Lecture 5 One Fish Two Fish Blowfish Blue
Lecture 5: One Fish, Two Fish, Blowfish, Blue Fish The algorithm might look haphazard, but we did everything for a reason. Nothing is in Twofish by chance. Anything in the algorithm that we couldn't justify, we removed. The result is a lean, mean algorithm that is strong and conceptually simple. Bruce Schneier CS 551: Security and Privacy David Evans University of Virginia 30 Aug 2000 University of Virginia CS 551 http: //www. cs. virginia. edu/~evans Computer Science
Menu • Clipper • AES Program • AES Candidates – RC 6 – Blowfish 30 Aug 2000 University of Virginia CS 551 2
Problem Set 1 30 Aug 2000 University of Virginia CS 551 3
Breaking Grades File • Not in my office or any UVA computer • Home PC: C: cs 551grades. txt (encrypted) • Adelphia Cable Modem • Project proposals are web pages • My browser is set to disallow Active. X, allow Java and Java. Script 30 Aug 2000 University of Virginia CS 551 4
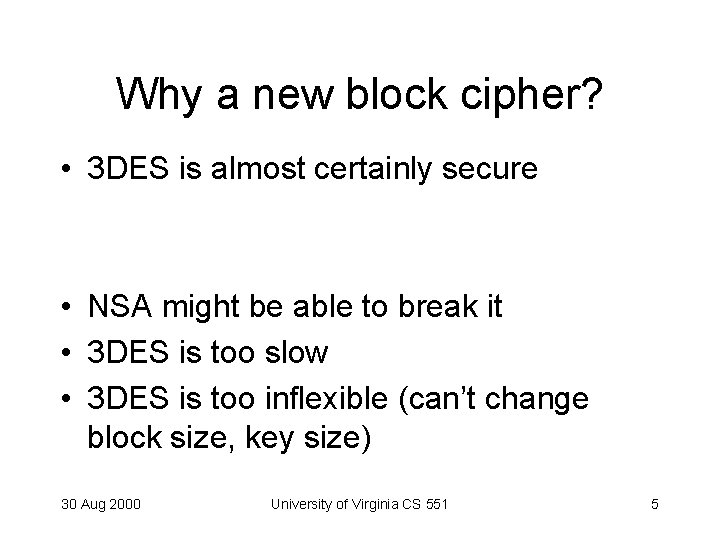
Why a new block cipher? • 3 DES is almost certainly secure • NSA might be able to break it • 3 DES is too slow • 3 DES is too inflexible (can’t change block size, key size) 30 Aug 2000 University of Virginia CS 551 5
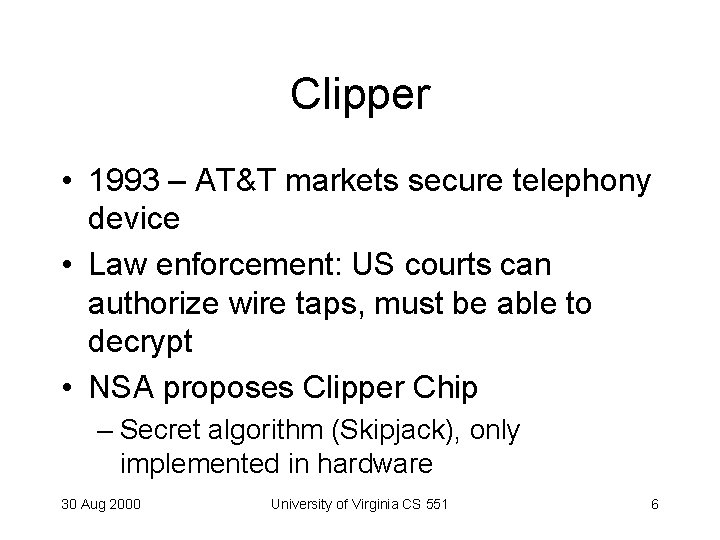
Clipper • 1993 – AT&T markets secure telephony device • Law enforcement: US courts can authorize wire taps, must be able to decrypt • NSA proposes Clipper Chip – Secret algorithm (Skipjack), only implemented in hardware 30 Aug 2000 University of Virginia CS 551 6
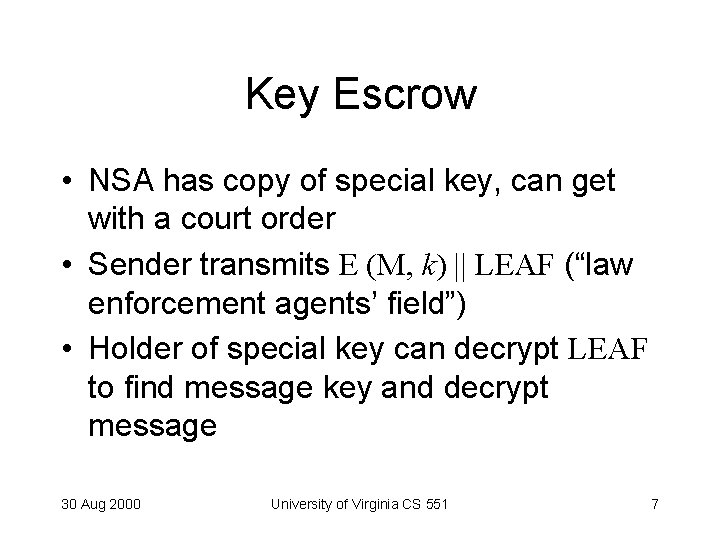
Key Escrow • NSA has copy of special key, can get with a court order • Sender transmits E (M, k) || LEAF (“law enforcement agents’ field”) • Holder of special key can decrypt LEAF to find message key and decrypt message 30 Aug 2000 University of Virginia CS 551 7
