Lecture 5 Authenticated encryption TEK 4500 22 09
- Slides: 76
Lecture 5 – Authenticated encryption TEK 4500 22. 09. 2020 Håkon Jacobsen hakon. jacobsen@its. uio. no
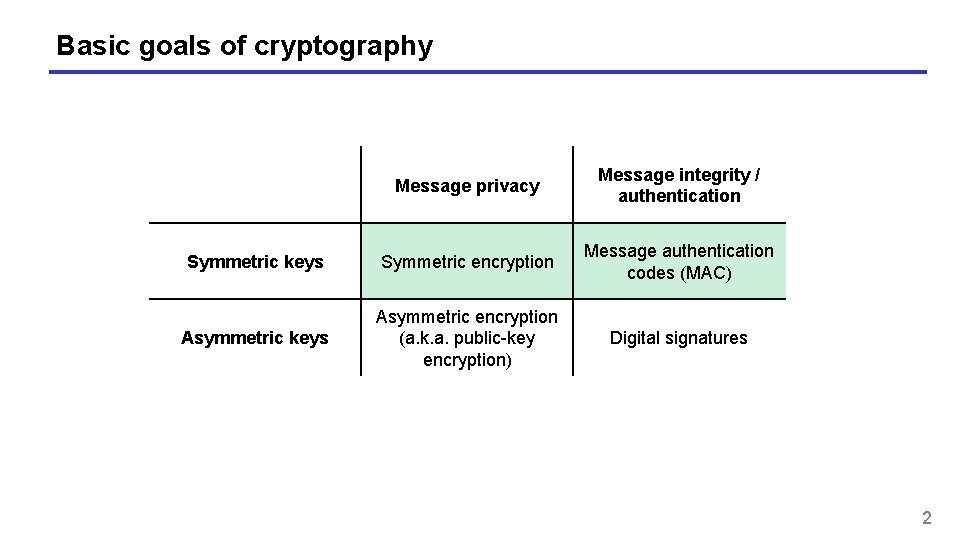
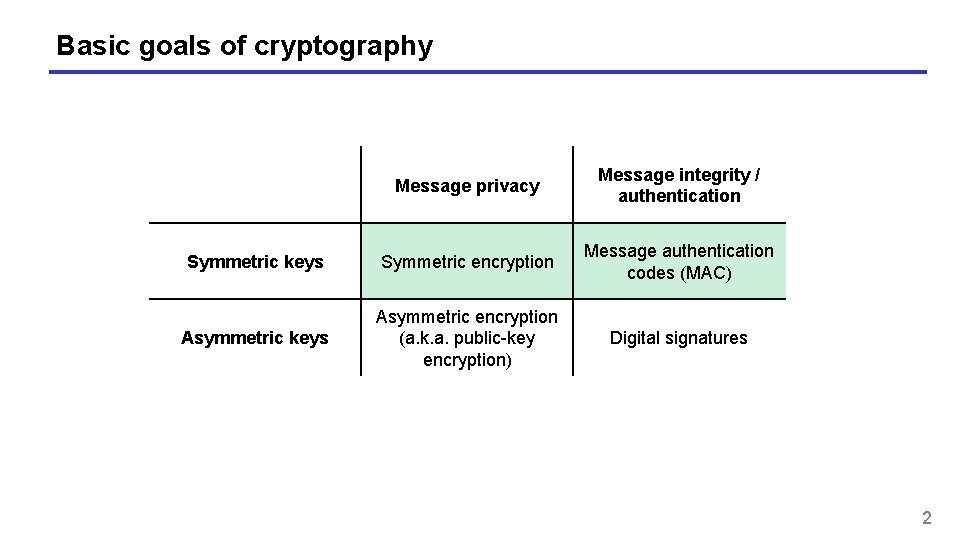
Basic goals of cryptography Message privacy Message integrity / authentication Symmetric keys Symmetric encryption Message authentication codes (MAC) Asymmetric keys Asymmetric encryption (a. k. a. public-key encryption) Digital signatures 2
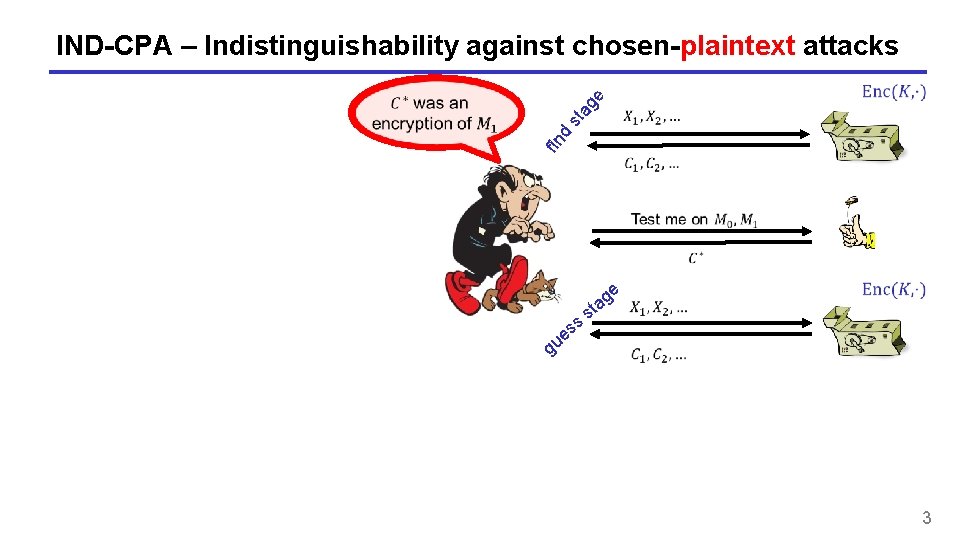
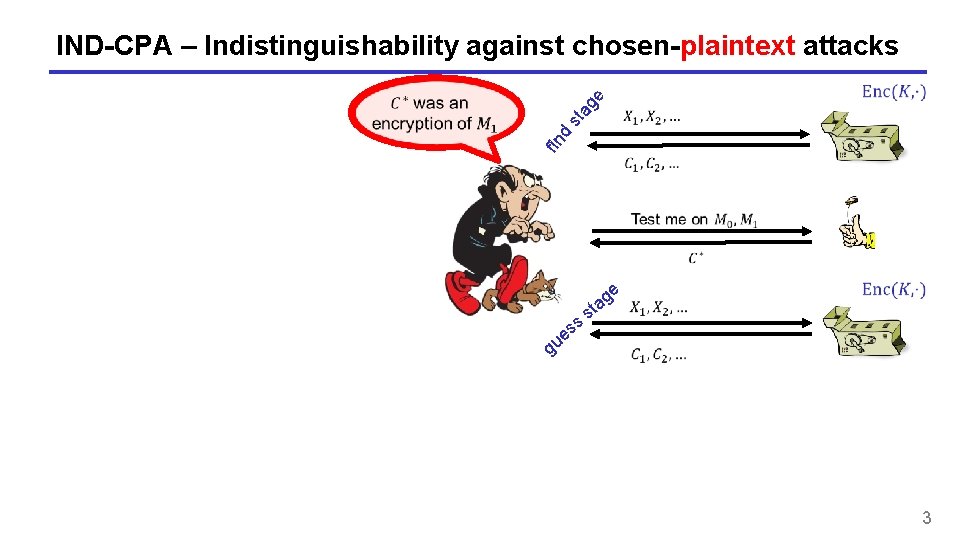
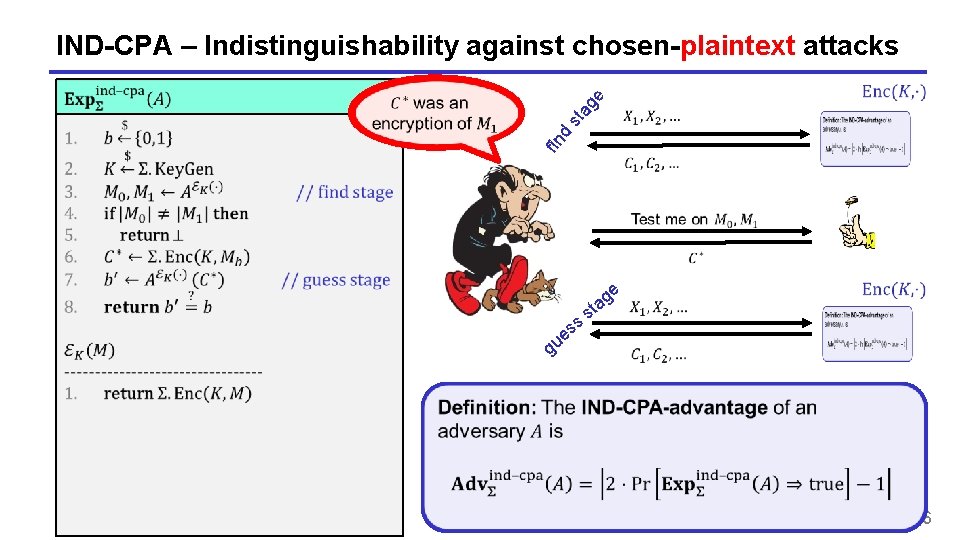
fin d st ag e IND-CPA – Indistinguishability against chosen-plaintext attacks ss e u ge a st g 3
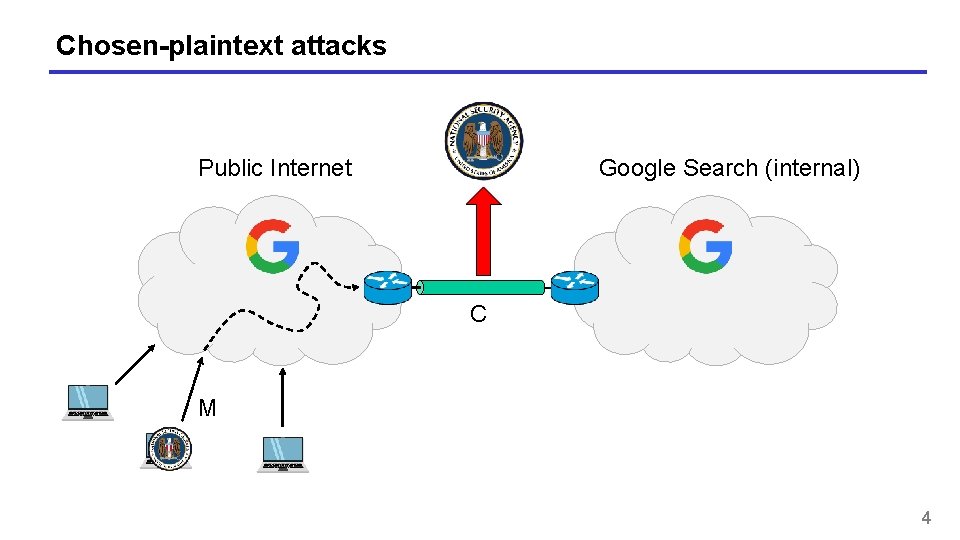
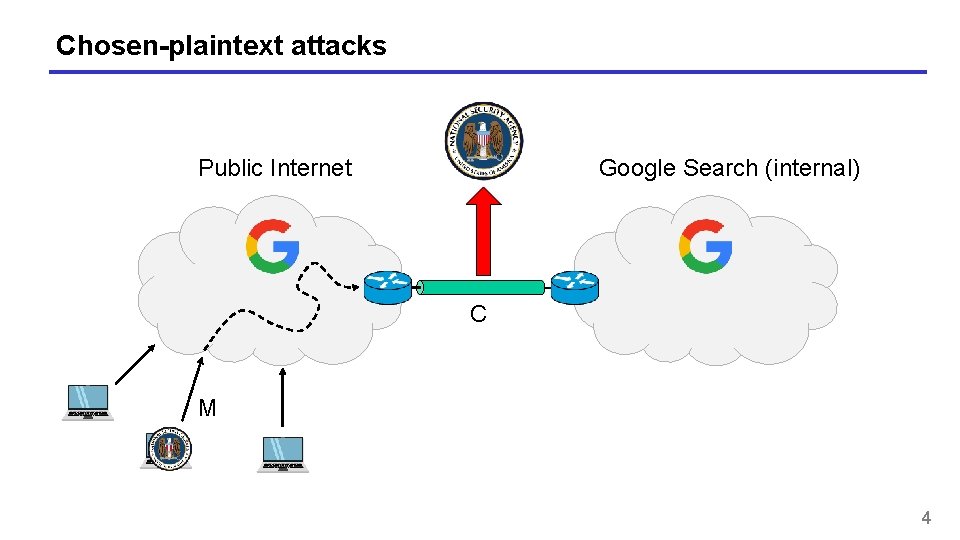
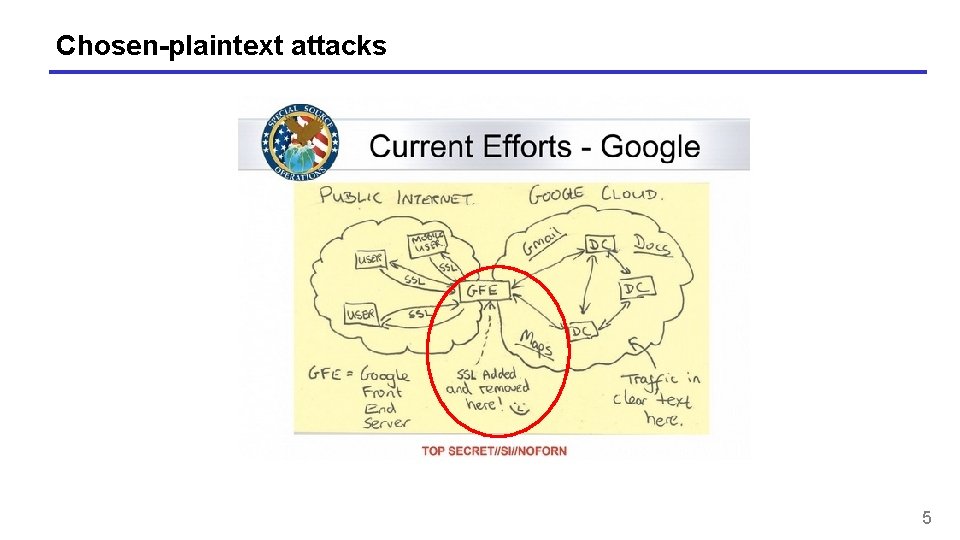
Chosen-plaintext attacks Public Internet Google Search (internal) C M 4
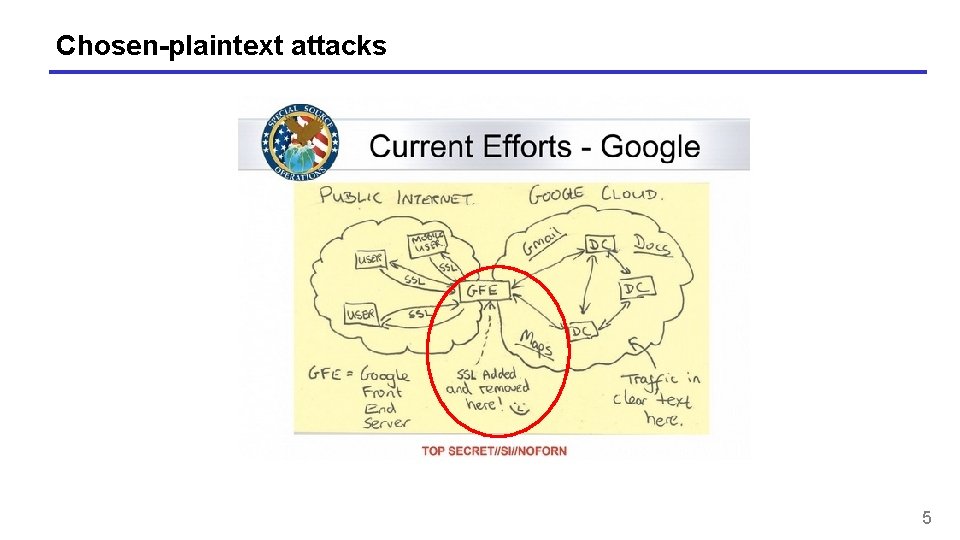
Chosen-plaintext attacks 5
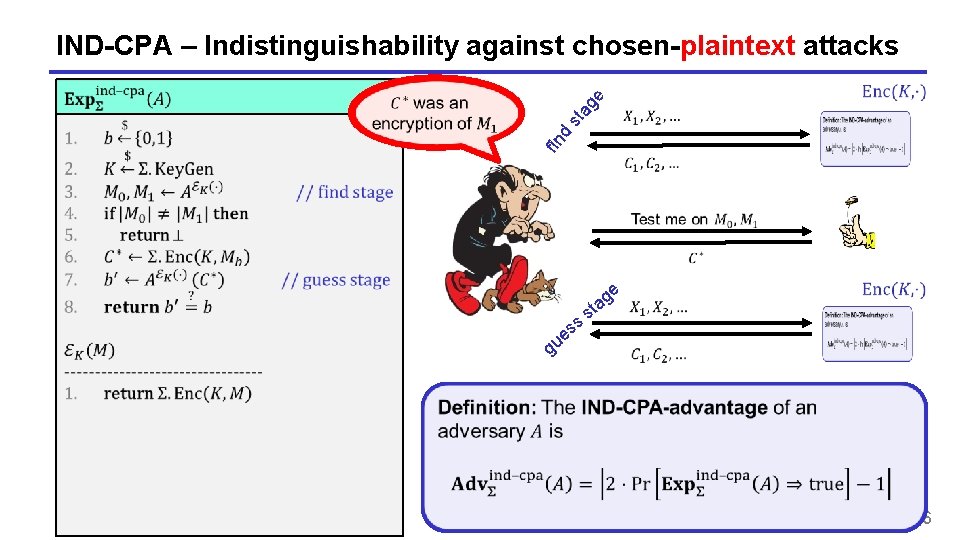
fin d st ag e IND-CPA – Indistinguishability against chosen-plaintext attacks ss e u ge a st g 6
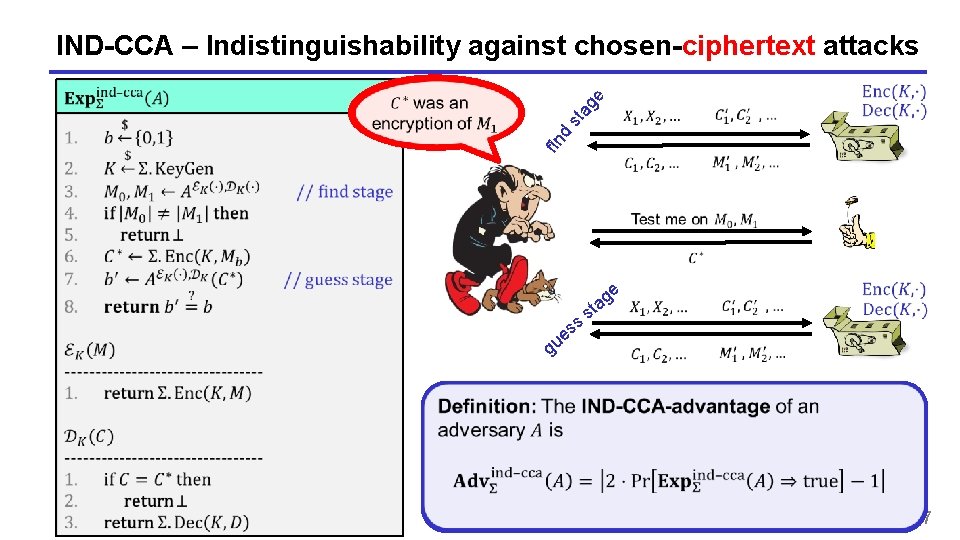
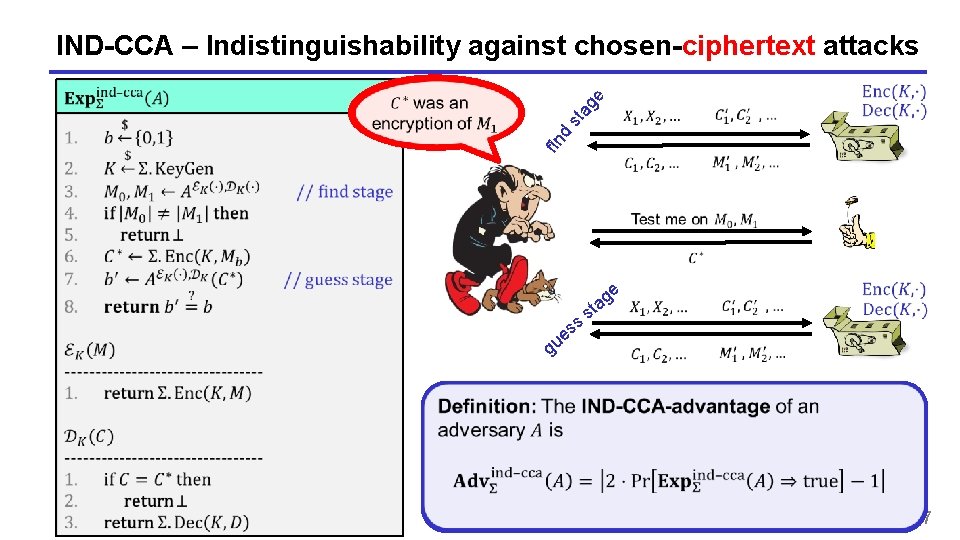
fin d st ag e IND-CCA – Indistinguishability against chosen-ciphertext attacks ss e u ge a st g 7
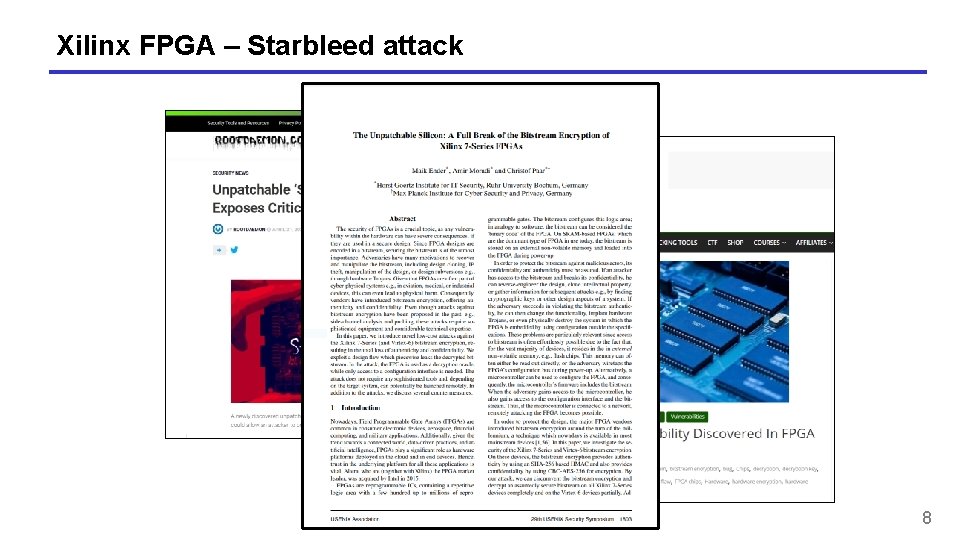
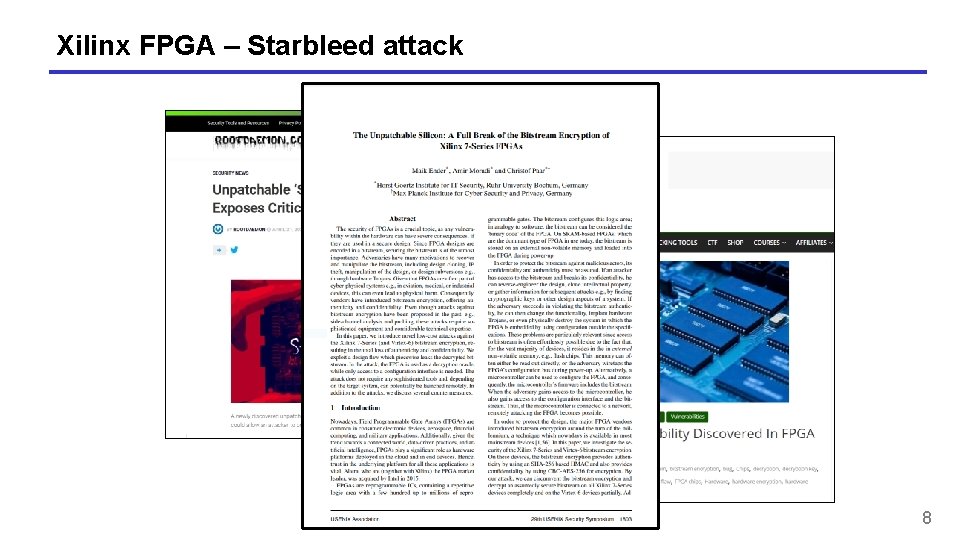
Xilinx FPGA – Starbleed attack 8
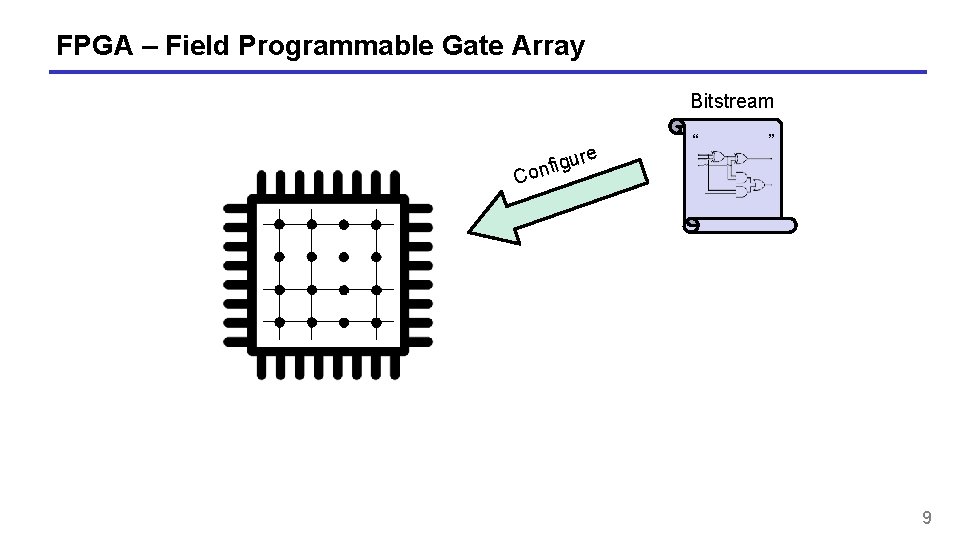
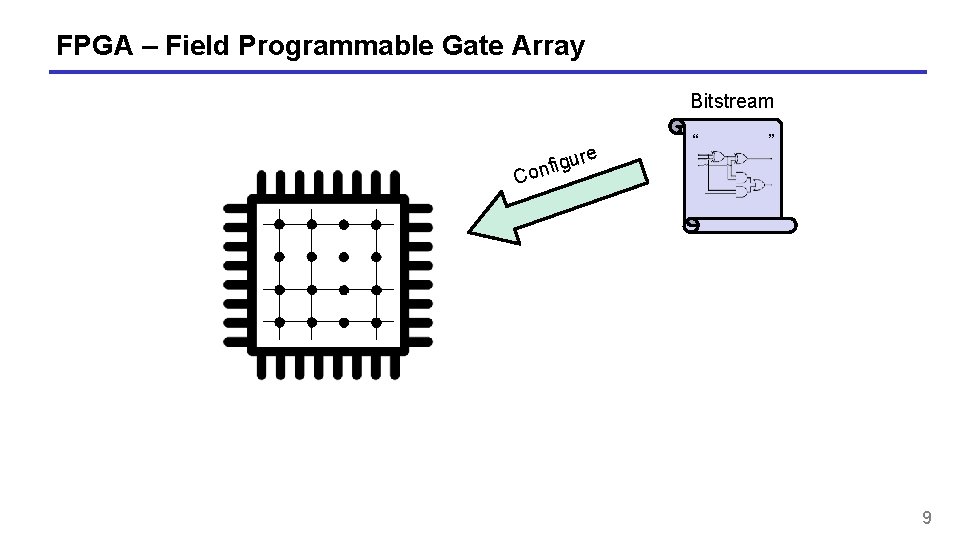
FPGA – Field Programmable Gate Array Bitstream e r u g i f on “ ” C 9
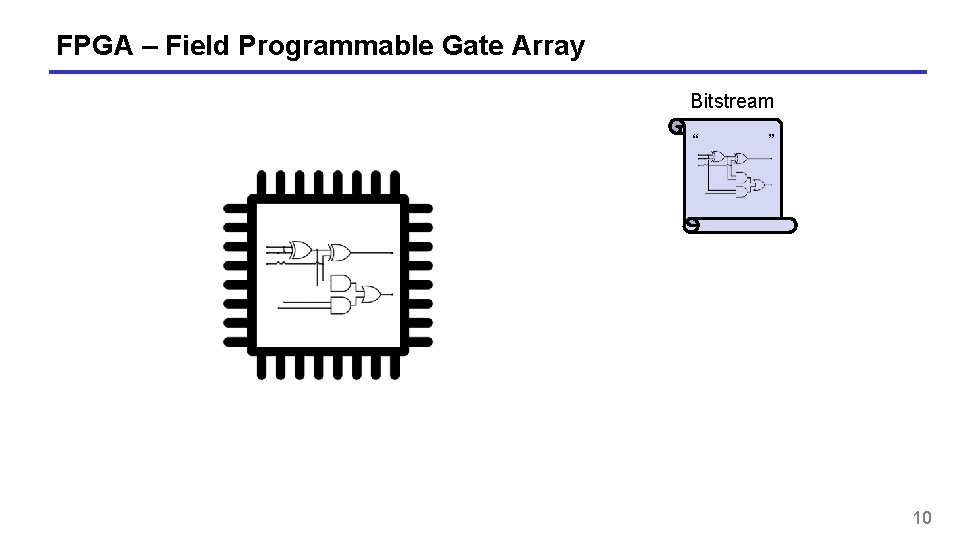
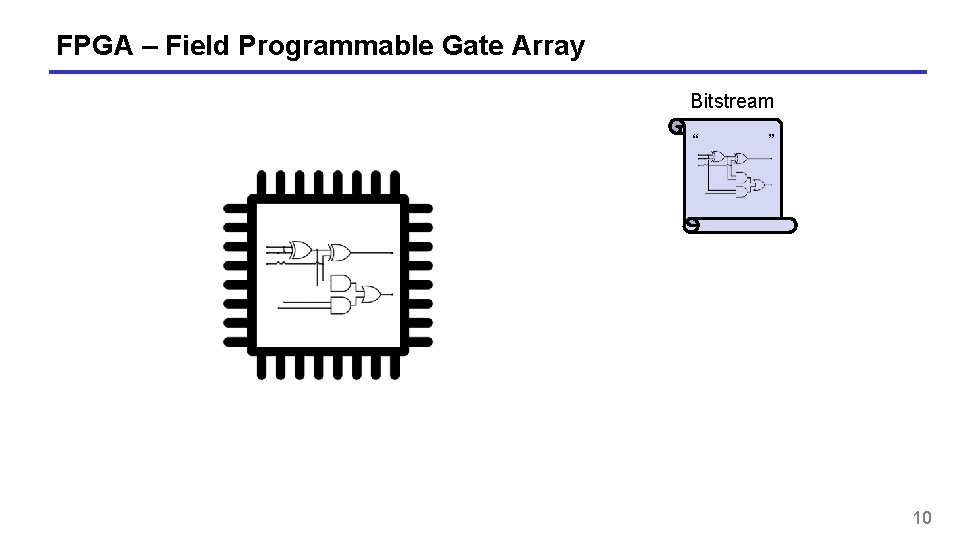
