Lecture 13 CS 3516 These slides are generated
![Cable access network cable headend MAP frame for Interval [t 1, t 2] Downstream Cable access network cable headend MAP frame for Interval [t 1, t 2] Downstream](https://slidetodoc.com/presentation_image/1e414d7cca78bb4112317c5dce486cdf/image-31.jpg)
- Slides: 53
Lecture 13 CS 3516: These slides are generated from those made available by the authors of our text. Computer Networking: A Top Down Approach 6 th edition Jim Kurose, Keith Ross Addison-Wesley March 2012 Introduction 1 -1
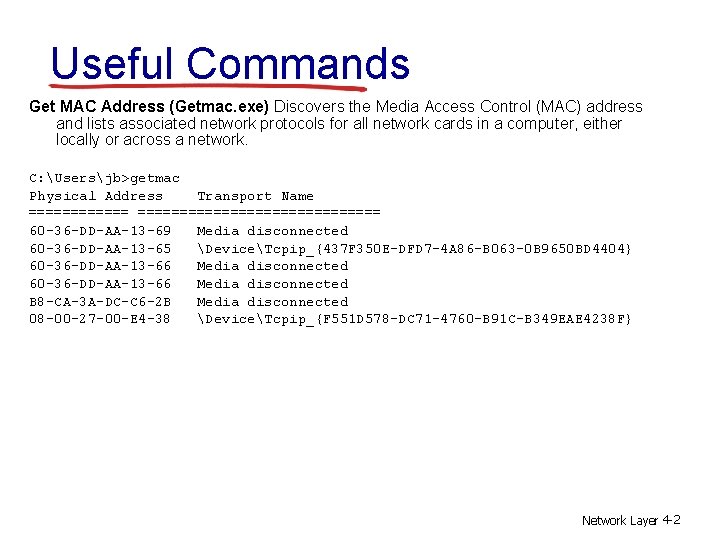
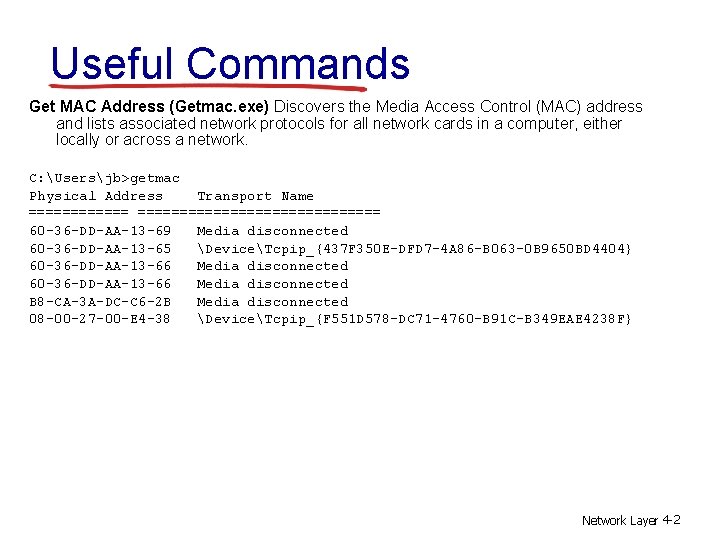
Useful Commands Get MAC Address (Getmac. exe) Discovers the Media Access Control (MAC) address and lists associated network protocols for all network cards in a computer, either locally or across a network. C: Usersjb>getmac Physical Address Transport Name ===================== 60 -36 -DD-AA-13 -69 Media disconnected 60 -36 -DD-AA-13 -65 DeviceTcpip_{437 F 350 E-DFD 7 -4 A 86 -B 063 -0 B 9650 BD 4404} 60 -36 -DD-AA-13 -66 Media disconnected B 8 -CA-3 A-DC-C 6 -2 B Media disconnected 08 -00 -27 -00 -E 4 -38 DeviceTcpip_{F 551 D 578 -DC 71 -4760 -B 91 C-B 349 EAE 4238 F} Network Layer 4 -2
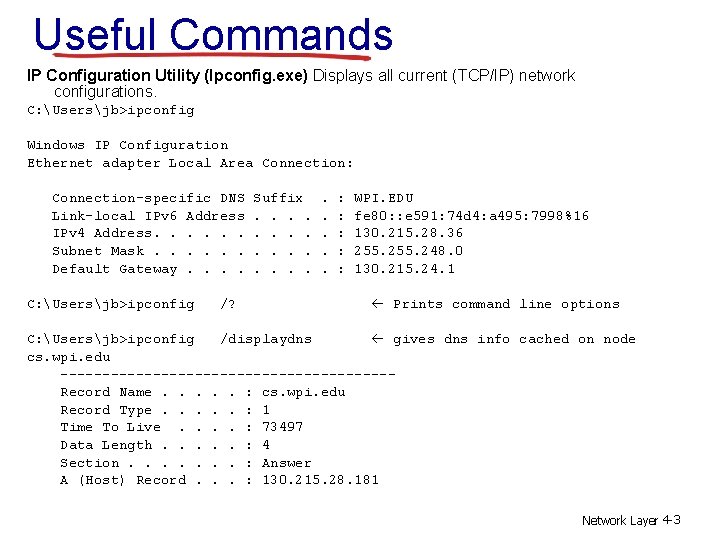
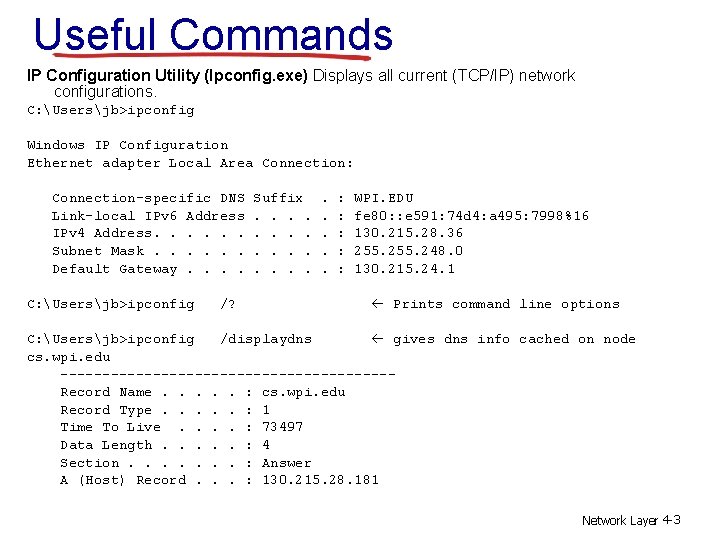
Useful Commands IP Configuration Utility (Ipconfig. exe) Displays all current (TCP/IP) network configurations. C: Usersjb>ipconfig Windows IP Configuration Ethernet adapter Local Area Connection: Connection-specific DNS Link-local IPv 6 Address IPv 4 Address. . . Subnet Mask. . . Default Gateway. . C: Usersjb>ipconfig /? Suffix. . . . . : : : WPI. EDU fe 80: : e 591: 74 d 4: a 495: 7998%16 130. 215. 28. 36 255. 248. 0 130. 215. 24. 1 Prints command line options C: Usersjb>ipconfig /displaydns gives dns info cached on node cs. wpi. edu --------------------Record Name. . . : cs. wpi. edu Record Type. . . : 1 Time To Live. . : 73497 Data Length. . . : 4 Section. . . . : Answer A (Host) Record. . . : 130. 215. 28. 181 Network Layer 4 -3
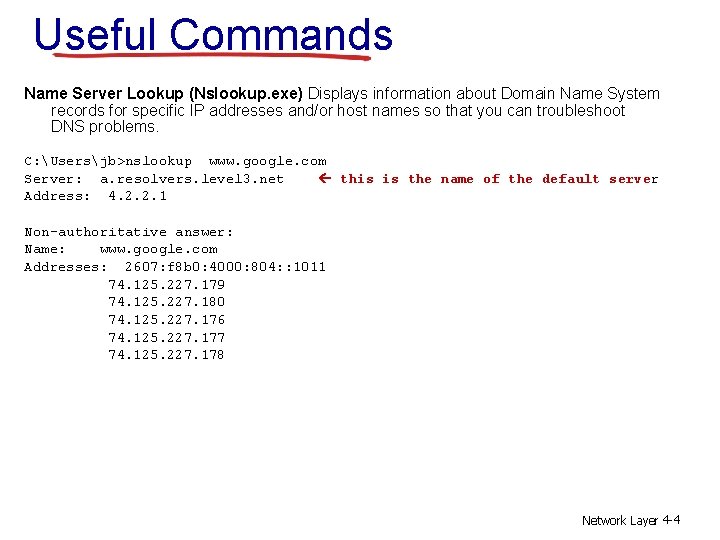
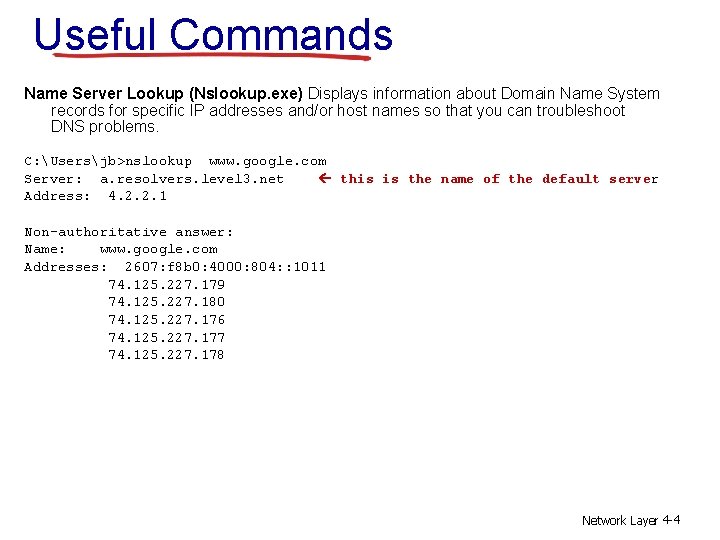
Useful Commands Name Server Lookup (Nslookup. exe) Displays information about Domain Name System records for specific IP addresses and/or host names so that you can troubleshoot DNS problems. C: Usersjb>nslookup www. google. com Server: a. resolvers. level 3. net this is the name of the default server Address: 4. 2. 2. 1 Non-authoritative answer: Name: www. google. com Addresses: 2607: f 8 b 0: 4000: 804: : 1011 74. 125. 227. 179 74. 125. 227. 180 74. 125. 227. 176 74. 125. 227. 177 74. 125. 227. 178 Network Layer 4 -4
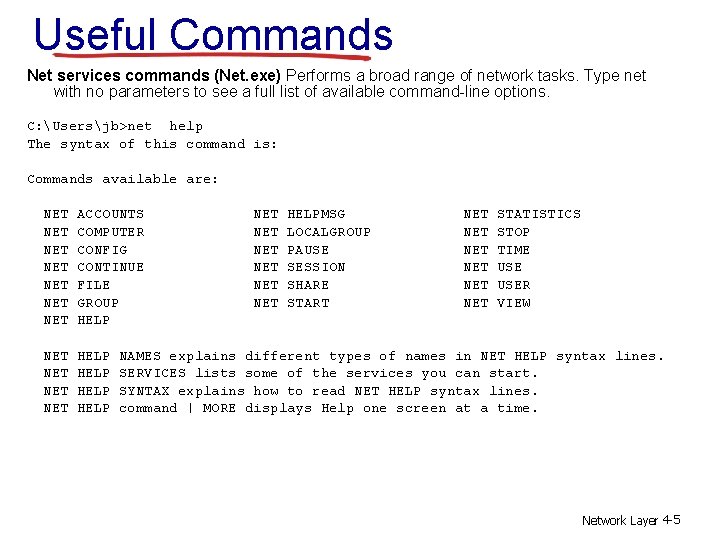
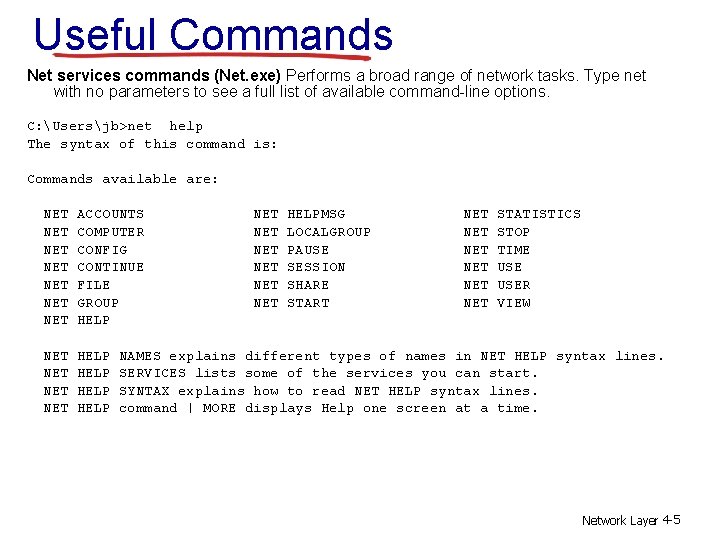
Useful Commands Net services commands (Net. exe) Performs a broad range of network tasks. Type net with no parameters to see a full list of available command-line options. C: Usersjb>net help The syntax of this command is: Commands available are: NET NET ACCOUNTS COMPUTER CONFIG CONTINUE FILE GROUP HELP NET NET HELP NET NET NET HELPMSG LOCALGROUP PAUSE SESSION SHARE START NET NET NET STATISTICS STOP TIME USER VIEW NAMES explains different types of names in NET HELP syntax lines. SERVICES lists some of the services you can start. SYNTAX explains how to read NET HELP syntax lines. command | MORE displays Help one screen at a time. Network Layer 4 -5
