Lecture 1 Introduction to Cryptography Lecturer Meysam Alishahi
- Slides: 76
Lecture 1 Introduction to Cryptography Lecturer: Meysam Alishahi Design By: Z. Faraji and H. Hajiabolhassan Modified by: F. Moazami 6/7/2021
References: 1. Johannes A. Buchmann, Introduction to Cryptography, First Edition, 2000. 2. D. R. Stinson, Cryptography: Theory and Practice, Third Edition, 2006. K 3. H. Delfs and H. Knebl, Introduction to Cryptography: Principles and Application, Second Edition, 2007. 6/7/2021
Plan 1. Introduction 2. Classical Cryptosystems 3. Cryptanalysis 6/7/2021
Caesar Shift Cipher 6/7/2021
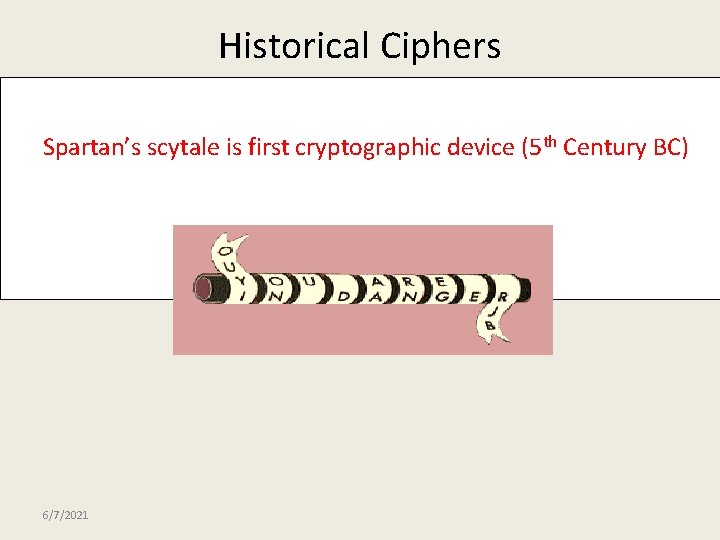
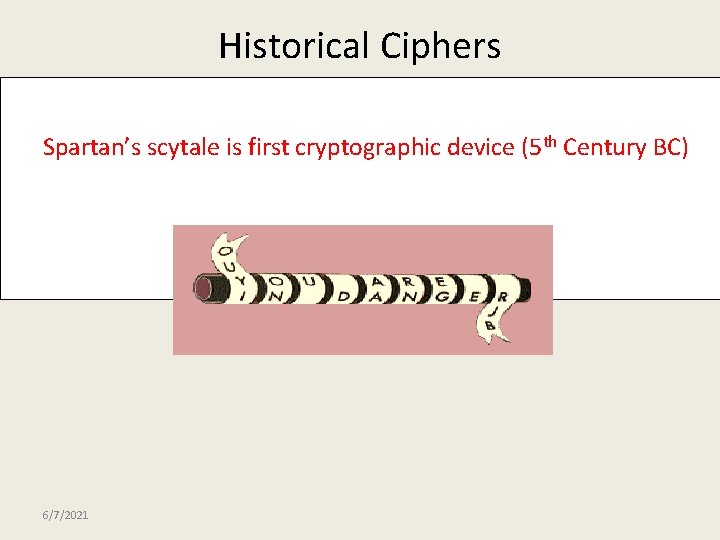
Historical Ciphers Spartan’s scytale is first cryptographic device (5 th Century BC) 6/7/2021
Jefferson Disk First invented by Thomas Jefferson in 1975. This cipher did not become well-known. The system was used by the United State Army from 1923 until 1942 as the M-94. Jefferson's device had 36 disks. 6/7/2021
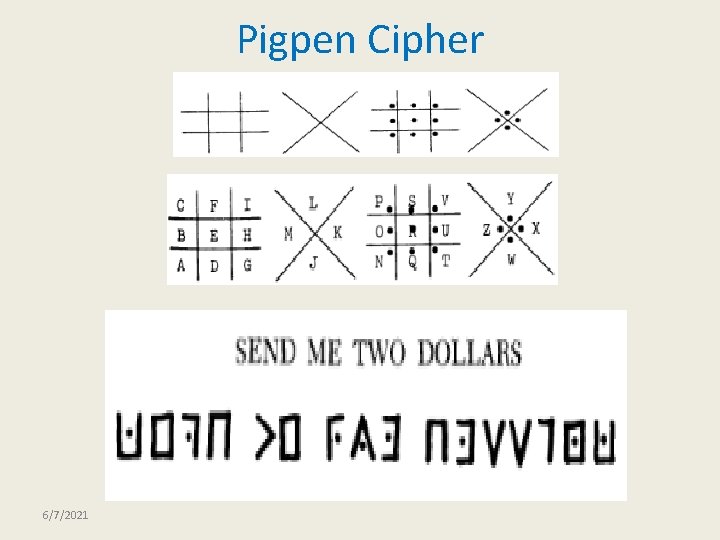
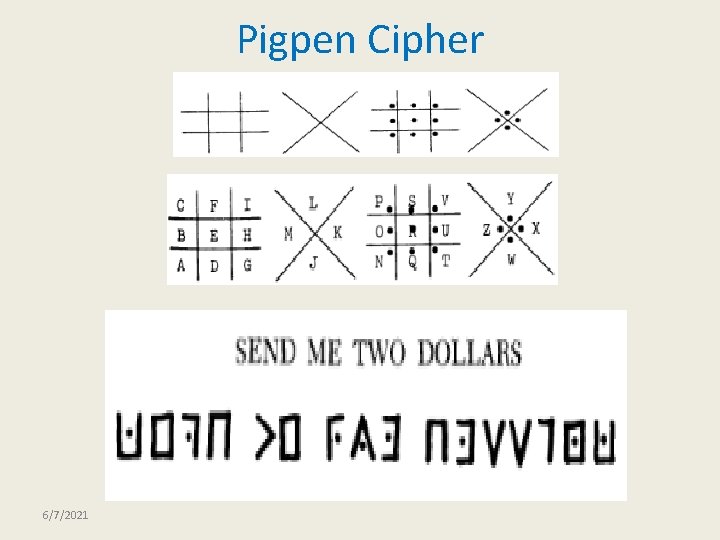
Pigpen Cipher 6/7/2021
