Linux Kongress 2009 Dresden IKEv 2 based VPNs
Linux Kongress 2009 Dresden IKEv 2 -based VPNs using strong. Swan Prof. Dr. Andreas Steffen andreas. steffen@strongswan. org Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 1
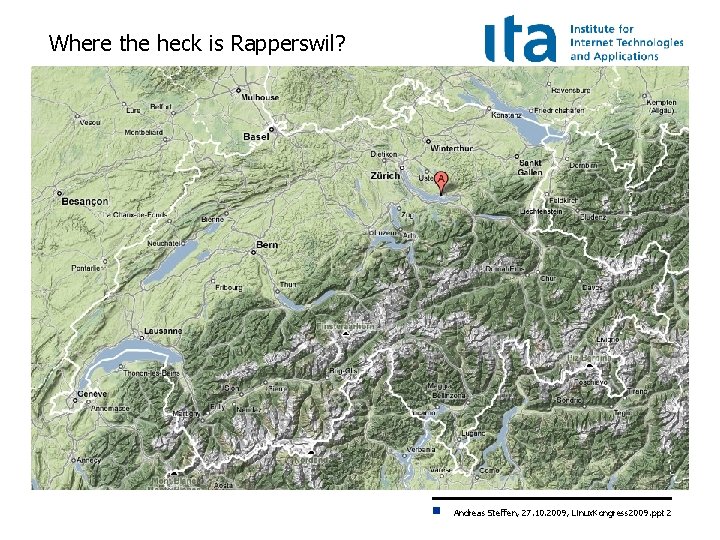
Where the heck is Rapperswil? Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 2
HSR - Hochschule für Technik Rapperswil • • • University of Applied Sciences with about 1000 students Faculty of Information Technology (300 -400 students) Bachelor Course (3 years), Master Course (+1. 5 years) Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 3
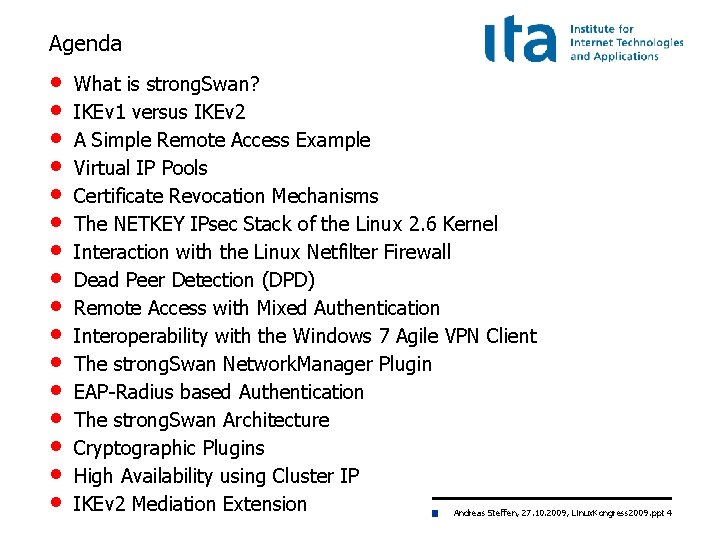
Agenda • • • • What is strong. Swan? IKEv 1 versus IKEv 2 A Simple Remote Access Example Virtual IP Pools Certificate Revocation Mechanisms The NETKEY IPsec Stack of the Linux 2. 6 Kernel Interaction with the Linux Netfilter Firewall Dead Peer Detection (DPD) Remote Access with Mixed Authentication Interoperability with the Windows 7 Agile VPN Client The strong. Swan Network. Manager Plugin EAP-Radius based Authentication The strong. Swan Architecture Cryptographic Plugins High Availability using Cluster IP IKEv 2 Mediation Extension Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 4
Linux Kongress 2009 Dresden What is strong. Swan? Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 5
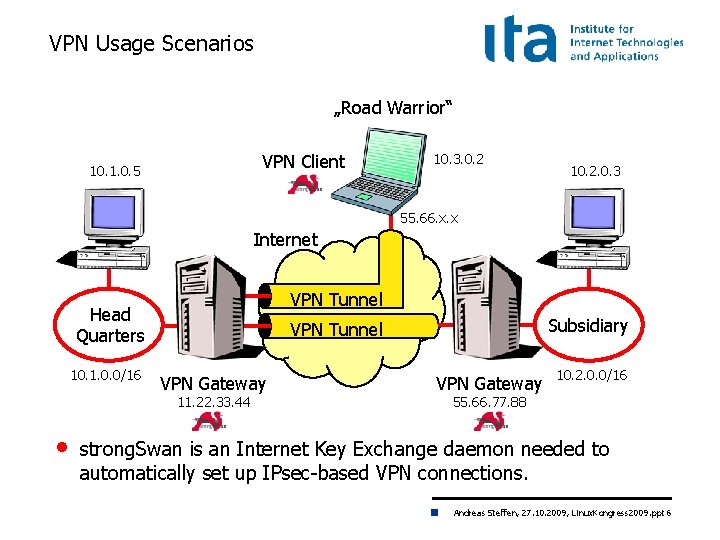
VPN Usage Scenarios „Road Warrior“ VPN Client 10. 1. 0. 5 10. 3. 0. 2 10. 2. 0. 3 55. 66. x. x Internet VPN Tunnel Head Quarters 10. 1. 0. 0/16 VPN Gateway 11. 22. 33. 44 • Subsidiary VPN Tunnel VPN Gateway 10. 2. 0. 0/16 55. 66. 77. 88 strong. Swan is an Internet Key Exchange daemon needed to automatically set up IPsec-based VPN connections. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 6
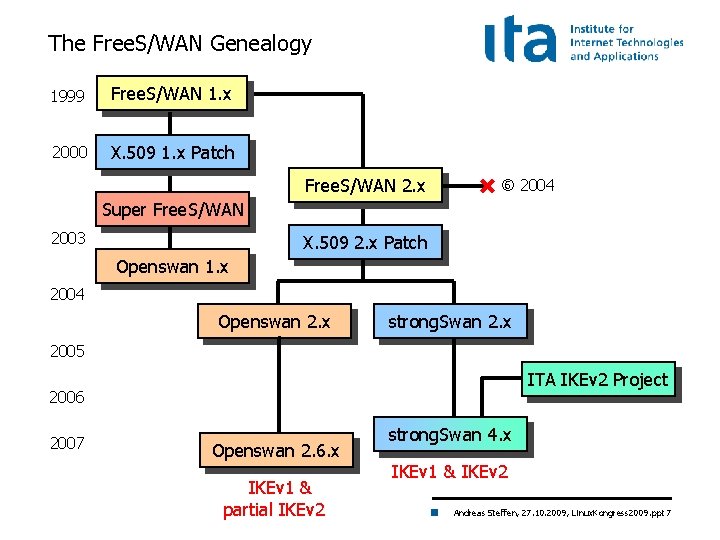
The Free. S/WAN Genealogy 1999 Free. S/WAN 1. x 2000 X. 509 1. x Patch Free. S/WAN 2. x 2004 Super Free. S/WAN 2003 X. 509 2. x Patch Openswan 1. x 2004 Openswan 2. x strong. Swan 2. x 2005 ITA IKEv 2 Project 2006 2007 Openswan 2. 6. x IKEv 1 & partial IKEv 2 strong. Swan 4. x IKEv 1 & IKEv 2 Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 7
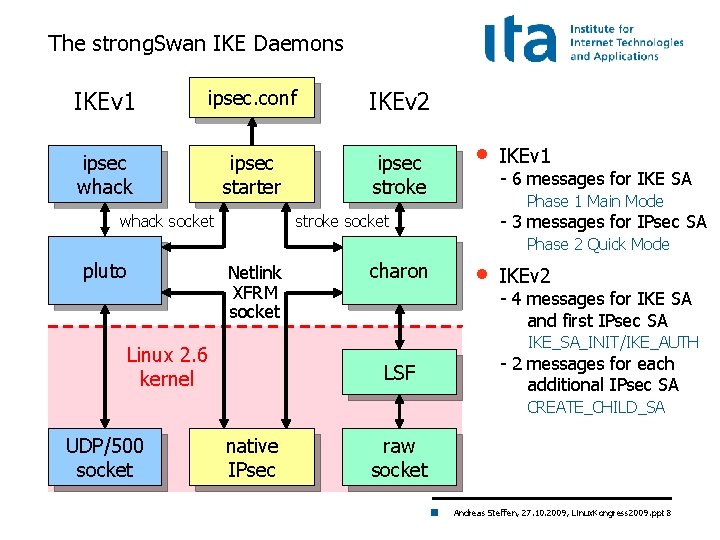
The strong. Swan IKE Daemons IKEv 1 ipsec. conf IKEv 2 ipsec whack ipsec starter ipsec stroke whack socket • IKEv 1 - 6 messages for IKE SA Phase 1 Main Mode - 3 messages for IPsec SA stroke socket Phase 2 Quick Mode pluto Netlink XFRM socket charon • IKEv 2 - 4 messages for IKE SA and first IPsec SA IKE_SA_INIT/IKE_AUTH Linux 2. 6 kernel LSF - 2 messages for each additional IPsec SA CREATE_CHILD_SA UDP/500 socket native IPsec raw socket Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 8
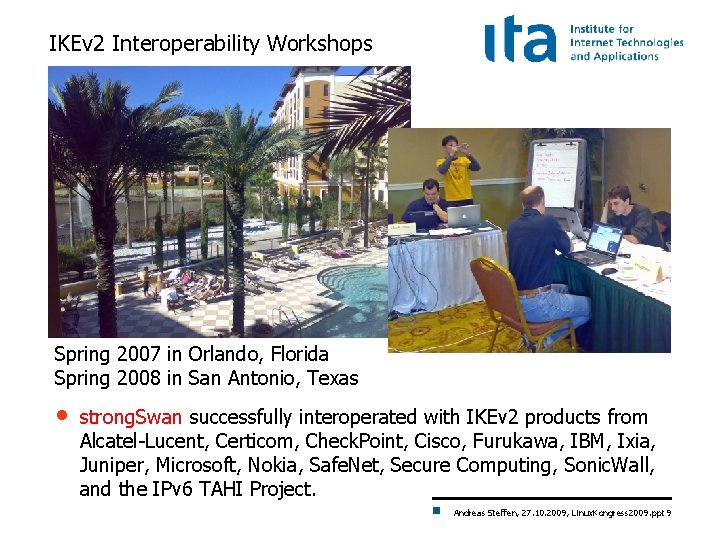
IKEv 2 Interoperability Workshops Spring 2007 in Orlando, Florida Spring 2008 in San Antonio, Texas • strong. Swan successfully interoperated with IKEv 2 products from Alcatel-Lucent, Certicom, Check. Point, Cisco, Furukawa, IBM, Ixia, Juniper, Microsoft, Nokia, Safe. Net, Secure Computing, Sonic. Wall, and the IPv 6 TAHI Project. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 9
Linux Kongress 2009 Dresden IVEv 1 versus IKEv 2 Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 10
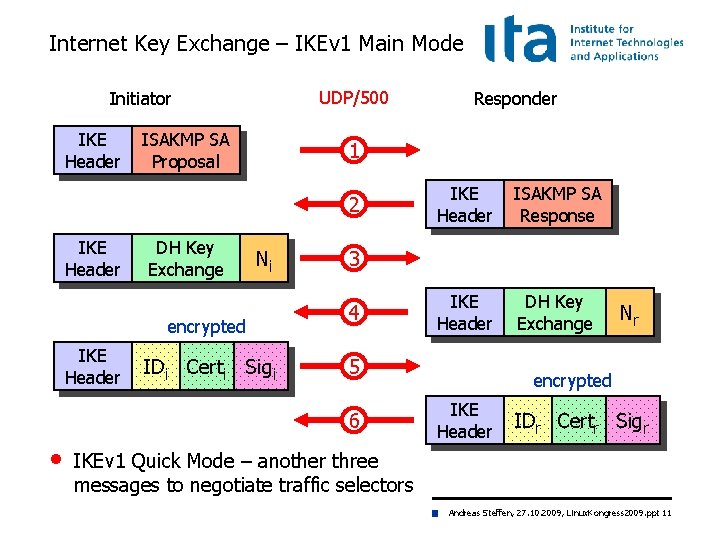
Internet Key Exchange – IKEv 1 Main Mode UDP/500 Initiator IKE Header ISAKMP SA Proposal 1 2 IKE Header DH Key Exchange Ni encrypted IKE Header IDi Certi Sigi IKE Header ISAKMP SA Response IKE Header DH Key Exchange 3 4 5 6 • Responder Nr encrypted IKE Header IDr Certr Sigr IKEv 1 Quick Mode – another three messages to negotiate traffic selectors Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 11
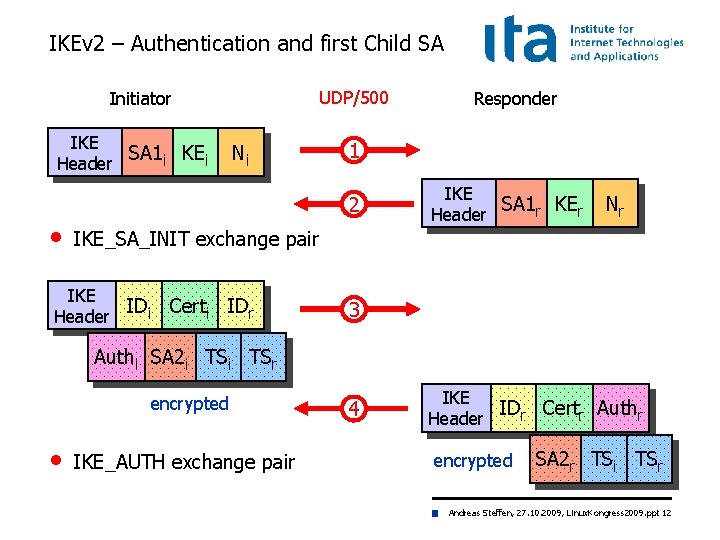
IKEv 2 – Authentication and first Child SA UDP/500 Initiator IKE SA 1 i KEi Header Ni 1 2 • Responder IKE SA 1 r KEr Header Nr IKE_SA_INIT exchange pair IKE IDi Header Certi IDr 3 Authi SA 2 i TSr encrypted • IKE_AUTH exchange pair 4 IKE IDr Certr Authr Header encrypted SA 2 r TSi TSr Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 12
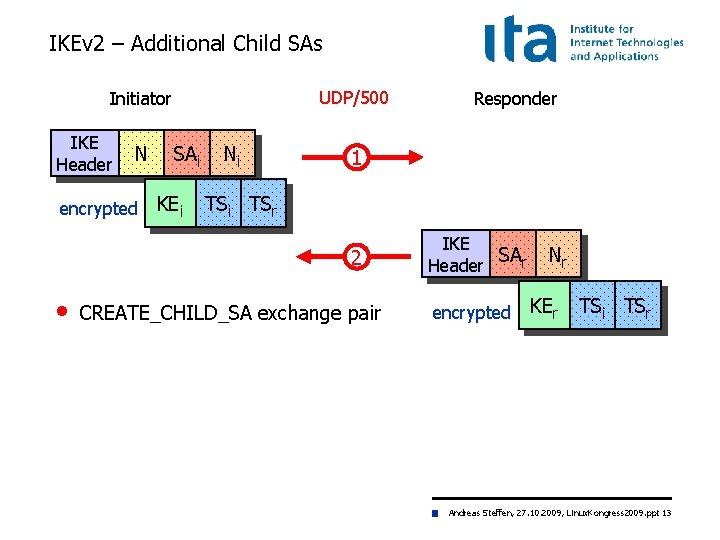
IKEv 2 – Additional Child SAs UDP/500 Initiator IKE Header N encrypted SAi KEi Ni 1 TSi TSr 2 • Responder CREATE_CHILD_SA exchange pair IKE SAr Header encrypted Nr KEr TSi TSr Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 13
Linux Kongress 2009 Dresden A Simple Remote Access Example Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 14
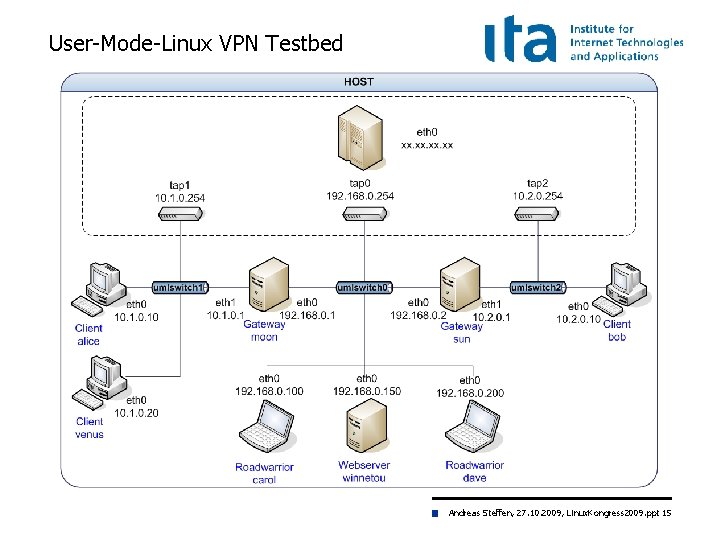
User-Mode-Linux VPN Testbed Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 15
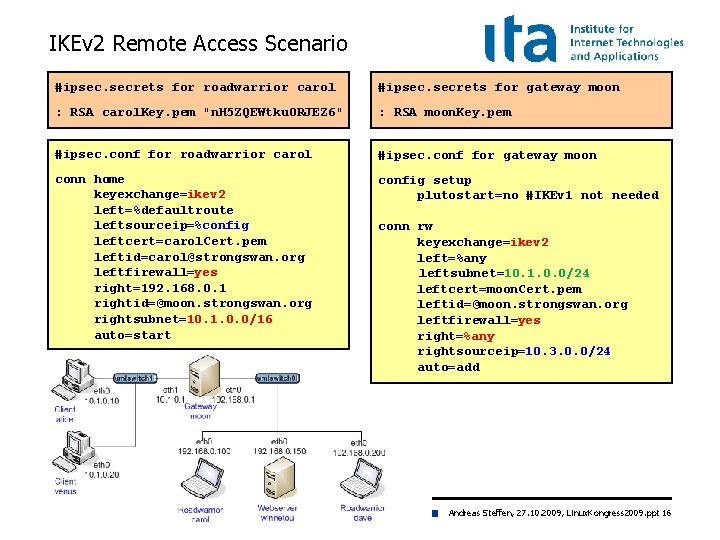
IKEv 2 Remote Access Scenario #ipsec. secrets for roadwarrior carol #ipsec. secrets for gateway moon : RSA carol. Key. pem "n. H 5 ZQEWtku 0 RJEZ 6" : RSA moon. Key. pem #ipsec. conf for roadwarrior carol #ipsec. conf for gateway moon conn home keyexchange=ikev 2 left=%defaultroute leftsourceip=%config leftcert=carol. Cert. pem leftid=carol@strongswan. org leftfirewall=yes right=192. 168. 0. 1 rightid=@moon. strongswan. org rightsubnet=10. 1. 0. 0/16 auto=start config setup plutostart=no #IKEv 1 not needed conn rw keyexchange=ikev 2 left=%any leftsubnet=10. 1. 0. 0/24 leftcert=moon. Cert. pem leftid=@moon. strongswan. org leftfirewall=yes right=%any rightsourceip=10. 3. 0. 0/24 auto=add Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 16
