Malware Classification And Detection Matt Banick Malware A
Malware Classification And Detection Matt Banick
Malware – A Brief Introduction � Broad Definition: “Let us take the easy one first. "Malware" is short for malicious software and is typically used as a catch-all term to refer to any software designed to cause damage to a single computer, server, or computer network, whether it's a virus, spyware, et al. ” (1)
Classification � How to Classify Malware? ◦ Trojan, Virus, Worm, Spyware, etc ◦ Level of compromise? � Security Classification? ◦ Degree of OS compromise ◦ Changes ◦ Security Compromise
Malware Classification Levels � “Stealth” Malware Taxonomy � Malware re-definition ◦ Joanna Rutkowska ◦ Changes in OS Kernel ◦ Security applications ◦ Other processes � Four types (0 -3) � No true order
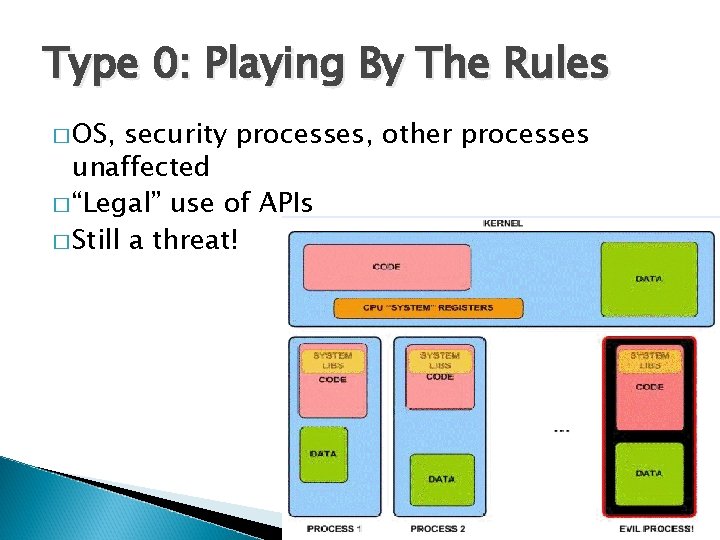
Type 0: Playing By The Rules � OS, security processes, other processes unaffected � “Legal” use of APIs � Still a threat!
Type 1: Constant No More � Malware changes ‘constant’ data � True ‘system compromise’
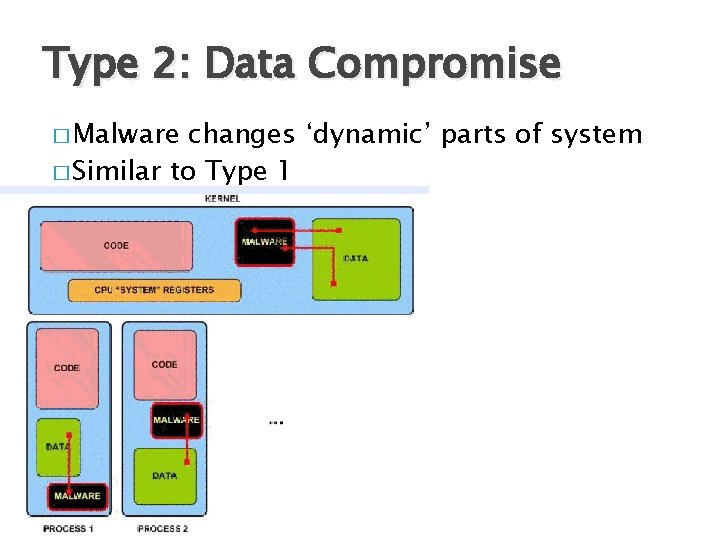
Type 2: Data Compromise � Malware changes ‘dynamic’ parts of system � Similar to Type 1
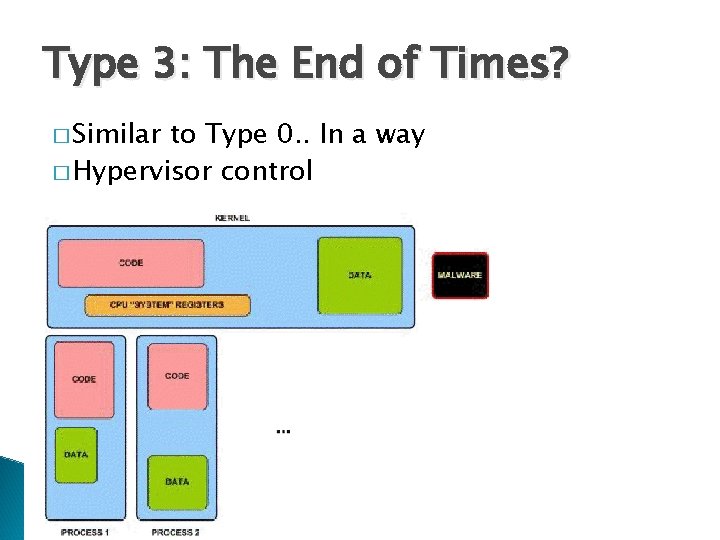
Type 3: The End of Times? � Similar to Type 0. . In a way � Hypervisor control
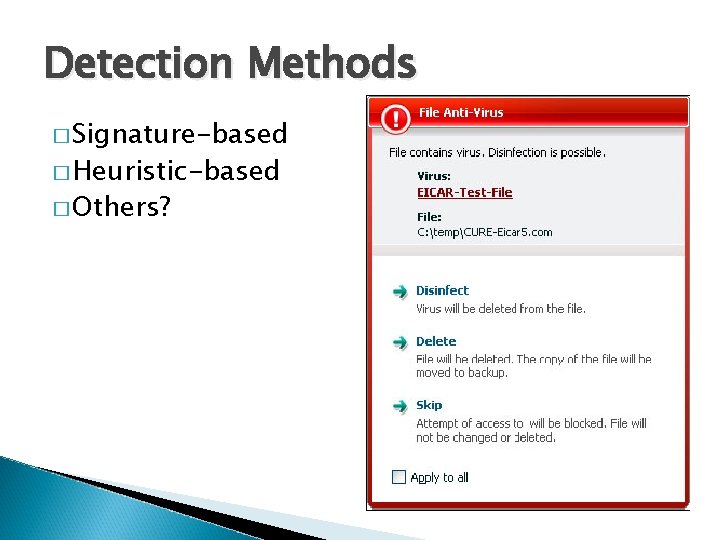
Detection Methods � Signature-based � Heuristic-based � Others?
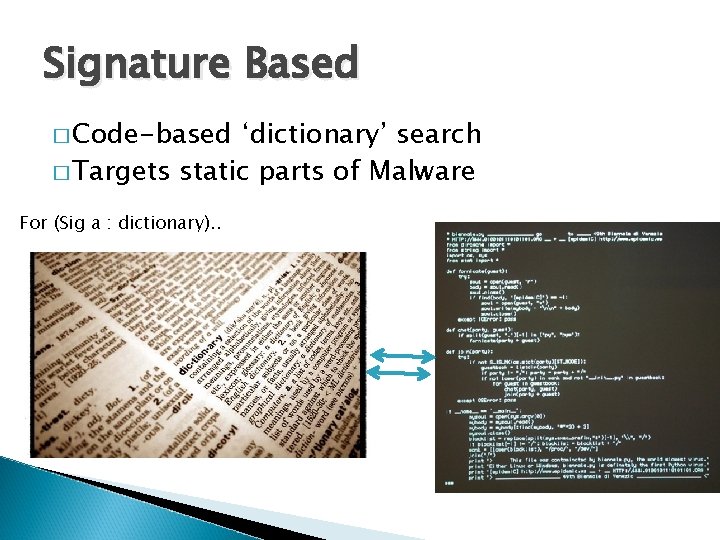
Signature Based � Code-based ‘dictionary’ search � Targets static parts of Malware For (Sig a : dictionary). .
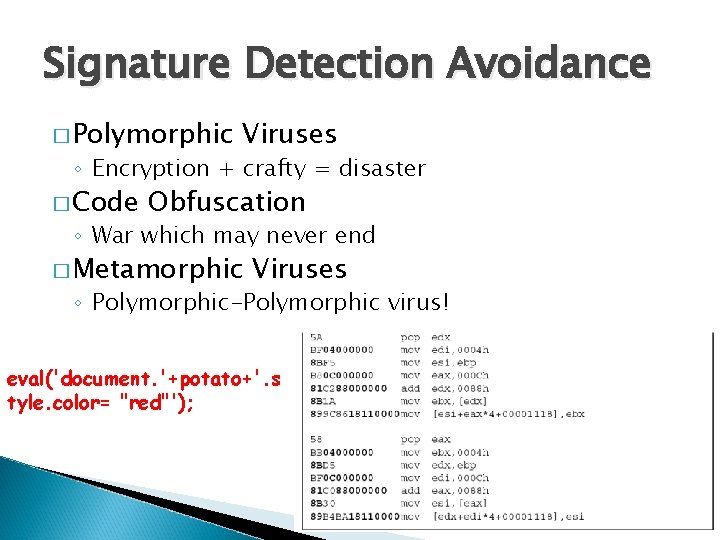
Signature Detection Avoidance � Polymorphic Viruses ◦ Encryption + crafty = disaster � Code Obfuscation ◦ War which may never end � Metamorphic Viruses ◦ Polymorphic-Polymorphic virus! eval('document. '+potato+'. s tyle. color= "red"');
