LIS 508 using Debian GNULinux Thomas Krichel 2010
LIS 508 using Debian GNU/Linux Thomas Krichel 2010 -01 -10
ssh • The main protocol we use to communicate with the server is the secure shell “ssh”. • The server has to have ssh server software installed. • Any rented server will have this. • Otherwise run “aptitude install opensshserver”
installing putty • Go to your favorite search engine to search for putty. • If you have administrator rights install the installer version. • Since you have already installed winscp, you should have no further problems.
putty options • In the window/translation choose UTF-8, always. • Find out what the size of your screen for the font that you are using, and save that in your session. • For wotan, the port is 22, ssh. • You can choose to disable the annoying bell.
how is ssh secure • ssh uses public key cryptography. • It can cope with serveral crytographic algorithm. The most common one is rsa. • In public key cryptography, you have two keys. • One is the private key. • The second is the public key.
private key • Using the private key, I can decrypt a message that has been encrypted using my public key. • Somebody can check that I am who I claim to be because by keeping the private key private, I am the only one who can decrypt it.
authorizing keys • If you want to give your friend access to an account, you can ask her for her public key. • You will then authorize the public key by storing it in a file with authorized keys. • When an somebody comes along and pretends to be your friend you can challenge her to decode a message encoded with your friends public key.
public key • Using the public key, I can encrypt a message and send it to you. • Once the message is encrypted, I can not decode it any more. The public key can not be used to decode a message. • This is the reason why the encryption key can be made public.
communication with the server • Assume we are using a Microsoft Windows client. • For file editing and manipulation, we use putty. • For file transfer, we use winscp. • Both are available on the web.
password authentication • When we login to a machine, we give a password for the user that we login as. • This a common form of authenticiation. • The idea is that we keep the password secret.
key authenticatiton • ssh uses public key • This a common form of authenticiation. • The idea is that we keep the password secret.
key creation • “ssh-keygen” is the command to use to create a key. Answer all questions with the <ENTER> key. • “cd. ssh” and “ls -l” shows you the contents of the directory. ssh created in the first step. • The file “id_rsa. pub” has your public key.
authorized_keys • In. ssh, you can maintain a file “authorized_keys” that contains the public keys of all users you authorize to access the account, one line per user. • “cp id_rsa. pub authorized_keys” will authorize yourself. Then “ssh user@wotan” will allow you to login again as you on wotan. • You can also create a public key with putty.
issuing commands • While you are logged in, you talk to the computer by issuing commands. • Your commands are read by command line interpreter. • The command line interpreter is called a shell. • You are using the Bourne Again Shell, bash.
bash features • bash allows to browse the command history with the up/down arrow keys. • bash allows to edit commands with the left/right arrow keys. • You can complete command file names with <TAB>. • bash comes with a language of commands that allows to write batch files. • “exit” is the command to leave the shell.
environment variables • These are variables used by the shell. • Two important ones are – $HOME your home directory – $PATH the location where bash will search for executable files. • echo $HOME will show your home directory. • “env” is a command that can be used to see all environment variables.
bash initialization • Files that start with a dot are hidden. They are only seen with “ls -a”. • . bashrc is a file written in bash language that is run every time bash is started. • . bash_profile or. profile is run when the shell is started at login. • You can customize these files.
files, directories and links • Files are continuous chunks data on disks that are required for software applications. • Directories are files that contain other files. Microsoft calls them folders. • In UNIX, the directory separator is “/” • The top directory is “/” on its own.
home directory • When you first log in to wotan you are placed in your home directory /home/username • “cd” is the command that gets you back to the home directory. • The home directory is also abbreviated as “~“ • cd ~user gets you to the home of user. • “cd ~” does what?
