Luxury Luxury Dispensable q INESSENTIAL q SUPPLEMENTAL q
Luxury

Luxury = Dispensable q INESSENTIAL q SUPPLEMENTAL q EXPENSIVE

Cyber Security is No Longer a Luxury

LYUBOMIR IVANOV • Software Engineer @ Paysafe • Technical Trainer • Security Enthusiast
Agenda q Recent Cyber Security Issues q Cyber Security Trends and Threats in Industrial Control Systems q Rules of Thumb
What happened recently?

Denial of Service attacks

GITHUB q Publicly available third party servers used to conduct the attack q In fact you can find 58486 on the link below https: //github. com/Sec. Ops-Institute/memcached-server-iplist/blob/master/memcached-servers. txt

DYN q Botnet of Io. T devices (CCTV cameras, baby phones, toasters, fridges, etc. ) q Disrupted major world-wide services such as: Twitter q Amazon q Pay. Pal q Netflix q

Viruses/worms
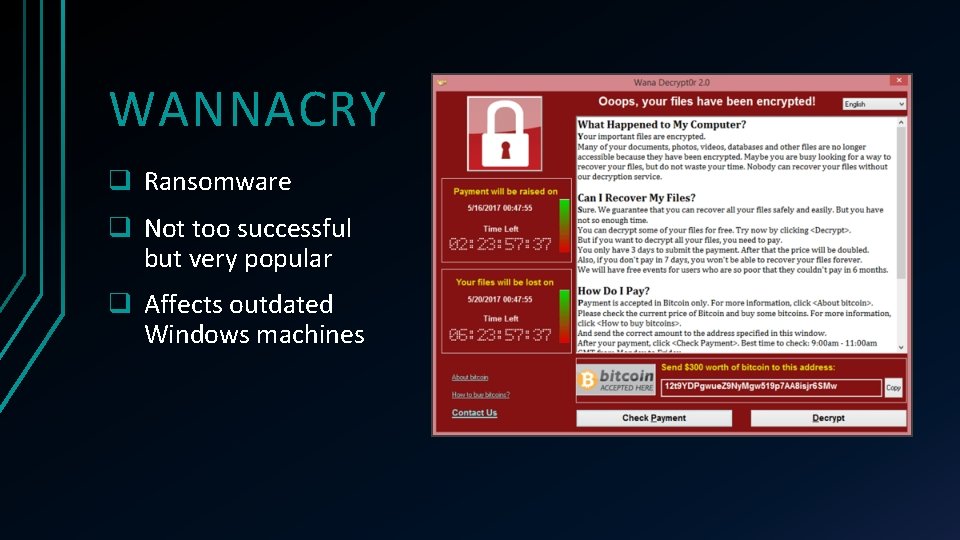
WANNACRY q Ransomware q Not too successful but very popular q Affects outdated Windows machines
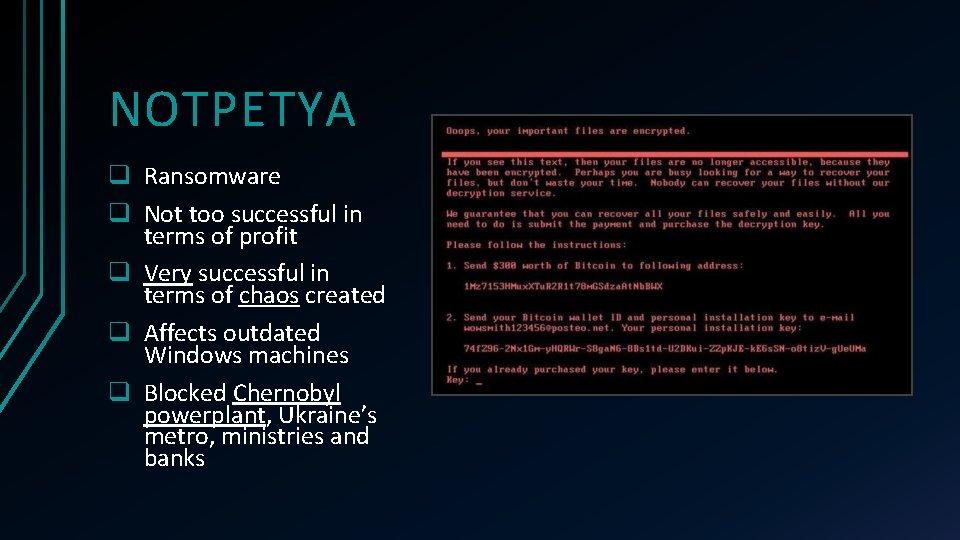
NOTPETYA q Ransomware q Not too successful in terms of profit q Very successful in terms of chaos created q Affects outdated Windows machines q Blocked Chernobyl powerplant, Ukraine’s metro, ministries and banks

Data breaches
EQUIFAX q 143 million Social Security Numbers leaked q CFO tried to cover up the story and sell shares before acknowledging publicly
MACRON’S AND CLINTON’S CAMPAIGNS q Private email communication leaked
Data misuse
FACEBOOK q 87 million users enhanced profile information shared without consent q Used for targeted advertisement for election campaign q Arguably turned the tides in the US election

