Major Communications Cables Points of Convergence ATT Verizon
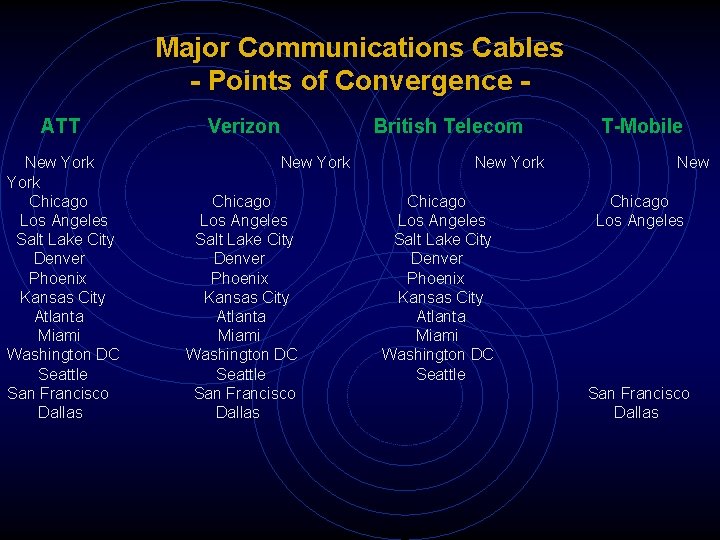
Major Communications Cables - Points of Convergence ATT Verizon British Telecom T-Mobile New York Chicago Los Angeles Salt Lake City Denver Phoenix Kansas City Atlanta Miami Washington DC Seattle San Francisco Dallas New York Chicago Los Angeles Salt Lake City Denver Phoenix Kansas City Atlanta Miami Washington DC Seattle New Chicago Los Angeles San Francisco Dallas
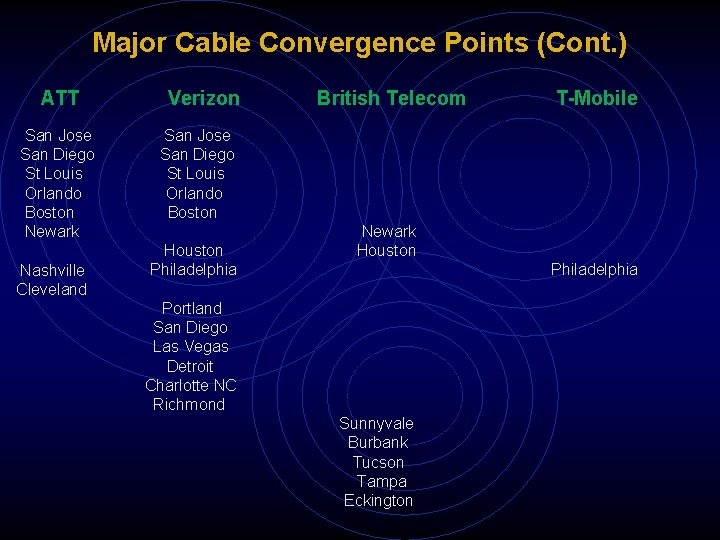
Major Cable Convergence Points (Cont. ) ATT Verizon San Jose San Diego St Louis Orlando Boston Newark Nashville Cleveland British Telecom T-Mobile San Jose San Diego St Louis Orlando Boston Houston Philadelphia Newark Houston Philadelphia Portland San Diego Las Vegas Detroit Charlotte NC Richmond Sunnyvale Burbank Tucson Tampa Eckington