~/public_html • The web server on wotan will map requests to http: //wotan. liu. edu/~user to show the file ~user/public_html/index. html • The web server will map requests to http: //wotan. liu. edu/~user/file to show the file ~user/public_html/file • The server will do this by virtue of a configuration option.
changing directory, listing files • “cd directory” changes into the directory • the current directory is “. ” • its parent directory is “. . ” • “ls” lists files
users and groups • “root” is the user name of the superuser. • The superuser has all privileges. • There are other physical users, i. e. persons using the machine • There are users that are virtual, usually created to run a daemon. For example, the web sever in run by a user www-data. • Arbitrary users can be put together in groups.
permission model • Permission of files are given – to the owner of the file – to the group of the file – and to the rest of the world • A group is a grouping of users. Unix allows to define any number of groups and make users a member of it. • The rest of the world are all other users who have access to the system. That includes www-data!
listing files • “ls” lists files • “ls -l” make a long listing. It contains – elementary type and permissions (see next slide) – owner – group – size – date – name
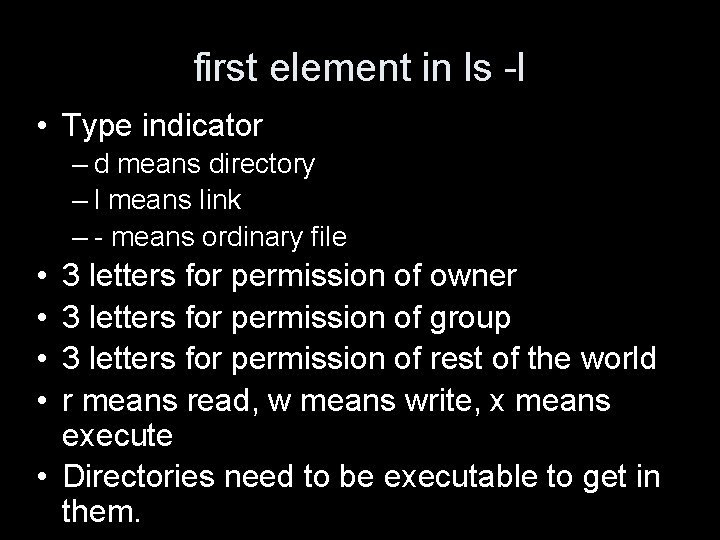
