Lecture 2 Breaking Unbreakable Ciphers Confronted with the
Lecture 2: Breaking Unbreakable Ciphers Confronted with the prospect of defeat, the Allied cryptanalysts had worked night and day to penetrate German ciphers. It would appear that fear was the main driving force, and that adversity is one of the foundations of successful codebreaking. Simon Singh, The Code Book CS 551: Security and Privacy David Evans University of Virginia 30 Aug 2000 University of Virginia CS 551 http: //www. cs. virginia. edu/~evans Computer Science
Menu • Survey Results • Vigenère – “Le Chiffre Indéchiffrable” • Shannon Principles: Perfect Ciphers 30 Aug 2000 University of Virginia CS 551 2
Survey Results • • Forged email: 15 out of 41 Broken into systems: 8 out of 41 PGP: 1 regular, 3 occasional Movies/Books: Sneakers (14), Hackers (4), Mission Impossible (2), Wargames (2), Cryptonomicon (2), Matrix, Takedown, Enemy of the State, Cuckoo’s Egg, Maximum Security, The Net 30 Aug 2000 University of Virginia CS 551 3
Vigenère • Invented by Blaise de Vigenère, ~1550 • Considered unbreakable for 300 years • Broken by Charles Babbage but kept secret to help British in Crimean War • Attack discovered independently by Friedrich Kasiski, 1863. 30 Aug 2000 University of Virginia CS 551 4
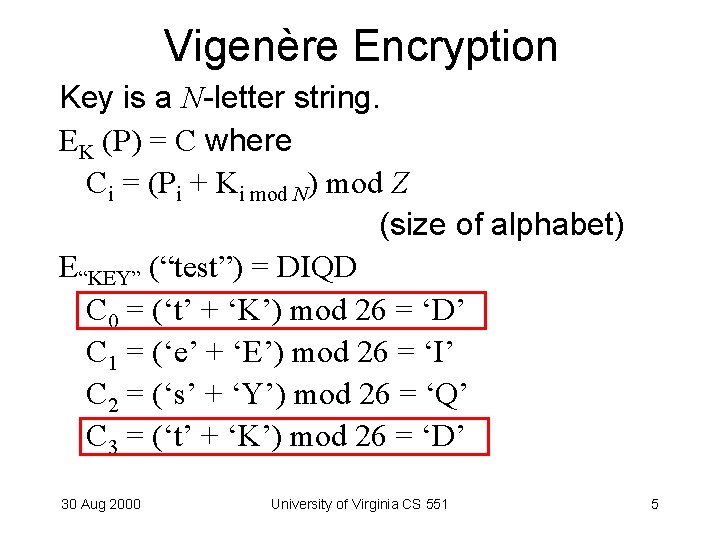