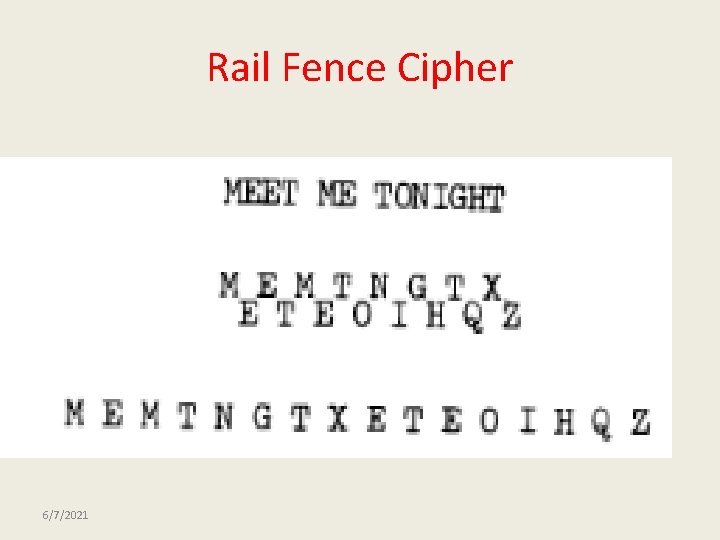
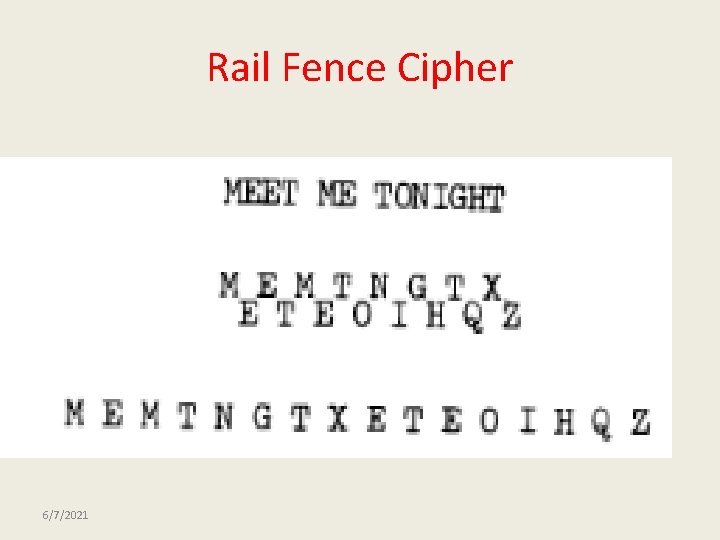
Rail Fence Cipher 6/7/2021
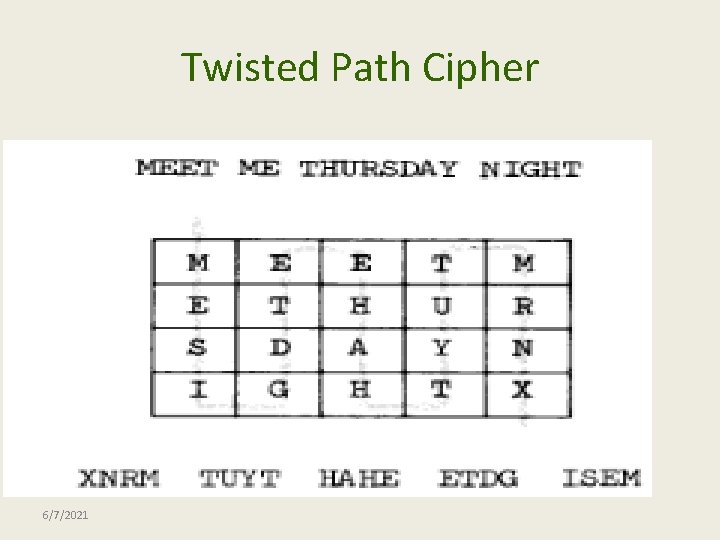
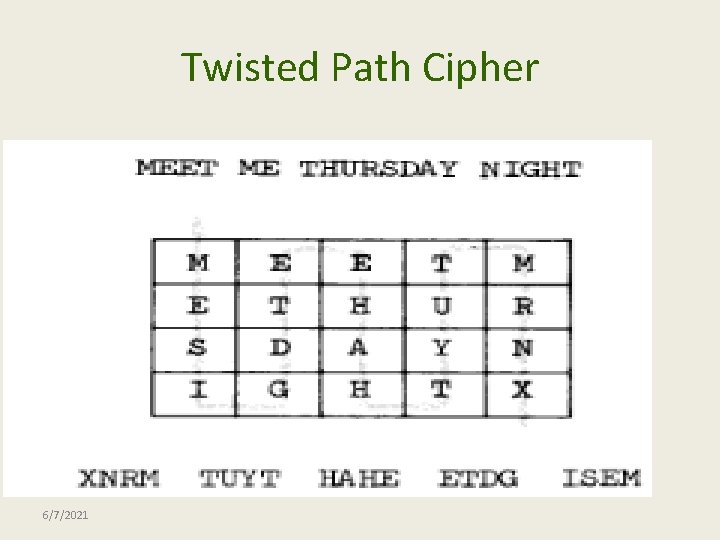
Twisted Path Cipher 6/7/2021
Cryptography In the past: the art of encrypting messages (mostly for the military applications). Now: the science of securing digital communication and transactions (encryption, authentication, digital signatures, e-cash, auctions, etc. . ) 6/7/2021
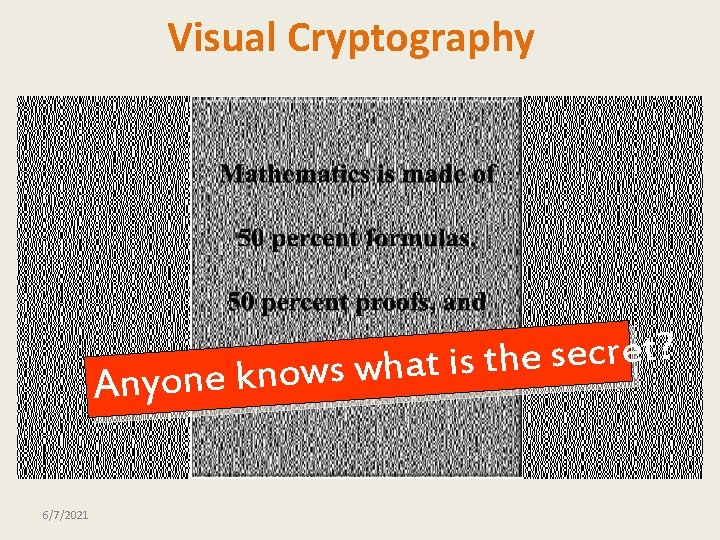
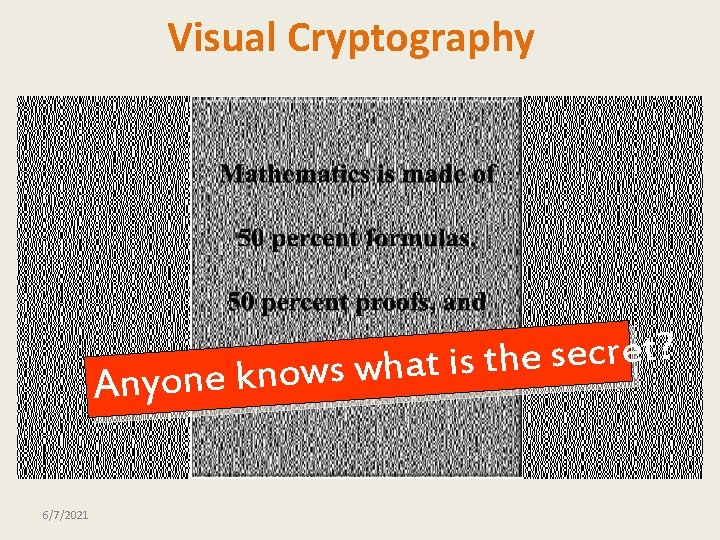