first element in ls -l • Type indicator – d means directory – l means link – - means ordinary file • • 3 letters for permission of owner 3 letters for permission of group 3 letters for permission of rest of the world r means read, w means write, x means execute • Directories need to be executable to get in them.
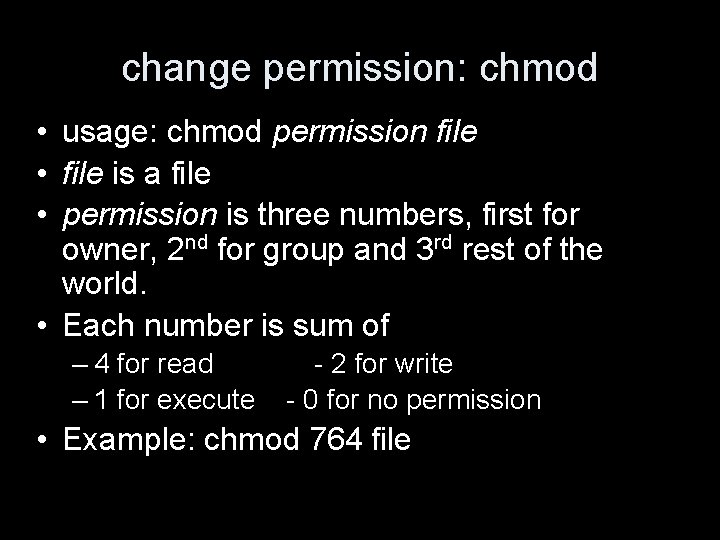
change permission: chmod • usage: chmod permission file • file is a file • permission is three numbers, first for owner, 2 nd for group and 3 rd rest of the world. • Each number is sum of – 4 for read – 1 for execute - 2 for write - 0 for no permission • Example: chmod 764 file
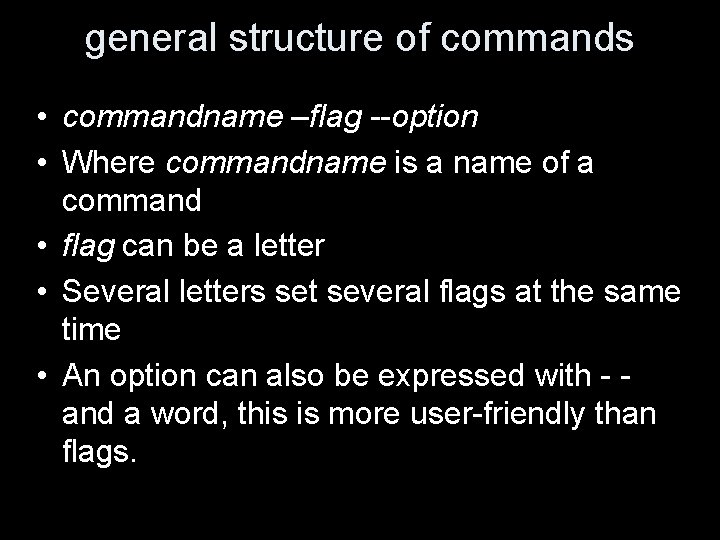
general structure of commands • commandname –flag --option • Where commandname is a name of a command • flag can be a letter • Several letters set several flags at the same time • An option can also be expressed with - and a word, this is more user-friendly than flags.
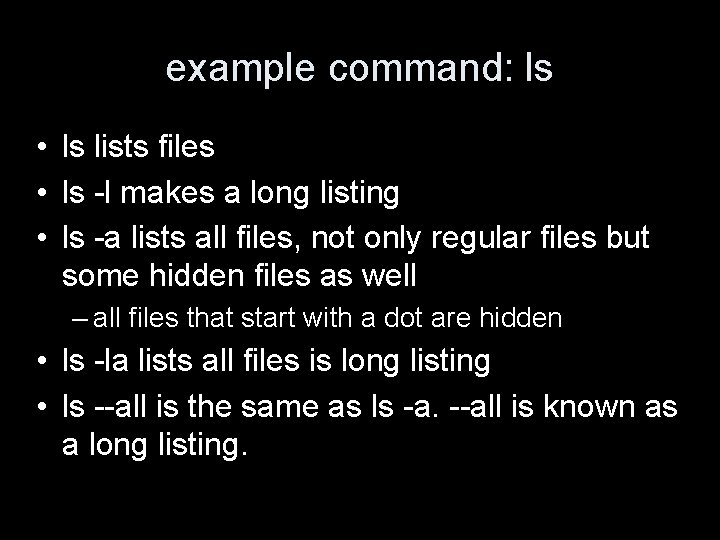
example command: ls • ls lists files • ls -l makes a long listing • ls -a lists all files, not only regular files but some hidden files as well – all files that start with a dot are hidden • ls -la lists all files is long listing • ls --all is the same as ls -a. --all is known as a long listing.
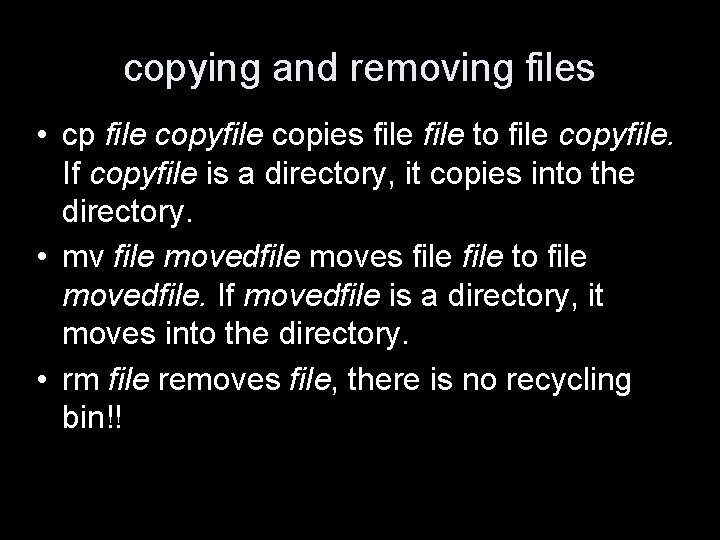
copying and removing files • cp file copyfile copies file to file copyfile. If copyfile is a directory, it copies into the directory. • mv file movedfile moves file to file movedfile. If movedfile is a directory, it moves into the directory. • rm file removes file, there is no recycling bin!!
