LISP Multiprovider VPN draftshenlispmultiprovidervpn00 Naiming Shen Dino Farinacci
- Slides: 6
LISP Multiprovider VPN draft-shen-lisp-multiprovider-vpn-00 Naiming Shen, Dino Farinacci IETF 91, Honolulu
Multi-Provider Use Case • With multiple LISP providers each maintain their own mapping database system (MSP) • Providers have their own crypto mechanisms and encryption keys over LISP tunnels • VRF and LISP Instance ID may be used with the LISP tunnels • One VRF site of one provider wants to communicate with another VRF site of a different LISP provider (Inter-Provider VPN) in a secure way • The communication may involve multi-providers 6/11/2021 2
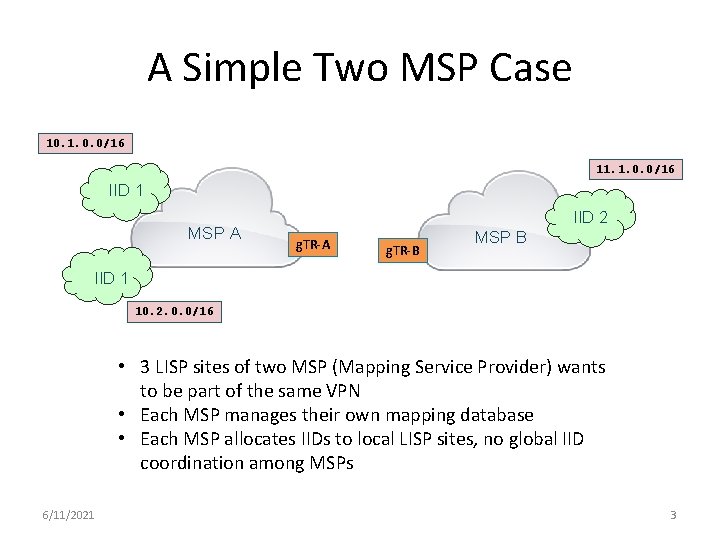
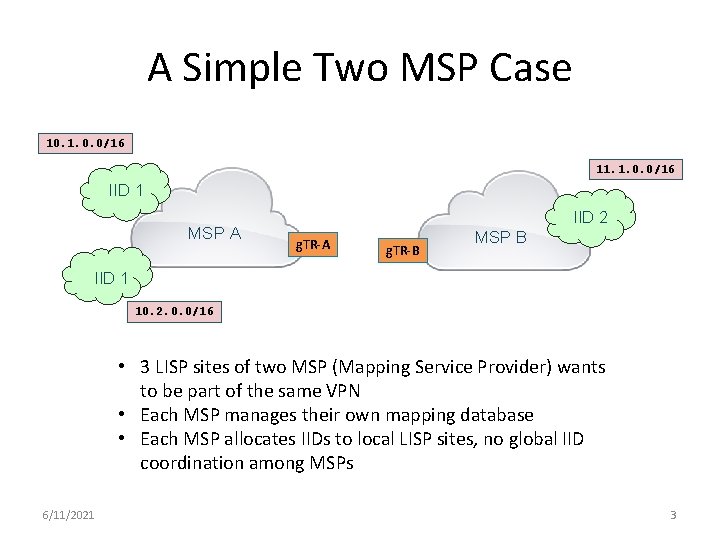
A Simple Two MSP Case 10. 1. 0. 0/16 11. 1. 0. 0/16 IID 1 MSP A IID 2 g. TR-A g. TR-B MSP B IID 1 10. 2. 0. 