Managing and Securing the Information System CHAPTER 5

- Slides: 46
Managing and Securing the Information System CHAPTER 5
“Over 60% of the people who have a security breach, have a breach on systems that they aren't actively managing. If we would just take the time to understand where our critical information is, and then manage those systems properly, the risk reduction would be enormous. ” Dorian Cougias, Network Frontiers
Computer Dependence �How important are computers to hospitality organizations? �Turn the computer system off during a rush period and observe the consequences. �Keeping computer downtime to a minimum in guest related areas (e. g. , reservations and front desk) is critical.
Mission-Critical Systems �Mission-critical systems are systems that whose reliable performance is crucial to the successful performance of the organization in which it is used. �For a hotel, mission critical systems are central reservation system (CRS) and property management system (PMS). �For a restaurant, mission critical system is Point of Sale system (POS).
Maintaining the Systems �To make sure that these systems are up and running, there needs to be a systematic approach to maintain them. Enterprise Level Unit level (restaurant or hotel) User level (remote access- guest or staff)
All businesses are subject to business disruptions �The reasons may be different such as Fire Flood Earthquakes Vandalism Stealing Human error Utility disruptions (such as power outages) Malicious threats from outsiders or misuse of systems.
Disaster Contingency Recovery Plan �Although a DCRP is vital, it is primarily a reactive approach (i. e. , a corrective control) and not a comprehensive plan for risk management. �In contrast, a business continuity plan (BCP) seeks to eliminate or reduce the impact of a disaster condition before the condition occurs.
Business Continuity Plan �Business Continuity Planning (BCP) is an interdisciplinary concept used to create and validate a practiced logistical plan for how an organization will recover and restore partially or completely interrupted critical function(s) within a predetermined time after a disaster or extended disruption.
Common Causes of System Failure 1. 2. 3. 4. 5. 6. 7. Operator Error Hardware Failure Power Problems Software Bug System Overload Virus Spyware Apple Ad Keylogger Hardware
Operator Error �Various operator errors can cause system failure �Common errors include improper handling of lengthy processing routines (e. g. , end-of-day audit), database maintenance (e. g. , changing and deleting data), and hardware (e. g. , moving a hard disk without parking the read/write head). �Providing thorough training and establishing careful procedures reduce operator mistakes
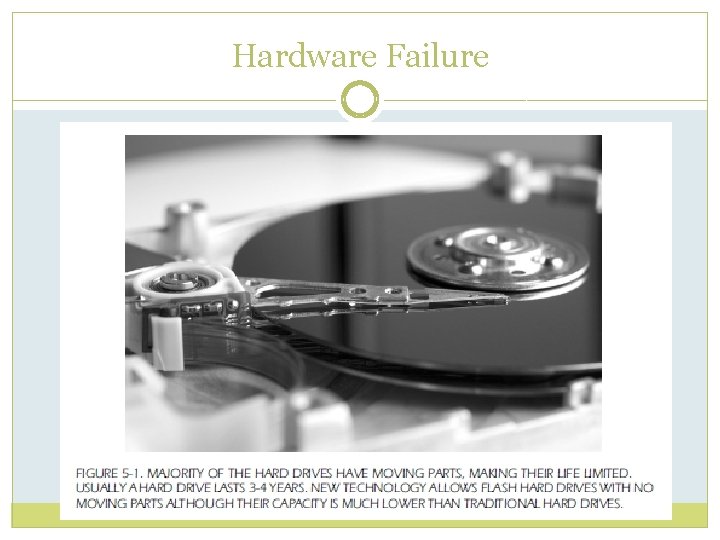
Hardware Failure
Hardware Failure �Five basic measures reduce hardware malfunctions: 1. 2. 3. 4. 5. Keep the temperature and relative humidity at the appropriate levels Keep equipment clean Keep magnets away from computers Keep Water and corrosive agents away from computers Establish a preventative maintenance program
Fault-Tolerant �A fault-tolerant computer is equipped with a backup system enabling it to function despite the failure of certain internal hardware components such as a hard drive or disk controller card.
