Leverage Big Data in Cybersecurity Atos Prescriptive SOC
Leverage Big Data in Cybersecurity Atos Prescriptive SOC © Atos
Agenda Atos Prescriptive SOC: Intro Data Science in Cybersecurity Big Data: Connecting Everything © Atos
Prescriptive SOC
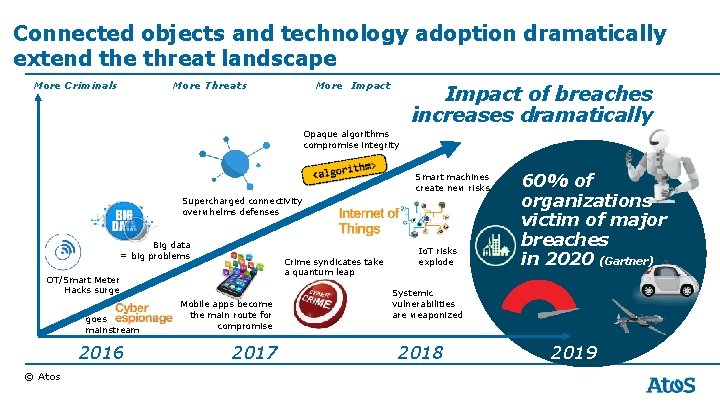
Connected objects and technology adoption dramatically extend the threat landscape More Criminals More Threats More Impact of breaches increases dramatically Opaque algorithms compromise integrity Smart machines create new risks Supercharged connectivity overwhelms defenses Big data = big problems Crime syndicates take a quantum leap OT/Smart Meter Hacks surge goes mainstream 2016 © Atos Mobile apps become the main route for compromise 2017 Io. T risks explode 60% of organizations victim of major breaches in 2020 (Gartner) Systemic vulnerabilities are weaponized 2018 2019
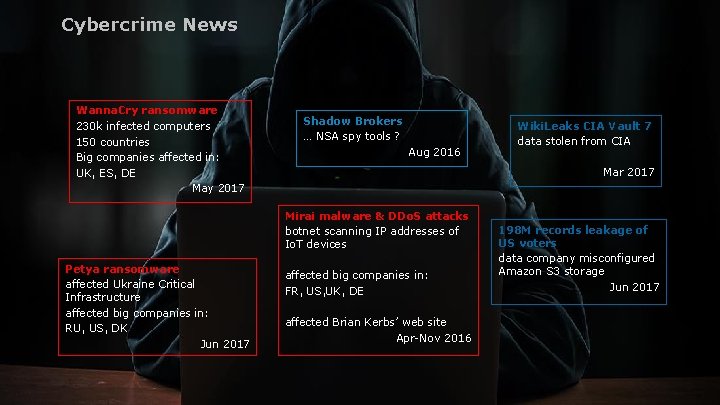
Cybercrime News Wanna. Cry ransomware 230 k infected computers 150 countries Big companies affected in: UK, ES, DE May 2017 Shadow Brokers DEFEND ASSESS … NSA spy tools ? Aug 2016 CX Integrated Innovation security Mirai malware & DDo. S attacks botnet scanning IP addresses of Io. T devices Petya ransomware affected big companies in: affected Ukraine Critical FR, US, UK, DE Infrastructure ENABLE GUARANTEE affected big companies in: affected Brian Kerbs’ web site RU, US, DK Apr-Nov 2016 Jun 2017 © Atos Wiki. Leaks CIA Vault 7 Situational data stolen from CIA Awareness Mar 2017 How to get ready for active defense? 198 M records leakage of US voters data company misconfigured Amazon S 3 storage Jun 2017
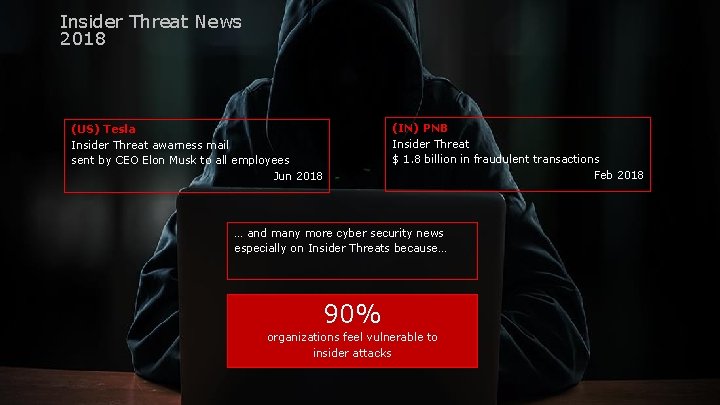