Visual Cryptography ? t e r c e s e h t s i t a h w s w o n k e Anyon 6/7/2021
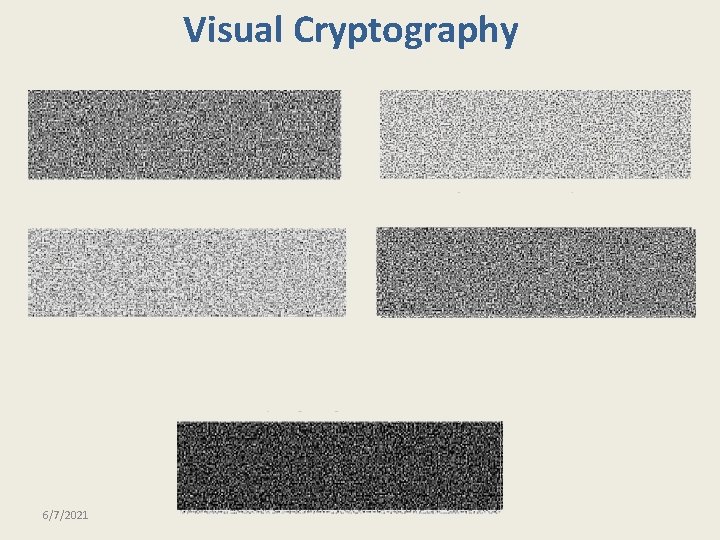
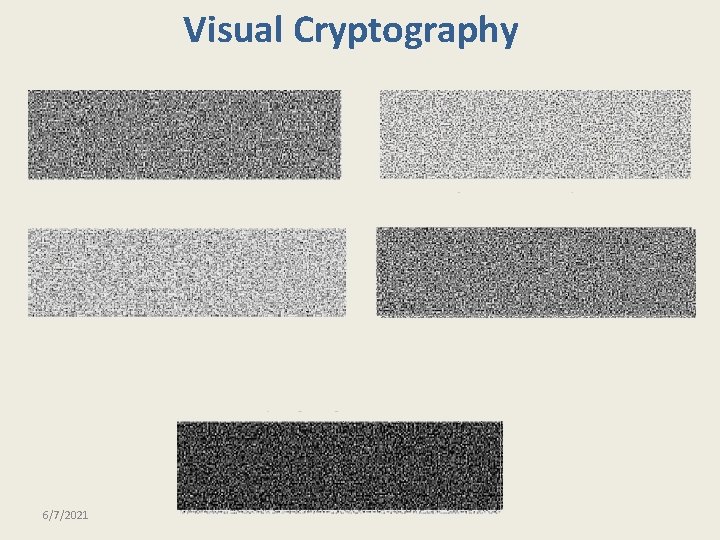
Visual Cryptography 6/7/2021
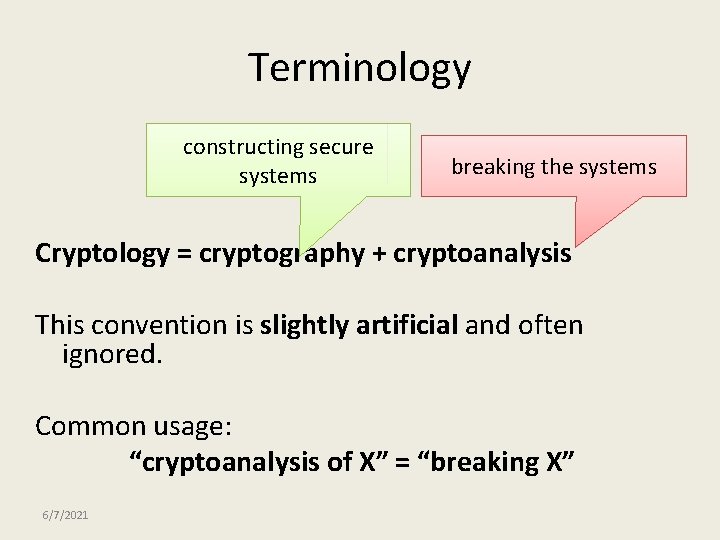
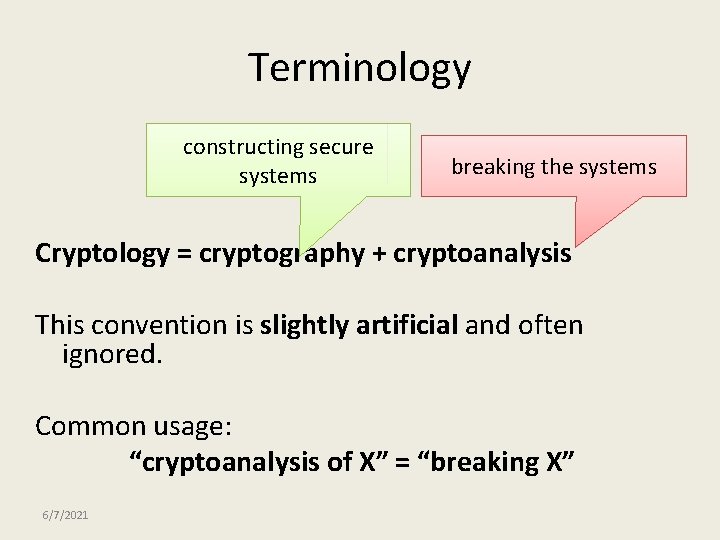
Terminology constructing secure systems breaking the systems Cryptology = cryptography + cryptoanalysis This convention is slightly artificial and often ignored. Common usage: “cryptoanalysis of X” = “breaking X” 6/7/2021
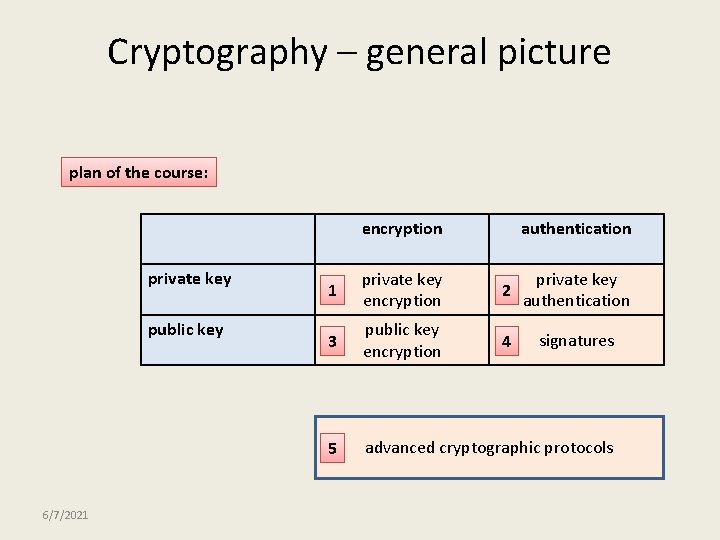
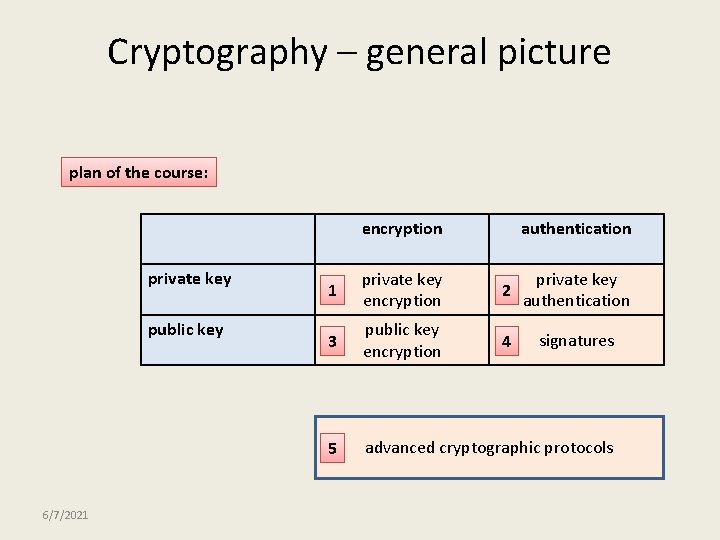