FPGA – Field Programmable Gate Array Bitstream “ ” 10
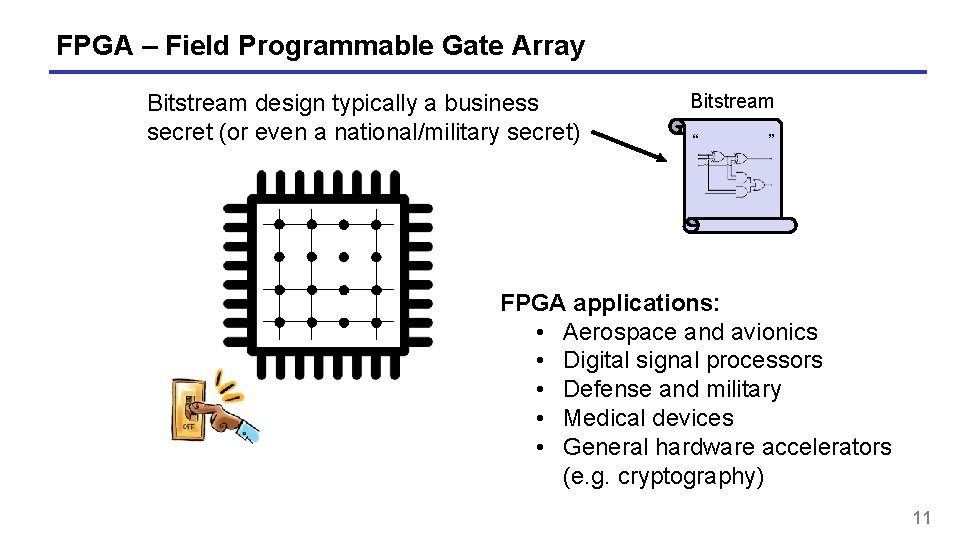
FPGA – Field Programmable Gate Array Bitstream design typically a business secret (or even a national/military secret) Bitstream “ ” FPGA applications: • Aerospace and avionics • Digital signal processors • Defense and military • Medical devices • General hardware accelerators (e. g. cryptography) 11
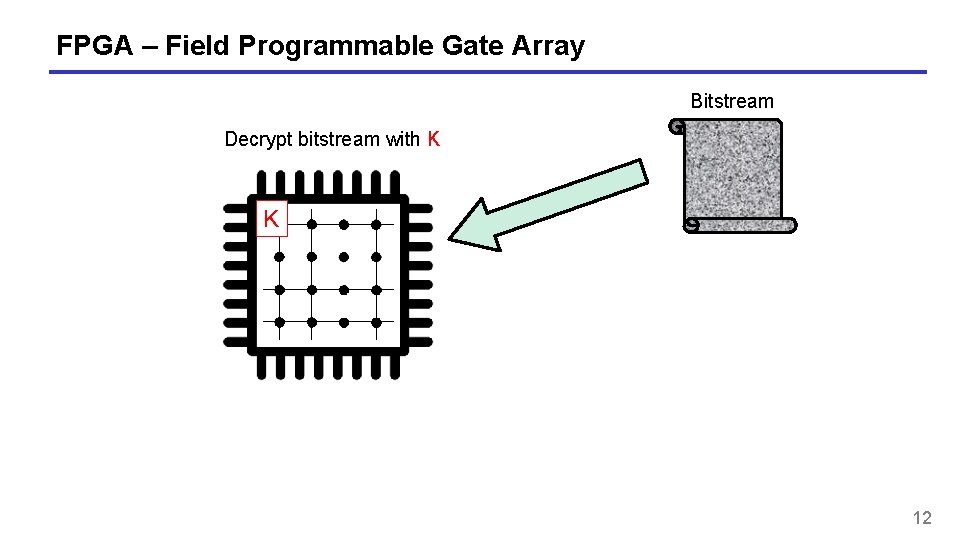
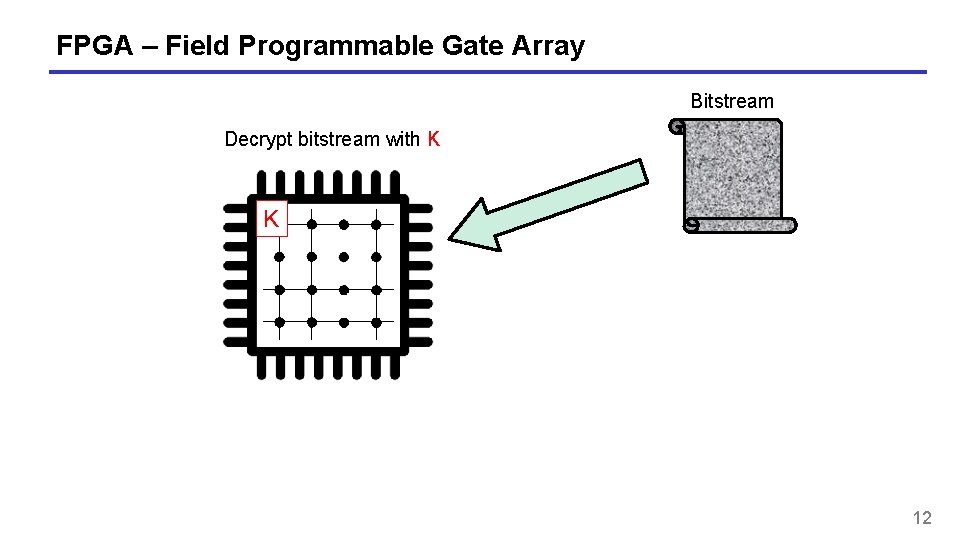
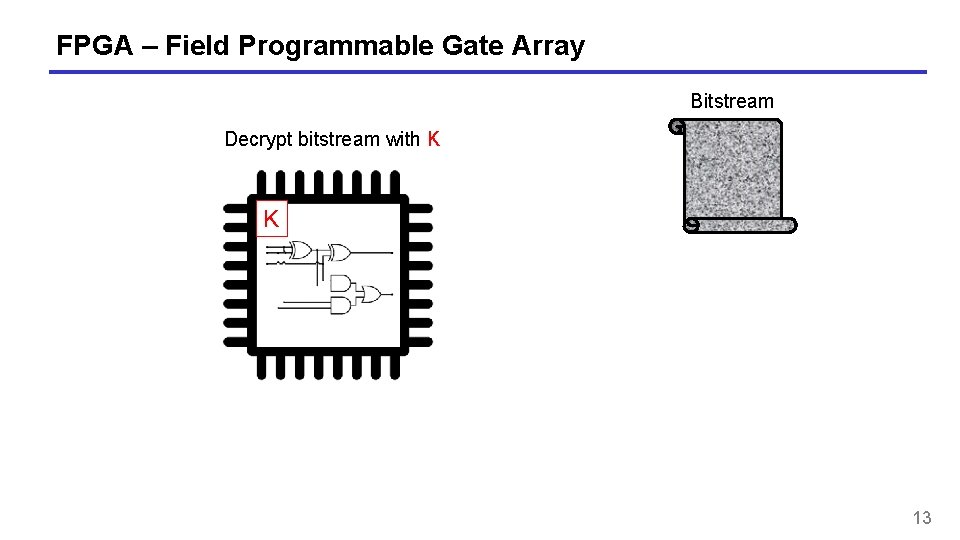
FPGA – Field Programmable Gate Array Bitstream Decrypt bitstream with K K 12
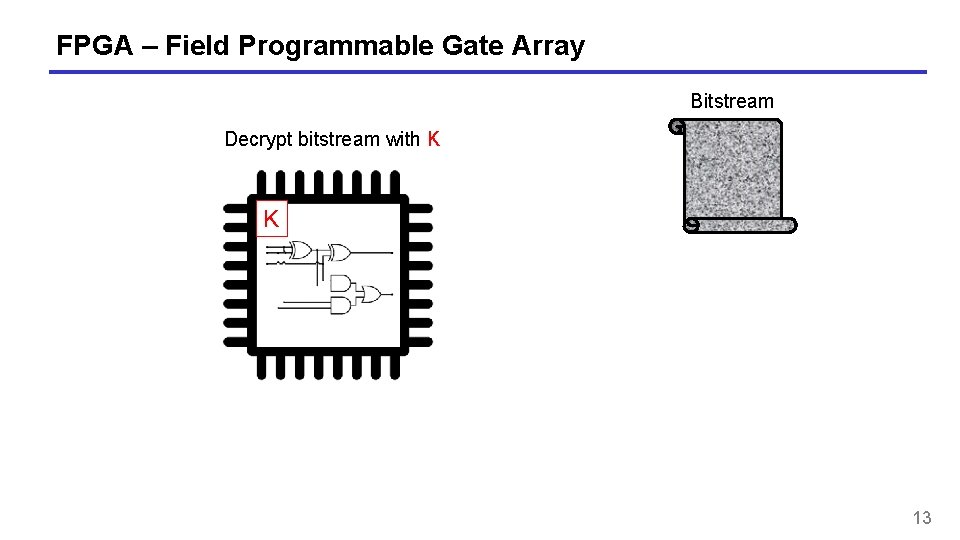
FPGA – Field Programmable Gate Array Bitstream Decrypt bitstream with K K 13
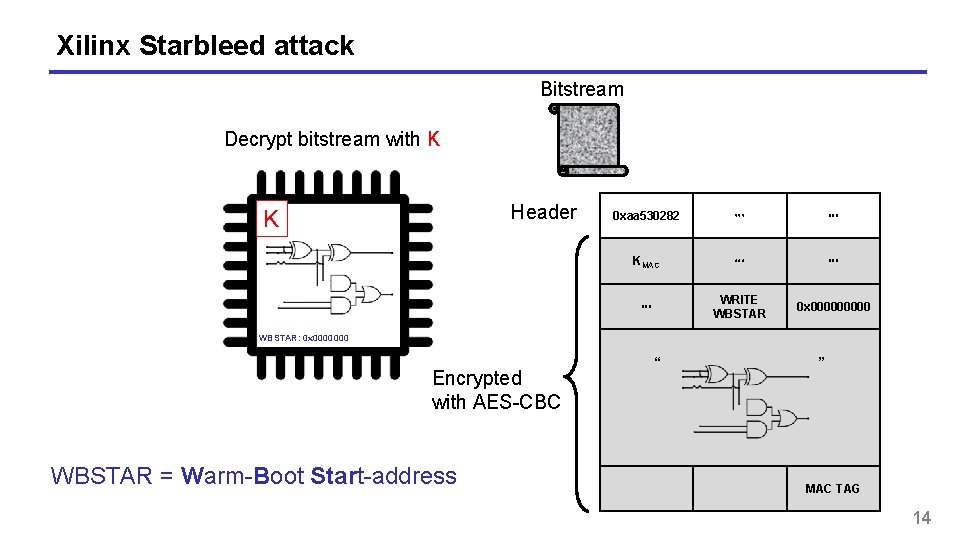
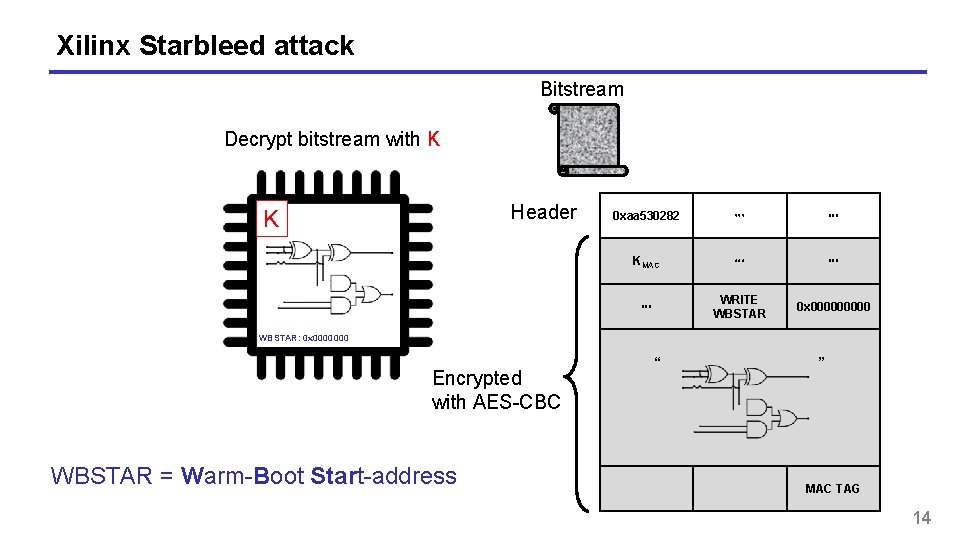
Xilinx Starbleed attack Bitstream Decrypt bitstream with K Header K 0 xaa 530282 ⋯ ⋯ KMAC ⋯ ⋯ ⋯ WRITE WBSTAR 0 x 00000 WBSTAR: 0 x 0000000 Encrypted with AES-CBC WBSTAR = Warm-Boot Start-address “ ” MAC TAG 14
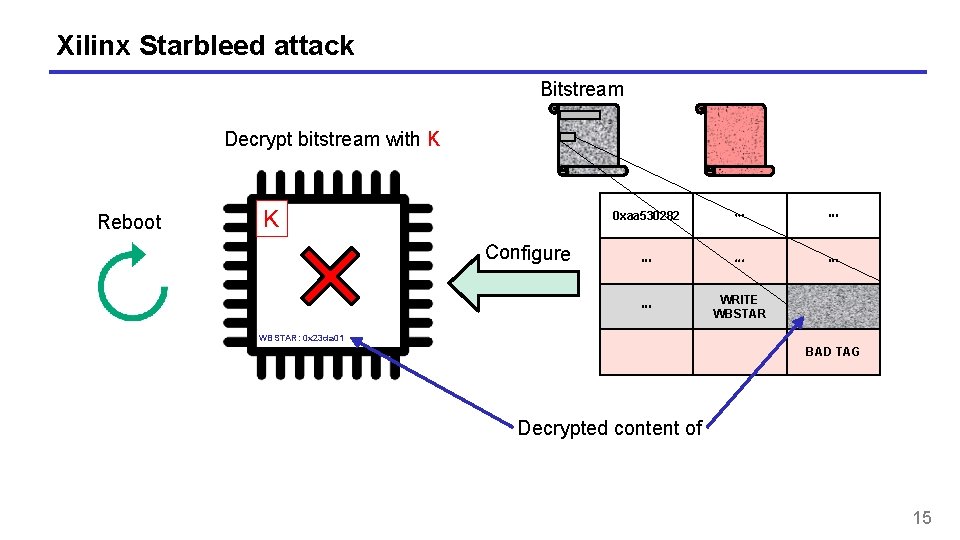
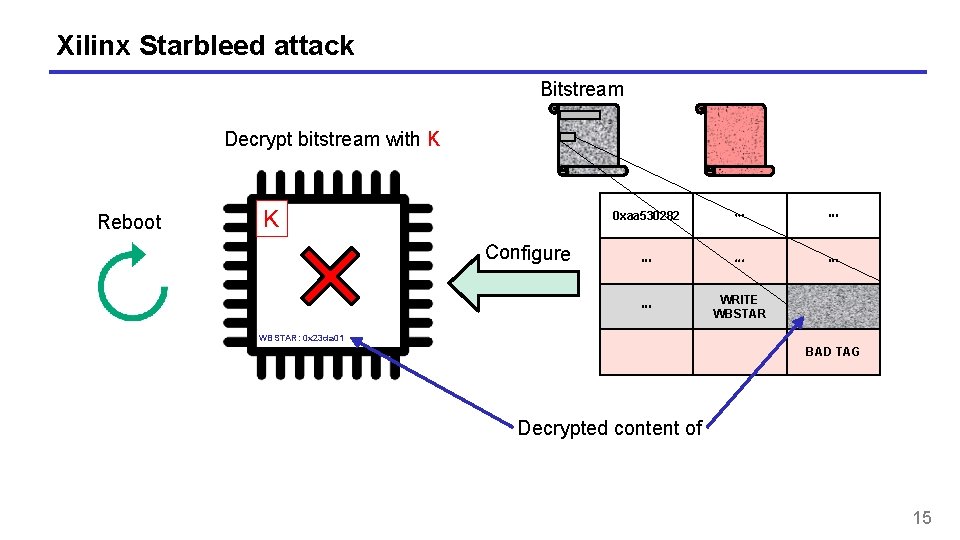
Xilinx Starbleed attack Bitstream Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 23 da 01 BAD TAG Decrypted content of 15
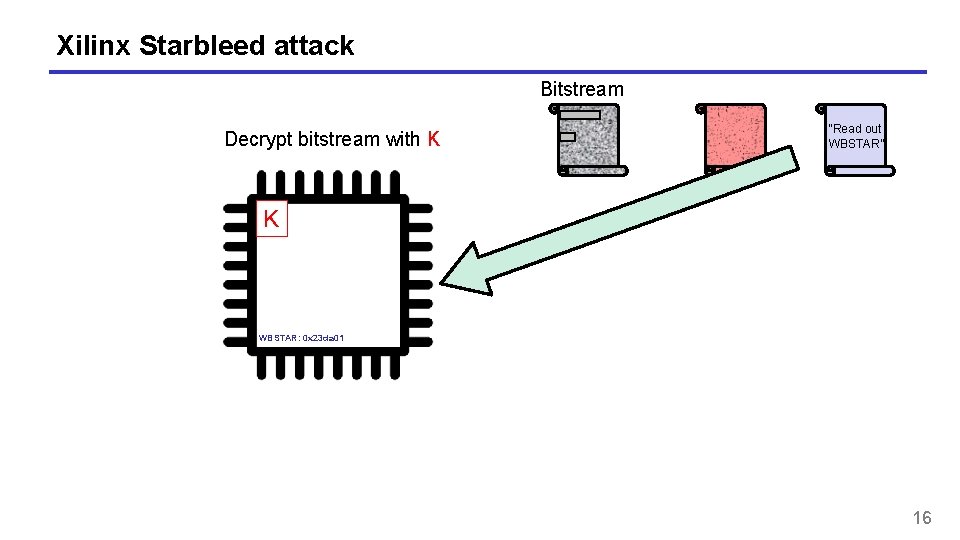
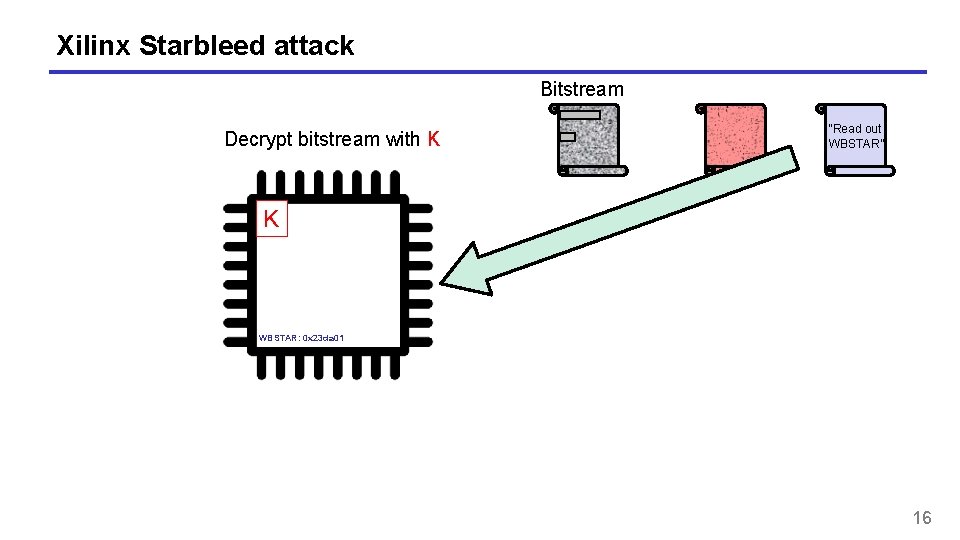
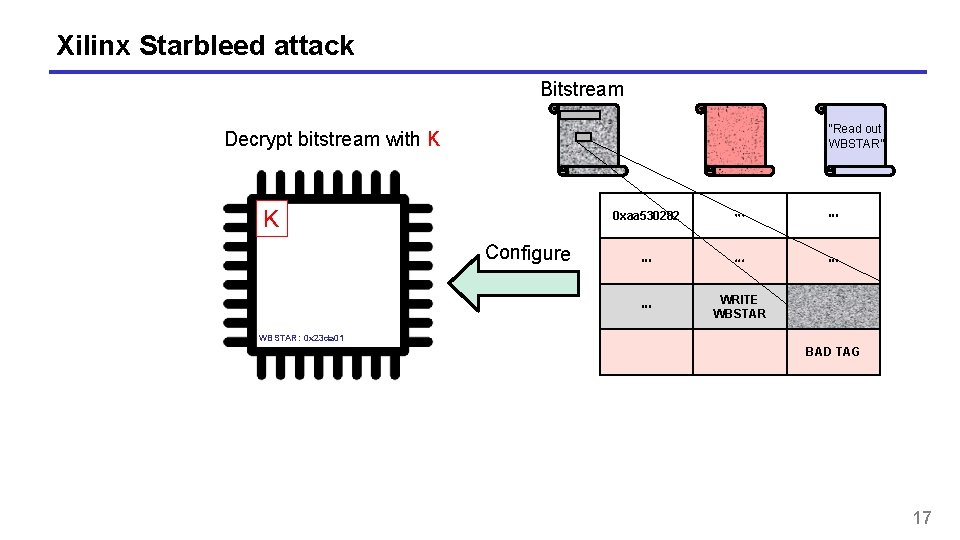
Xilinx Starbleed attack Bitstream Decrypt bitstream with K “Read out WBSTAR” K WBSTAR: 0 x 23 da 01 16
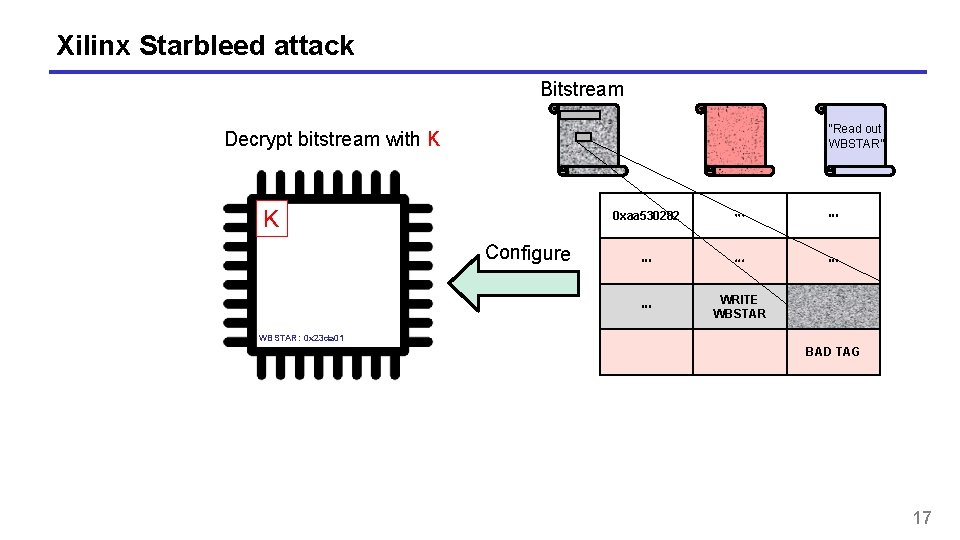
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 23 da 01 BAD TAG 17
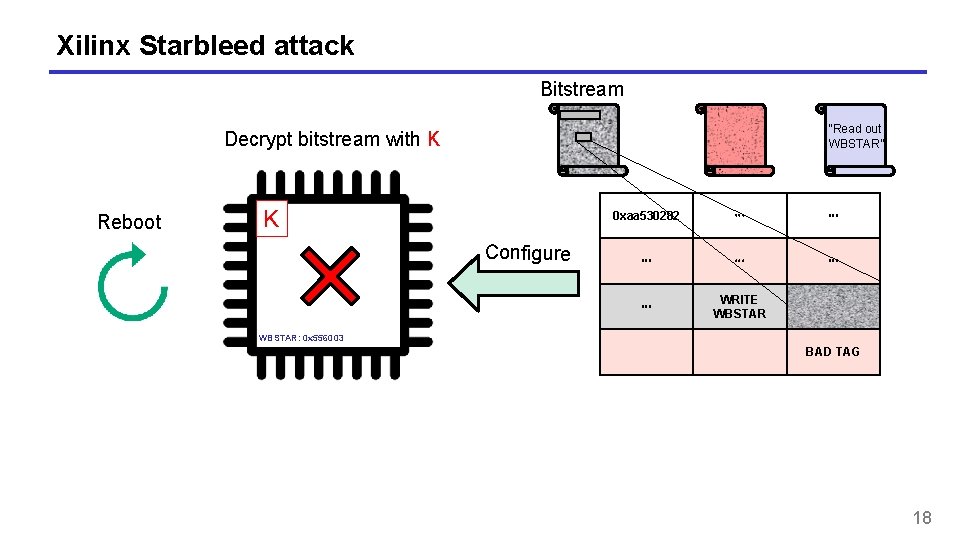
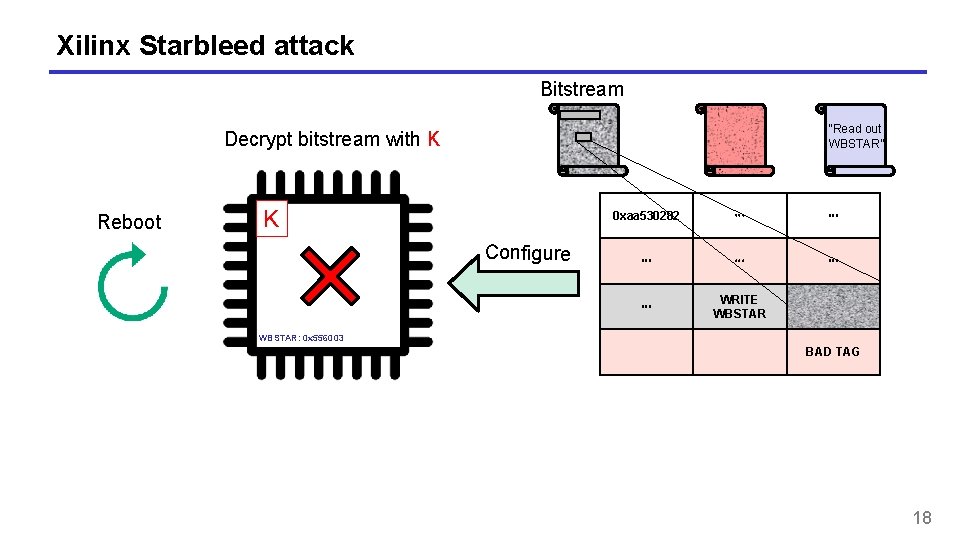