Insider Threat News 2018 (US) Tesla Insider Threat awarness mail sent by CEO Elon Musk to all employees Jun 2018 (IN) PNB Insider Threat $ 1. 8 billion in fraudulent transactions Feb 2018 … and many more cyber security news especially on Insider Threats because… 90% organizations feel vulnerable to insider attacks © Atos

Be ready for unexpected Shield your company with Security Solutions and. . …with Big Data and Data Science © Atos
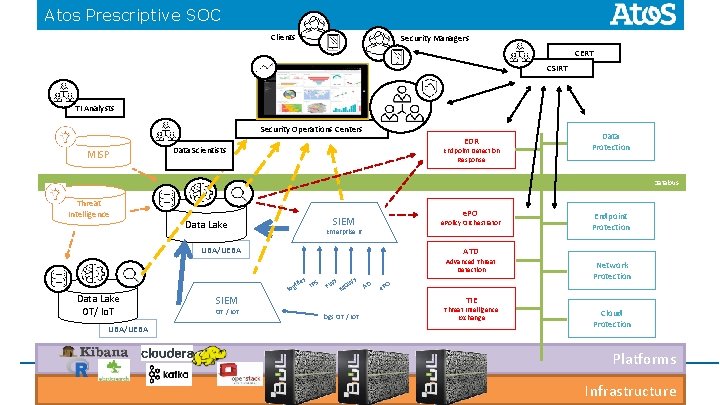
Atos Prescriptive SOC Clients Security Managers CERT CSIRT TI Analysts Security Operations Centers MISP EDR Data Scientists Endpoint Detection Response Data Protection Databus Threat Intelligence e. PO SIEM Data Lake e. Policy Orchestrator Enterprise IT UBA/UEBA ATD Advanced Threat Detection Data Lake OT/ Io. T UBA/UEBA s file IPS og SIEM OT / Io. T Endpoint Protection l s FW s W MG AD O Network Protection e. P TIE logs OT / Io. T Threat Intelligence Exchange Cloud Protection Platforms Infrastructure

Data Science in Cybersecurity
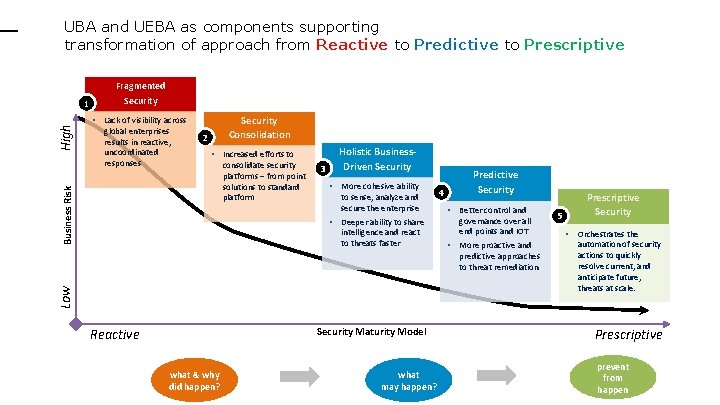
UBA and UEBA as components supporting transformation of approach from Reactive to Predictive to Prescriptive Security Consolidation • Lack of visibility across global enterprises results in reactive, uncoordinated responses 2 • Increased efforts to Business Risk High 1 Fragmented Security consolidate security platforms – from point solutions to standard platform 3 Holistic Business. Driven Security • More cohesive ability to sense, analyze and secure the enterprise • Deeper ability to share intelligence and react to threats faster 4 Predictive Security • Better control and governance over all end points and IOT • More proactive and Low predictive approaches to threat remediation Security Maturity Model Reactive what & why did happen? what may happen? 5 Prescriptive Security • Orchestrates the automation of security actions to quickly resolve current, and anticipate future, threats at scale. Prescriptive prevent from happen