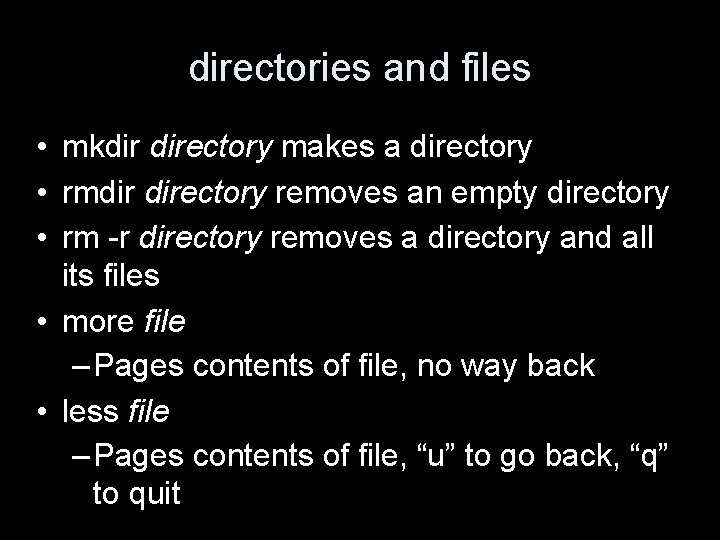
directories and files • mkdir directory makes a directory • rmdir directory removes an empty directory • rm -r directory removes a directory and all its files • more file – Pages contents of file, no way back • less file – Pages contents of file, “u” to go back, “q” to quit
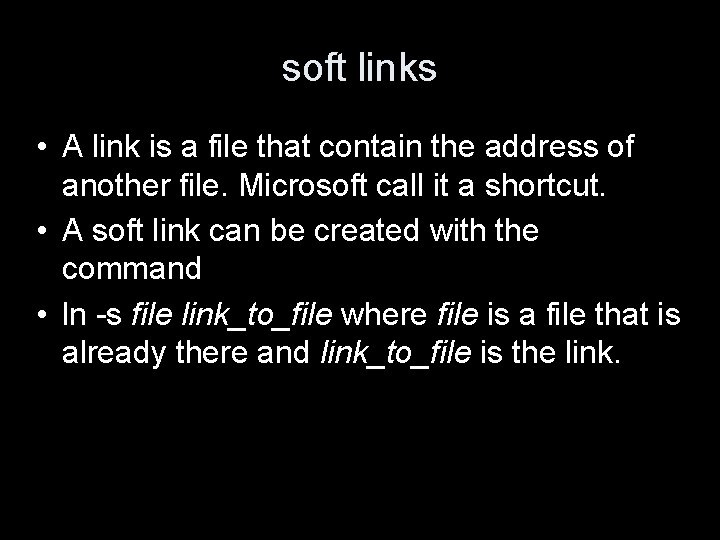
soft links • A link is a file that contain the address of another file. Microsoft call it a shortcut. • A soft link can be created with the command • ln -s file link_to_file where file is a file that is already there and link_to_file is the link.
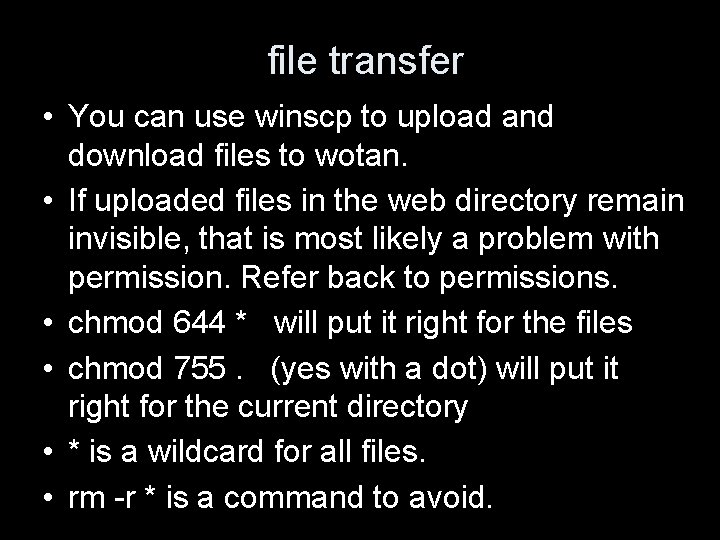
file transfer • You can use winscp to upload and download files to wotan. • If uploaded files in the web directory remain invisible, that is most likely a problem with permission. Refer back to permissions. • chmod 644 * will put it right for the files • chmod 755. (yes with a dot) will put it right for the current directory • * is a wildcard for all files. • rm -r * is a command to avoid.
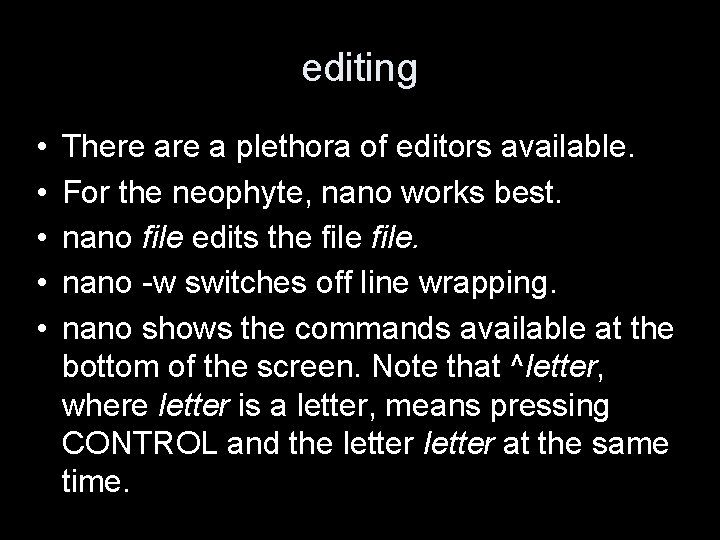
editing • • • There a plethora of editors available. For the neophyte, nano works best. nano file edits the file. nano -w switches off line wrapping. nano shows the commands available at the bottom of the screen. Note that ^letter, where letter is a letter, means pressing CONTROL and the letter at the same time.
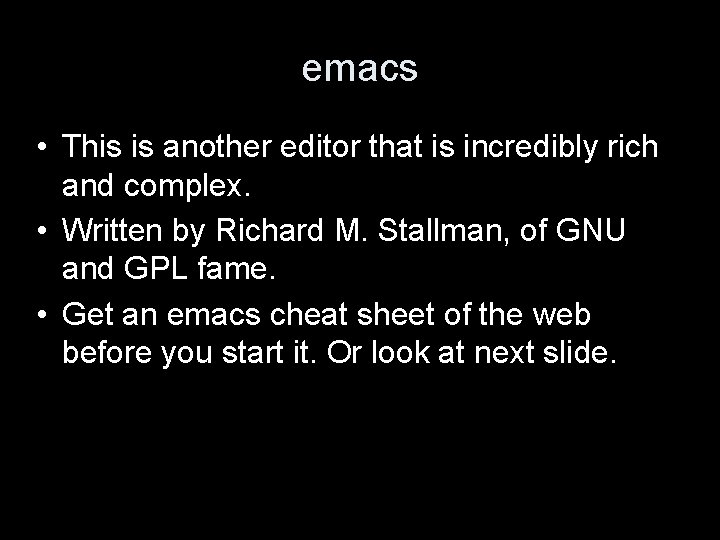
emacs • This is another editor that is incredibly rich and complex. • Written by Richard M. Stallman, of GNU and GPL fame. • Get an emacs cheat sheet of the web before you start it. Or look at next slide.
