MACAW A Media Access Protocol for Wireless LANs

- Slides: 22
MACAW: A Media Access Protocol for Wireless LAN’s Smita Vemulapalli Sandeep Kakumanu
Introduction n This paper describes a MAC protocol for a single channel wireless LAN, developed at Xerox Corporation, Palo Alto. MACAW is an improvement over another MAC protocol named MACA. This protocol uses an RTS-CTS-DS-DATAACK message exchange and a backoff algorithm.
How is a wireless MAC different from a wired one? 1. 2. 3. 4. Contention is at the receiver and not the sender (Hence, CSMA inappropriate). Congestion is location dependent. Learning about congestion levels must be a collective enterprise. Synchronization information about contention periods should be available at all nodes.
The Xerox setup n n 5 MHz “near-field” radio technology - its low operating frequency eliminates multi path effects – suitable for indoor wireless LANs. Infrastructure consists of “base stations”, installed in the ceiling and “pads”, which are like the wireless LAN cards. Single 256 kbps channel - all the wireless communication occurs between a pad and a base station. The base stations are connected by an Ethernet.
Issues in wireless Media Access n n n “Collision” – receiver is in range of two transmitters and is unable cleanly receive signal from either station. “Capture” – receiver is in range of two transmitters but is able to receive signal from closer station. “Interference” – receiver is in range of one transmitter and slightly out of range of another, but is unable to cleanly receive the closer station signal because of interfering presence of the other.
