Lecture 12 Decrypting Work Circle Fractal by Ramsey
Lecture 12: Decrypting Work Circle Fractal by Ramsey Arnaoot and Qi Wang CS 200: Computer Science David Evans University of Virginia 12 February 2003 CS 200 Spring 2003 http: //www. cs. virginia. edu/evans Computer Science
Menu • Measuring Work • Faster (? ) Sorting • PS 4: Cryptology 12 February 2003 CS 200 Spring 2003 2
Sorting (define (sort cf lst) (if (null? lst) lst (let ((most (find-most cf lst))) (cons most (sort cf (delete lst most)))))) (define (find-most cf lst) (insertl (lambda (c 1 c 2) (if (cf c 1 c 2)) lst (car lst))) • How much work is sort? • We measure work using orders of growth: How does work grow with problem size? 12 February 2003 CS 200 Spring 2003 3
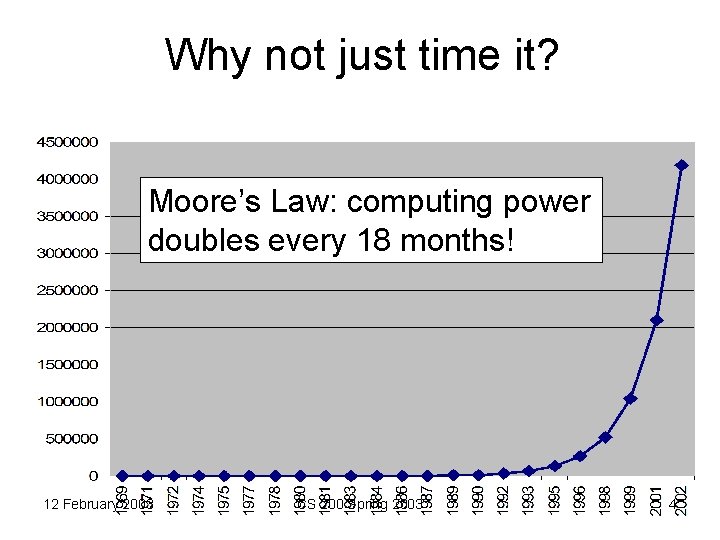
Why not just time it? Moore’s Law: computing power doubles every 18 months! 12 February 2003 CS 200 Spring 2003 4
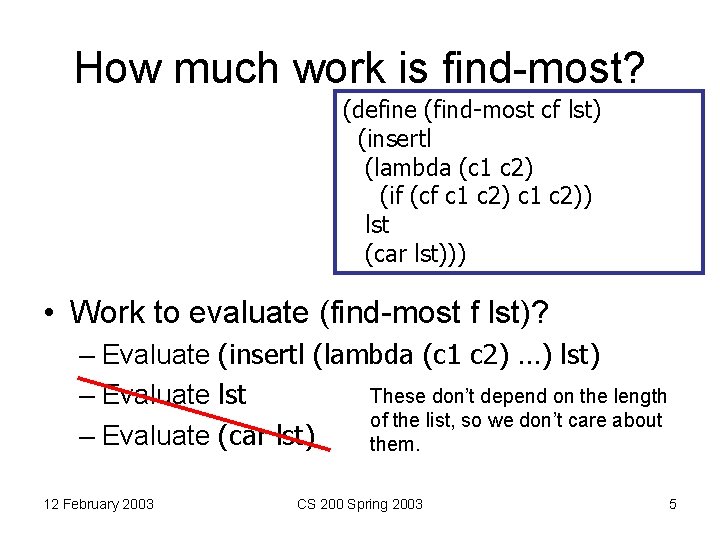
How much work is find-most? (define (find-most cf lst) (insertl (lambda (c 1 c 2) (if (cf c 1 c 2)) lst (car lst))) • Work to evaluate (find-most f lst)? – Evaluate (insertl (lambda (c 1 c 2) …) lst) These don’t depend on the length – Evaluate lst of the list, so we don’t care about – Evaluate (car lst) them. 12 February 2003 CS 200 Spring 2003 5