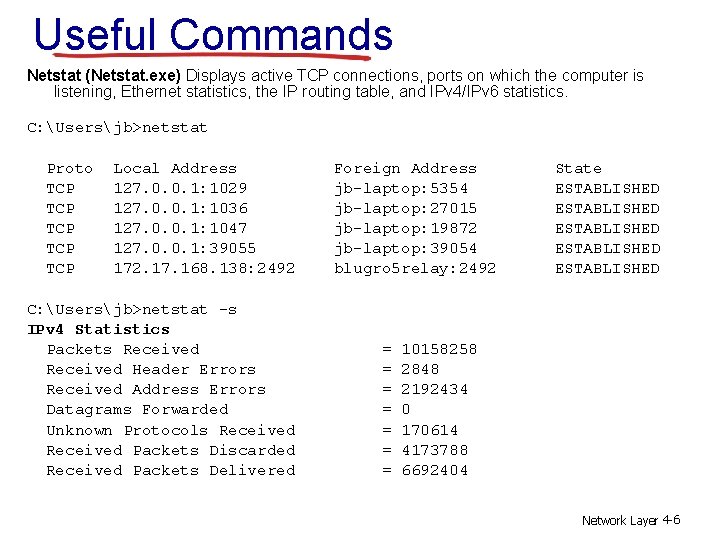
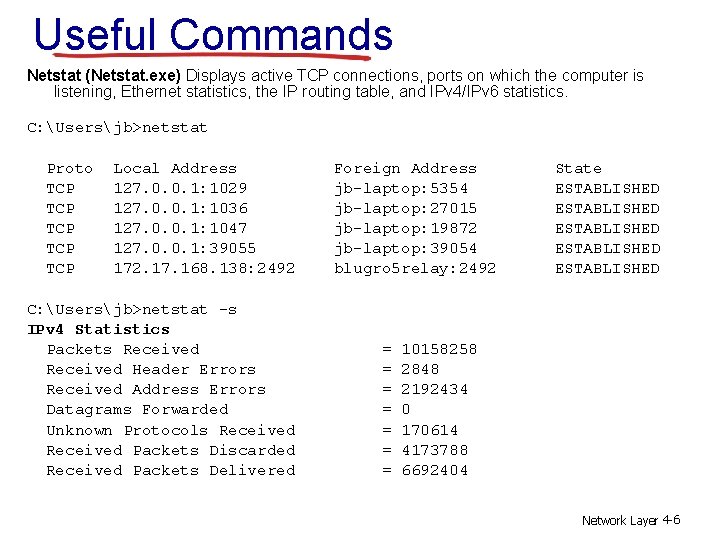
Useful Commands Netstat (Netstat. exe) Displays active TCP connections, ports on which the computer is listening, Ethernet statistics, the IP routing table, and IPv 4/IPv 6 statistics. C: Usersjb>netstat Proto TCP TCP TCP Local Address 127. 0. 0. 1: 1029 127. 0. 0. 1: 1036 127. 0. 0. 1: 1047 127. 0. 0. 1: 39055 172. 17. 168. 138: 2492 C: Usersjb>netstat -s IPv 4 Statistics Packets Received Header Errors Received Address Errors Datagrams Forwarded Unknown Protocols Received Packets Discarded Received Packets Delivered Foreign Address jb-laptop: 5354 jb-laptop: 27015 jb-laptop: 19872 jb-laptop: 39054 blugro 5 relay: 2492 = = = = State ESTABLISHED ESTABLISHED 10158258 2848 2192434 0 170614 4173788 6692404 Network Layer 4 -6
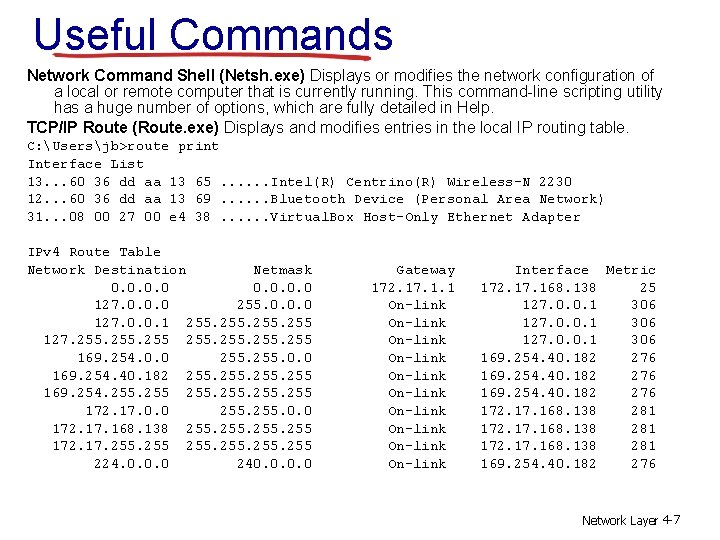
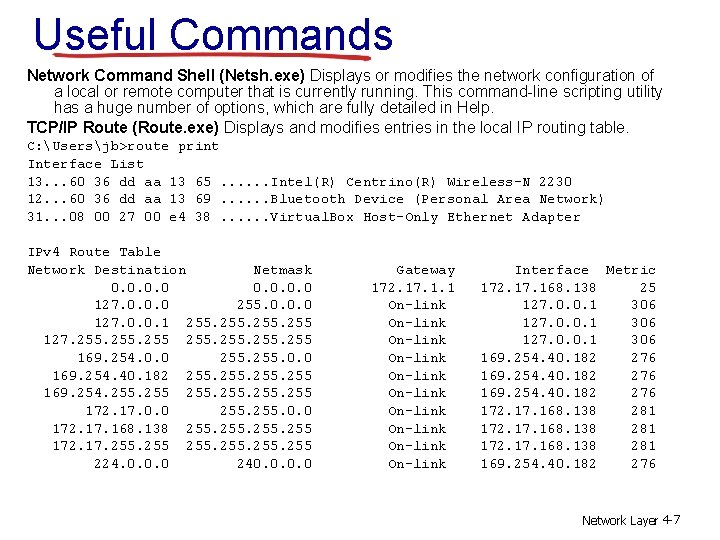
Useful Commands Network Command Shell (Netsh. exe) Displays or modifies the network configuration of a local or remote computer that is currently running. This command-line scripting utility has a huge number of options, which are fully detailed in Help. TCP/IP Route (Route. exe) Displays and modifies entries in the local IP routing table. C: Usersjb>route print Interface List 13. . . 60 36 dd aa 13 65. . . Intel(R) Centrino(R) Wireless-N 2230 12. . . 60 36 dd aa 13 69. . . Bluetooth Device (Personal Area Network) 31. . . 08 00 27 00 e 4 38. . . Virtual. Box Host-Only Ethernet Adapter IPv 4 Route Table Network Destination Netmask 0. 0 127. 0. 0. 0 255. 0. 0. 0 127. 0. 0. 1 255 127. 255 169. 254. 0. 0 255. 0. 0 169. 254. 40. 182 255 169. 254. 255 255 172. 17. 0. 0 255. 0. 0 172. 17. 168. 138 255 172. 17. 255 255 224. 0. 0. 0 240. 0 Gateway 172. 17. 1. 1 On-link On-link On-link Interface Metric 172. 17. 168. 138 25 127. 0. 0. 1 306 169. 254. 40. 182 276 172. 17. 168. 138 281 169. 254. 40. 182 276 Network Layer 4 -7
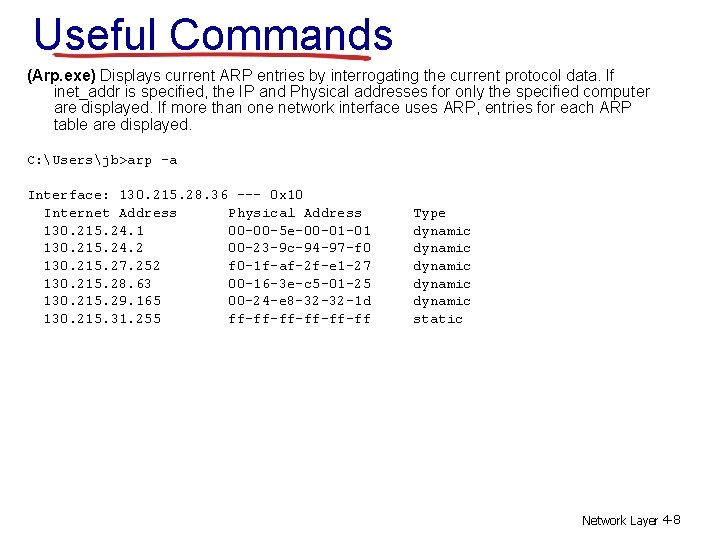
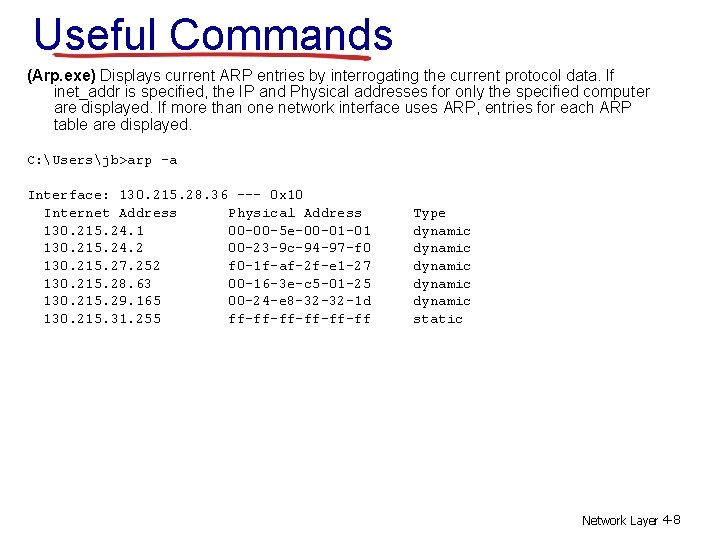
Useful Commands (Arp. exe) Displays current ARP entries by interrogating the current protocol data. If inet_addr is specified, the IP and Physical addresses for only the specified computer are displayed. If more than one network interface uses ARP, entries for each ARP table are displayed. C: Usersjb>arp -a Interface: 130. 215. 28. 36 --- 0 x 10 Internet Address Physical Address 130. 215. 24. 1 00 -00 -5 e-00 -01 -01 130. 215. 24. 2 00 -23 -9 c-94 -97 -f 0 130. 215. 27. 252 f 0 -1 f-af-2 f-e 1 -27 130. 215. 28. 63 00 -16 -3 e-c 5 -01 -25 130. 215. 29. 165 00 -24 -e 8 -32 -32 -1 d 130. 215. 31. 255 ff-ff-ff-ff Type dynamic dynamic static Network Layer 4 -8
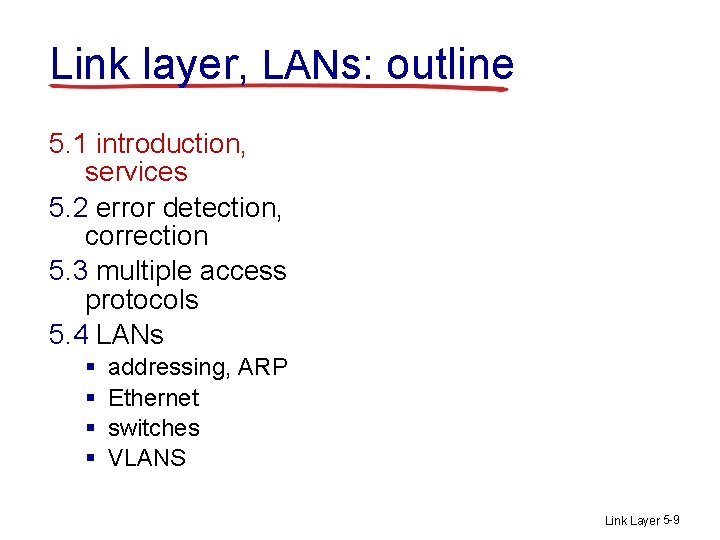
Link layer, LANs: outline 5. 1 introduction, services 5. 2 error detection, correction 5. 3 multiple access protocols 5. 4 LANs § § addressing, ARP Ethernet switches VLANS Link Layer 5 -9
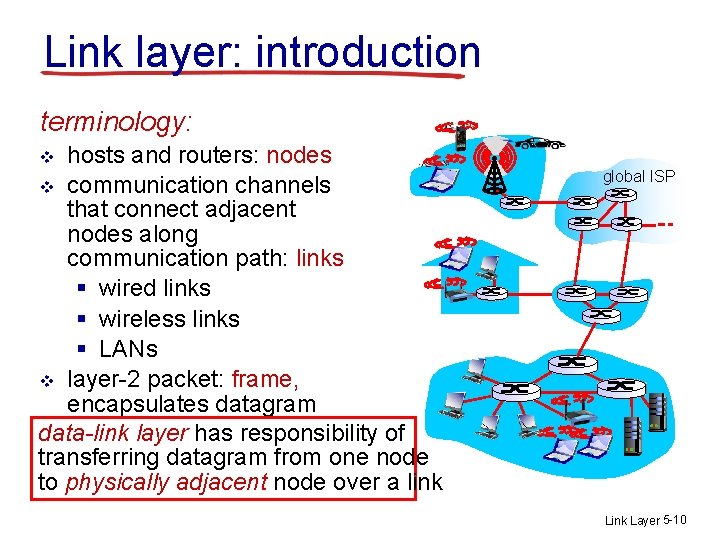
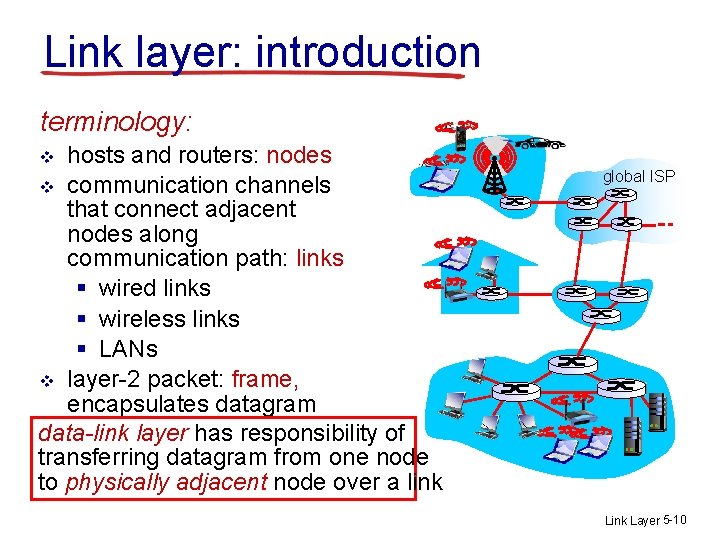
Link layer: introduction terminology: hosts and routers: nodes v communication channels that connect adjacent nodes along communication path: links § wired links § wireless links § LANs v layer-2 packet: frame, encapsulates datagram data-link layer has responsibility of transferring datagram from one node to physically adjacent node over a link v global ISP Link Layer 5 -10