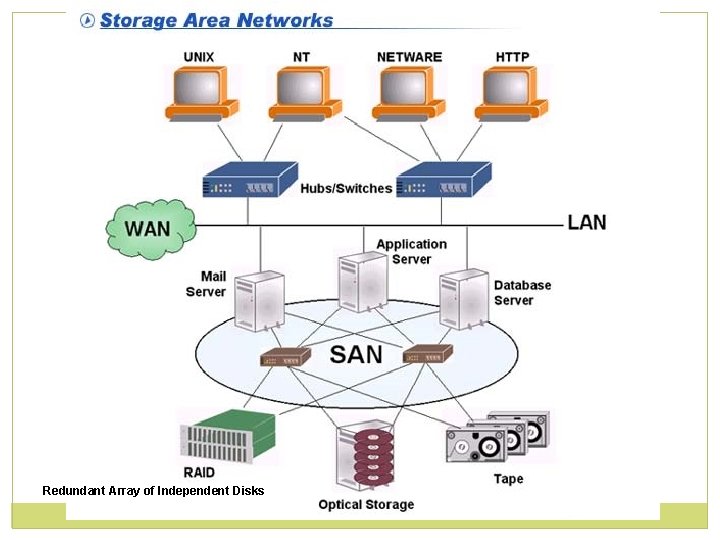
Storage Area Network �A storage area network (SAN) is an architecture to attach remote computer storage devices such as disk arrays to servers in such a way that, to the operating system, the devices appear as locally attached
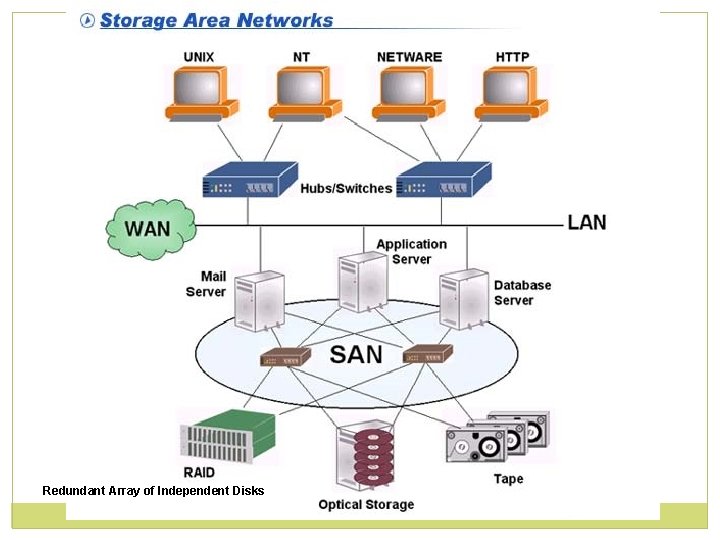
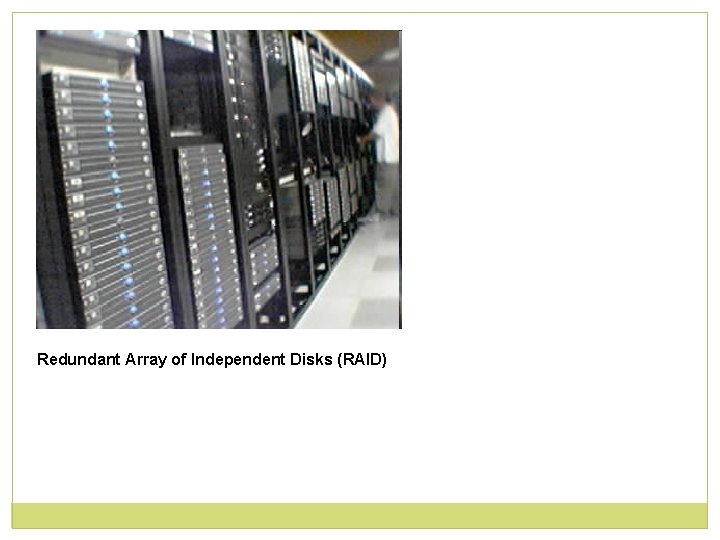
Redundant Array of Independent Disks
Redundant Array of Independent Disks (RAID)
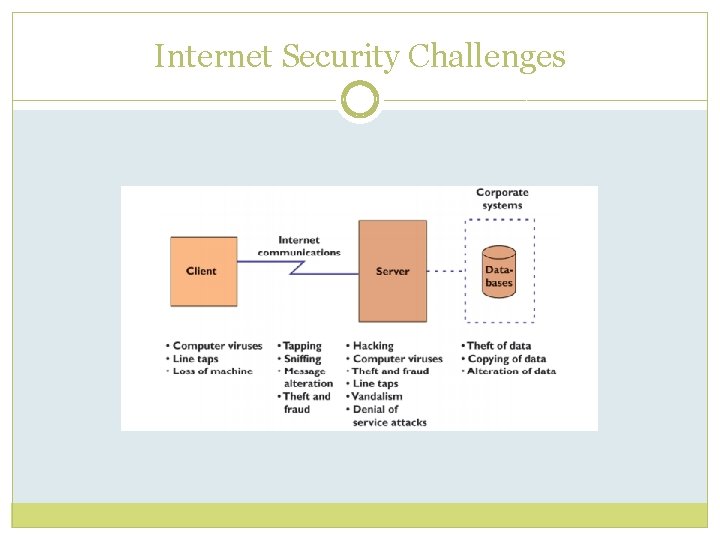
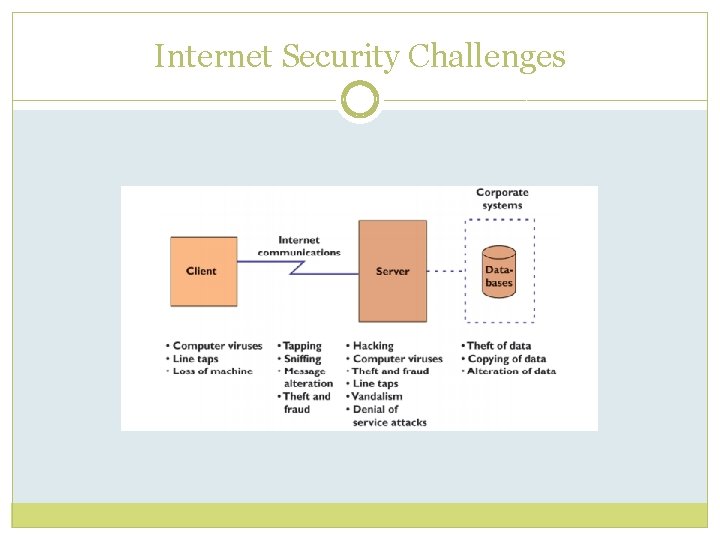
Internet Security Challenges
Power Problems �Power line trouble causes 70 percent of hardware and software failures. �Symptoms include burned components, garbled transactions, memory loss, corrupted data, lost data, and unexplained intermittent problems.
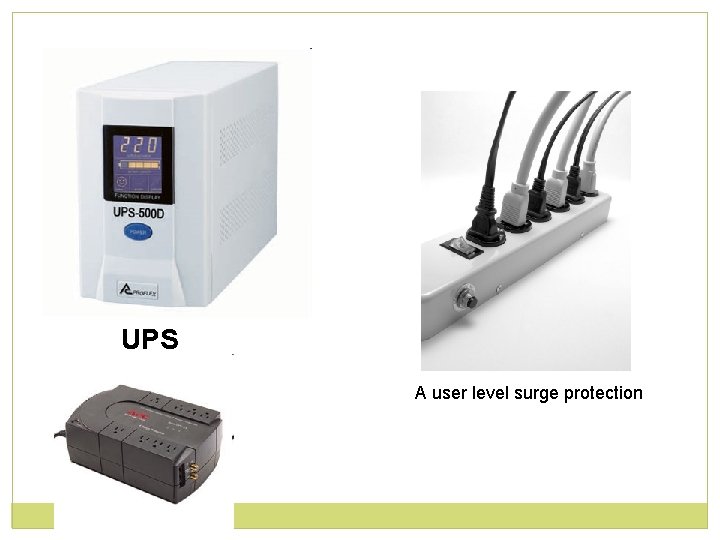
Power Problems �To avoid power disturbances, the following measures should be implemented. 1. 2. 3. Surge protection Proper wiring and grounding Uninterruptible Power Supply (UPS)