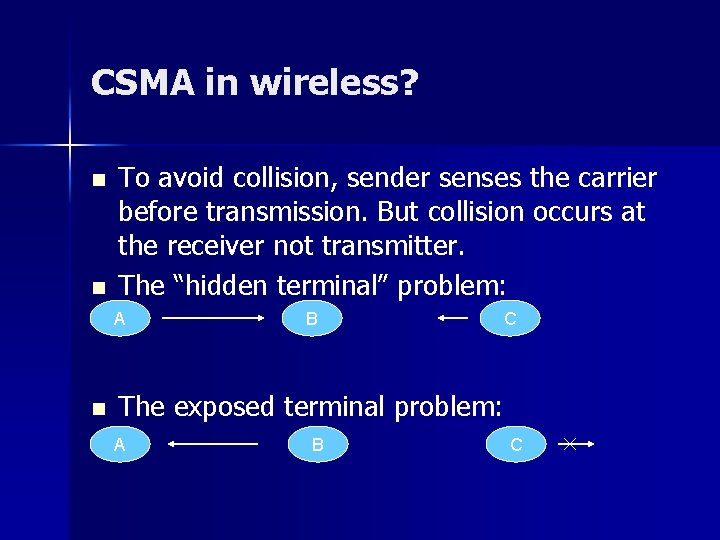
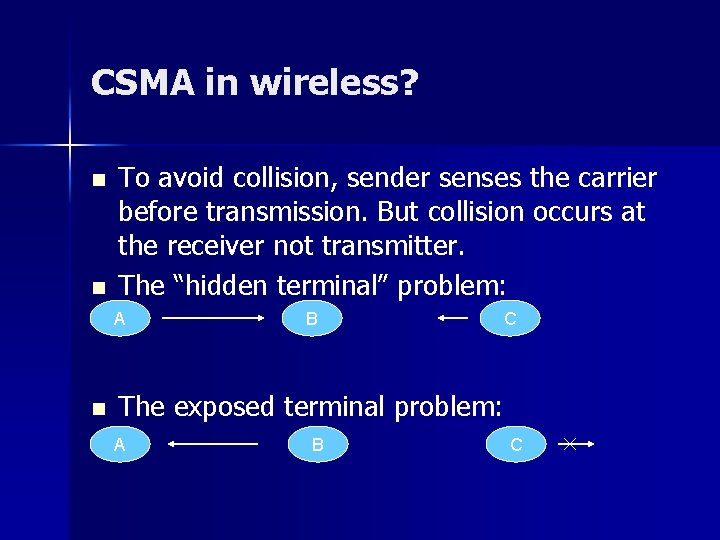
CSMA in wireless? n n To avoid collision, sender senses the carrier before transmission. But collision occurs at the receiver not transmitter. The “hidden terminal” problem: A n B C The exposed terminal problem: A B C
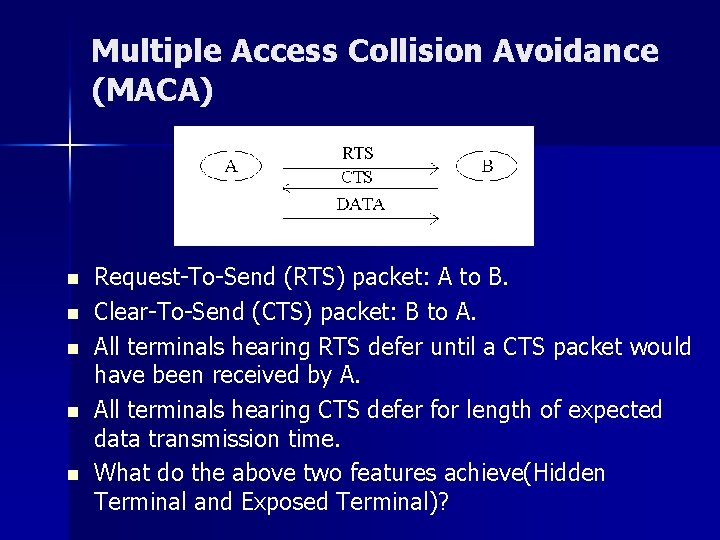
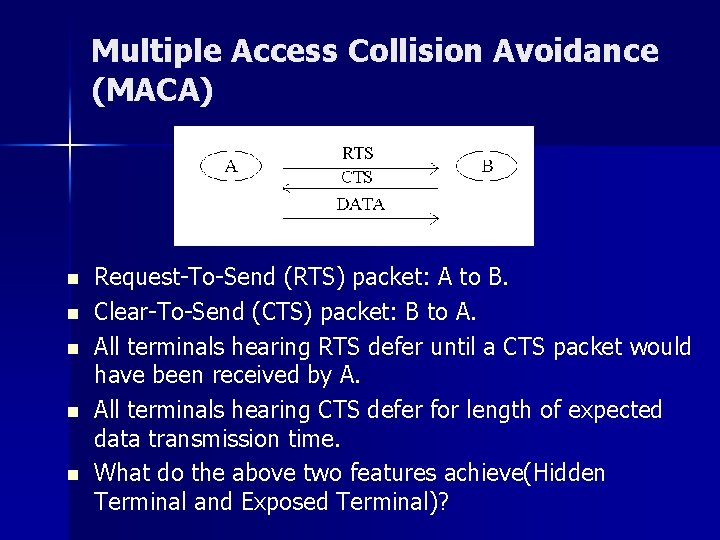
Multiple Access Collision Avoidance (MACA) n n n Request-To-Send (RTS) packet: A to B. Clear-To-Send (CTS) packet: B to A. All terminals hearing RTS defer until a CTS packet would have been received by A. All terminals hearing CTS defer for length of expected data transmission time. What do the above two features achieve(Hidden Terminal and Exposed Terminal)?

MACAW Features Backoff algorithm. Multiple Stream model. Basic Message Exchange n n n – – – ACK DS RRTS
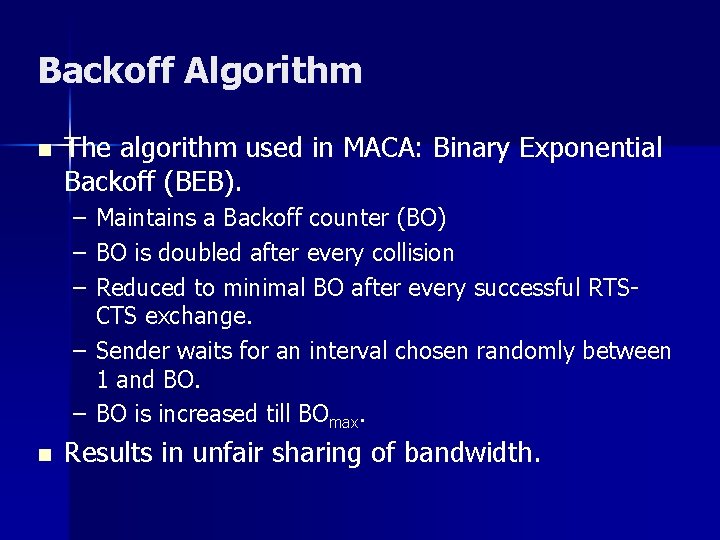
Backoff Algorithm n The algorithm used in MACA: Binary Exponential Backoff (BEB). – – – Maintains a Backoff counter (BO) BO is doubled after every collision Reduced to minimal BO after every successful RTSCTS exchange. – Sender waits for an interval chosen randomly between 1 and BO. – BO is increased till BOmax. n Results in unfair sharing of bandwidth.