Cryptography – general picture plan of the course: encryption private key public key 6/7/2021 authentication 1 private key encryption 2 private key authentication 3 public key encryption 4 signatures 5 advanced cryptographic protocols
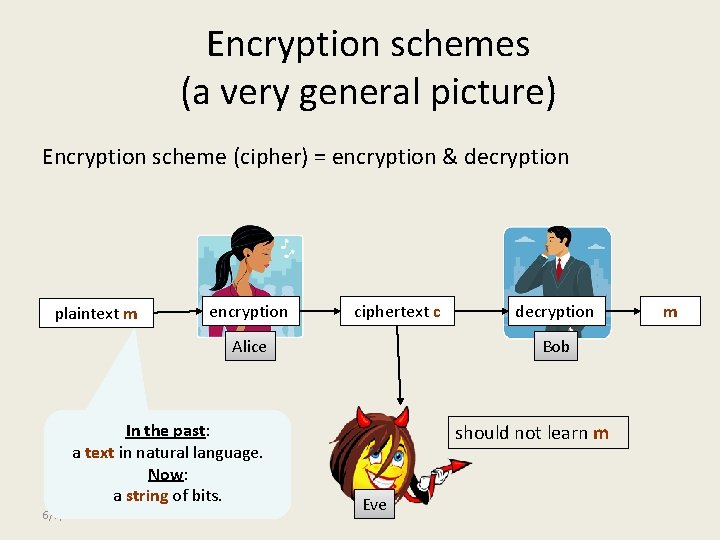
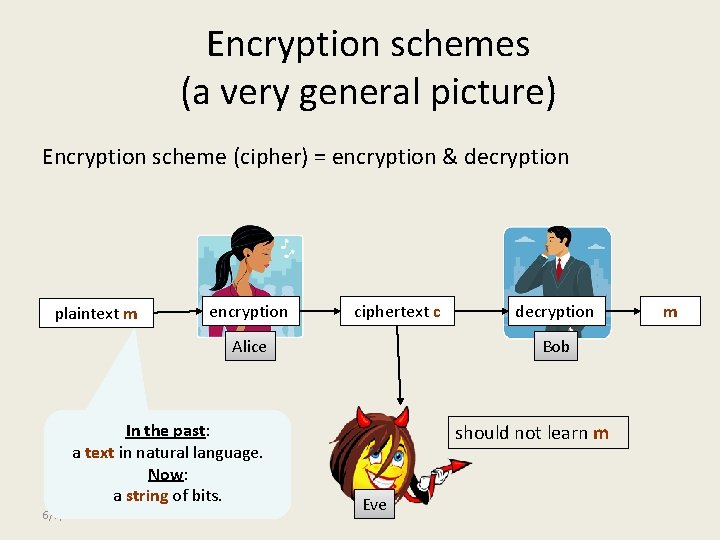
Encryption schemes (a very general picture) Encryption scheme (cipher) = encryption & decryption plaintext m encryption ciphertext c Alice In the past: a text in natural language. Now: a string of bits. 6/7/2021 decryption Bob should not learn m Eve m