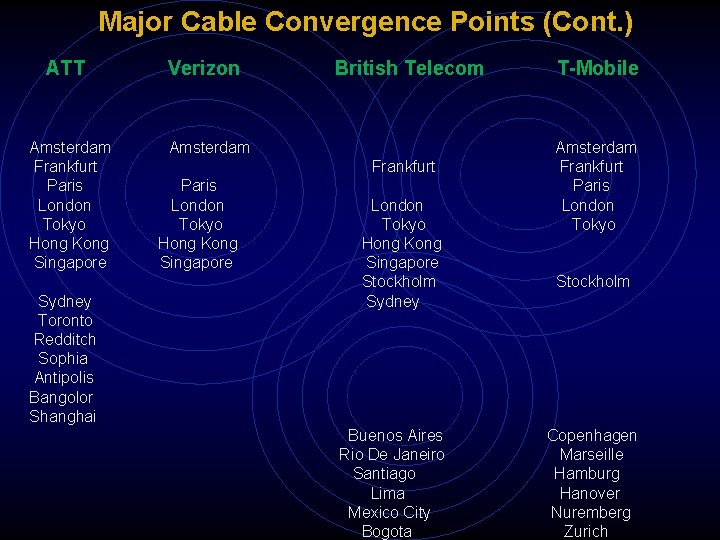
Major Cable Convergence Points (Cont. ) ATT Verizon Amsterdam Frankfurt Paris London Tokyo Hong Kong Singapore Sydney Toronto Redditch Sophia Antipolis Bangolor Shanghai British Telecom T-Mobile Amsterdam Frankfurt Paris London Tokyo Hong Kong Singapore Stockholm Sydney Buenos Aires Rio De Janeiro Santiago Lima Mexico City Bogota Amsterdam Frankfurt Paris London Tokyo Stockholm Copenhagen Marseille Hamburg Hanover Nuremberg Zurich
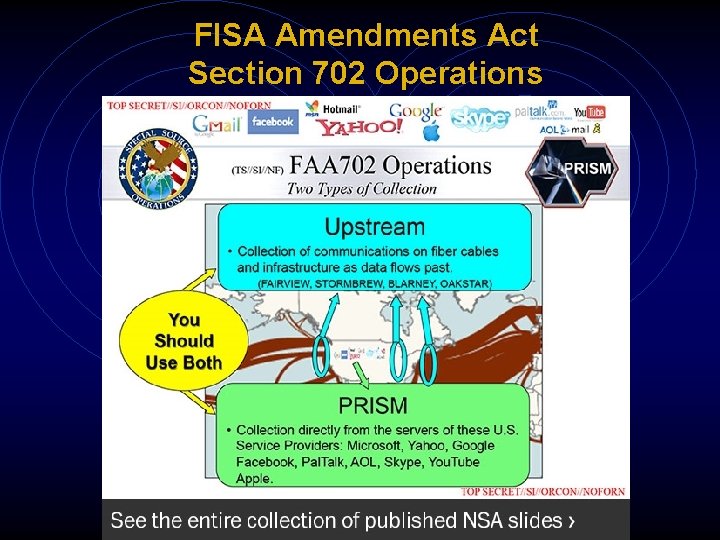
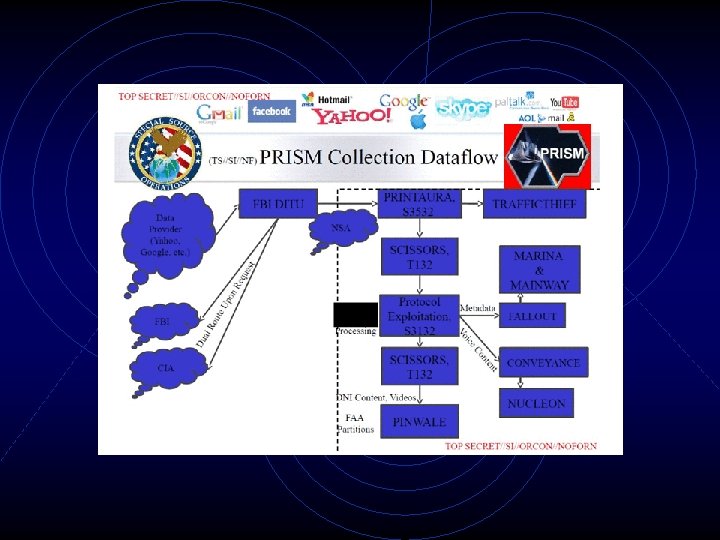
FISA Amendments Act Section 702 Operations

FAIRVIEW Sites
3 Global Public Service Telephone Network Switching System
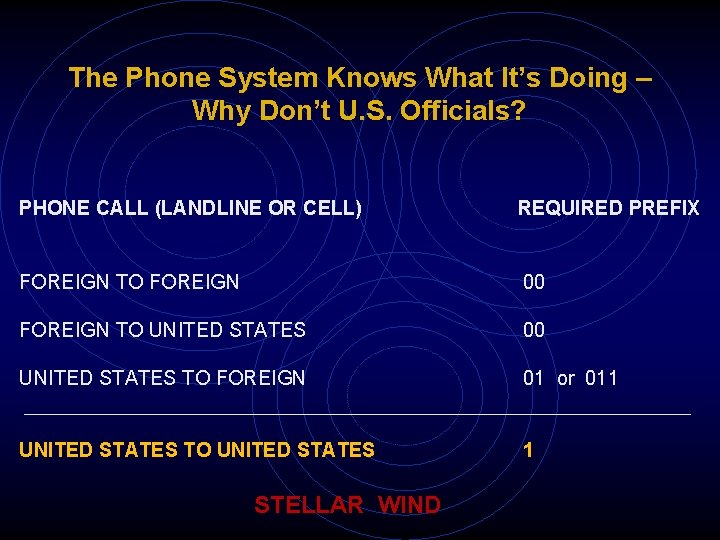