Modifications used in MACAW 1. After every successful transmission all pads are made to have the same BO. (What is the problem with this? ). 2. Gentler adjustment (MILD): • • Upon collision Finc(x) = MIN [ 1. 5 x, BOmax]. Upon success Fdec(x) = MAX [ x-1, BOmin].
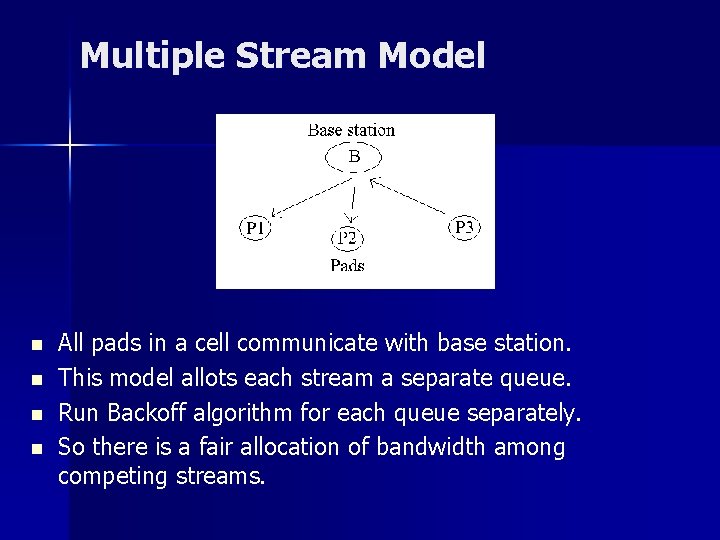
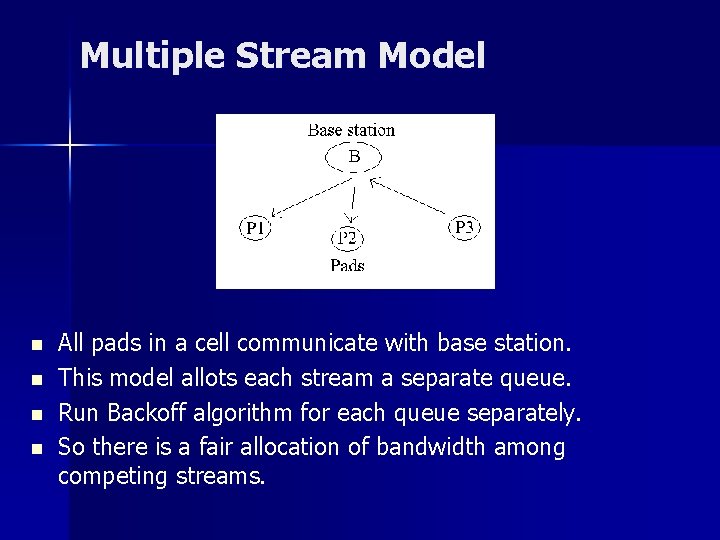
Multiple Stream Model n n All pads in a cell communicate with base station. This model allots each stream a separate queue. Run Backoff algorithm for each queue separately. So there is a fair allocation of bandwidth among competing streams.
Basic Message Exchange 1. ACK – Reliability at link layer. – TCP timeouts will result in huge delays for retransmissions. – Receiver sends ACK to the sender once DATA is received. – When ACK is lost sender sends a new RTS for retransmission and receiver returns an ACK instead of a CTS.