![IKEv 2 Connection Setup carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD] generating IKE_SA_INIT IKEv 2 Connection Setup carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD] generating IKE_SA_INIT](http://slidetodoc.com/presentation_image_h/ab2d5f5848e0f5e78ba34d3e41c2c55d/image-17.jpg)
IKEv 2 Connection Setup carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD] generating IKE_SA_INIT request [SA KE No N(NATD_S_IP) N(NATD_D_IP)] sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] received packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] parsed IKE_SA_INIT response [SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ] generating IKE_AUTH request [IDi CERTREQ IDr AUTH CP SA TSi TSr] sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] received packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] parsed IKE_AUTH response [IDr CERT AUTH CP SA TSi TSr N(AUTH_LFT)] installing new virtual IP 10. 3. 0. 1 established CHILD_SA successfully moon 05[NET] 05[ENC] 05[NET] 06[ENC] 06[IKE] 06[AUD] 06[ENC] 06[NET] • received packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] parsed IKE_SA_INIT request [SA KE No N(NATD_S_IP) N(NATD_D_IP)] generating IKE_SA_INIT response [SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ] sending packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] received packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] parsed IKE_AUTH request [IDi CERTREQ IDr AUTH CP SA TSi TSr] peer requested virtual IP %any assigning virtual IP 10. 3. 0. 1 to peer established CHILD_SA successfully generating IKE_AUTH response [IDr CERT AUTH CP SA TSi TSr N(AUTH_LFT)] sending packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] No port floating to 4500 with mobike=no Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 17
![IKEv 2 Connection Setup with MOBIKE carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD] IKEv 2 Connection Setup with MOBIKE carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD]](http://slidetodoc.com/presentation_image_h/ab2d5f5848e0f5e78ba34d3e41c2c55d/image-18.jpg)
IKEv 2 Connection Setup with MOBIKE carol 05[ENC] 05[NET] 06[ENC] 06[NET] 07[ENC] 07[IKE] 07[AUD] generating IKE_SA_INIT request [SA KE No N(NATD_S_IP) N(NATD_D_IP)] sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] received packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] parsed IKE_SA_INIT response [SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ] generating IKE_AUTH request [IDi. . N(MOBIKE_SUP) N(ADD_6_ADDR)] sending packet: from 192. 168. 0. 100[4500] to 192. 168. 0. 1[4500] received packet: from 192. 168. 0. 1[4500] to 192. 168. 0. 100[4500] parsed IKE_AUTH response [IDr. . N(MOBIKE_SUP) N(ADD_4_ADDR) N(ADD_6_ADDR)+] installing new virtual IP 10. 3. 0. 1 established CHILD_SA successfully moon 05[NET] 05[ENC] 05[NET] 06[ENC] 06[IKE] 06[AUD] 06[ENC] 06[NET] • received packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] parsed IKE_SA_INIT request [SA KE No N(NATD_S_IP) N(NATD_D_IP)] generating IKE_SA_INIT response [SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ] sending packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] received packet: from 192. 168. 0. 100[4500] to 192. 168. 0. 1[4500] parsed IKE_AUTH request [IDi. . N(MOBIKE_SUP) N(ADD_6_ADDR)] peer requested virtual IP %any assigning virtual IP 10. 3. 0. 1 to peer established CHILD_SA successfully generating IKE_AUTH resp [IDr. . N(MOBIKE_SUP) N(ADD_4_ADDR) N(ADD_6_ADDR)+] sending packet: from 192. 168. 0. 1[4500] to 192. 168. 0. 100[4500] Port floating to 4500 by default Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 18
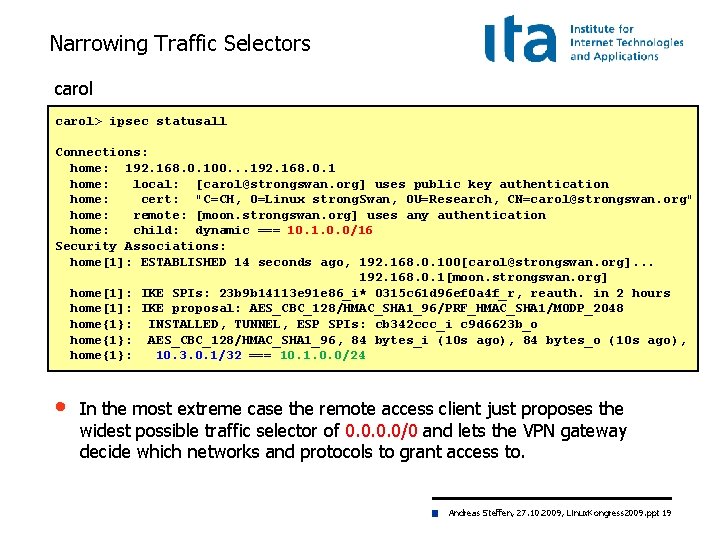
Narrowing Traffic Selectors carol> ipsec statusall Connections: home: 192. 168. 0. 100. . . 192. 168. 0. 1 home: local: [carol@strongswan. org] uses public key authentication home: cert: "C=CH, O=Linux strong. Swan, OU=Research, CN=carol@strongswan. org" home: remote: [moon. strongswan. org] uses any authentication home: child: dynamic === 10. 1. 0. 0/16 Security Associations: home[1]: ESTABLISHED 14 seconds ago, 192. 168. 0. 100[carol@strongswan. org]. . . 192. 168. 0. 1[moon. strongswan. org] home[1]: IKE SPIs: 23 b 9 b 14113 e 91 e 86_i* 0315 c 61 d 96 ef 0 a 4 f_r, reauth. in 2 hours home[1]: IKE proposal: AES_CBC_128/HMAC_SHA 1_96/PRF_HMAC_SHA 1/MODP_2048 home{1}: INSTALLED, TUNNEL, ESP SPIs: cb 342 ccc_i c 9 d 6623 b_o home{1}: AES_CBC_128/HMAC_SHA 1_96, 84 bytes_i (10 s ago), 84 bytes_o (10 s ago), home{1}: 10. 3. 0. 1/32 === 10. 1. 0. 0/24 • In the most extreme case the remote access client just proposes the widest possible traffic selector of 0. 0/0 and lets the VPN gateway decide which networks and protocols to grant access to. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 19
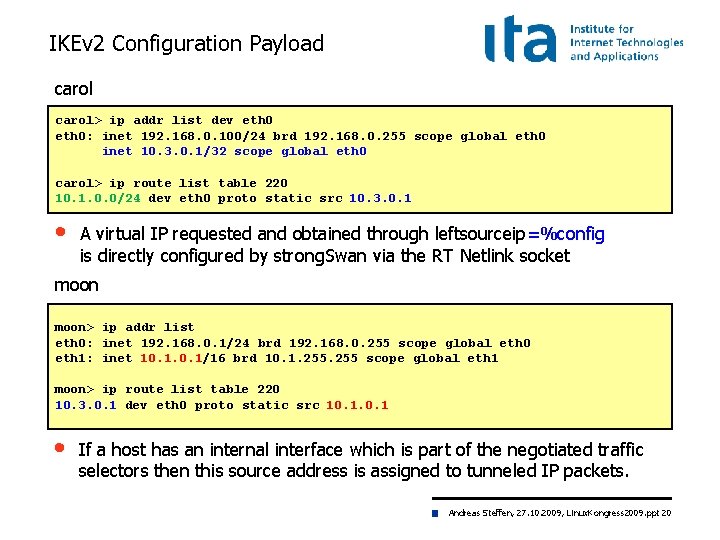