Vigenère Encryption Key is a N-letter string. EK (P) = C where Ci = (Pi + Ki mod N) mod Z (size of alphabet) E“KEY” (“test”) = DIQD C 0 = (‘t’ + ‘K’) mod 26 = ‘D’ C 1 = (‘e’ + ‘E’) mod 26 = ‘I’ C 2 = (‘s’ + ‘Y’) mod 26 = ‘Q’ C 3 = (‘t’ + ‘K’) mod 26 = ‘D’ 30 Aug 2000 University of Virginia CS 551 5
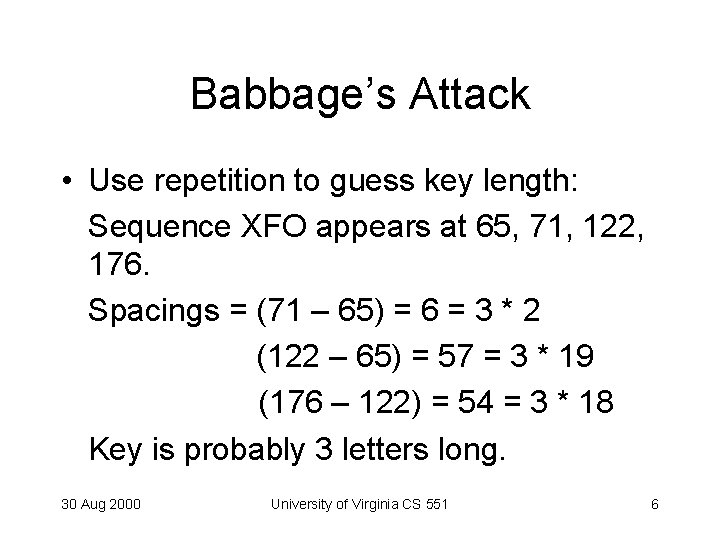
Babbage’s Attack • Use repetition to guess key length: Sequence XFO appears at 65, 71, 122, 176. Spacings = (71 – 65) = 6 = 3 * 2 (122 – 65) = 57 = 3 * 19 (176 – 122) = 54 = 3 * 18 Key is probably 3 letters long. 30 Aug 2000 University of Virginia CS 551 6
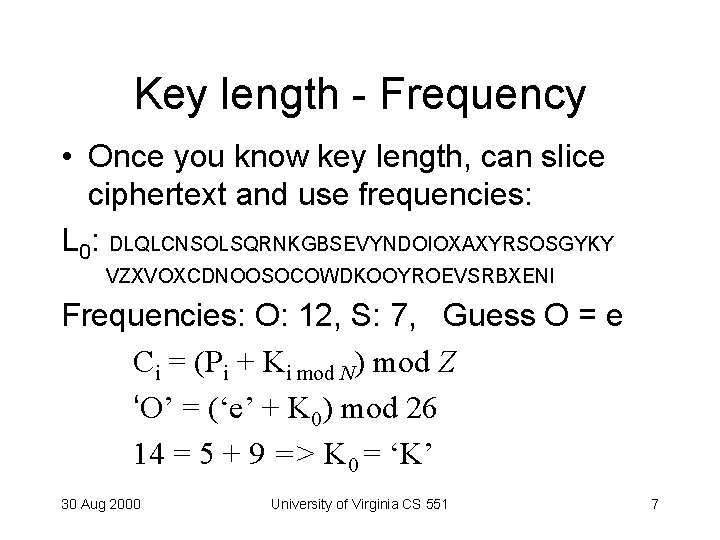
Key length - Frequency • Once you know key length, can slice ciphertext and use frequencies: L 0: DLQLCNSOLSQRNKGBSEVYNDOIOXAXYRSOSGYKY VZXVOXCDNOOSOCOWDKOOYROEVSRBXENI Frequencies: O: 12, S: 7, Guess O = e Ci = (Pi + Ki mod N) mod Z ‘O’ = (‘e’ + K 0) mod 26 14 = 5 + 9 => K 0 = ‘K’ 30 Aug 2000 University of Virginia CS 551 7
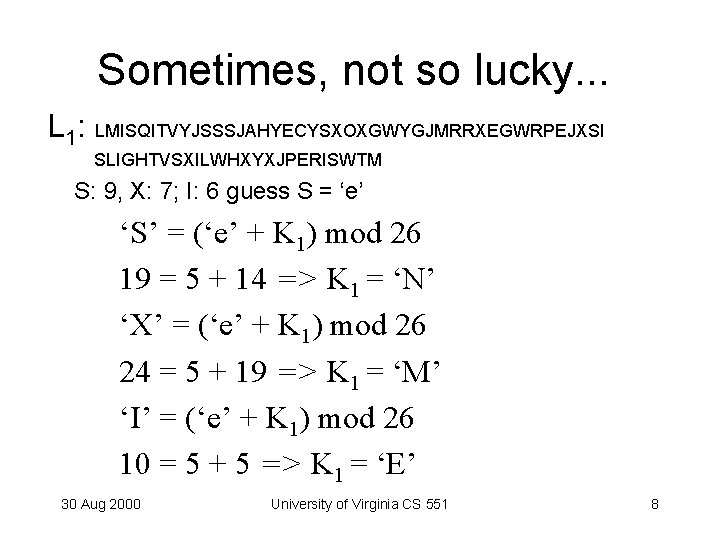
Sometimes, not so lucky. . . L 1: LMISQITVYJSSSJAHYECYSXOXGWYGJMRRXEGWRPEJXSI SLIGHTVSXILWHXYXJPERISWTM S: 9, X: 7; I: 6 guess S = ‘e’ ‘S’ = (‘e’ + K 1) mod 26 19 = 5 + 14 => K 1 = ‘N’ ‘X’ = (‘e’ + K 1) mod 26 24 = 5 + 19 => K 1 = ‘M’ ‘I’ = (‘e’ + K 1) mod 26 10 = 5 + 5 => K 1 = ‘E’ 30 Aug 2000 University of Virginia CS 551 8