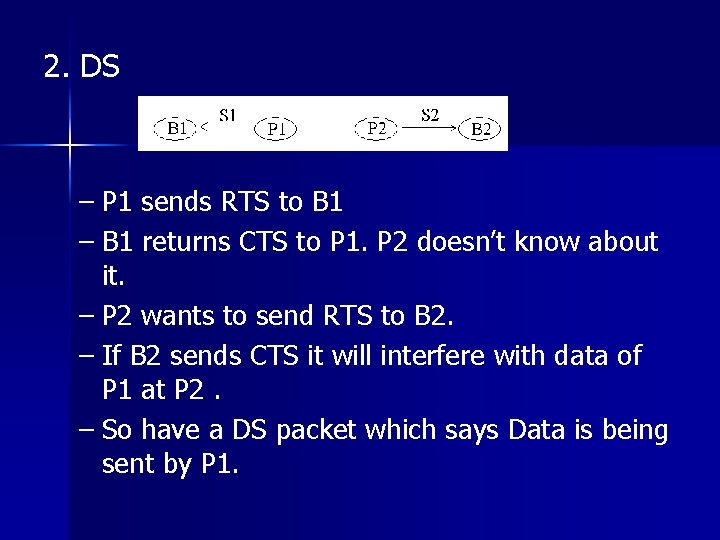
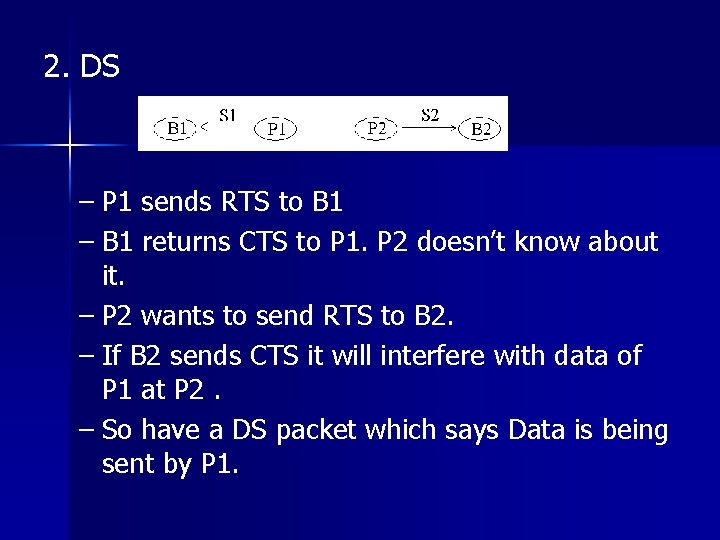
2. DS – P 1 sends RTS to B 1 – B 1 returns CTS to P 1. P 2 doesn’t know about it. – P 2 wants to send RTS to B 2. – If B 2 sends CTS it will interfere with data of P 1 at P 2. – So have a DS packet which says Data is being sent by P 1.
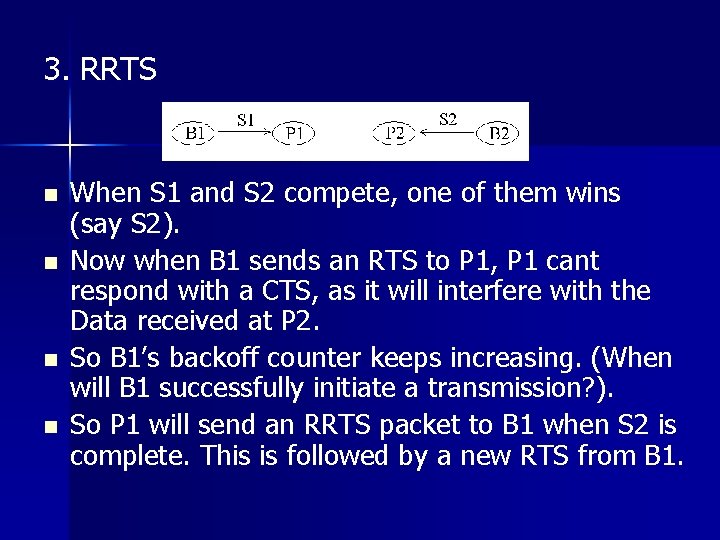
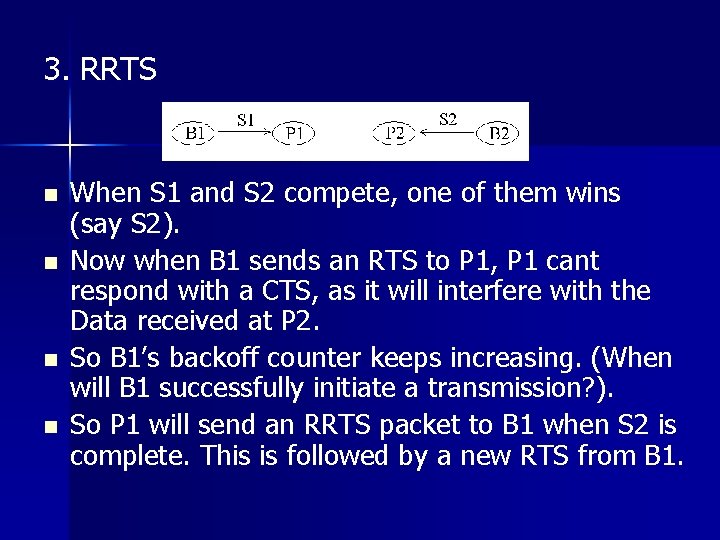
3. RRTS n n When S 1 and S 2 compete, one of them wins (say S 2). Now when B 1 sends an RTS to P 1, P 1 cant respond with a CTS, as it will interfere with the Data received at P 2. So B 1’s backoff counter keeps increasing. (When will B 1 successfully initiate a transmission? ). So P 1 will send an RRTS packet to B 1 when S 2 is complete. This is followed by a new RTS from B 1.