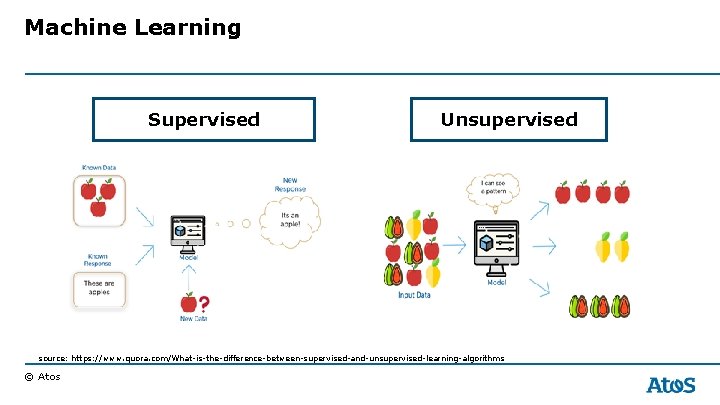
Machine Learning Supervised Unsupervised source: https: //www. quora. com/What-is-the-difference-between-supervised-and-unsupervised-learning-algorithms © Atos
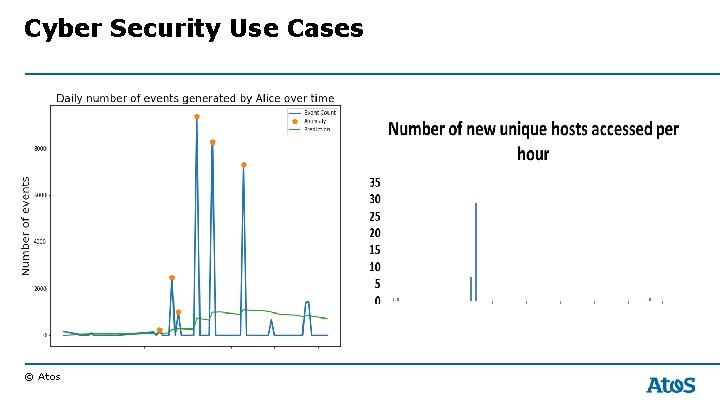
Cyber Security Use Cases © Atos
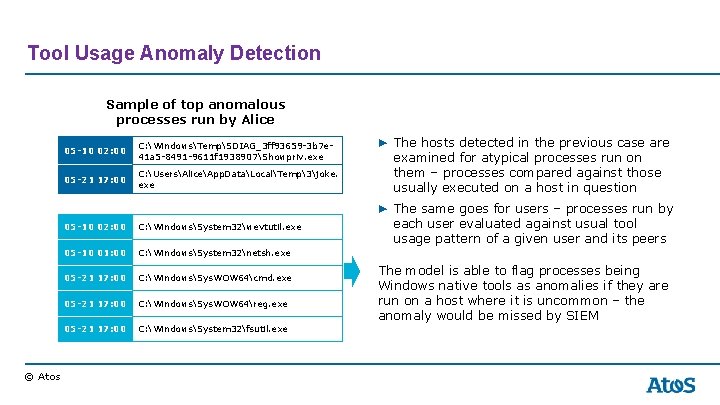
Tool Usage Anomaly Detection Sample of top anomalous processes run by Alice © Atos 05 -10 02: 00 C: WindowsTempSDIAG_3 ff 93659 -3 b 7 e 41 a 5 -8491 -9611 f 1938907Showpriv. exe 05 -21 17: 00 C: UsersAliceApp. DataLocalTemp3joke. exe 05 -10 02: 00 C: WindowsSystem 32wevtutil. exe 05 -10 01: 00 C: WindowsSystem 32netsh. exe 05 -21 17: 00 C: WindowsSys. WOW 64cmd. exe 05 -21 17: 00 C: WindowsSys. WOW 64reg. exe 05 -21 17: 00 C: WindowsSystem 32fsutil. exe ▶ The hosts detected in the previous case are examined for atypical processes run on them – processes compared against those usually executed on a host in question ▶ The same goes for users – processes run by each user evaluated against usual tool usage pattern of a given user and its peers The model is able to flag processes being Windows native tools as anomalies if they are run on a host where it is uncommon – the anomaly would be missed by SIEM

Big Data
© Atos 16
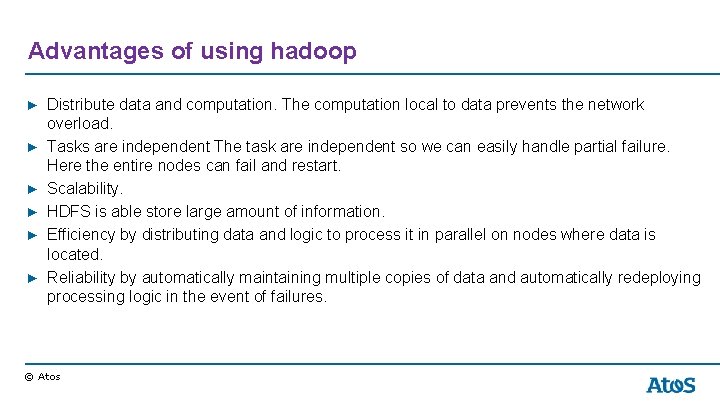