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 556003 BAD TAG 18
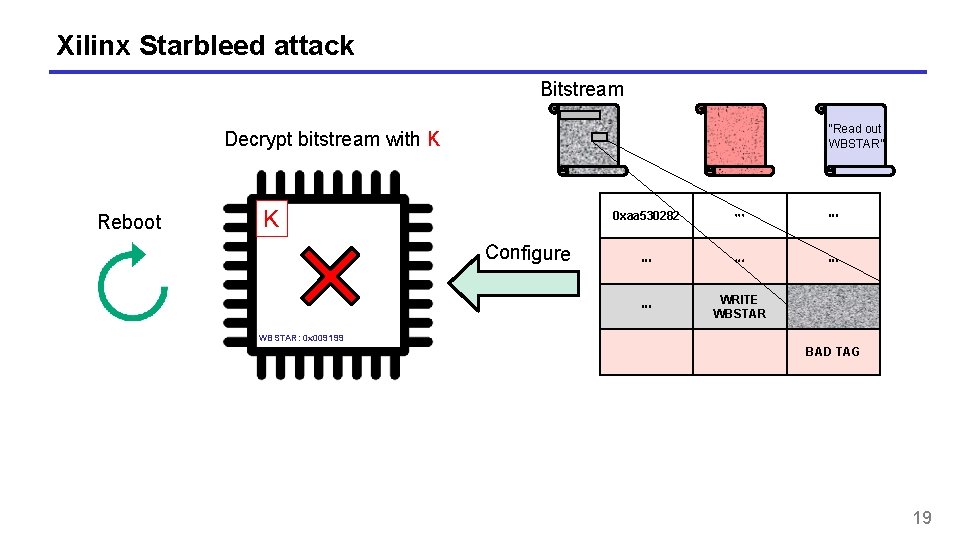
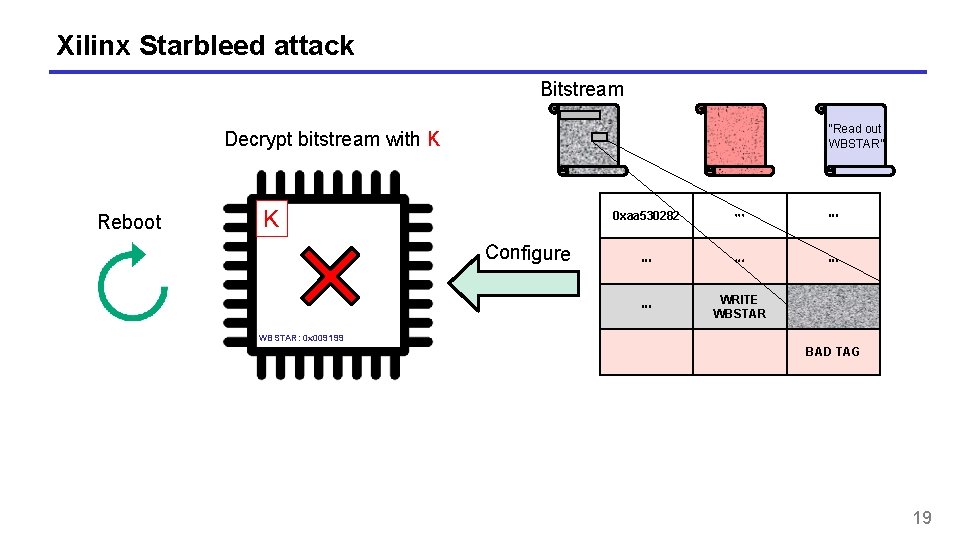
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 009199 BAD TAG 19
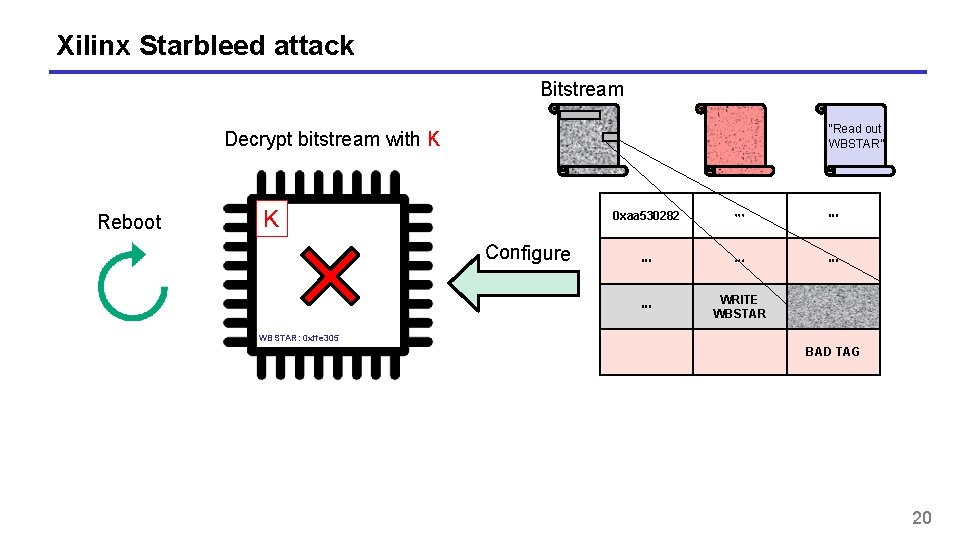
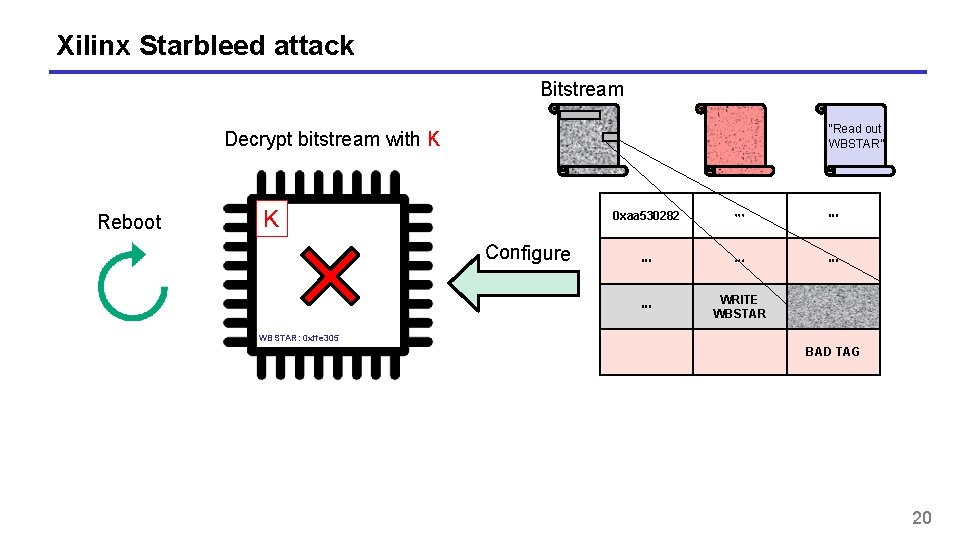
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 xffe 305 BAD TAG 20
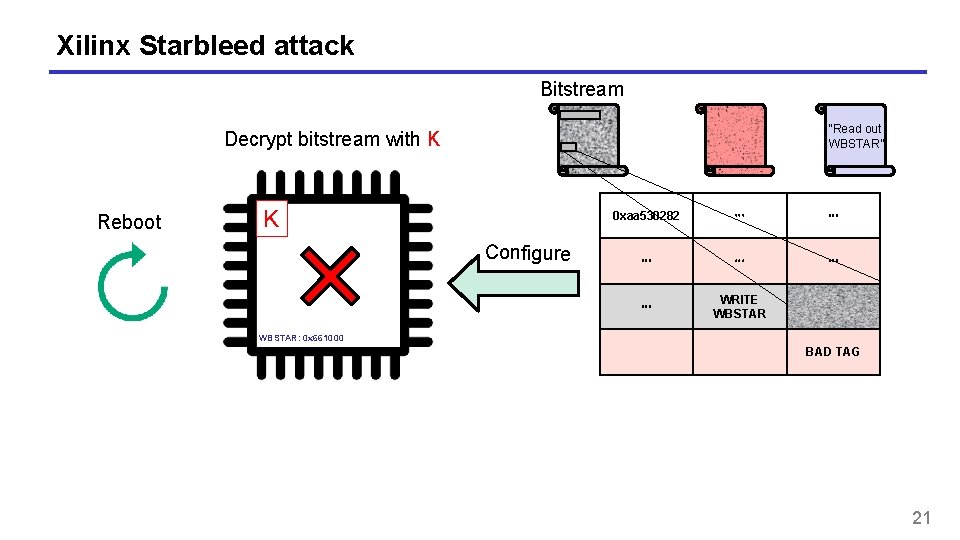
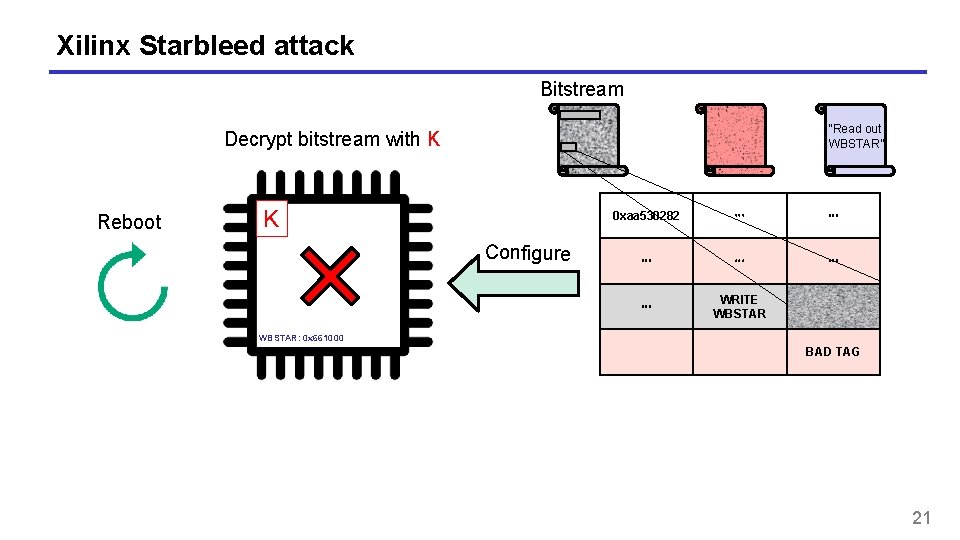
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 661000 BAD TAG 21
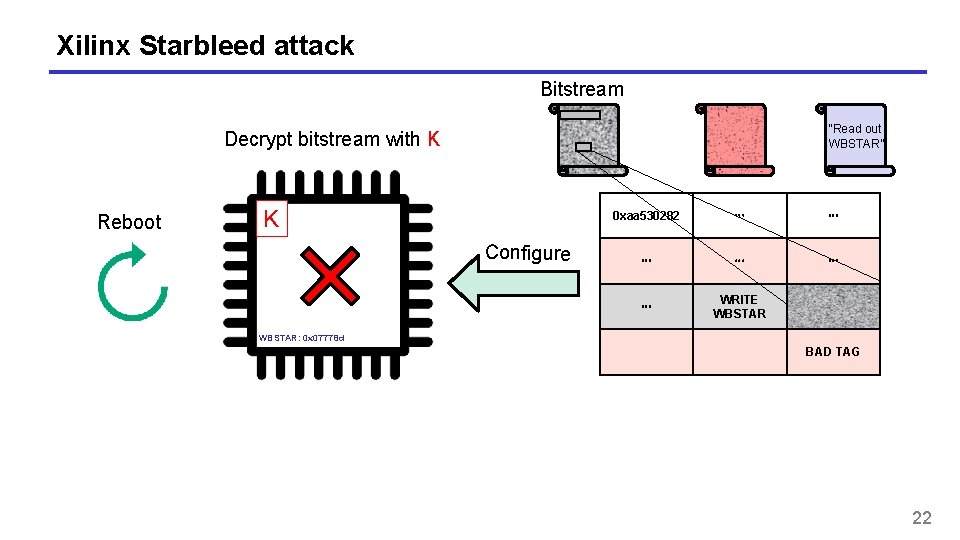
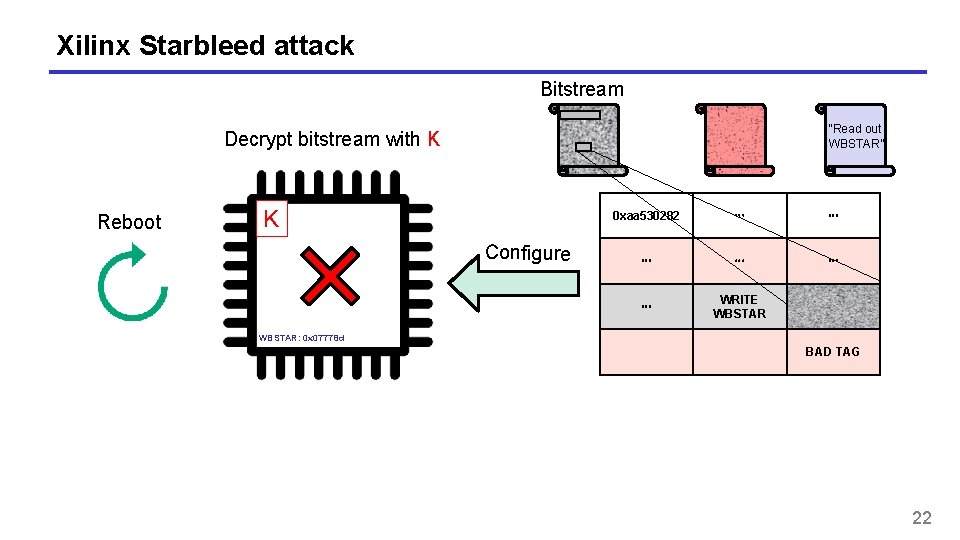
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K Configure 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR: 0 x 07778 d BAD TAG 22
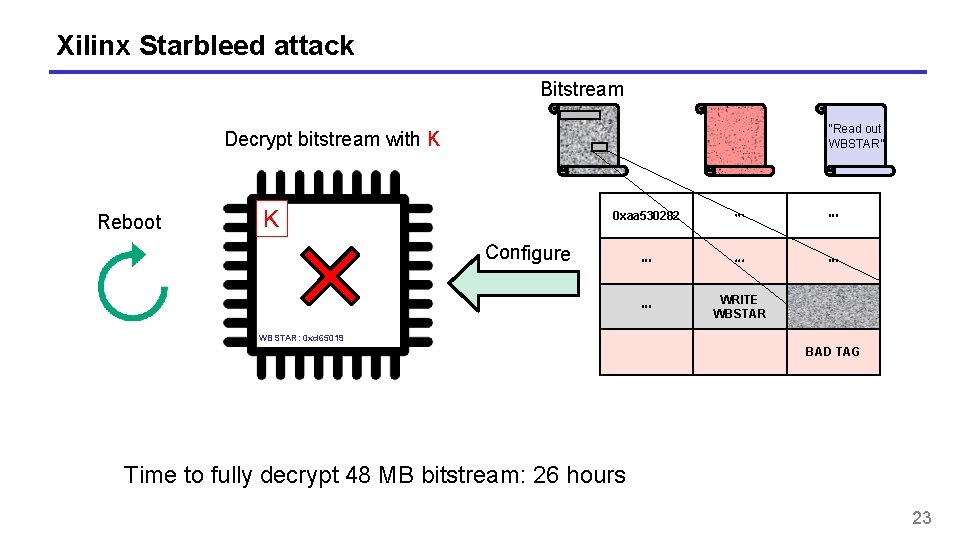
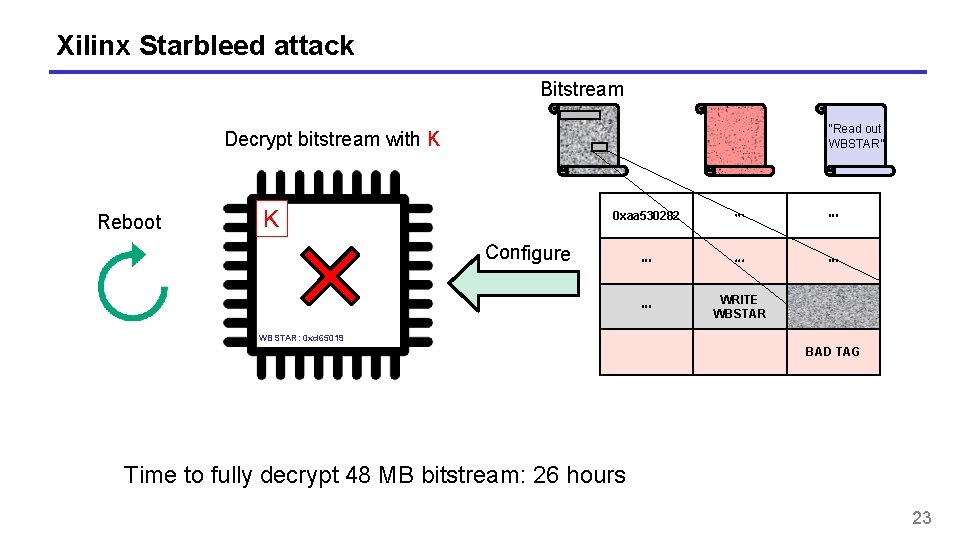
Xilinx Starbleed attack Bitstream “Read out WBSTAR” Decrypt bitstream with K Reboot K 0 xaa 530282 ⋯ ⋯ ⋯ WRITE WBSTAR Configure WBSTAR: 0 xd 65019 BAD TAG Time to fully decrypt 48 MB bitstream: 26 hours 23
Padding oracles • Full decryption oracles are not always available/needed • Padding attacks: • Chosen-ciphertext attacks that exploit small timing variations when decrypting different ciphertexts • Only a limited "decryption" oracle available to the attacker • First described by Serge Vaudenay (2002) based on CBC-encryption in TLS and IPsec 24
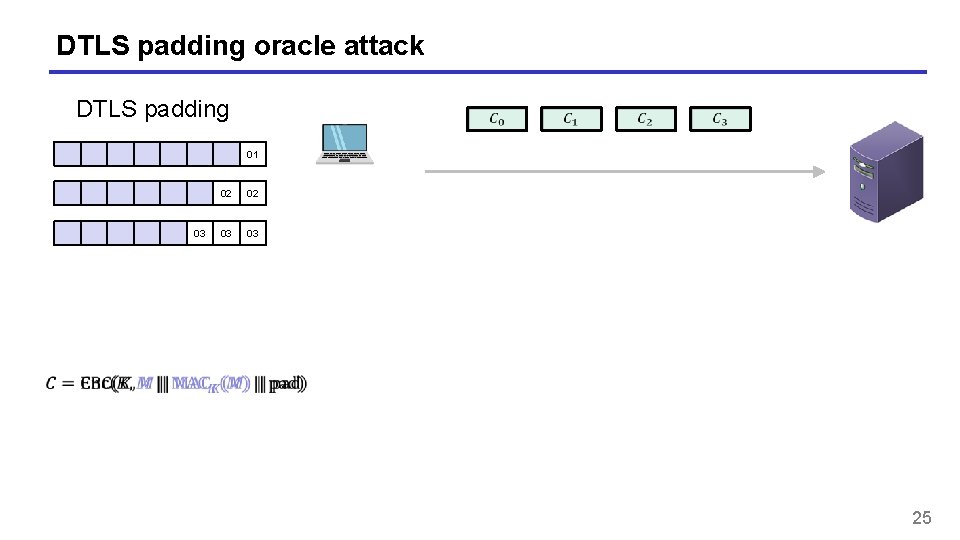
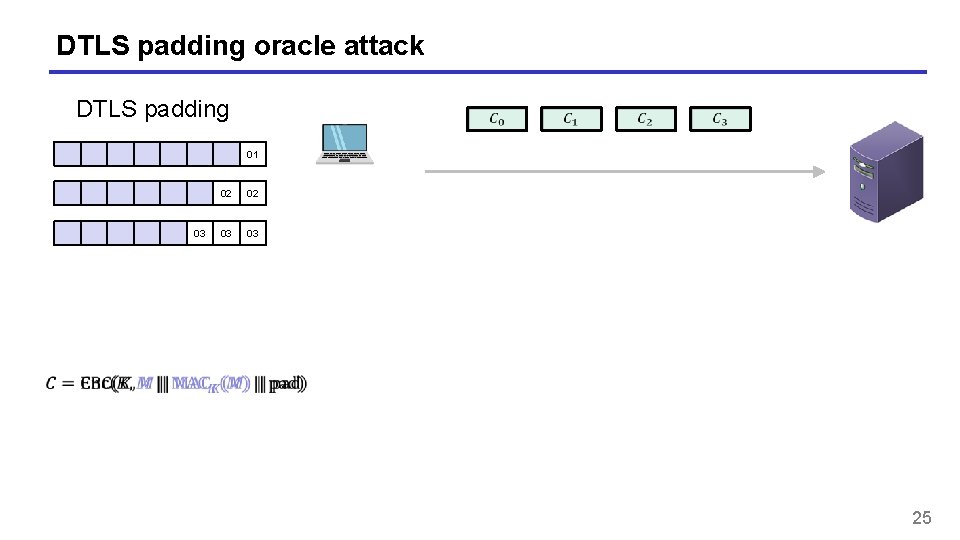
DTLS padding oracle attack DTLS padding 01 03 02 02 03 03 25
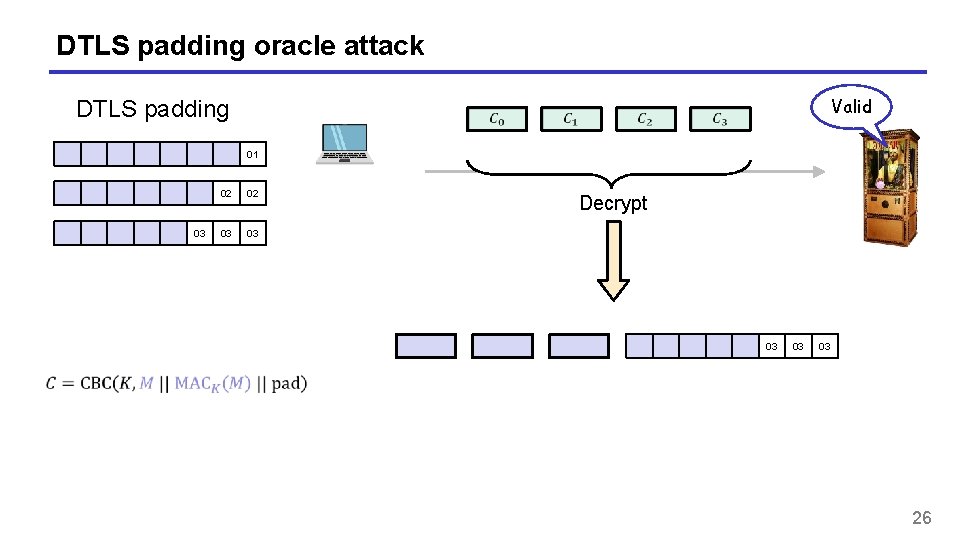
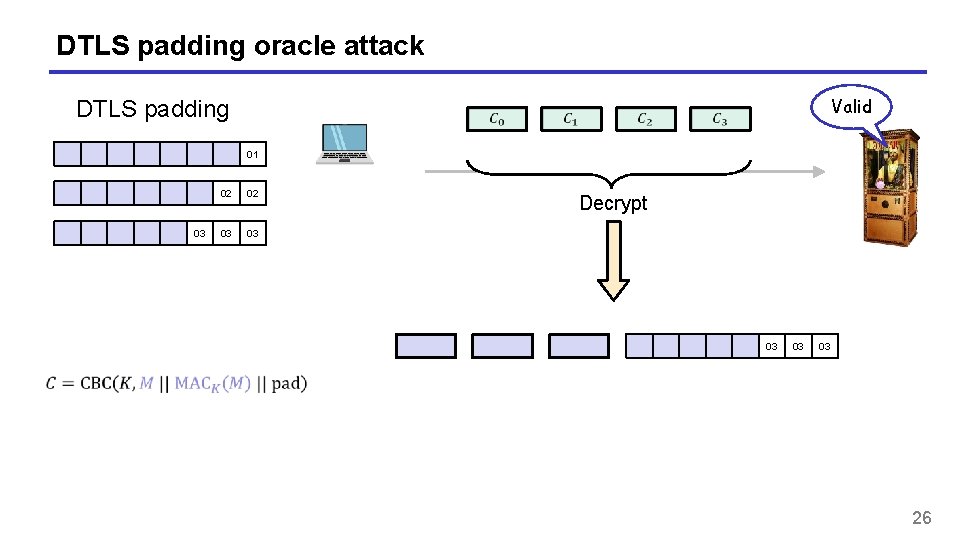