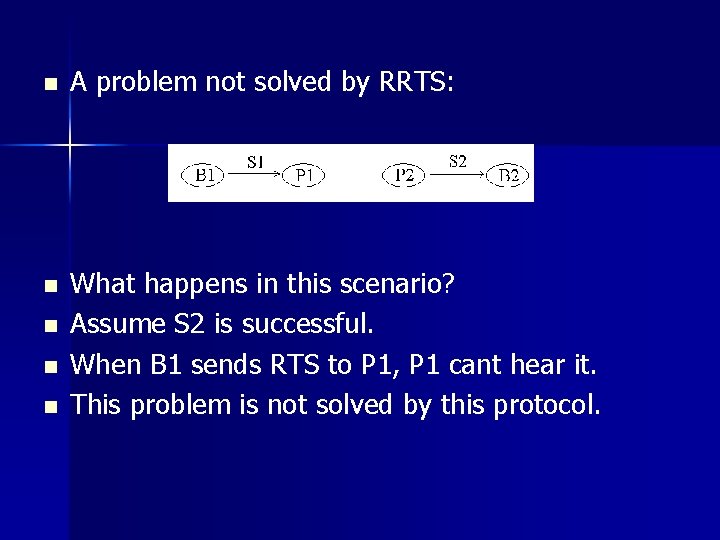
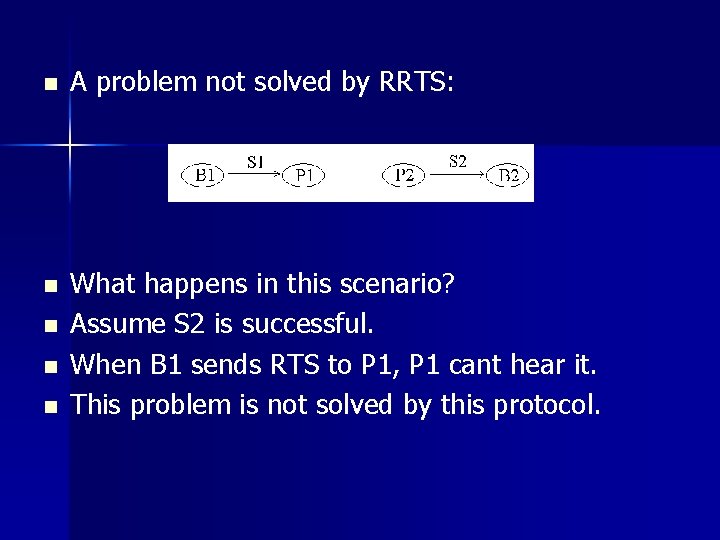
n A problem not solved by RRTS: n What happens in this scenario? Assume S 2 is successful. When B 1 sends RTS to P 1, P 1 cant hear it. This problem is not solved by this protocol. n n n
4. Multicast n n n Sender has to send to more than one receiver. What problems can you expect? The CTS of different receivers will collide. So basically