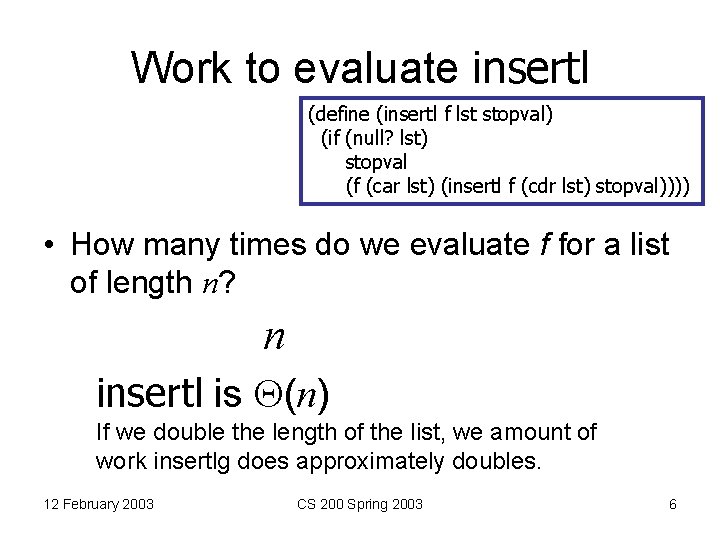
Work to evaluate insertl (define (insertl f lst stopval) (if (null? lst) stopval (f (car lst) (insertl f (cdr lst) stopval)))) • How many times do we evaluate f for a list of length n? n insertl is (n) If we double the length of the list, we amount of work insertlg does approximately doubles. 12 February 2003 CS 200 Spring 2003 6
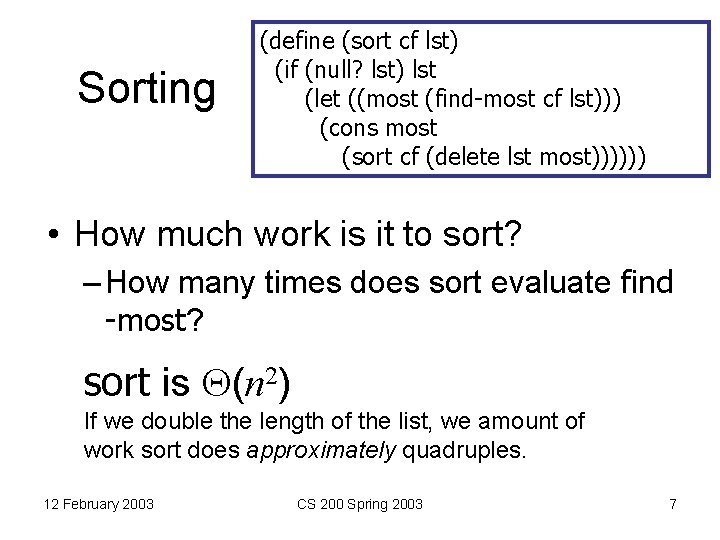
Sorting (define (sort cf lst) (if (null? lst) lst (let ((most (find-most cf lst))) (cons most (sort cf (delete lst most)))))) • How much work is it to sort? – How many times does sort evaluate find -most? sort is (n 2) If we double the length of the list, we amount of work sort does approximately quadruples. 12 February 2003 CS 200 Spring 2003 7
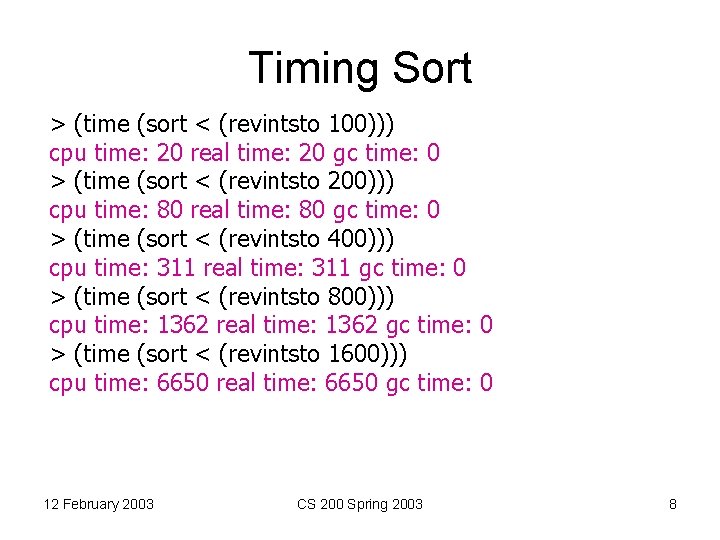
Timing Sort > (time (sort < (revintsto 100))) cpu time: 20 real time: 20 gc time: 0 > (time (sort < (revintsto 200))) cpu time: 80 real time: 80 gc time: 0 > (time (sort < (revintsto 400))) cpu time: 311 real time: 311 gc time: 0 > (time (sort < (revintsto 800))) cpu time: 1362 real time: 1362 gc time: 0 > (time (sort < (revintsto 1600))) cpu time: 6650 real time: 6650 gc time: 0 12 February 2003 CS 200 Spring 2003 8