IKEv 2 Configuration Payload carol> ip addr list dev eth 0: inet 192. 168. 0. 100/24 brd 192. 168. 0. 255 scope global eth 0 inet 10. 3. 0. 1/32 scope global eth 0 carol> ip route list table 220 10. 1. 0. 0/24 dev eth 0 proto static src 10. 3. 0. 1 • A virtual IP requested and obtained through leftsourceip=%config is directly configured by strong. Swan via the RT Netlink socket moon> ip addr list eth 0: inet 192. 168. 0. 1/24 brd 192. 168. 0. 255 scope global eth 0 eth 1: inet 10. 1/16 brd 10. 1. 255 scope global eth 1 moon> ip route list table 220 10. 3. 0. 1 dev eth 0 proto static src 10. 1 • If a host has an internal interface which is part of the negotiated traffic selectors then this source address is assigned to tunneled IP packets. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 20
Linux Kongress 2009 Dresden Virtual IP Address Pools Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 21
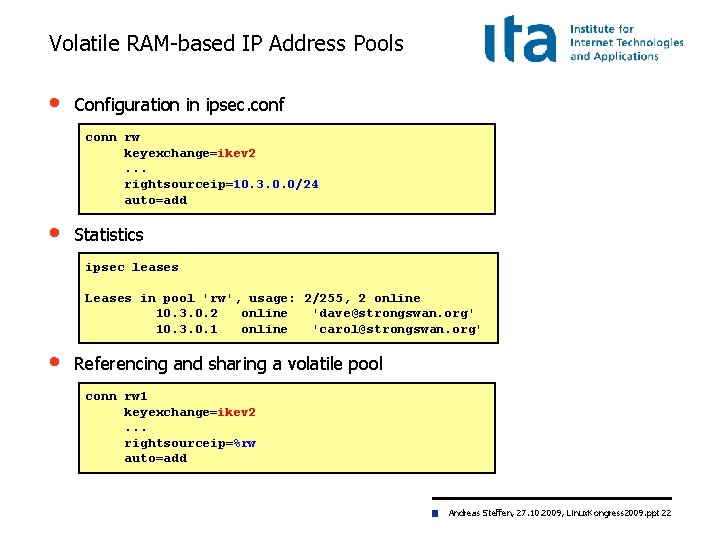
Volatile RAM-based IP Address Pools • Configuration in ipsec. conf conn rw keyexchange=ikev 2. . . rightsourceip=10. 3. 0. 0/24 auto=add • Statistics ipsec leases Leases in pool 'rw', usage: 2/255, 2 online 10. 3. 0. 2 online 'dave@strongswan. org' 10. 3. 0. 1 online 'carol@strongswan. org' • Referencing and sharing a volatile pool conn rw 1 keyexchange=ikev 2. . . rightsourceip=%rw auto=add Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 22
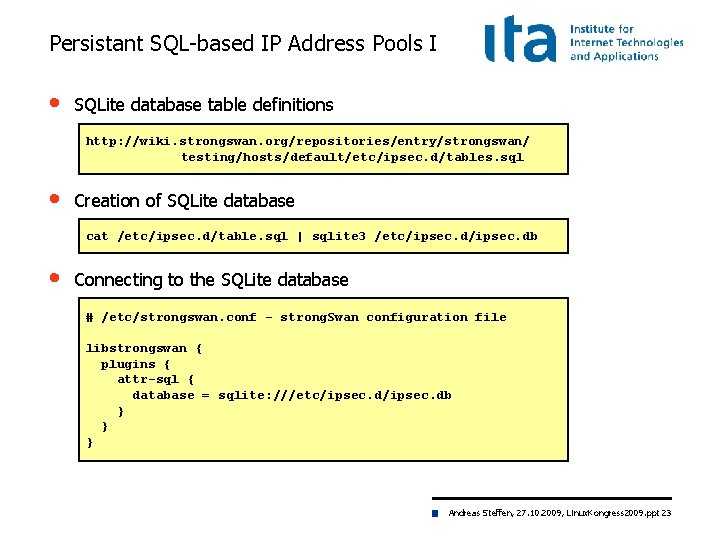
Persistant SQL-based IP Address Pools I • SQLite database table definitions http: //wiki. strongswan. org/repositories/entry/strongswan/ testing/hosts/default/etc/ipsec. d/tables. sql • Creation of SQLite database cat /etc/ipsec. d/table. sql | sqlite 3 /etc/ipsec. db • Connecting to the SQLite database # /etc/strongswan. conf - strong. Swan configuration file libstrongswan { plugins { attr-sql { database = sqlite: ///etc/ipsec. db } } } Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 23
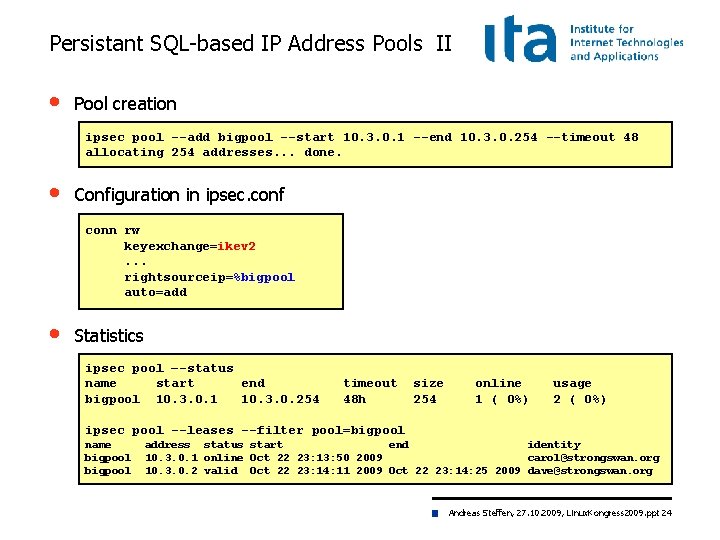
Persistant SQL-based IP Address Pools II • Pool creation ipsec pool --add bigpool --start 10. 3. 0. 1 --end 10. 3. 0. 254 --timeout 48 allocating 254 addresses. . . done. • Configuration in ipsec. conf conn rw keyexchange=ikev 2. . . rightsourceip=%bigpool auto=add • Statistics ipsec pool –-status name start end bigpool 10. 3. 0. 1 10. 3. 0. 254 timeout 48 h size 254 online 1 ( 0%) usage 2 ( 0%) ipsec pool --leases --filter pool=bigpool name bigpool address status start end identity 10. 3. 0. 1 online Oct 22 23: 13: 50 2009 carol@strongswan. org 10. 3. 0. 2 valid Oct 22 23: 14: 11 2009 Oct 22 23: 14: 25 2009 dave@strongswan. org Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 24
Linux Kongress 2009 Dresden Certificate Revocation Mechanisms Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 25
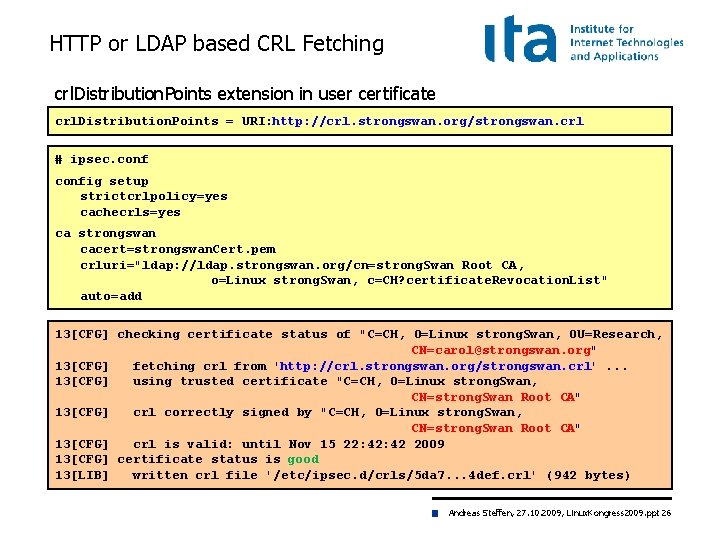
HTTP or LDAP based CRL Fetching crl. Distribution. Points extension in user certificate crl. Distribution. Points = URI: http: //crl. strongswan. org/strongswan. crl # ipsec. config setup strictcrlpolicy=yes cachecrls=yes ca strongswan cacert=strongswan. Cert. pem crluri="ldap: //ldap. strongswan. org/cn=strong. Swan Root CA, o=Linux strong. Swan, c=CH? certificate. Revocation. List" auto=add 13[CFG] checking certificate status of "C=CH, O=Linux strong. Swan, OU=Research, CN=carol@strongswan. org" 13[CFG] fetching crl from 'http: //crl. strongswan. org/strongswan. crl'. . . 13[CFG] using trusted certificate "C=CH, O=Linux strong. Swan, CN=strong. Swan Root CA" 13[CFG] crl correctly signed by "C=CH, O=Linux strong. Swan, CN=strong. Swan Root CA" 13[CFG] crl is valid: until Nov 15 22: 42 2009 13[CFG] certificate status is good 13[LIB] written crl file '/etc/ipsec. d/crls/5 da 7. . . 4 def. crl' (942 bytes) Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 26
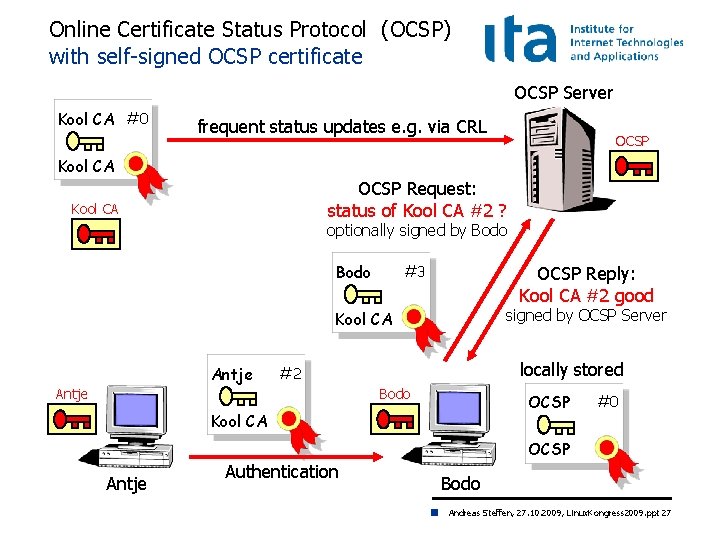
Online Certificate Status Protocol (OCSP) with self-signed OCSP certificate OCSP Server Kool CA #0 frequent status updates e. g. via CRL OCSP Kool CA OCSP Request: status of Kool CA #2 ? Kool CA optionally signed by Bodo #3 OCSP Reply: Kool CA #2 good signed by OCSP Server Kool CA Antje locally stored #2 Antje Bodo OCSP Kool CA #0 OCSP Antje Authentication Bodo Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 27
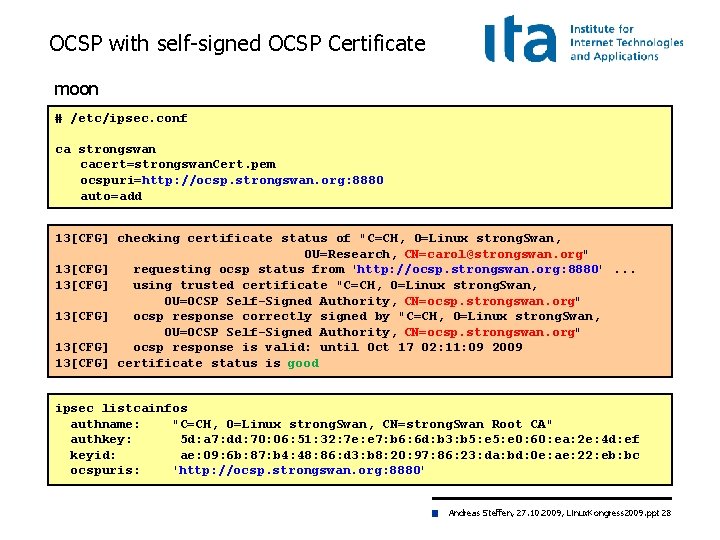
OCSP with self-signed OCSP Certificate moon # /etc/ipsec. conf ca strongswan cacert=strongswan. Cert. pem ocspuri=http: //ocsp. strongswan. org: 8880 auto=add 13[CFG] checking certificate status of "C=CH, O=Linux strong. Swan, OU=Research, CN=carol@strongswan. org" 13[CFG] requesting ocsp status from 'http: //ocsp. strongswan. org: 8880'. . . 13[CFG] using trusted certificate "C=CH, O=Linux strong. Swan, OU=OCSP Self-Signed Authority, CN=ocsp. strongswan. org" 13[CFG] ocsp response correctly signed by "C=CH, O=Linux strong. Swan, OU=OCSP Self-Signed Authority, CN=ocsp. strongswan. org" 13[CFG] ocsp response is valid: until Oct 17 02: 11: 09 2009 13[CFG] certificate status is good ipsec listcainfos authname: "C=CH, O=Linux strong. Swan, CN=strong. Swan Root CA" authkey: 5 d: a 7: dd: 70: 06: 51: 32: 7 e: e 7: b 6: 6 d: b 3: b 5: e 0: 60: ea: 2 e: 4 d: ef keyid: ae: 09: 6 b: 87: b 4: 48: 86: d 3: b 8: 20: 97: 86: 23: da: bd: 0 e: ae: 22: eb: bc ocspuris: 'http: //ocsp. strongswan. org: 8880' Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 28
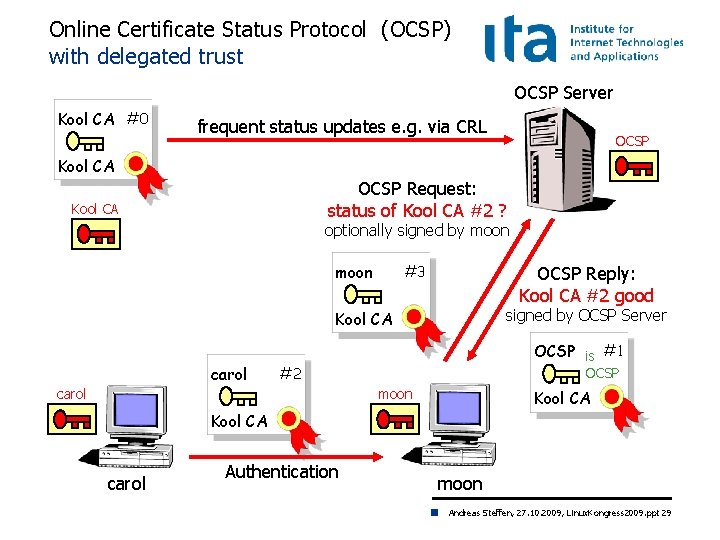
