Lecture 9 Cryptographic Authentication objectives and classification oneway
Lecture 9: Cryptographic Authentication • objectives and classification • one-way – secret key – public key • mutual – secret key – public key • establishing session key 1
Authentication Objectives and Classification • Objectives – Authentication (what was that again? ) • one-way • mutual – Immunity from attacks – efficiency: minimum number of messages exchanged – bootstrapping a session: establishing a session key • types of authentication – password authentication (authenticating humans or machines on their behalf) • what’s wrong with it? – cryptographic challenge-response • secret key • public key 2
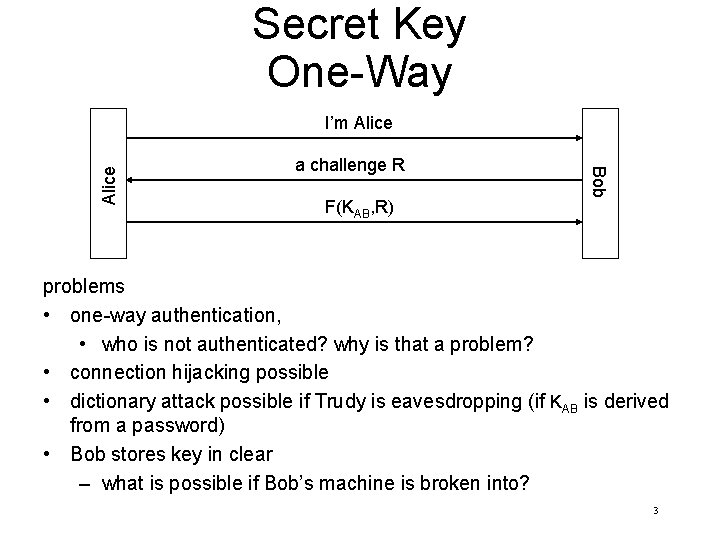
Secret Key One-Way a challenge R F(KAB, R) Bob Alice I’m Alice problems • one-way authentication, • who is not authenticated? why is that a problem? • connection hijacking possible • dictionary attack possible if Trudy is eavesdropping (if KAB is derived from a password) • Bob stores key in clear – what is possible if Bob’s machine is broken into? 3
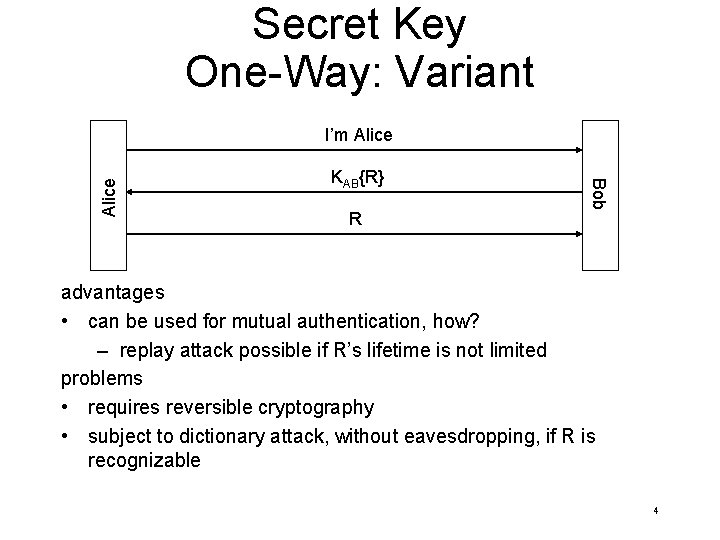
Secret Key One-Way: Variant KAB{R} R Bob Alice I’m Alice advantages • can be used for mutual authentication, how? – replay attack possible if R’s lifetime is not limited problems • requires reversible cryptography • subject to dictionary attack, without eavesdropping, if R is recognizable 4
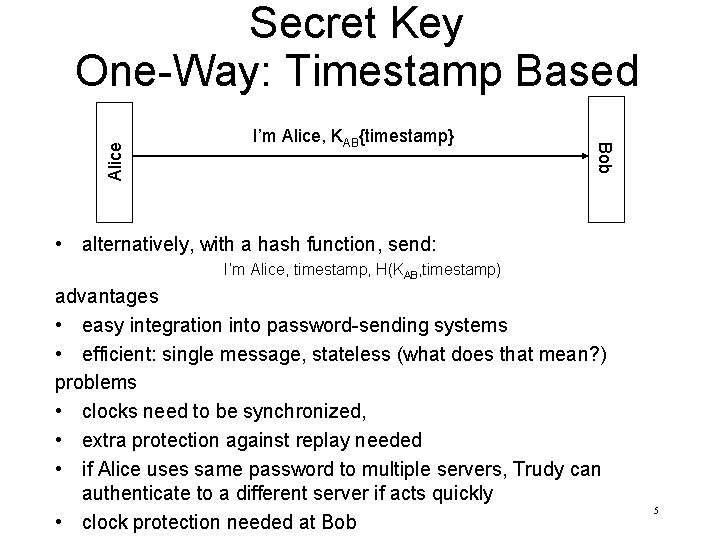
I’m Alice, KAB{timestamp} Bob Alice Secret Key One-Way: Timestamp Based • alternatively, with a hash function, send: I’m Alice, timestamp, H(KAB, timestamp) advantages • easy integration into password-sending systems • efficient: single message, stateless (what does that mean? ) problems • clocks need to be synchronized, • extra protection against replay needed • if Alice uses same password to multiple servers, Trudy can authenticate to a different server if acts quickly • clock protection needed at Bob 5