don’t send CTS (Just have RTS followed by Data). When RTS is sent the overhearing stations defer for the length of the following data transmissions. But still contention can take place (How? )
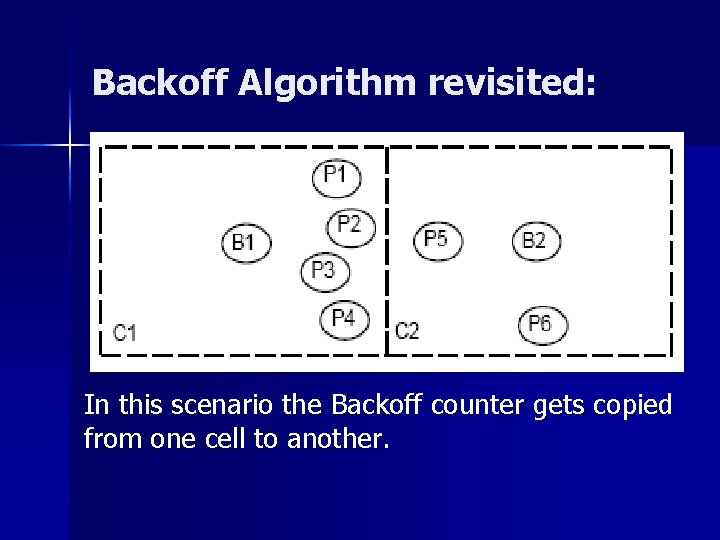
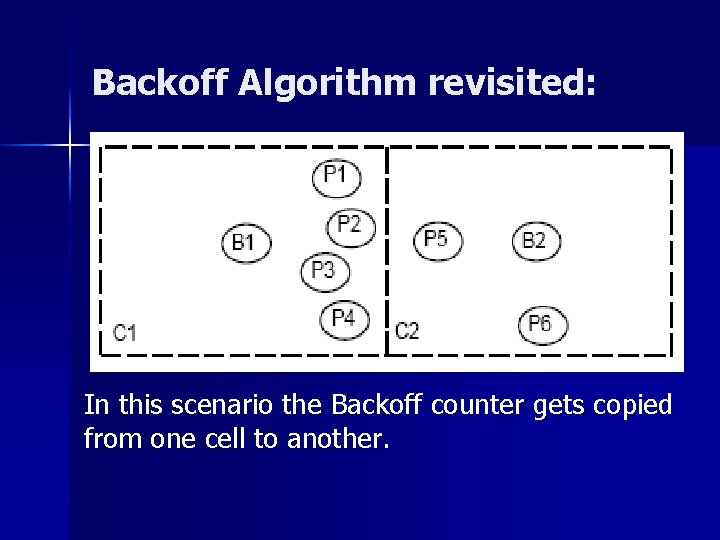
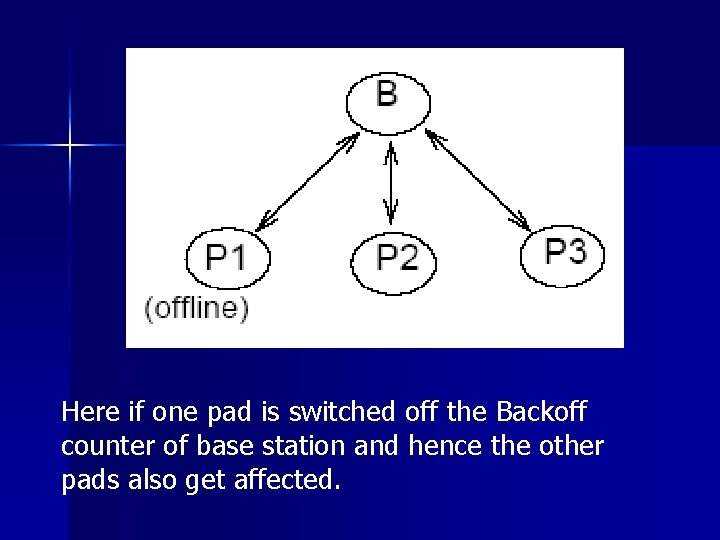
Backoff Algorithm revisited: In this scenario the Backoff counter gets copied from one cell to another.