Link layer: context v v datagram transferred by different link protocols over different links: § e. g. , Ethernet on first link, frame relay on intermediate links, 802. 11 on last link each link protocol provides different services § e. g. , may or may not provide rdt over link v framing, link access: § encapsulate datagram into frame, adding header, trailer § channel access if shared medium § “MAC” addresses used in frame headers to identify source, dest • different from IP address! reliable delivery between adjacent nodes we learned how to do this already – Transport layer seldom used on low bit-error link (fiber, some twisted pair) wireless links: high error rates Q: why both link-level and end-end reliability? Link Layer 5 -11
Link layer services (more) v flow control: § pacing between adjacent sending and receiving nodes v error detection: § errors caused by signal attenuation, noise. § receiver detects presence of errors: • signals sender for retransmission or drops frame v error correction: § receiver identifies and corrects bit error(s) without resorting to retransmission v half-duplex and full-duplex § with half duplex, nodes at both ends of link can transmit, but not at same time Link Layer 5 -12
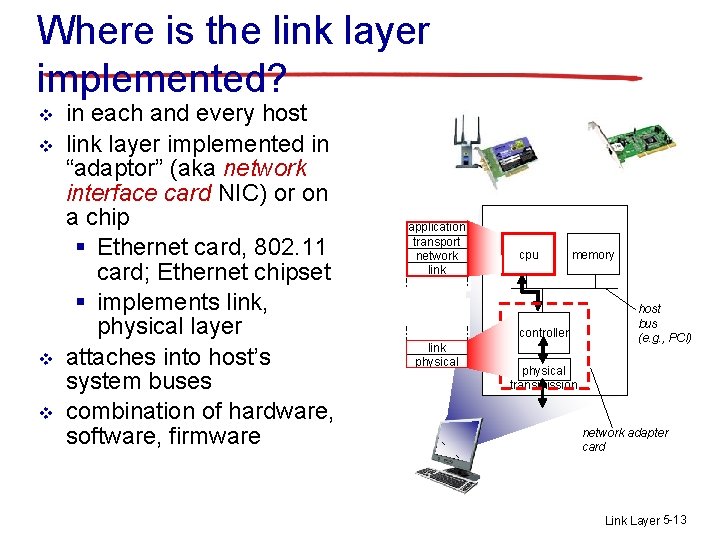
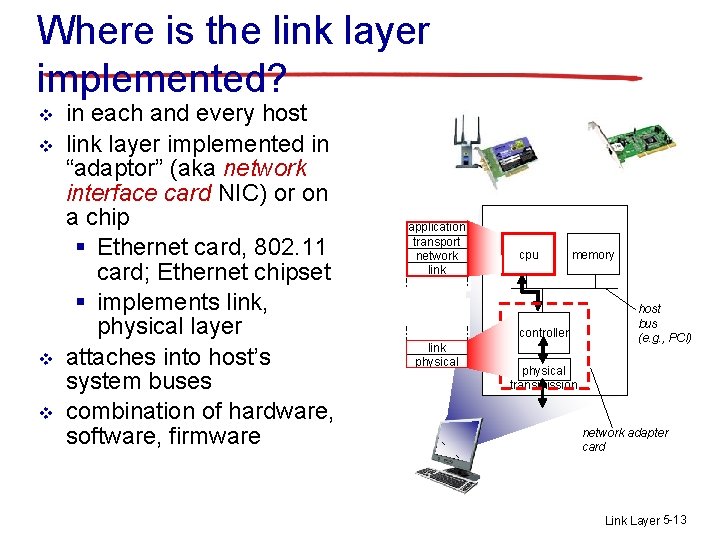
Where is the link layer implemented? v v in each and every host link layer implemented in “adaptor” (aka network interface card NIC) or on a chip § Ethernet card, 802. 11 card; Ethernet chipset § implements link, physical layer attaches into host’s system buses combination of hardware, software, firmware application transport network link cpu memory controller link physical host bus (e. g. , PCI) physical transmission network adapter card Link Layer 5 -13
Link layer, LANs: outline 5. 1 introduction, services 5. 2 error detection, correction 5. 3 multiple access protocols 5. 4 LANs § § SKIPPED addressing, ARP Ethernet switches VLANS Link Layer 5 -14
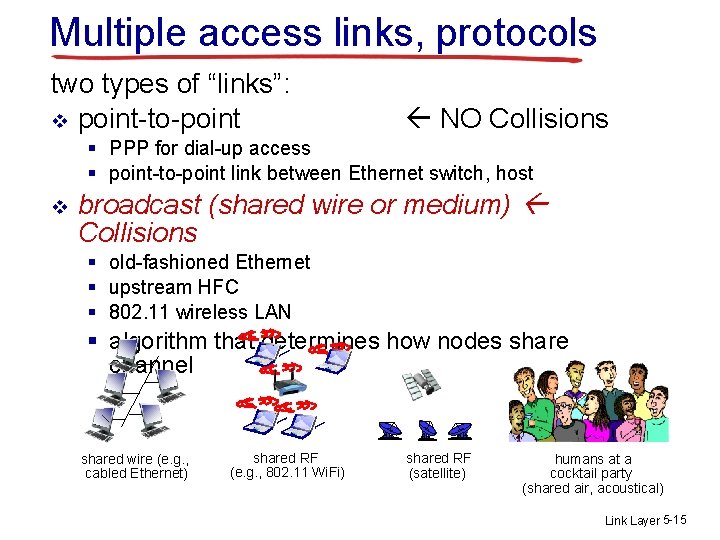
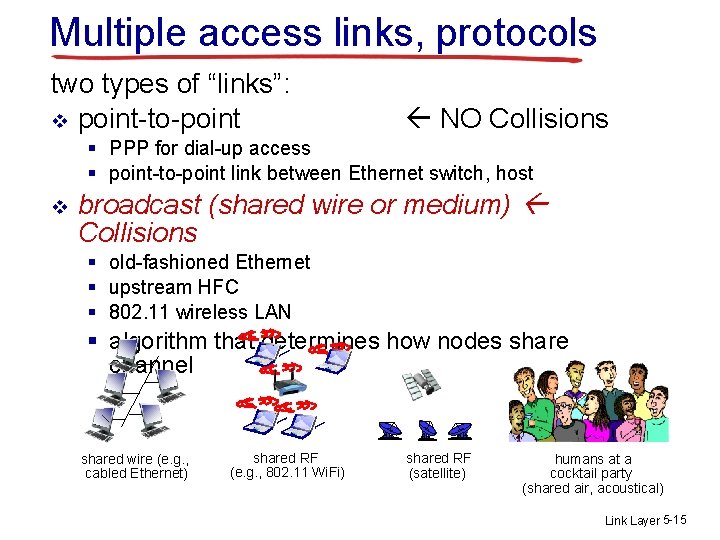
Multiple access links, protocols two types of “links”: v point-to-point NO Collisions § PPP for dial-up access § point-to-point link between Ethernet switch, host v broadcast (shared wire or medium) Collisions § old-fashioned Ethernet § upstream HFC § 802. 11 wireless LAN § algorithm that determines how nodes share channel shared wire (e. g. , cabled Ethernet) shared RF (e. g. , 802. 11 Wi. Fi) shared RF (satellite) humans at a cocktail party (shared air, acoustical) Link Layer 5 -15
MAC protocols: taxonomy three broad classes of sharing: v channel partitioning § divide channel into smaller “pieces” (time slots, frequency, code) § allocate piece to node for exclusive use § Subdividing the capacity – TDM, FDM v random access § channel not divided, allow collisions § “recover” from collisions v “taking turns” § nodes take turns, but nodes with more to send can take longer turns Link Layer 5 -16
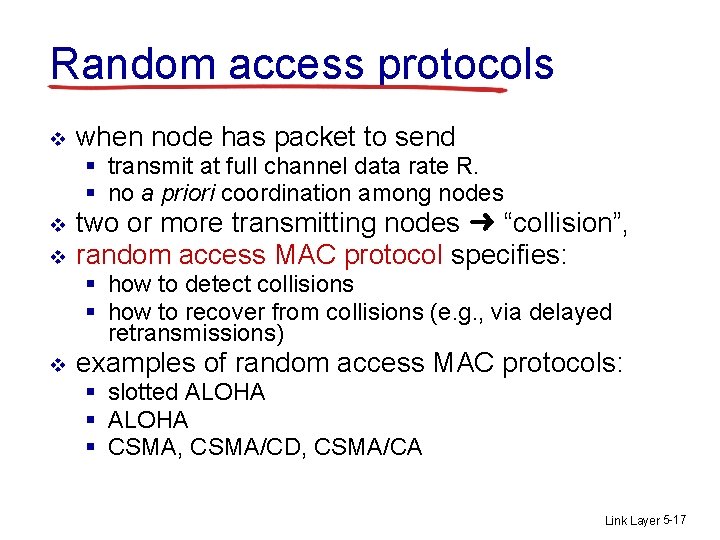
Random access protocols v when node has packet to send § transmit at full channel data rate R. § no a priori coordination among nodes v v two or more transmitting nodes ➜ “collision”, random access MAC protocol specifies: § how to detect collisions § how to recover from collisions (e. g. , via delayed retransmissions) v examples of random access MAC protocols: § slotted ALOHA § CSMA, CSMA/CD, CSMA/CA Link Layer 5 -17