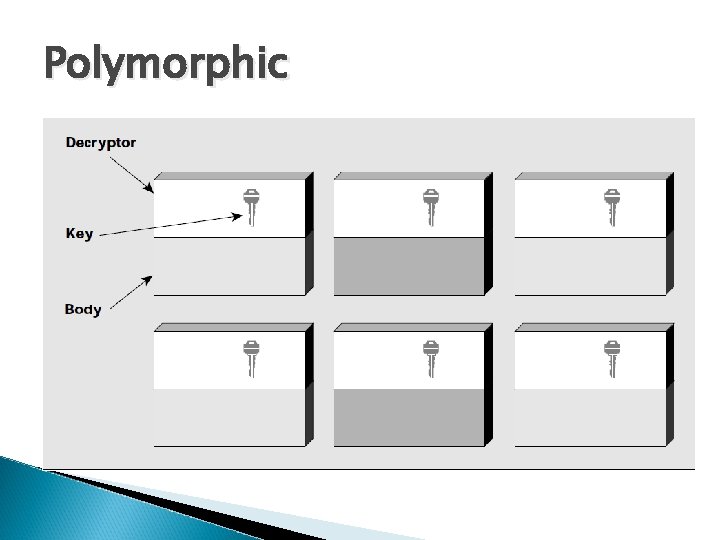
Polymorphic
Heuristic Based � Can ◦ ◦ include different concepts Virus activity Instruction oddities File activity Network activity � Static ◦ Code review � Dynamic ◦ Watch and wait…
Heuristic Troubles � False-positives can be costly ◦ User indifference ◦ PR nightmare ◦ Slow While (a < 5000) sleep(5); //random code Some_malicious_code //random code Some_more_malicious_code //random code … etc.
User Based � What “Should” occur? � Emerging research � Math based (in a way…) � Problems ◦ Dynamic web pages ◦ Analysis is costly ◦ White-listing processes
References � � � � � http: //technet. microsoft. com/en-us/library/dd 632948. aspx (1) Sony Rootkit: http: //blogs. technet. com/b/markrussinovich/archive/2005/10/31/sony-rootkits-and-digital-rightsmanagement-gone-too-far. aspx Polymorphic Viruses: http: //www. symantec. com/avcenter/reference/striker. pdf Obfuscation: http: //delivery. acm. org/10. 1145/1780000/1772720/p 281 cova. pdf? key 1=1772720&key 2=0800233031&coll=DL&dl=ACM&ip=129. 244. 189. 101&CFID=17197576&CFTOKEN=8574 6334 Metamorphic Viruses: http: //www. symantec. com/avcenter/reference/hunting. for. metamorphic. pdf RDAE & Other info: http: //docs. google. com/viewer? a=v&q=cache: p 2 Xz. CVP 51 GQJ: www. waset. org/journals/waset/v 3445. pdf+RDA+decryption+engines&hl=en&gl=us&pid=bl&srcid=ADGEESj 7 KEk. EBTke. J 5 ydlc. Aaf. ATSGutw. Plsj. A 8 mz. G 6 d_bsn. Ak Ube. Oo. ZSnfe 6 BIGNC 4 ff. QZpac. WFGze. KWhs. H 8 JMn 7 Lk. Ydf. Cw. Od 2 q-Vk. Dnyvrun. TVf. M 4 CSQOO 1 xui 6 u. B 3 DUg. EBc 3 m. X_n 3&sig=AHIEtb. Qu 67 h 41 KBk. C 3 Hj. ISYFce. Sr. QFQZUQ Samsung Issue: http: //www. thetechherald. com/article. php/201113/6997/Samsung-keylogger-fears-based-on-falsepositives Heuristic Basics: http: //vx. netlux. org/lib/static/vdat/epheurs 1. htm More Heuristics (Dynamic): http: //service 1. symantec. com/legal/publishedpatents. nsf/0/4 b 4 a 30633137923 b 88256 df 7005 d 6 b 5 d/$FILE/United%20 Stat es%20 Patent%206, 357, 008. htm � User-based detection: http: //otc. rutgers. edu/pdf/Yao-09 -046. pdf � User-based detection cont: http: //people. cs. vt. edu/danfeng/papers/paper 106_icics 2009. pdf � Blue Pill wrap: http: //securitywatch. eweek. com/showdown_at_the_blue_pill_corral. html
Picture References � � � http: //www. google. com/imgres? imgurl=http: //withfriendship. com/images/b/8701/trojan-horsevirus. png&imgrefurl=http: //withfriendship. com/user/pintu/trojan-horsevirus. php&usg=__p. BZIK 81 bo. UOn. TGwvq 22 gg. To 4 dpk=&h=413&w=551&sz=28&hl=en&start=8&sig 2=Itoi 02 OTbd 0 L 3 Ac. Sia. HDDQ&zoom=1&tbnid=c. Ukl 2 JE K 07 AXKM: &tbnh=100&tbnw=133&ei=l. UGr. Td. CQHu. Xm 0 QG 3 itz 5 CA&prev=/images%3 Fq%3 DTrojan%2 Bhorse%26 um%3 D 1%26 hl%3 Den%26 client%3 Dfirefoxa%26 sa%3 DN%26 rls%3 Dorg. mozilla: en-US: official%26 biw%3 D 1600%26 bih%3 D 707%26 tbm%3 Disch&um=1&itbs=1 http: //www. google. com/imgres? imgurl=http: //www. topnews. in/files/sony_logo_1. jpg&imgrefurl=http: //www. topnews. in/technologyupdate/sony&usg=__IWFxwk. G 68 KOn. UXwbhf. Lw 8 wy. Cv 4=&h=400&w=600&sz=12&hl=en&start=0&sig 2=5 d. GNYCEjtqlyq. Xv. Qe 8 a. Sg. Q&zoom=1&tbnid=pk. P 8 v. Bh. PZ 6 WRM: &tbnh=143&tbnw=214&ei=TEmr. TYH 8 IMba 0 QG 21 e. Wd. CQ&prev=/images%3 Fq%3 DSony%26 um%3 D 1%26 hl%3 Den%26 client%3 Dfirefoxa%26 rls%3 Dorg. mozilla: en. US: official%26 biw%3 D 