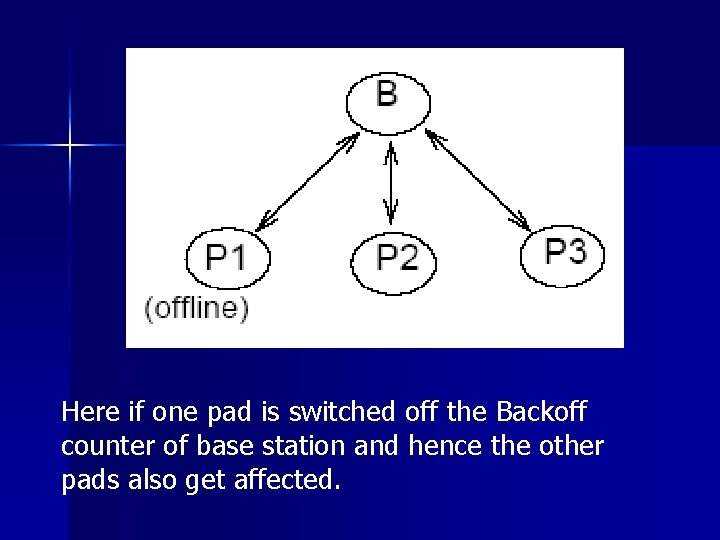
Here if one pad is switched off the Backoff counter of base station and hence the other pads also get affected.
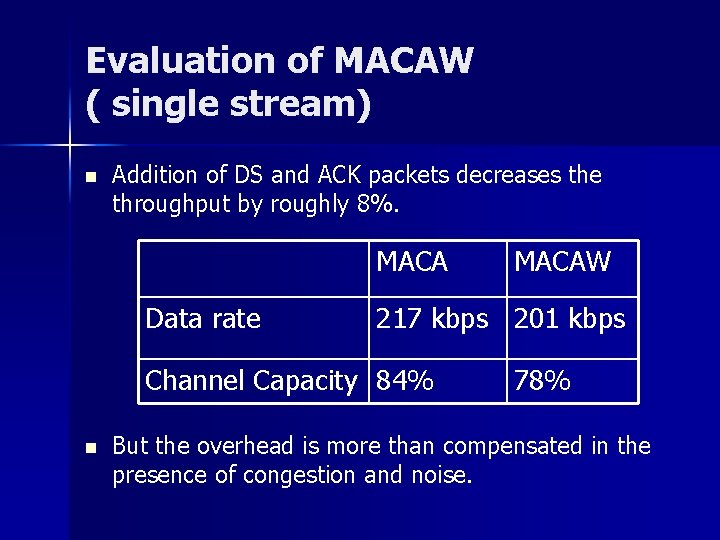
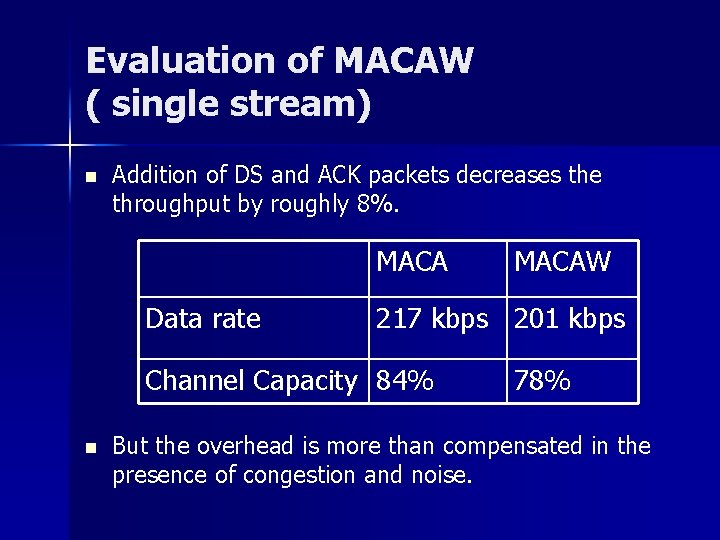
Evaluation of MACAW ( single stream) n Addition of DS and ACK packets decreases the throughput by roughly 8%. MACA Data rate 217 kbps 201 kbps Channel Capacity 84% n MACAW 78% But the overhead is more than compensated in the presence of congestion and noise.