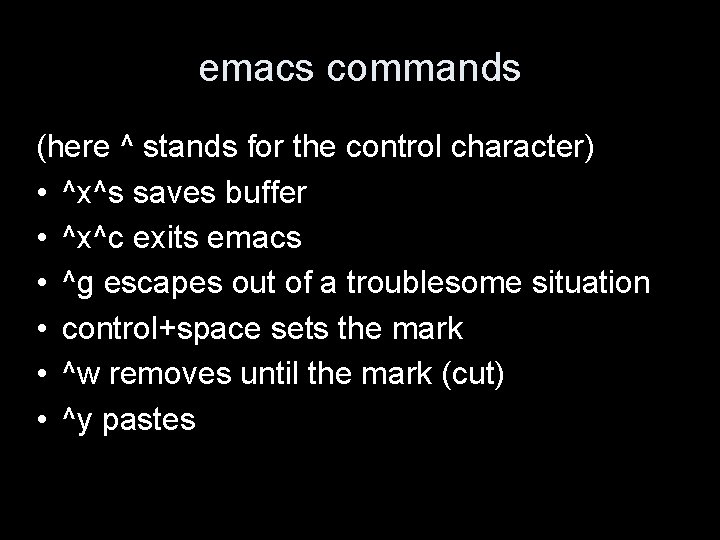
emacs commands (here ^ stands for the control character) • ^x^s saves buffer • ^x^c exits emacs • ^g escapes out of a troublesome situation • control+space sets the mark • ^w removes until the mark (cut) • ^y pastes
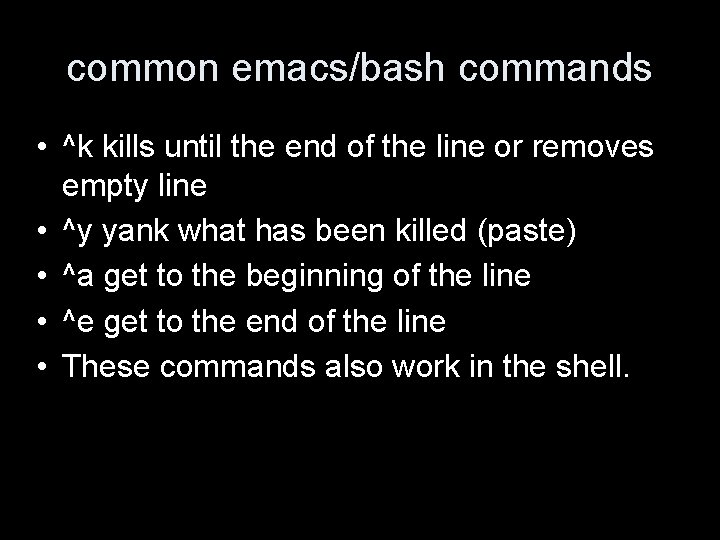
common emacs/bash commands • ^k kills until the end of the line or removes empty line • ^y yank what has been killed (paste) • ^a get to the beginning of the line • ^e get to the end of the line • These commands also work in the shell.
emacs modes • Just like people get into different moods, emacs gets into different modes. • One mode that will split your pants is the PHP mode. • Then look how emacs checks for completion of parenthesis, braces, brackets, and the ; and use the tab character to indent.
copy and paste • Putty allows to copy and paste text between windows and wotan. • On the windows machine, it uses the windows approach to copy and paste • On wotan machine, – you copy by highlighting with the mouse’ left button – you paste using the middle button – if you don't have a middle button, use left and right together
man • man is the manual lookup command • You usually say “man command” if you want to have an overview over the command. • man -k keyword looks up the man pages on the computer for pages with the keyword. I don't find this very effictive ; -(
echo • echo is a command to desplay a line of text. • Example: echo foo
cat • This is a program that displays the contents of a file. • Use like “cat file” to display the contents of the file. •
more • This is a paging utility. • It is mostly used as part of a pipe. • You take the output of a command pipe it to the input of the next command • Example “cat longfile | more” • | is the piping operator.