DTLS padding oracle attack Valid DTLS padding 01 03 02 02 03 03 Decrypt 03 03 03 26
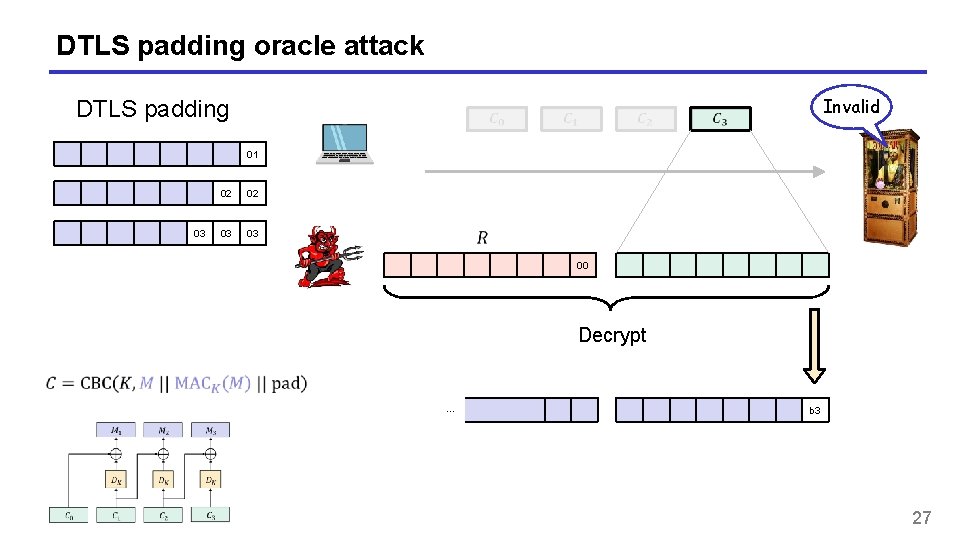
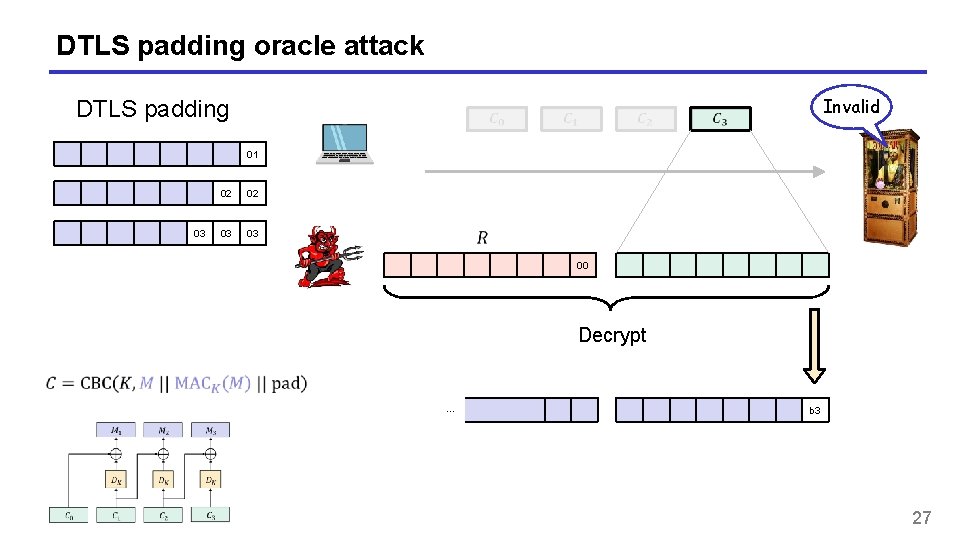
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 00 Decrypt … b 3 27
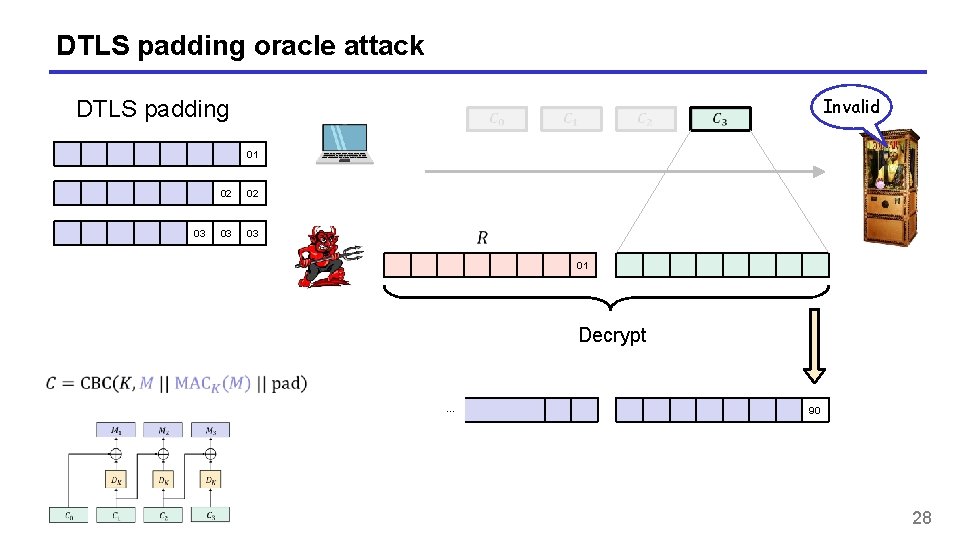
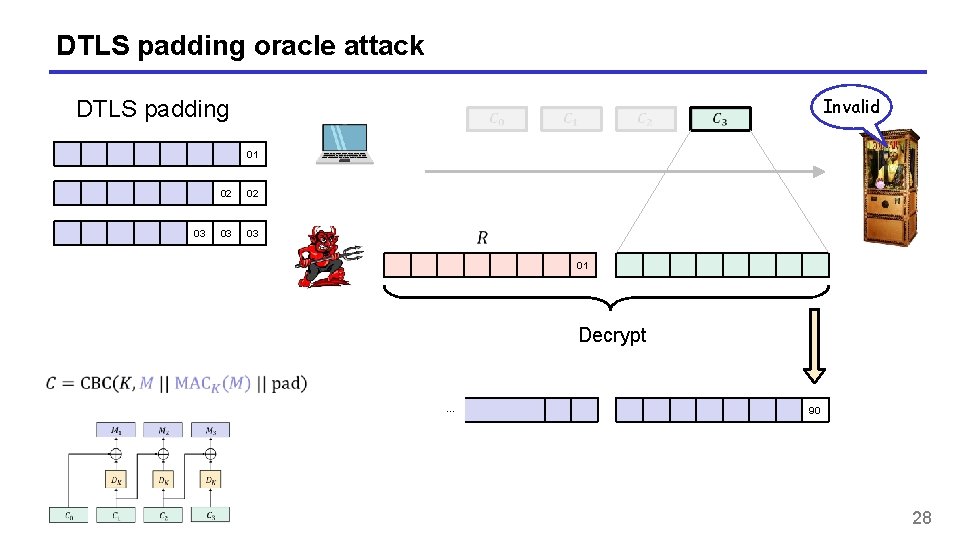
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 01 Decrypt … 90 28
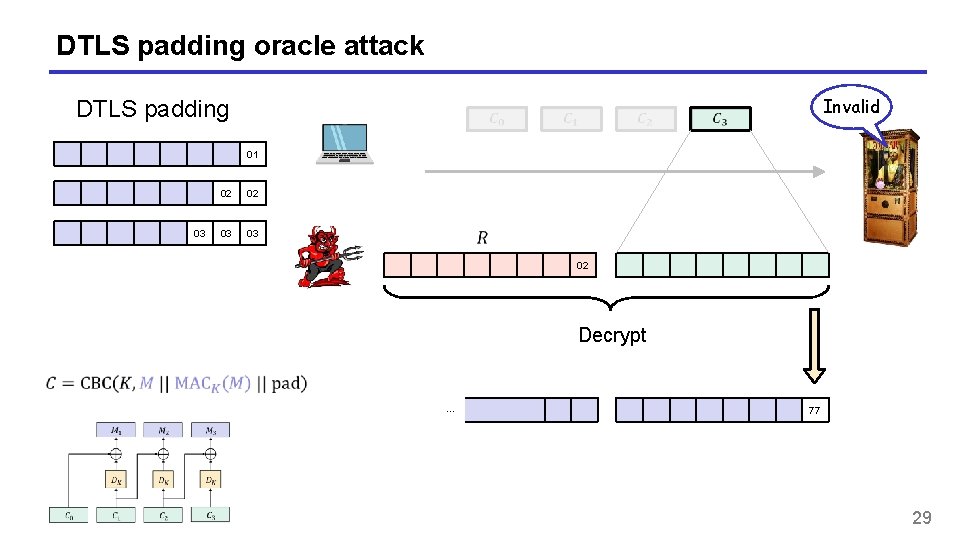
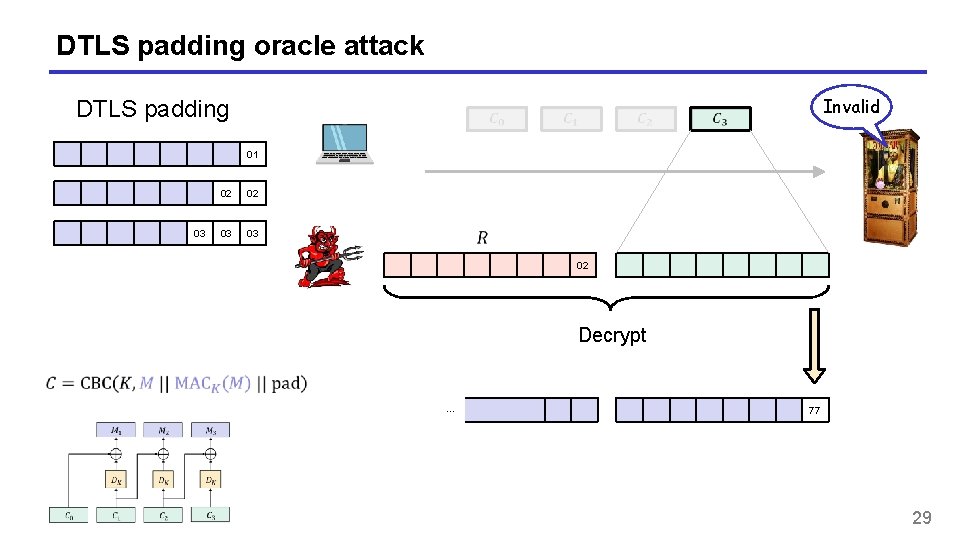
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 02 Decrypt … 77 29
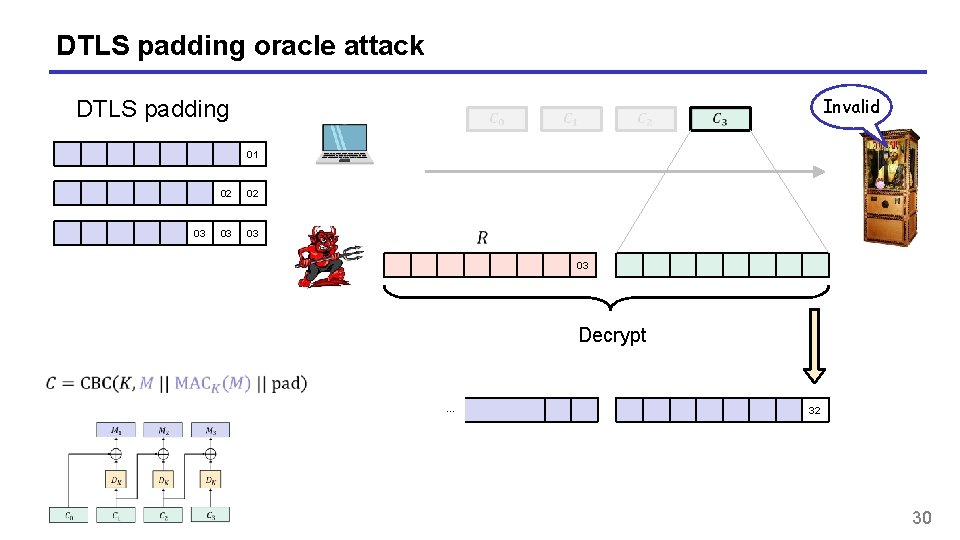
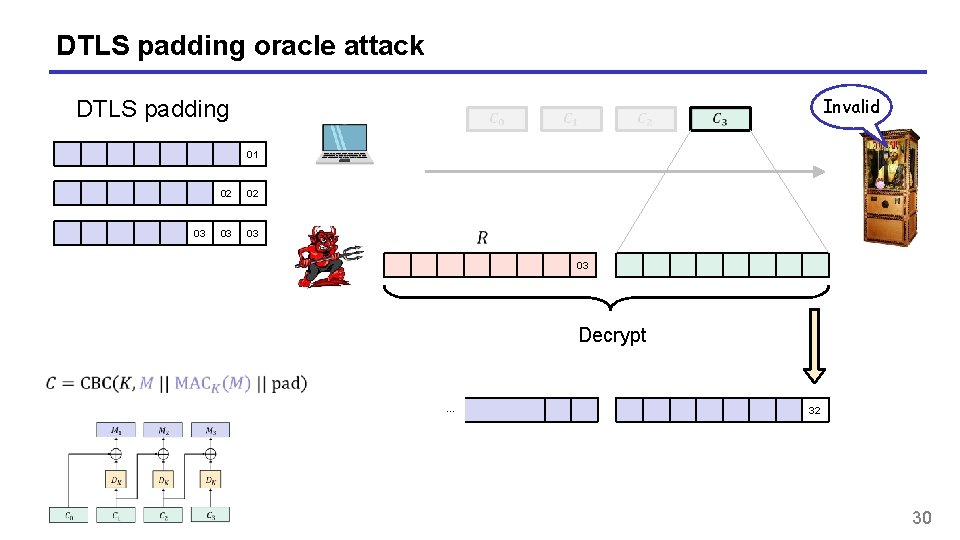
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 03 Decrypt … 32 30
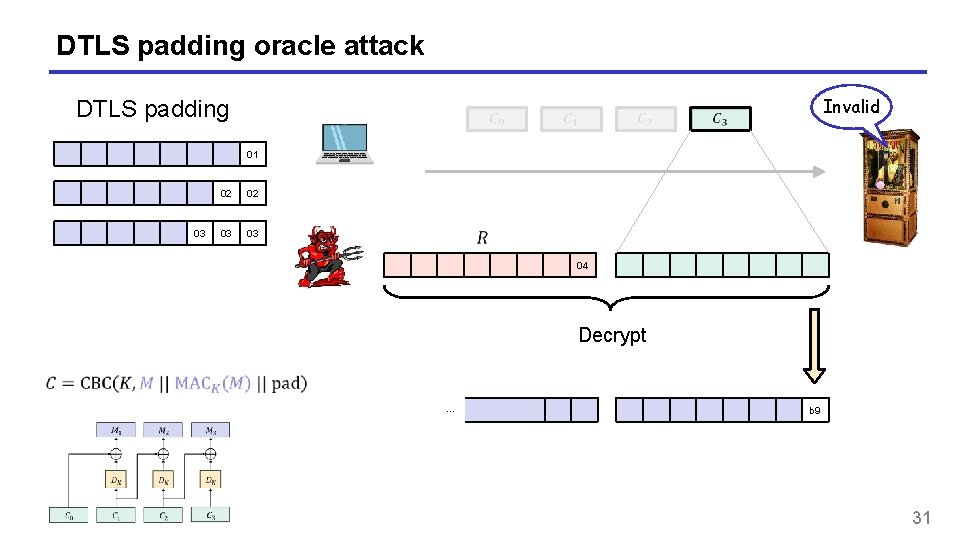
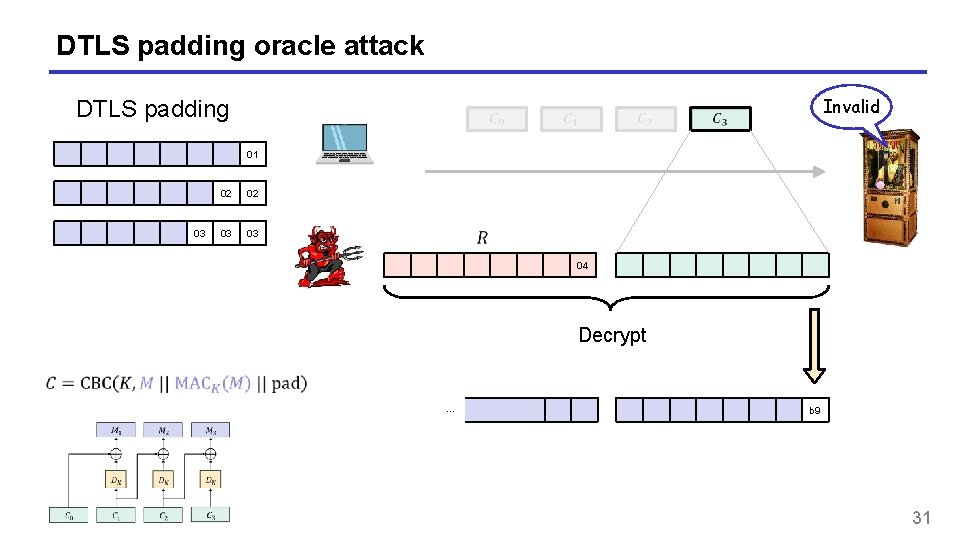
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 04 Decrypt … b 9 31
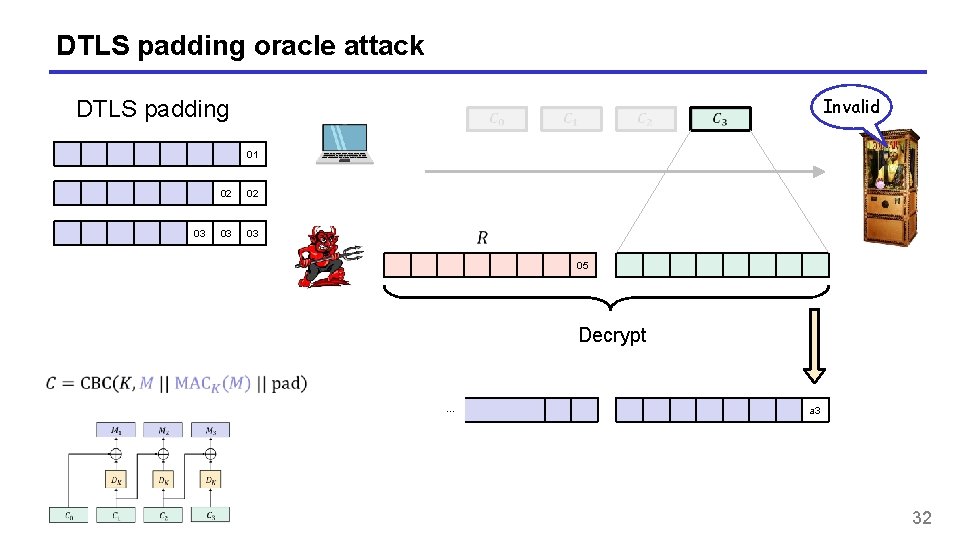
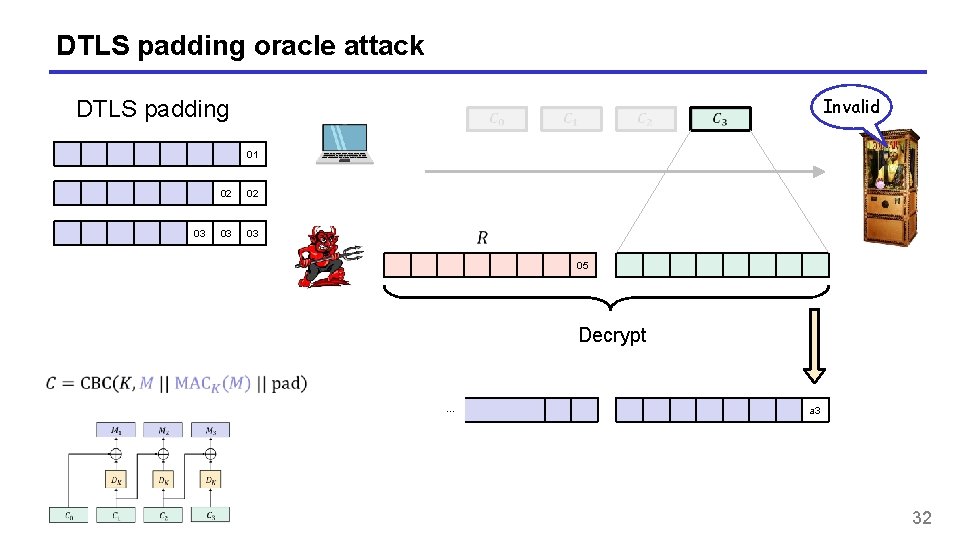
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 05 Decrypt … a 3 32
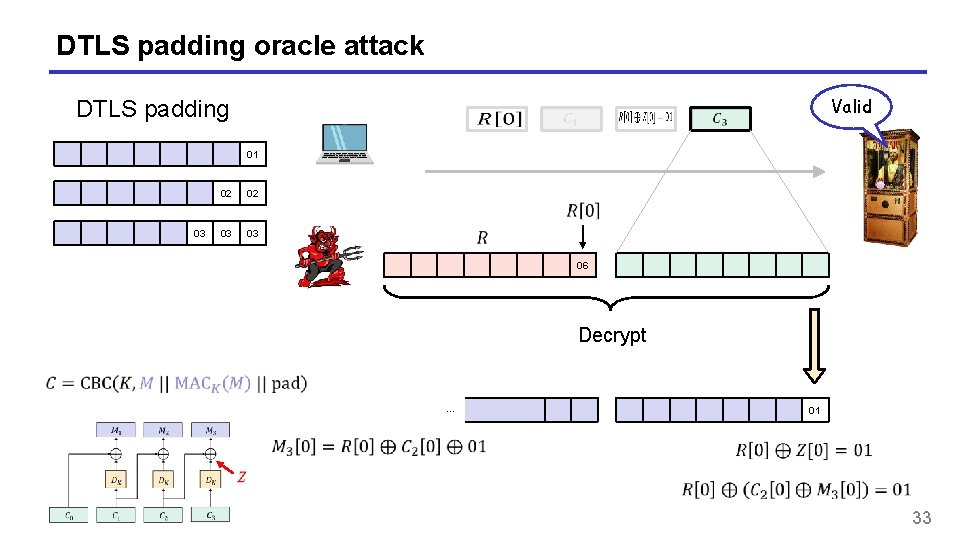
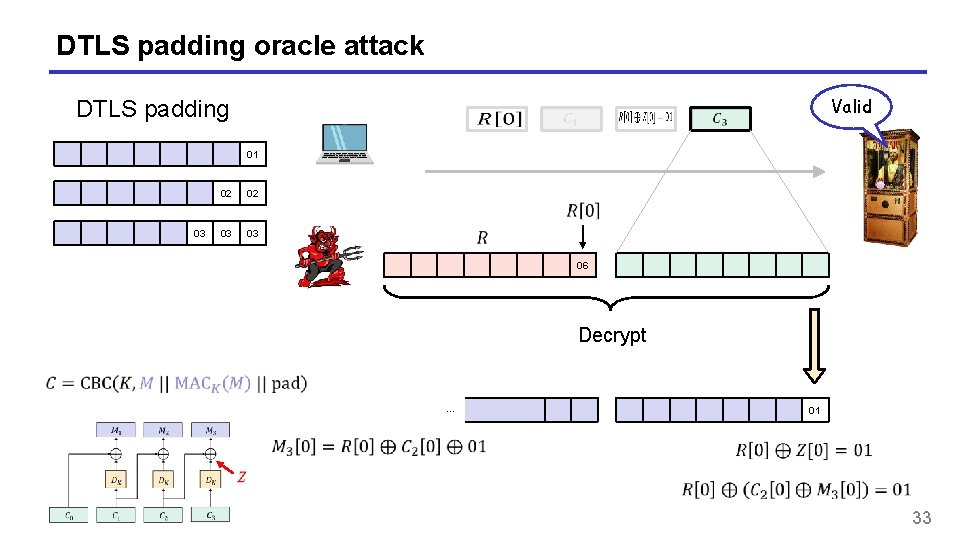
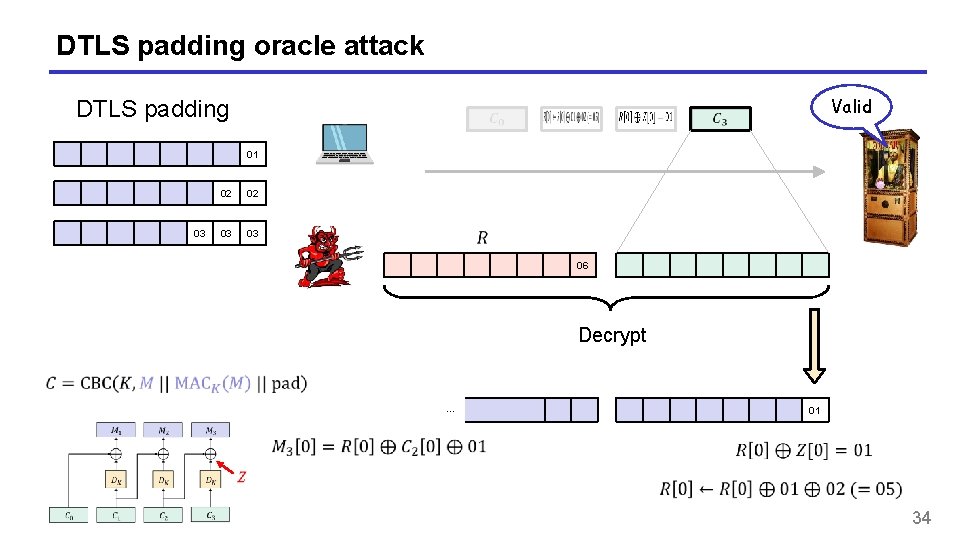
DTLS padding oracle attack Valid DTLS padding 01 03 02 02 03 03 06 Decrypt … 01 33
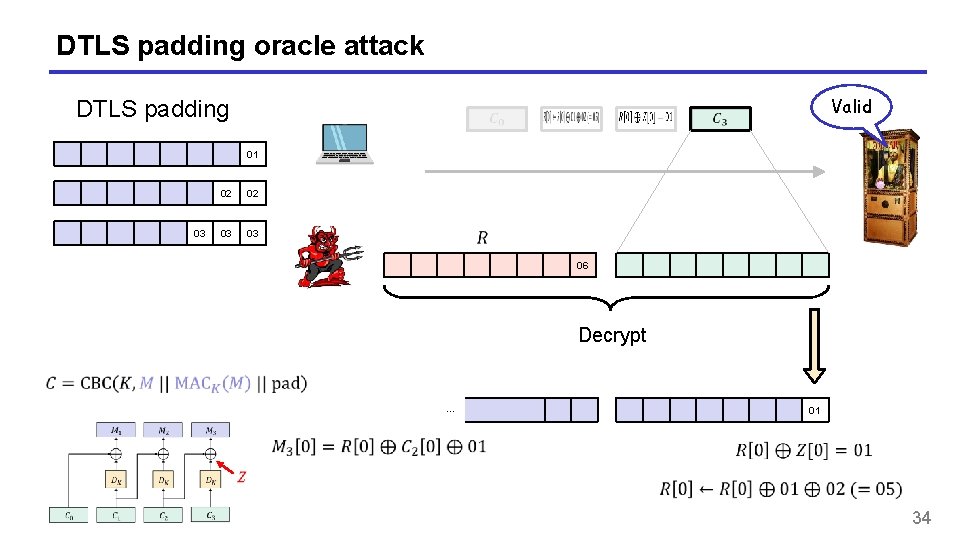
DTLS padding oracle attack Valid DTLS padding 01 03 02 02 03 03 06 Decrypt … 01 34
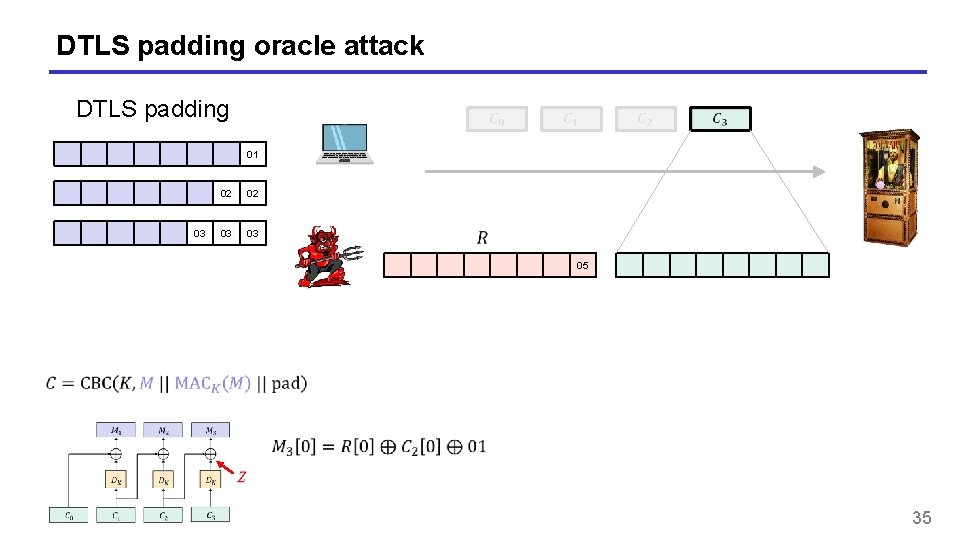
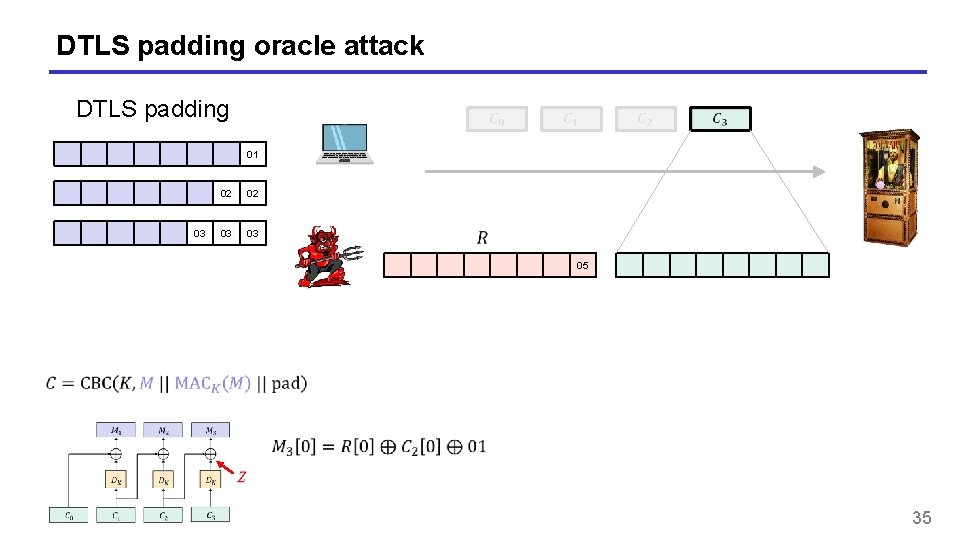
DTLS padding oracle attack DTLS padding 01 03 02 02 03 03 05 35
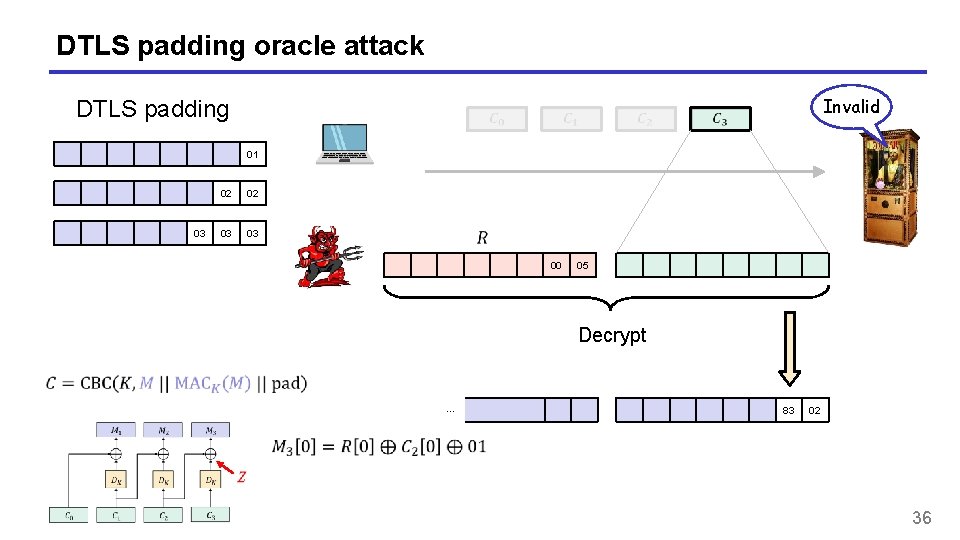
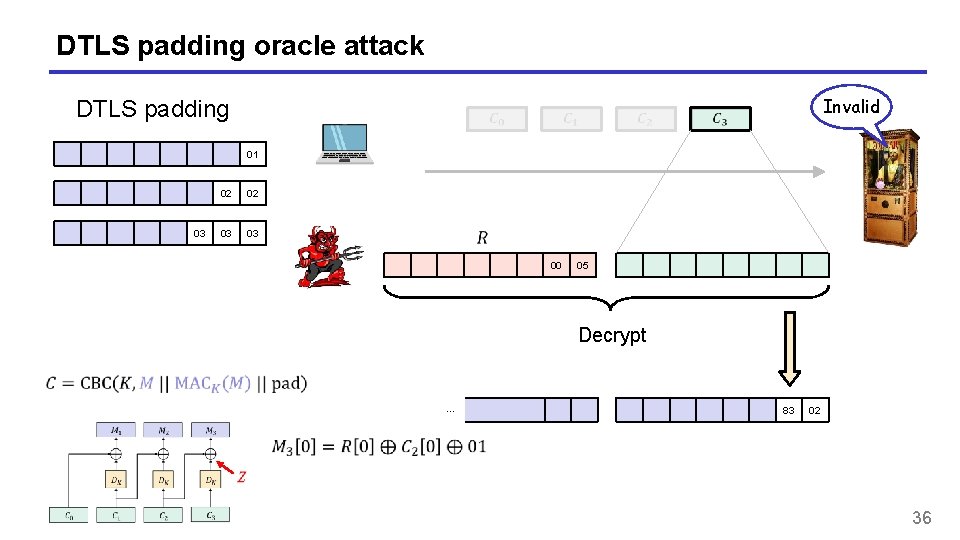
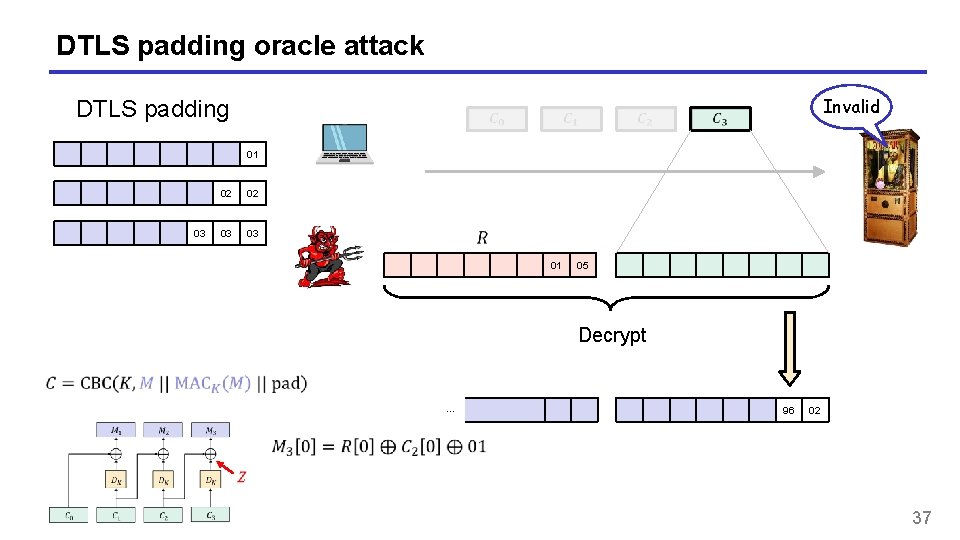