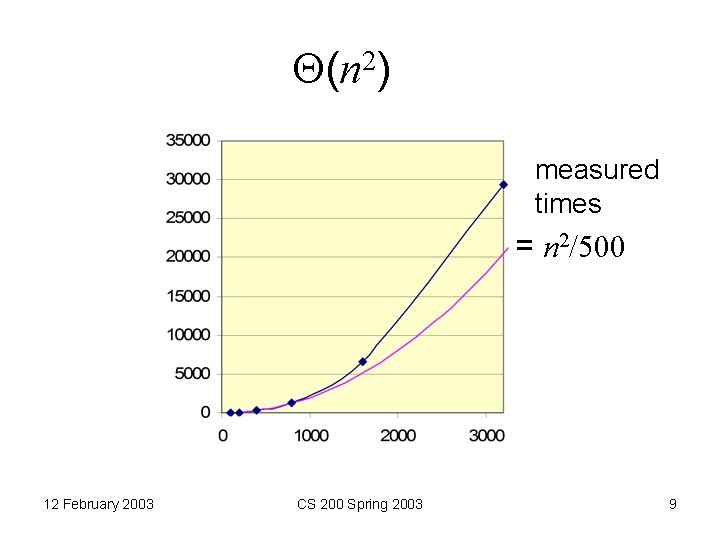
(n 2) measured times = n 2/500 12 February 2003 CS 200 Spring 2003 9
Is our sort good enough? Takes over 1 second to sort 1000 -length list. How long would it take to sort 1 million items? 1 s = time to sort 1000 4 s ~ time to sort 2000 1 M is 1000 * 1000 (n 2) Sorting time is n 2 so, sorting 1000 times as many items will take 10002 times as long = 1 million seconds ~ 11 days Note: there are 800 Million VISA cards in circulation. It would take 20, 000 years to process a VISA transaction at this rate. 12 February 2003 CS 200 Spring 2003 10
Divide and Conquer sorting? • Bubble sort: find the lowest in the list, add it to the front of the result of sorting the list after deleting the lowest • Insertion sort: insert the first element of the list in the right place in the sorted rest of the list 12 February 2003 CS 200 Spring 2003 11

insertsort (define (insertsort cf lst) (if (null? lst) null (insertel cf (car lst) (insertsort cf (cdr lst))))) 12 February 2003 CS 200 Spring 2003 12
insertel (define (insertel cf el lst) (if (null? lst) (list el) (if (cf el (car lst)) (cons el lst) (cons (car lst) (insertel cf el (cdr lst)))))) 12 February 2003 CS 200 Spring 2003 13