The Phone System Knows What It’s Doing – Why Don’t U. S. Officials? PHONE CALL (LANDLINE OR CELL) REQUIRED PREFIX FOREIGN TO FOREIGN 00 FOREIGN TO UNITED STATES 00 UNITED STATES TO FOREIGN 01 or 011 UNITED STATES TO UNITED STATES 1 STELLAR WIND
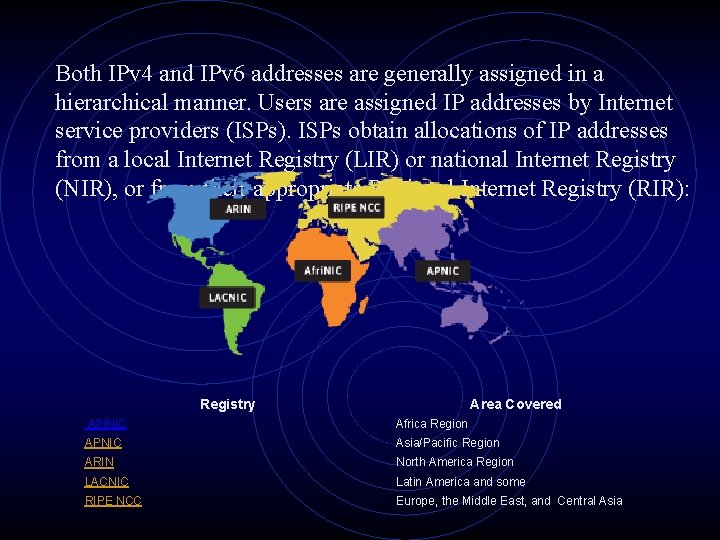
Both IPv 4 and IPv 6 addresses are generally assigned in a hierarchical manner. Users are assigned IP addresses by Internet service providers (ISPs). ISPs obtain allocations of IP addresses from a local Internet Registry (LIR) or national Internet Registry (NIR), or from their appropriate Regional Internet Registry (RIR): Registry Area Covered Afri. NIC Africa Region APNIC Asia/Pacific Region ARIN North America Region LACNIC Latin America and some RIPE NCC Europe, the Middle East, and Central Asia
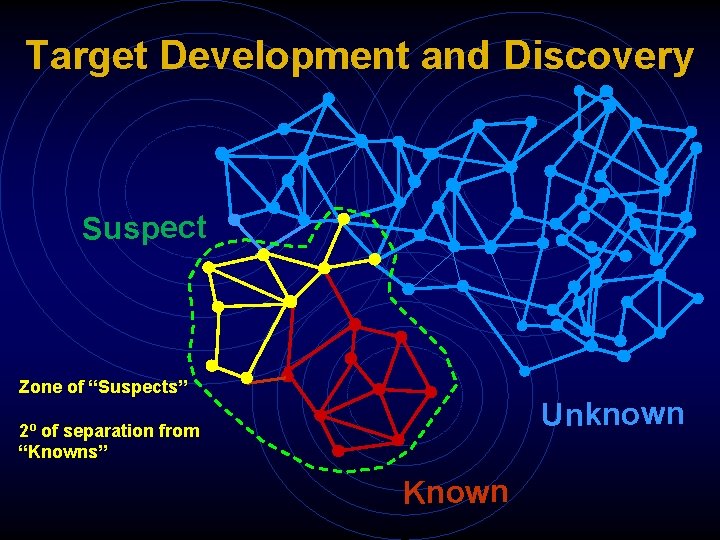
Target Development and Discovery Suspect Zone of “Suspects” Unknown 2º of separation from “Knowns” Known