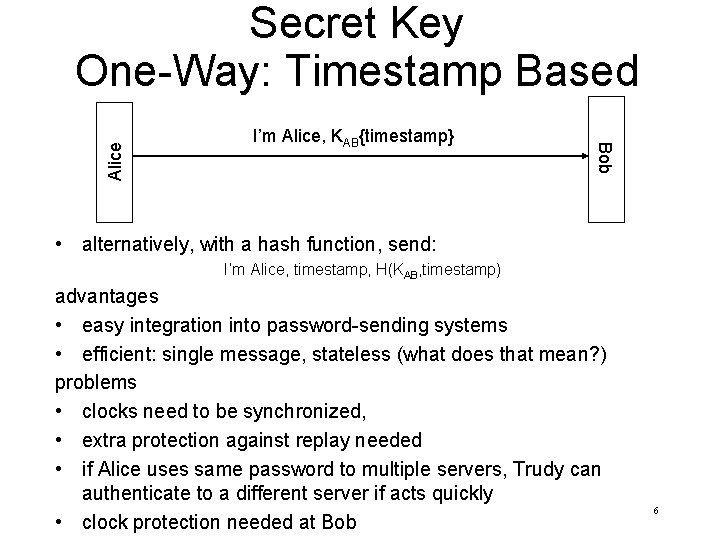
I’m Alice, KAB{timestamp} Bob Alice Secret Key One-Way: Timestamp Based • alternatively, with a hash function, send: I’m Alice, timestamp, H(KAB, timestamp) advantages • easy integration into password-sending systems • efficient: single message, stateless (what does that mean? ) problems • clocks need to be synchronized, • extra protection against replay needed • if Alice uses same password to multiple servers, Trudy can authenticate to a different server if acts quickly • clock protection needed at Bob 6
![Public Key, One-Way R [R]A Bob Alice I’m Alice where []A is Alice’s signature. Public Key, One-Way R [R]A Bob Alice I’m Alice where []A is Alice’s signature.](http://slidetodoc.com/presentation_image_h/a4f83e46f921a97f8c4dc2cb7dc5d1c2/image-7.jpg)
Public Key, One-Way R [R]A Bob Alice I’m Alice where []A is Alice’s signature. Can this be done with encryption? problem • Trudy can get Alice to sign/decrypt any text he chooses, how? – why is decryption useful? solution • don’t use the same key for authentication and other purposes • give structure (formatting) (e. g. type field) to challenge so it cannot be mistaken for other things 7
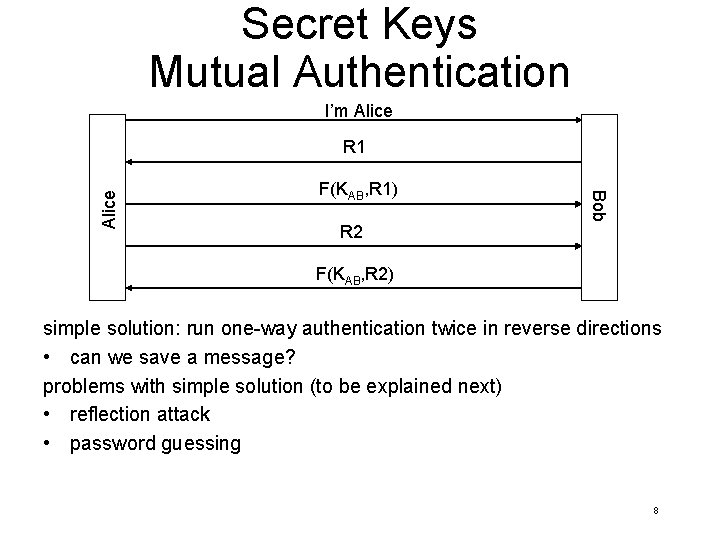
Secret Keys Mutual Authentication I’m Alice F(KAB, R 1) Bob Alice R 1 R 2 F(KAB, R 2) simple solution: run one-way authentication twice in reverse directions • can we save a message? problems with simple solution (to be explained next) • reflection attack • password guessing 8
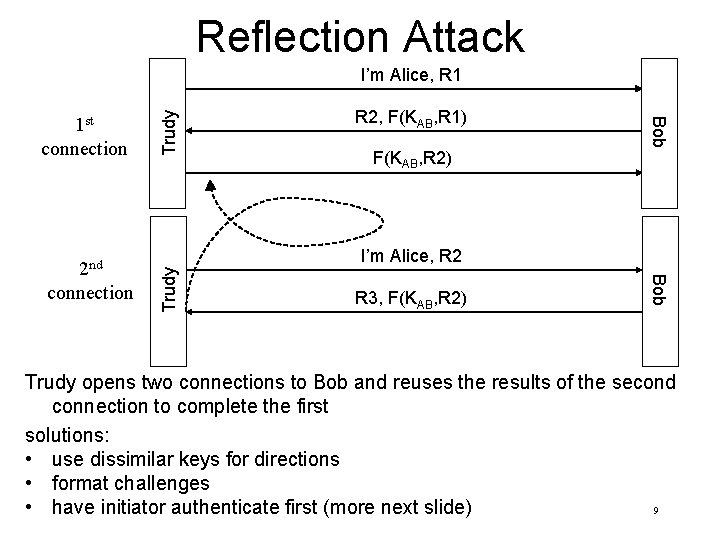