Advantages of using hadoop ▶ Distribute data and computation. The computation local to data prevents the network overload. ▶ Tasks are independent The task are independent so we can easily handle partial failure. Here the entire nodes can fail and restart. ▶ Scalability. ▶ HDFS is able store large amount of information. ▶ Efficiency by distributing data and logic to process it in parallel on nodes where data is located. ▶ Reliability by automatically maintaining multiple copies of data and automatically redeploying processing logic in the event of failures. © Atos
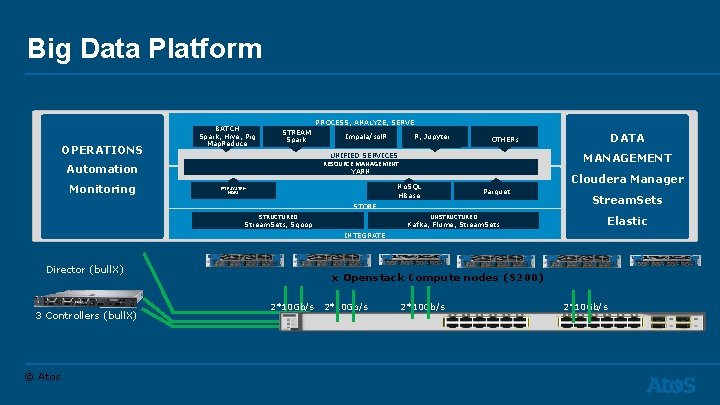
Big Data Platform OPERATIONS BATCH Spark, Hive, Pig Map. Reduce PROCESS, ANALYZE, SERVE STREAM Spark MANAGEMENT No. SQL HBase FILESYSTEM HDFS Cloudera Manager Parquet STORE STRUCTURED Stream. Sets, Sqoop DATA OTHERs UNIFIED SERVICES RESOURCE MANAGEMENT YARN Automation Monitoring R, Jupyter Impala/sol. R UNSTRUCTURED Kafka, Flume, Stream. Sets Elastic INTEGRATE Director (bull. X) 3 Controllers (bull. X) © Atos x Openstack Compute nodes (S 200) 2*10 Gb/s
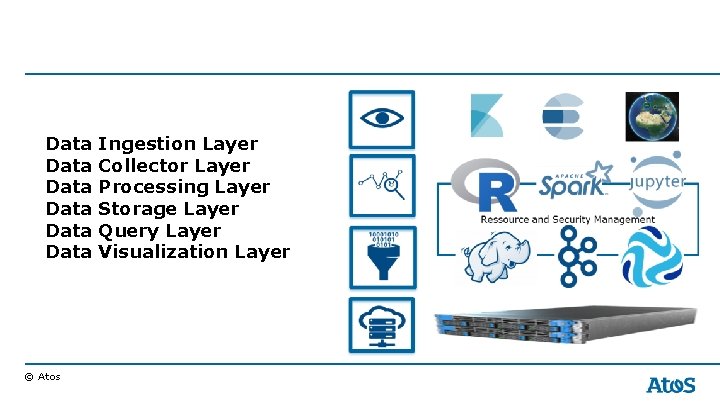
Data Data © Atos Ingestion Layer Collector Layer Processing Layer Storage Layer Query Layer Visualization Layer
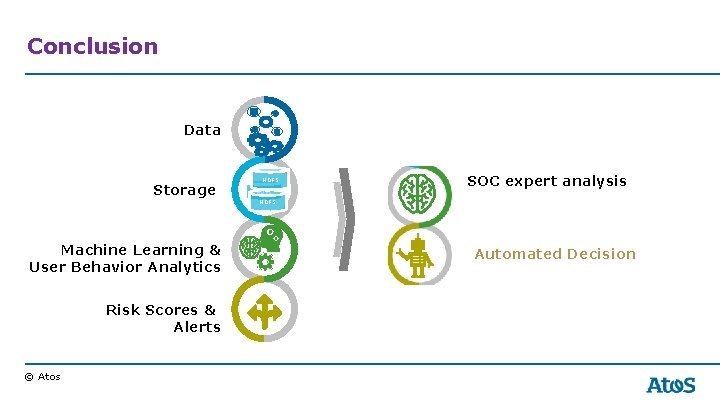
Conclusion Data Storage HDFS Machine Learning & User Behavior Analytics Risk Scores & Alerts © Atos SOC expert analysis HDFS SIEM Automated Decision
Thank you ! For more information please contact: T+40 356 221151 corina-stefania. nebela@atos. net Atos, the Atos logo, Atos Codex, Atos Consulting, Atos Worldgrid, Bull, Canopy, equens. Worldline, Unify, Worldline and Zero Email are registered trademarks of the Atos group. August 2018. © 2018 Atos. Confidential information owned by Atos, to be used by the recipient only. This document, or any part of it, may not be reproduced, copied, circulated and/or distributed nor quoted without prior written approval from Atos.

© Atos
- Slides: 22