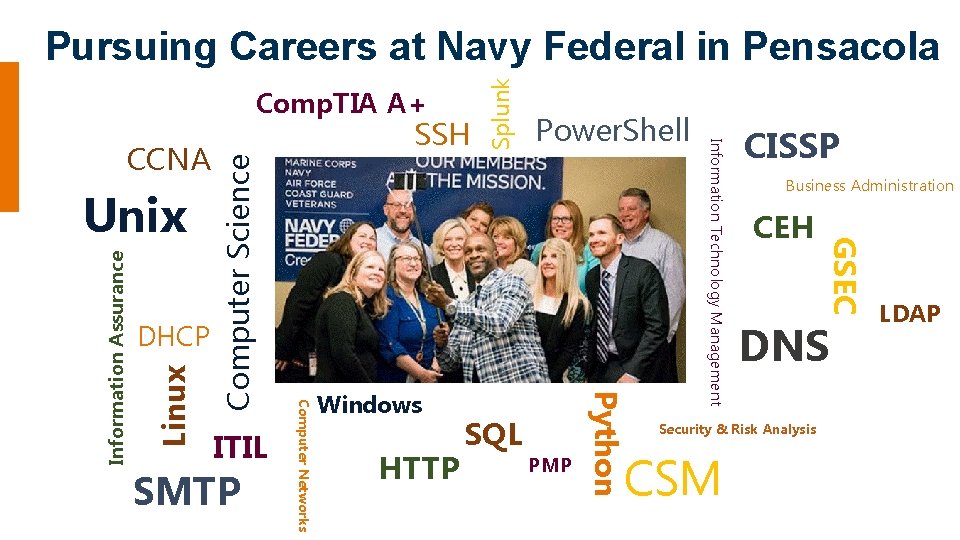
Comp. TIA A+ Computer Science Linux SMTP Windows HTTP SQL PMP Python ITIL Computer Networks Information Assurance DHCP CISSP Business Administration CEH GSEC Unix Power. Shell Information Technology Management CCNA SSH Splunk Pursuing Careers at Navy Federal in Pensacola DNS LDAP Security & Risk Analysis CSM 18

Thank you 19