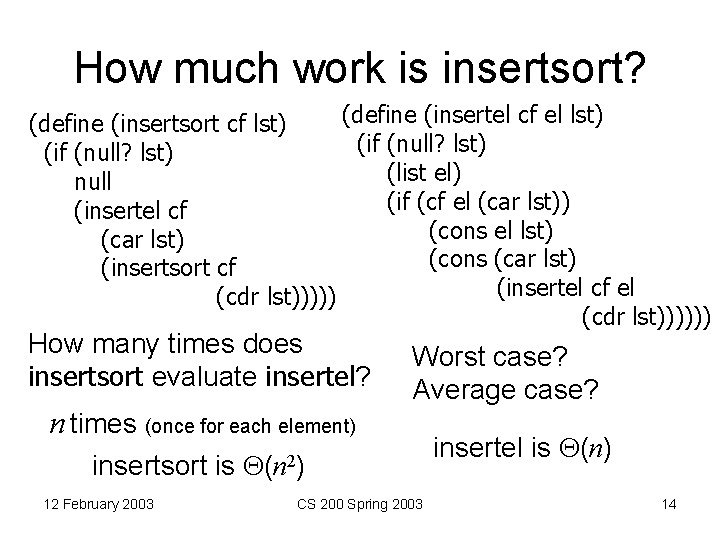
How much work is insertsort? (define (insertel cf el lst) (define (insertsort cf lst) (if (null? lst) (list el) null (if (cf el (car lst)) (insertel cf (cons el lst) (car lst) (cons (car lst) (insertsort cf (insertel cf el (cdr lst)))))) How many times does insertsort evaluate insertel? n times (once for each element) insertsort is 12 February 2003 Worst case? Average case? (n 2) CS 200 Spring 2003 insertel is (n) 14
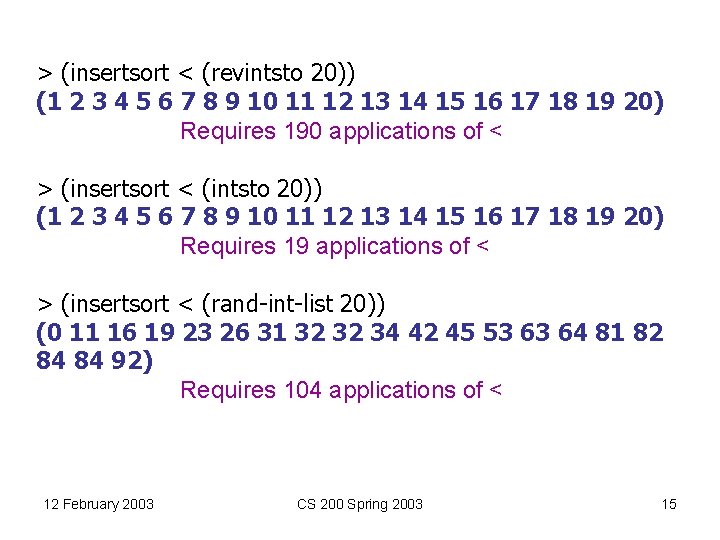
> (insertsort < (revintsto 20)) (1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20) Requires 190 applications of < > (insertsort < (intsto 20)) (1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20) Requires 19 applications of < > (insertsort < (rand-int-list 20)) (0 11 16 19 23 26 31 32 32 34 42 45 53 63 64 81 82 84 84 92) Requires 104 applications of < 12 February 2003 CS 200 Spring 2003 15
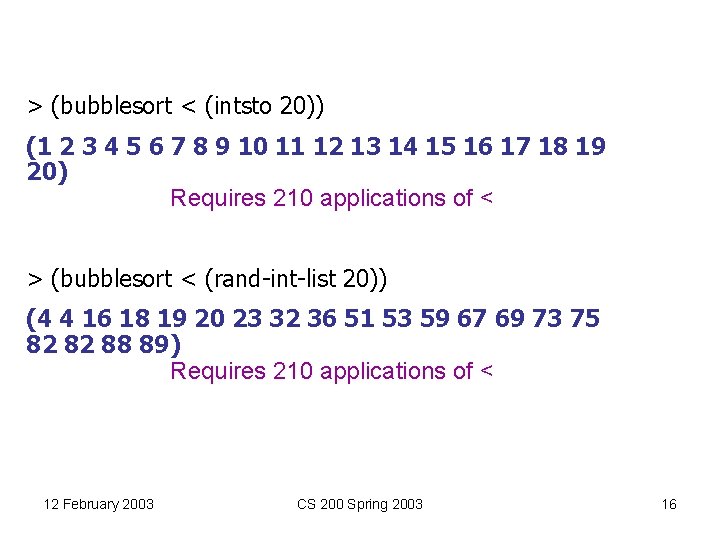
> (bubblesort < (intsto 20)) (1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20) Requires 210 applications of < > (bubblesort < (rand-int-list 20)) (4 4 16 18 19 20 23 32 36 51 53 59 67 69 73 75 82 82 88 89) Requires 210 applications of < 12 February 2003 CS 200 Spring 2003 16