Reflection Attack F(KAB, R 2) Trudy I’m Alice, R 2 R 3, F(KAB, R 2) Bob 2 nd connection R 2, F(KAB, R 1) Bob 1 st connection Trudy I’m Alice, R 1 Trudy opens two connections to Bob and reuses the results of the second connection to complete the first solutions: • use dissimilar keys for directions • format challenges 9 • have initiator authenticate first (more next slide)
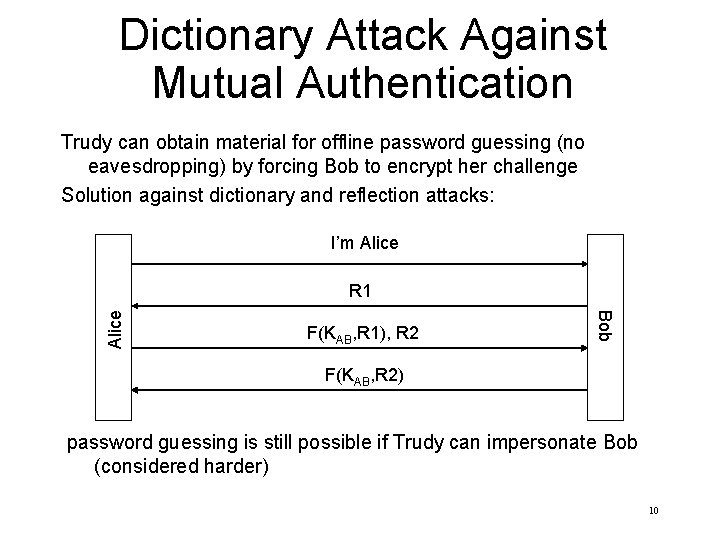
Dictionary Attack Against Mutual Authentication Trudy can obtain material for offline password guessing (no eavesdropping) by forcing Bob to encrypt her challenge Solution against dictionary and reflection attacks: I’m Alice F(KAB, R 1), R 2 Bob Alice R 1 F(KAB, R 2) password guessing is still possible if Trudy can impersonate Bob (considered harder) 10
![I’m Alice, [{R}B]A Bob Alice Mutual Authentication Public Keys • [] – signature, {} I’m Alice, [{R}B]A Bob Alice Mutual Authentication Public Keys • [] – signature, {}](http://slidetodoc.com/presentation_image_h/a4f83e46f921a97f8c4dc2cb7dc5d1c2/image-11.jpg)
I’m Alice, [{R}B]A Bob Alice Mutual Authentication Public Keys • [] – signature, {} – encryption • why does Alice sign R? • (minor) problem, – assume R is going to be used as conversation key, if Trudy records the conversation and, after the conversation is over, overruns Bob (breaks into Bob’s computer and learns his secrets), she can decode the conversation • why overrunning Alice won’t help? – we already know the solution, what is it? 11
Establishing Session Key secret keys • knowing , KAB and R modify them in some way, ex: (KAB+1){R} – why not KAB{R}? – KAB{R+1} ? public keys • send additional random nonces(a number that is used only once) {R}A , {R}B and use them to derive a session key. 12
- Slides: 12