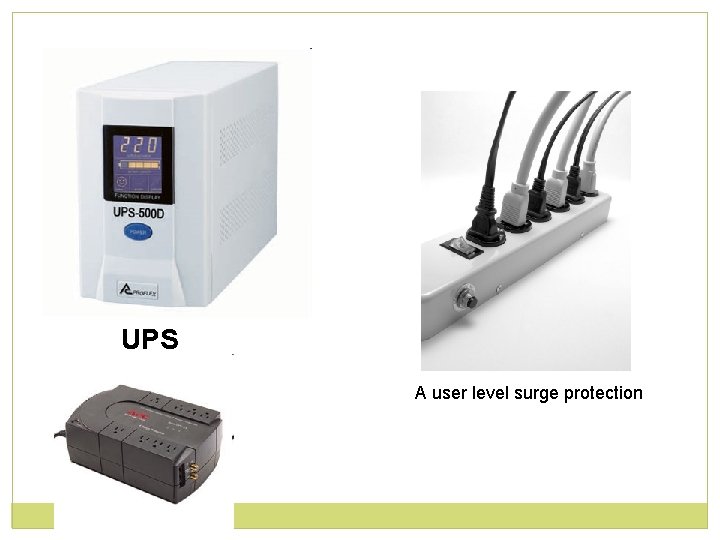
UPS A user level surge protection
Software Bug �A bug is a logic error in the program preventing it from working properly �For example, one hospitality accounting program aborts if the user forgets to turn on the printer before printing a financial statement
System Overload �Placing too many demands on a computer can greatly diminish its performance and may cause system failure. �Causes of system overloads include: 1. 2. 3. 4. 5. Insufficient Central Processing Unit (CPU) Clock Speed. Inadequate Random Access Memory (RAM) Slow Mechanical Components File Fragmentation Inadequate Disk Storage
External hard drive that can be connected to computer by USB or Firewire
Virus �Virus spreads by copying itself from one program to the next, changing or destroying each program that it infects without the user knowing it. �The carrier of a virus is a program that appears legitimate called a TROJAN HORSE