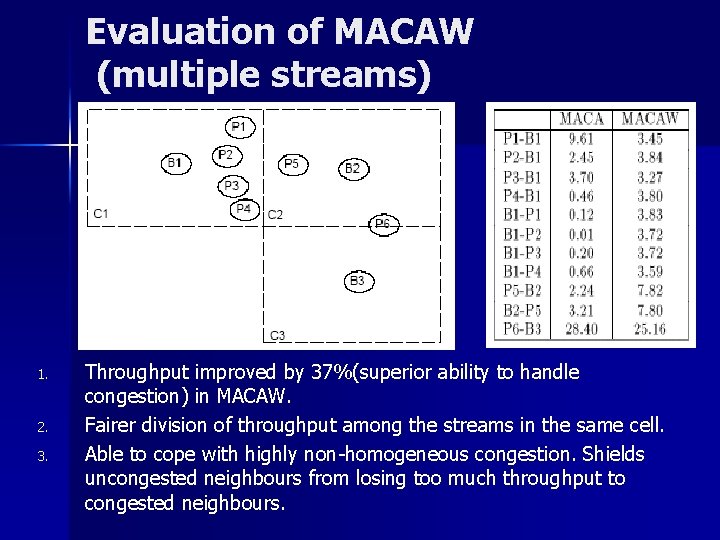
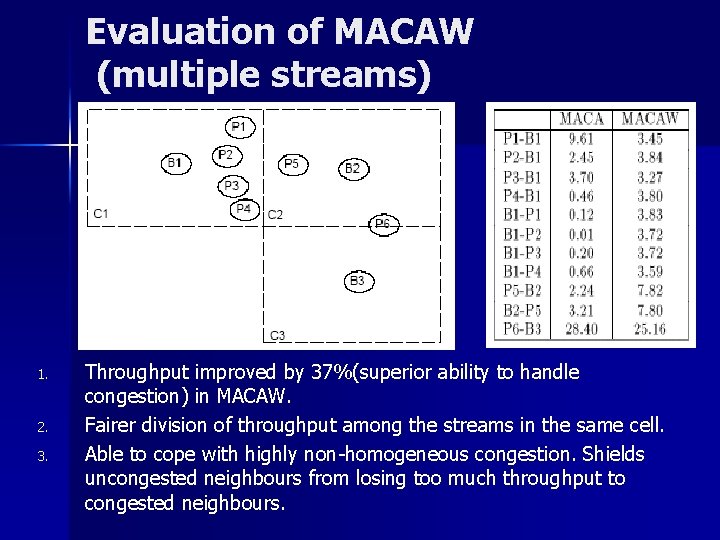
Evaluation of MACAW (multiple streams) 1. 2. 3. Throughput improved by 37%(superior ability to handle congestion) in MACAW. Fairer division of throughput among the streams in the same cell. Able to cope with highly non-homogeneous congestion. Shields uncongested neighbours from losing too much throughput to congested neighbours.
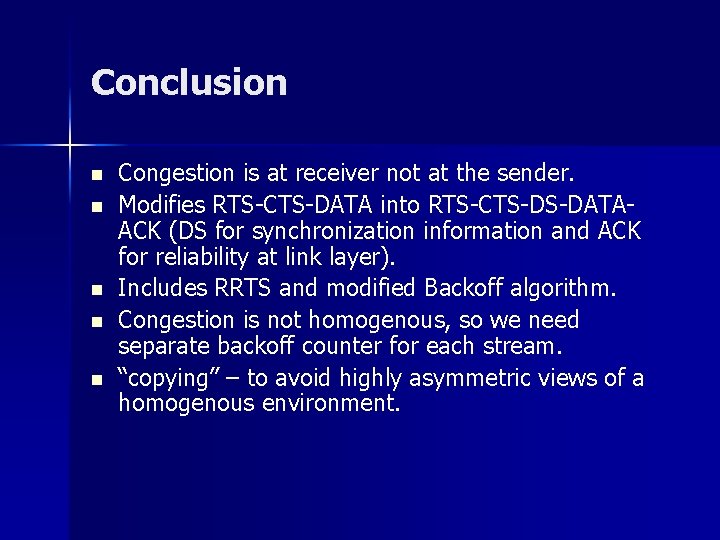
Conclusion n n Congestion is at receiver not at the sender. Modifies RTS-CTS-DATA into RTS-CTS-DS-DATAACK (DS for synchronization information and ACK for reliability at link layer). Includes RRTS and modified Backoff algorithm. Congestion is not homogenous, so we need separate backoff counter for each stream. “copying” – to avoid highly asymmetric views of a homogenous environment.
Critique n n n This is a well written paper. It gives out all the assumptions made and most of the pitfalls of the algorithm. Individual scenarios are analyzed in detail. This protocol is based on the Xerox setup and includes assumptions of the physical layer like exponential decay of signals. It does not solve all the media access problems of the wireless environment: multicast scenario, the scenario where RTS couldn’t be heard.