Online Certificate Status Protocol (OCSP) with delegated trust OCSP Server Kool CA #0 frequent status updates e. g. via CRL OCSP Kool CA OCSP Request: status of Kool CA #2 ? Kool CA optionally signed by moon #3 OCSP Reply: Kool CA #2 good signed by OCSP Server Kool CA carol OCSP is #1 #2 carol OCSP moon Kool CA carol Authentication moon Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 29
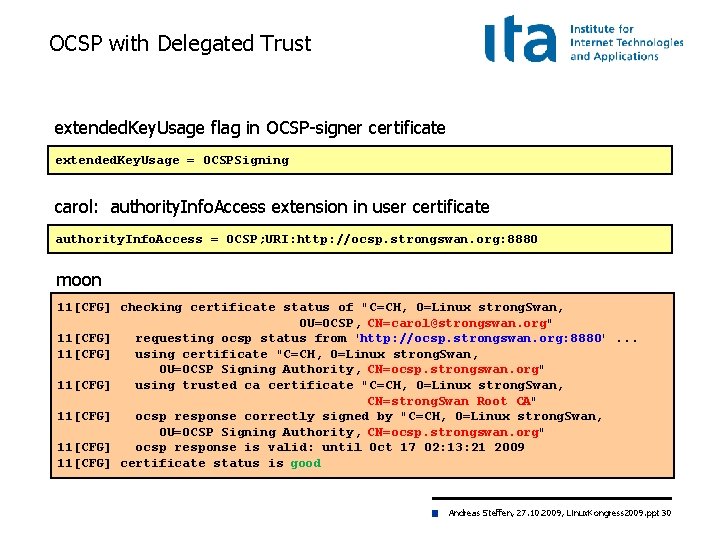
OCSP with Delegated Trust extended. Key. Usage flag in OCSP-signer certificate extended. Key. Usage = OCSPSigning carol: authority. Info. Access extension in user certificate authority. Info. Access = OCSP; URI: http: //ocsp. strongswan. org: 8880 moon 11[CFG] checking certificate status of "C=CH, O=Linux strong. Swan, OU=OCSP, CN=carol@strongswan. org" 11[CFG] requesting ocsp status from 'http: //ocsp. strongswan. org: 8880'. . . 11[CFG] using certificate "C=CH, O=Linux strong. Swan, OU=OCSP Signing Authority, CN=ocsp. strongswan. org" 11[CFG] using trusted ca certificate "C=CH, O=Linux strong. Swan, CN=strong. Swan Root CA" 11[CFG] ocsp response correctly signed by "C=CH, O=Linux strong. Swan, OU=OCSP Signing Authority, CN=ocsp. strongswan. org" 11[CFG] ocsp response is valid: until Oct 17 02: 13: 21 2009 11[CFG] certificate status is good Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 30
Linux Kongress 2009 Dresden The NETKEY IPsec Stack of the Linux 2. 6 Kernel Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 31
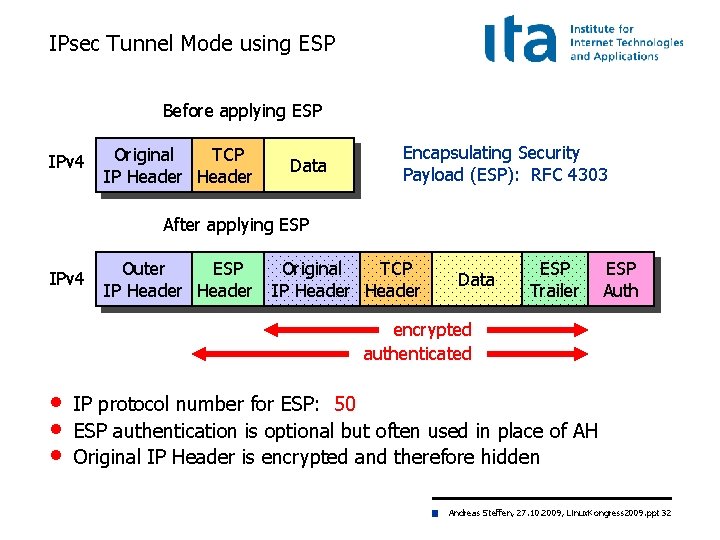
IPsec Tunnel Mode using ESP Before applying ESP IPv 4 Original TCP IP Header Data Encapsulating Security Payload (ESP): RFC 4303 After applying ESP IPv 4 Outer ESP IP Header Original TCP IP Header Data ESP Trailer ESP Auth encrypted authenticated • • • IP protocol number for ESP: 50 ESP authentication is optional but often used in place of AH Original IP Header is encrypted and therefore hidden Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 32
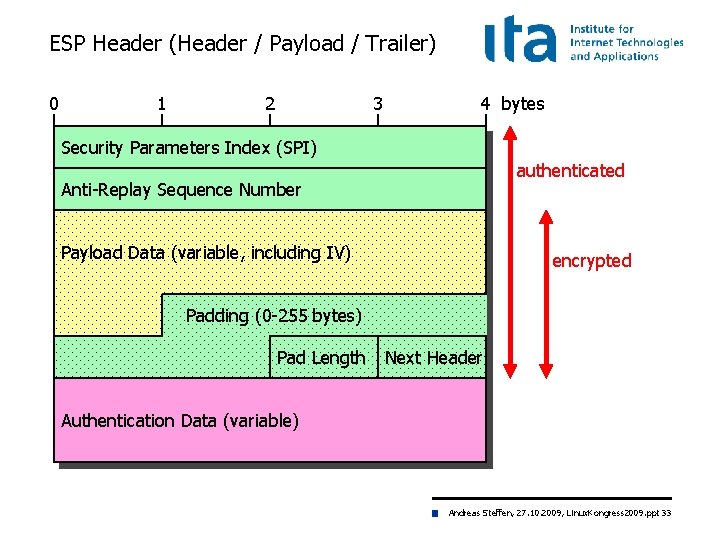
ESP Header (Header / Payload / Trailer) 0 1 2 3 4 bytes Security Parameters Index (SPI) authenticated Anti-Replay Sequence Number Payload Data (variable, îAfter applying ESP including IV) encrypted Padding (0 -255 bytes) Pad Length Next Header Authentication Data (variable) Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 33
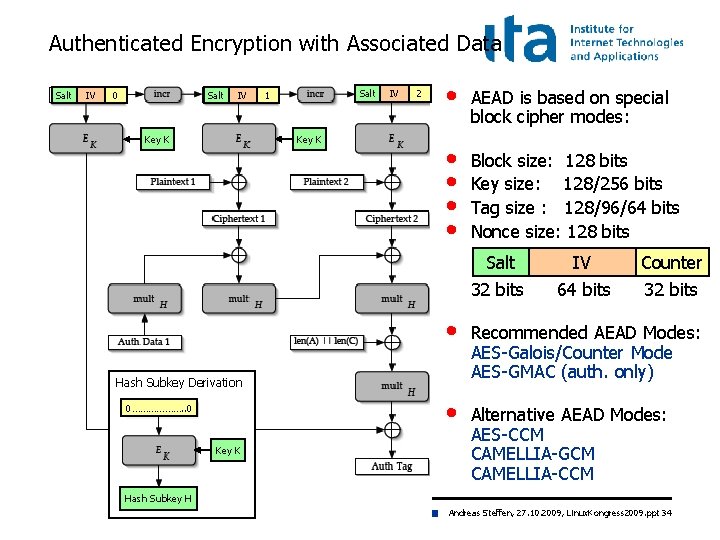
Authenticated Encryption with Associated Data Salt IV 0 Salt IV Key K Salt 1 Key K IV 2 • AEAD is based on special block cipher modes: • • Block size: 128 bits Key size: 128/256 bits Tag size : 128/96/64 bits Nonce size: 128 bits Key K IV Counter 32 bits 64 bits 32 bits • Recommended AEAD Modes: AES-Galois/Counter Mode AES-GMAC (auth. only) • Alternative AEAD Modes: AES-CCM CAMELLIA-GCM CAMELLIA-CCM Hash Subkey Derivation 0………………. . 0 Salt Hash Subkey H Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 34
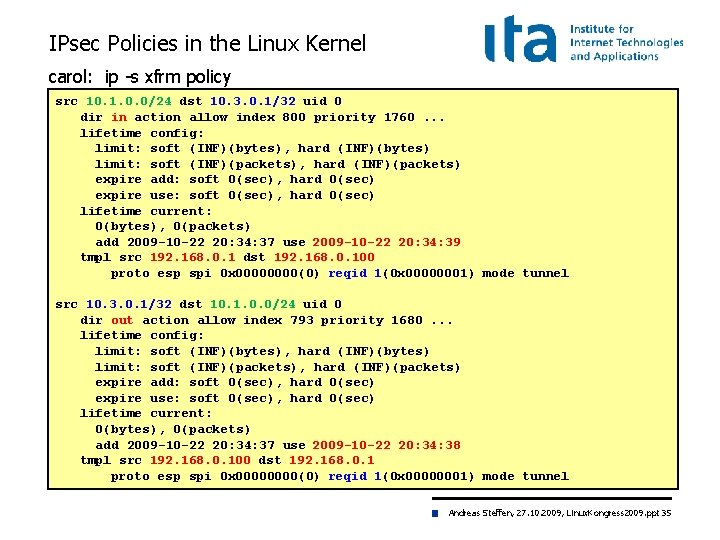
IPsec Policies in the Linux Kernel carol: ip -s xfrm policy src 10. 1. 0. 0/24 dst 10. 3. 0. 1/32 uid 0 dir in action allow index 800 priority 1760. . . lifetime config: limit: soft (INF)(bytes), hard (INF)(bytes) limit: soft (INF)(packets), hard (INF)(packets) expire add: soft 0(sec), hard 0(sec) expire use: soft 0(sec), hard 0(sec) lifetime current: 0(bytes), 0(packets) add 2009 -10 -22 20: 34: 37 use 2009 -10 -22 20: 34: 39 tmpl src 192. 168. 0. 1 dst 192. 168. 0. 100 proto esp spi 0 x 0000(0) reqid 1(0 x 00000001) mode tunnel src 10. 3. 0. 1/32 dst 10. 1. 0. 0/24 uid 0 dir out action allow index 793 priority 1680. . . lifetime config: limit: soft (INF)(bytes), hard (INF)(bytes) limit: soft (INF)(packets), hard (INF)(packets) expire add: soft 0(sec), hard 0(sec) expire use: soft 0(sec), hard 0(sec) lifetime current: 0(bytes), 0(packets) add 2009 -10 -22 20: 34: 37 use 2009 -10 -22 20: 34: 38 tmpl src 192. 168. 0. 100 dst 192. 168. 0. 1 proto esp spi 0 x 0000(0) reqid 1(0 x 00000001) mode tunnel Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 35
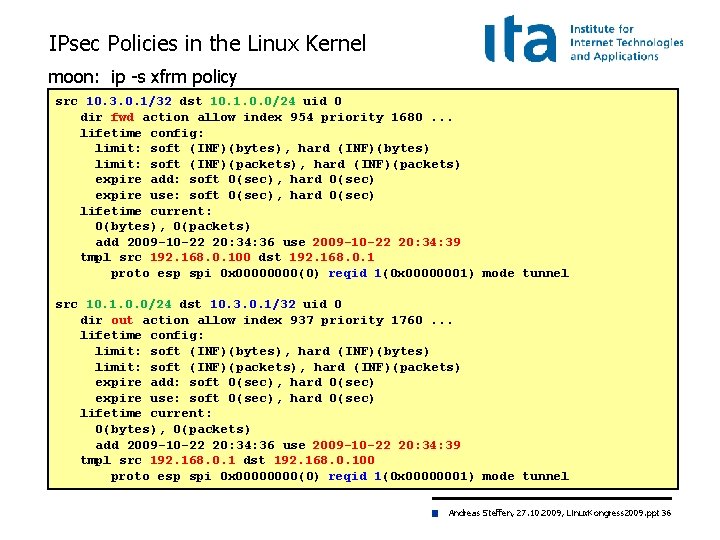
IPsec Policies in the Linux Kernel moon: ip -s xfrm policy src 10. 3. 0. 1/32 dst 10. 1. 0. 0/24 uid 0 dir fwd action allow index 954 priority 1680. . . lifetime config: limit: soft (INF)(bytes), hard (INF)(bytes) limit: soft (INF)(packets), hard (INF)(packets) expire add: soft 0(sec), hard 0(sec) expire use: soft 0(sec), hard 0(sec) lifetime current: 0(bytes), 0(packets) add 2009 -10 -22 20: 34: 36 use 2009 -10 -22 20: 34: 39 tmpl src 192. 168. 0. 100 dst 192. 168. 0. 1 proto esp spi 0 x 0000(0) reqid 1(0 x 00000001) mode tunnel src 10. 1. 0. 0/24 dst 10. 3. 0. 1/32 uid 0 dir out action allow index 937 priority 1760. . . lifetime config: limit: soft (INF)(bytes), hard (INF)(bytes) limit: soft (INF)(packets), hard (INF)(packets) expire add: soft 0(sec), hard 0(sec) expire use: soft 0(sec), hard 0(sec) lifetime current: 0(bytes), 0(packets) add 2009 -10 -22 20: 34: 36 use 2009 -10 -22 20: 34: 39 tmpl src 192. 168. 0. 1 dst 192. 168. 0. 100 proto esp spi 0 x 0000(0) reqid 1(0 x 00000001) mode tunnel Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 36
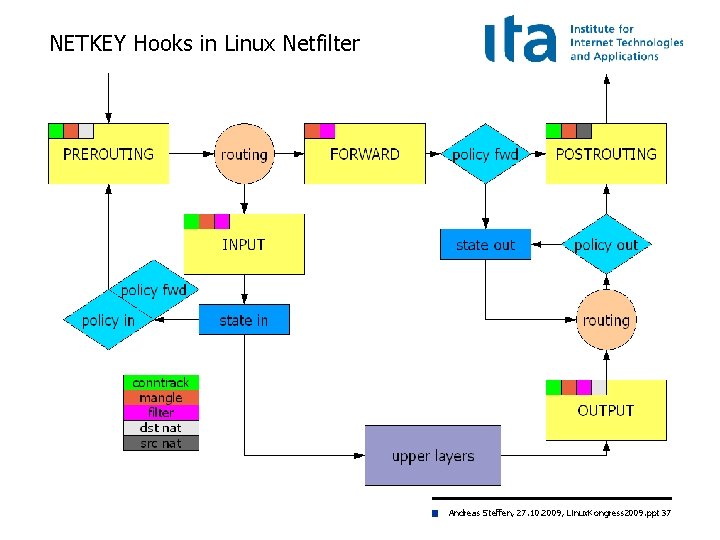
NETKEY Hooks in Linux Netfilter Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 37