30 Aug 2000 University of Virginia CS 551 9
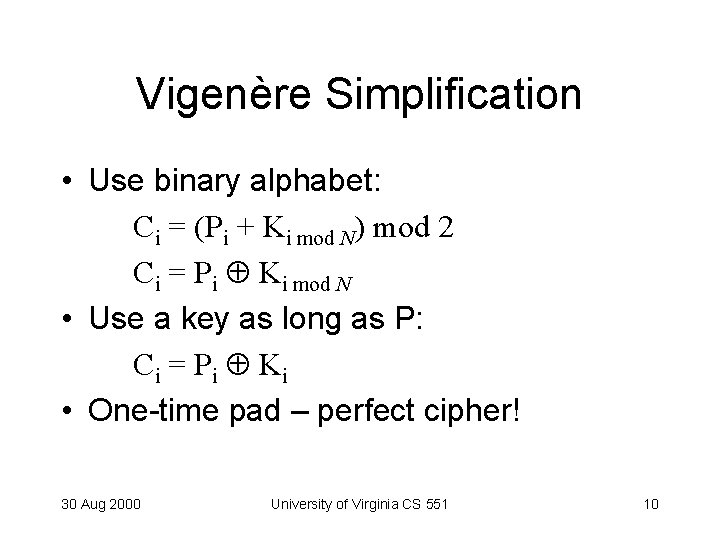
Vigenère Simplification • Use binary alphabet: Ci = (Pi + Ki mod N) mod 2 Ci = Pi Ki mod N • Use a key as long as P: C i = P i Ki • One-time pad – perfect cipher! 30 Aug 2000 University of Virginia CS 551 10
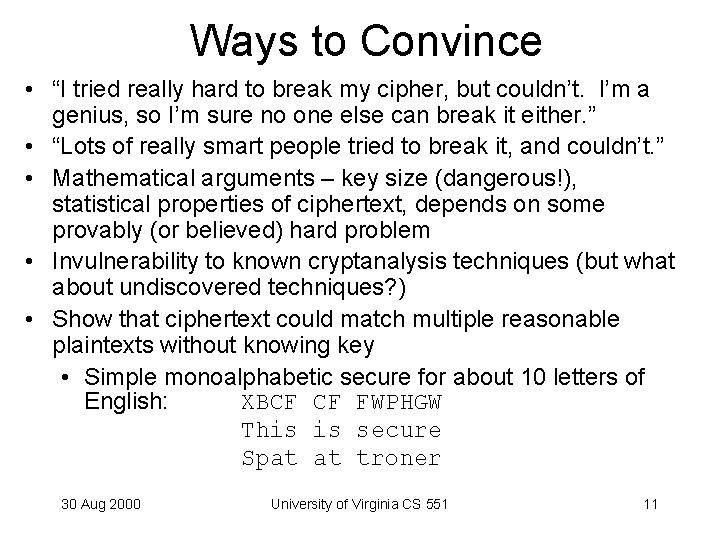
Ways to Convince • “I tried really hard to break my cipher, but couldn’t. I’m a genius, so I’m sure no one else can break it either. ” • “Lots of really smart people tried to break it, and couldn’t. ” • Mathematical arguments – key size (dangerous!), statistical properties of ciphertext, depends on some provably (or believed) hard problem • Invulnerability to known cryptanalysis techniques (but what about undiscovered techniques? ) • Show that ciphertext could match multiple reasonable plaintexts without knowing key • Simple monoalphabetic secure for about 10 letters of English: XBCF CF FWPHGW This is secure Spat at troner 30 Aug 2000 University of Virginia CS 551 11
Real World Standard • Attacker probably has details of algorithm • Attacker has a limited amount of ciphertext, often has known plaintext, occasionally has chosen plaintext • Breaking a cipher means the attacker can read a secret message 30 Aug 2000 University of Virginia CS 551 12
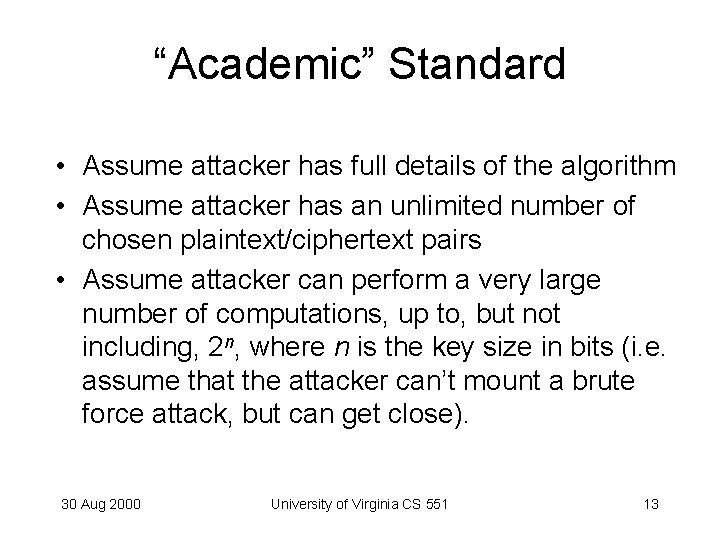