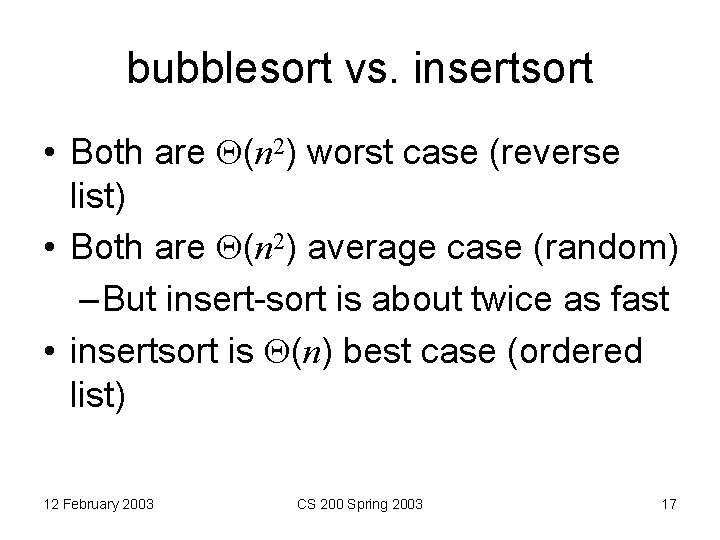
bubblesort vs. insertsort • Both are (n 2) worst case (reverse list) • Both are (n 2) average case (random) – But insert-sort is about twice as fast • insertsort is (n) best case (ordered list) 12 February 2003 CS 200 Spring 2003 17
Can we do better? • Think about this for next time • Hint: think about the trees in SICP 2. 2 12 February 2003 CS 200 Spring 2003 18
Cryptology (CS 588 Condensed) 12 February 2003 CS 200 Spring 2003 19
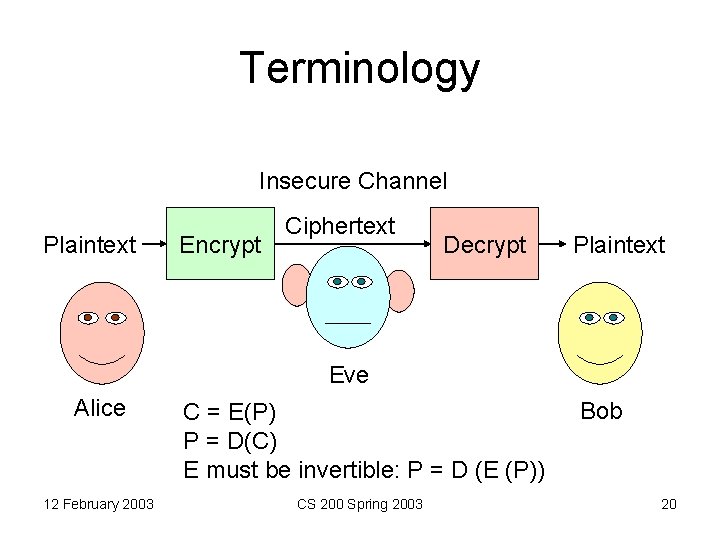
Terminology Insecure Channel Plaintext Encrypt Ciphertext Decrypt Plaintext Eve Alice 12 February 2003 C = E(P) P = D(C) E must be invertible: P = D (E (P)) CS 200 Spring 2003 Bob 20
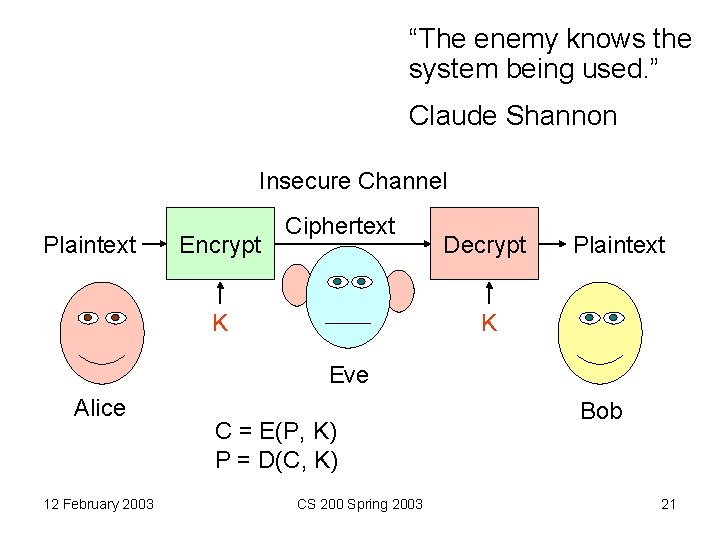
“The enemy knows the system being used. ” Claude Shannon Insecure Channel Plaintext Encrypt Ciphertext K Decrypt Plaintext K Eve Alice 12 February 2003 C = E(P, K) P = D(C, K) CS 200 Spring 2003 Bob 21
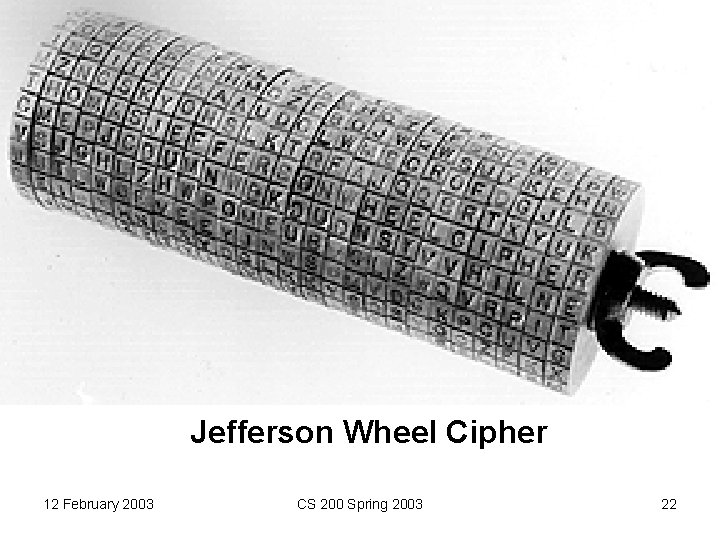
Jefferson Wheel Cipher 12 February 2003 CS 200 Spring 2003 22
