Lus Filipe Roque February 19 th 2019 Lus
Luís Filipe Roque February 19 th , 2019
@Luís Roque • ICT Teacher • ICT Coordinator responsible for entire school group • Teachers Trainer 2

Concerns as Citizens 4
Concerns as Teachers 5
How to make a PC safe? A German security specialist presented its already famous "2 rules" of total security
The 2 rules of Herbert Rule number 1 Don´t buy a computer!
The 2 rules of Herbert Rule number 2 If you purchased a computer, do not turn it on!
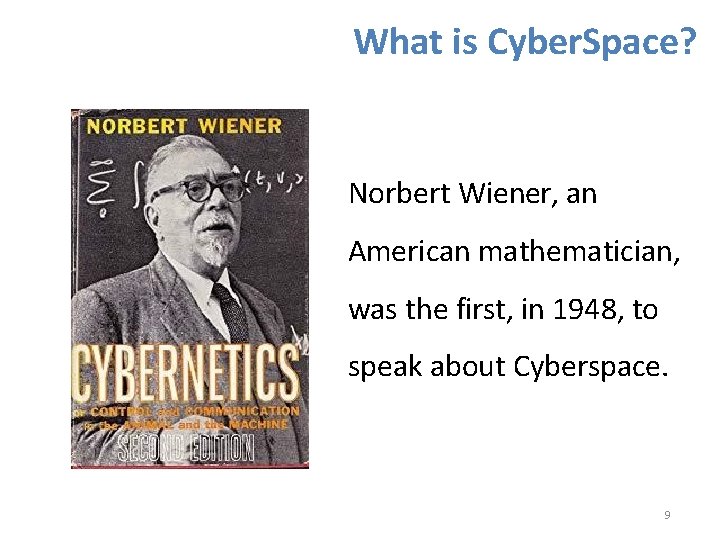
What is Cyber. Space? Norbert Wiener, an American mathematician, was the first, in 1948, to speak about Cyberspace. 9

What is Cyber. Space? Complex environment, values and interests materializing an area of collective responsibility, which results from the interaction between people, information systems, technological equipment and digital networks, including the internet 10
What is Cyber. Security? Set of measures and actions of prevention, monitoring, detection, reaction, analysis and correction which aim to maintain the desired security state and guarantee the confidentiality, integrity and availability of information, digital networks and information systems in cyberspace 11
Dimensions of Safety • Physical Security • Logical Security • Best Practices 12
Physical security How to protect equipment and information against users who do not have authorization to access them. 13
Logic Security A set of resources run to protect the system, data and programs against attempts by unknown people or programs. 14
I have nothing to hide • Automatic access to websites (e. g. Bank accounts ) • Miscellaneous Documents • Conversations with family and friends • Photos • Videos • Lists of passwords … 15

16
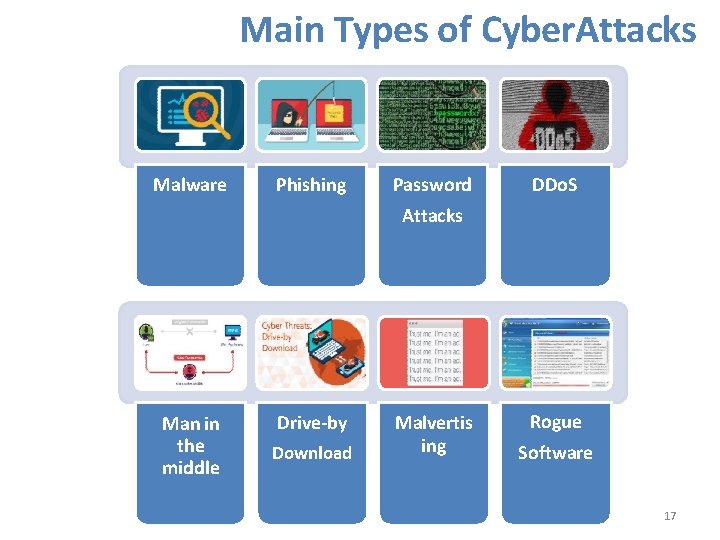
Main Types of Cyber. Attacks Malware Phishing Password DDo. S Attacks Man in the middle Drive-by Download Malvertis ing Rogue Software 17
Malware Malicious software is any part of software that has been written to cause damage to data, devices, or persons 18
Phishing Attacks usually carried out by emails apparently from trusted entities where people are invited to enter sensitive data 19
Passwords Attacks An attempt to obtain or decrypt a user’s password for ilegal use. Hackers can use cracking programs, dictionary attacks, and password sniffers in password attacks. 20
DDo. S Distributed denial of services (DDo. S) attacks are a subclasse of denial of services (Do. S) attacks. A DDo. S attack envolves multiple connected online devices, collectively know as a botnet, wich are used to overwhelm a target website with fake traffic. 21
Man in the middle Form of attack in which the data exchanged between two parties (e. g. you and your bank) are somehow intercepted, recorded and possibly altered by the attacker without the victims noticing 22
Drive-by download Occur when vulnerable computers get infected by just visiting a website. Findings from latest Microsoft Security Intelligence Report and many of its previous volumes reveal that Drive-by Exploits have become the top web security threat to worry about. 23
Malvertising Criminally-controlled adverts which intentionally infect people and businesses. These can be any ad on any site – often ones which you use as part of your everyday Internet usage. 24
Rogue Software Also called smitfraud or scareware, this type of software is defined as malware. It is designed specifically to damage or disrupt a computer system. In this case, not only is the software going to disrupt your system, it´s going to try and trick you into making a purchase using your credit card. 25