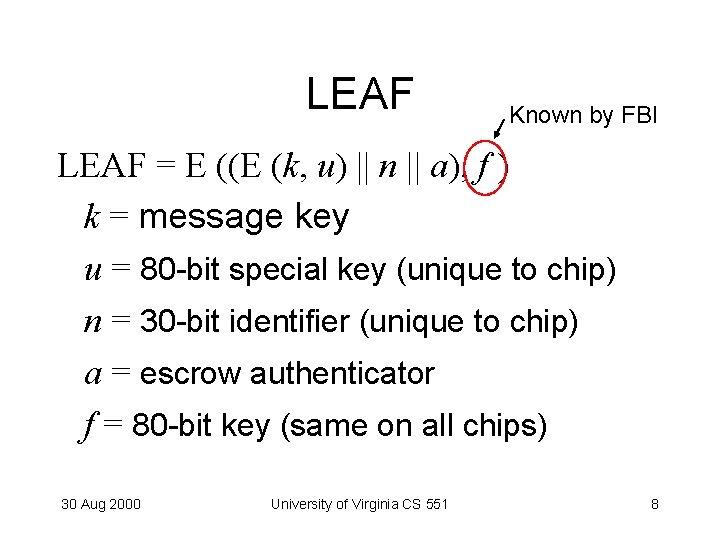
LEAF Known by FBI LEAF = E ((E (k, u) || n || a), f ) k = message key u = 80 -bit special key (unique to chip) n = 30 -bit identifier (unique to chip) a = escrow authenticator f = 80 -bit key (same on all chips) 30 Aug 2000 University of Virginia CS 551 8
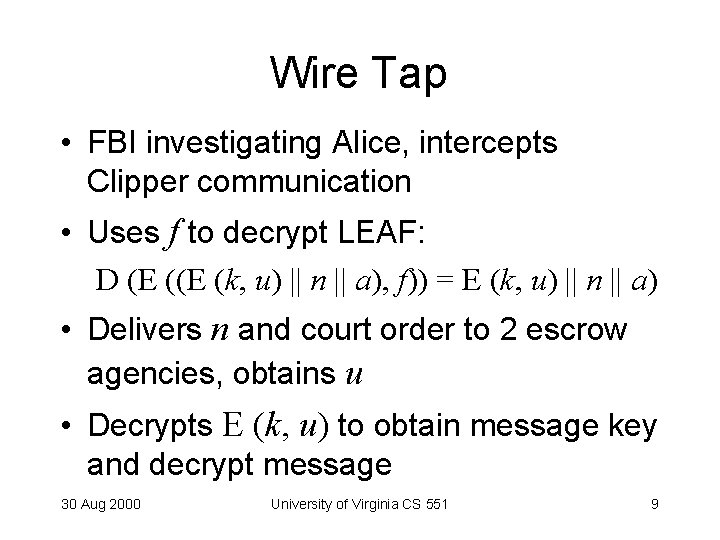
Wire Tap • FBI investigating Alice, intercepts Clipper communication • Uses f to decrypt LEAF: D (E (k, u) || n || a), f)) = E (k, u) || n || a) • Delivers n and court order to 2 escrow agencies, obtains u • Decrypts E (k, u) to obtain message key and decrypt message 30 Aug 2000 University of Virginia CS 551 9
Two Escrow Agencies • Proposal didn’t specify who (one probably NSA) • Divide u so neither one can decrypt messages on their own (even if they obtain f) • One gets u X, other gets X 30 Aug 2000 University of Virginia CS 551 10
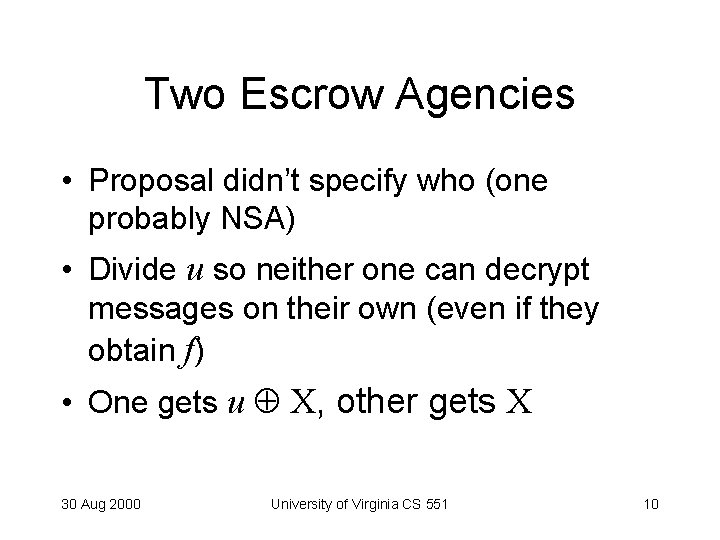
Clipper Security • How do you prevent criminals from transmitting wrong LEAF? – Use a checksum • But, easy to find LEAF with right checksum with brute-force attack – NSA solution: put it in hardware, inspect all Clipper devices • Still vulnerable to out-of-the box device 30 Aug 2000 University of Virginia CS 551 11
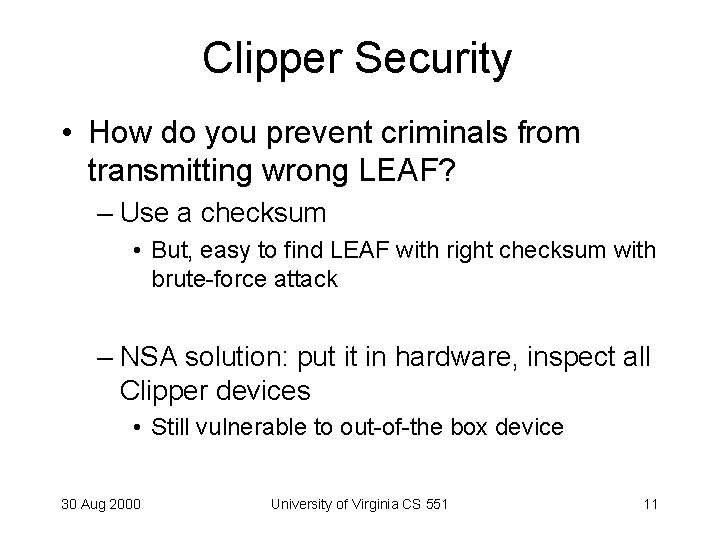
Clipper Politics • Not widely adopted, administration backed down – Secret algorithm – Public relations disaster • Didn’t involve academic cryptographers early • Proposal was rushed, in particular hadn’t figured out who would be escrow agencies • Lessons learned well for AES process • See http: //www. eff. org/pub/Privacy/Key_escrow/Clipper/ 30 Aug 2000 University of Virginia CS 551 12