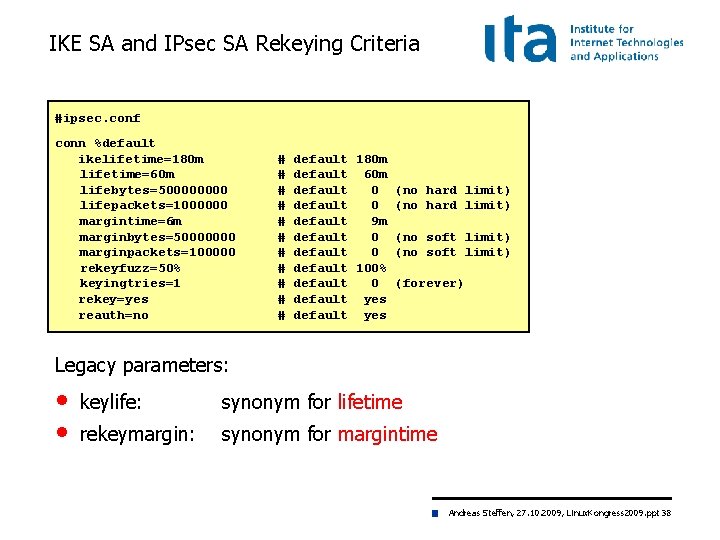
IKE SA and IPsec SA Rekeying Criteria #ipsec. conf conn %default ikelifetime=180 m lifetime=60 m lifebytes=50000 lifepackets=1000000 margintime=6 m marginbytes=50000000 marginpackets=100000 rekeyfuzz=50% keyingtries=1 rekey=yes reauth=no # # # default 180 m default 60 m default 0 (no hard limit) default 9 m default 0 (no soft limit) default 100% default 0 (forever) default yes Legacy parameters: • • keylife: synonym for lifetime rekeymargin: synonym for margintime Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 38
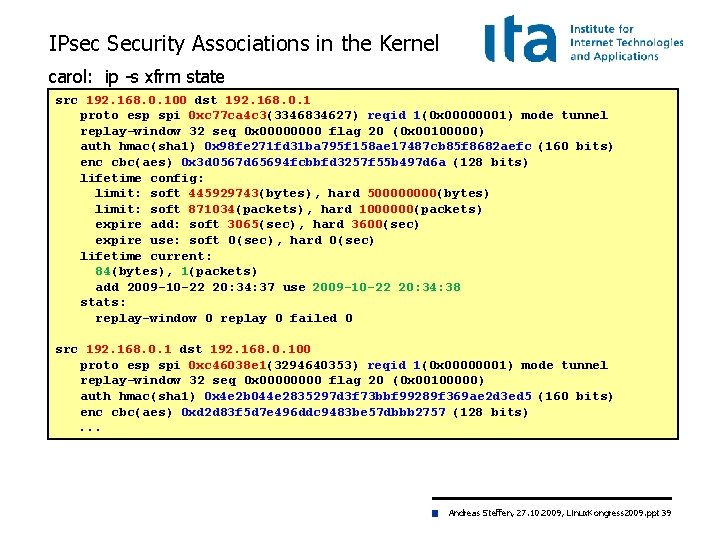
IPsec Security Associations in the Kernel carol: ip -s xfrm state src 192. 168. 0. 100 dst 192. 168. 0. 1 proto esp spi 0 xc 77 ca 4 c 3(3346834627) reqid 1(0 x 00000001) mode tunnel replay-window 32 seq 0 x 0000 flag 20 (0 x 00100000) auth hmac(sha 1) 0 x 98 fe 271 fd 31 ba 795 f 158 ae 17487 cb 85 f 8682 aefc (160 bits) enc cbc(aes) 0 x 3 d 0567 d 65694 fcbbfd 3257 f 55 b 497 d 6 a (128 bits) lifetime config: limit: soft 445929743(bytes), hard 50000(bytes) limit: soft 871034(packets), hard 1000000(packets) expire add: soft 3065(sec), hard 3600(sec) expire use: soft 0(sec), hard 0(sec) lifetime current: 84(bytes), 1(packets) add 2009 -10 -22 20: 34: 37 use 2009 -10 -22 20: 34: 38 stats: replay-window 0 replay 0 failed 0 src 192. 168. 0. 1 dst 192. 168. 0. 100 proto esp spi 0 xc 46038 e 1(3294640353) reqid 1(0 x 00000001) mode tunnel replay-window 32 seq 0 x 0000 flag 20 (0 x 00100000) auth hmac(sha 1) 0 x 4 e 2 b 044 e 2835297 d 3 f 73 bbf 99289 f 369 ae 2 d 3 ed 5 (160 bits) enc cbc(aes) 0 xd 2 d 83 f 5 d 7 e 496 ddc 9483 be 57 dbbb 2757 (128 bits). . . Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 39
Linux Kongress 2009 Dresden Interaction with the Linux Netfilter Firewall Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 40
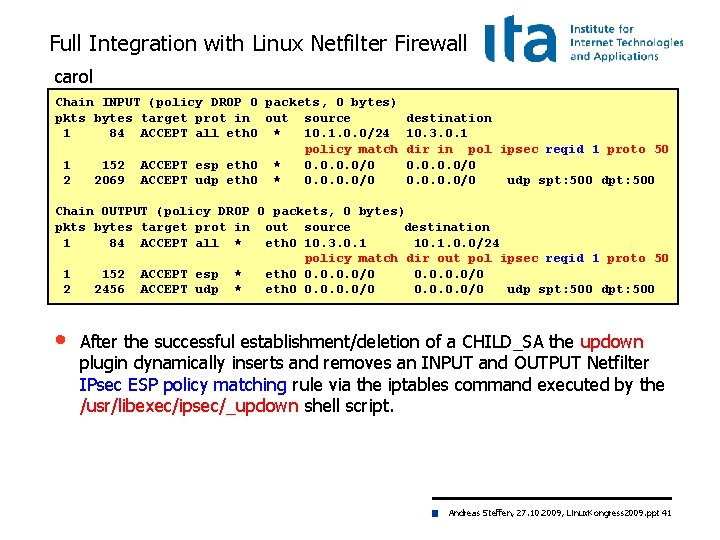
Full Integration with Linux Netfilter Firewall carol Chain INPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source 1 84 ACCEPT all eth 0 * 10. 1. 0. 0/24 policy match 1 152 ACCEPT esp eth 0 * 0. 0/0 2 2069 ACCEPT udp eth 0 * 0. 0/0 destination 10. 3. 0. 1 dir in pol ipsec reqid 1 proto 50 0. 0/0 udp spt: 500 dpt: 500 Chain OUTPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 1 84 ACCEPT all * eth 0 10. 3. 0. 1 10. 1. 0. 0/24 policy match dir out pol ipsec reqid 1 proto 50 1 152 ACCEPT esp * eth 0 0. 0/0 2 2456 ACCEPT udp * eth 0 0. 0/0 udp spt: 500 dpt: 500 • After the successful establishment/deletion of a CHILD_SA the updown plugin dynamically inserts and removes an INPUT and OUTPUT Netfilter IPsec ESP policy matching rule via the iptables command executed by the /usr/libexec/ipsec/_updown shell script. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 41
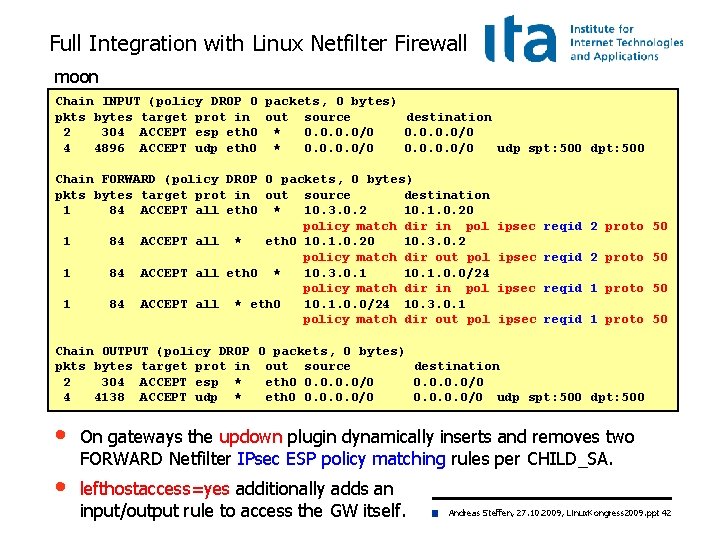
Full Integration with Linux Netfilter Firewall moon Chain INPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 2 304 ACCEPT esp eth 0 * 0. 0/0 4 4896 ACCEPT udp eth 0 * 0. 0/0 udp spt: 500 dpt: 500 Chain FORWARD (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 1 84 ACCEPT all eth 0 * 10. 3. 0. 2 10. 1. 0. 20 policy match dir in pol 1 84 ACCEPT all * eth 0 10. 1. 0. 20 10. 3. 0. 2 policy match dir out pol 1 84 ACCEPT all eth 0 * 10. 3. 0. 1 10. 1. 0. 0/24 policy match dir in pol 1 84 ACCEPT all * eth 0 10. 1. 0. 0/24 10. 3. 0. 1 policy match dir out pol ipsec reqid 2 proto 50 ipsec reqid 1 proto 50 Chain OUTPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 2 304 ACCEPT esp * eth 0 0. 0/0 4 4138 ACCEPT udp * eth 0 0. 0/0 udp spt: 500 dpt: 500 • On gateways the updown plugin dynamically inserts and removes two FORWARD Netfilter IPsec ESP policy matching rules per CHILD_SA. • lefthostaccess=yes additionally adds an input/output rule to access the GW itself. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 42
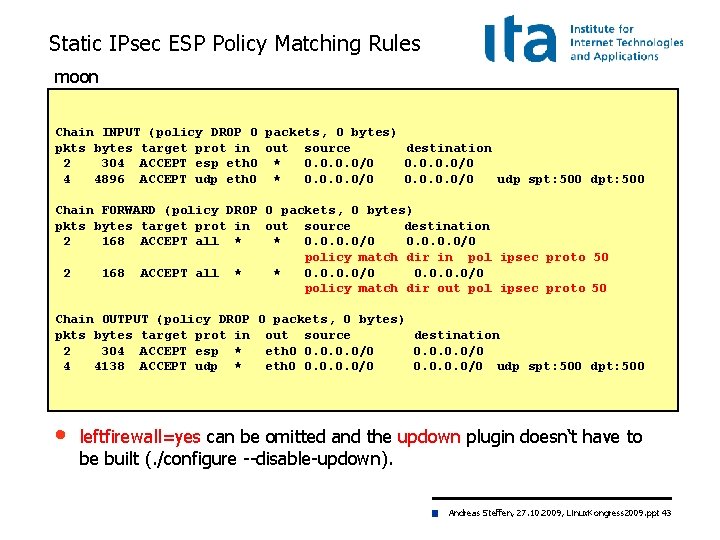
Static IPsec ESP Policy Matching Rules moon Chain INPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 2 304 ACCEPT esp eth 0 * 0. 0/0 4 4896 ACCEPT udp eth 0 * 0. 0/0 udp spt: 500 dpt: 500 Chain FORWARD (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 2 168 ACCEPT all * * 0. 0/0 policy match dir in pol ipsec proto 50 2 168 ACCEPT all * * 0. 0/0 policy match dir out pol ipsec proto 50 Chain OUTPUT (policy DROP 0 packets, 0 bytes) pkts bytes target prot in out source destination 2 304 ACCEPT esp * eth 0 0. 0/0 4 4138 ACCEPT udp * eth 0 0. 0/0 udp spt: 500 dpt: 500 • leftfirewall=yes can be omitted and the updown plugin doesn‘t have to be built (. /configure --disable-updown). Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 43
Linux Kongress 2009 Dresden Dead Peer Detection (DPD) Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 44
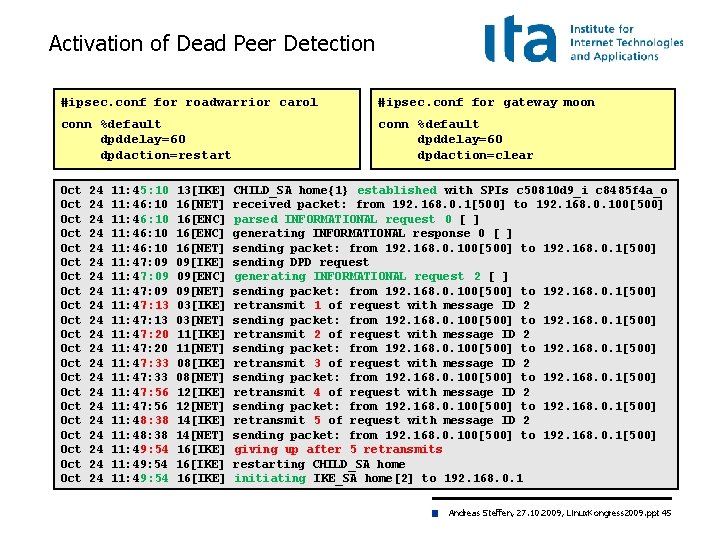