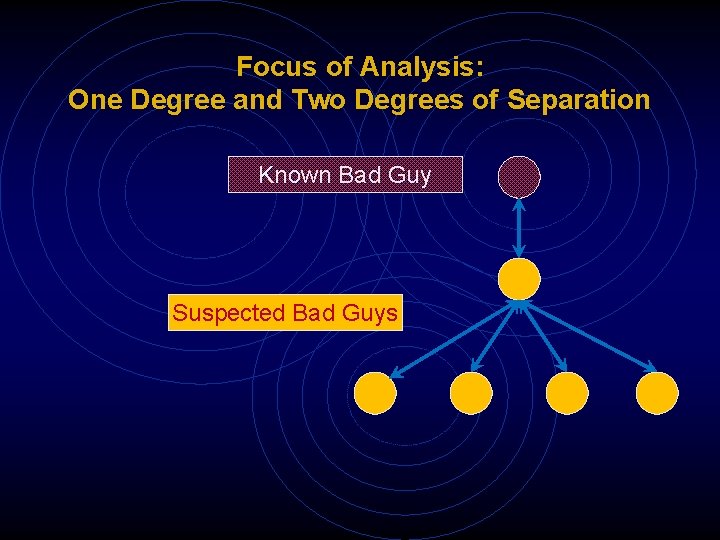
Focus of Analysis: One Degree and Two Degrees of Separation Known Bad Guy Suspected Bad Guys
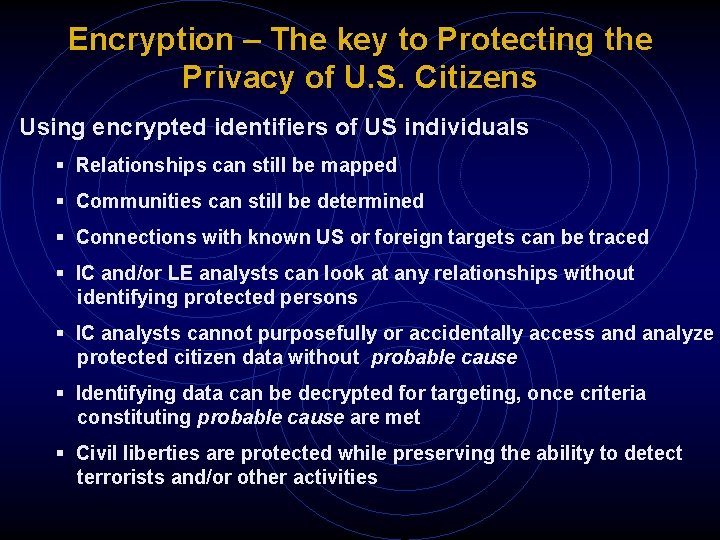
Encryption – The key to Protecting the Privacy of U. S. Citizens Using encrypted identifiers of US individuals § Relationships can still be mapped § Communities can still be determined § Connections with known US or foreign targets can be traced § IC and/or LE analysts can look at any relationships without identifying protected persons § IC analysts cannot purposefully or accidentally access and analyze protected citizen data without probable cause § Identifying data can be decrypted for targeting, once criteria constituting probable cause are met § Civil liberties are protected while preserving the ability to detect terrorists and/or other activities
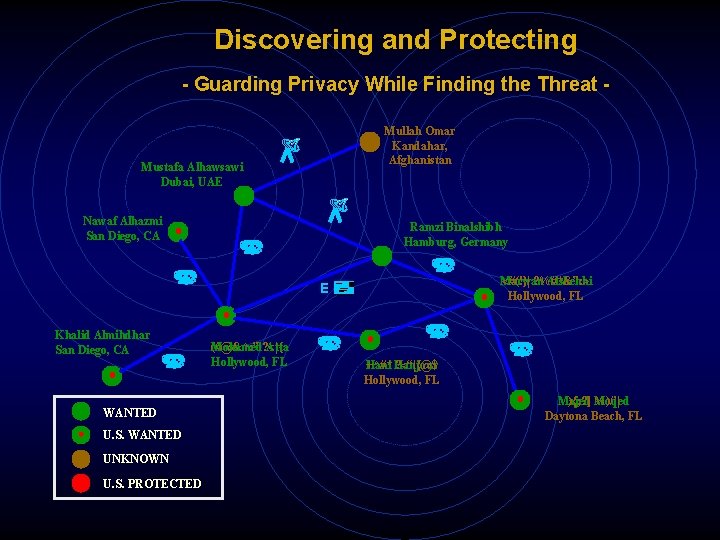