AES • 1996: NIST initiates program to choose Advanced Encryption Standard to replace DES • Requests algorithm submissions: 15 • Requirements: – – Secure for next 50 -100 years Performance: faster than 3 DES Support 128, 192 and 256 bit keys Must be a block cipher 30 Aug 2000 University of Virginia CS 551 13
AES Process • Open Design – DES: design criteria for S-boxes kept secret • Many decent choices – DES: only one acceptable algorithm • Public cryptanalysis efforts before choice – Heavy involvements of academic community, all leading public cryptographers • Very conservative: 4 year+ process 30 Aug 2000 University of Virginia CS 551 14
AES Round 1 • 15 submissions accepted • Weak ciphers quickly eliminated – Magenta broken at conference! • 5 finalists selected – Security v. performance is main tradeoff – With enough complexity, can make anything secure, challenge is to make something simple secure 30 Aug 2000 University of Virginia CS 551 15
AES Finalists • MARS (IBM) • RC 6 (Rivest, et. al. ) • Rijndael (top Belgium cryptographers) • Serpent (Anderson, Biham, Knudsen) • Twofish (Schneier, et. al. ) 30 Aug 2000 University of Virginia CS 551 16
From RC 5 to RC 6 in seven easy steps From Rivest’s RC 6 talk, http: //www. rsasecurity. com/rsalabs/aes/ 30 Aug 2000 University of Virginia CS 551
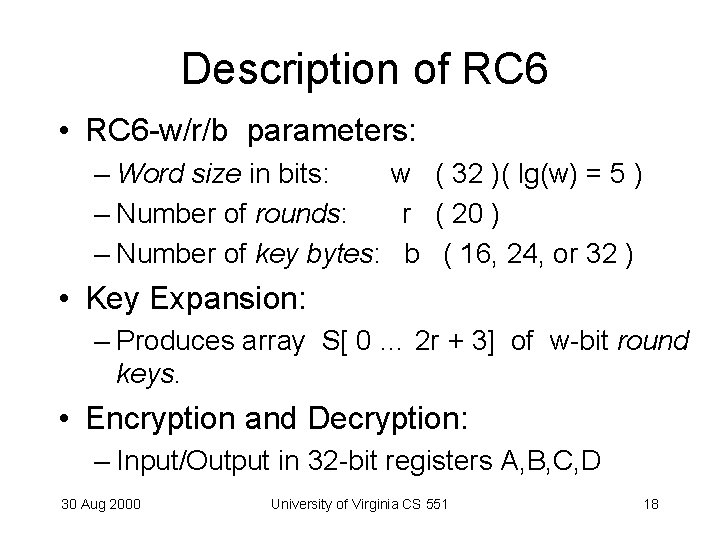
Description of RC 6 • RC 6 -w/r/b parameters: – Word size in bits: w ( 32 )( lg(w) = 5 ) – Number of rounds: r ( 20 ) – Number of key bytes: b ( 16, 24, or 32 ) • Key Expansion: – Produces array S[ 0 … 2 r + 3] of w-bit round keys. • Encryption and Decryption: – Input/Output in 32 -bit registers A, B, C, D 30 Aug 2000 University of Virginia CS 551 18
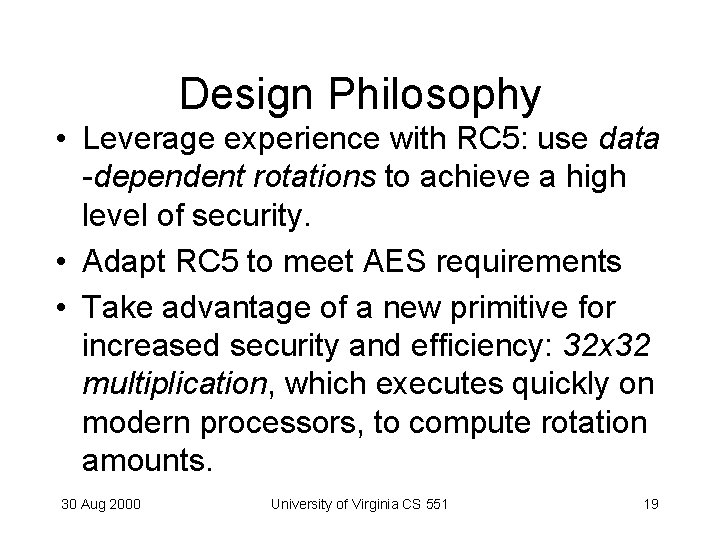