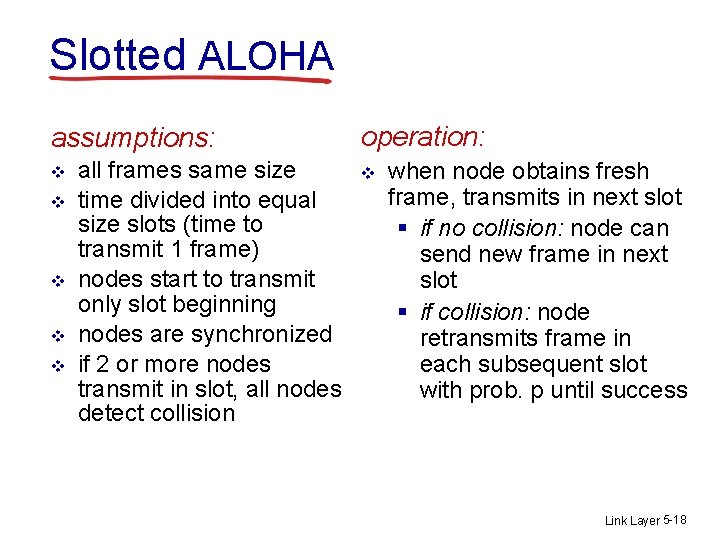
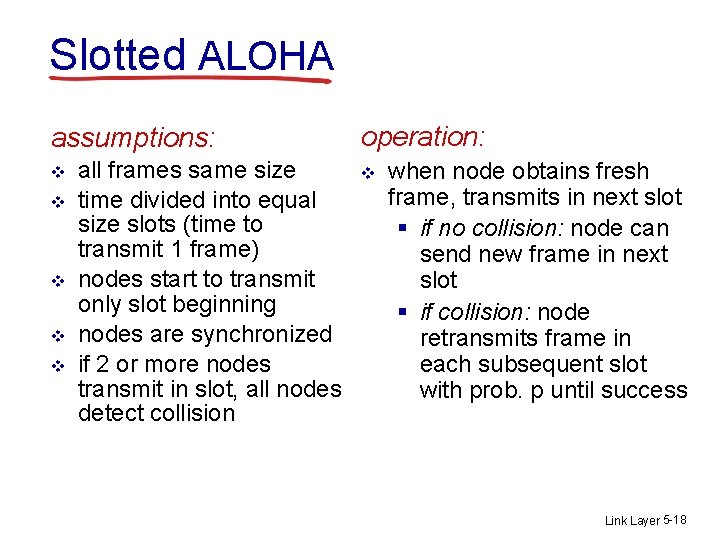
Slotted ALOHA assumptions: v v v all frames same size time divided into equal size slots (time to transmit 1 frame) nodes start to transmit only slot beginning nodes are synchronized if 2 or more nodes transmit in slot, all nodes detect collision operation: v when node obtains fresh frame, transmits in next slot § if no collision: node can send new frame in next slot § if collision: node retransmits frame in each subsequent slot with prob. p until success Link Layer 5 -18
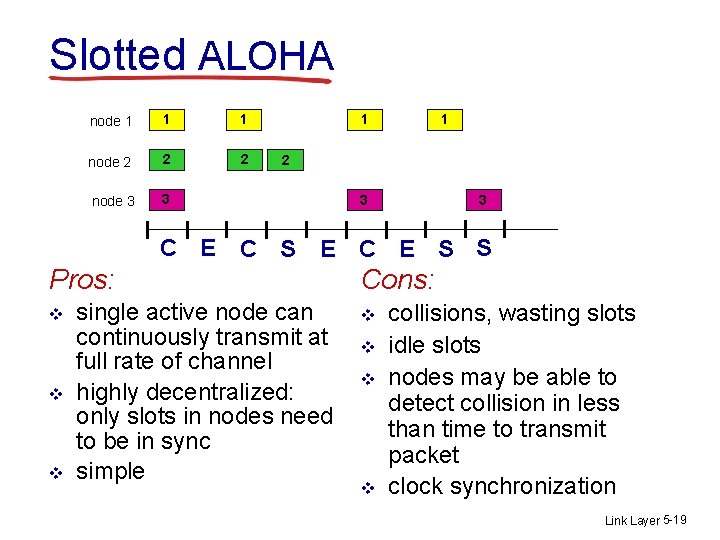
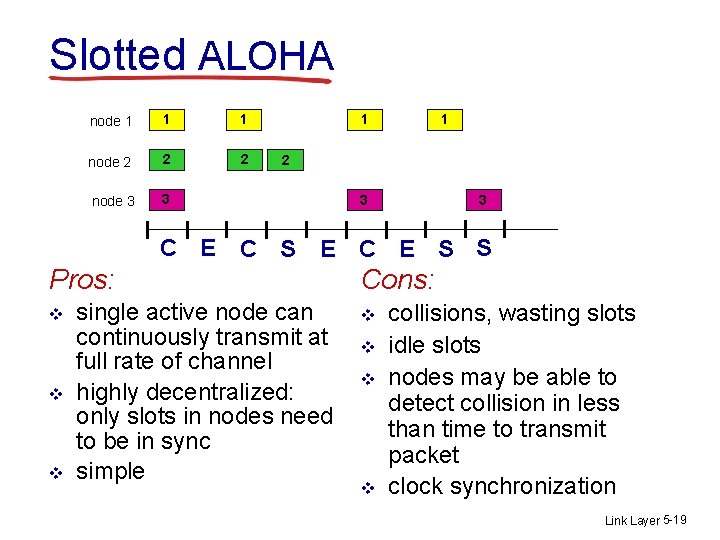
Slotted ALOHA node 1 1 1 node 2 2 2 node 3 3 1 1 2 3 3 C E C S E C E S S Pros: v v v single active node can continuously transmit at full rate of channel highly decentralized: only slots in nodes need to be in sync simple Cons: v v collisions, wasting slots idle slots nodes may be able to detect collision in less than time to transmit packet clock synchronization Link Layer 5 -19
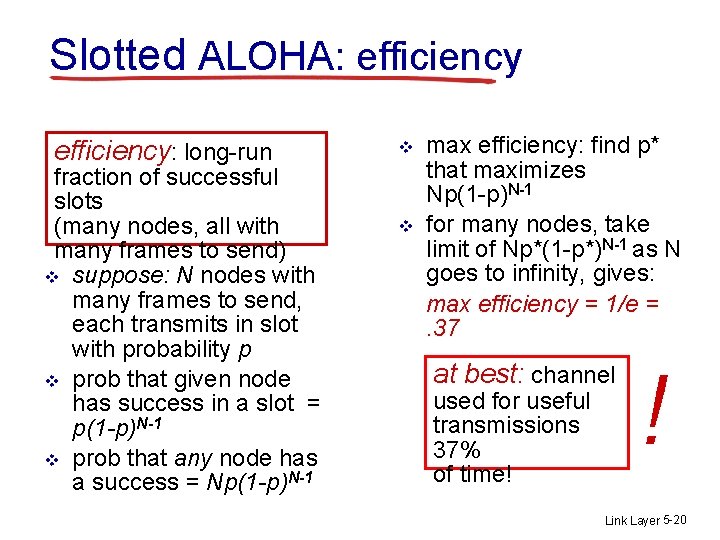
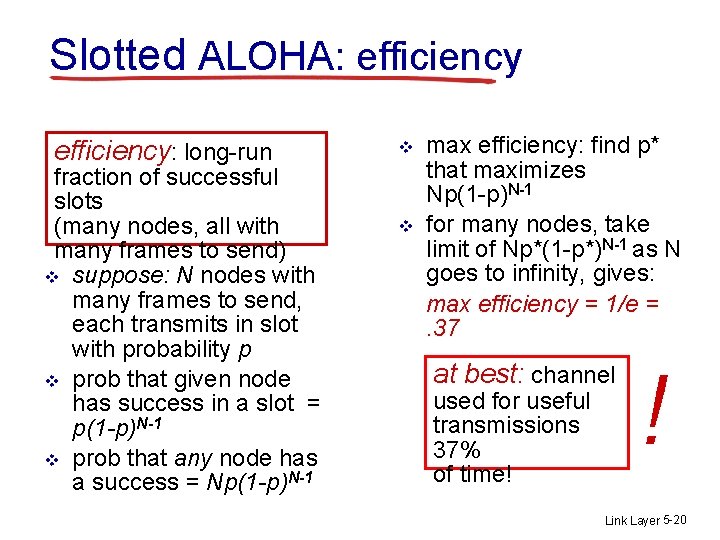
Slotted ALOHA: efficiency: long-run fraction of successful slots (many nodes, all with many frames to send) v suppose: N nodes with many frames to send, each transmits in slot with probability p v prob that given node has success in a slot = p(1 -p)N-1 v prob that any node has a success = Np(1 -p)N-1 v v max efficiency: find p* that maximizes Np(1 -p)N-1 for many nodes, take limit of Np*(1 -p*)N-1 as N goes to infinity, gives: max efficiency = 1/e =. 37 at best: channel used for useful transmissions 37% of time! ! Link Layer 5 -20
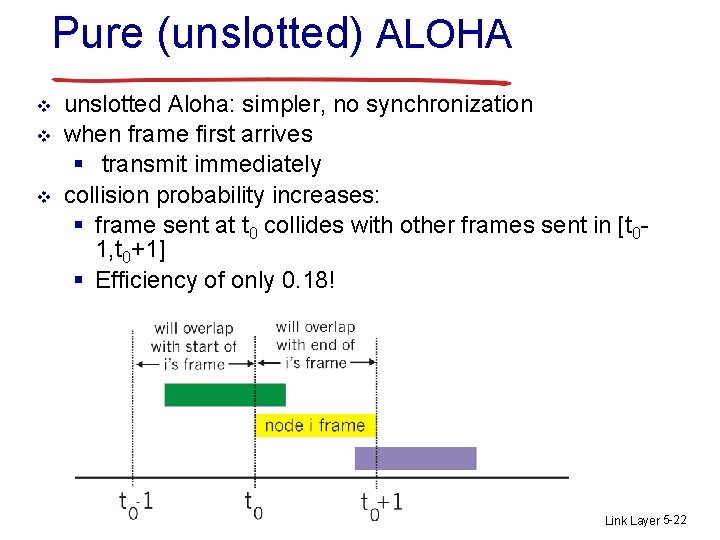
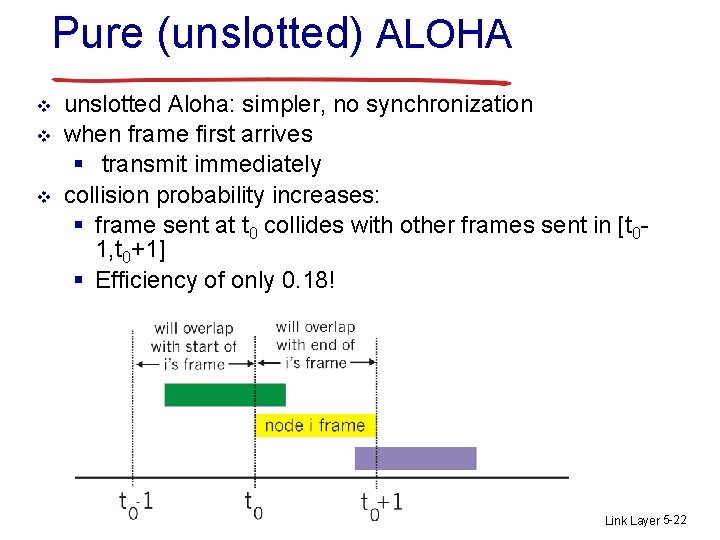
Slotted ALOHA: efficiency max efficiency: find p* that maximizes F(p) = Np(1 -p)N-1 v max efficiency when F’(p) = 0 d. F/dp = d (Np(1 -p)N-1 ) /dp = N(1 -p)N-1 + Np(N-1)(1 -p)N-2 v N(1 -p)N-1 = Np(N-1)(1 -p)N-1/ (1 – p) 1 = p(N – 1) / ( 1 – p) ( 1 – p ) = p ( N – 1) = p. N - p 1 = p. N p = 1 / N F(max) = N(1/N)(1 -(1/N))N-1 = ( 1 – 1/N ) N-1 As N goes to infinity F(max) = 1 / e = 0. 37 Link Layer 5 -21
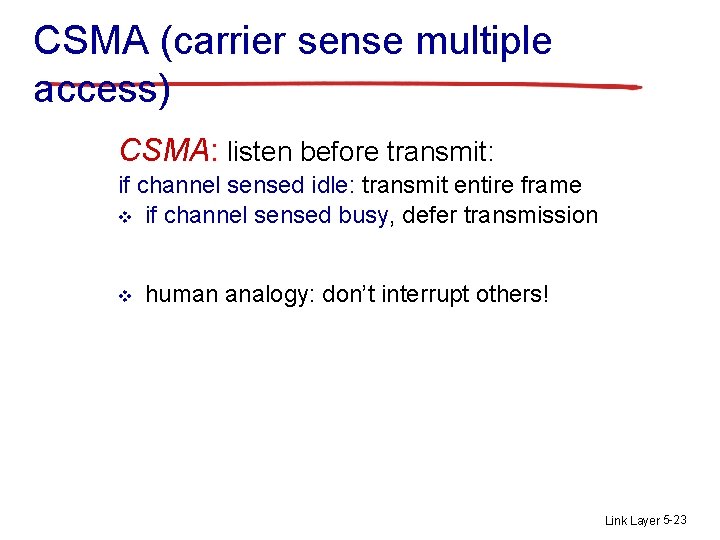
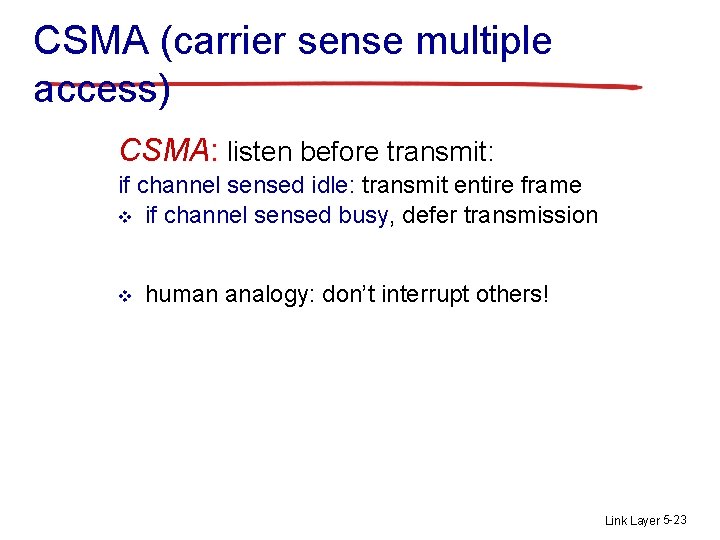
Pure (unslotted) ALOHA v v v unslotted Aloha: simpler, no synchronization when frame first arrives § transmit immediately collision probability increases: § frame sent at t 0 collides with other frames sent in [t 01, t 0+1] § Efficiency of only 0. 18! Link Layer 5 -22
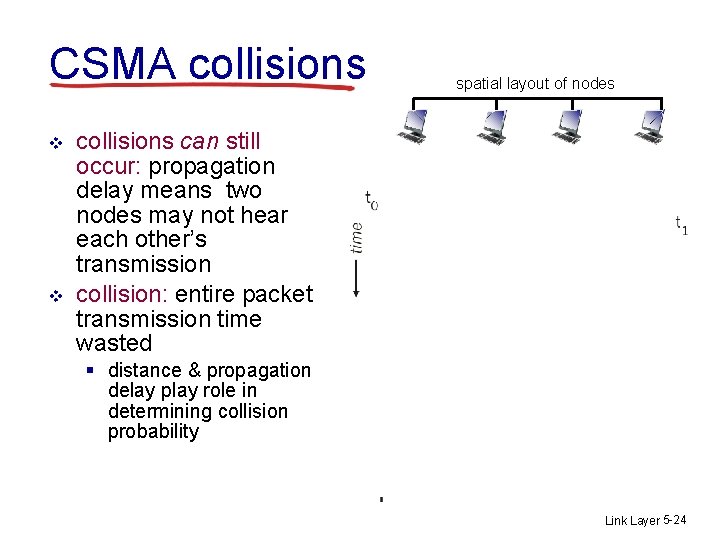
CSMA (carrier sense multiple access) CSMA: listen before transmit: if channel sensed idle: transmit entire frame v if channel sensed busy, defer transmission v human analogy: don’t interrupt others! Link Layer 5 -23
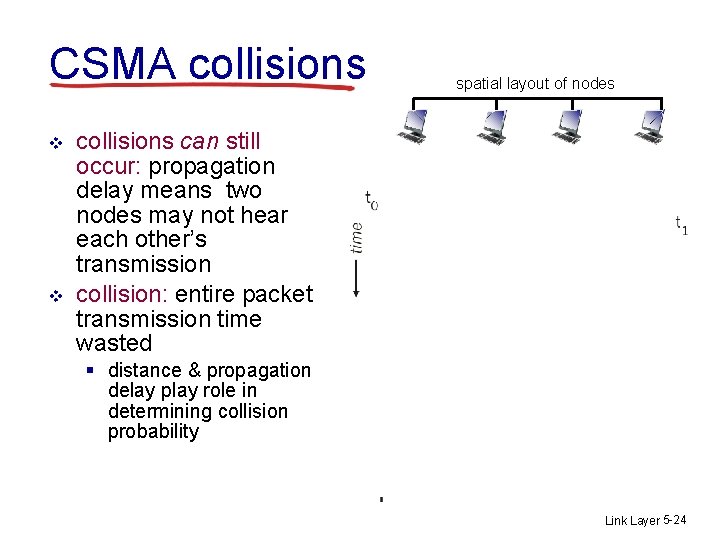
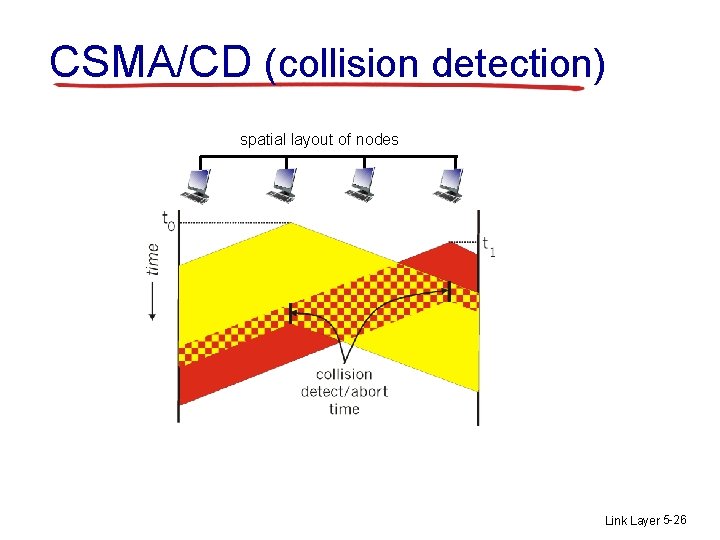
CSMA collisions v v spatial layout of nodes collisions can still occur: propagation delay means two nodes may not hear each other’s transmission collision: entire packet transmission time wasted § distance & propagation delay play role in determining collision probability Link Layer 5 -24