Enigma • About 50, 000 used by Nazi’s in WWII • Modified throughout WWII, believed to be perfectly secure • Broken by Bletchley Park led by Alan Turing (and 30, 000 others) • First computer (Collossus) developed to break Nazi codes (but kept secret through 1970 s) • Allies used decrypted Enigma messages to plan D-Day 12 February 2003 CS 200 Spring 2003 23
Bletchley Park 12 February 2003 CS 200 Spring 2003 24
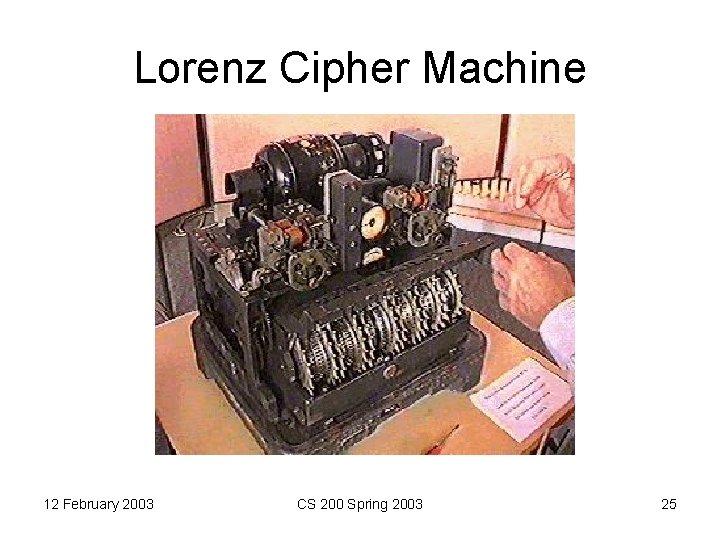
Lorenz Cipher Machine 12 February 2003 CS 200 Spring 2003 25
![Perfectly Secure Cipher: One-Time Pad • Mauborgne/Vernam [1917] • xor ( ): 0 0=0 Perfectly Secure Cipher: One-Time Pad • Mauborgne/Vernam [1917] • xor ( ): 0 0=0](http://slidetodoc.com/presentation_image/9ddac8e9fd2139f3c78f27bef730d200/image-26.jpg)
Perfectly Secure Cipher: One-Time Pad • Mauborgne/Vernam [1917] • xor ( ): 0 0=0 1 0=1 0 1=1 1 1=0 a a=0 a 0=a a b b=a • E(P, K) = P K D(C, K) = C K = (P K) K = P 12 February 2003 CS 200 Spring 2003 26
Why perfectly secure? For any given ciphertext, all plaintexts are equally possible. Ciphertext: Key: Plaintext: 12 February 2003 0100111110101 1 1100000100110 B 1000111010011 = “CS” 0 CS 200 Spring 2003 27
If its “perfect” why is it broken? • Cannot reuse K • Need to generate truly random bit sequence as long as all messages • Need to securely distribute key 12 February 2003 CS 200 Spring 2003 28