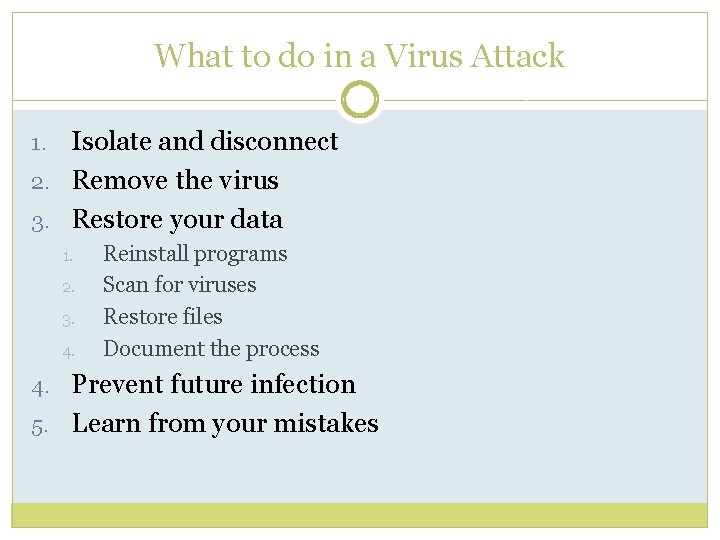
What to do in a Virus Attack Isolate and disconnect 2. Remove the virus 3. Restore your data 1. 2. 3. 4. Reinstall programs Scan for viruses Restore files Document the process 4. Prevent future infection 5. Learn from your mistakes
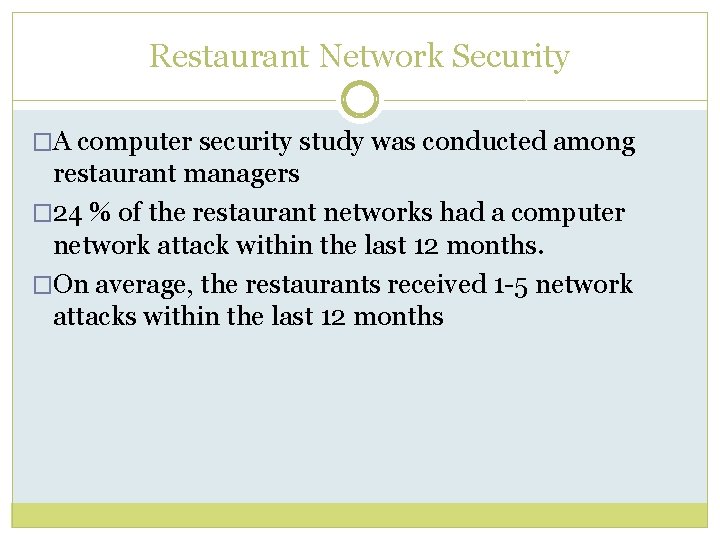
Restaurant Network Security �A computer security study was conducted among restaurant managers � 24 % of the restaurant networks had a computer network attack within the last 12 months. �On average, the restaurants received 1 -5 network attacks within the last 12 months
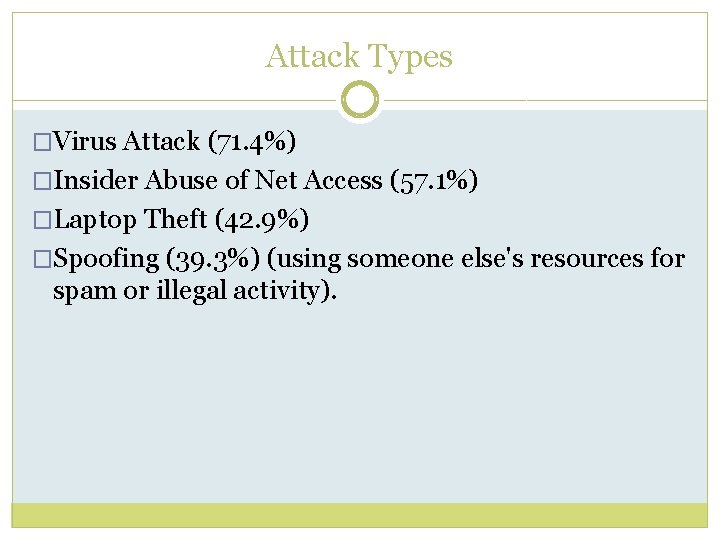
Attack Types �Virus Attack (71. 4%) �Insider Abuse of Net Access (57. 1%) �Laptop Theft (42. 9%) �Spoofing (39. 3%) (using someone else's resources for spam or illegal activity).