Design Philosophy • Leverage experience with RC 5: use data -dependent rotations to achieve a high level of security. • Adapt RC 5 to meet AES requirements • Take advantage of a new primitive for increased security and efficiency: 32 x 32 multiplication, which executes quickly on modern processors, to compute rotation amounts. 30 Aug 2000 University of Virginia CS 551 19
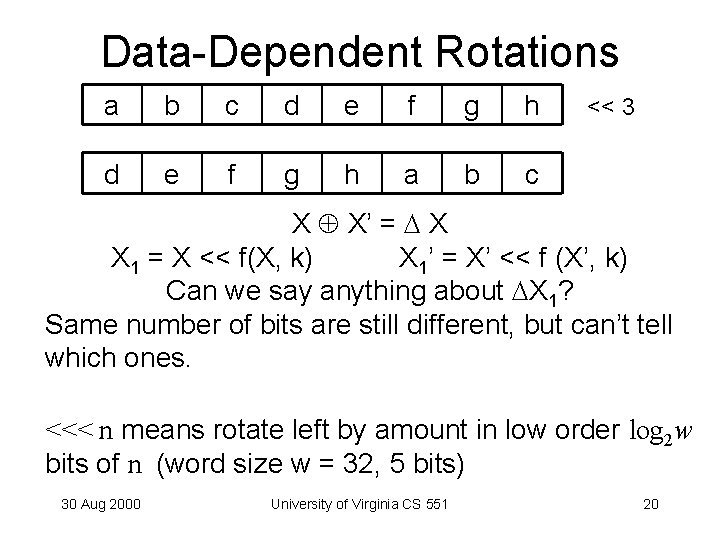
Data-Dependent Rotations a b c d e f g h a b c << 3 X X’ = X X 1 = X << f(X, k) X 1’ = X’ << f (X’, k) Can we say anything about X 1? Same number of bits are still different, but can’t tell which ones. <<< n means rotate left by amount in low order log 2 w bits of n (word size w = 32, 5 bits) 30 Aug 2000 University of Virginia CS 551 20
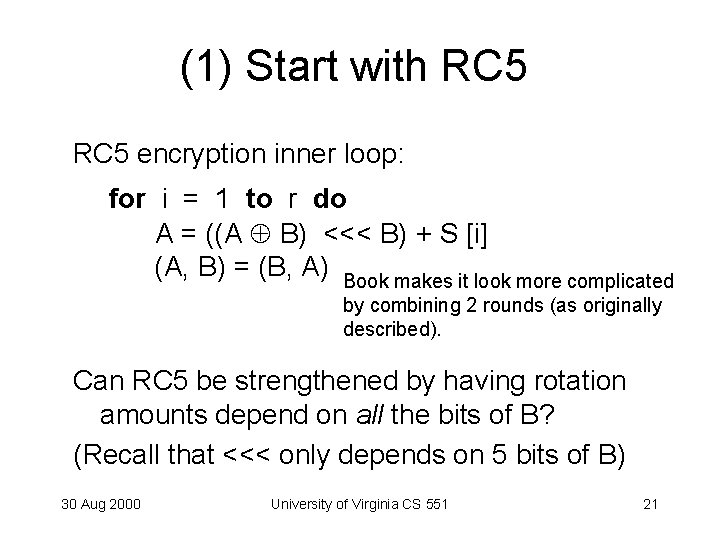
(1) Start with RC 5 encryption inner loop: for i = 1 to r do A = ((A B) <<< B) + S [i] (A, B) = (B, A) Book makes it look more complicated by combining 2 rounds (as originally described). Can RC 5 be strengthened by having rotation amounts depend on all the bits of B? (Recall that <<< only depends on 5 bits of B) 30 Aug 2000 University of Virginia CS 551 21
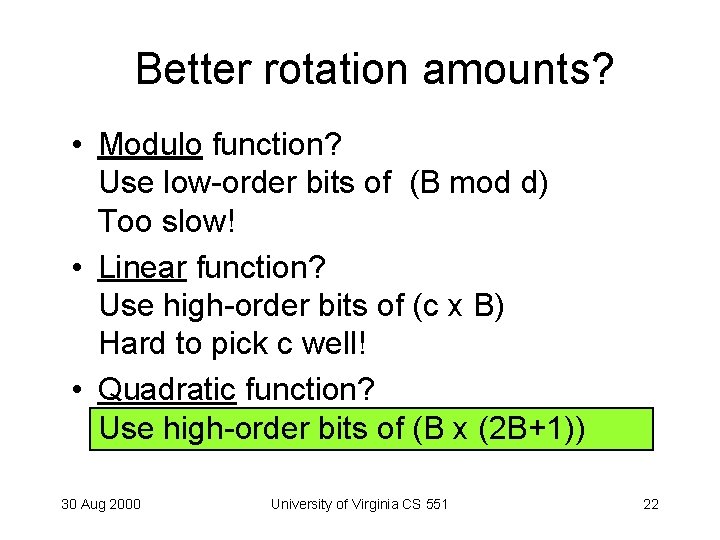
Better rotation amounts? • Modulo function? Use low-order bits of (B mod d) Too slow! • Linear function? Use high-order bits of (c x B) Hard to pick c well! • Quadratic function? Use high-order bits of (B x (2 B+1)) 30 Aug 2000 University of Virginia CS 551 22
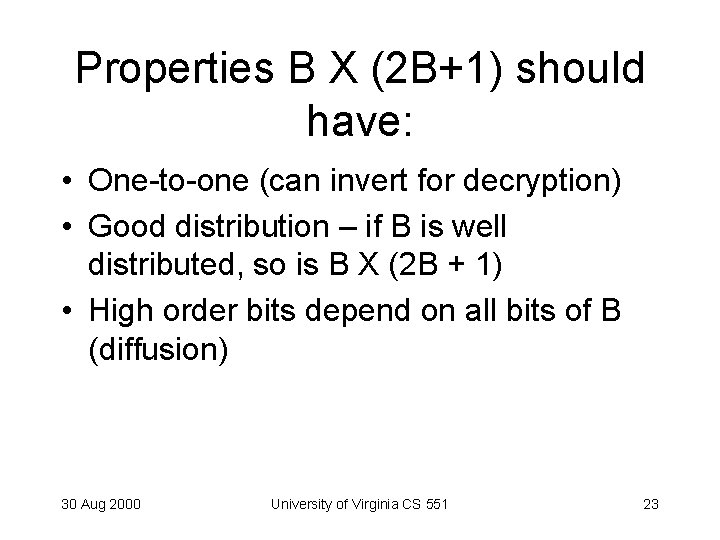
Properties B X (2 B+1) should have: • One-to-one (can invert for decryption) • Good distribution – if B is well distributed, so is B X (2 B + 1) • High order bits depend on all bits of B (diffusion) 30 Aug 2000 University of Virginia CS 551 23
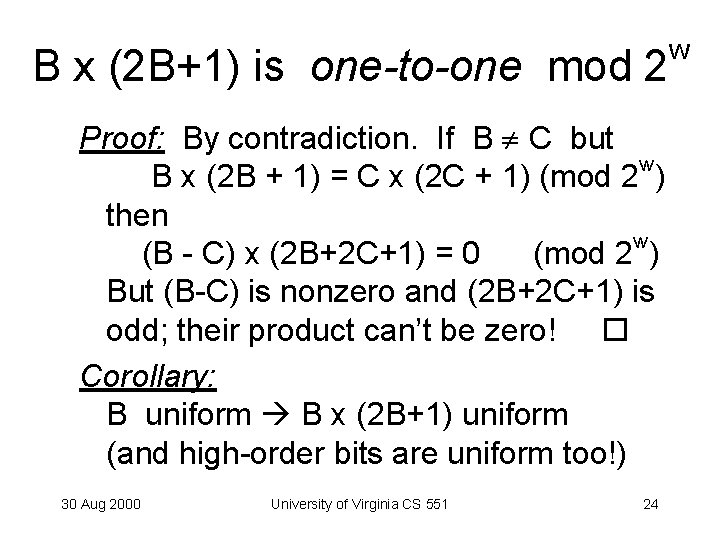
B x (2 B+1) is one-to-one mod 2 Proof: By contradiction. If B C but w B x (2 B + 1) = C x (2 C + 1) (mod 2 ) then w (B - C) x (2 B+2 C+1) = 0 (mod 2 ) But (B-C) is nonzero and (2 B+2 C+1) is odd; their product can’t be zero! Corollary: B uniform B x (2 B+1) uniform (and high-order bits are uniform too!) 30 Aug 2000 University of Virginia CS 551 24 w