Discovering and Protecting - Guarding Privacy While Finding the Threat - Mullah Omar Kandahar, Afghanistan Mustafa Alhawsawi Dubai, UAE Nawaf Alhazmi San Diego, CA Ramzi Binalshibh Hamburg, Germany Marwan Alshehhi <#(!}| ? %#*&”: > Hollywood, FL E Khalid Almihdhar San Diego, CA WANTED U. S. WANTED UNKNOWN U. S. PROTECTED Mohamed Atta (#@&^: ” ? <|{ Hollywood, FL Hani Hanjour +^#* ? <“|{@$ Hollywood, FL Majed Moqed ){; ? ] %)/’| Daytona Beach, FL
Community Transaction Timeline
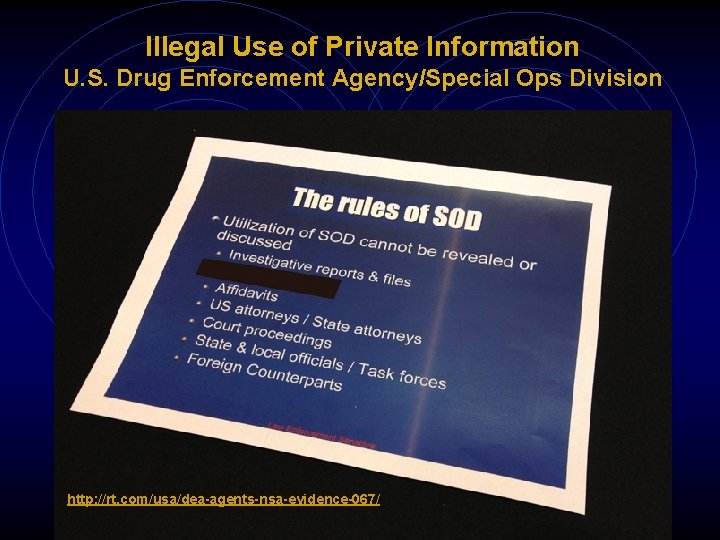
Illegal Use of Private Information U. S. Drug Enforcement Agency/Special Ops Division http: //rt. com/usa/dea-agents-nsa-evidence-067/
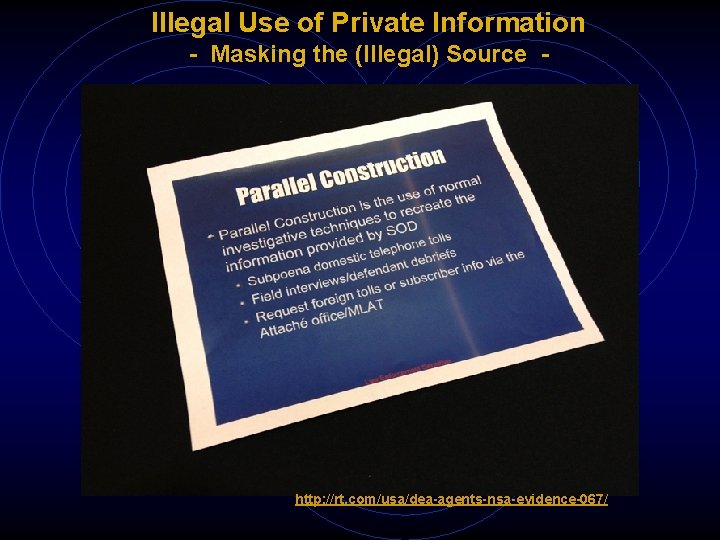
Illegal Use of Private Information - Masking the (Illegal) Source - http: //rt. com/usa/dea-agents-nsa-evidence-067/
- Slides: 21