less • This is a paging utility. It does more than more. • You can use the command “u” to go up. • You must use the command “q” to leave the page.
du • du is a command to look at disk usage. • du -s makes a summary, rather than listing the usage of every. • The size is give in kilobytes. A kilobyte is 1024 bytes, not 1000 bytes.
ln -s • ln -s origin target makes a link from a target file target to an original file origin. • Then when you access target you get the same contents as in origin. • This concept is knows as a shortcut in Microsoft windows.
ssh • ssh user@host logs you in as user on the host can be a DNS name or an IP address. • If you don't have you public keys in the remote account's. ssh/autorized_keys file, you will be prompted for a password.
slogin • slogin is a bit of a synonym for ssh. • I use it often “slogin host -l user”.
scp • This copies files from one host to another. You can use it has complicated as “scp user 1@host 1: file 1 user 2@host 2: file 2. • But often one of the users is the current user on the current host. In that case the user@host: bit can be left out. • If you don't have permissions via keys you will be prompted for passwords.
date • date says what time it is. • This depends on the locale, as set of conventions to deal with language issues.
find • finds file in a directory. • This is a very important and powerful command. • Example: “find. -type f -name '*. deb'” finds all regular files ending with “deb” • The most powerful feature is “-exec command ; ” that executes a command on the files found. Each file is represented by {}
find examples • find ~/public_html -name '*. html' -exec cp {} {}. org ; • find ~/public_html -name '*. css' -exec cat {} >> /tmp/master. css ;
output and error • In programs that ran on the shell, there are two concepts, the output and the error. • The output is what is written by the command in normal operation, e. g. a list of files for ls. The output is often empty, for example for the cp command. • The error of a command is what is reported when an error occurs. Example “cp foo bar” will generate an error when there is no file foo.
output redirection • The redirect the output of a command to a file, use > or >> • Example “echo foo > /tmp/foo. file” • When you use “>” the file will be created anew. • When you use “>>” the output will be appended to an existing file, if any.
error redirection • The redirect the output of a command to a file, use “ 2>” or “ 2>>” • Example “cp foo 2> /tmp/error. file” • When you use “ 2>” the file will be created anew. • When you use “ 2>>” the error will be appended to an existing file, if any.
pipes • The piping operator | connects the output of one command to the input of another. • Example: echo “hi thomas” | mutt krichel@openlib. org
grep • grep is a very important utility to look up a pattern in a file, as in “grep pattern file”. • Pattern is often just a string of what we want to find. • But in the pattern, the following will have special meaning: ( ) +. ? * []. • grep -r finds the pattern recursively.
cut • Cut cuts parts of an output.
sort and uniq • sorts entries in it's input. Example: “last | cut -f 1 | sort” gives you a sorted list of last users. • uniq gives uniq values in an sorted list. The list has to be sorted first. Example “last | cut -f 1 | sort | uniq”
crontab files • /etc/crontab is the system wide crontab. • /etc/cron. d, /etc/cron. monthly, /etc/cron. daily, /etc/cron. weekly have more cron examples for your viewing pleasure. • Output and error from a crontab entry is sent by local mail to the user. • This is one reason of having mail at least set up locally, i. e. from the machine to users on the same machine.
crontab entries • You can create a file that contains commands you want to schedule regularly, and the schedule • The file contains lines of the form minutes hour day_of_month day_of_week. There day_of_week ranges form 0 to 6 with 0 being Sunday. • Save this in a file say etc/crontab. • 05 00 13 * 5 five past midnight on Friday 13 th.
crontab call • “crontab –l “ lists entries • “contab file” sets a contab file
http: //openlib. org/home/krichel Thank you for your attention! Please switch off machines before leaving!
- Slides: 62