“Academic” Standard • Assume attacker has full details of the algorithm • Assume attacker has an unlimited number of chosen plaintext/ciphertext pairs • Assume attacker can perform a very large number of computations, up to, but not including, 2 n, where n is the key size in bits (i. e. assume that the attacker can’t mount a brute force attack, but can get close). 30 Aug 2000 University of Virginia CS 551 13
![Shannon’s Theory [1945] Message space: { M 1, M 2, . . . , Shannon’s Theory [1945] Message space: { M 1, M 2, . . . ,](http://slidetodoc.com/presentation_image/779f6d001bfd9f67478105da80075d2c/image-14.jpg)
Shannon’s Theory [1945] Message space: { M 1, M 2, . . . , Mn } Assume finite number of messages Each message has probability p(M 1) + p(M 2) +. . . + p(Mn) = 1 Key space: { K 1, K 2, . . . , Kl } (Based on Eli Biham’s notes) 30 Aug 2000 University of Virginia CS 551 14
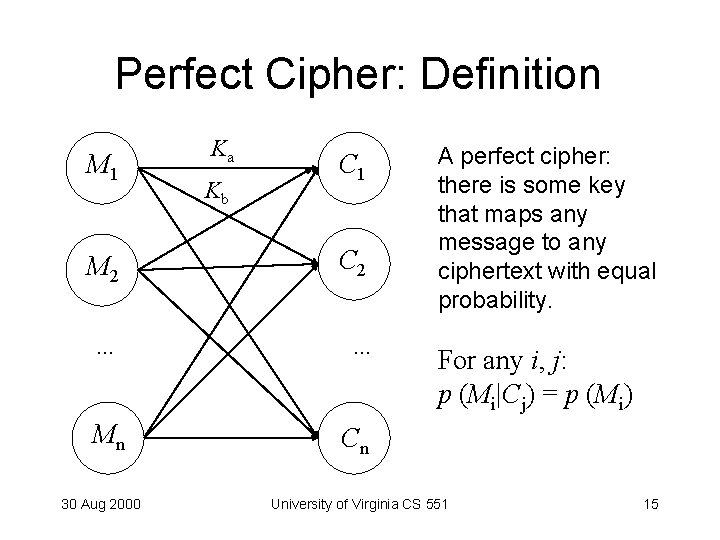
Perfect Cipher: Definition M 1 Ka Kb C 1 M 2 C 2 . . . Mn 30 Aug 2000 A perfect cipher: there is some key that maps any message to any ciphertext with equal probability. For any i, j: p (Mi|Cj) = p (Mi) Cn University of Virginia CS 551 15
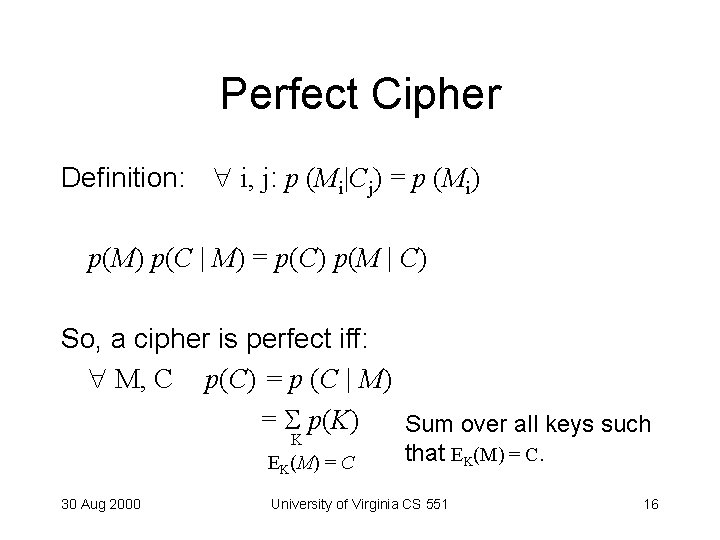