CSMA/CD (collision detection) CSMA/CD: carrier sensing, deferral as in CSMA § collisions detected within short time § colliding transmissions aborted, reducing channel wastage v collision detection: § easy in wired LANs: measure signal strengths, compare transmitted, received signals § difficult in wireless LANs: received signal strength overwhelmed by local transmission strength v human analogy: the polite conversationalist Link Layer 5 -25
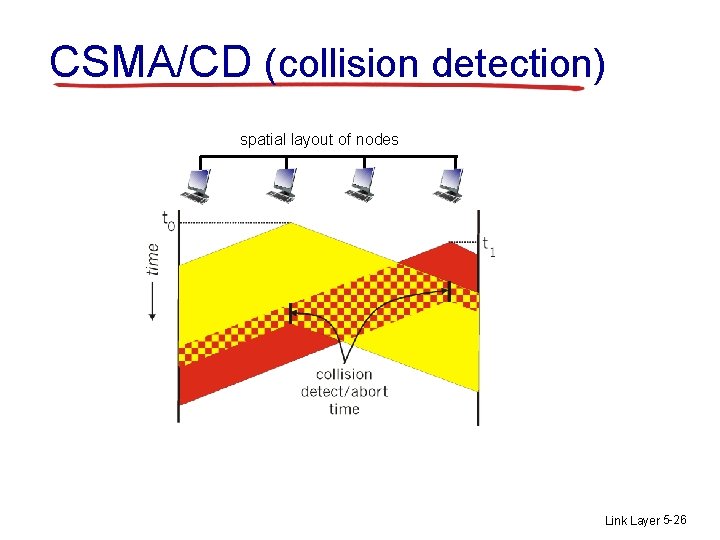
CSMA/CD (collision detection) spatial layout of nodes Link Layer 5 -26
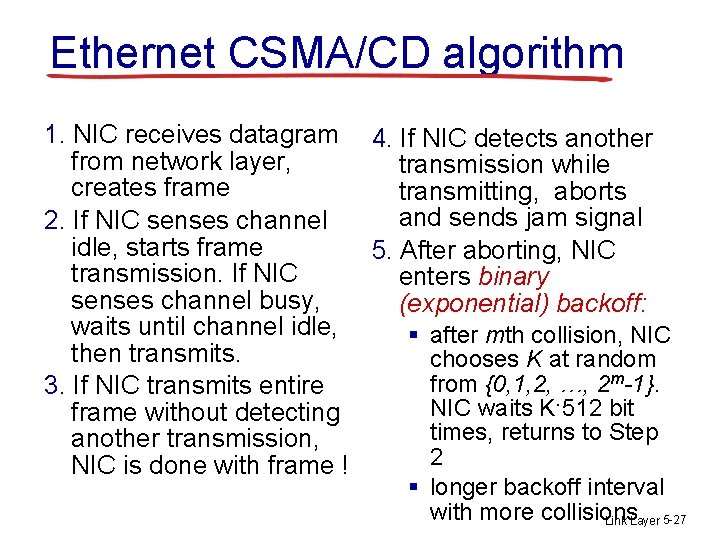
Ethernet CSMA/CD algorithm 1. NIC receives datagram 4. If NIC detects another from network layer, transmission while creates frame transmitting, aborts and sends jam signal 2. If NIC senses channel idle, starts frame 5. After aborting, NIC transmission. If NIC enters binary senses channel busy, (exponential) backoff: waits until channel idle, § after mth collision, NIC then transmits. chooses K at random from {0, 1, 2, …, 2 m-1}. 3. If NIC transmits entire NIC waits K·512 bit frame without detecting times, returns to Step another transmission, 2 NIC is done with frame ! § longer backoff interval with more collisions Link Layer 5 -27
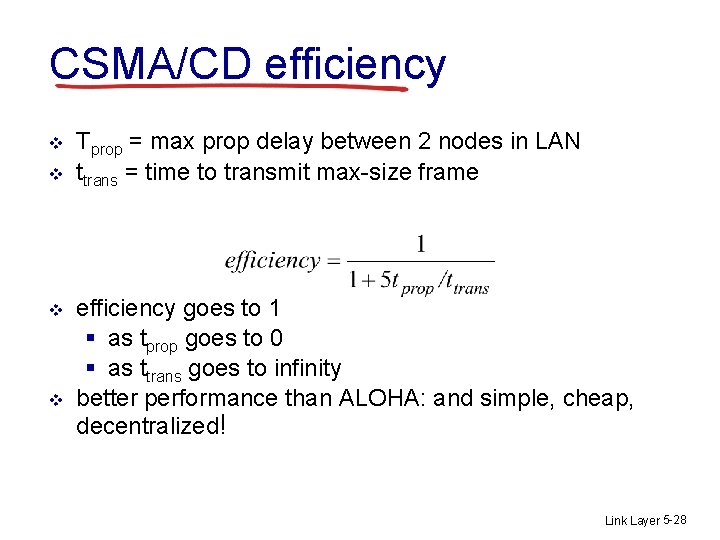
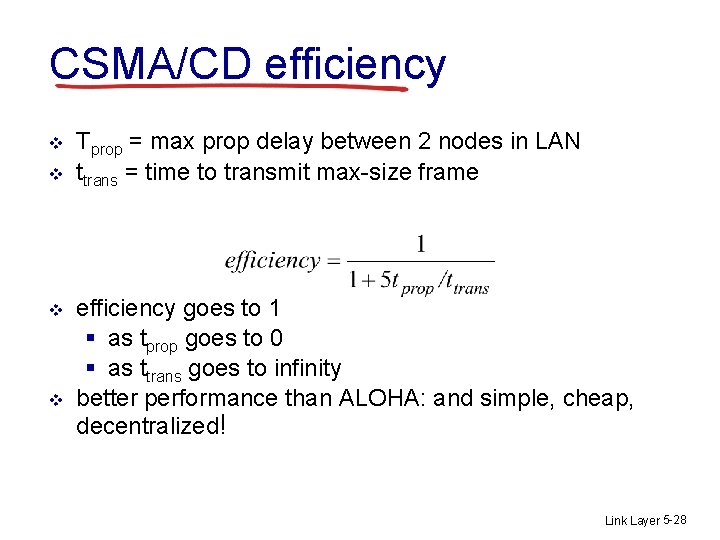
CSMA/CD efficiency v v Tprop = max prop delay between 2 nodes in LAN ttrans = time to transmit max-size frame efficiency goes to 1 § as tprop goes to 0 § as ttrans goes to infinity better performance than ALOHA: and simple, cheap, decentralized! Link Layer 5 -28
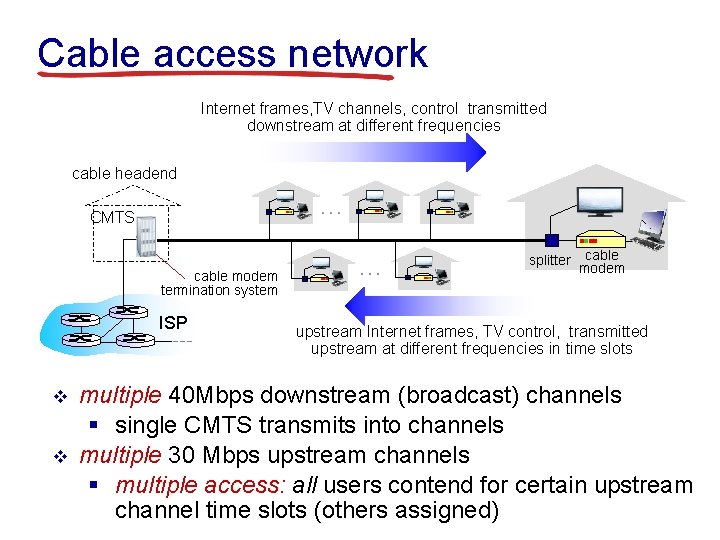
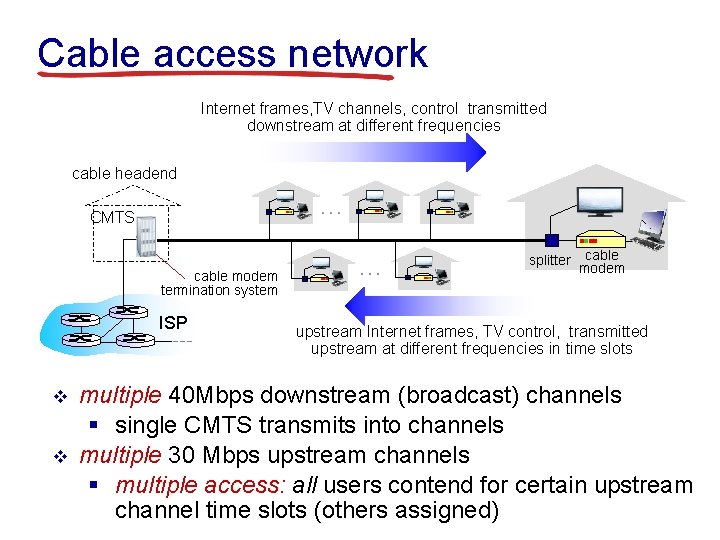
“Taking turns” MAC protocols token passing: v v v control token passed from one node to next sequentially. token message (nothing concerns: to send) § token overhead T § latency § single point of failure (token) T data Link Layer 5 -29
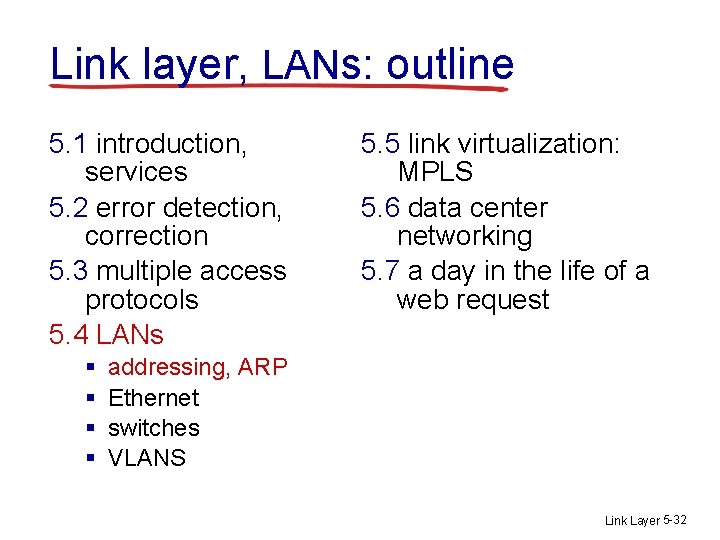
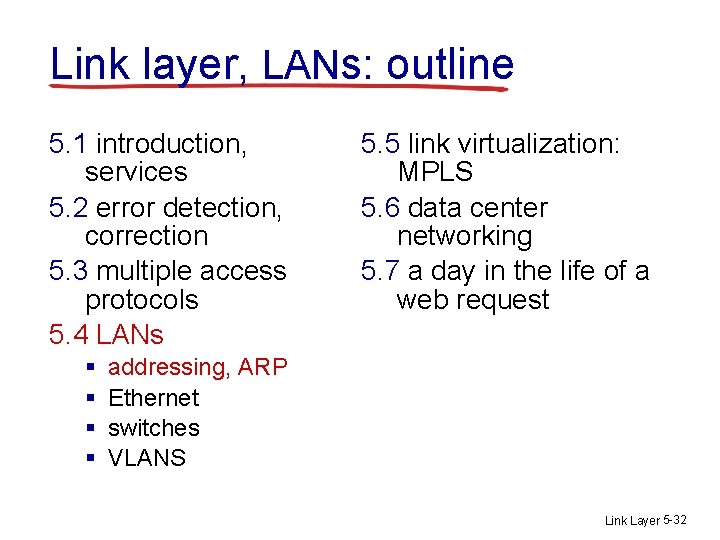
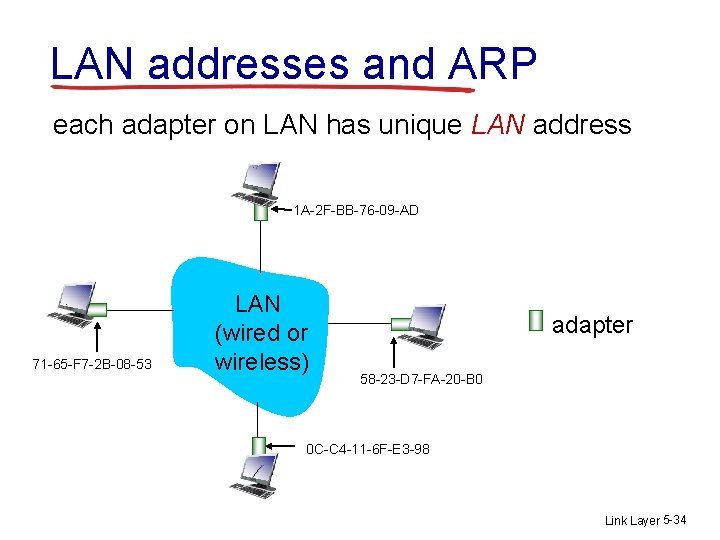
Cable access network Internet frames, TV channels, control transmitted downstream at different frequencies cable headend … CMTS cable modem termination system ISP v v … splitter cable modem upstream Internet frames, TV control, transmitted upstream at different frequencies in time slots multiple 40 Mbps downstream (broadcast) channels § single CMTS transmits into channels multiple 30 Mbps upstream channels § multiple access: all users contend for certain upstream channel time slots (others assigned)
![Cable access network cable headend MAP frame for Interval t 1 t 2 Downstream Cable access network cable headend MAP frame for Interval [t 1, t 2] Downstream](https://slidetodoc.com/presentation_image/1e414d7cca78bb4112317c5dce486cdf/image-31.jpg)
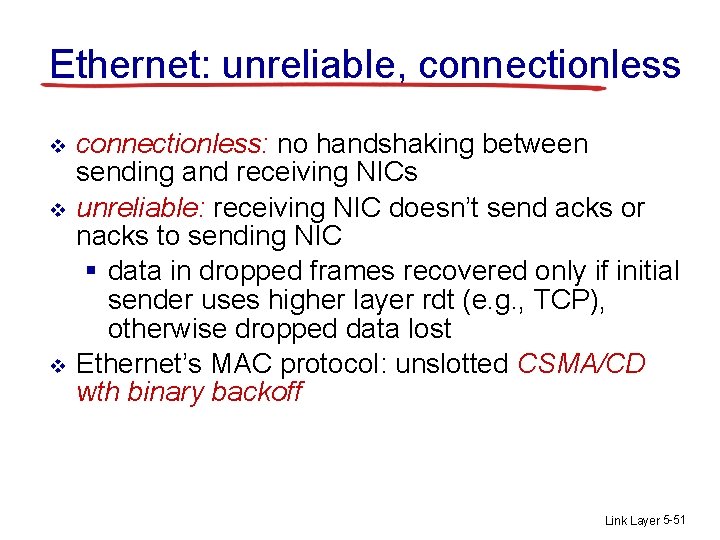
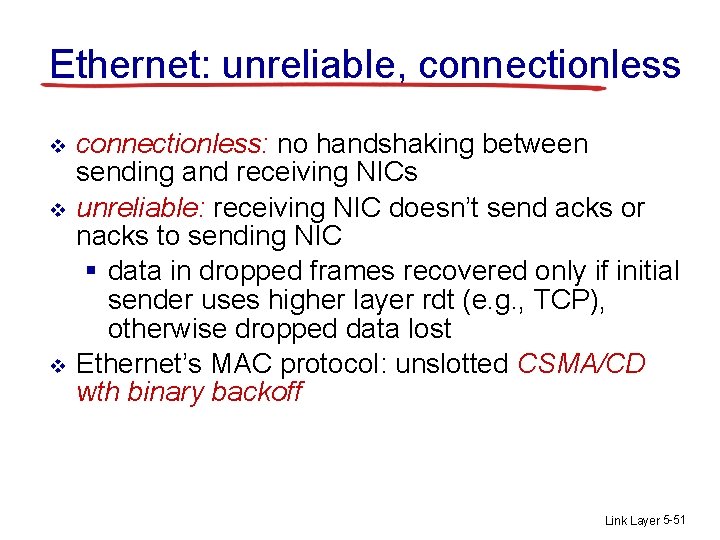
Cable access network cable headend MAP frame for Interval [t 1, t 2] Downstream channel i CMTS Upstream channel j t 1 Minislots containing minislots request frames t 2 Residences with cable modems Assigned minislots containing cable modem upstream data frames DOCSIS: data over cable service interface spec v v FDM over upstream, downstream frequency channels TDM upstream: some slots assigned, some have contention § downstream MAP frame: assigns upstream slots § request for upstream slots (and data) transmitted random access (binary backoff) in selected Link slots Layer 5 -31