0/16 • 3 LISP sites of two MSP (Mapping Service Provider) wants to be part of the same VPN • Each MSP manages their own mapping database • Each MSP allocates IIDs to local LISP sites, no global IID coordination among MSPs 6/11/2021 3
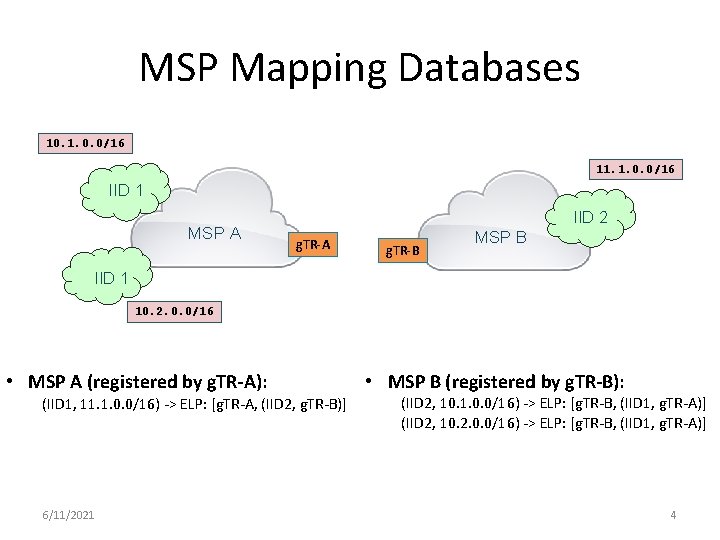
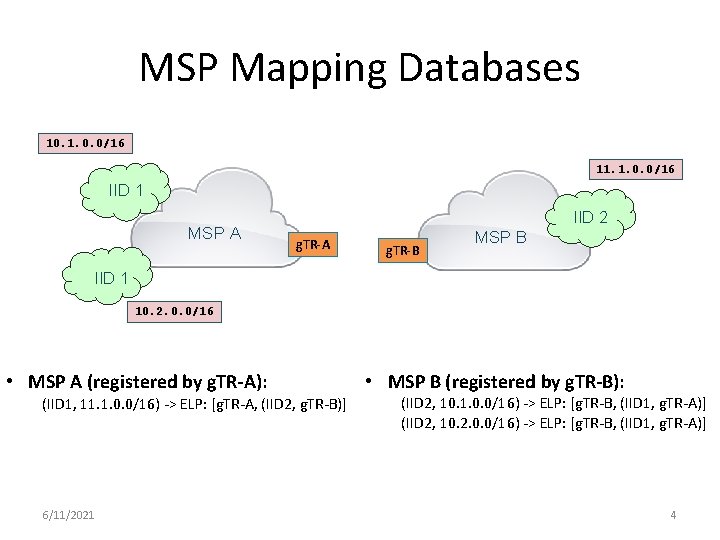
MSP Mapping Databases 10. 1. 0. 0/16 11. 1. 0. 0/16 IID 1 MSP A IID 2 g. TR-A g. TR-B MSP B IID 1 10. 2. 0. 0/16 • MSP A (registered by g. TR-A): (IID 1, 11. 1. 0. 0/16) -> ELP: [g. TR-A, (IID 2, g. TR-B)] 6/11/2021 • MSP B (registered by g. TR-B): (IID 2, 10. 1. 0. 0/16) -> ELP: [g. TR-B, (IID 1, g. TR-A)] (IID 2, 10. 2. 0. 0/16) -> ELP: [g. TR-B, (IID 1, g. TR-A)] 4
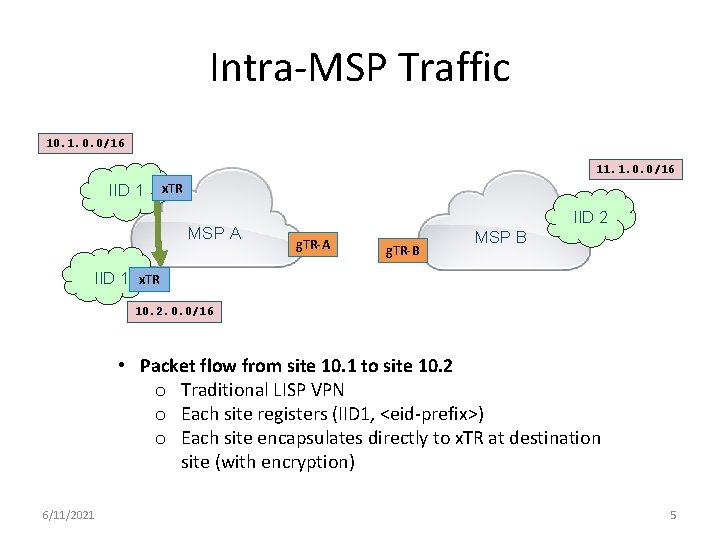
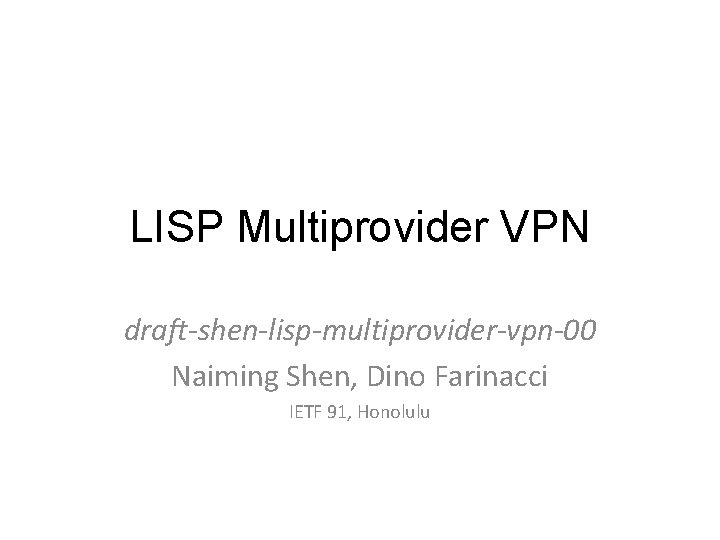
Intra-MSP Traffic 10. 1. 0. 0/16 11. 1. 0. 0/16 IID 1 x. TR MSP A IID 2 g. TR-A g. TR-B MSP B IID 1 x. TR 10. 2. 0. 0/16 • Packet flow from site 10. 1 to site 10. 2 o Traditional LISP VPN o Each site registers (IID 1, <eid-prefix>) o Each site encapsulates directly to x. TR at destination site (with encryption) 6/11/2021 5