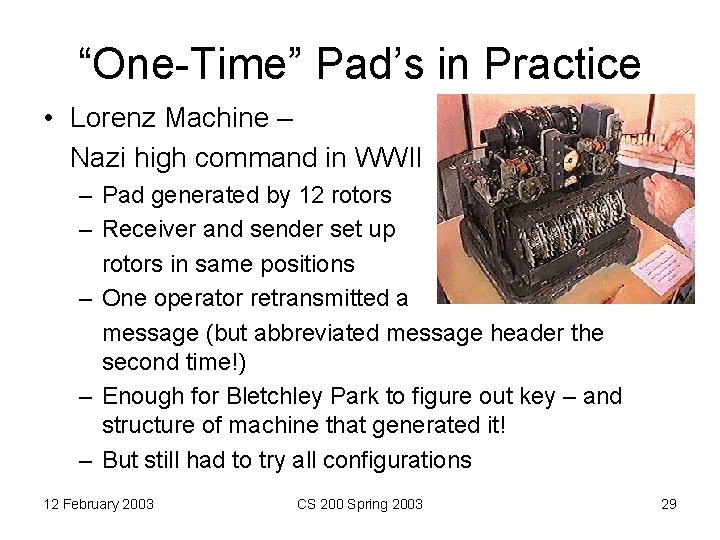
“One-Time” Pad’s in Practice • Lorenz Machine – Nazi high command in WWII – Pad generated by 12 rotors – Receiver and sender set up rotors in same positions – One operator retransmitted a message (but abbreviated message header the second time!) – Enough for Bletchley Park to figure out key – and structure of machine that generated it! – But still had to try all configurations 12 February 2003 CS 200 Spring 2003 29
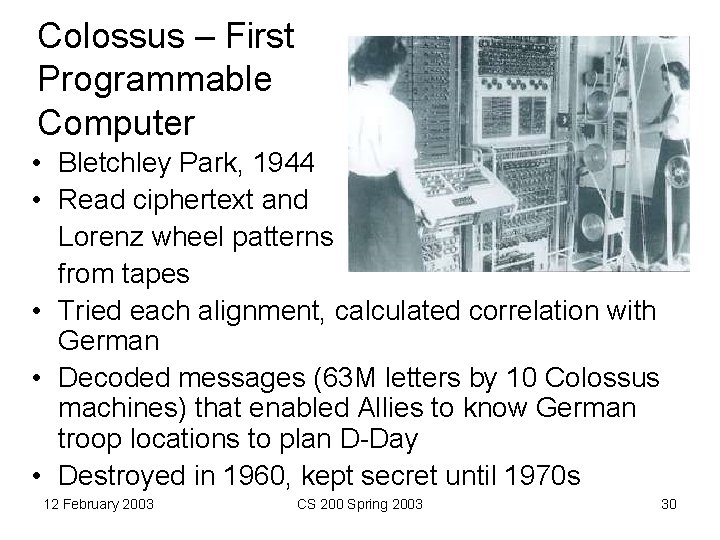
Colossus – First Programmable Computer • Bletchley Park, 1944 • Read ciphertext and Lorenz wheel patterns from tapes • Tried each alignment, calculated correlation with German • Decoded messages (63 M letters by 10 Colossus machines) that enabled Allies to know German troop locations to plan D-Day • Destroyed in 1960, kept secret until 1970 s 12 February 2003 CS 200 Spring 2003 30
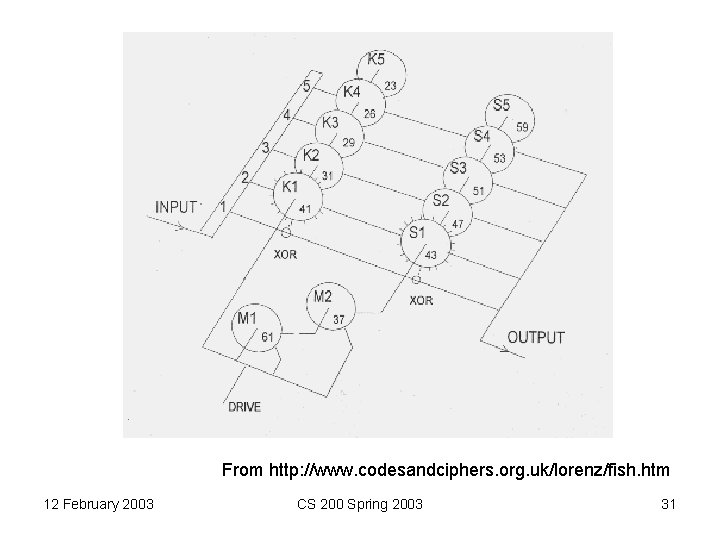
From http: //www. codesandciphers. org. uk/lorenz/fish. htm 12 February 2003 CS 200 Spring 2003 31