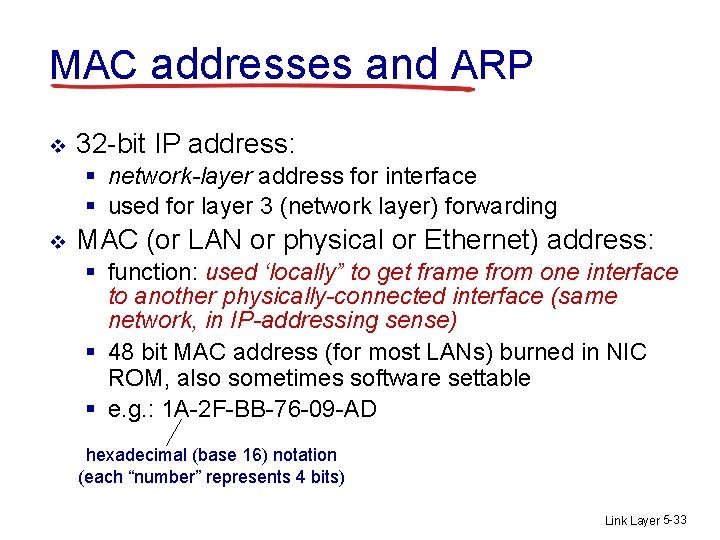
Link layer, LANs: outline 5. 1 introduction, services 5. 2 error detection, correction 5. 3 multiple access protocols 5. 4 LANs § § 5. 5 link virtualization: MPLS 5. 6 data center networking 5. 7 a day in the life of a web request addressing, ARP Ethernet switches VLANS Link Layer 5 -32
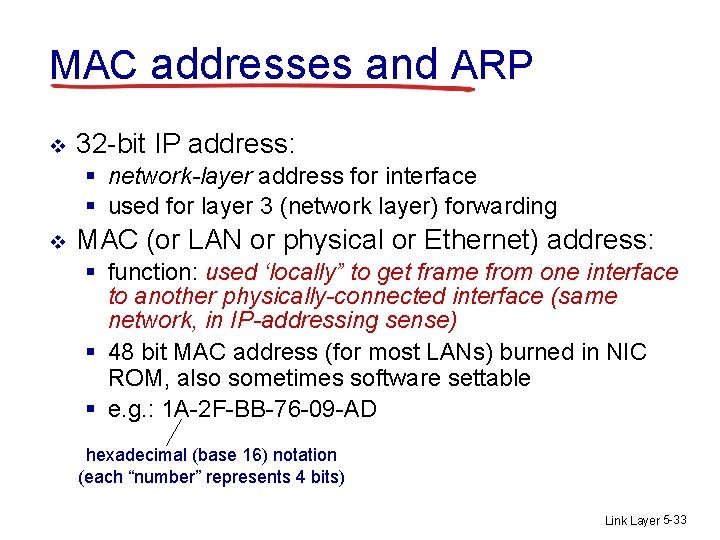
MAC addresses and ARP v 32 -bit IP address: § network-layer address for interface § used for layer 3 (network layer) forwarding v MAC (or LAN or physical or Ethernet) address: § function: used ‘locally” to get frame from one interface to another physically-connected interface (same network, in IP-addressing sense) § 48 bit MAC address (for most LANs) burned in NIC ROM, also sometimes software settable § e. g. : 1 A-2 F-BB-76 -09 -AD hexadecimal (base 16) notation (each “number” represents 4 bits) Link Layer 5 -33
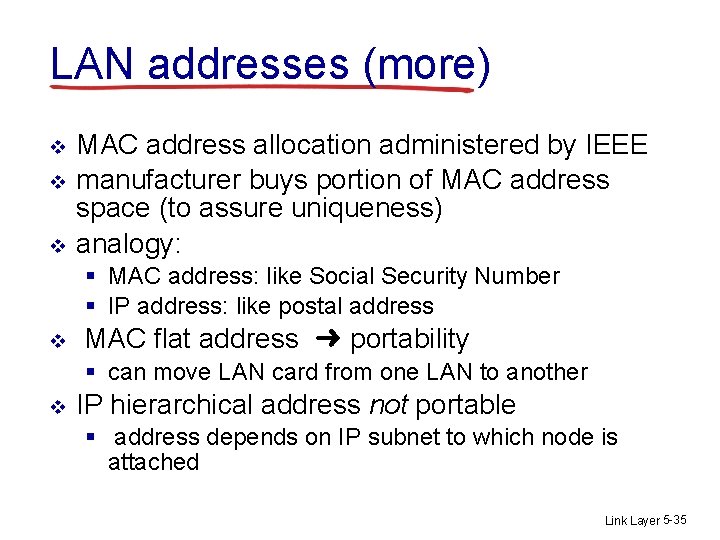
LAN addresses and ARP each adapter on LAN has unique LAN address 1 A-2 F-BB-76 -09 -AD 71 -65 -F 7 -2 B-08 -53 LAN (wired or wireless) adapter 58 -23 -D 7 -FA-20 -B 0 0 C-C 4 -11 -6 F-E 3 -98 Link Layer 5 -34
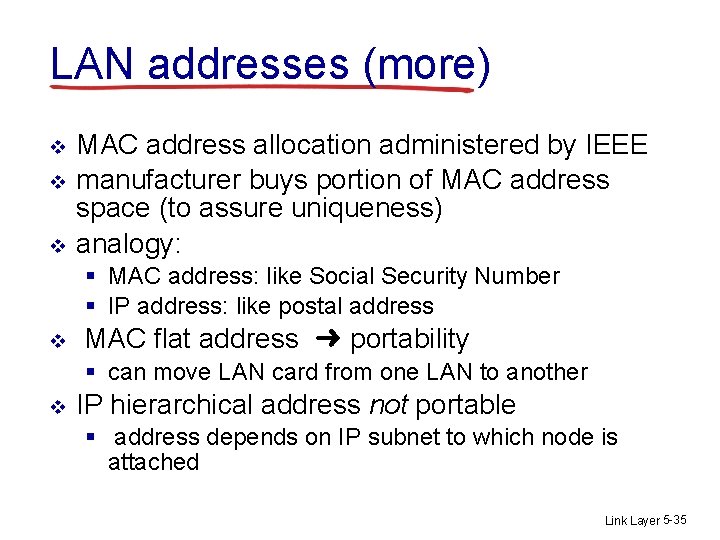
LAN addresses (more) v v v MAC address allocation administered by IEEE manufacturer buys portion of MAC address space (to assure uniqueness) analogy: § MAC address: like Social Security Number § IP address: like postal address v MAC flat address ➜ portability § can move LAN card from one LAN to another v IP hierarchical address not portable § address depends on IP subnet to which node is attached Link Layer 5 -35
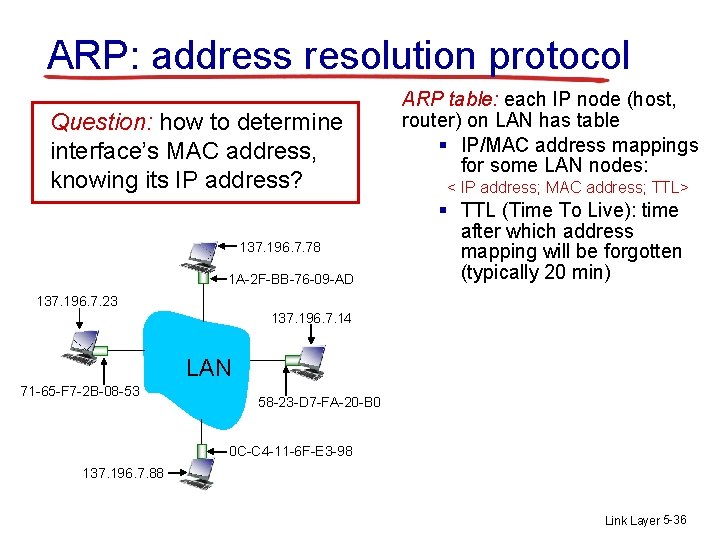
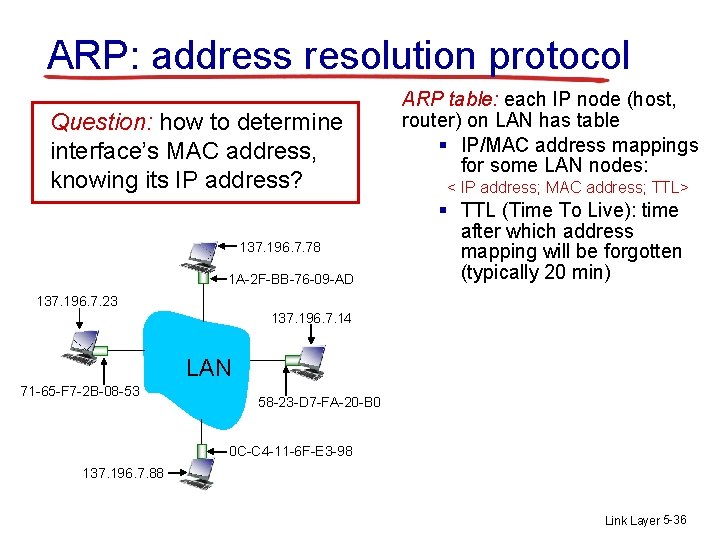
ARP: address resolution protocol Question: how to determine interface’s MAC address, knowing its IP address? 137. 196. 7. 78 1 A-2 F-BB-76 -09 -AD ARP table: each IP node (host, router) on LAN has table § IP/MAC address mappings for some LAN nodes: < IP address; MAC address; TTL> § TTL (Time To Live): time after which address mapping will be forgotten (typically 20 min) 137. 196. 7. 23 137. 196. 7. 14 LAN 71 -65 -F 7 -2 B-08 -53 58 -23 -D 7 -FA-20 -B 0 0 C-C 4 -11 -6 F-E 3 -98 137. 196. 7. 88 Link Layer 5 -36
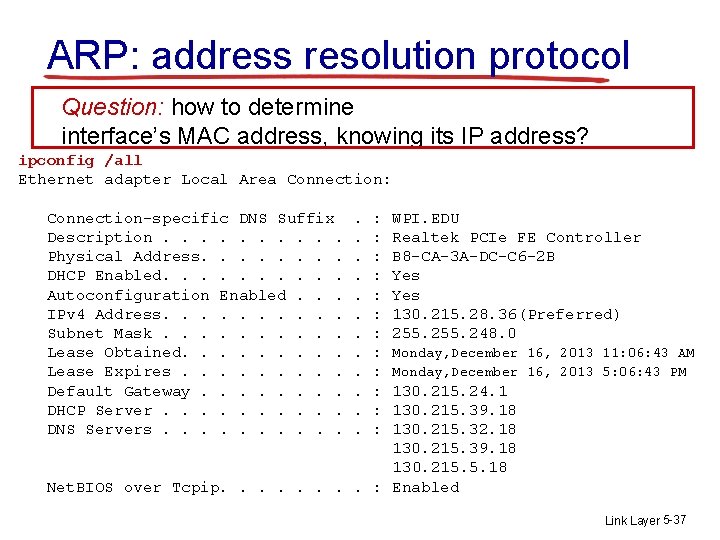
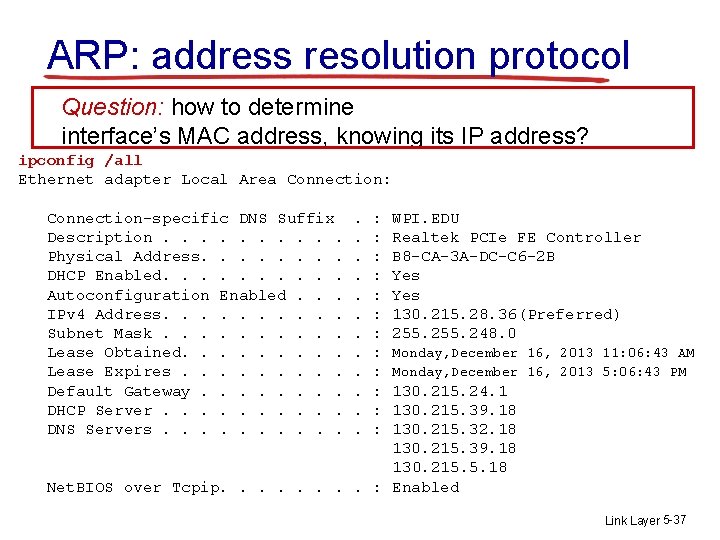
ARP: address resolution protocol Question: how to determine interface’s MAC address, knowing its IP address? ipconfig /all Ethernet adapter Local Area Connection: Connection-specific DNS Suffix Description. . Physical Address. . . . DHCP Enabled. . Autoconfiguration Enabled. . . IPv 4 Address. . Subnet Mask. . Lease Obtained. . Lease Expires. . Default Gateway. . . . DHCP Server. . DNS Servers. . . . . : : : WPI. EDU Realtek PCIe FE Controller B 8 -CA-3 A-DC-C 6 -2 B Yes 130. 215. 28. 36(Preferred) 255. 248. 0 Monday, December 16, 2013 11: 06: 43 AM Monday, December 16, 2013 5: 06: 43 PM 130. 215. 24. 1 130. 215. 39. 18 130. 215. 32. 18 130. 215. 39. 18 130. 215. 5. 18 Net. BIOS over Tcpip. . . . : Enabled Link Layer 5 -37