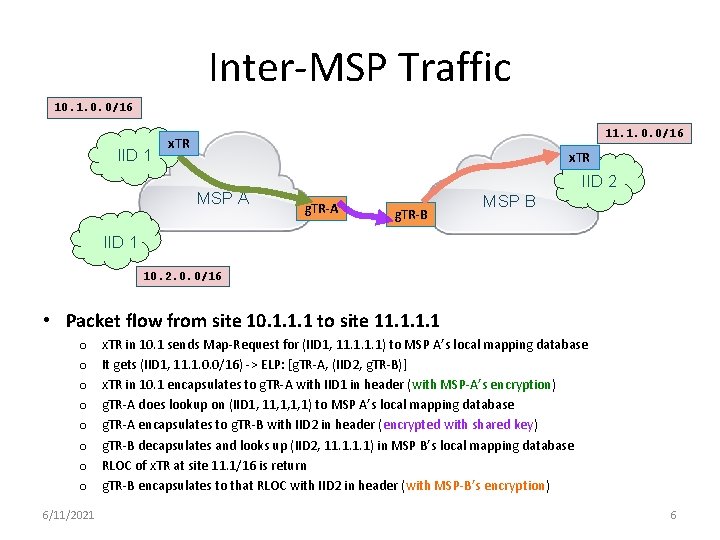
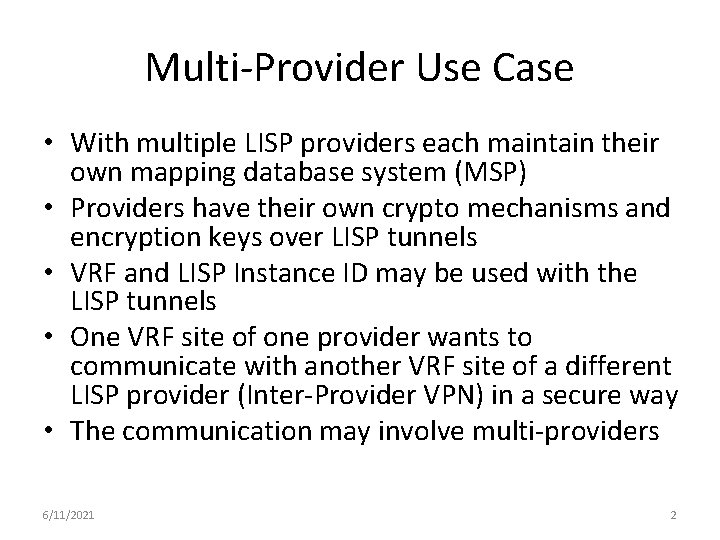
Inter-MSP Traffic 10. 1. 0. 0/16 IID 1 11. 1. 0. 0/16 x. TR MSP A IID 2 g. TR-A g. TR-B MSP B IID 1 10. 2. 0. 0/16 • Packet flow from site 10. 1. 1. 1 to site 11. 1 o o o o 6/11/2021 x. TR in 10. 1 sends Map-Request for (IID 1, 11. 1) to MSP A’s local mapping database It gets (IID 1, 11. 1. 0. 0/16) -> ELP: [g. TR-A, (IID 2, g. TR-B)] x. TR in 10. 1 encapsulates to g. TR-A with IID 1 in header (with MSP-A’s encryption) g. TR-A does lookup on (IID 1, 1, 1, 1) to MSP A’s local mapping database g. TR-A encapsulates to g. TR-B with IID 2 in header (encrypted with shared key) g. TR-B decapsulates and looks up (IID 2, 11. 1) in MSP B’s local mapping database RLOC of x. TR at site 11. 1/16 is return g. TR-B encapsulates to that RLOC with IID 2 in header (with MSP-B’s encryption) 6