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 00 05 Decrypt … 83 02 36
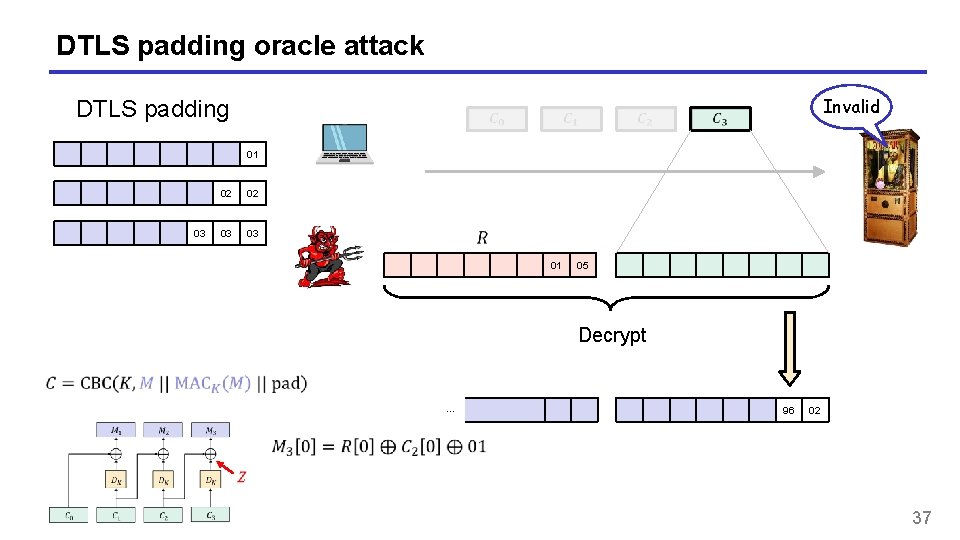
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 01 05 Decrypt … 96 02 37
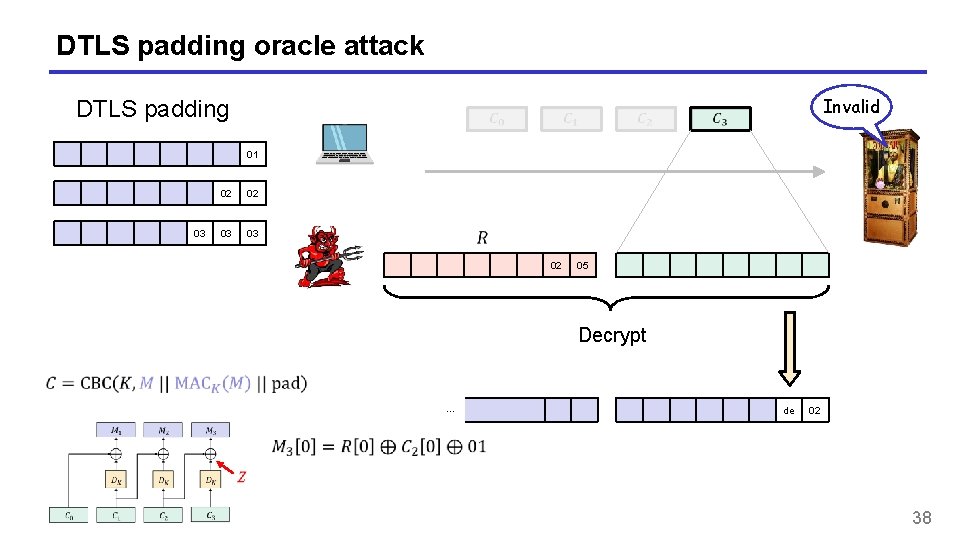
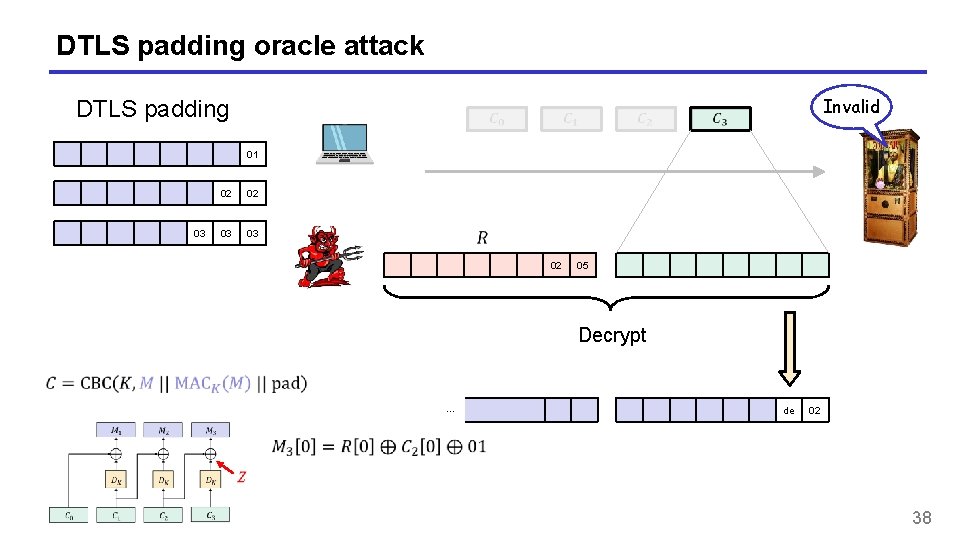
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 02 05 Decrypt … de 02 38
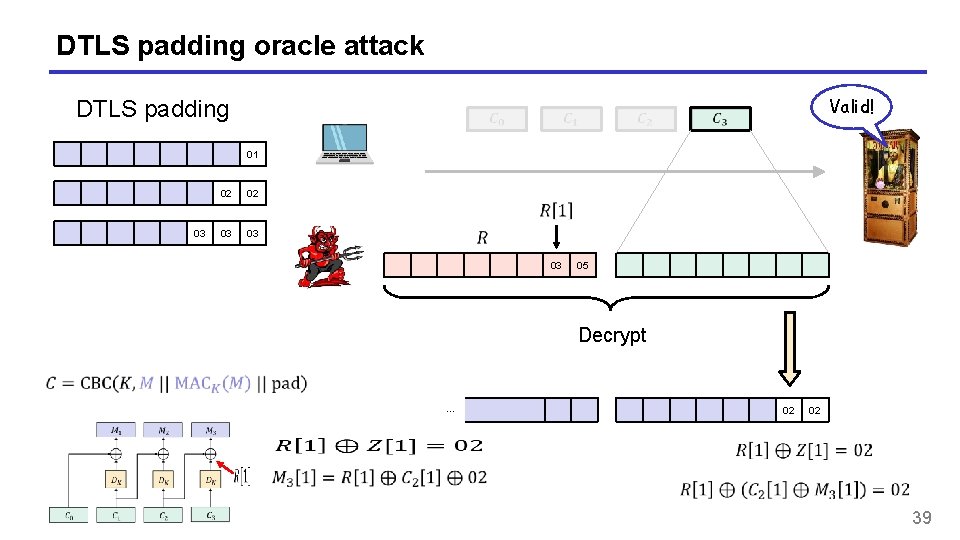
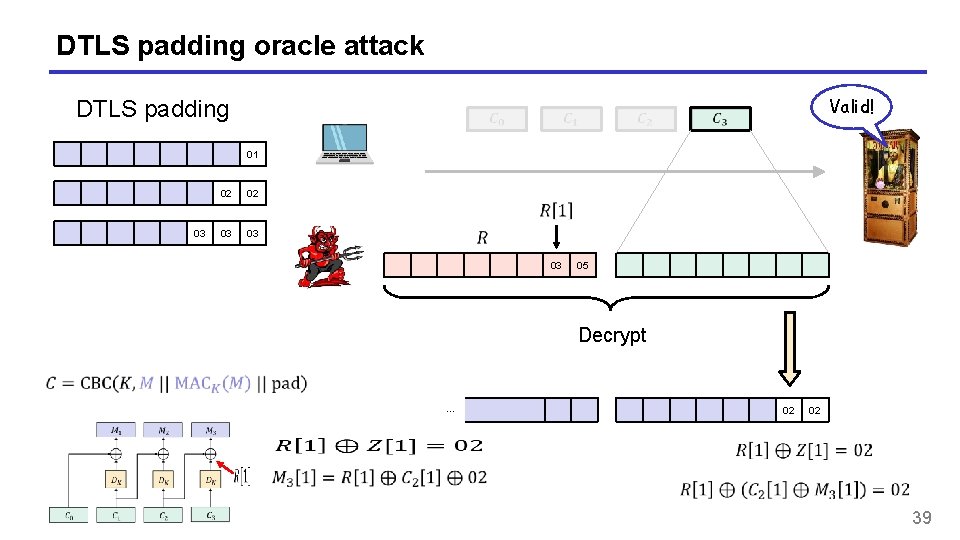
DTLS padding oracle attack Valid! DTLS padding 01 03 02 02 03 03 03 05 Decrypt … 02 02 39
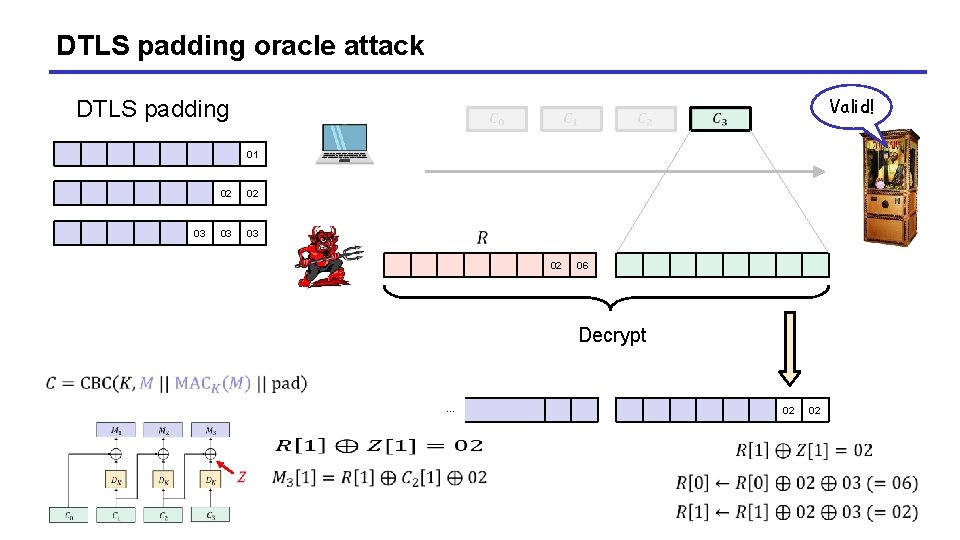
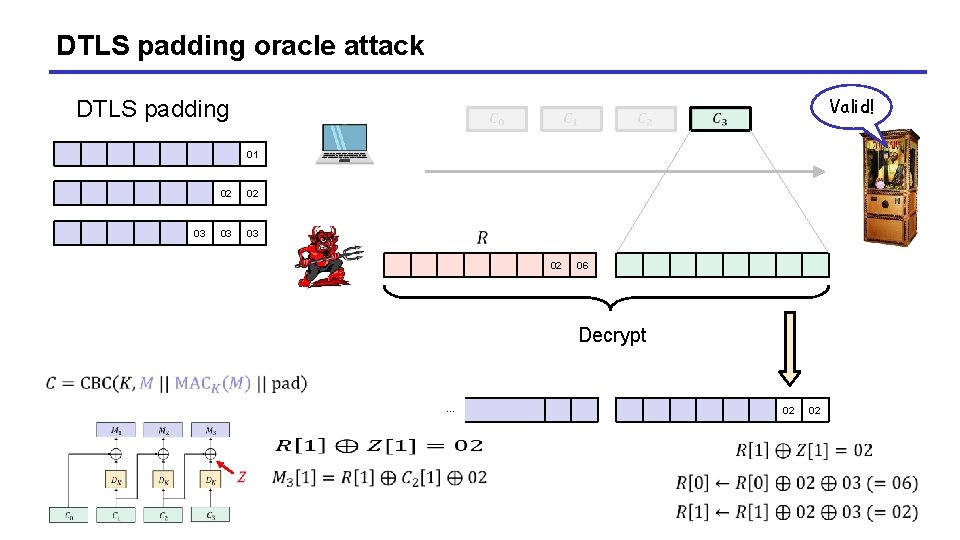
DTLS padding oracle attack Valid! DTLS padding 01 03 02 02 03 03 02 06 Decrypt … 02 02
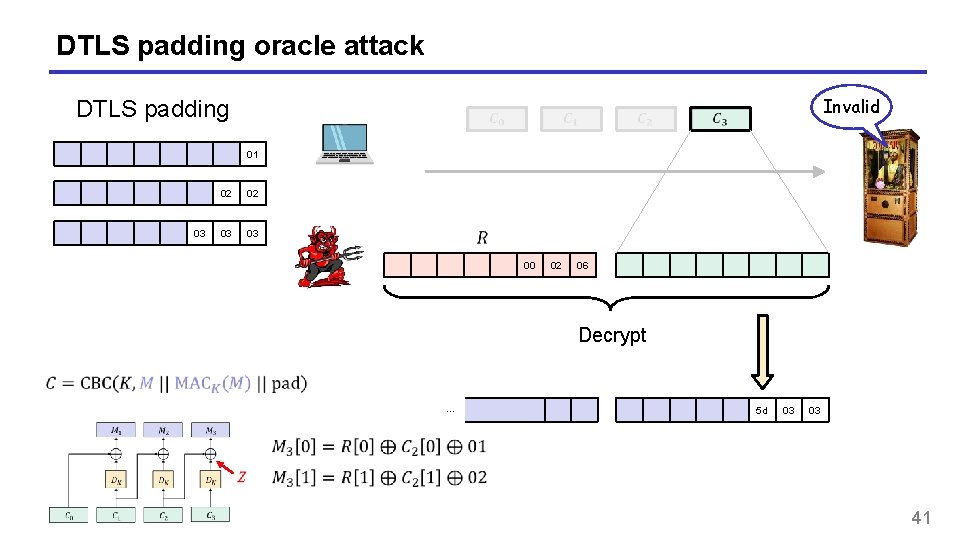
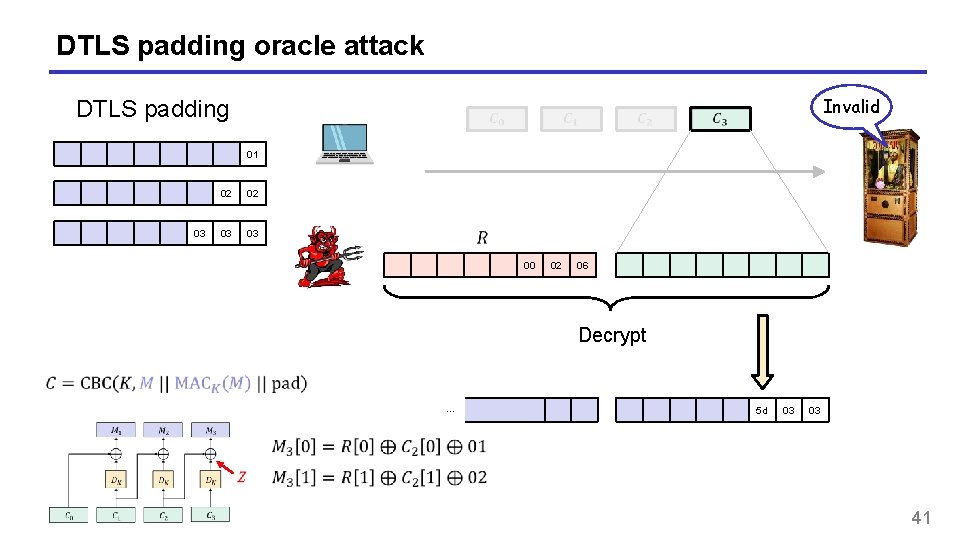
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 00 02 06 Decrypt … 5 d 03 03 41
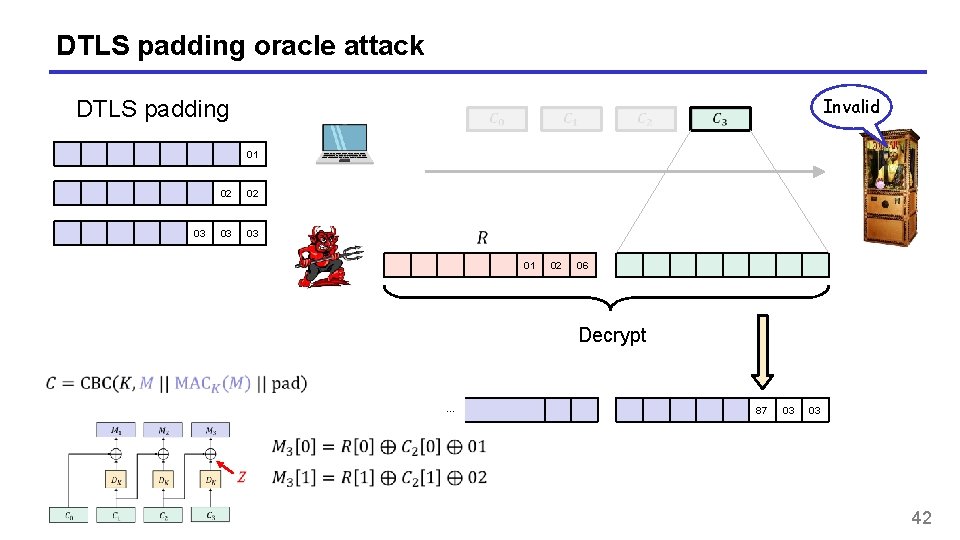
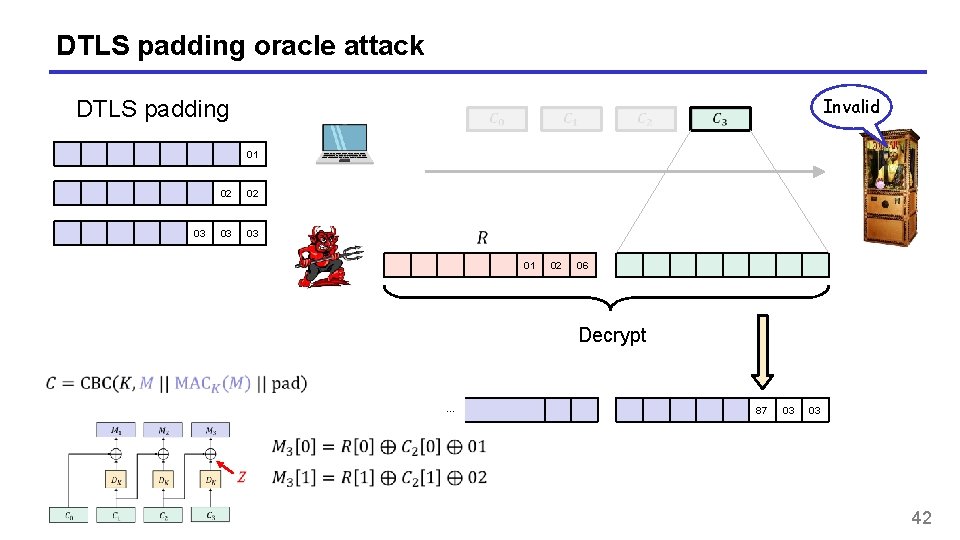
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 01 02 06 Decrypt … 87 03 03 42
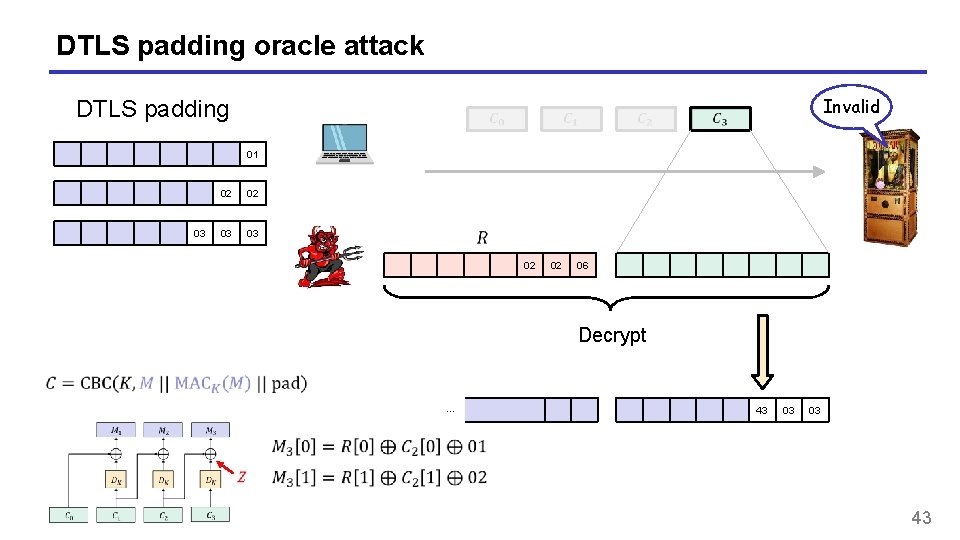
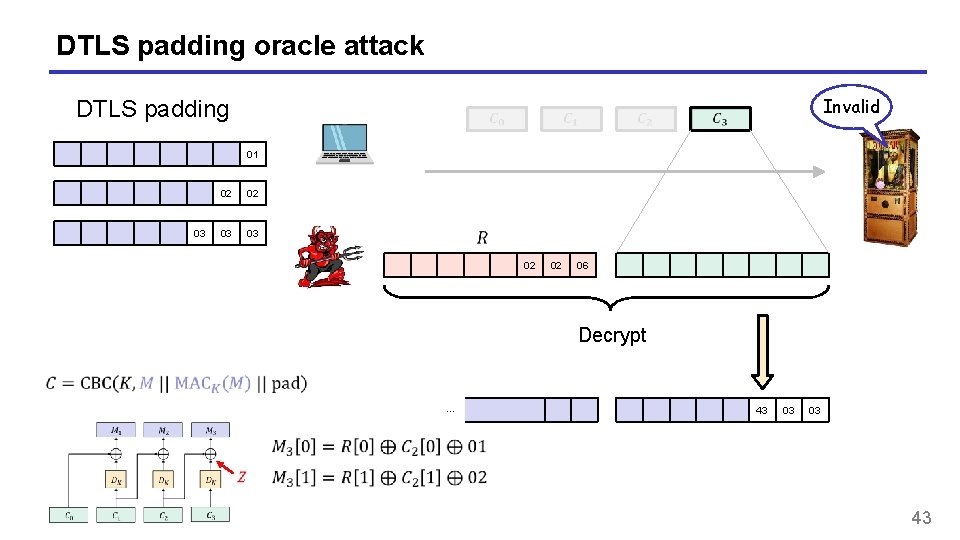
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 02 02 06 Decrypt … 43 03 03 43
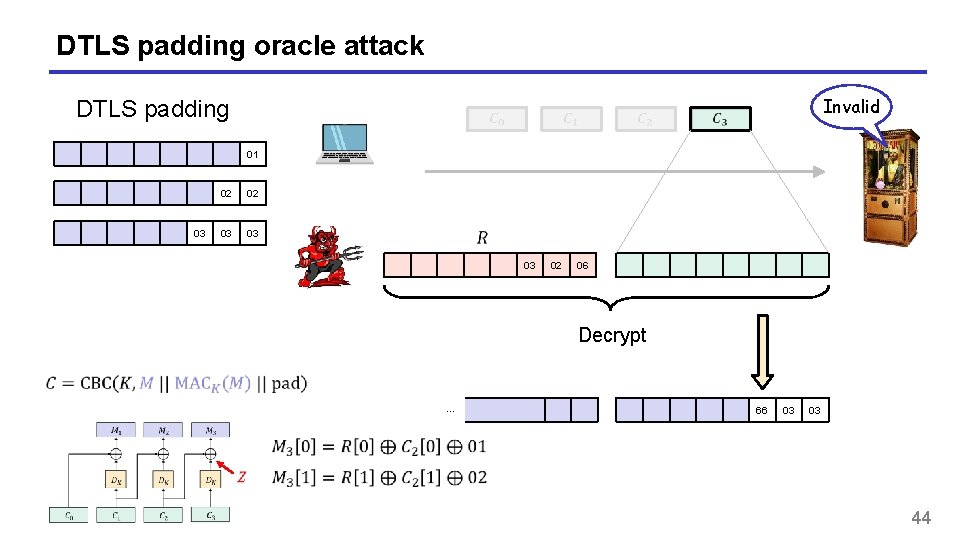
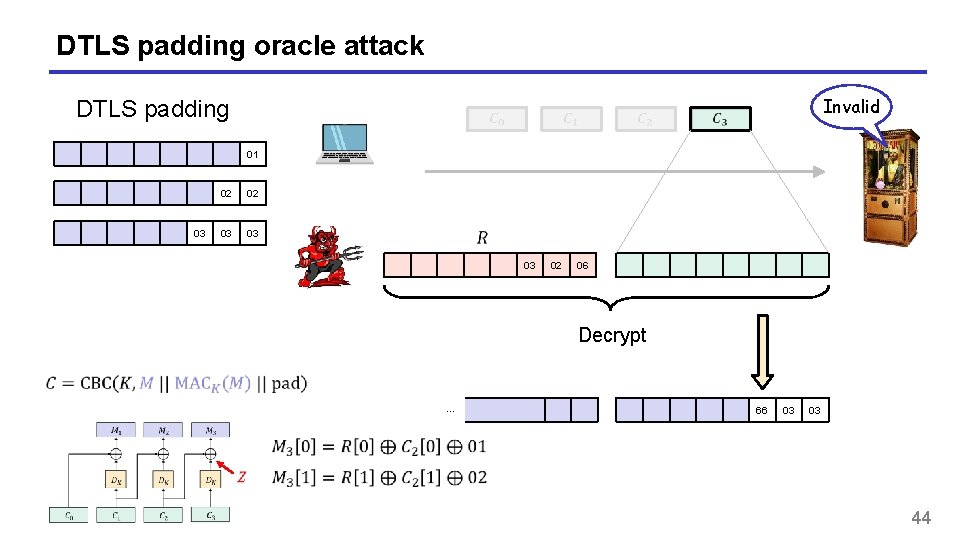
DTLS padding oracle attack Invalid DTLS padding 01 03 02 02 03 03 03 02 06 Decrypt … 66 03 03 44
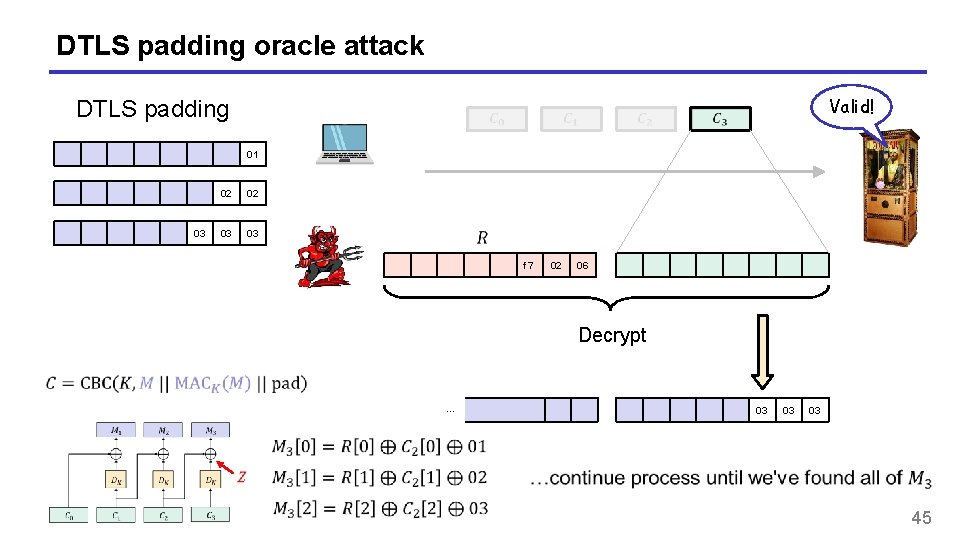
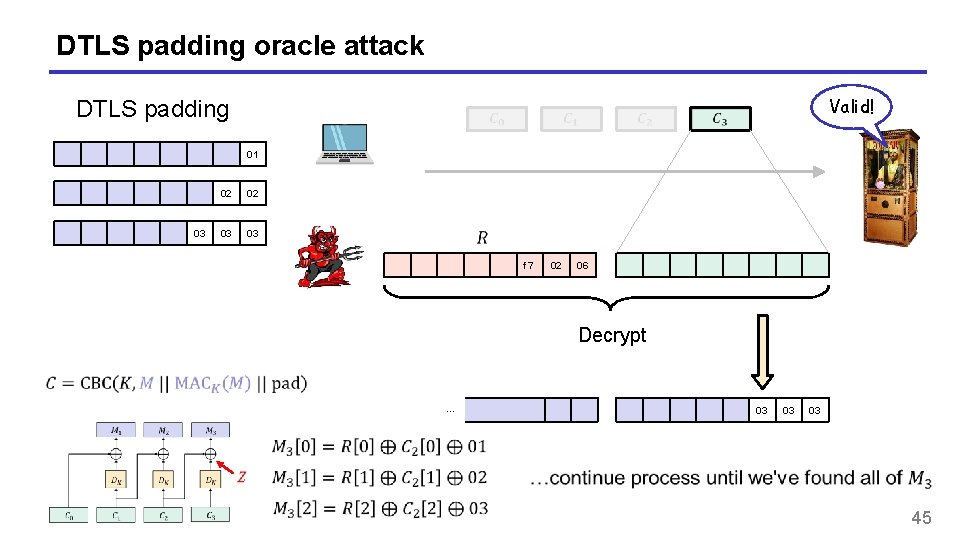
DTLS padding oracle attack Valid! DTLS padding 01 03 02 02 03 03 f 7 02 06 Decrypt … 03 03 03 45
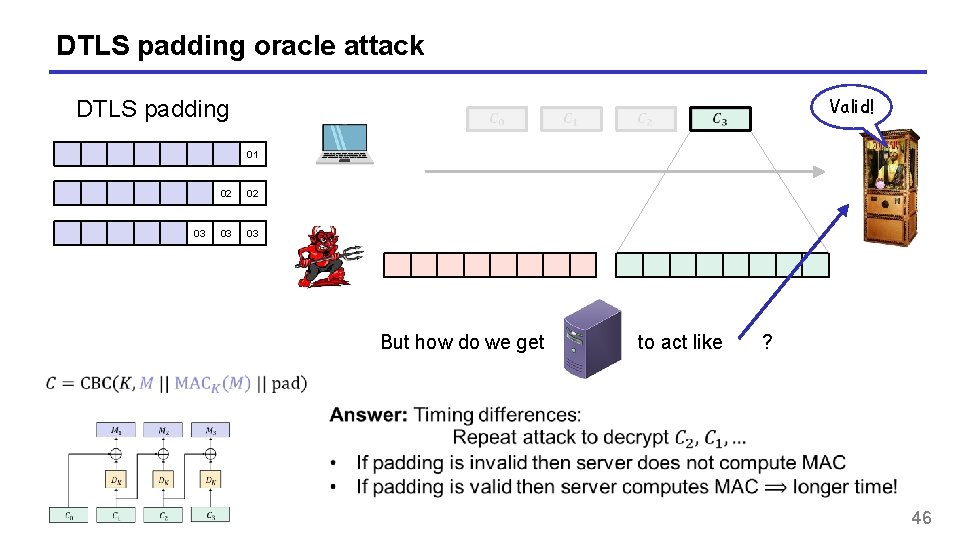
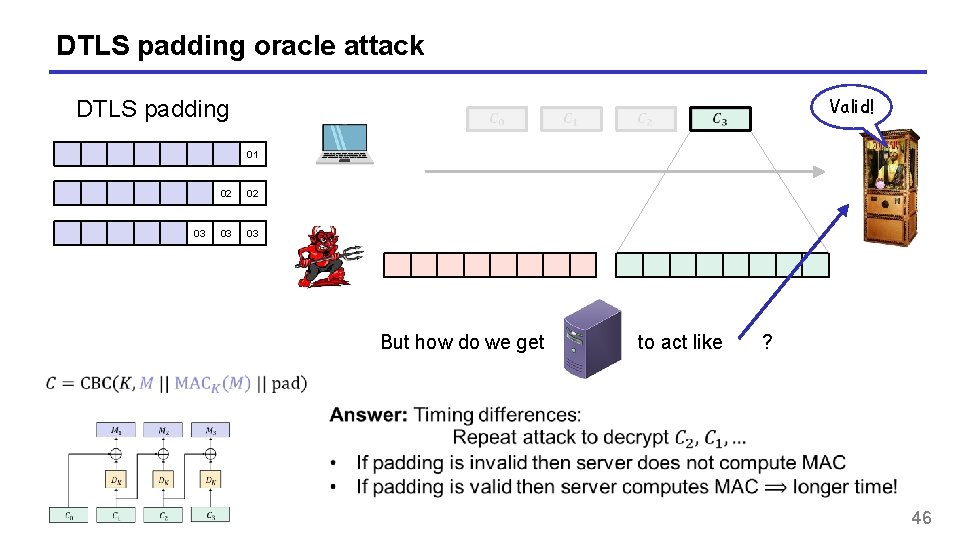