ARP protocol: same LAN v A wants to send datagram to B § B’s MAC address not in A’s ARP table. v A broadcasts ARP query packet, containing B's IP address § dest MAC address = FFFF-FF-FF § all nodes on LAN receive ARP query v v B receives ARP packet, replies to A with its (B's) MAC address § frame sent to A’s MAC address (unicast) A caches (saves) IP-to. MAC address pair in its ARP table until information becomes old (times out) § soft state: information that times out (goes away) unless refreshed v ARP is “plug-and-play”: § nodes create their ARP tables without intervention from net administrator Link Layer 5 -38
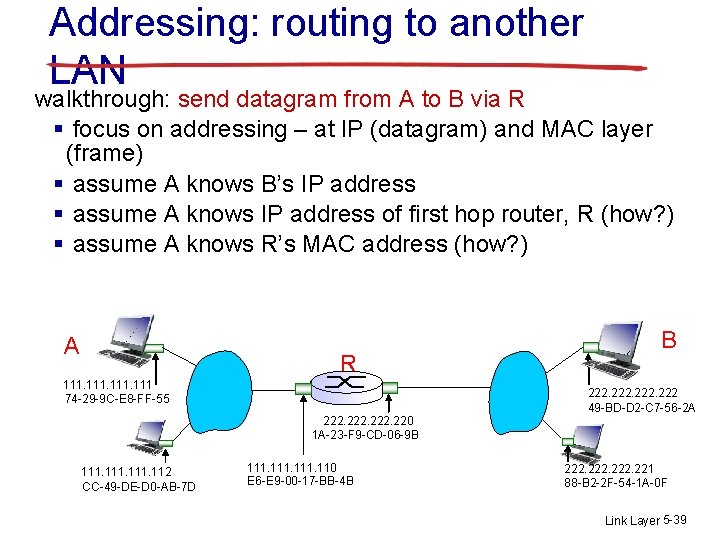
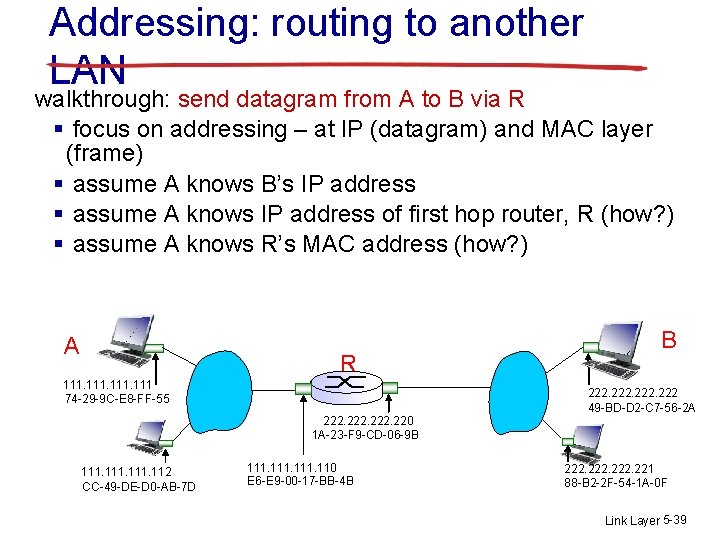
Addressing: routing to another LAN walkthrough: send datagram from A to B via R § focus on addressing – at IP (datagram) and MAC layer (frame) § assume A knows B’s IP address § assume A knows IP address of first hop router, R (how? ) § assume A knows R’s MAC address (how? ) A R 111 74 -29 -9 C-E 8 -FF-55 B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -39
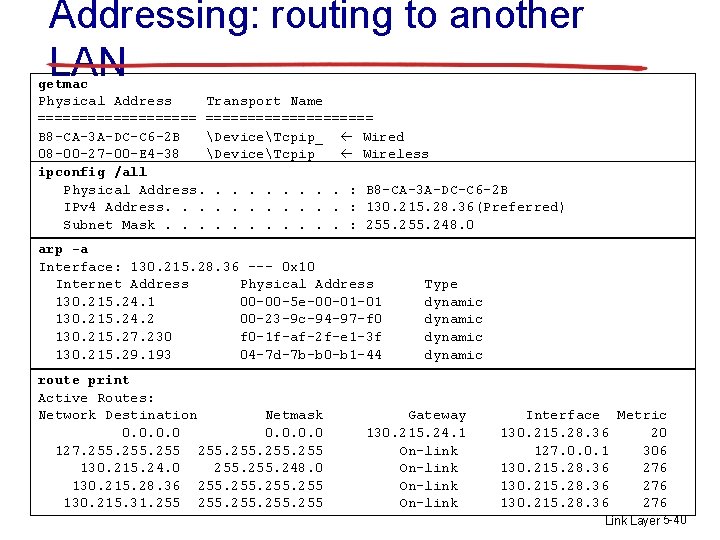
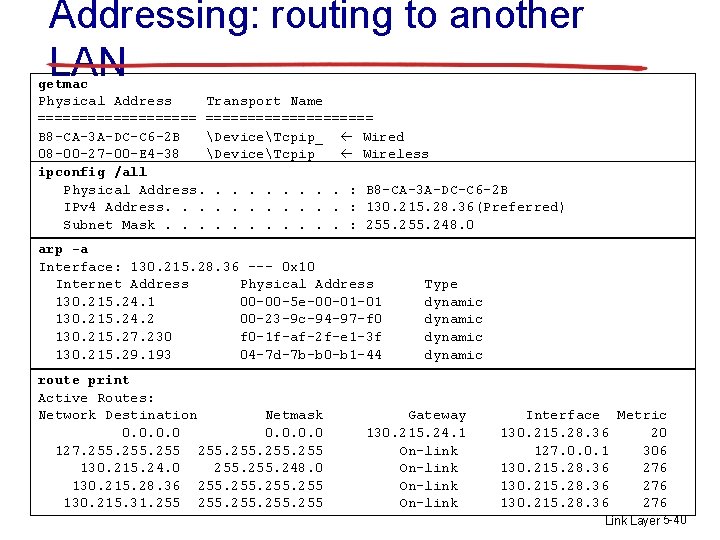
Addressing: routing to another LAN getmac Physical Address Transport Name ==================== B 8 -CA-3 A-DC-C 6 -2 B DeviceTcpip_ Wired 08 -00 -27 -00 -E 4 -38 DeviceTcpip_ Wireless ipconfig /all Physical Address. . : B 8 -CA-3 A-DC-C 6 -2 B IPv 4 Address. . . : 130. 215. 28. 36(Preferred) Subnet Mask. . . : 255. 248. 0 arp -a Interface: 130. 215. 28. 36 --- 0 x 10 Internet Address Physical Address 130. 215. 24. 1 00 -00 -5 e-00 -01 -01 130. 215. 24. 2 00 -23 -9 c-94 -97 -f 0 130. 215. 27. 230 f 0 -1 f-af-2 f-e 1 -3 f 130. 215. 29. 193 04 -7 d-7 b-b 0 -b 1 -44 route print Active Routes: Network Destination Netmask 0. 0 127. 255 130. 215. 24. 0 255. 248. 0 130. 215. 28. 36 255 130. 215. 31. 255 Type dynamic Gateway 130. 215. 24. 1 On-link Interface Metric 130. 215. 28. 36 20 127. 0. 0. 1 306 130. 215. 28. 36 276 Link Layer 5 -40
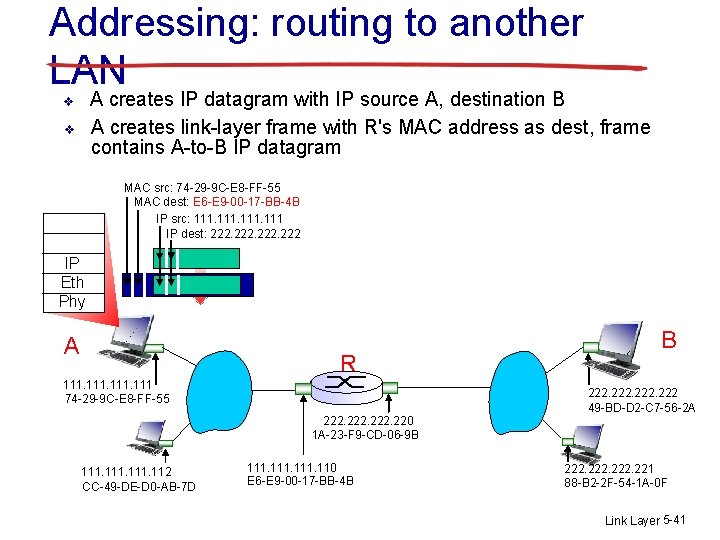
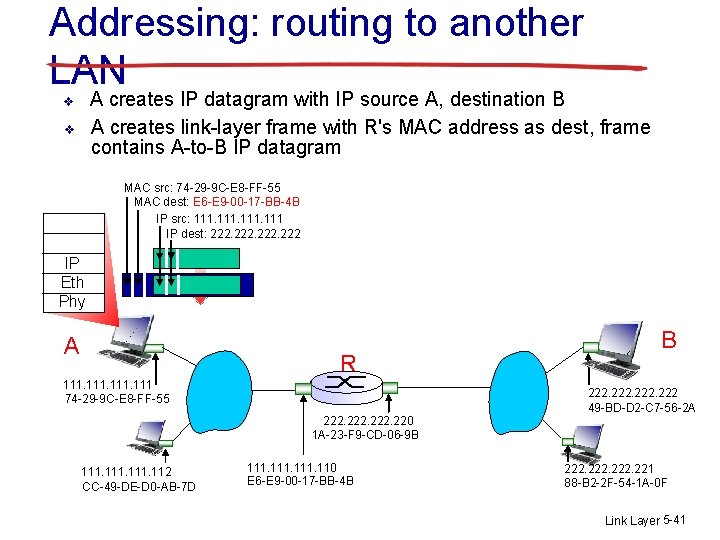
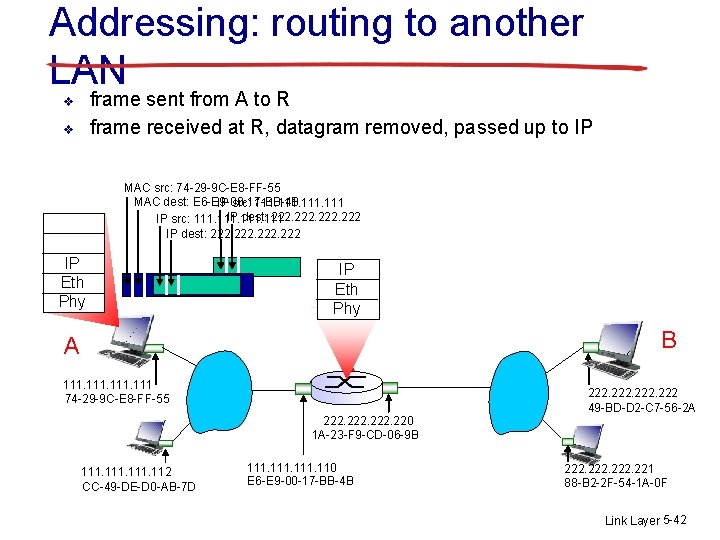
Addressing: routing to another LAN A creates IP datagram with IP source A, destination B A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram v v MAC src: 74 -29 -9 C-E 8 -FF-55 MAC dest: E 6 -E 9 -00 -17 -BB-4 B IP src: 111 IP dest: 222 IP Eth Phy A R 111 74 -29 -9 C-E 8 -FF-55 B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -41
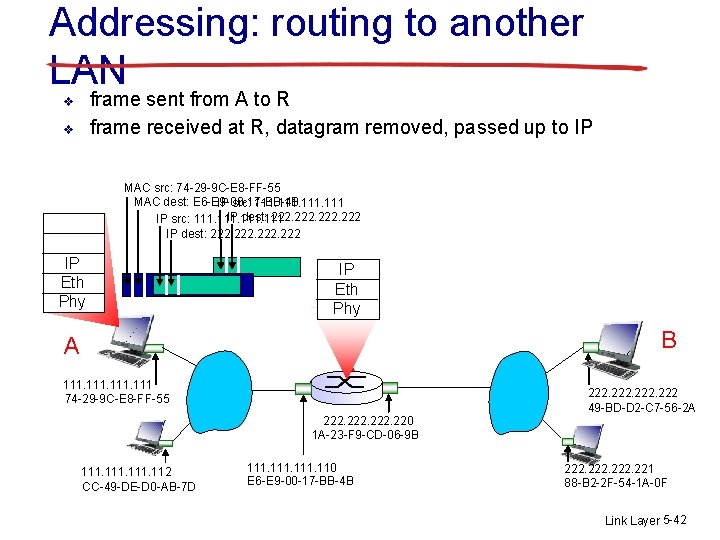
Addressing: routing to another LAN frame sent from A to R frame received at R, datagram removed, passed up to IP v v MAC src: 74 -29 -9 C-E 8 -FF-55 MAC dest: E 6 -E 9 -00 -17 -BB-4 B IP src: 111 IP dest: 222 IP Eth Phy A IP Eth Phy R 111 74 -29 -9 C-E 8 -FF-55 B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -42
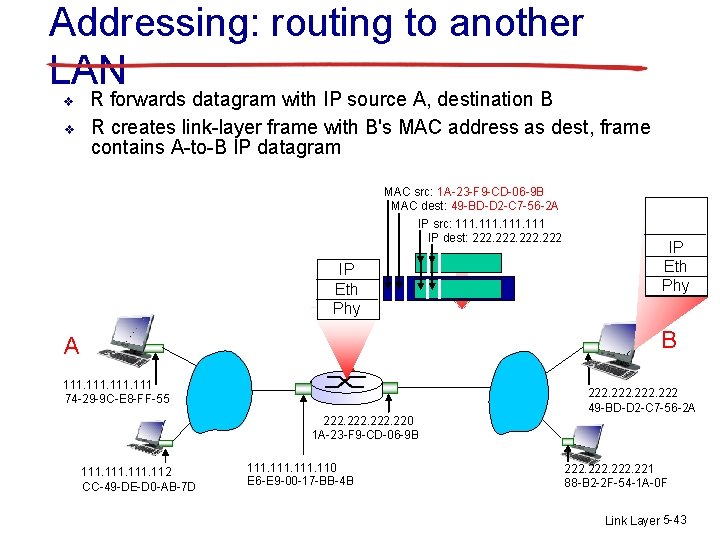
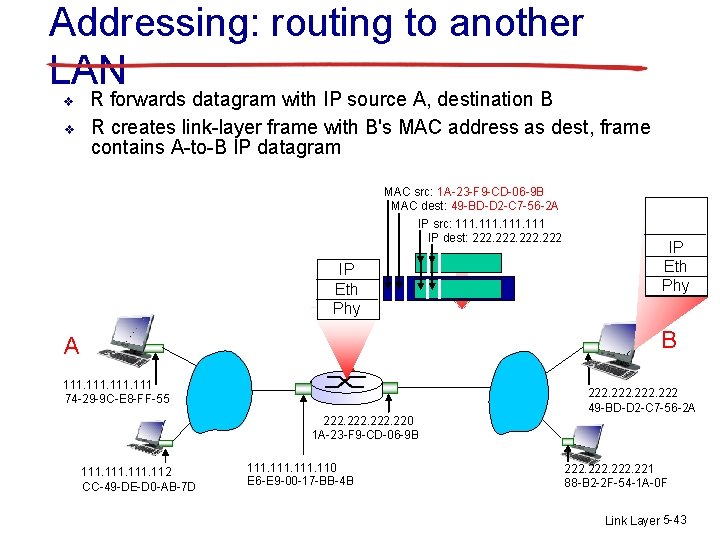
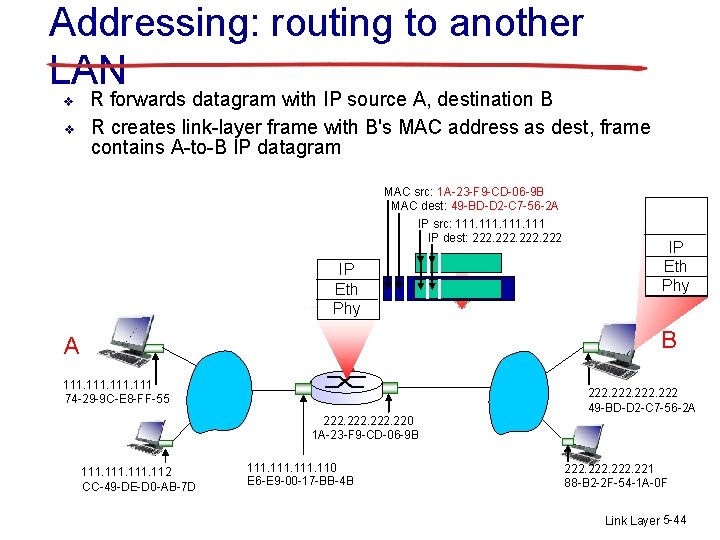
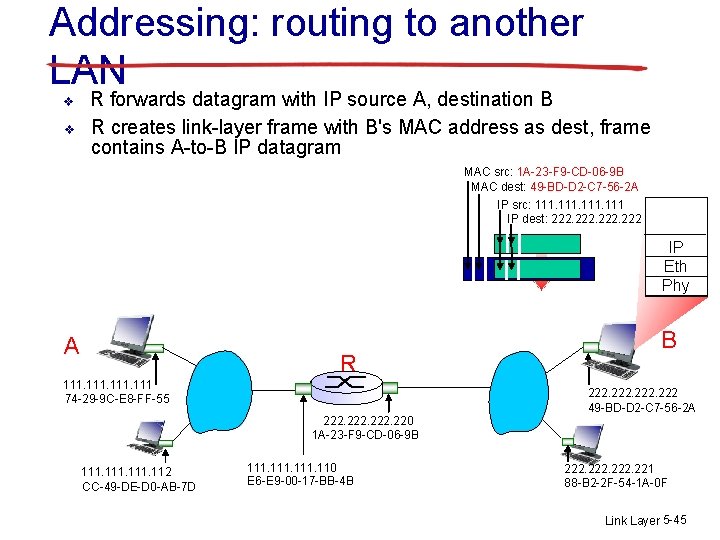
Addressing: routing to another LAN v v R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1 A-23 -F 9 -CD-06 -9 B MAC dest: 49 -BD-D 2 -C 7 -56 -2 A IP src: 111 IP dest: 222 IP Eth Phy A R 111 74 -29 -9 C-E 8 -FF-55 IP Eth Phy B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -43
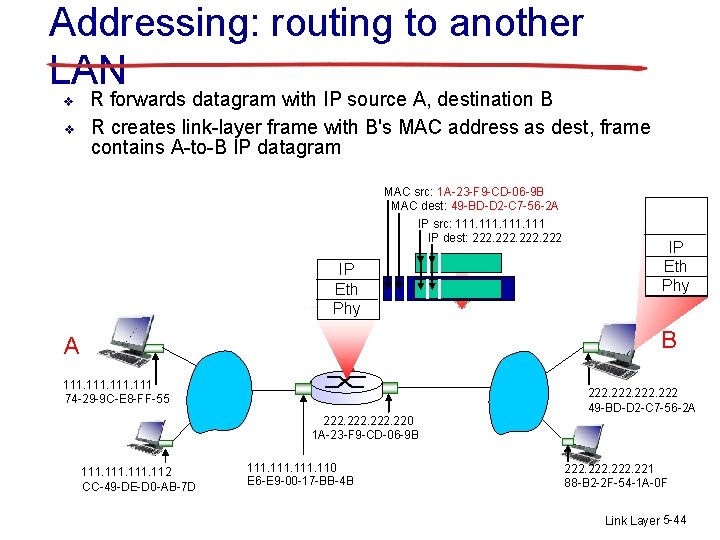
Addressing: routing to another LAN v v R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1 A-23 -F 9 -CD-06 -9 B MAC dest: 49 -BD-D 2 -C 7 -56 -2 A IP src: 111 IP dest: 222 IP Eth Phy A R 111 74 -29 -9 C-E 8 -FF-55 IP Eth Phy B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -44