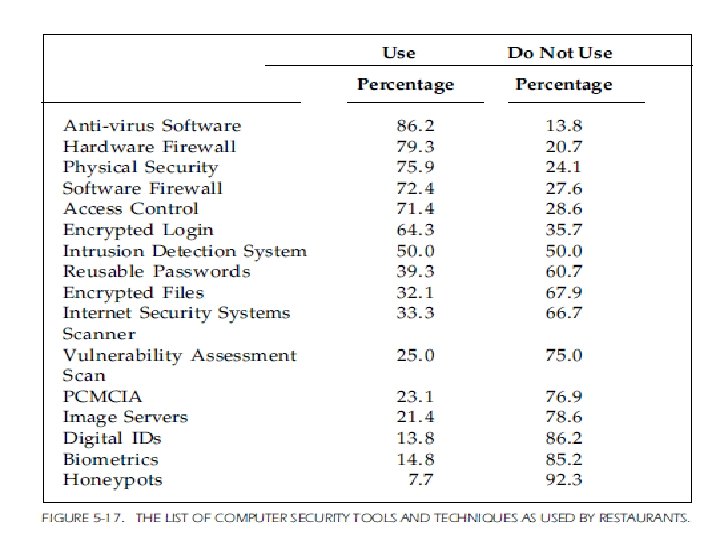
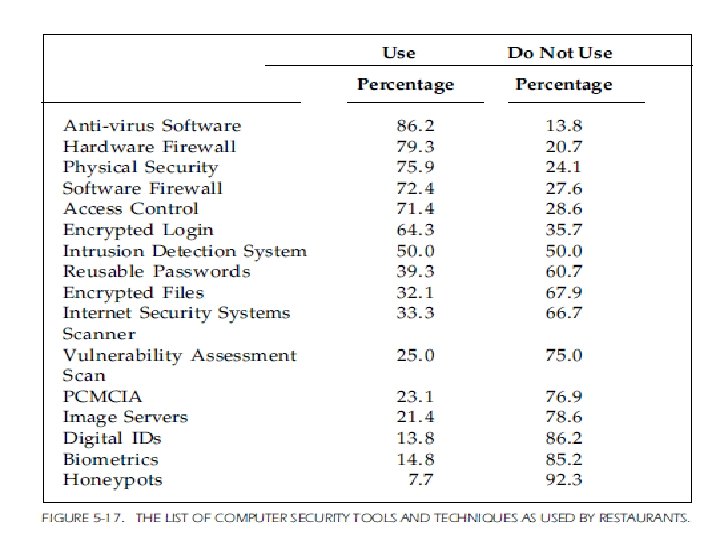
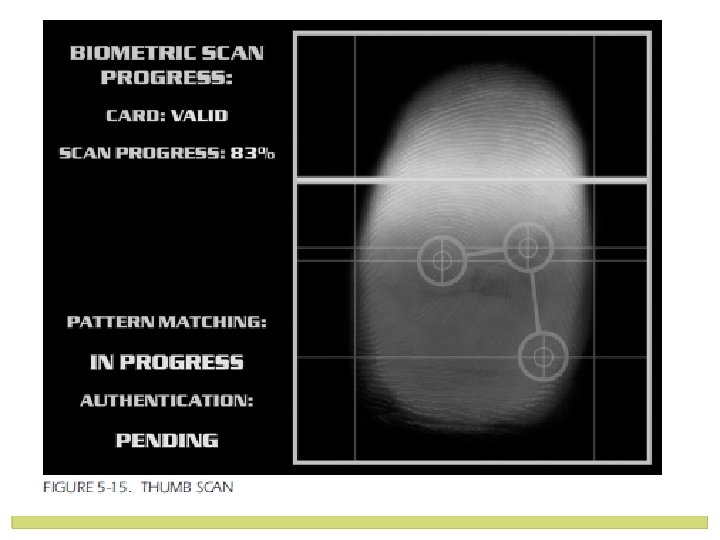
Protection from Attacks �The most used protection tool is anti-virus software (86. 2%), hardware firewall (79. 3%) and physical security (75. 9%). �The least used network security tools are honeypots (7. 7%) and biometrics (14. 8%).