26
Do Backup The loss of personal information cause even more problems than the loss of the device itself. So, make sure that all your important information is well stored in various places. 27
Stay up to date Make sure your device's operating systems and applications have up-todate security updates. This prevents software with known vulnerabilities from being abused by cybercriminals. 28
Use Robust Passwords With 10 or more characters Character combination Words with purposeful errors They do not derive from the name of the user or any close relative Not derived from personal information 29
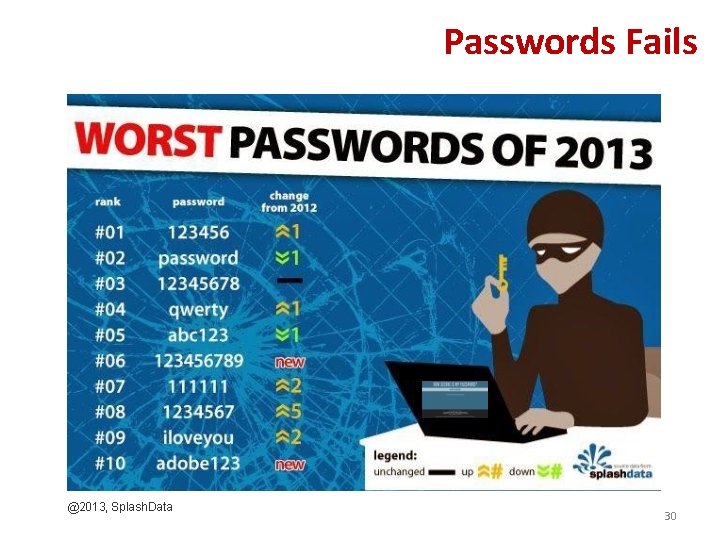
Passwords Fails @2013, Splash. Data 30
Block intruders Regardless of the devices, make sure that your screen is protected with a strong and unique password or PIN code, or one of the biometric authentication methods available, such as fingerprint reader or facial recognition. 31
Reduce Digital Footprint Consider becoming a digital minimalist for a while and leave most of your devices at home. In this way, not only will you have less equipment than you can afford to lose as you are giving less opportunities for personal information being stolen by cybercriminals. 32
Moderate in Social Networks Resist the temptation to share on social networks, for example, that you and your family will be away from home in a certain period of time. Doing so may expose you to a physical intrusion of your home. 33
Browse incognito 34