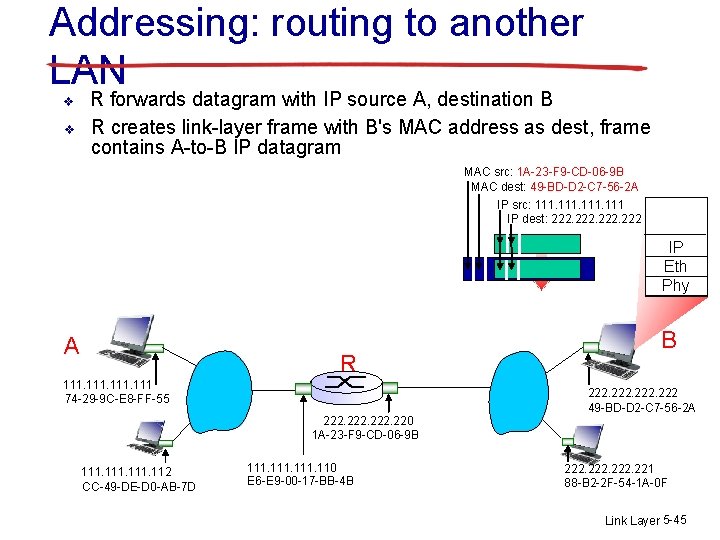
Addressing: routing to another LAN v v R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1 A-23 -F 9 -CD-06 -9 B MAC dest: 49 -BD-D 2 -C 7 -56 -2 A IP src: 111 IP dest: 222 IP Eth Phy A R 111 74 -29 -9 C-E 8 -FF-55 B 222 49 -BD-D 2 -C 7 -56 -2 A 222. 220 1 A-23 -F 9 -CD-06 -9 B 111. 112 CC-49 -DE-D 0 -AB-7 D 111. 110 E 6 -E 9 -00 -17 -BB-4 B 222. 221 88 -B 2 -2 F-54 -1 A-0 F Link Layer 5 -45
Link layer, LANs: outline 5. 1 introduction, services 5. 2 error detection, correction 5. 3 multiple access protocols 5. 4 LANs § § 5. 5 link virtualization: MPLS 5. 6 data center networking 5. 7 a day in the life of a web request addressing, ARP Ethernet switches VLANS Link Layer 5 -46
Ethernet “dominant” wired LAN technology: v cheap $20 for NIC v first widely used LAN technology v simpler, cheaper than token LANs and ATM v kept up with speed race: 10 Mbps – 10 Gbps Metcalfe’s Ethernet sketch Link Layer 5 -47
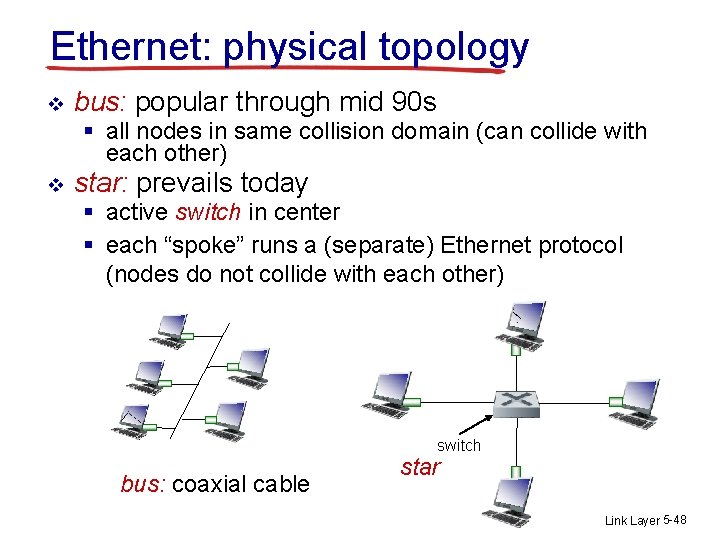
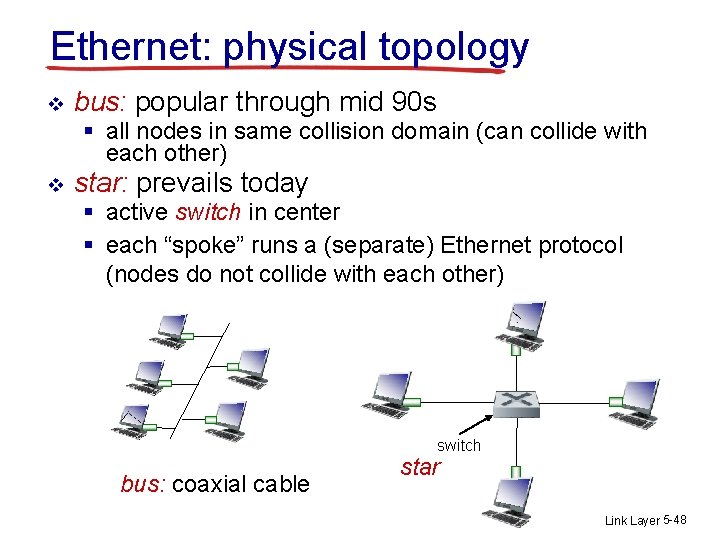
Ethernet: physical topology v bus: popular through mid 90 s § all nodes in same collision domain (can collide with each other) v star: prevails today § active switch in center § each “spoke” runs a (separate) Ethernet protocol (nodes do not collide with each other) switch bus: coaxial cable star Link Layer 5 -48
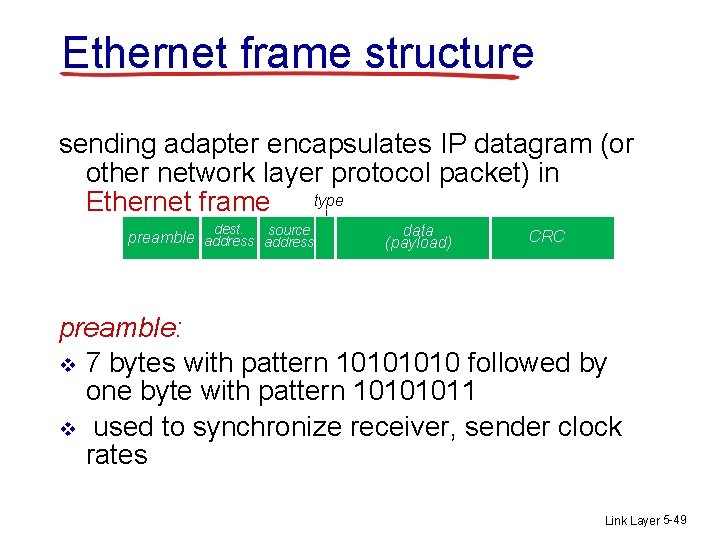
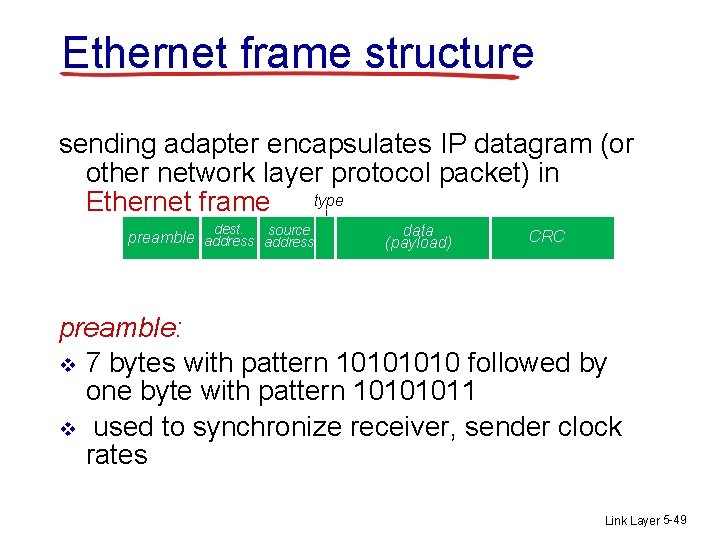
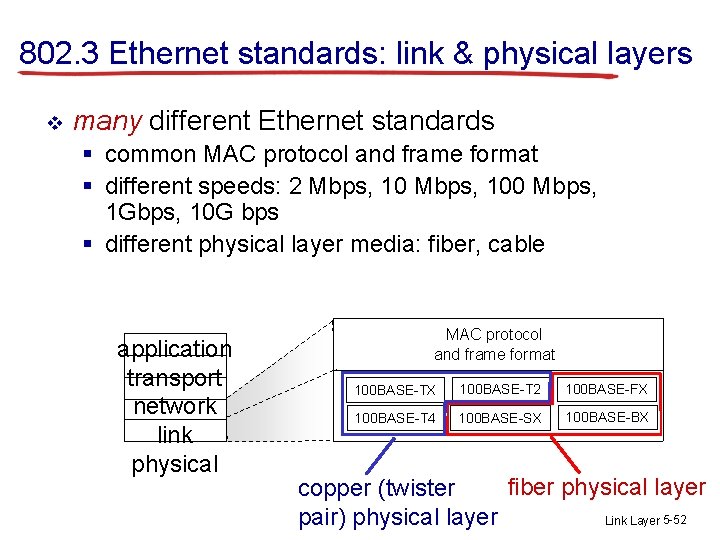
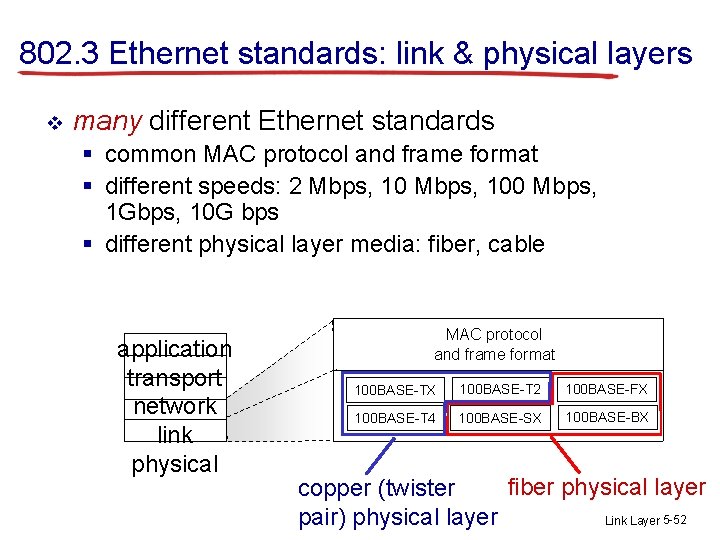
Ethernet frame structure sending adapter encapsulates IP datagram (or other network layer protocol packet) in type Ethernet frame dest. source preamble address data (payload) CRC preamble: v 7 bytes with pattern 1010 followed by one byte with pattern 10101011 v used to synchronize receiver, sender clock rates Link Layer 5 -49
Ethernet frame structure (more) v addresses: 6 byte source, destination MAC addresses § if adapter receives frame with matching destination address, or with broadcast address (e. g. ARP packet), it passes data in frame to network layer protocol § otherwise, adapter discards frame v v type: indicates higher layer protocol (mostly IP but others possible, e. g. , Novell IPX, Apple. Talk) CRC: cyclic redundancy check at receiver § error detected: frame is dropped type dest. source preamble address data (payload) CRC Link Layer 5 -50
Ethernet: unreliable, connectionless v v v connectionless: no handshaking between sending and receiving NICs unreliable: receiving NIC doesn’t send acks or nacks to sending NIC § data in dropped frames recovered only if initial sender uses higher layer rdt (e. g. , TCP), otherwise dropped data lost Ethernet’s MAC protocol: unslotted CSMA/CD wth binary backoff Link Layer 5 -51
802. 3 Ethernet standards: link & physical layers v many different Ethernet standards § common MAC protocol and frame format § different speeds: 2 Mbps, 100 Mbps, 1 Gbps, 10 G bps § different physical layer media: fiber, cable application transport network link physical MAC protocol and frame format 100 BASE-TX 100 BASE-T 2 100 BASE-FX 100 BASE-T 4 100 BASE-SX 100 BASE-BX fiber physical layer copper (twister Link Layer 5 -52 pair) physical layer
The End is Near!