Perfect Cipher Definition: i, j: p (Mi|Cj) = p (Mi) p(M) p(C | M) = p(C) p(M | C) So, a cipher is perfect iff: M, C p(C) = p (C | M) = p(K) Sum over all keys such K EK(M) = C 30 Aug 2000 that EK(M) = C. University of Virginia CS 551 16
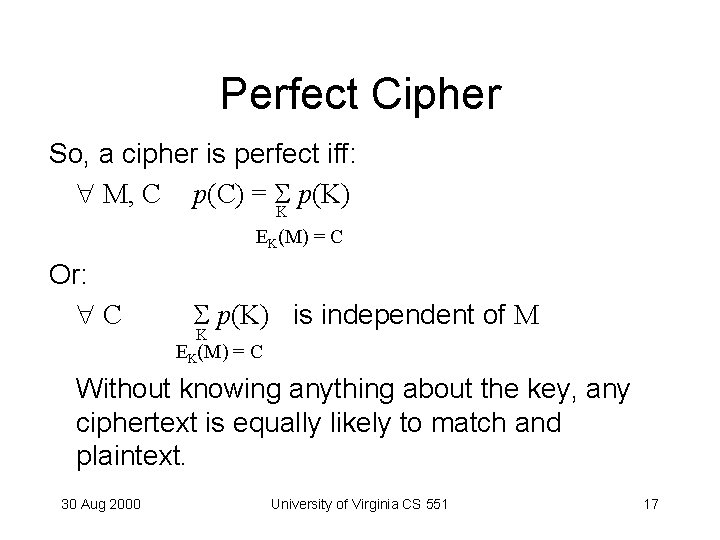
Perfect Cipher So, a cipher is perfect iff: M, C p(C) = p(K) K EK(M) = C Or: C p(K) is independent of M K EK(M) = C Without knowing anything about the key, any ciphertext is equally likely to match and plaintext. 30 Aug 2000 University of Virginia CS 551 17
Example: Monoalphabetic • Random monoalphabetic substitution for one letter message: C, M: p(C) = p(C | M) = 1/26. 30 Aug 2000 University of Virginia CS 551 18
Example: One-Time Pad For each bit: p(Ci = 0) = p(Ci = 0 | Mi = 1) = ½ since Ci = Ki Mi p (Ki Mi = 0) = p (Ki = 1) * p (Mi = 1) + p (Ki = 0) * p (Mi = 0) Truly random K means p (Ki = 1) = p (Ki = 0) = ½ * p (Mi = 1) + ½ * p (Mi = 0) = ½ * (p (Mi = 1) + p (Mi = 0)) = ½ All key bits are independent, so: p(C) = p(C | M) QED. 30 Aug 2000 University of Virginia CS 551 19
Perfect Cipher Keyspace Theorem: If a cipher is perfect, there must be at least as many keys (l) are there are possible messages (n). 30 Aug 2000 University of Virginia CS 551 20
Proof by Contradiction Suppose there is a perfect cipher with l < n. (More messages than keys. ) Let C 0 be some ciphertext with p(C 0) > 0. There exist m messages M such that M = DK(C 0 ) n - m messages M 0 such that M 0 DK(C 0 ) We know 1 m l < n so n - m > 0 and there is at least one message M 0. 30 Aug 2000 University of Virginia CS 551 21