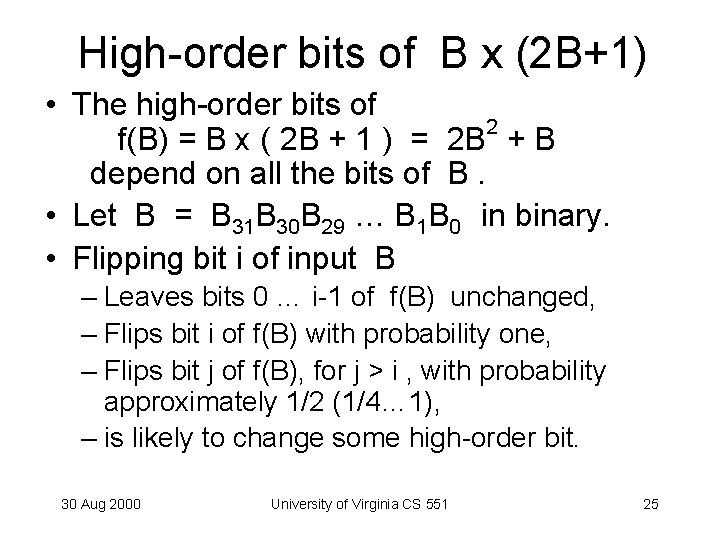
High-order bits of B x (2 B+1) • The high-order bits of 2 f(B) = B x ( 2 B + 1 ) = 2 B + B depend on all the bits of B. • Let B = B 31 B 30 B 29 … B 1 B 0 in binary. • Flipping bit i of input B – Leaves bits 0 … i-1 of f(B) unchanged, – Flips bit i of f(B) with probability one, – Flips bit j of f(B), for j > i , with probability approximately 1/2 (1/4… 1), – is likely to change some high-order bit. 30 Aug 2000 University of Virginia CS 551 25
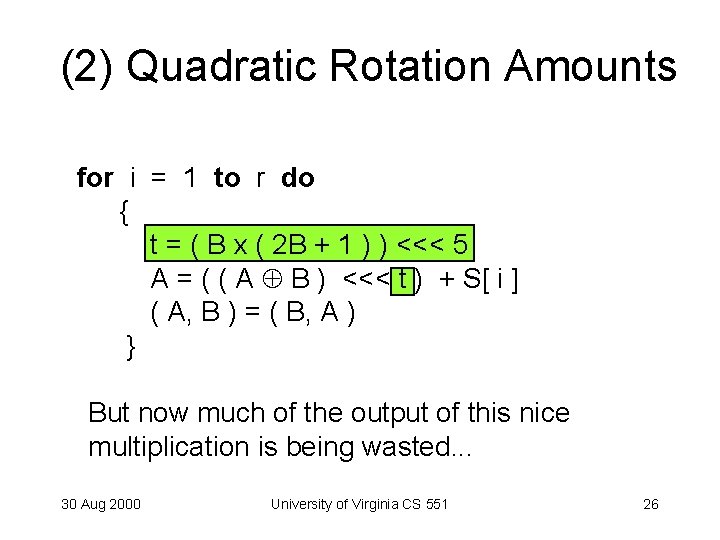
(2) Quadratic Rotation Amounts for i = 1 to r do { t = ( B x ( 2 B + 1 ) ) <<< 5 A = ( ( A B ) <<< t ) + S[ i ] ( A, B ) = ( B, A ) } But now much of the output of this nice multiplication is being wasted. . . 30 Aug 2000 University of Virginia CS 551 26
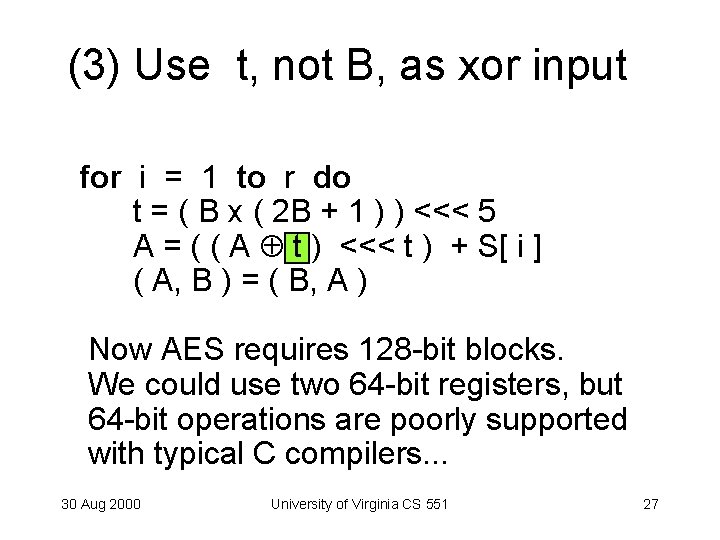
(3) Use t, not B, as xor input for i = 1 to r do t = ( B x ( 2 B + 1 ) ) <<< 5 A = ( ( A t ) <<< t ) + S[ i ] ( A, B ) = ( B, A ) Now AES requires 128 -bit blocks. We could use two 64 -bit registers, but 64 -bit operations are poorly supported with typical C compilers. . . 30 Aug 2000 University of Virginia CS 551 27
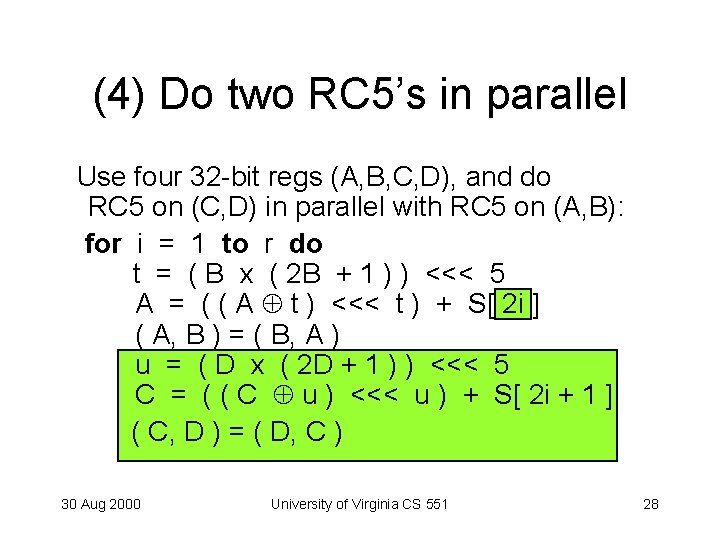
(4) Do two RC 5’s in parallel Use four 32 -bit regs (A, B, C, D), and do RC 5 on (C, D) in parallel with RC 5 on (A, B): for i = 1 to r do t = ( B x ( 2 B + 1 ) ) <<< 5 A = ( ( A t ) <<< t ) + S[ 2 i ] ( A, B ) = ( B, A ) u = ( D x ( 2 D + 1 ) ) <<< 5 C = ( ( C u ) <<< u ) + S[ 2 i + 1 ] ( C, D ) = ( D, C ) 30 Aug 2000 University of Virginia CS 551 28
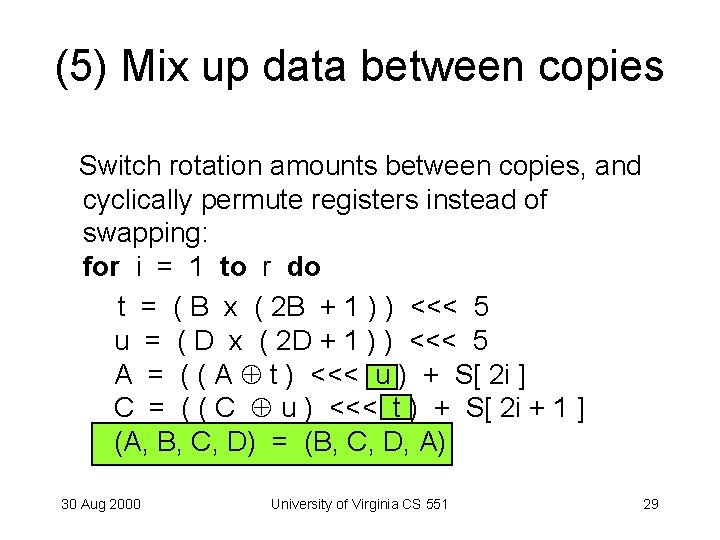