DTLS padding oracle attack Valid! DTLS padding 01 03 02 02 03 03 But how do we get to act like ? 46
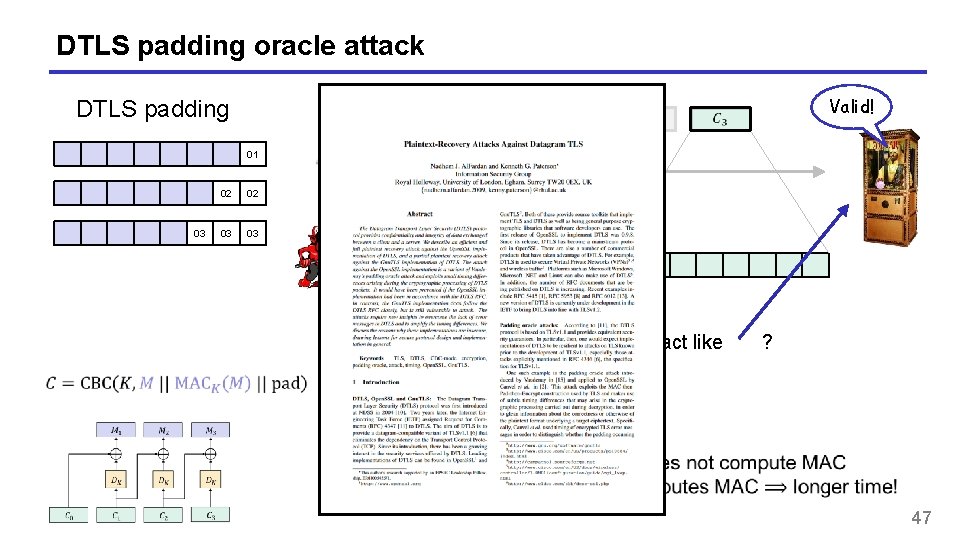
DTLS padding oracle attack Valid! DTLS padding 01 03 02 02 03 03 But how do we get to act like ? 47
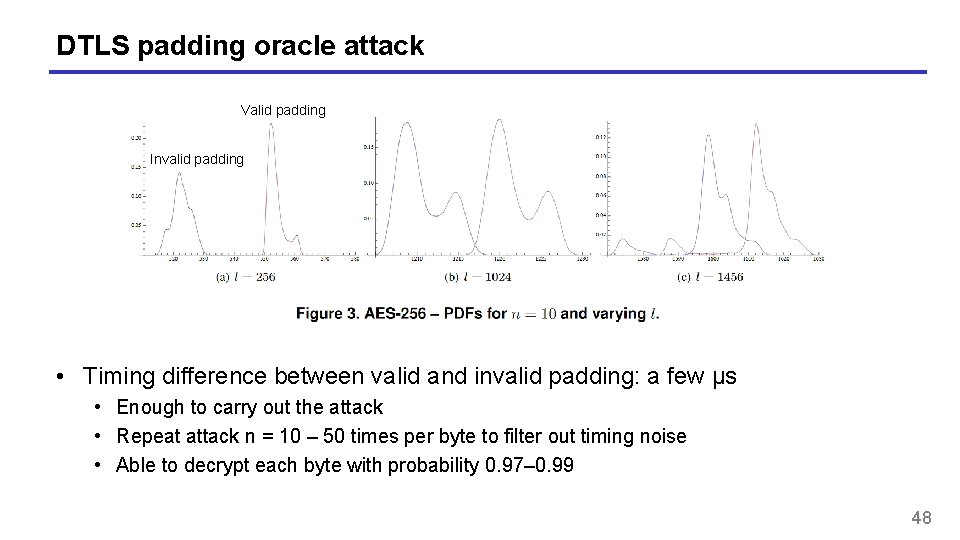
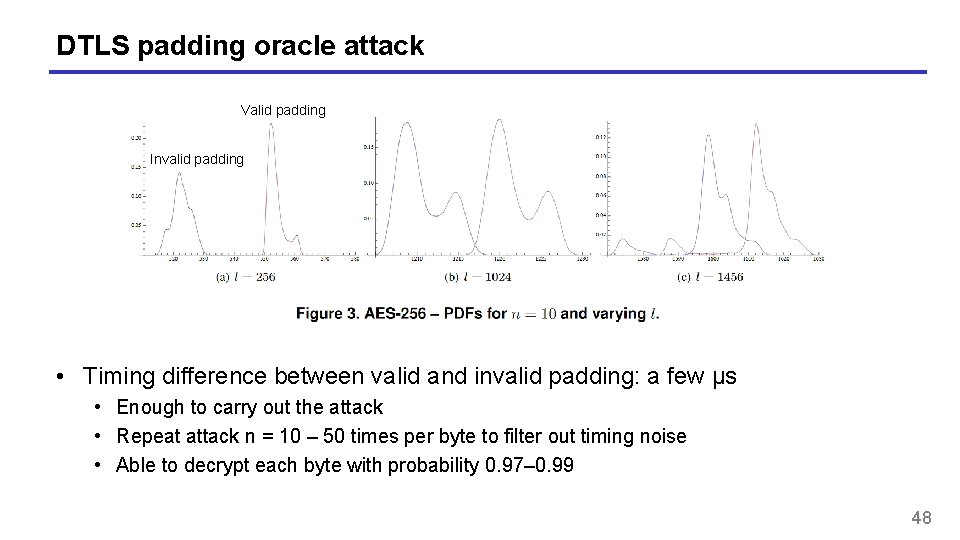
DTLS padding oracle attack Valid padding Invalid padding • Timing difference between valid and invalid padding: a few μs • Enough to carry out the attack • Repeat attack n = 10 – 50 times per byte to filter out timing noise • Able to decrypt each byte with probability 0. 97– 0. 99 48
DTLS padding oracle attack – conclusions 49
Authenticated encryption – definitions 50
Authenticated encryption • Want privacy and integrity from a single primitive: an authenticated encryption scheme • Syntactically the same as a normal encryption scheme 51
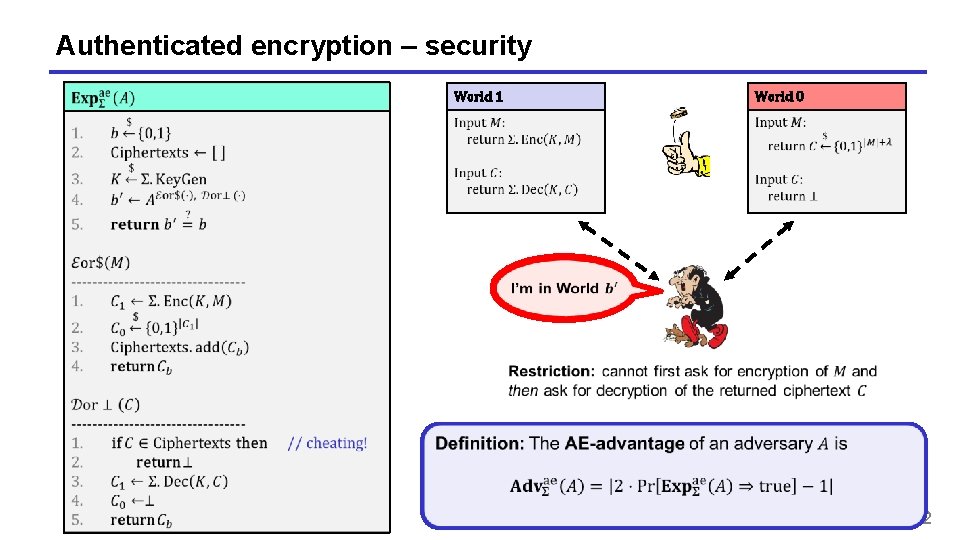
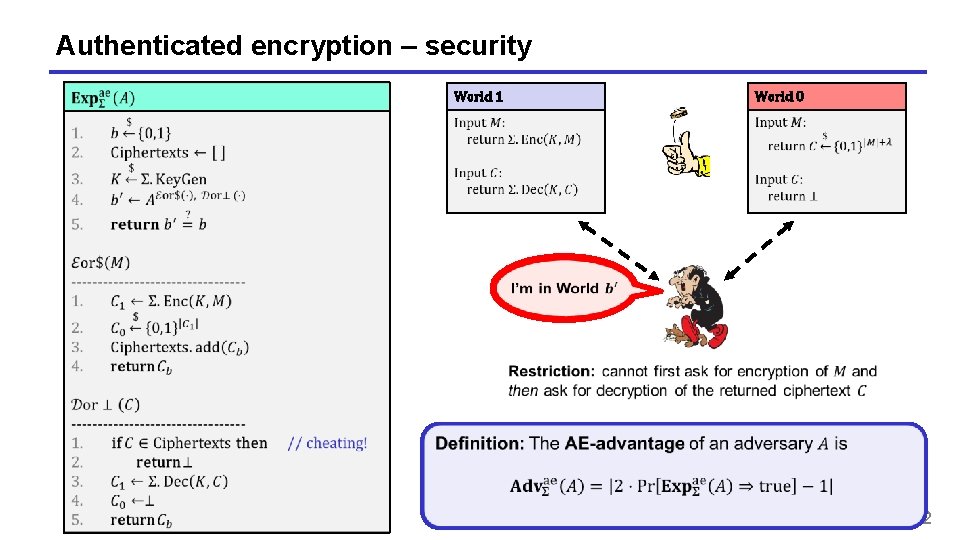
Authenticated encryption – security World 1 World 0 52
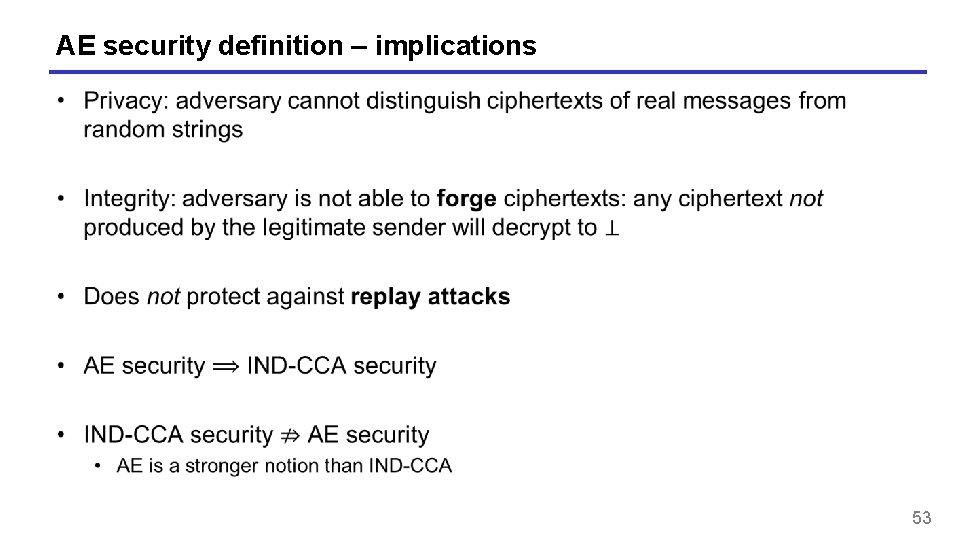
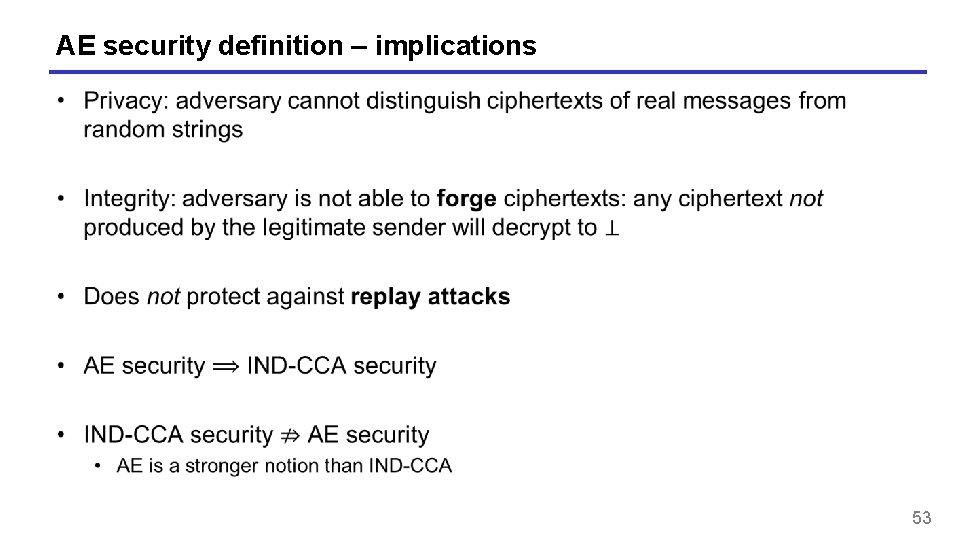
AE security definition – implications 53
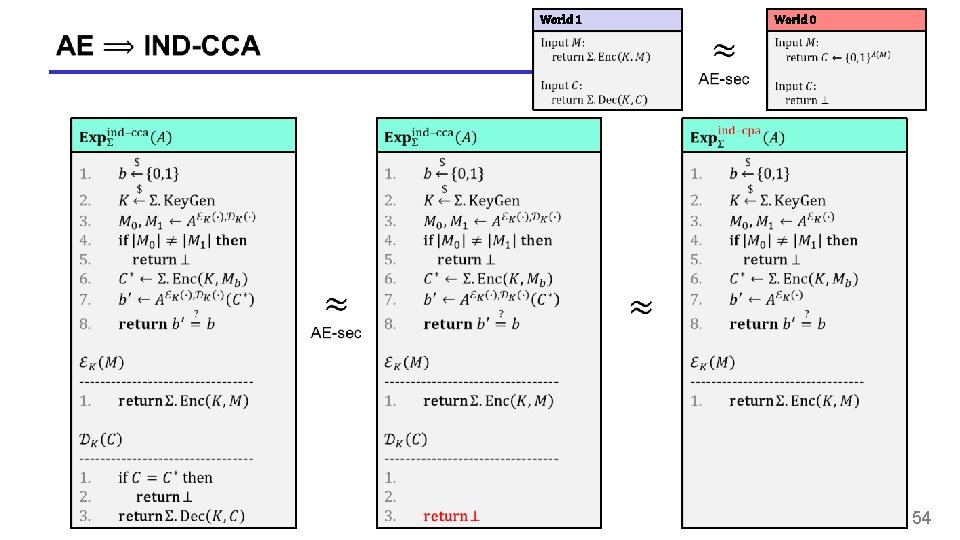
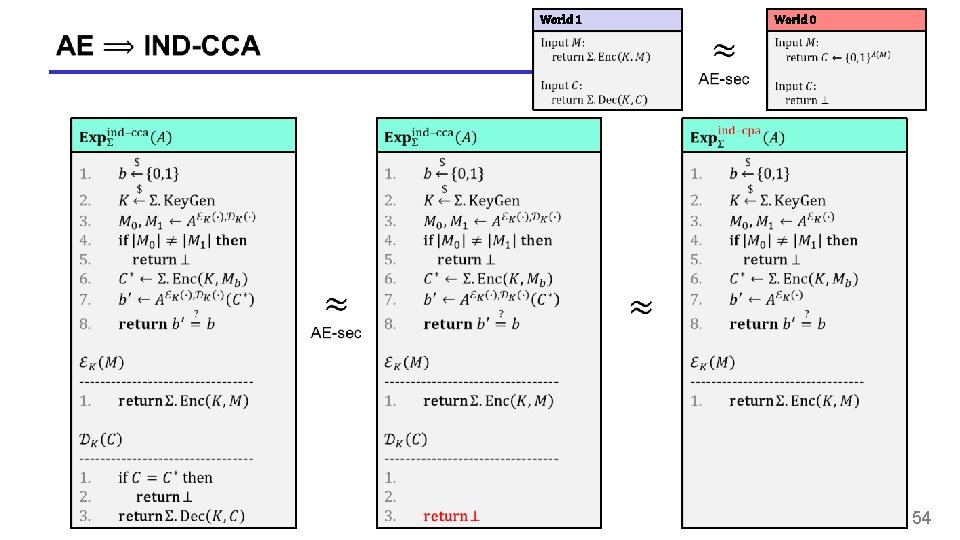
World 1 World 0 54
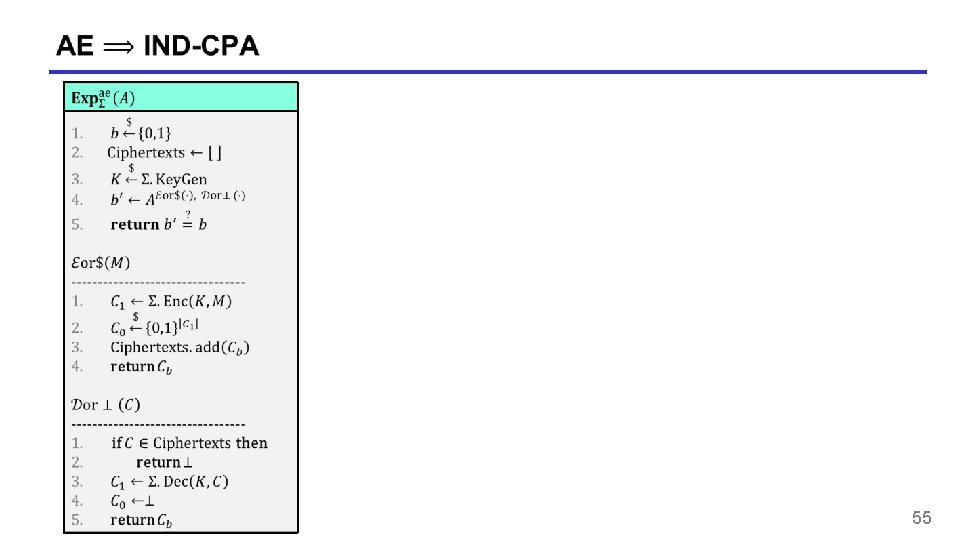
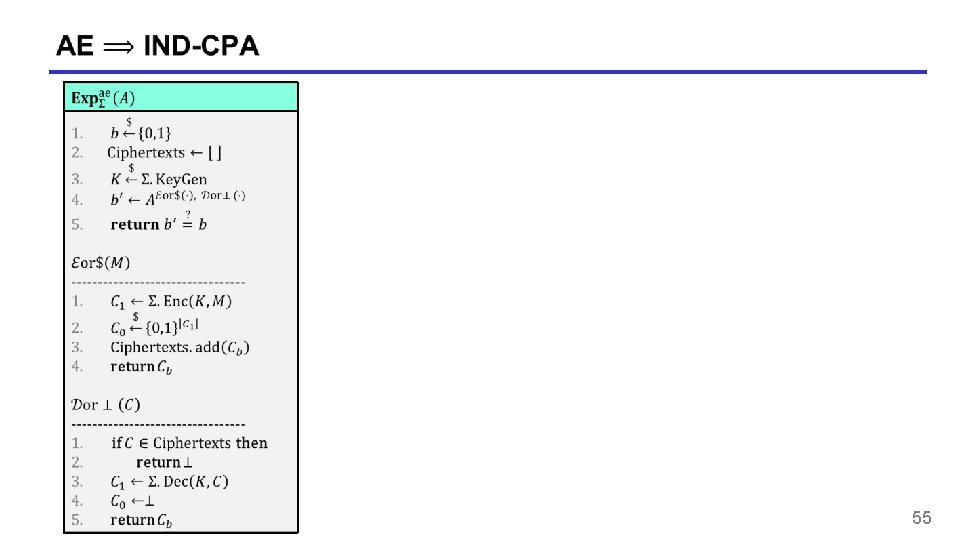
55
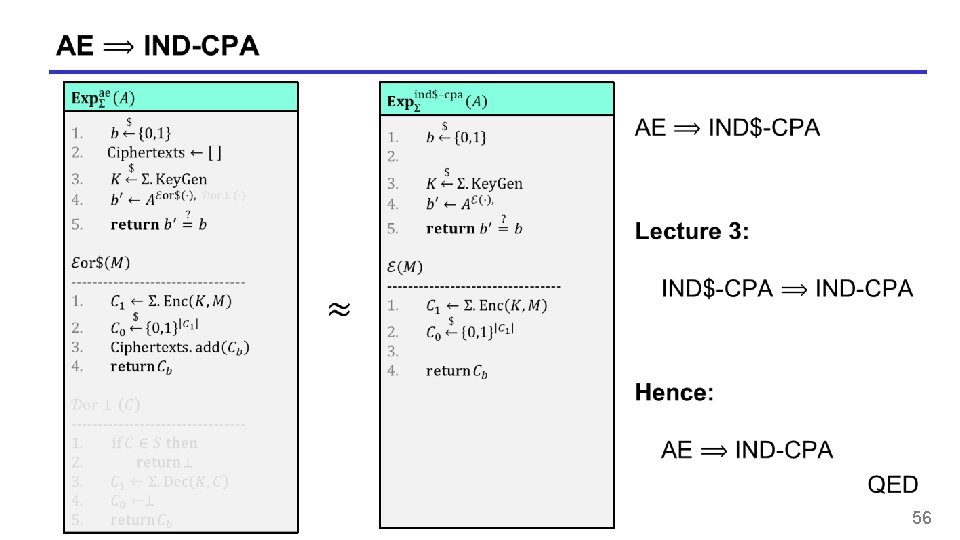
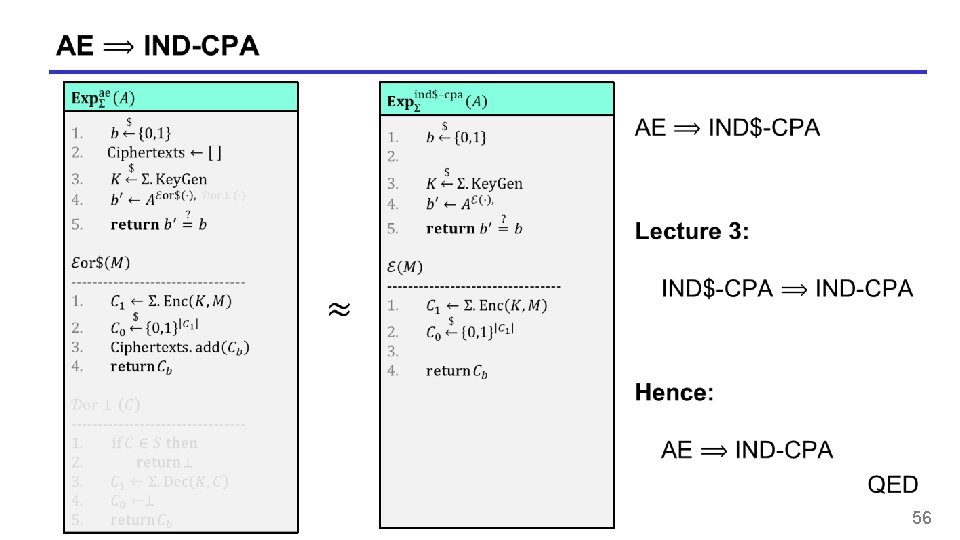
56
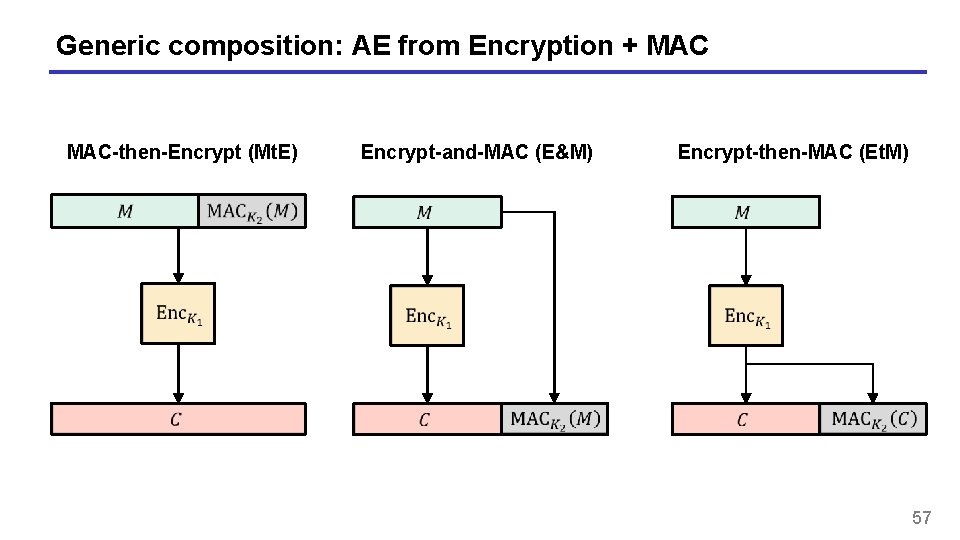
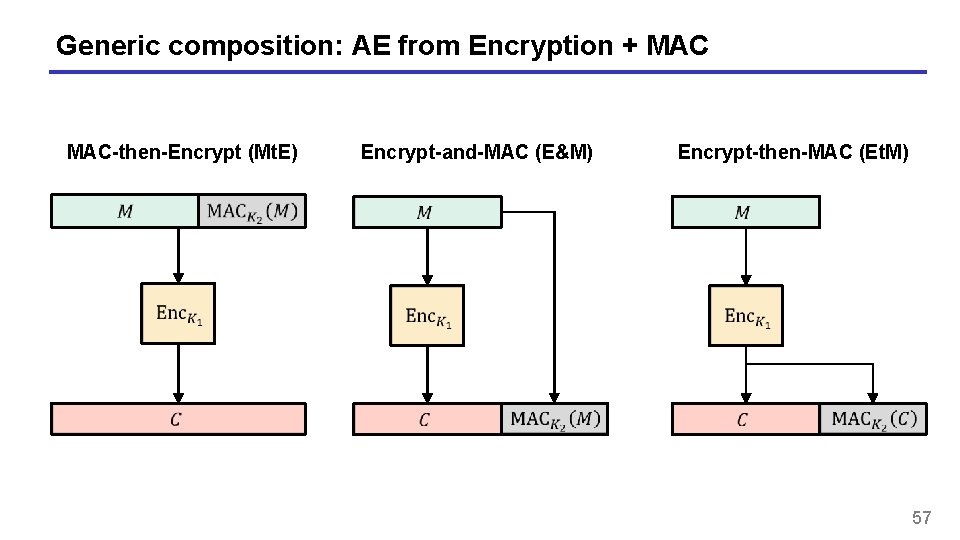
Generic composition: AE from Encryption + MAC-then-Encrypt (Mt. E) Encrypt-and-MAC (E&M) Encrypt-then-MAC (Et. M) 57
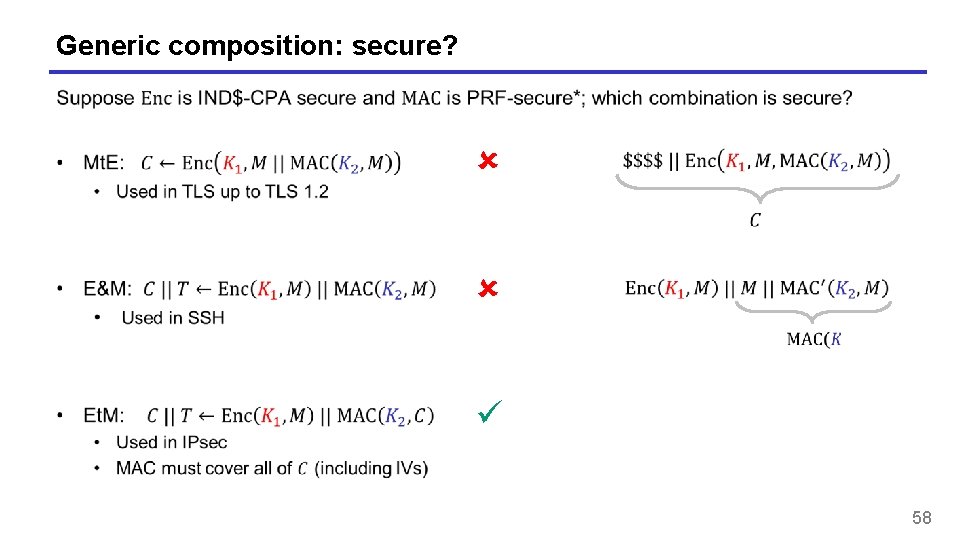