Problem Set 4 • Break a simplified Lorenz Cipher • Removed one wheel, made initial positions of all groups of wheels have to match • Small rotors • Its REALLY AMAZING that the British were able to break the real Lorenz in 1943 and it is still hard for us today! 12 February 2003 CS 200 Spring 2003 32
Motivation Helps… Confronted with the prospect of defeat, the Allied cryptanalysts had worked night and day to penetrate German ciphers. It would appear that fear was the main driving force, and that adversity is one of the foundations of successful codebreaking. Simon Singh, The Code Book 12 February 2003 CS 200 Spring 2003 33
Modern Ciphers • 128 -bit keys, encrypt 128 -bit blocks • Brute force attack – Try 1 Trillion keys per second – Would take 10790283070806000000 years to try all keys! – If that’s not enough, can use 256 -bit key • No known techniques that do better than brute force search 12 February 2003 CS 200 Spring 2003 34
Charge • PS 4: Cryptology – No new Computer Science concepts – Lots of practice with lists and recursion • Think about faster ways of sorting • Read Tyson’s essay (before Friday) – How does it relate to (n 2) – How does it relate to grade inflation – Don’t misinterpret it as telling you to run out and get tatoos and piercings! 12 February 2003 CS 200 Spring 2003 35
- Slides: 35