(5) Mix up data between copies Switch rotation amounts between copies, and cyclically permute registers instead of swapping: for i = 1 to r do t = ( B x ( 2 B + 1 ) ) <<< 5 u = ( D x ( 2 D + 1 ) ) <<< 5 A = ( ( A t ) <<< u ) + S[ 2 i ] C = ( ( C u ) <<< t ) + S[ 2 i + 1 ] (A, B, C, D) = (B, C, D, A) 30 Aug 2000 University of Virginia CS 551 29
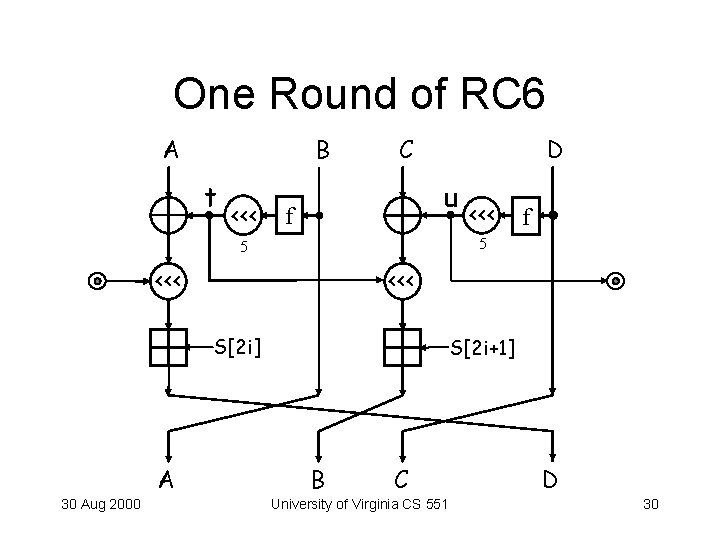
One Round of RC 6 A B t <<< C D u f <<< S[2 i] 30 Aug 2000 f 5 5 A <<< S[2 i+1] B C University of Virginia CS 551 D 30
![Key Expansion (Same as RC 5’s) • Input: array L [0 … c-1] of Key Expansion (Same as RC 5’s) • Input: array L [0 … c-1] of](http://slidetodoc.com/presentation_image_h/2eb6ed6b6299cbbddcecb2a51f2d16c8/image-31.jpg)
Key Expansion (Same as RC 5’s) • Input: array L [0 … c-1] of input key words • Output: array S [0 … 43] of round key words • Procedure: S [0] = 0 x. B 7 E 15163 = Odd[(e-2)232] for i = 1 to 43 do S[i] = S[i-1] + 0 x 9 E 3779 B 9 = Odd[( -1)232] A=B=i=j=0 for s = 1 to 132 do A = S[ i ] = (S[ i ] + A + B) <<< 3 B = L[ j ] = (L[ j ] + A + B) <<< (A + B ) i = (i + 1) mod 44 j = (j + 1) mod c 30 Aug 2000 University of Virginia CS 551 31
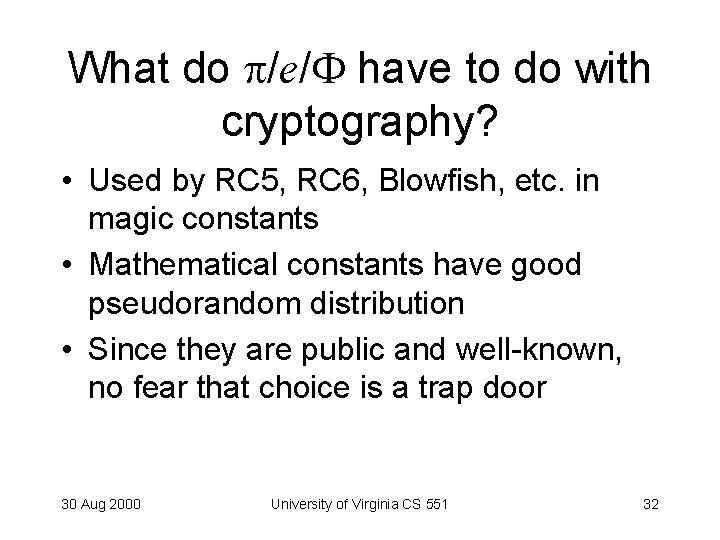
What do /e/ have to do with cryptography? • Used by RC 5, RC 6, Blowfish, etc. in magic constants • Mathematical constants have good pseudorandom distribution • Since they are public and well-known, no fear that choice is a trap door 30 Aug 2000 University of Virginia CS 551 32
![(6) Add Pre- and Post-Whitening B = B + S[ 0 ] D = (6) Add Pre- and Post-Whitening B = B + S[ 0 ] D =](http://slidetodoc.com/presentation_image_h/2eb6ed6b6299cbbddcecb2a51f2d16c8/image-33.jpg)
(6) Add Pre- and Post-Whitening B = B + S[ 0 ] D = D + S[ 1 ] for i = 1 to r do t = ( B x ( 2 B + 1 ) ) <<< 5 u = ( D x ( 2 D + 1 ) ) <<< 5 A = ( ( A t ) <<< u ) + S[ 2 i ] C = ( ( C u ) <<< t ) + S[ 2 i + 1 ] (A, B, C, D) = (B, C, D, A) A = A + S[ 2 r + 2 ] C = C + S[ 2 r + 3 ] 30 Aug 2000 University of Virginia CS 551 33