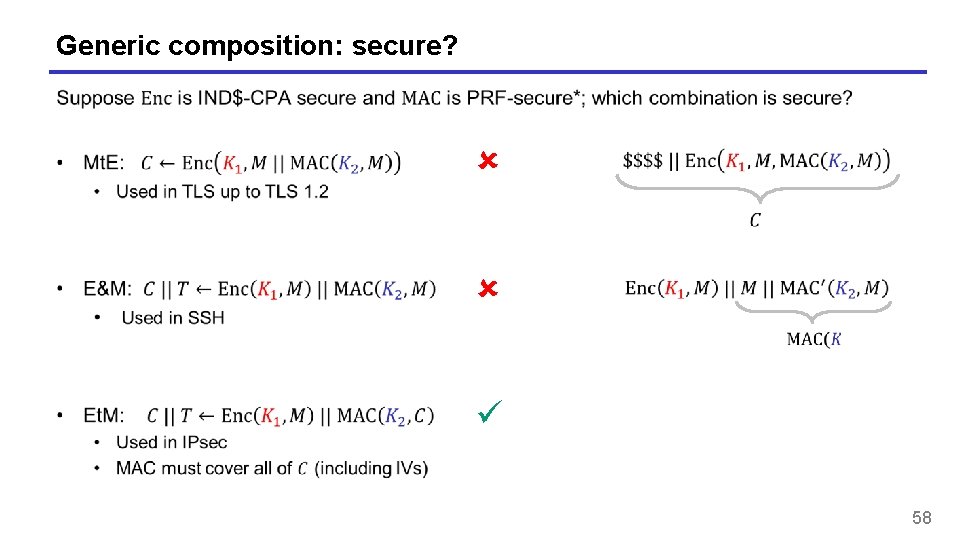
Generic composition: secure? 58
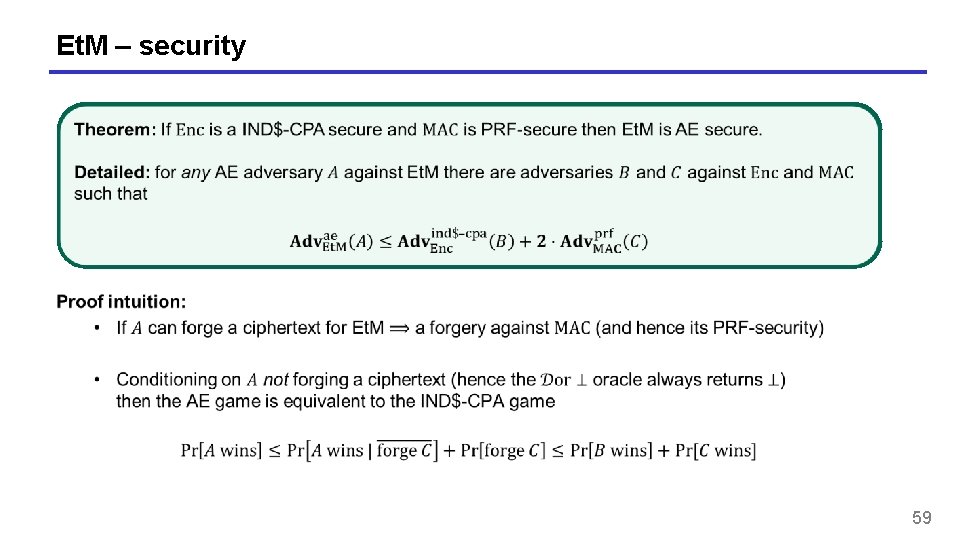
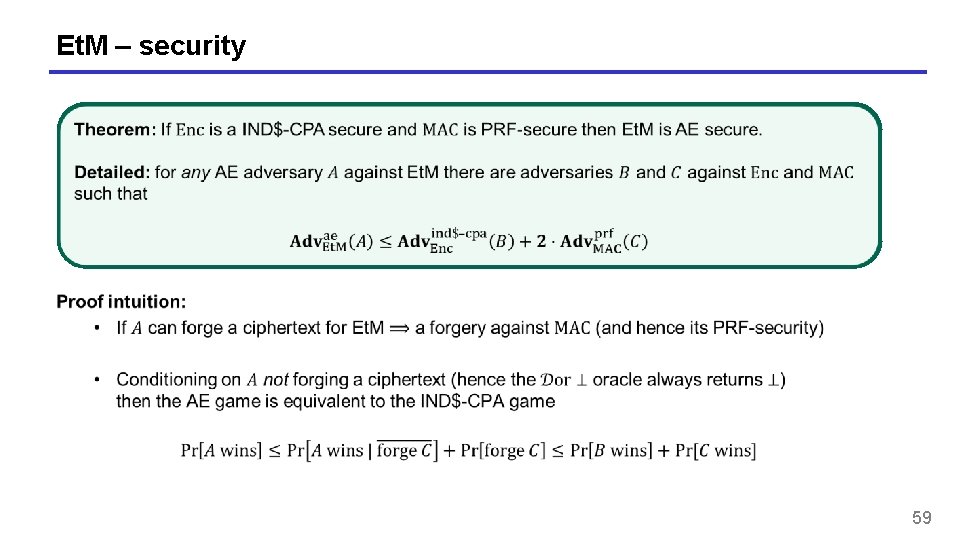
Et. M – security 59
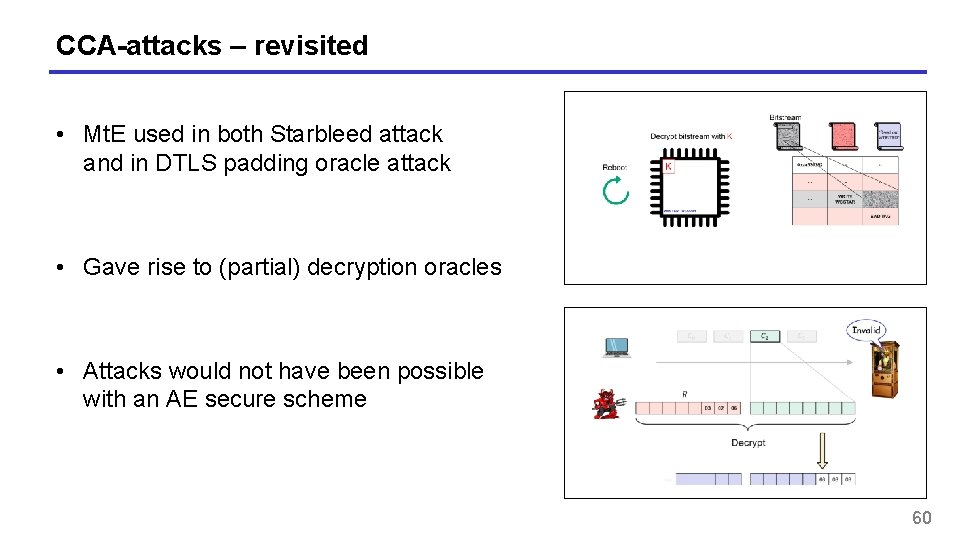
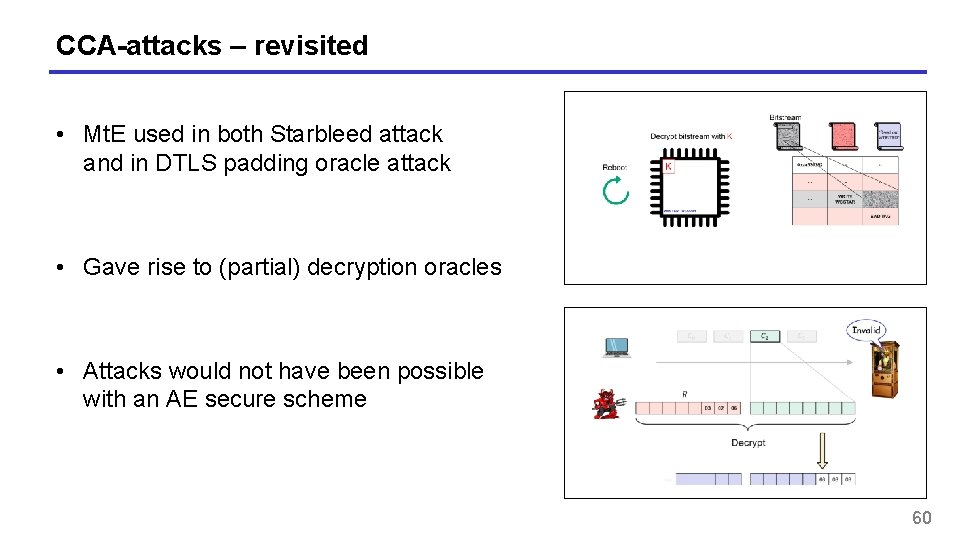
CCA-attacks – revisited • Mt. E used in both Starbleed attack and in DTLS padding oracle attack • Gave rise to (partial) decryption oracles • Attacks would not have been possible with an AE secure scheme 60
AEAD – Authenticated encryption with associated data 61
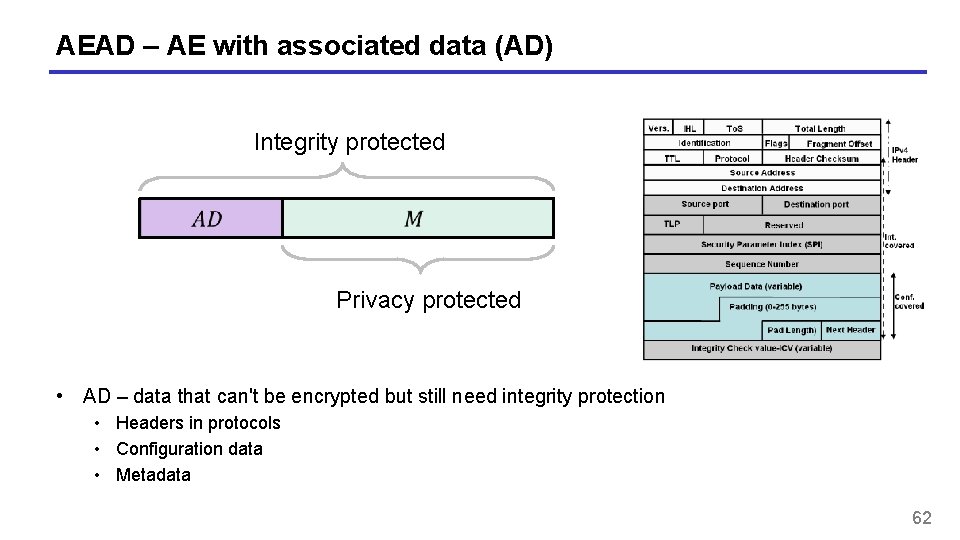
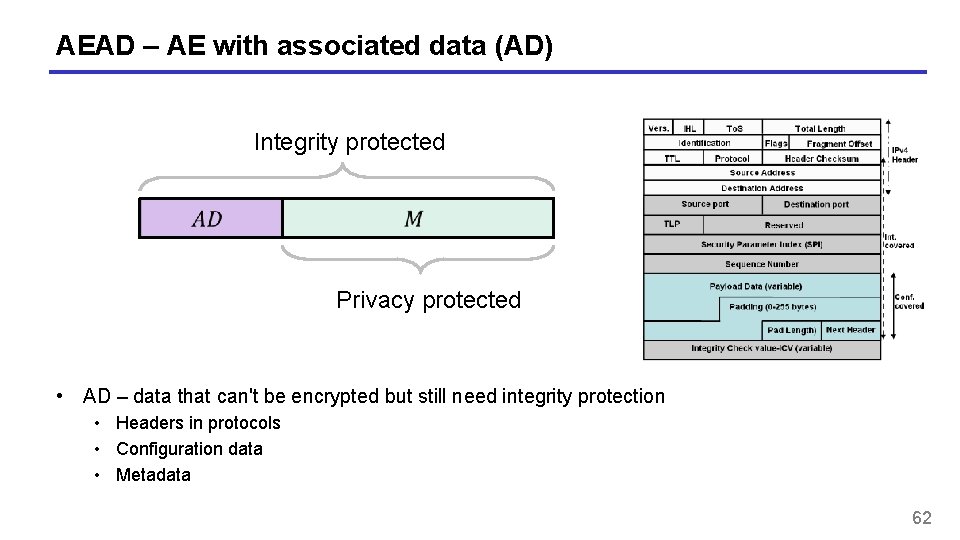
AEAD – AE with associated data (AD) Integrity protected Privacy protected • AD – data that can't be encrypted but still need integrity protection • Headers in protocols • Configuration data • Metadata 62
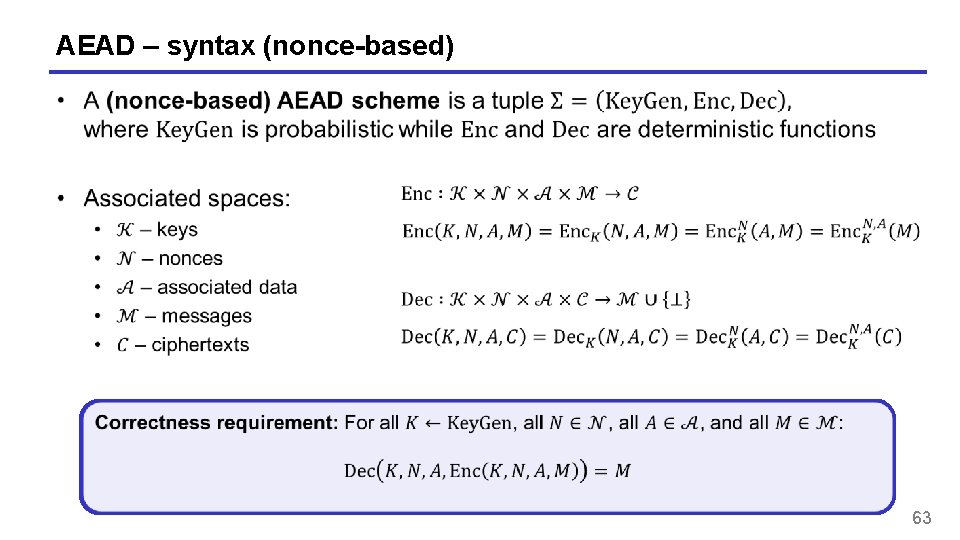
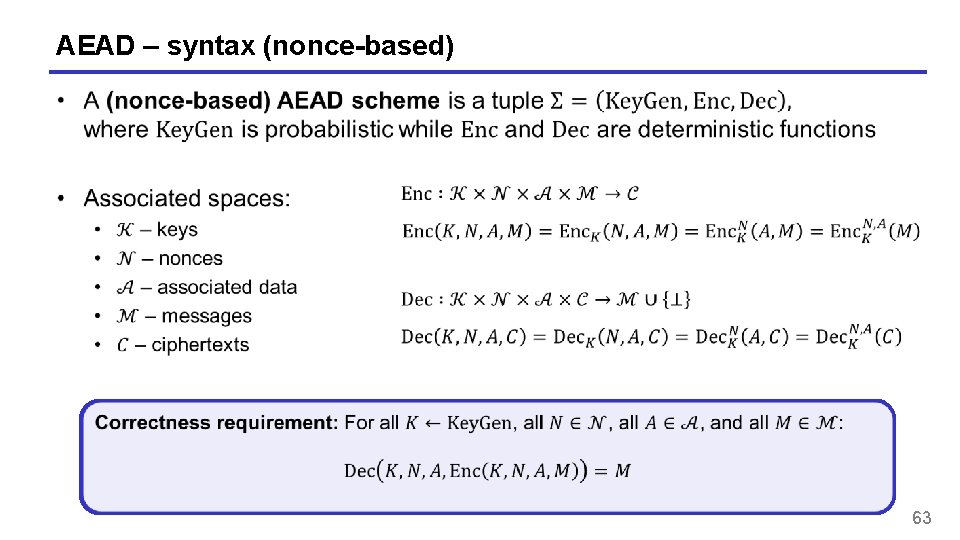
AEAD – syntax (nonce-based) 63
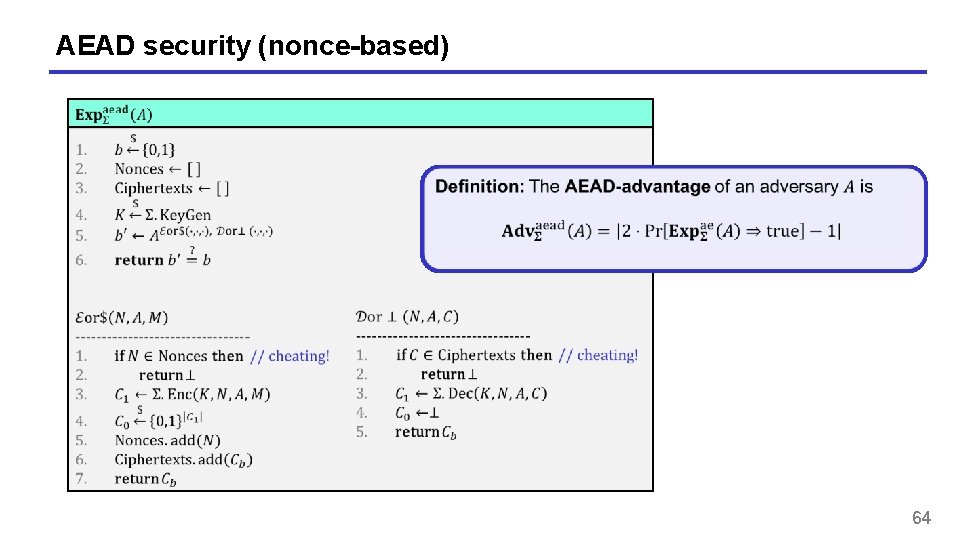
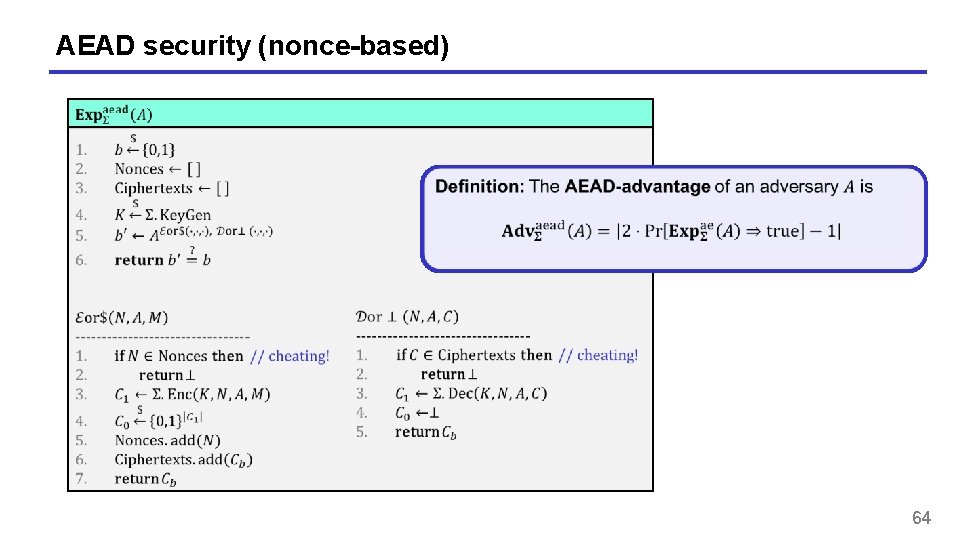
AEAD security (nonce-based) 64
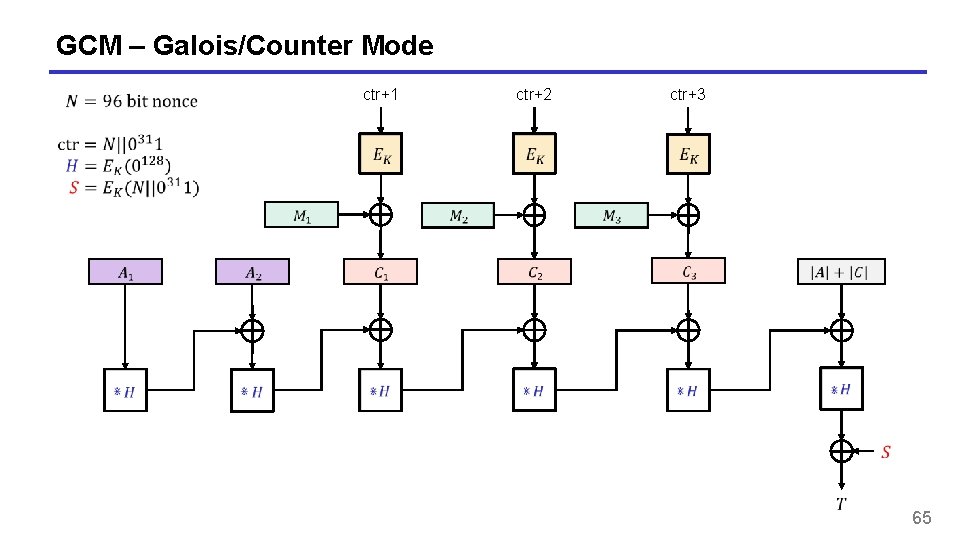
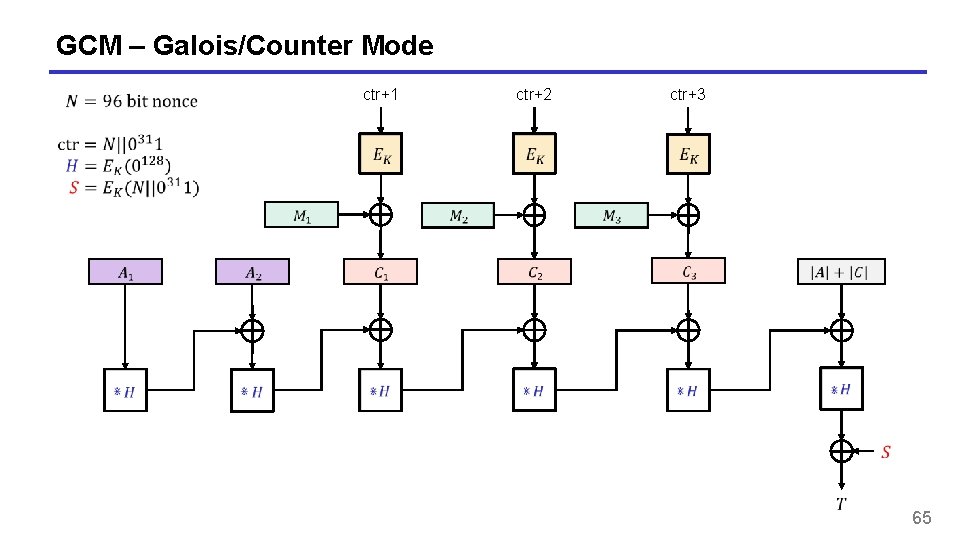
GCM – Galois/Counter Mode ctr+1 ctr+2 ctr+3 65
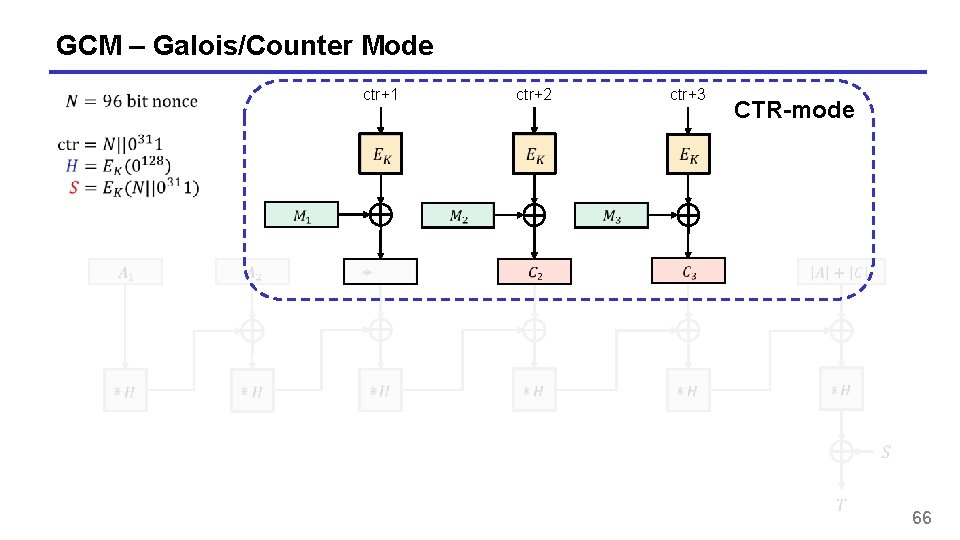
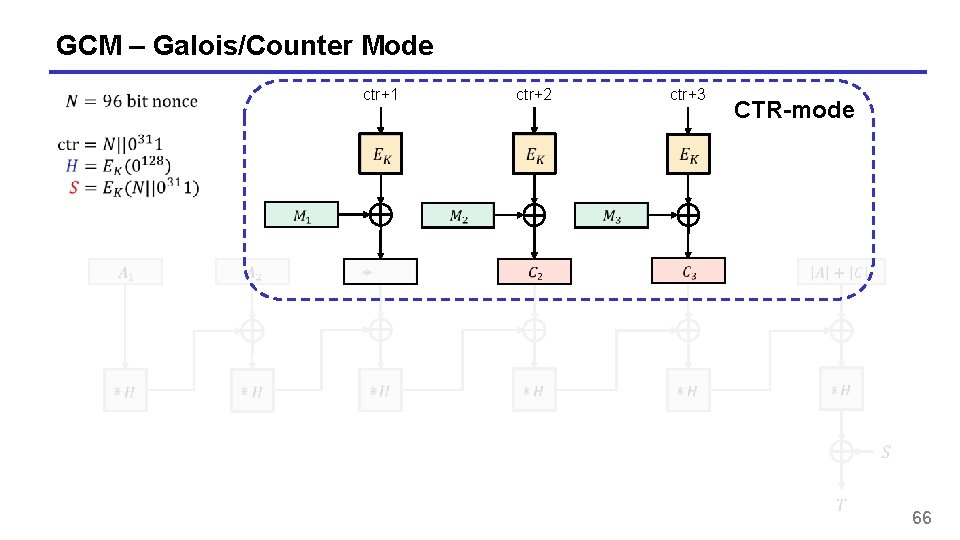
GCM – Galois/Counter Mode ctr+1 ctr+2 ctr+3 CTR-mode 66
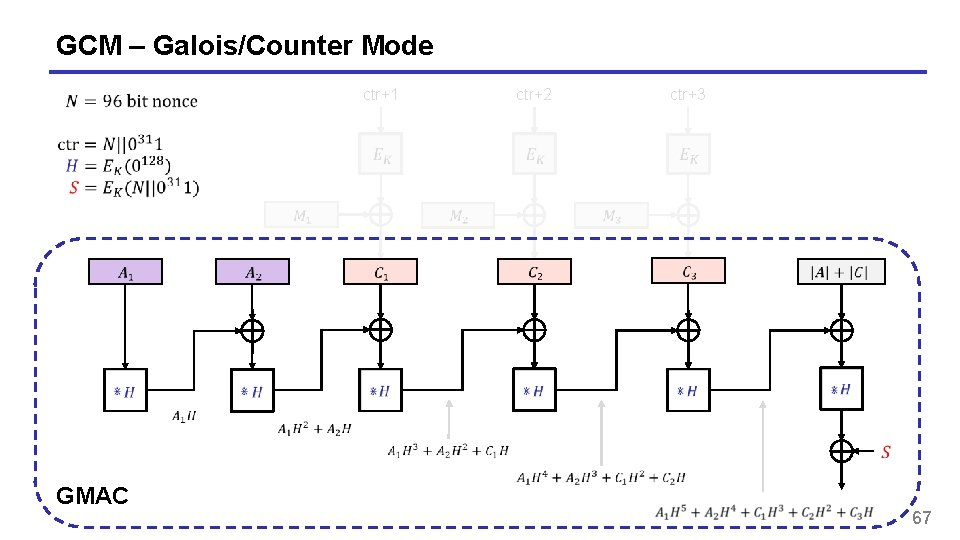
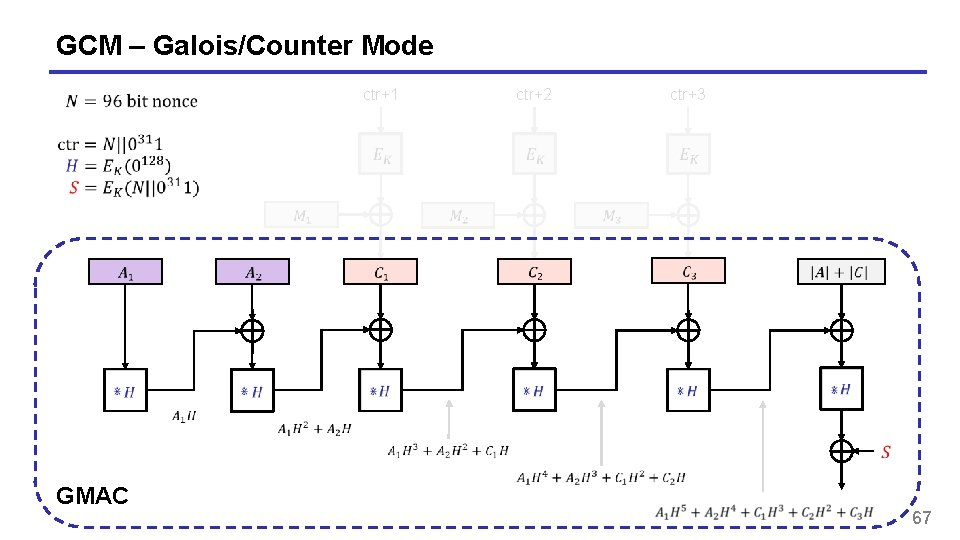
GCM – Galois/Counter Mode ctr+1 GMAC ctr+2 ctr+3 67
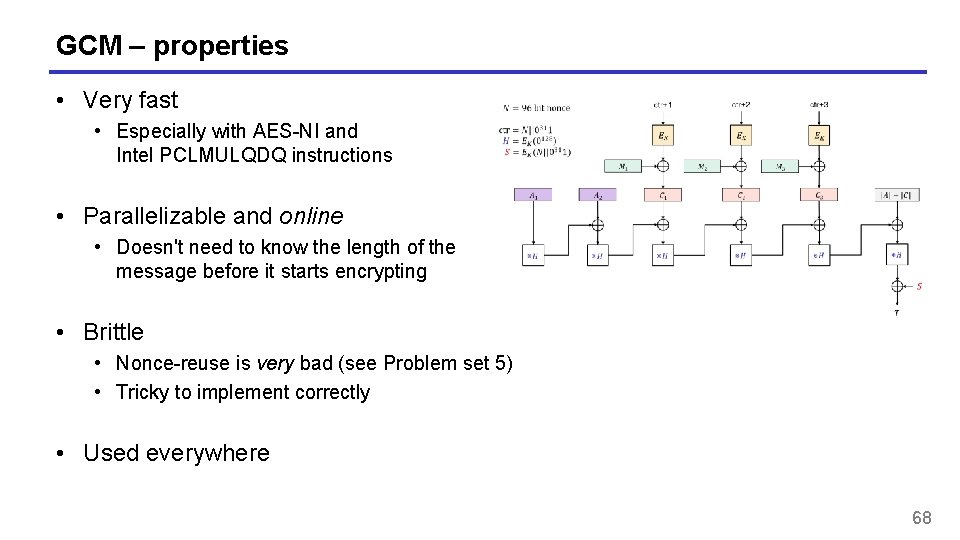
GCM – properties • Very fast • Especially with AES-NI and Intel PCLMULQDQ instructions • Parallelizable and online • Doesn't need to know the length of the message before it starts encrypting • Brittle • Nonce-reuse is very bad (see Problem set 5) • Tricky to implement correctly • Used everywhere 68