Spyware �Spyware is computer software that is installed secretly on a computer to intercept or take partial control over the user's interaction with the computer, without the user's informed consent
Backup Strategies �Backup Frequency �Backup Method �Rotation of Secondary Storage Media �Hardcopy
Computer Security �Security violation examples include: Salespeople copying the hotel client list onto a USB drive and selling it to a competitor Front-desk clerks receiving cash to settle guest folios, but instead pocketing the cash and transferring the outstanding balance to a bogus city ledger account or “black hole” account. Employees gaining access to payroll records and changing wage rates. Servers voiding entree items off guest checks after collecting cash.
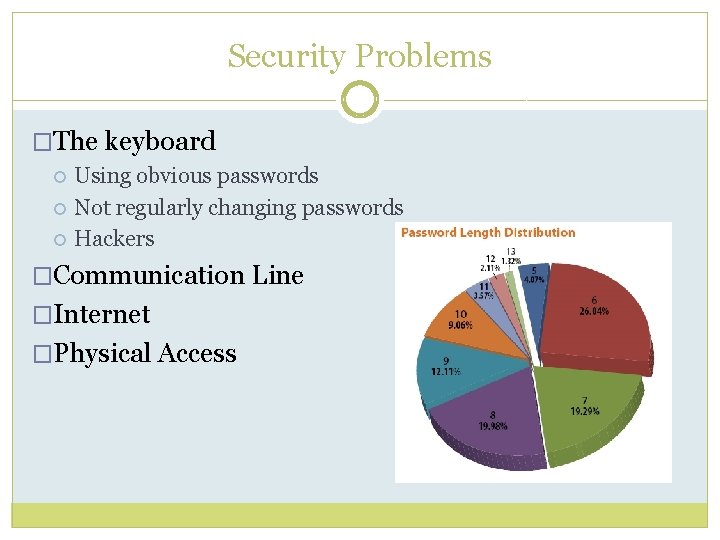
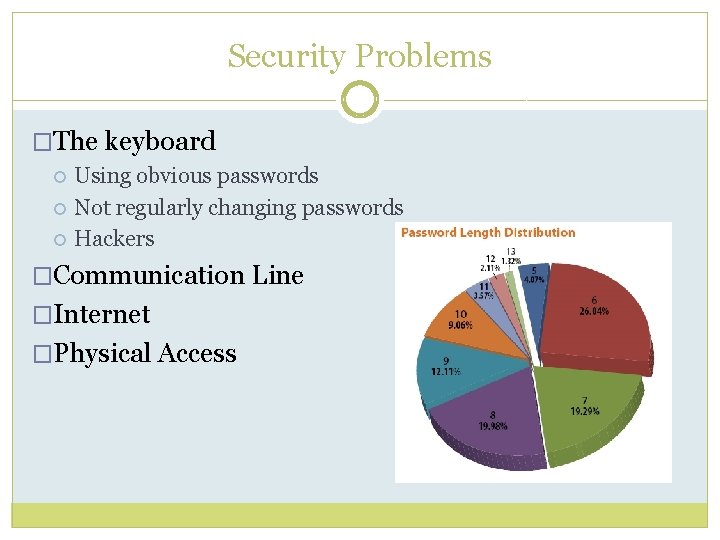
Security Problems �The keyboard Using obvious passwords Not regularly changing passwords Hackers �Communication Line �Internet �Physical Access