1600%26 bih%3 D 707%26 tbm%3 Disch&um=1&itbs=1&iact=hc&vpx=138&vpy=150&dur=58897&hovh=183&hovw=275&tx=201&ty=9 3&oei=TEmr. TYH 8 IMba 0 QG 21 e. Wd. CQ&page=1&ndsp=21&ved=1 t: 429, r: 0, s: 0 http: //www. google. com/imgres? imgurl=http: //images. amazon. com/images/G/01/software/detail-page/kasperskyvirus. jpg&imgrefurl=http: //www. amazon. com/Kaspersky-Anti-Virus-7 -0 -OLDVERSION/dp/B 000 U 819 A 2&usg=__o. Jrp_d. VVIHZ 2 A 2 T 6 c 6 r 7 f 8 Bos 9 s=&h=385&w=300&sz=27&hl=en&start=0&sig 2=Mp. Ywwna 9 pcxc 2 Nqb 9 c. HGhw&zoom= 1&tbnid=mj 4 A 1 x. EQl. KMe. WM: &tbnh=133&tbnw=104&ei=SRCv. Ta. C 6 Go. Xa 0 QGl 9 ryo. Cw&prev=/images%3 Fq%3 Dvirus%2 Bdetection%26 hl%3 Den%26 biw%3 D 16 00%26 bih%3 D 707%26 gbv%3 D 2%26 tbm%3 Disch&itbs=1&iact=hc&vpx=131&vpy=70&dur=307&hovh=209&hovw=163&tx=108&ty=124&oei=SRCv. Ta. C 6 Go Xa 0 QGl 9 ryo. Cw&page=1&ndsp=33&ved=1 t: 429, r: 0, s: 0 http: //www. google. com/imgres? imgurl=http: //vxheavens. com/lib/img/mjp 00/biennale. py_code 72. jpg&imgrefurl=http: //vxheavens. com/lib/mjp 00. html&usg=__d 9 ctj. Qol 4 n 95 KZa 9 g 1 i. S 3 sfa. YKI=&h=329&w=346&sz=175&hl=en&start=21&sig 2=U 9 qp. V Qz 1 A 0 w. TEWp. MR 8 Re. Bw&zoom=1&tbnid=Ba 1 Unp. Ci 56 sn. OM: &tbnh=127&tbnw=125&ei=TBmv. TYqj. Iozeg. Qfs 9 I 3 x. Cw&prev=/search%3 Fq%3 Dcode%26 hl%3 De n%26 client%3 Dfirefox-a%26 rls%3 Dorg. mozilla: en. US: official%26 biw%3 D 1600%26 bih%3 D 707%26 site%3 Dsearch%26 tbm%3 Disch 0%2 C 760&um=1&itbs=1&iact=hc&vpx=223&vpy=327&dur=244&hovh=219& hovw=230&tx=70&ty=139&oei=KBmv. Tcmr. EO-L 0 QGUk 9 Gj. Cw&page=2&ndsp=38&ved=1 t: 429, r: 29, s: 21&biw=1600&bih=707 http: //www. thetechherald. com/article. php/201113/6997/Samsung-keylogger-fears-based-on-false-positives
- Slides: 17