Activation of Dead Peer Detection #ipsec. conf for roadwarrior carol #ipsec. conf for gateway moon conn %default dpddelay=60 dpdaction=restart conn %default dpddelay=60 dpdaction=clear Oct Oct Oct Oct Oct Oct 24 24 24 24 24 24 11: 45: 10 11: 46: 10 11: 47: 09 11: 47: 13 11: 47: 20 11: 47: 33 11: 47: 56 11: 48: 38 11: 49: 54 13[IKE] 16[NET] 16[ENC] 16[NET] 09[IKE] 09[ENC] 09[NET] 03[IKE] 03[NET] 11[IKE] 11[NET] 08[IKE] 08[NET] 12[IKE] 12[NET] 14[IKE] 14[NET] 16[IKE] CHILD_SA home{1} established with SPIs c 50810 d 9_i c 8485 f 4 a_o received packet: from 192. 168. 0. 1[500] to 192. 168. 0. 100[500] parsed INFORMATIONAL request 0 [ ] generating INFORMATIONAL response 0 [ ] sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] sending DPD request generating INFORMATIONAL request 2 [ ] sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] retransmit 1 of request with message ID 2 sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] retransmit 2 of request with message ID 2 sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] retransmit 3 of request with message ID 2 sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] retransmit 4 of request with message ID 2 sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] retransmit 5 of request with message ID 2 sending packet: from 192. 168. 0. 100[500] to 192. 168. 0. 1[500] giving up after 5 retransmits restarting CHILD_SA home initiating IKE_SA home[2] to 192. 168. 0. 1 Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 45
Linux Kongress 2009 Dresden Remote-Access with Mixed Authentication Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 46
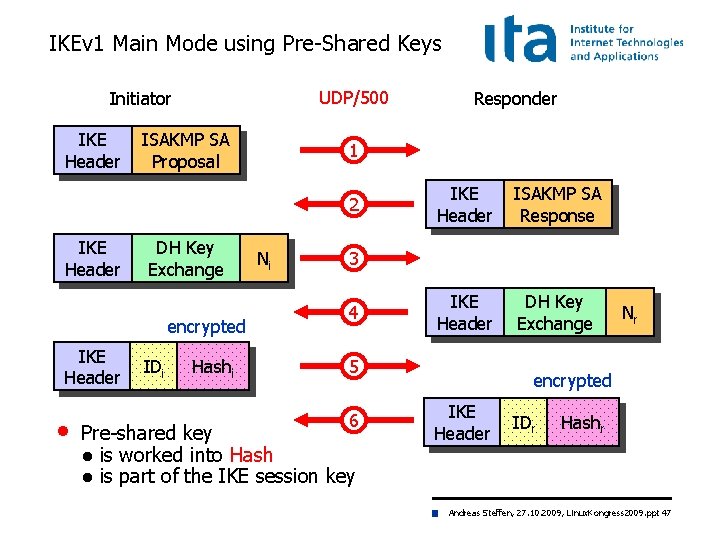
IKEv 1 Main Mode using Pre-Shared Keys UDP/500 Initiator IKE Header ISAKMP SA Proposal 1 2 IKE Header DH Key Exchange encrypted IKE Header • IDi Hashi Responder Ni IKE Header ISAKMP SA Response IKE Header DH Key Exchange 3 4 5 6 Pre-shared key ● is worked into Hash ● is part of the IKE session key Nr encrypted IKE Header IDr Hashr Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 47
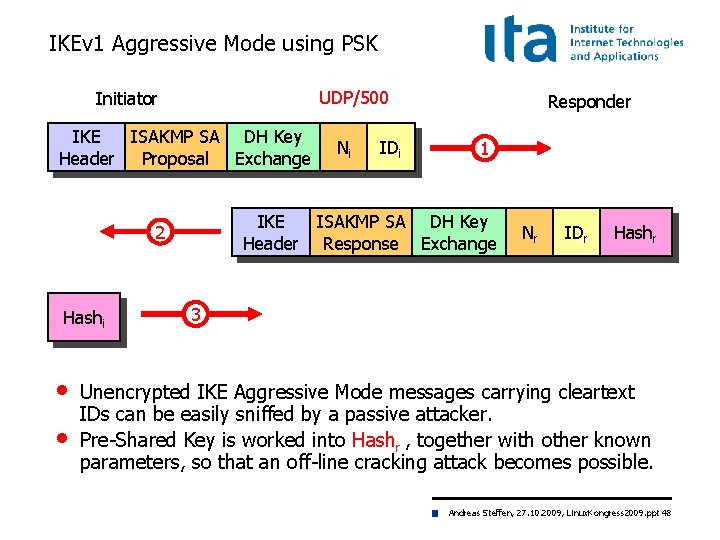
IKEv 1 Aggressive Mode using PSK UDP/500 Initiator IKE ISAKMP SA DH Key Header Proposal Exchange • • IDi 1 IKE ISAKMP SA DH Key Header Response Exchange 2 Hashi Ni Responder Nr IDr Hashr 3 Unencrypted IKE Aggressive Mode messages carrying cleartext IDs can be easily sniffed by a passive attacker. Pre-Shared Key is worked into Hashr , together with other known parameters, so that an off-line cracking attack becomes possible. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 48
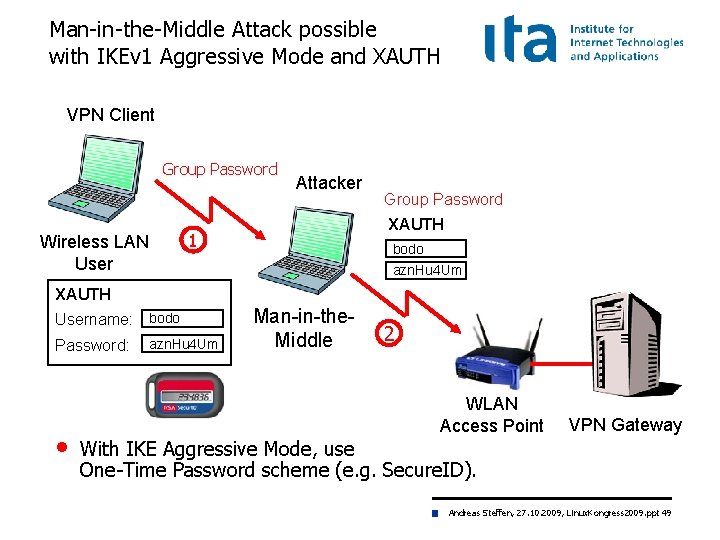
Man-in-the-Middle Attack possible with IKEv 1 Aggressive Mode and XAUTH VPN Client Group Password Attacker XAUTH 1 Wireless LAN User Group Password bodo azn. Hu 4 Um XAUTH Username: bodo Password: • azn. Hu 4 Um Man-in-the. Middle 2 WLAN Access Point VPN Gateway With IKE Aggressive Mode, use One-Time Password scheme (e. g. Secure. ID). Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 49
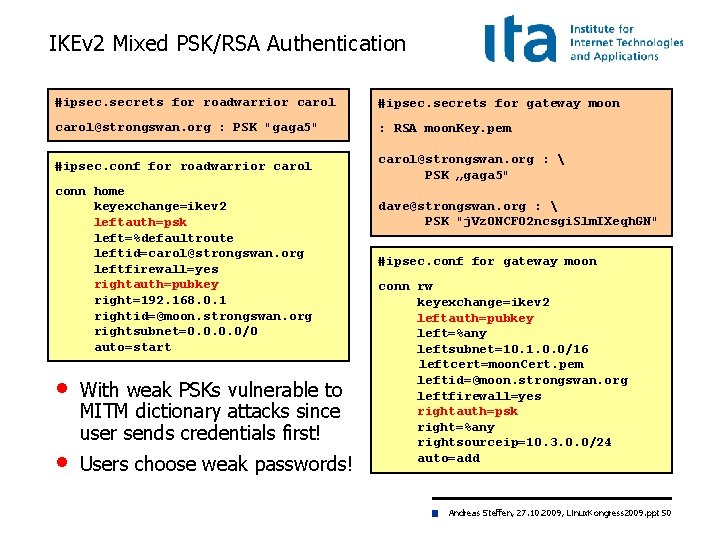
IKEv 2 Mixed PSK/RSA Authentication #ipsec. secrets for roadwarrior carol #ipsec. secrets for gateway moon carol@strongswan. org : PSK "gaga 5" : RSA moon. Key. pem #ipsec. conf for roadwarrior carol@strongswan. org : PSK „gaga 5" conn home keyexchange=ikev 2 leftauth=psk left=%defaultroute leftid=carol@strongswan. org leftfirewall=yes rightauth=pubkey right=192. 168. 0. 1 rightid=@moon. strongswan. org rightsubnet=0. 0/0 auto=start • • With weak PSKs vulnerable to MITM dictionary attacks since user sends credentials first! Users choose weak passwords! dave@strongswan. org : PSK "j. Vz. ONCF 02 ncsgi. Slm. IXeqh. GN" #ipsec. conf for gateway moon conn rw keyexchange=ikev 2 leftauth=pubkey left=%any leftsubnet=10. 1. 0. 0/16 leftcert=moon. Cert. pem leftid=@moon. strongswan. org leftfirewall=yes rightauth=psk right=%any rightsourceip=10. 3. 0. 0/24 auto=add Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 50
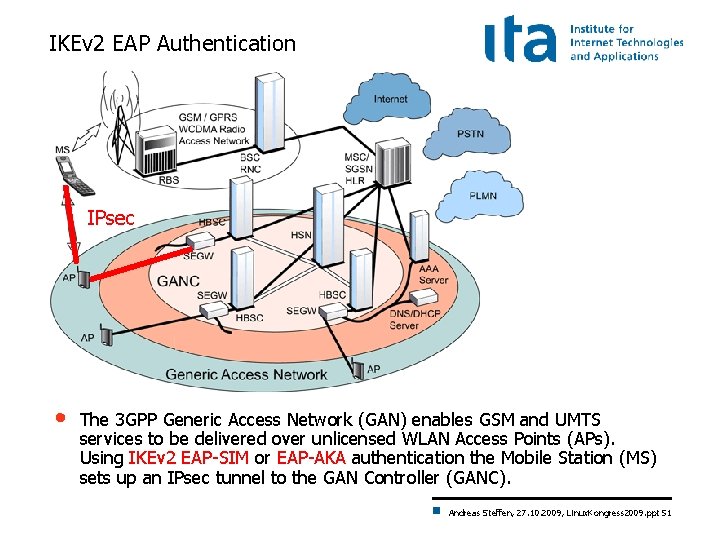
IKEv 2 EAP Authentication IPsec • The 3 GPP Generic Access Network (GAN) enables GSM and UMTS services to be delivered over unlicensed WLAN Access Points (APs). Using IKEv 2 EAP-SIM or EAP-AKA authentication the Mobile Station (MS) sets up an IPsec tunnel to the GAN Controller (GANC). Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 51
Linux Kongress 2009 Dresden Interoperability with the Windows 7 Agile VPN Client Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 52
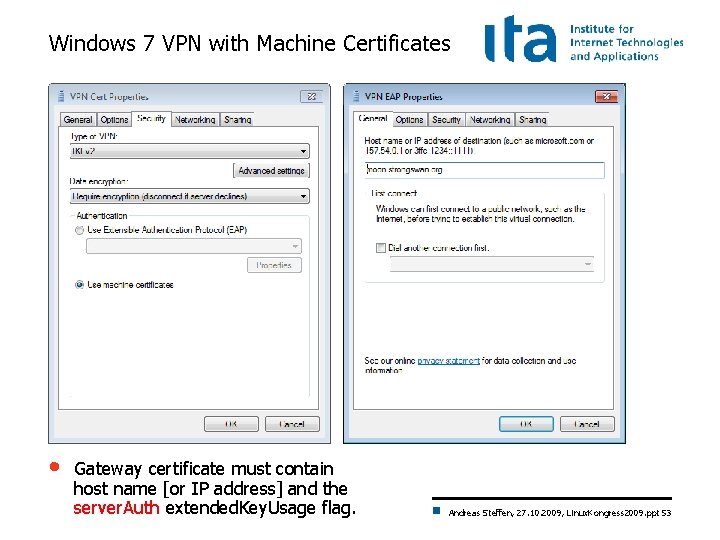
Windows 7 VPN with Machine Certificates • Gateway certificate must contain host name [or IP address] and the server. Auth extended. Key. Usage flag. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 53
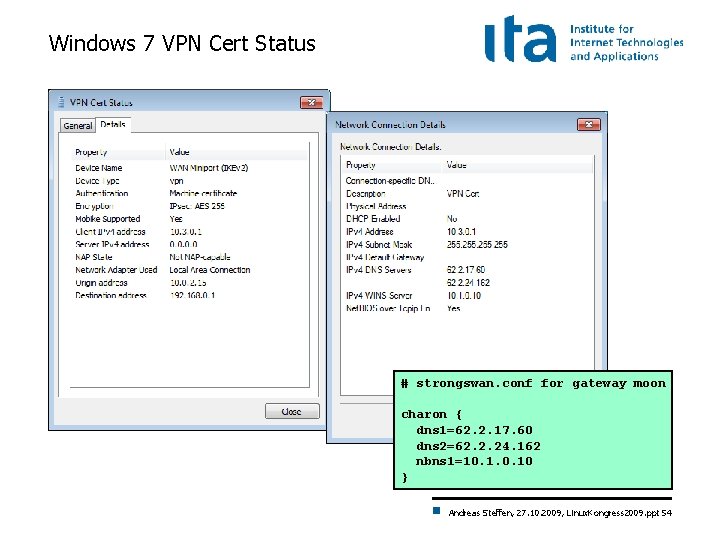
Windows 7 VPN Cert Status # strongswan. conf for gateway moon charon { dns 1=62. 2. 17. 60 dns 2=62. 2. 24. 162 nbns 1=10. 10 } Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 54
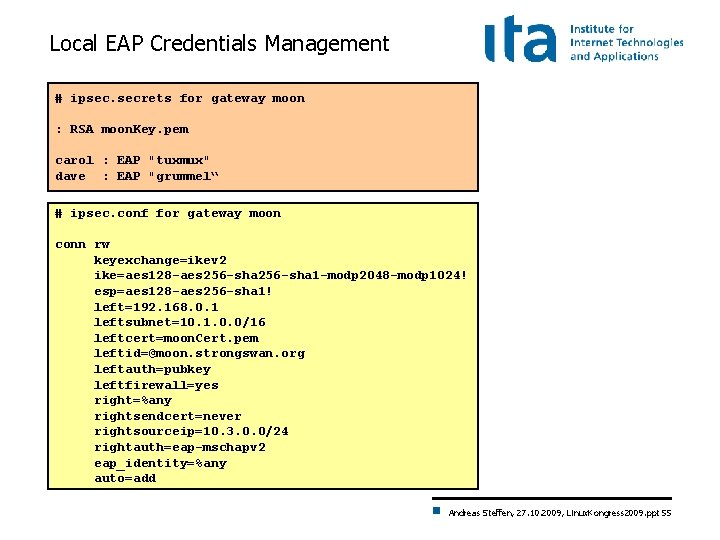
Local EAP Credentials Management # ipsec. secrets for gateway moon : RSA moon. Key. pem carol : EAP "tuxmux" dave : EAP "grummel“ # ipsec. conf for gateway moon conn rw keyexchange=ikev 2 ike=aes 128 -aes 256 -sha 1 -modp 2048 -modp 1024! esp=aes 128 -aes 256 -sha 1! left=192. 168. 0. 1 leftsubnet=10. 1. 0. 0/16 leftcert=moon. Cert. pem leftid=@moon. strongswan. org leftauth=pubkey leftfirewall=yes right=%any rightsendcert=never rightsourceip=10. 3. 0. 0/24 rightauth=eap-mschapv 2 eap_identity=%any auto=add Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 55