Most Common Passwords
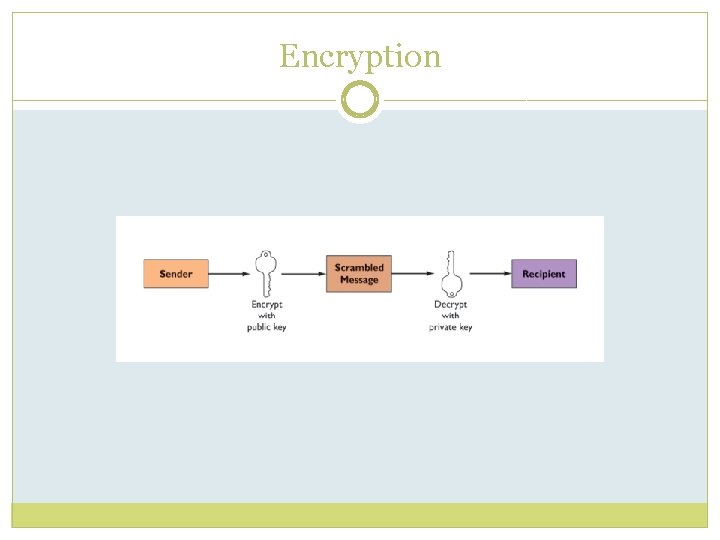
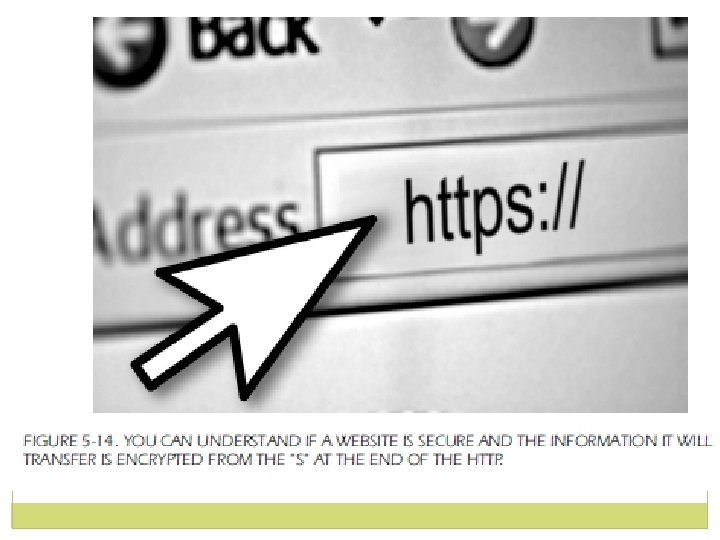
Encryption �In the case of transmitting data over the Internet protocol, using a secure, encrypted way of communication is also a key to secure data transmission. �Computer encryption is based on the science of cryptography, which has been used throughout history. Vidoe: Encryption of Credit Card Data
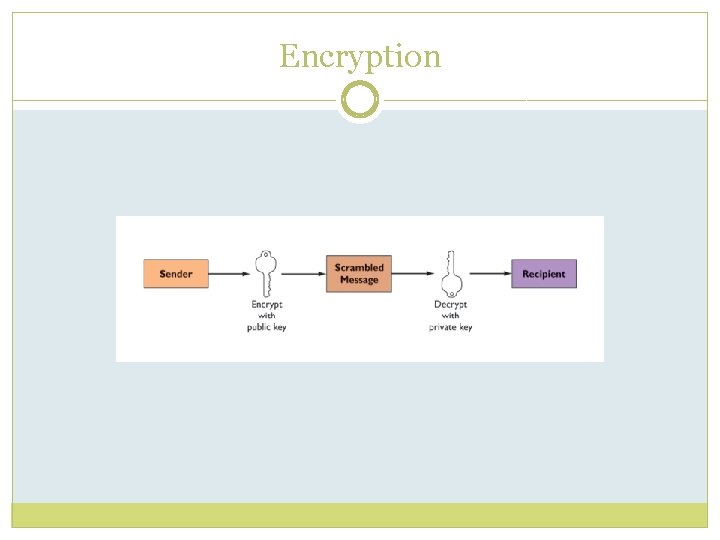
Encryption
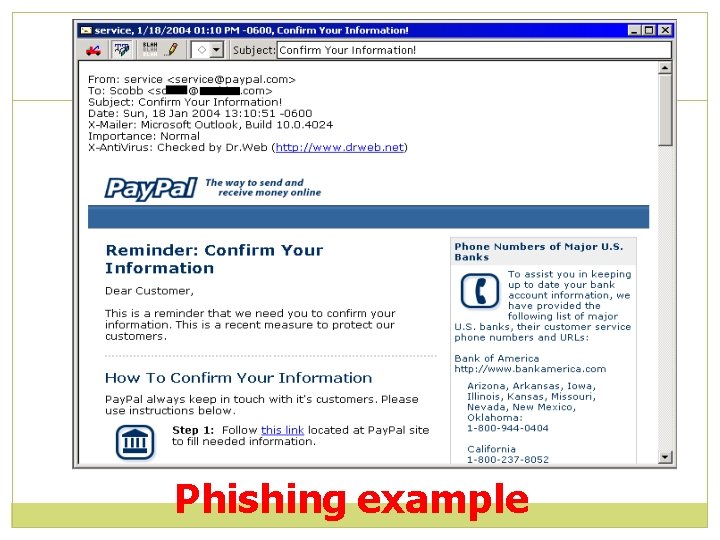
Phishing is a technique used by strangers to "fish" for information about you, information that you would not normally disclose to a stranger, such as your bank account number, PIN, and other personal identifiers such as your National Insurance number. These messages often contain company/bank logos that look legitimate and use flowery or legalistic language about improving security by confirming your identity details.