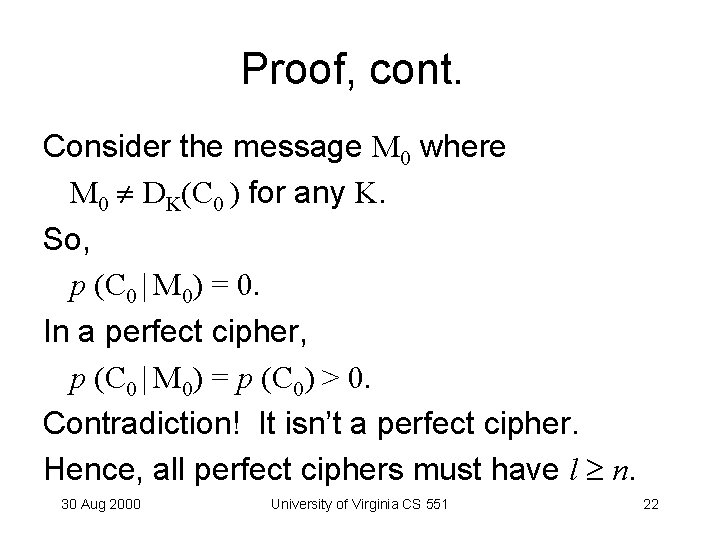
Proof, cont. Consider the message M 0 where M 0 DK(C 0 ) for any K. So, p (C 0 | M 0) = 0. In a perfect cipher, p (C 0 | M 0) = p (C 0) > 0. Contradiction! It isn’t a perfect cipher. Hence, all perfect ciphers must have l n. 30 Aug 2000 University of Virginia CS 551 22
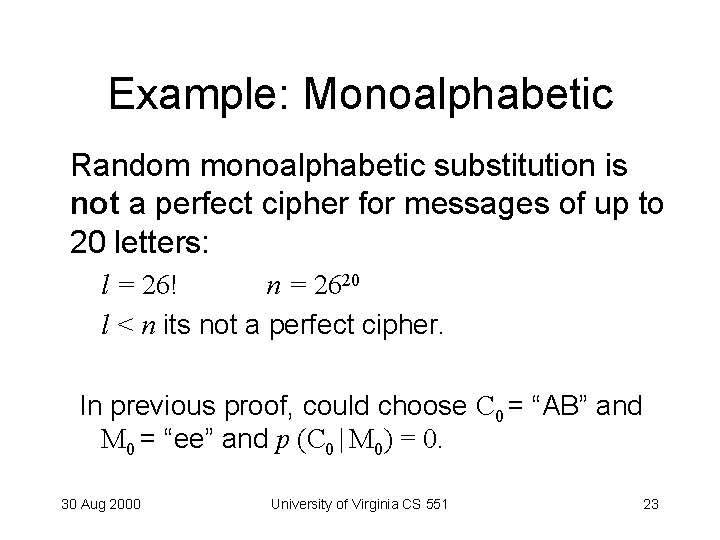
Example: Monoalphabetic Random monoalphabetic substitution is not a perfect cipher for messages of up to 20 letters: l = 26! n = 2620 l < n its not a perfect cipher. In previous proof, could choose C 0 = “AB” and M 0 = “ee” and p (C 0 | M 0) = 0. 30 Aug 2000 University of Virginia CS 551 23
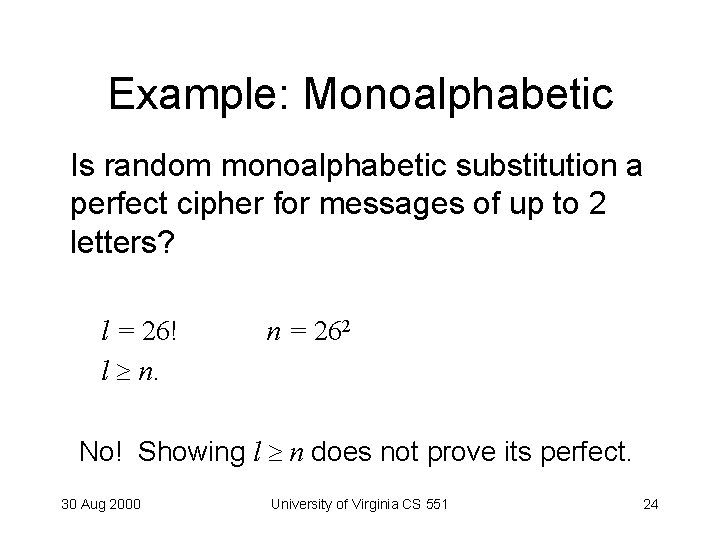
Example: Monoalphabetic Is random monoalphabetic substitution a perfect cipher for messages of up to 2 letters? l = 26! l n. n = 262 No! Showing l n does not prove its perfect. 30 Aug 2000 University of Virginia CS 551 24
![Information Theory • [Shannon 1948] • Entropy (H): – Amount of information in a Information Theory • [Shannon 1948] • Entropy (H): – Amount of information in a](http://slidetodoc.com/presentation_image/779f6d001bfd9f67478105da80075d2c/image-25.jpg)