Hardware vulnerabilities
SPECTER & MELTDOWN q Allows for a program to read another program’s operational data on the same physical host q Passwords, encryption keys and other sensitive data can be stolen

Cyber Security is a Necessity

Cyber Security – main goals q Confidentiality Information is only available to authorized parties q Integrity Accuracy and completeness of the data and its metadata q Availability A system must provide services whenever requested and only to authorized parties q Non-repudiation No party in a transaction can deny its involvement

Cyber Security in Industrial Control Systems (ICS)

ICS - software trends q Mobility q Remote access q Code modernization q Authentication alternatives
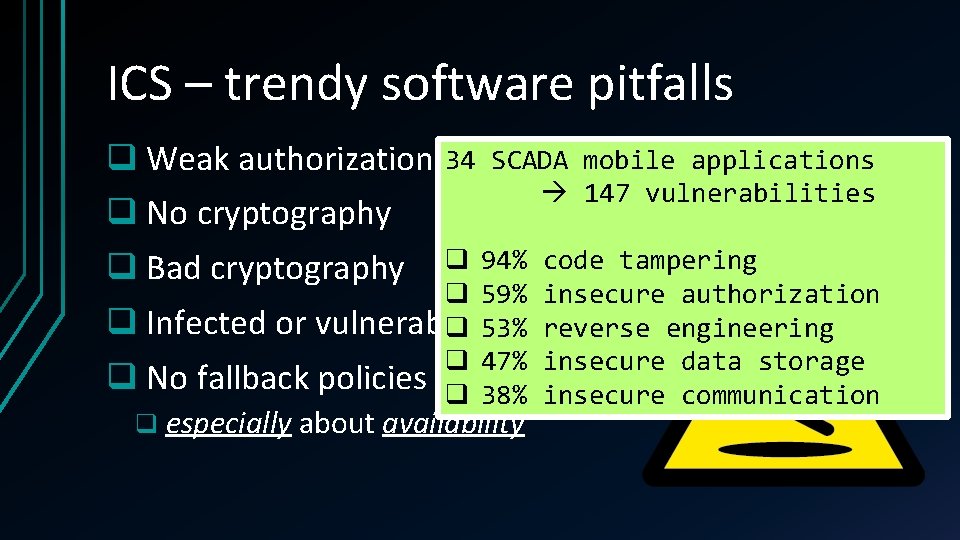
ICS – trendy software pitfalls q Weak authorization 34 q No cryptography SCADA mobile applications 147 vulnerabilities q 94% code tampering q 59% insecure authorization q Infected or vulnerable hosts q software 53% reverse engineering q 47% insecure data storage q No fallback policies q 38% insecure communication q Bad cryptography q especially about availability
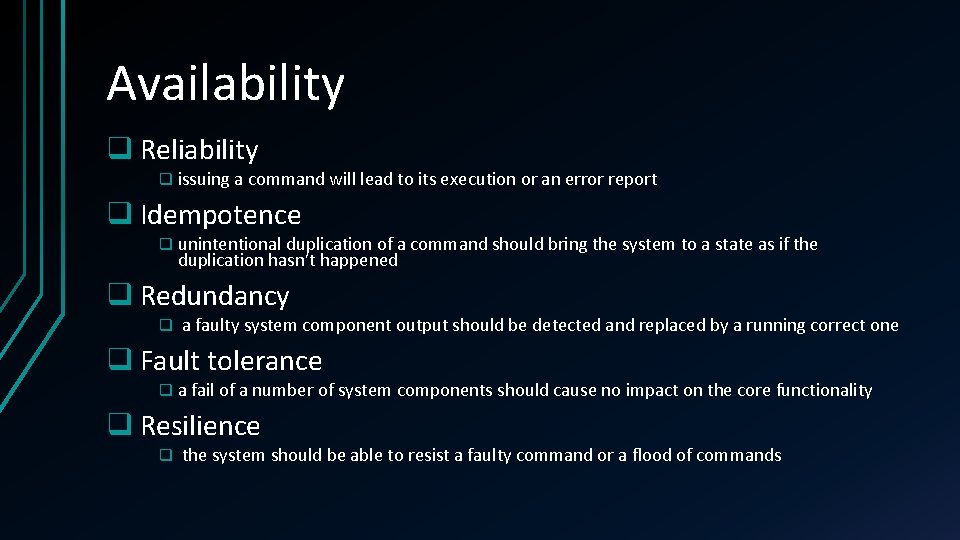
Availability q Reliability q issuing a command will lead to its execution or an error report q Idempotence q unintentional duplication of a command should bring the system to a state as if the duplication hasn’t happened q Redundancy q a faulty system component output should be detected and replaced by a running correct one q Fault tolerance q a fail of a number of system components should cause no impact on the core functionality q Resilience q the system should be able to resist a faulty command or a flood of commands

Cyber Security – how to do it ?

No formula to success
Some good points … q Hire security experts (!) q Cyber security is not only about software q Least privilege principle q What-if analysis q Don’t do your cryptography q N-version programming

Cyber Security is No Longer a Luxury Thank you!
- Slides: 30