Lecture 9 Other models Monitoring models l Reliability
Lecture 9 Other models: Monitoring models l Reliability and fault-tolerance models l Performance models. Scheduling policies. l Security models l 1
Student presentations and midterm I expect a progress report the week after the Spring break (March 18 – 24). The final project report is due the week before last. Midterm: two weeks from today – Material – Chapters 1, 2, and 3 up to the last lecture. l Open book. l 3 questions: 30 minutes l 2
Monitoring models A monitor could be a process responsible to establish the global state of a System. Intrusion – Heissenber’s uncertainty for quantum processes. Run: a total ordering of all events in the global history of a process. Cut: a subset of the local history of all processes. Frontier of a cut: the last event of every process in the cut. 3
Consistent and inconsistent cuts Consistent cut: a cut that agrees with causality. Inconsistent cut: violates causality. Causal history of an event: the smallest cut including the event. The snapshot algorithm of Chandy and Lamport. Checkpointing in parallel and distributed computing. 4
Consistent and inconsistent cuts 5
Causal history 6
The snapshot protocol (Chandy&Lamport) 7
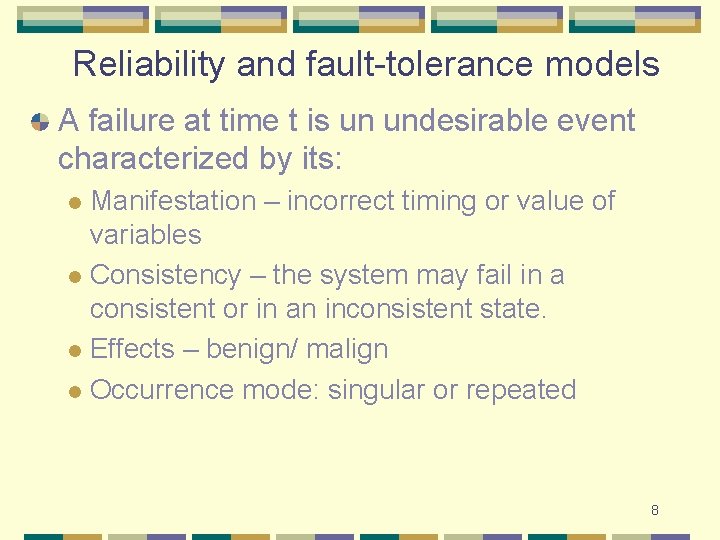
Reliability and fault-tolerance models A failure at time t is un undesirable event characterized by its: Manifestation – incorrect timing or value of variables l Consistency – the system may fail in a consistent or in an inconsistent state. l Effects – benign/ malign l Occurrence mode: singular or repeated l 8
![Failure modes for processes [P] and for communication channels [C] Crash - [P&C] Fail. Failure modes for processes [P] and for communication channels [C] Crash - [P&C] Fail.](http://slidetodoc.com/presentation_image_h2/8d6eabd9407cce58eebeb4174d0945c3/image-9.jpg)
Failure modes for processes [P] and for communication channels [C] Crash - [P&C] Fail. Stop - [P] Send Omissions - [P] Receive omissions - [P] General omissions – [P&C] Byzantine – [P&C] Arbitrary with message authentication - [P] Timing – [P] 9
Collective communication Broadcast and multicast. Applications: Routing in mobile ad hoc networks. l Routing in the Internet to disseminate topological information – flooding algorithms. l Used to achieve consensus. l Multicasting of audio and video streams to reduce the bandwidth. l Parallel algorithms – barrier synchronization. l 10
Collective communication 11
Properties of a broadcast algorithm (I) Validity – if a correct cc-process broadcasts a message m all correct cc-processes eventually deliver m. Agreement - if a correct cc-process delivers message m all correct cc-processes eventually deliver m. Integrity – every correct cc-process delivers m once and only if the message was broadcast by a cc-process 12
Properties of a broadcast algorithm (II) FIFO order – if a correct cc-process broadcasts a message m before m’ then no correct cc-processes delivers m’ unless it has previously delivered m. Causal order - if a correct cc-process broadcasts m that causally precedes m’ then no correct ccprocesses delivers m’ unless it has previously delivered m. Total order – if two correct cc-processes p and q both deliver messages m and m’ then p delivers m before m’ if and only if q delivers m before m’. 13
Broadcast primitives and their relationships 14
Performance models Resource sharing!!! Arrival process – distribution of inter-arrival times or arrival rates. Service process – distribution of service times or inter-departure times. Number of servers Quantities of interest: l l l Time in system, T Waiting time W Number in system, N Little’s law: N = T 15

16
Performance models Types of systems Deterministic D/D/1 l Markov arrival, Markov service - M/M/1 l Markov arrival, general service – M/G/1 l Batch arrival. l Server utilization : ratio of arrival rate to service rate. Stability: <= 1 necessary but not sufficient Time in system is finite l Number in system is finite l 17
Performance models When utilization tends to 1 time in system becomes unbounded. Network congestion. 18

19
20
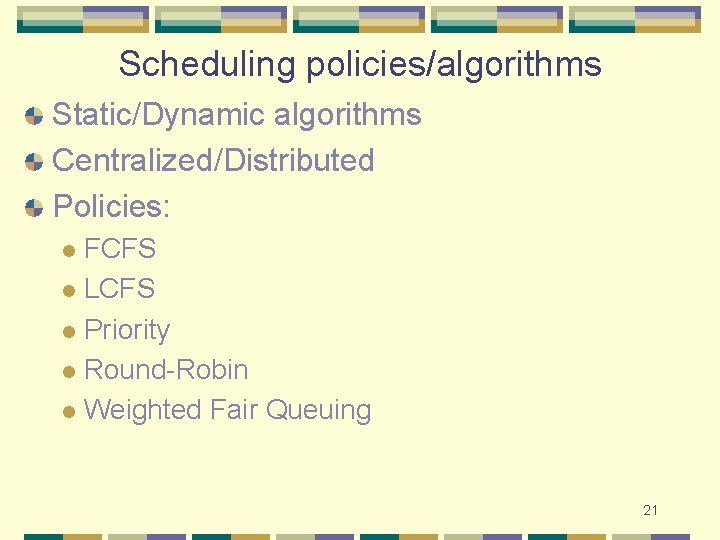
Scheduling policies/algorithms Static/Dynamic algorithms Centralized/Distributed Policies: FCFS l LCFS l Priority l Round-Robin l Weighted Fair Queuing l 21
Service policies for the server with vacation model Exhaustive Gated Semi-gated K-limitted 22
Scheduling on a grid Resources under the control of different administrative authorities. Resource reservations. Market-based scheduling algorithms. 23
Scheduling on a grid 24
Security models Problems and solutions: Confidentiality encription l Authentication authentication services l Authorization (controlled access to system resources) access control l 25
Secret key and public key cryptography 26
Major challenges in distributed systems Concurrency Mobility 27
28
- Slides: 28