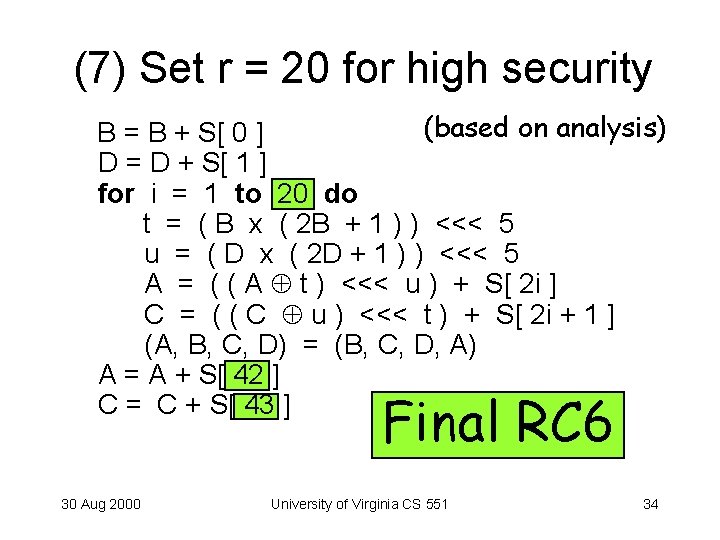
(7) Set r = 20 for high security (based on analysis) B = B + S[ 0 ] D = D + S[ 1 ] for i = 1 to 20 do t = ( B x ( 2 B + 1 ) ) <<< 5 u = ( D x ( 2 D + 1 ) ) <<< 5 A = ( ( A t ) <<< u ) + S[ 2 i ] C = ( ( C u ) <<< t ) + S[ 2 i + 1 ] (A, B, C, D) = (B, C, D, A) A = A + S[ 42 ] C = C + S[ 43 ] Final RC 6 30 Aug 2000 University of Virginia CS 551 34
![RC 6 Decryption (for AES) C = C – S [2 r + 3] RC 6 Decryption (for AES) C = C – S [2 r + 3]](http://slidetodoc.com/presentation_image_h/2eb6ed6b6299cbbddcecb2a51f2d16c8/image-35.jpg)
RC 6 Decryption (for AES) C = C – S [2 r + 3] A = A – S [2 r + 2] for i = r downto 1 do (A, B, C, D) = (D, A, B, C) u = (D x (2 D + 1)) <<< log 2(w) t = (B x (2 B + 1)) <<< log 2(w) C = ((C – S [2 i + 1]) >>> t ) u A = ((A – S [2 i]) >>> u ) t D = D - S[1] B = B - S[0] 30 Aug 2000 University of Virginia CS 551 35
DKEK (P) = P ? Exercise to the reader. . . Proof is worth 100 bonus points (1 problem set). 30 Aug 2000 University of Virginia CS 551 36
![Blowfish • • [Schneier 93] 64 -bit block cipher Much faster than DES Variable Blowfish • • [Schneier 93] 64 -bit block cipher Much faster than DES Variable](http://slidetodoc.com/presentation_image_h/2eb6ed6b6299cbbddcecb2a51f2d16c8/image-37.jpg)
Blowfish • • [Schneier 93] 64 -bit block cipher Much faster than DES Variable key length: 32 -448 bits • Many attempted crytanalyses, none successful yet • Widely used: ssh, Open. BSD, PGPFone 30 Aug 2000 University of Virginia CS 551 37
Key-Dependent S-Boxes • Differential Cryptanalysis depends on analyzing S-box input/output different probabilities • Change the S-boxes so you can’t do analysis 30 Aug 2000 University of Virginia CS 551 38