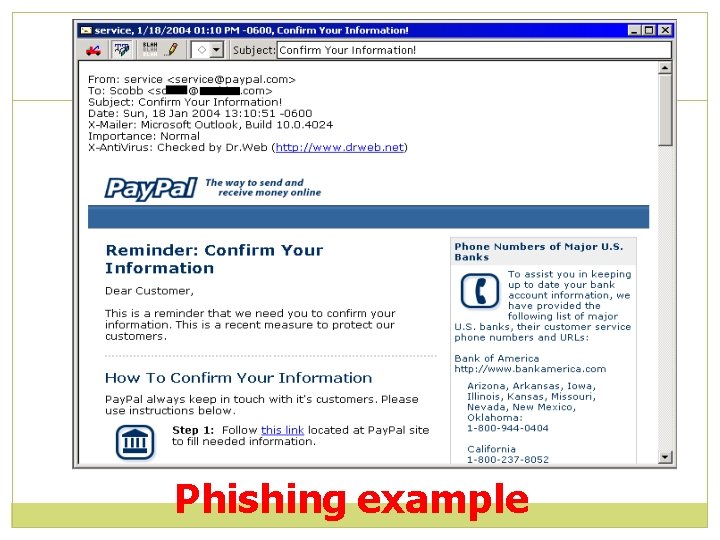
Phishing example
IT Compliance �Keeping IT systems in line with local, state, national and international level laws, regulations, standards, and policies. �The Payment Card Industry Council is a consortium of credit card issuing brands: Visa, Incorporated; American Express, Master. Card Worldwide, Discover Financial Services and JCB International
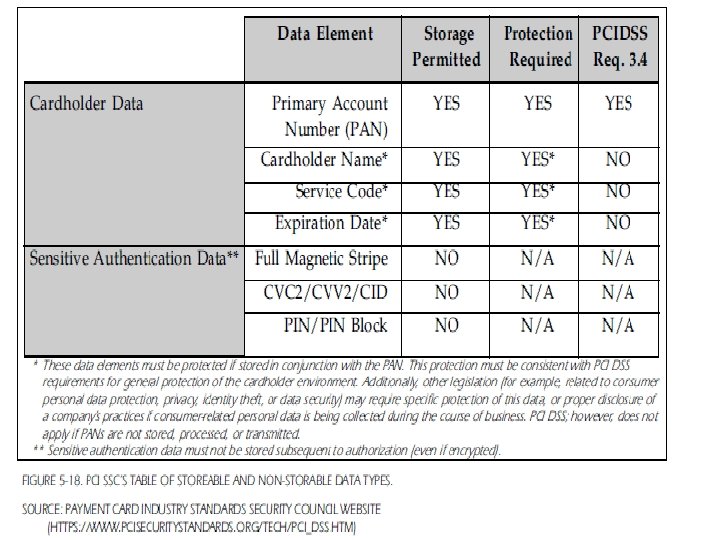
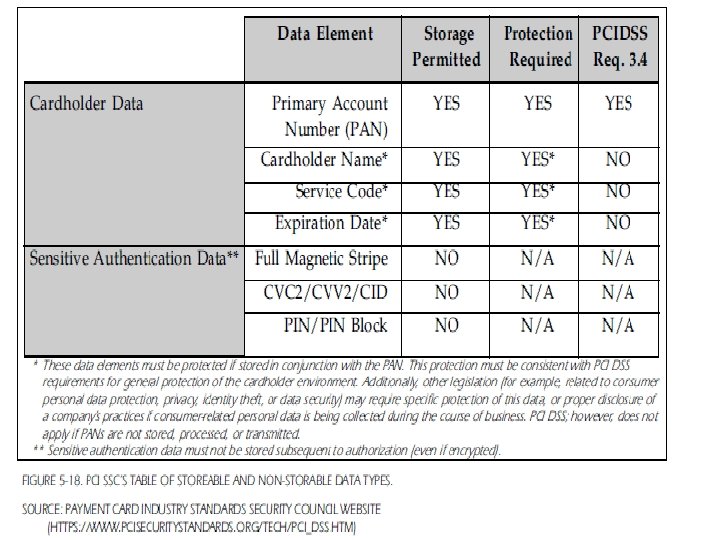
PCI DSS �PCI Council have formed this consortium to improve the security of the global payment system by protecting consumers, merchants and banks from frauds and hacks. �The consortium has created a set of Data Security Standards governing the protection of all sensitive cardholder data stored electronically or on paper. Video: PCI DSS Explained Website: PCI DSS
PCI DSS �Requirement 1: Install and maintain a firewall configuration to protect cardholder data �Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters �Requirement 3: Protect stored cardholder data �Requirement 4: Encrypt transmission of cardholder data across open, public networks
PCI DSS �Requirement 5: Use and regularly update anti-virus software �Requirement 6: Develop and maintain secure systems and applications �Requirement 7: Restrict access to cardholder data by business need to-know �Requirement 8: Assign a unique ID to each person with computer access
PCI DSS �Requirement 9: Restrict physical access to cardholder data. �Requirement 10: Track and monitor all access to network resources and cardholder data �Requirement 11: Regularly test security systems and processes �Requirement 12: Maintain a policy that addresses information security