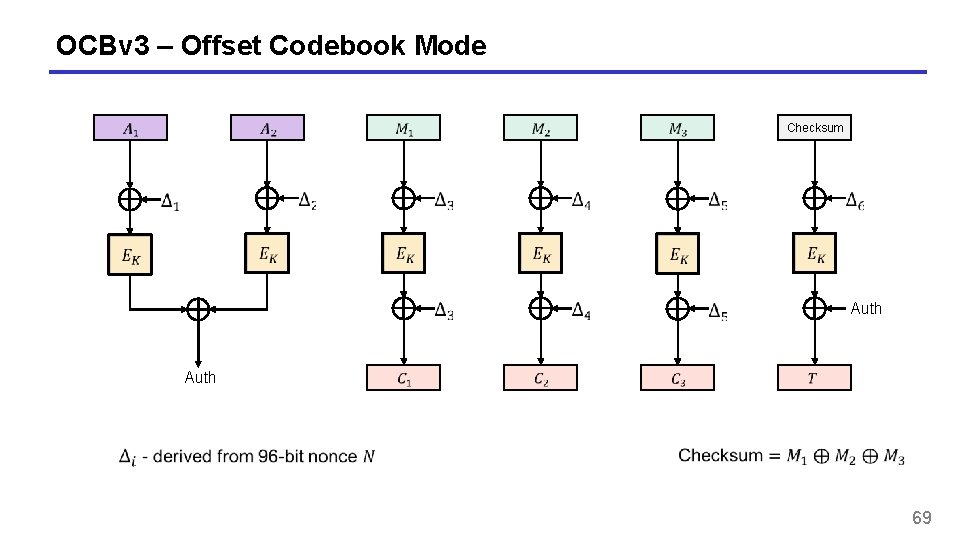
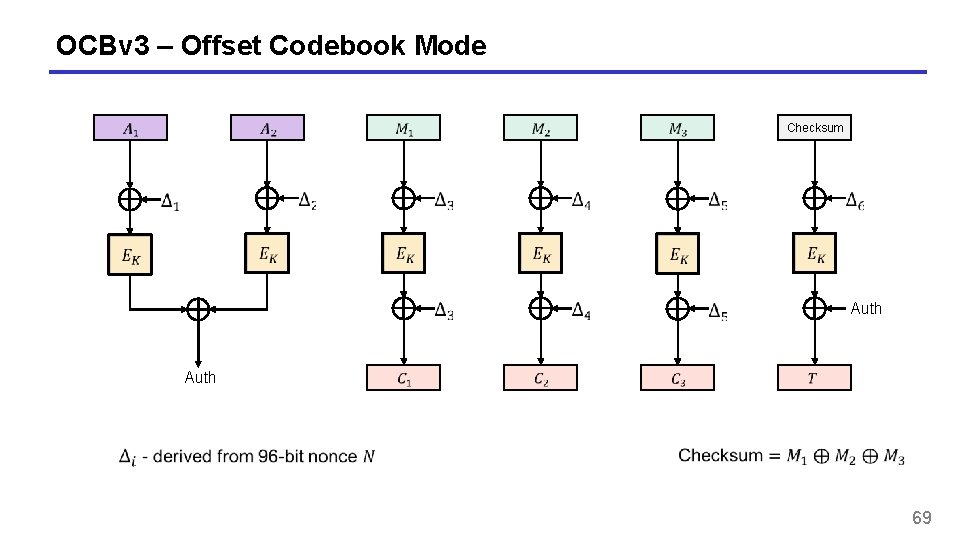
OCBv 3 – Offset Codebook Mode Checksum Auth 69
OCB – properties • The fastest AEAD algorithm in the west • Fully parallelizable and online • Incremental • Patented by Rogaway • Not used much 70
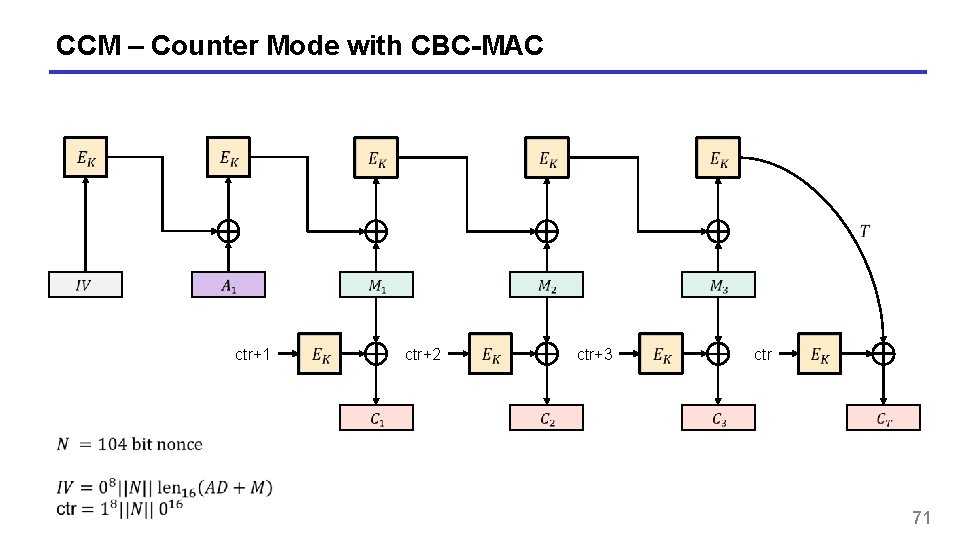
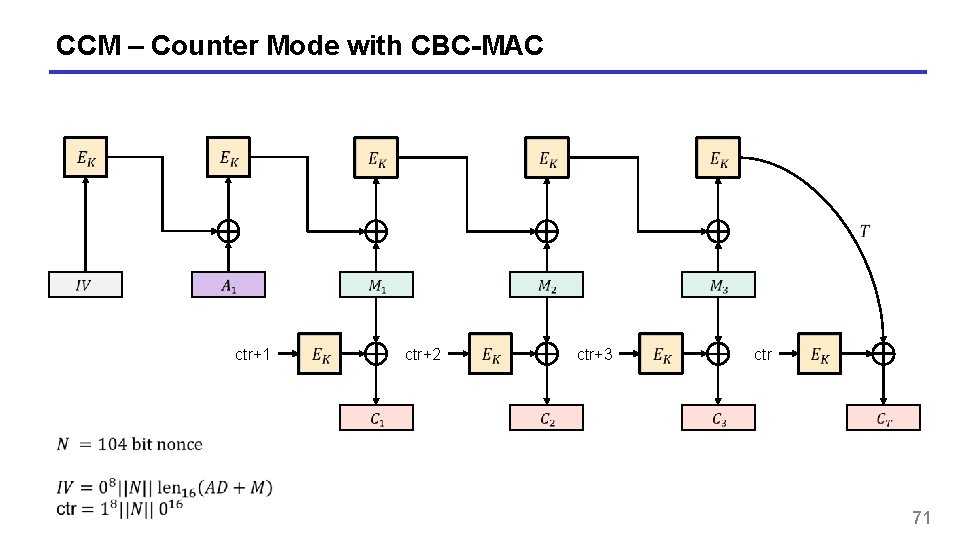
CCM – Counter Mode with CBC-MAC ctr+1 ctr+2 ctr+3 ctr 71
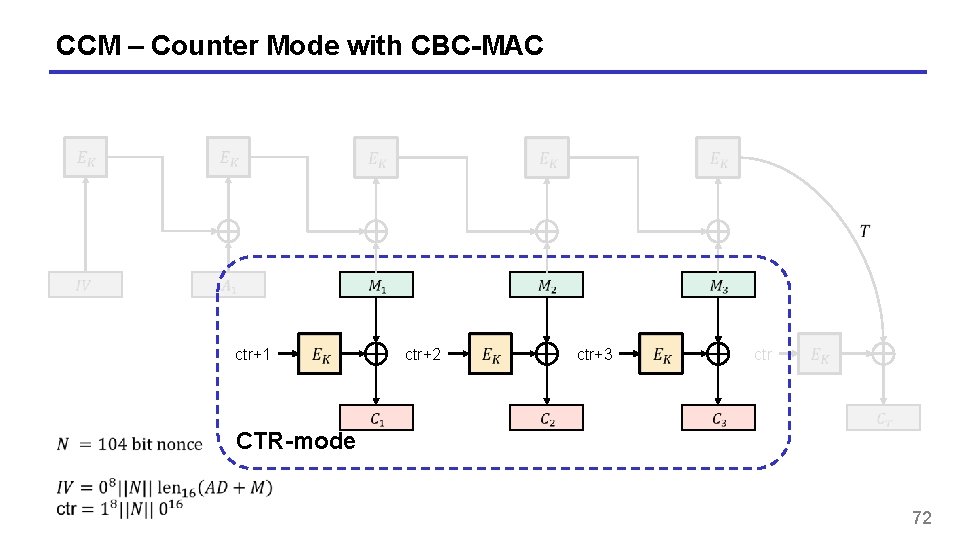
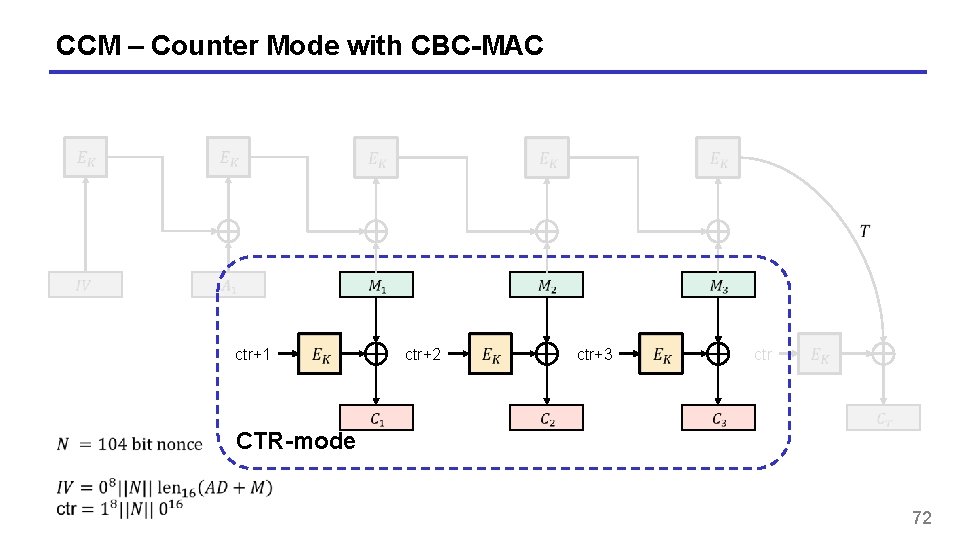
CCM – Counter Mode with CBC-MAC ctr+1 ctr+2 ctr+3 ctr CTR-mode 72
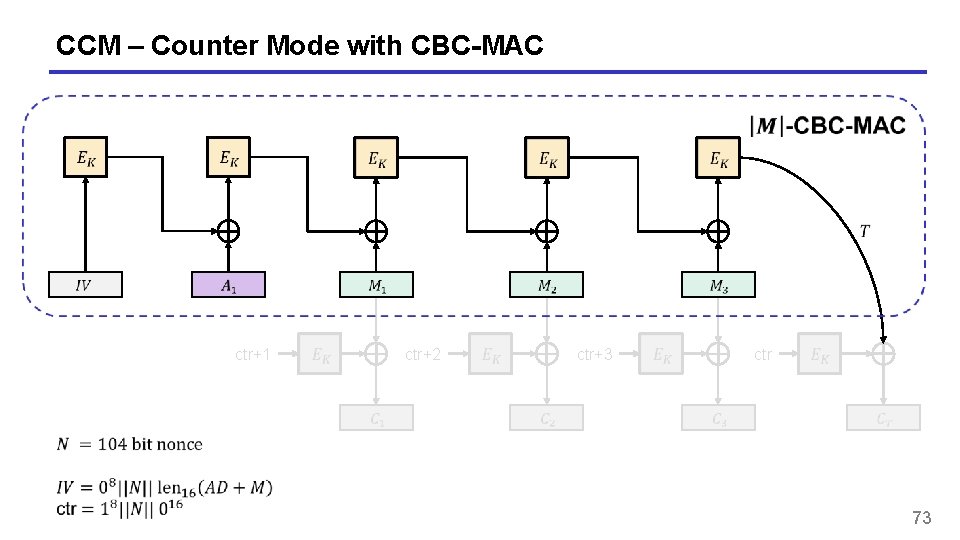
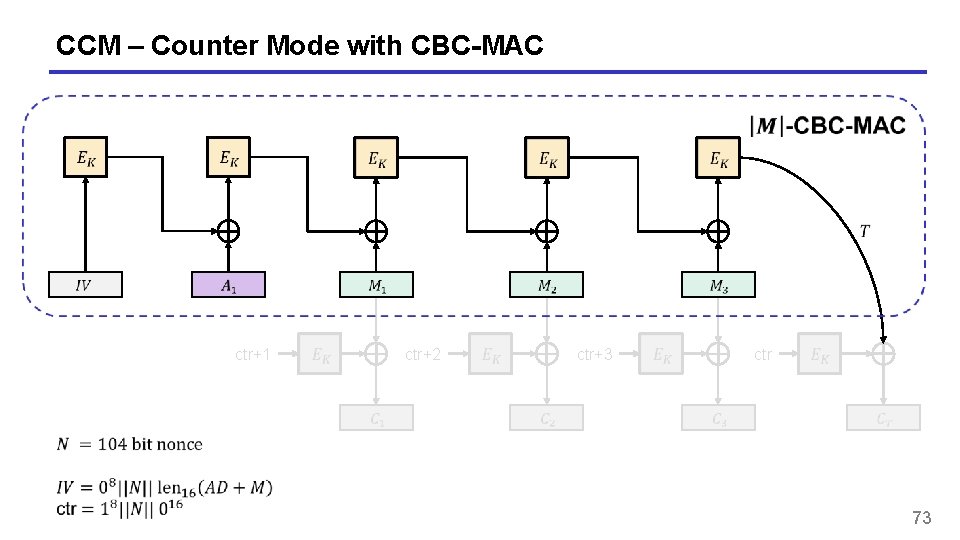
CCM – Counter Mode with CBC-MAC ctr+1 ctr+2 ctr+3 ctr 73
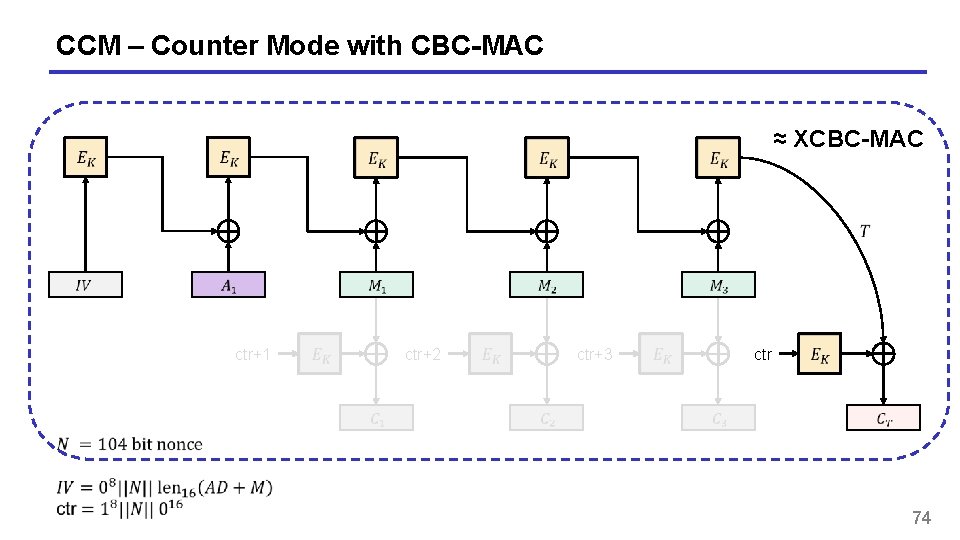
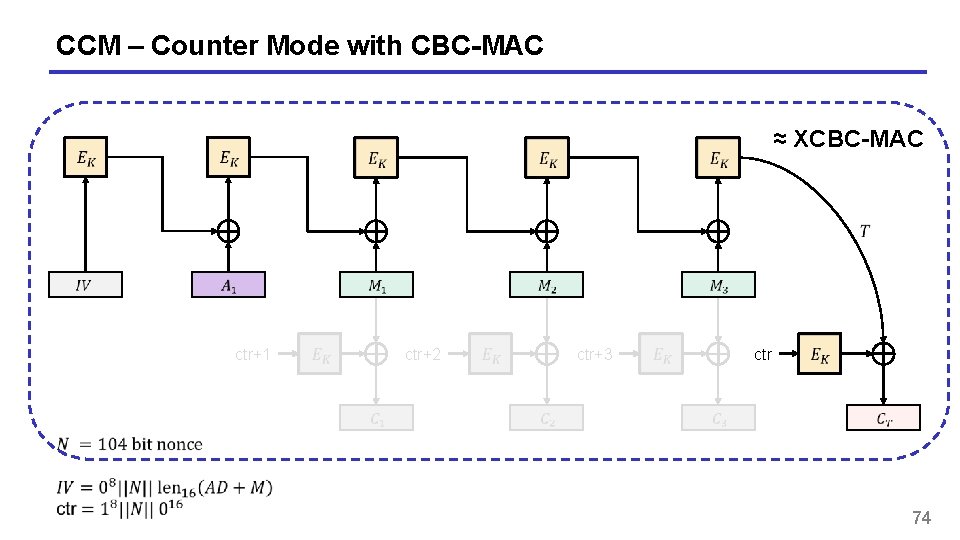
CCM – Counter Mode with CBC-MAC ≈ XCBC-MAC ctr+1 ctr+2 ctr+3 ctr 74
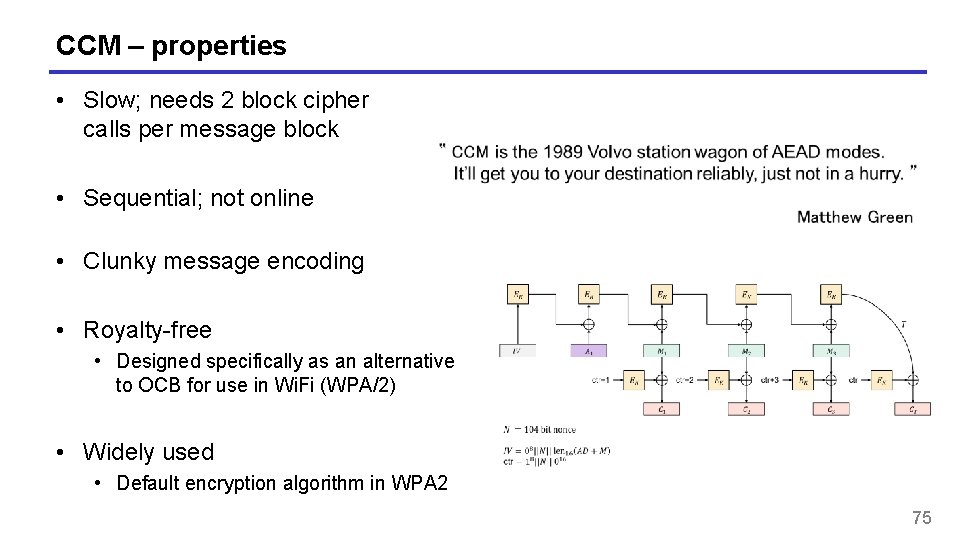
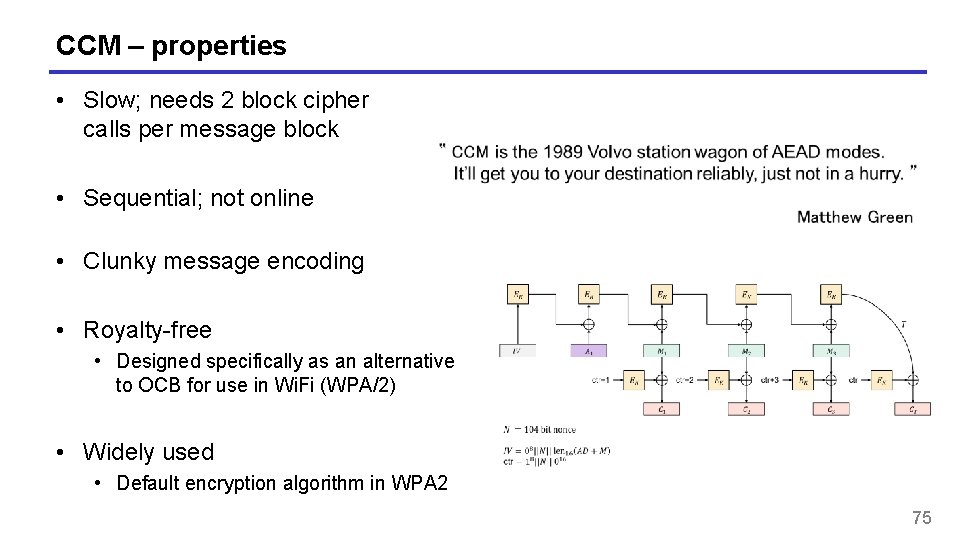
CCM – properties • Slow; needs 2 block cipher calls per message block • Sequential; not online • Clunky message encoding • Royalty-free • Designed specifically as an alternative to OCB for use in Wi. Fi (WPA/2) • Widely used • Default encryption algorithm in WPA 2 75
Summary • Authenticated encryption: privacy and intergrity in one primitive • AEAD: authenticated encryption with associated data: additional data that gets integrity protection, but not privacy protection (think protocol headers) • AEAD examples: • GCM • CCM • OCB • Next week: hash functions 76