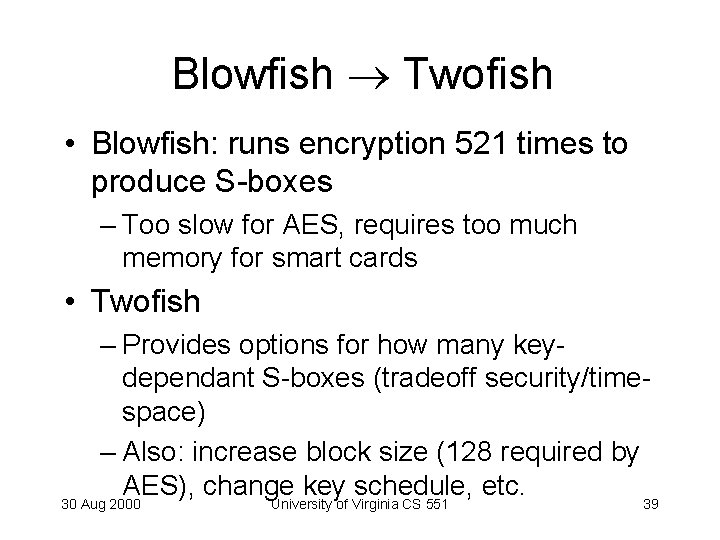
Blowfish Twofish • Blowfish: runs encryption 521 times to produce S-boxes – Too slow for AES, requires too much memory for smart cards • Twofish – Provides options for how many keydependant S-boxes (tradeoff security/timespace) – Also: increase block size (128 required by AES), change key schedule, etc. 30 Aug 2000 University of Virginia CS 551 39
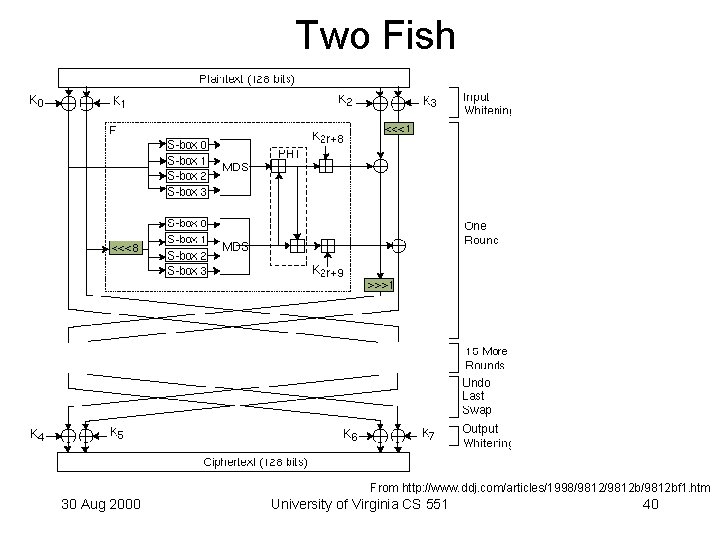
Two Fish From http: //www. ddj. com/articles/1998/9812 b/9812 bf 1. htm 30 Aug 2000 University of Virginia CS 551 40
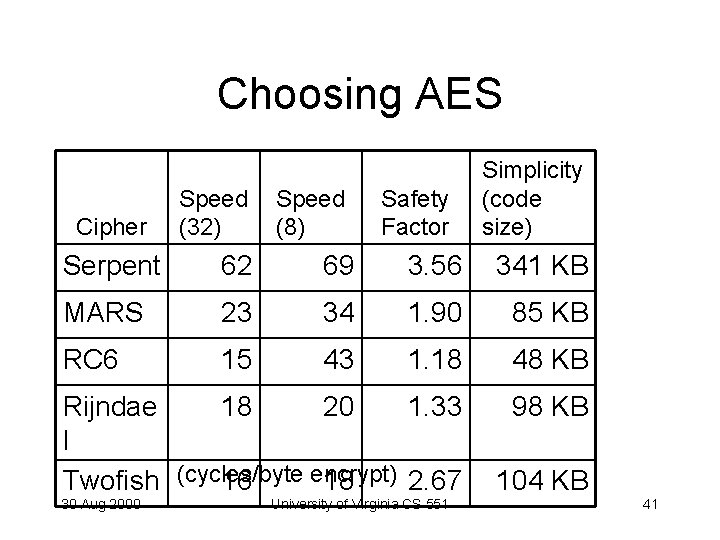
Choosing AES Cipher Speed (32) Speed (8) Safety Factor Simplicity (code size) Serpent 62 69 3. 56 341 KB MARS 23 34 1. 90 85 KB RC 6 15 43 1. 18 48 KB Rijndae 18 20 1. 33 l encrypt) Twofish (cycles/byte 16 18 2. 67 98 KB 30 Aug 2000 University of Virginia CS 551 104 KB 41
Performance/Security Just how paranoid are you? How much progress will happen in cryptanalysis? 30 Aug 2000 University of Virginia CS 551 42
AES Status August 31, 2000 - NIST is still on track to announce its proposed selection for the AES in late summer / early fall, and it is likely to occur sometime in September. HOWEVER, a specific date for the announcement has NOT been set at this time. When a date has been selected, it will be indicated here, to give the public as much advance notice as possible. http: //csrc. nist. gov/encryption/aes/ 30 Aug 2000 University of Virginia CS 551 43
Charge • Project Pre-Proposals due Monday • Challenge #1 still open, 2 new challenge problems: – RC 6 Decryption Proof – Break SDMI ($10 K reward!) • Next time: – Key Distribution • US Army communications officer • Public-Key Cryptosystems 30 Aug 2000 University of Virginia CS 551 44
- Slides: 44