Use a secure email 35
Beware of Wi-Fi free zones Carefully choose the network Disable file sharing and mark the Wi-Fi connection as a public network Never make updates or install applications using these networks Use two-factor authentication Make sure to log off after accessing any service you have accessed Forget the network after using it 36
Beware of card cloning Card cloning happens when all information about a particular card (your PIN - Personal Identification Number and its number) is copied 37
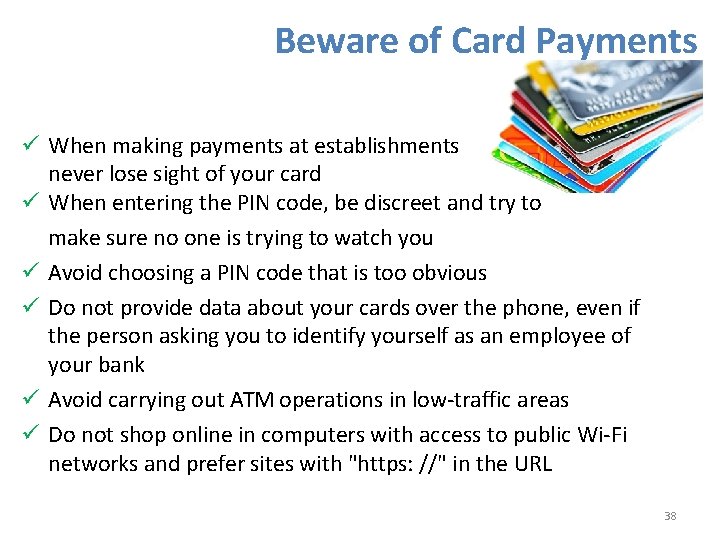
Beware of Card Payments When making payments at establishments never lose sight of your card When entering the PIN code, be discreet and try to make sure no one is trying to watch you Avoid choosing a PIN code that is too obvious Do not provide data about your cards over the phone, even if the person asking you to identify yourself as an employee of your bank Avoid carrying out ATM operations in low-traffic areas Do not shop online in computers with access to public Wi-Fi networks and prefer sites with "https: //" in the URL 38
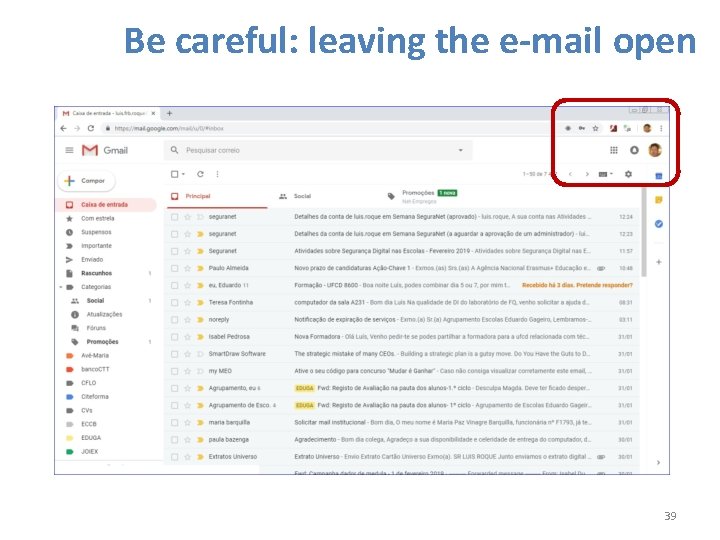
Be careful: leaving the e-mail open 39
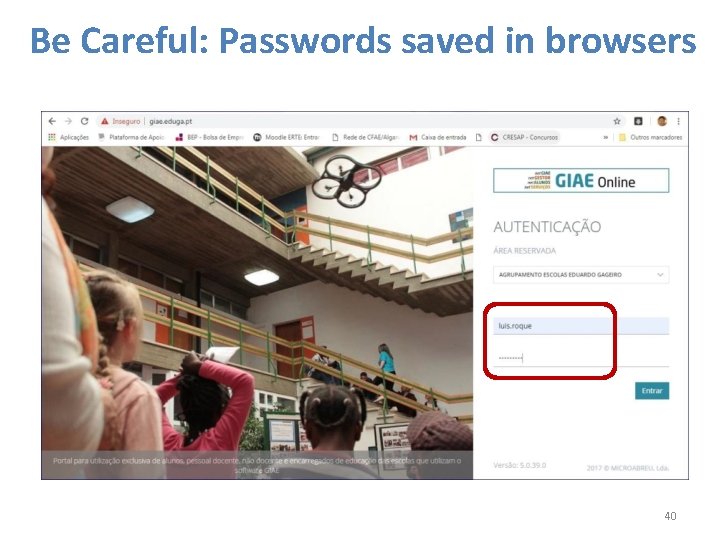
Be Careful: Passwords saved in browsers 40
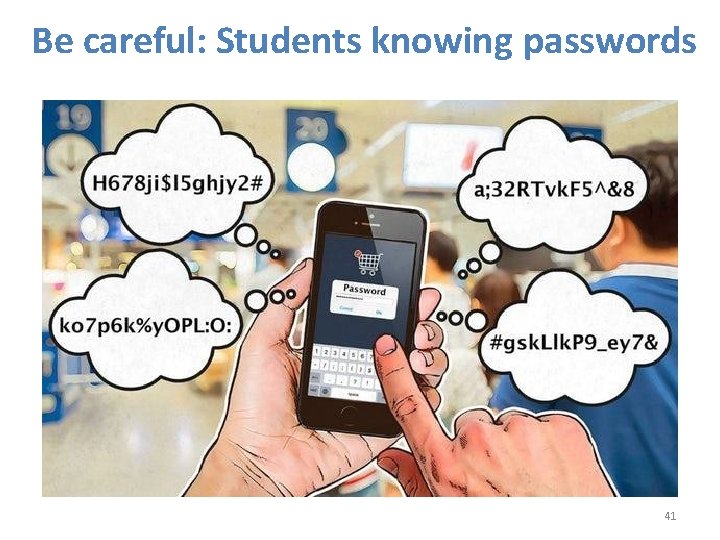
Be careful: Students knowing passwords 41

Be careful: Accessing Insecure Sites 42

Be Careful: Computer Maintenance Companies 43
In Summary +Caution +Safety -Risk -Privacy 44

Thank you 45
- Slides: 45