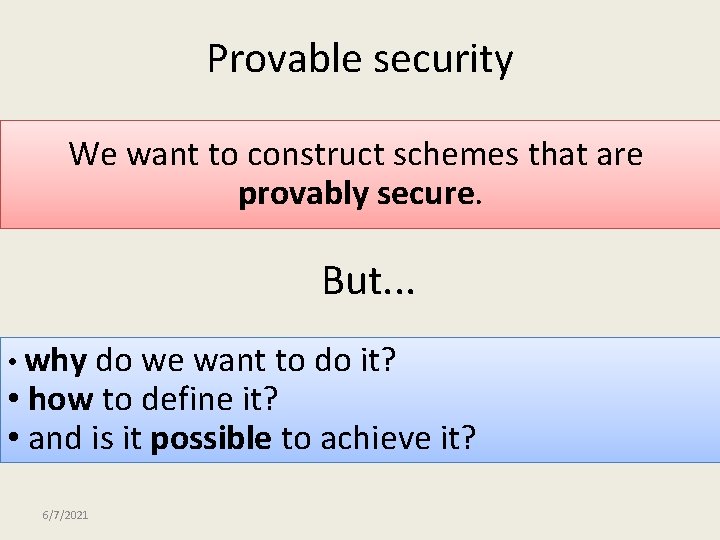
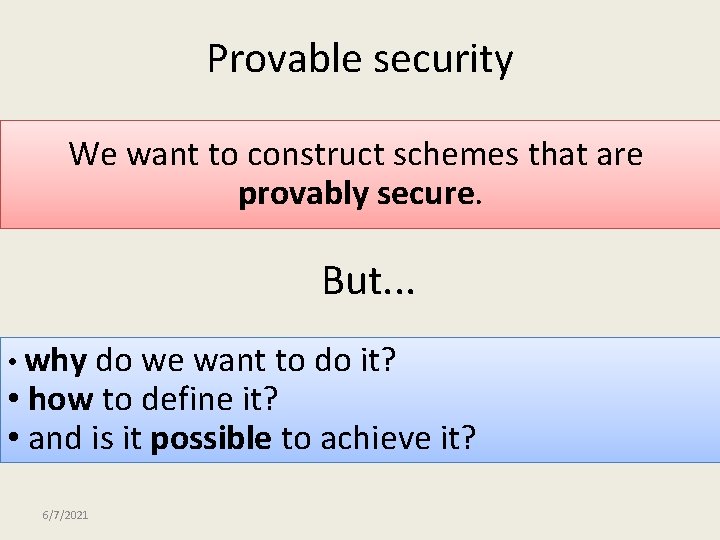
Provable security We want to construct schemes that are provably secure. But. . . • why do we want to do it? • how to define it? • and is it possible to achieve it? 6/7/2021
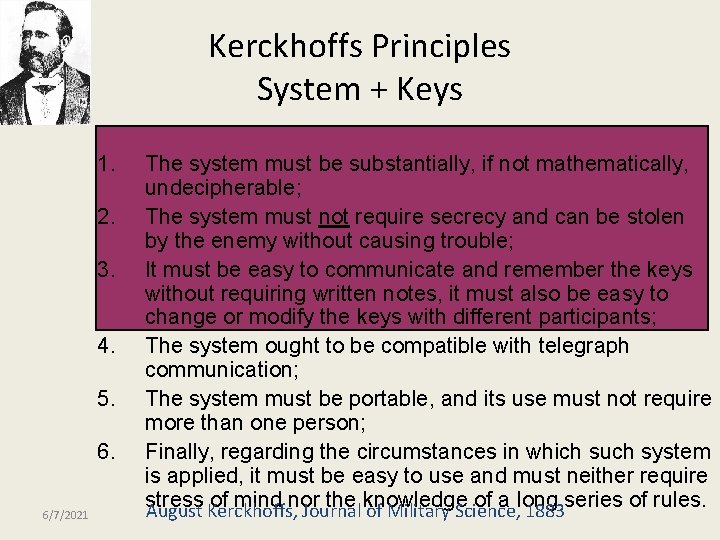
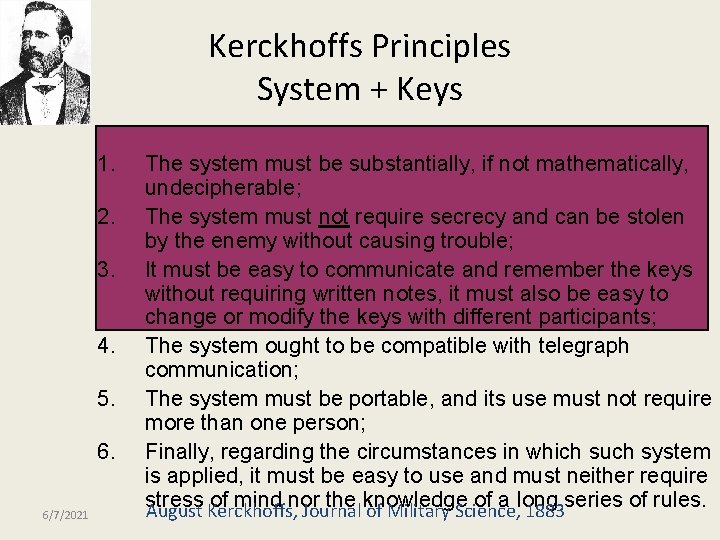
Kerckhoffs Principles System + Keys 1. 2. 3. 4. 5. 6. 6/7/2021 The system must be substantially, if not mathematically, undecipherable; The system must not require secrecy and can be stolen by the enemy without causing trouble; It must be easy to communicate and remember the keys without requiring written notes, it must also be easy to change or modify the keys with different participants; The system ought to be compatible with telegraph communication; The system must be portable, and its use must not require more than one person; Finally, regarding the circumstances in which such system is applied, it must be easy to use and must neither require stress of mind nor the knowledge of a long August Kerckhoffs, Journal of Military Science, 1883 series of rules.