Information Theory • [Shannon 1948] • Entropy (H): – Amount of information in a message H(M) = log 2 n where n is the number of possible meanings H (month of year) = log 2 12 3. 6 (need 4 bits to encode a year) 30 Aug 2000 University of Virginia CS 551 25
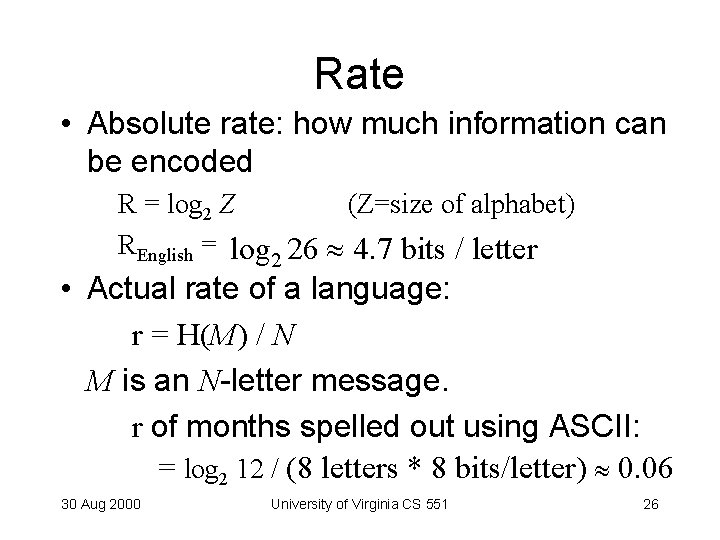
Rate • Absolute rate: how much information can be encoded R = log 2 Z (Z=size of alphabet) REnglish = log 2 26 4. 7 bits / letter • Actual rate of a language: r = H(M) / N M is an N-letter message. r of months spelled out using ASCII: = log 2 12 / (8 letters * 8 bits/letter) 0. 06 30 Aug 2000 University of Virginia CS 551 26
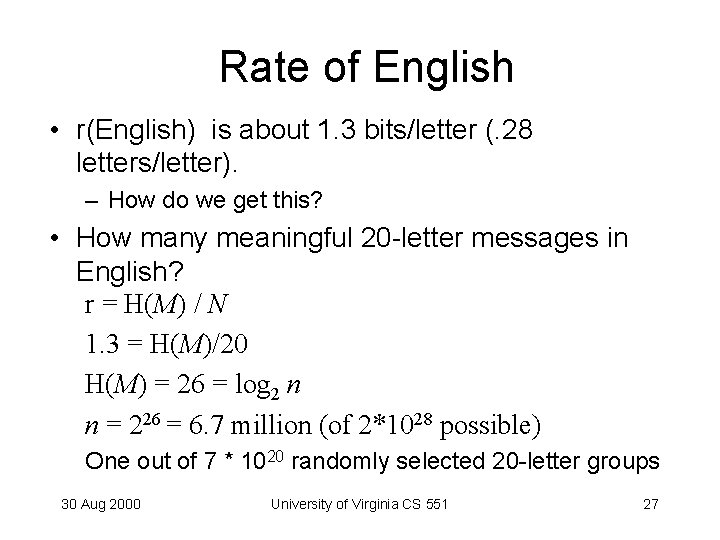
Rate of English • r(English) is about 1. 3 bits/letter (. 28 letters/letter). – How do we get this? • How many meaningful 20 -letter messages in English? r = H(M) / N 1. 3 = H(M)/20 H(M) = 26 = log 2 n n = 226 = 6. 7 million (of 2*1028 possible) One out of 7 * 1020 randomly selected 20 -letter groups 30 Aug 2000 University of Virginia CS 551 27
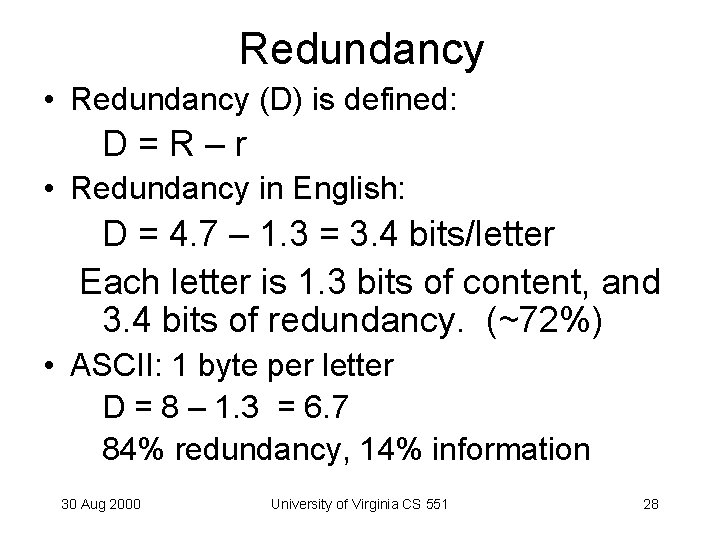
Redundancy • Redundancy (D) is defined: D=R–r • Redundancy in English: D = 4. 7 – 1. 3 = 3. 4 bits/letter Each letter is 1. 3 bits of content, and 3. 4 bits of redundancy. (~72%) • ASCII: 1 byte per letter D = 8 – 1. 3 = 6. 7 84% redundancy, 14% information 30 Aug 2000 University of Virginia CS 551 28