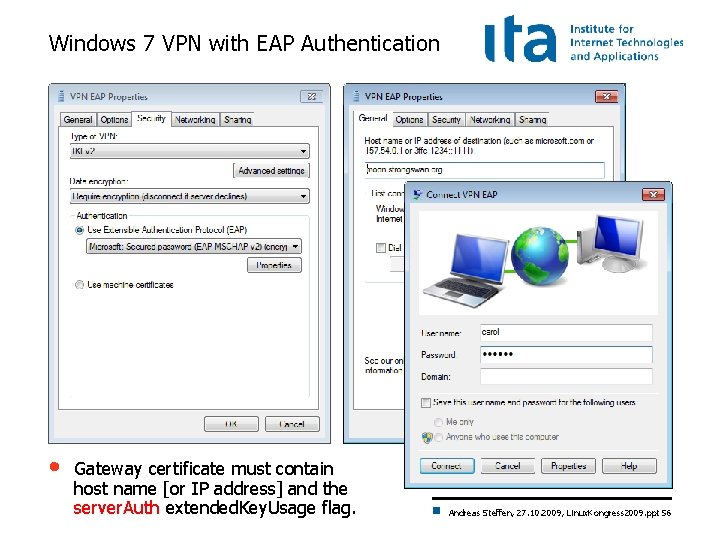
Windows 7 VPN with EAP Authentication • Gateway certificate must contain host name [or IP address] and the server. Auth extended. Key. Usage flag. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 56
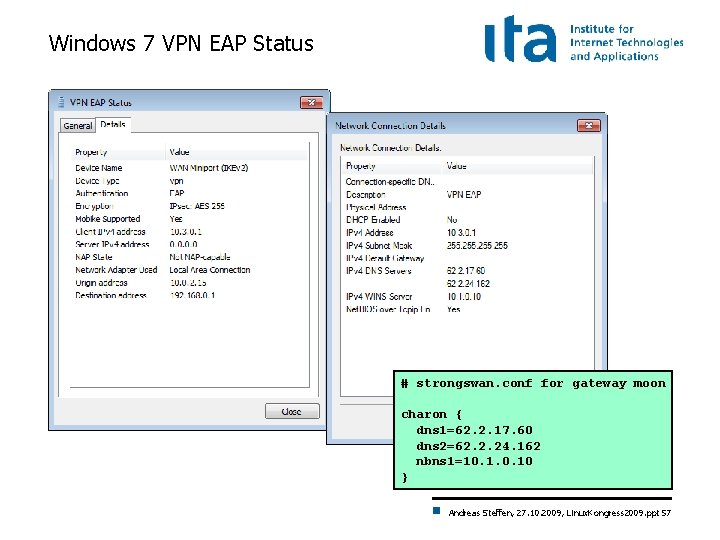
Windows 7 VPN EAP Status # strongswan. conf for gateway moon charon { dns 1=62. 2. 17. 60 dns 2=62. 2. 24. 162 nbns 1=10. 10 } Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 57
Linux Kongress 2009 Dresden The strong. Swan Network. Manager Plugin Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 58
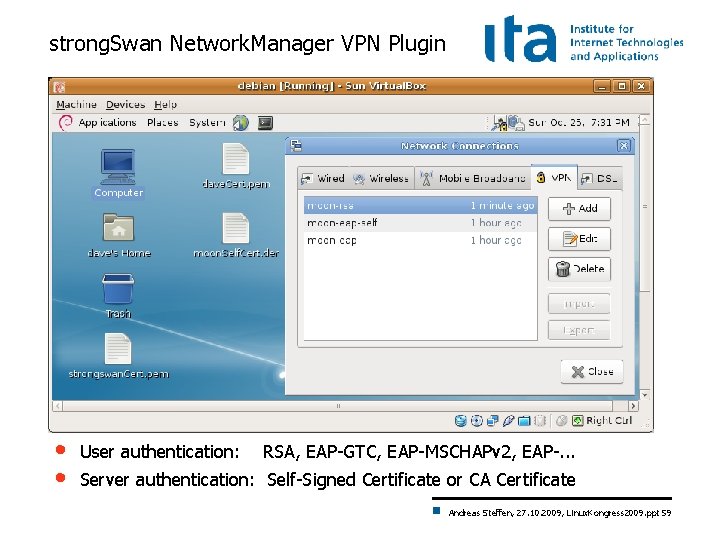
strong. Swan Network. Manager VPN Plugin • • User authentication: RSA, EAP-GTC, EAP-MSCHAPv 2, EAP-. . . Server authentication: Self-Signed Certificate or CA Certificate Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 59
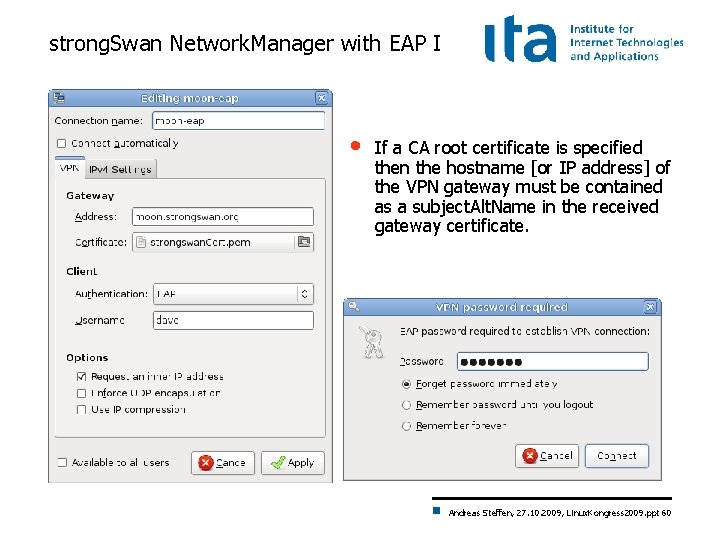
strong. Swan Network. Manager with EAP I • If a CA root certificate is specified then the hostname [or IP address] of the VPN gateway must be contained as a subject. Alt. Name in the received gateway certificate. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 60
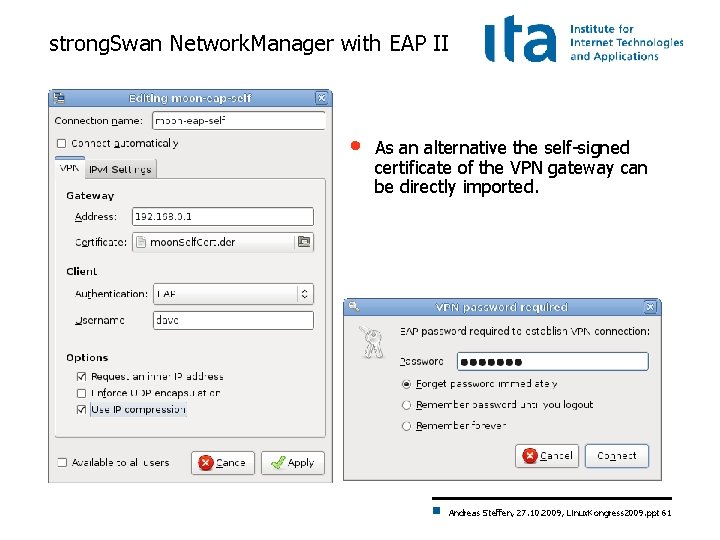
strong. Swan Network. Manager with EAP II • As an alternative the self-signed certificate of the VPN gateway can be directly imported. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 61
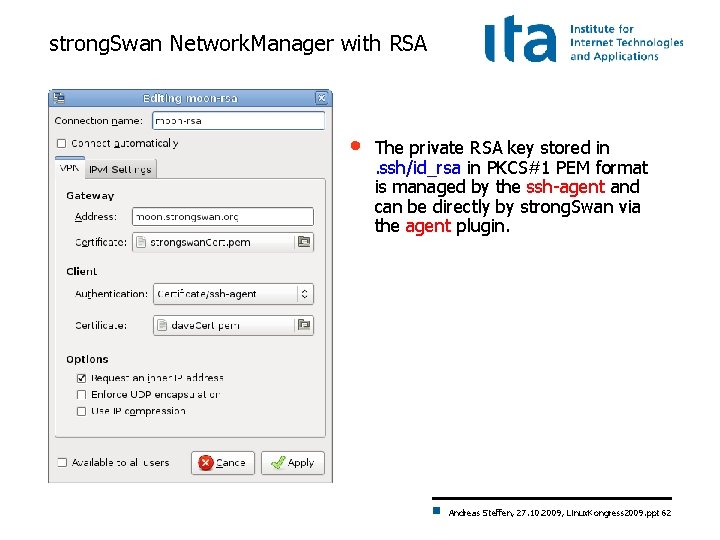
strong. Swan Network. Manager with RSA • The private RSA key stored in. ssh/id_rsa in PKCS#1 PEM format is managed by the ssh-agent and can be directly by strong. Swan via the agent plugin. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 62
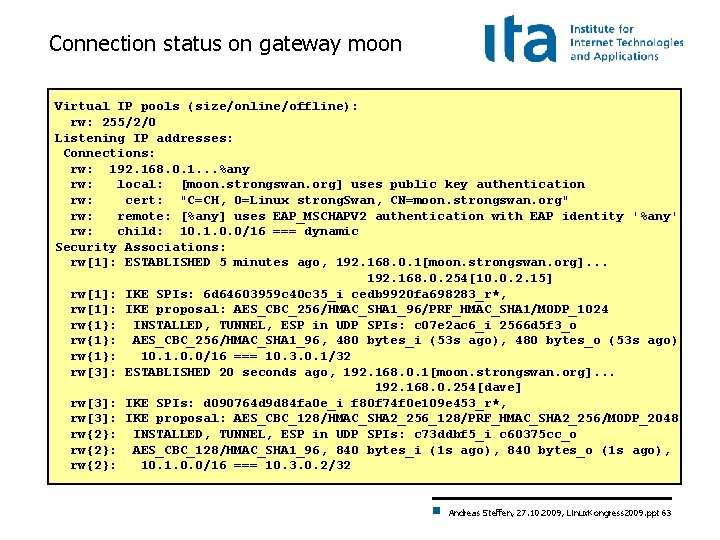
Connection status on gateway moon Virtual IP pools (size/online/offline): rw: 255/2/0 Listening IP addresses: Connections: rw: 192. 168. 0. 1. . . %any rw: local: [moon. strongswan. org] uses public key authentication rw: cert: "C=CH, O=Linux strong. Swan, CN=moon. strongswan. org" rw: remote: [%any] uses EAP_MSCHAPV 2 authentication with EAP identity '%any' rw: child: 10. 1. 0. 0/16 === dynamic Security Associations: rw[1]: ESTABLISHED 5 minutes ago, 192. 168. 0. 1[moon. strongswan. org]. . . 192. 168. 0. 254[10. 0. 2. 15] rw[1]: IKE SPIs: 6 d 64603959 c 40 c 35_i cedb 9920 fa 698283_r*, rw[1]: IKE proposal: AES_CBC_256/HMAC_SHA 1_96/PRF_HMAC_SHA 1/MODP_1024 rw{1}: INSTALLED, TUNNEL, ESP in UDP SPIs: c 07 e 2 ac 6_i 2566 d 5 f 3_o rw{1}: AES_CBC_256/HMAC_SHA 1_96, 480 bytes_i (53 s ago), 480 bytes_o (53 s ago) rw{1}: 10. 1. 0. 0/16 === 10. 3. 0. 1/32 rw[3]: ESTABLISHED 20 seconds ago, 192. 168. 0. 1[moon. strongswan. org]. . . 192. 168. 0. 254[dave] rw[3]: IKE SPIs: d 090764 d 9 d 84 fa 0 e_i f 80 f 74 f 0 e 109 e 453_r*, rw[3]: IKE proposal: AES_CBC_128/HMAC_SHA 2_256_128/PRF_HMAC_SHA 2_256/MODP_2048 rw{2}: INSTALLED, TUNNEL, ESP in UDP SPIs: c 73 ddbf 5_i c 60375 cc_o rw{2}: AES_CBC_128/HMAC_SHA 1_96, 840 bytes_i (1 s ago), 840 bytes_o (1 s ago), rw{2}: 10. 1. 0. 0/16 === 10. 3. 0. 2/32 Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 63
Linux Kongress 2009 Dresden EAP-Radius based Authentication Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 64
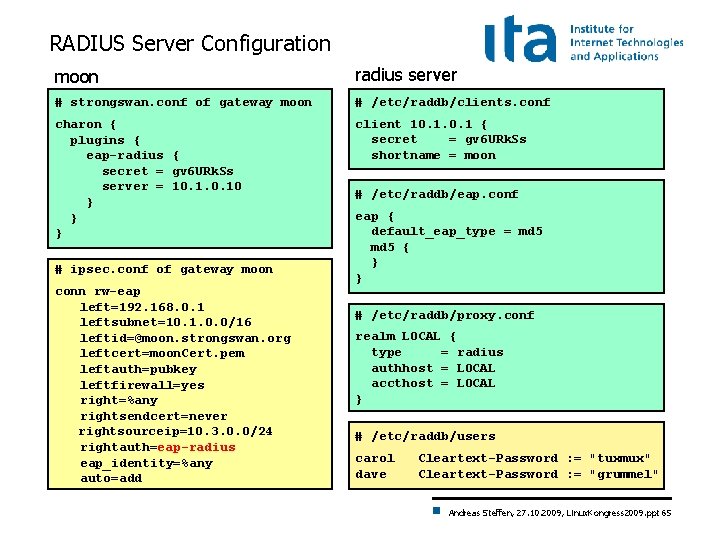
RADIUS Server Configuration moon radius server # strongswan. conf of gateway moon # /etc/raddb/clients. conf charon { plugins { eap-radius { secret = gv 6 URk. Ss server = 10. 10 } } } client 10. 1 { secret = gv 6 URk. Ss shortname = moon # ipsec. conf of gateway moon conn rw-eap left=192. 168. 0. 1 leftsubnet=10. 1. 0. 0/16 leftid=@moon. strongswan. org leftcert=moon. Cert. pem leftauth=pubkey leftfirewall=yes right=%any rightsendcert=never rightsourceip=10. 3. 0. 0/24 rightauth=eap-radius eap_identity=%any auto=add # /etc/raddb/eap. conf eap { default_eap_type = md 5 { } } # /etc/raddb/proxy. conf realm LOCAL { type = radius authhost = LOCAL accthost = LOCAL } # /etc/raddb/users carol dave Cleartext-Password : = "tuxmux" Cleartext-Password : = "grummel" Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 65
Linux Kongress 2009 Dresden strong. Swan Software Architecture Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 66
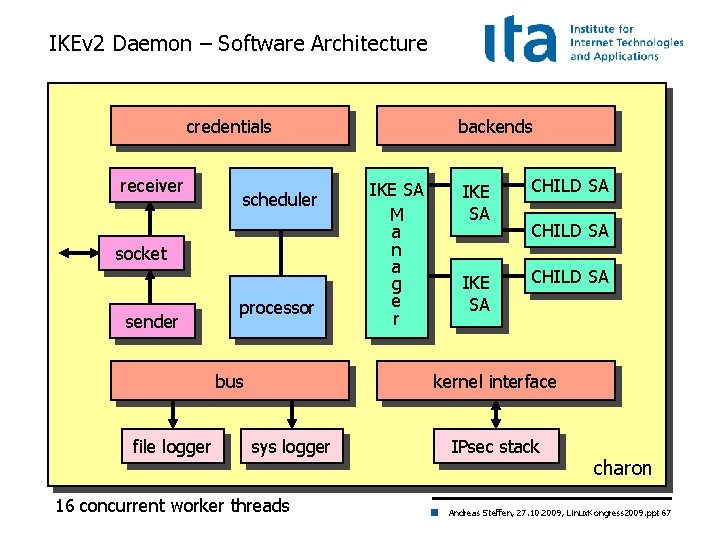
IKEv 2 Daemon – Software Architecture credentials receiver scheduler socket sender processor bus file logger backends IKE SA M a n a g e r IKE SA CHILD SA kernel interface sys logger 16 concurrent worker threads IPsec stack charon Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 67
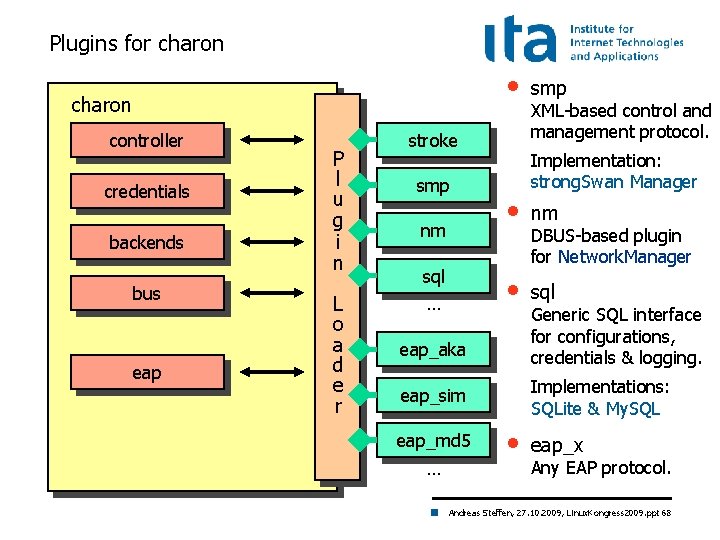
Plugins for charon • charon controller credentials backends bus eap P l u g i n L o a d e r stroke smp nm sql … Implementation: strong. Swan Manager nm • sql DBUS-based plugin for Network. Manager Generic SQL interface for configurations, credentials & logging. Implementations: SQLite & My. SQL eap_sim … XML-based control and management protocol. • eap_aka eap_md 5 smp • eap_x Any EAP protocol. Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 68
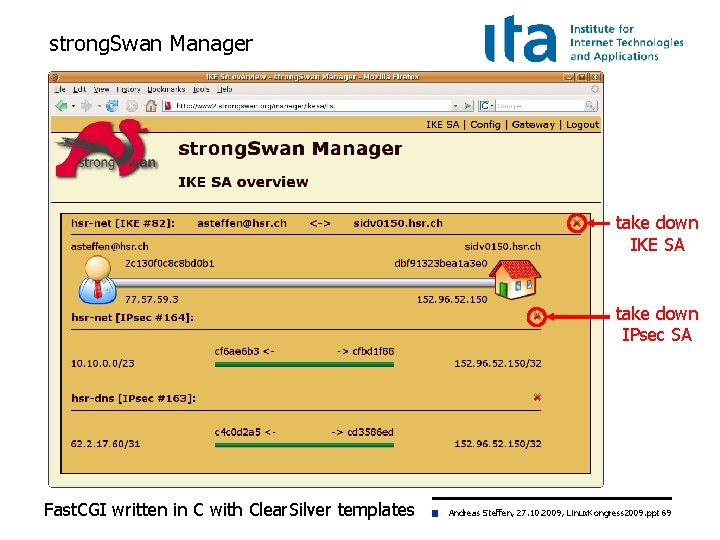
strong. Swan Manager take down IKE SA take down IPsec SA Fast. CGI written in C with Clear. Silver templates Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 69
