Mahdi The Messiah CPSC 620 Akash Mudubagilu Arindam
Mahdi The “Messiah” (CPSC 620) Akash Mudubagilu Arindam Gupta
Agenda • Computer Trojan • Mahdi • What makes it special • Mahdi Targets • Effects • How to remove • References
What is Trojan ? • A Trojan is a program that may appear to be legitimate, but in fact does something malicious. • Destructive program • steals information or harms the system • Does not replicate
Mahdi • Also known as Madi • Data-stealing Trojan • Attack relies on social engineering techniques to get onto targeted computers. • Records • • Keystrokes Screen shots Audio Steal text and image files
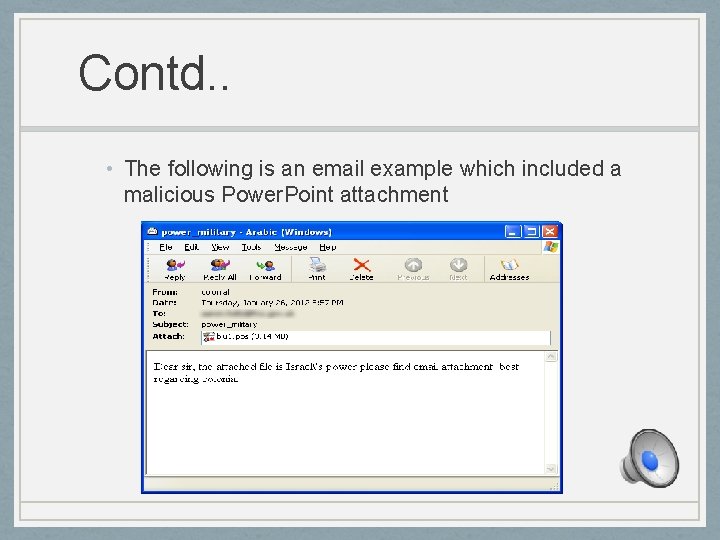
Contd. . • The following is an email example which included a malicious Power. Point attachment
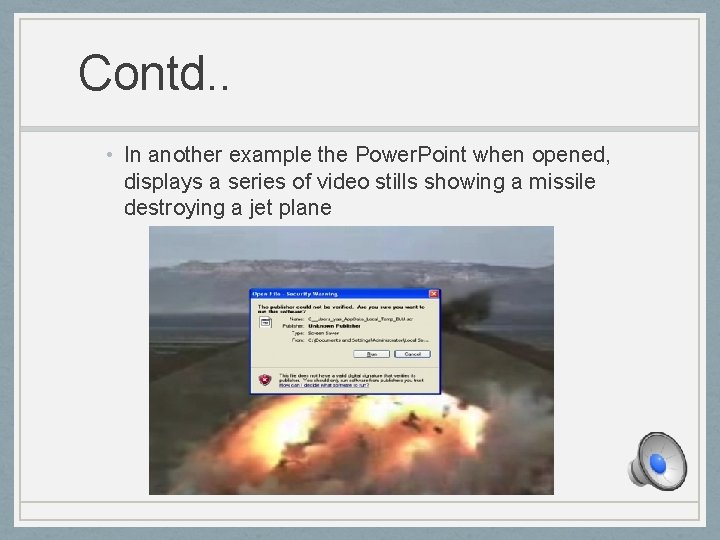
Contd. . • In another example the Power. Point when opened, displays a series of video stills showing a missile destroying a jet plane
What makes it special ? • Reference in the code to the word for the Islamic Messiah. • Use of Farsi Language. • Persian calendar format. • It can update itself. • The creators are still at work • Always takes latest code definition.
Contd. . • Communicates with command-control server • Uploads stolen data • Gets instructions from the server

Mahdi targets • Critical infrastructure firms • Engineering students, • Financial services firms • Government embassies located in Middle Eastern countries, with the majority of the infections in Iran. • Also been found in countries like United States and New Zealand.
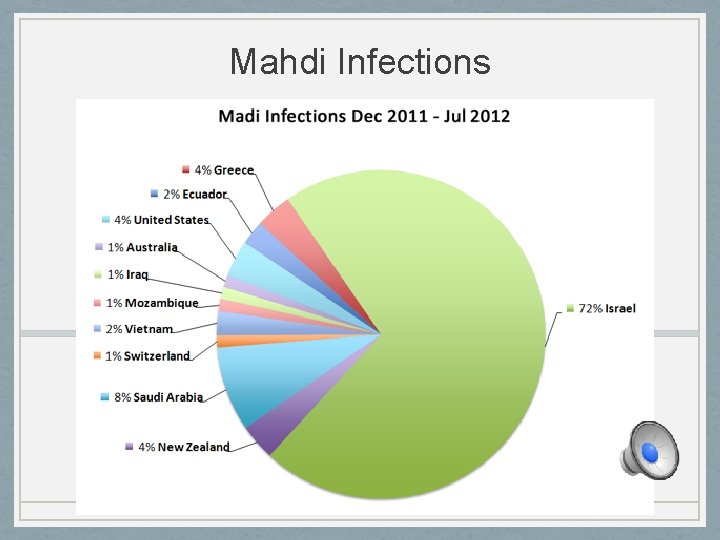
Mahdi Infections
Effects • Google and Yahoo searches are redirected. • Desktop background image and browser homepage settings changed. • Slows down the computer considerably. • Will get unwanted pop-ups. Also corrupts windows registry and uses it to deploy annoying pop-ups. • Large amount of data uploaded. • Might make the internet connection slow. • Uploads sensitive information to server.
How to Remove • Auto- Removal • System Restore. • Install a tool to remove the malware. • Manual Removal • Stop Mahdi process from Task Manager. • Uninstall Mahdi from Control Panel, Add/Remove programs. • Open windows registry, find and remove all Mahdi registry files. • Delete all Mahdi related files from the computer.
References • http: //news. cnet. com/8301 -1009_3 -57503949 -83/a-whos-whoof-mideast-targeted-malware/ • http: //news. cnet. com/8301 -1009_3 -57474405 -83/mahdimessiah-malware-targeted-israel-iran-pcs/ • http: //blog. seculert. com/2012/07/mahdi-cyberwar-savior. html • http: //www. symantec. com/connect/blogs/madi-attacks-seriessocial-engineering-campaigns • http: //www. nextgov. com/cybersecurity/2012/08/mahdi-spywareoperation-broadens-middle-east/57761/? oref=ng-channelriver • http: //www. reuters. com/article/2012/08/29/us-cybersecuritymiddleeast-id. USBRE 87 S 0 EK 20120829
- Slides: 13