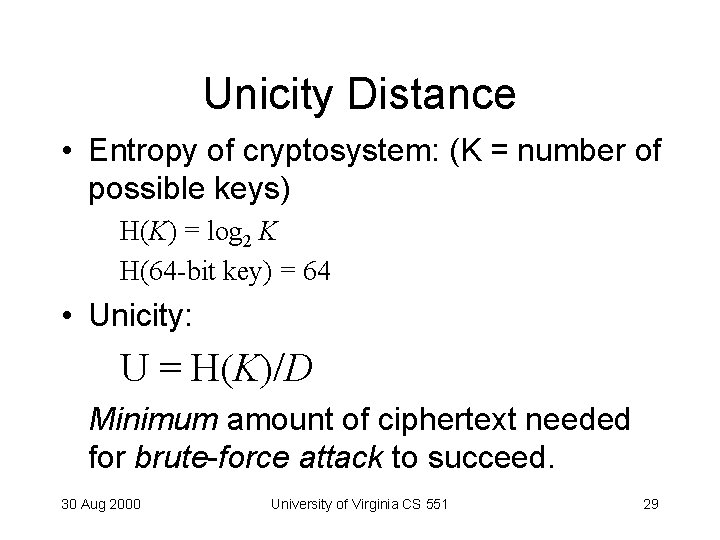
Unicity Distance • Entropy of cryptosystem: (K = number of possible keys) H(K) = log 2 K H(64 -bit key) = 64 • Unicity: U = H(K)/D Minimum amount of ciphertext needed for brute-force attack to succeed. 30 Aug 2000 University of Virginia CS 551 29
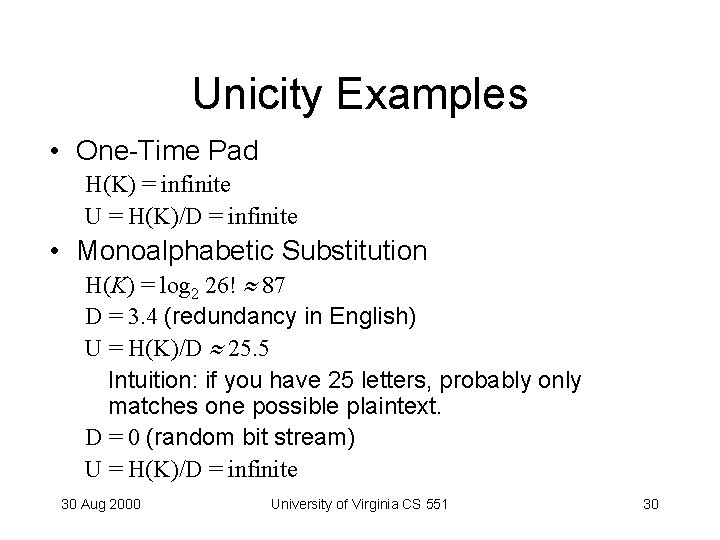
Unicity Examples • One-Time Pad H(K) = infinite U = H(K)/D = infinite • Monoalphabetic Substitution H(K) = log 2 26! 87 D = 3. 4 (redundancy in English) U = H(K)/D 25. 5 Intuition: if you have 25 letters, probably only matches one possible plaintext. D = 0 (random bit stream) U = H(K)/D = infinite 30 Aug 2000 University of Virginia CS 551 30
Unicity • Theoretical and probabilistic measure of how much ciphertext is needed to determine a unique plaintext • Does not indicate how much ciphertext is needed for cryptanalysis • If you have less than unicity distance ciphertext, can’t tell if guess is right. • As redundancy approaches 0, hard to cryptanalyze even simple cipher. 30 Aug 2000 University of Virginia CS 551 31
Charge • Problem Set 1: due next Monday • Next time: – Project team assignments • If I don’t have your survey yet, make sure I get it today! – DES – most widely used modern cipher 30 Aug 2000 University of Virginia CS 551 32
- Slides: 32