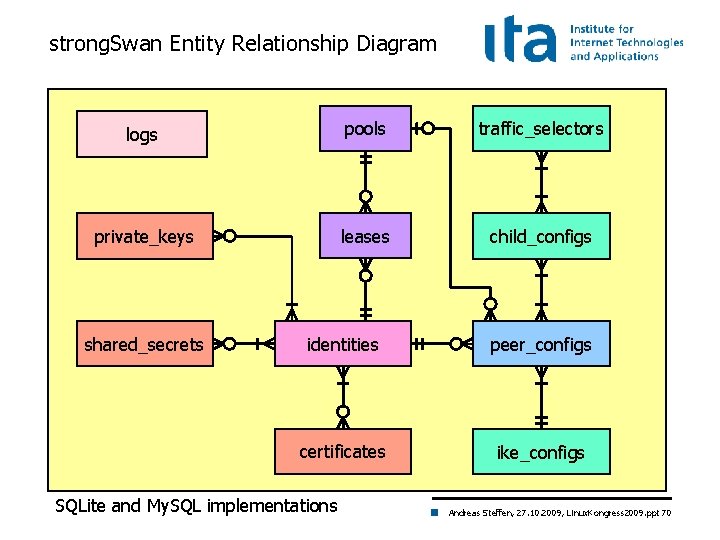
strong. Swan Entity Relationship Diagram logs pools traffic_selectors private_keys leases child_configs shared_secrets identities peer_configs certificates ike_configs SQLite and My. SQL implementations Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 70
Linux Kongress 2009 Dresden Cryptographic Plugins Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 71
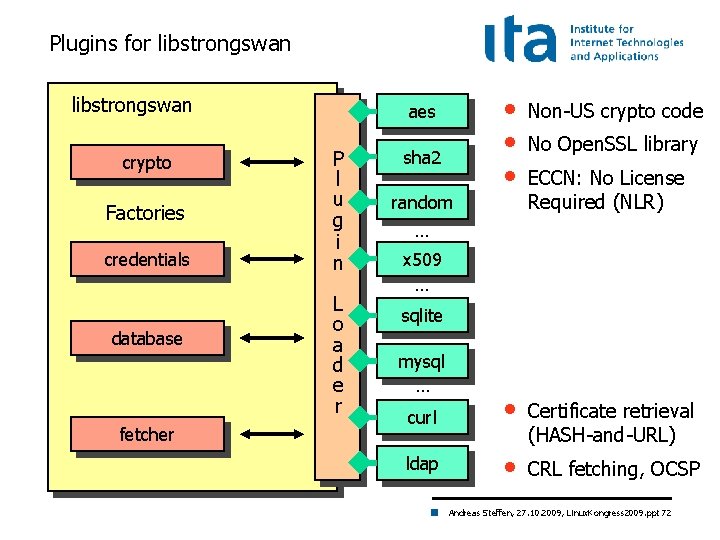
Plugins for libstrongswan crypto Factories credentials database fetcher • • • Non-US crypto code curl • Certificate retrieval (HASH-and-URL) ldap • CRL fetching, OCSP aes P l u g i n L o a d e r sha 2 random No Open. SSL library ECCN: No License Required (NLR) … x 509 … sqlite mysql … Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 72
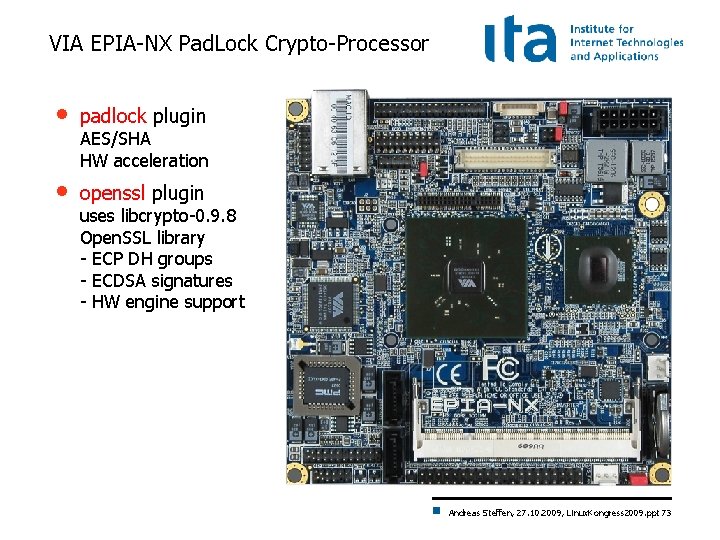
VIA EPIA-NX Pad. Lock Crypto-Processor • padlock plugin • openssl plugin AES/SHA HW acceleration uses libcrypto-0. 9. 8 Open. SSL library - ECP DH groups - ECDSA signatures - HW engine support Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 73
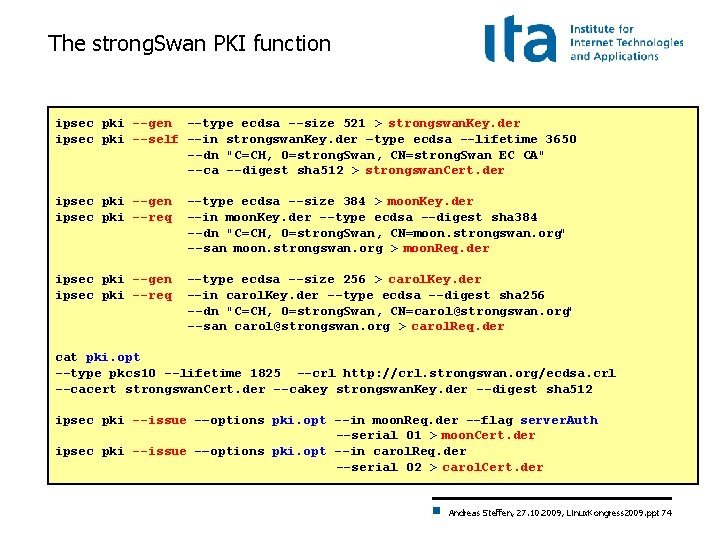
The strong. Swan PKI function ipsec pki --gen --type ecdsa --size 521 > strongswan. Key. der ipsec pki --self --in strongswan. Key. der –type ecdsa --lifetime 3650 --dn "C=CH, O=strong. Swan, CN=strong. Swan EC CA" --ca --digest sha 512 > strongswan. Cert. der ipsec pki --gen ipsec pki --req --type ecdsa --size 384 > moon. Key. der --in moon. Key. der --type ecdsa --digest sha 384 --dn "C=CH, O=strong. Swan, CN=moon. strongswan. org" --san moon. strongswan. org > moon. Req. der ipsec pki --gen ipsec pki --req --type ecdsa --size 256 > carol. Key. der --in carol. Key. der --type ecdsa --digest sha 256 --dn "C=CH, O=strong. Swan, CN=carol@strongswan. org" --san carol@strongswan. org > carol. Req. der cat pki. opt --type pkcs 10 --lifetime 1825 --crl http: //crl. strongswan. org/ecdsa. crl --cacert strongswan. Cert. der --cakey strongswan. Key. der --digest sha 512 ipsec pki --issue -–options pki. opt --in moon. Req. der --flag server. Auth --serial 01 > moon. Cert. der ipsec pki --issue -–options pki. opt --in carol. Req. der --serial 02 > carol. Cert. der Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 74
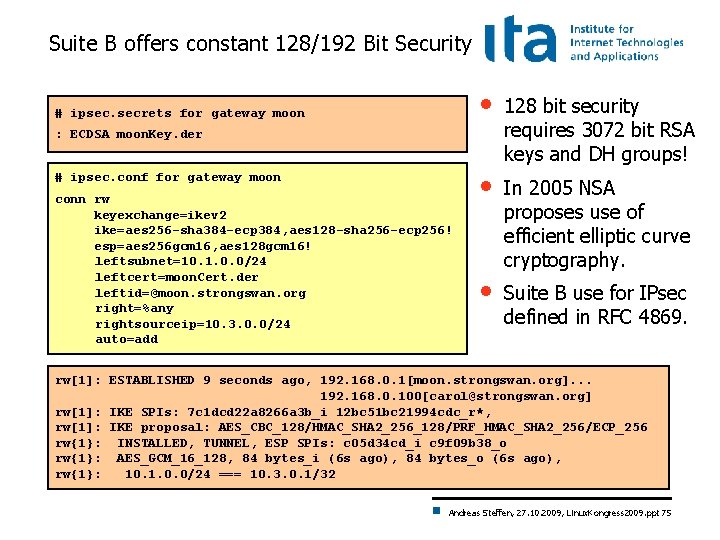
Suite B offers constant 128/192 Bit Security # ipsec. secrets for gateway moon • 128 bit security requires 3072 bit RSA keys and DH groups! • In 2005 NSA proposes use of efficient elliptic curve cryptography. • Suite B use for IPsec defined in RFC 4869. : ECDSA moon. Key. der # ipsec. conf for gateway moon conn rw keyexchange=ikev 2 ike=aes 256 -sha 384 -ecp 384, aes 128 -sha 256 -ecp 256! esp=aes 256 gcm 16, aes 128 gcm 16! leftsubnet=10. 1. 0. 0/24 leftcert=moon. Cert. der leftid=@moon. strongswan. org right=%any rightsourceip=10. 3. 0. 0/24 auto=add rw[1]: ESTABLISHED 9 seconds ago, 192. 168. 0. 1[moon. strongswan. org]. . . 192. 168. 0. 100[carol@strongswan. org] rw[1]: IKE SPIs: 7 c 1 dcd 22 a 8266 a 3 b_i 12 bc 51 bc 21994 cdc_r*, rw[1]: IKE proposal: AES_CBC_128/HMAC_SHA 2_256_128/PRF_HMAC_SHA 2_256/ECP_256 rw{1}: INSTALLED, TUNNEL, ESP SPIs: c 05 d 34 cd_i c 9 f 09 b 38_o rw{1}: AES_GCM_16_128, 84 bytes_i (6 s ago), 84 bytes_o (6 s ago), rw{1}: 10. 1. 0. 0/24 === 10. 3. 0. 1/32 Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 75
Linux Kongress 2009 Dresden High Availability using Cluster IP Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 76
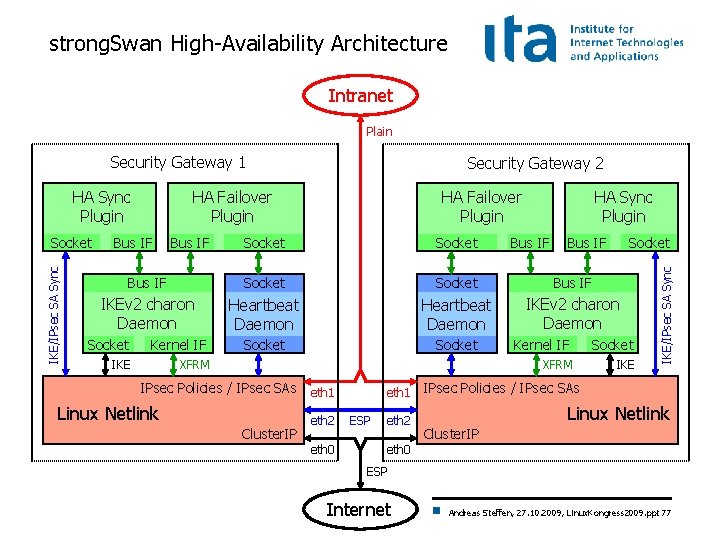
strong. Swan High-Availability Architecture Intranet Plain Security Gateway 1 IKE/IPsec SA Sync Socket HA Failover Plugin Bus IF HA Failover Plugin HA Sync Plugin Socket Bus IF IKEv 2 charon Daemon Heartbeat Daemon IKEv 2 charon Daemon Socket Kernel IF IKE XFRM IPsec Policies / IPsec SAs eth 1 Linux Netlink Cluster. IP eth 2 eth 0 eth 1 ESP eth 2 Bus IF Socket Kernel IF Socket XFRM IKE/IPsec SA Sync HA Sync Plugin Security Gateway 2 IPsec Policies / IPsec SAs Linux Netlink Cluster. IP eth 0 ESP Internet Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 77
Linux Kongress 2009 Dresden IKEv 2 Mediation Extension Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 78
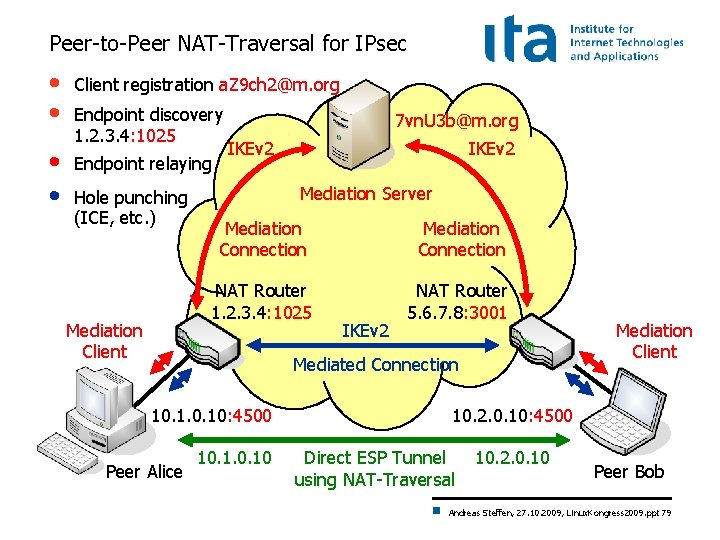
Peer-to-Peer NAT-Traversal for IPsec • • Client registration a. Z 9 ch 2@m. org Endpoint discovery 1. 2. 3. 4: 1025 Endpoint relaying Hole punching (ICE, etc. ) Mediation Client 7 vn. U 3 b@m. org IKEv 2 Mediation Server Mediation Connection NAT Router 1. 2. 3. 4: 1025 NAT Router 5. 6. 7. 8: 3001 IKEv 2 Mediated Connection 10. 10: 4500 Peer Alice 10. 10 Mediation Client 10. 2. 0. 10: 4500 Direct ESP Tunnel using NAT-Traversal 10. 2. 0. 10 Peer Bob Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 79
draft-brunner-ikev 2 -mediation released Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 80
Login at the strong. Swan Mediation Manager Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 81
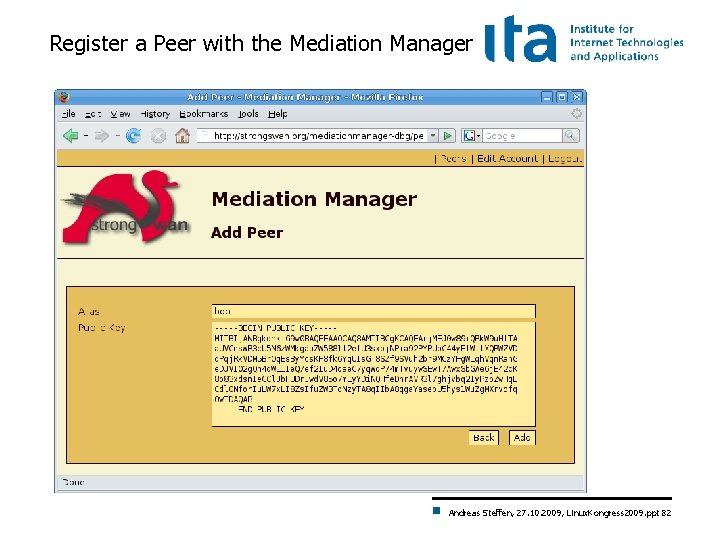
Register a Peer with the Mediation Manager Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 82
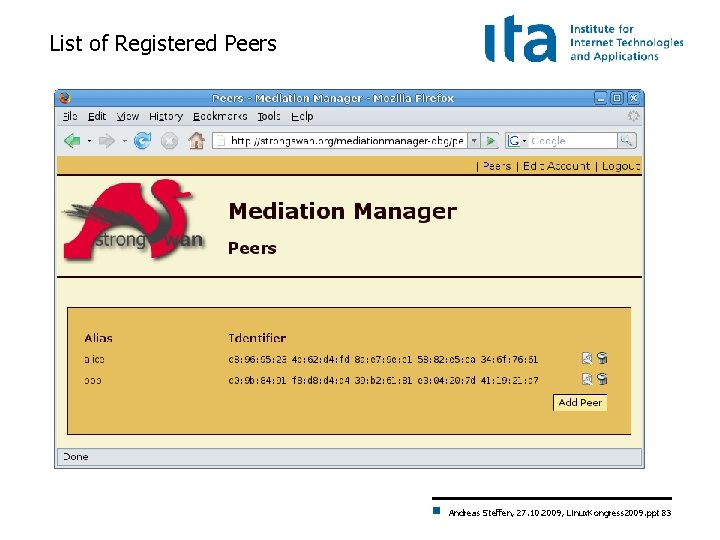
List of Registered Peers Andreas Steffen, 27. 10. 2009, Linux. Kongress 2009. ppt 83
- Slides: 83