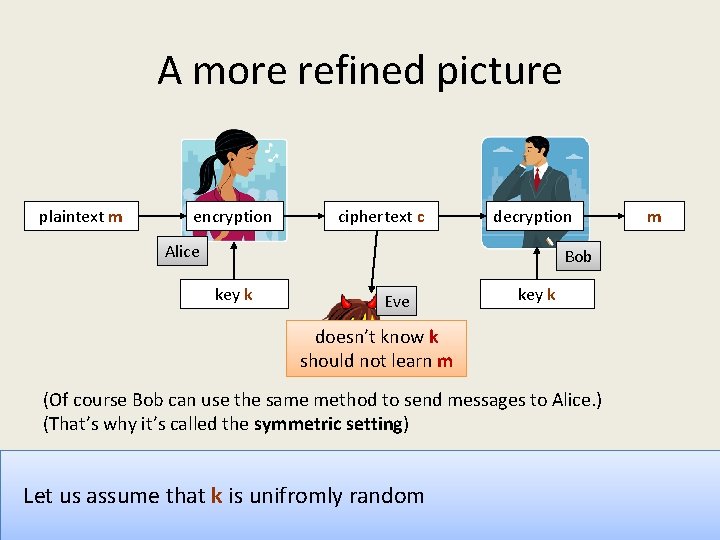
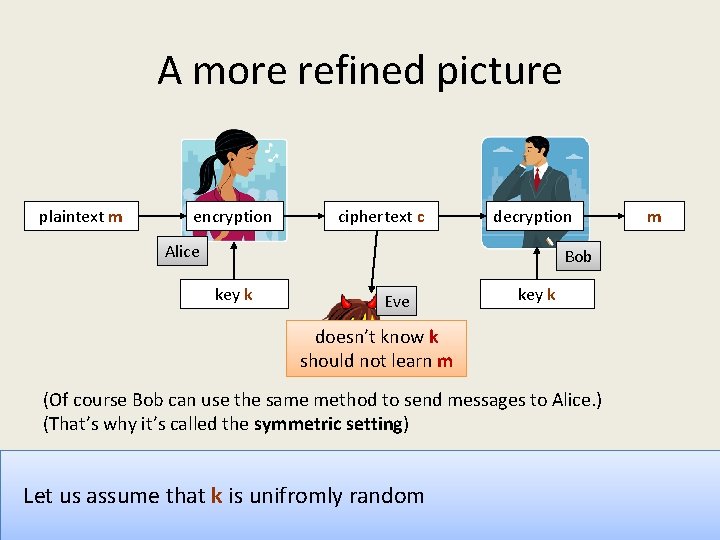
A more refined picture plaintext m encryption ciphertext c decryption Alice Bob key k Eve key k doesn’t know k should not learn m (Of course Bob can use the same method to send messages to Alice. ) (That’s why it’s called the symmetric setting) Let us assume that k is unifromly random 6/7/2021 m
Symmetric Cryptosystems Locking and unlocking with the same key 6/7/2021
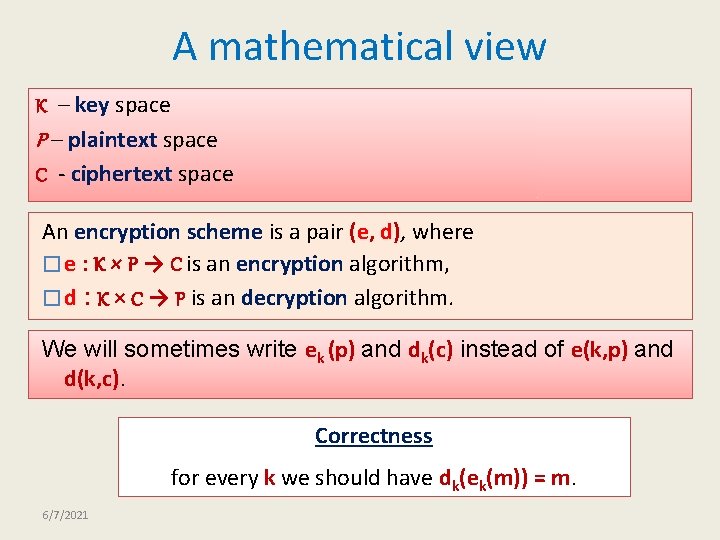
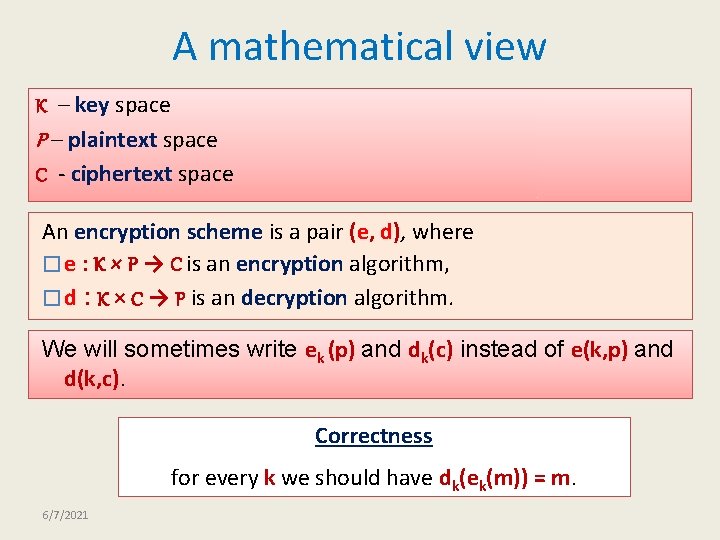
A mathematical view K – key space P – plaintext space C - ciphertext space An encryption scheme is a pair (e, d), where � e : K × P → C is an encryption algorithm, � d : K × C → P is an decryption algorithm. We will sometimes write ek (p) and dk(c) instead of e(k, p) and d(k, c). Correctness for every k we should have dk(ek(m)) = m. 6/7/2021
Plan 1. Introduction 2. Classical Cryptosystems 3. Cryptanalysis 6/7/2021
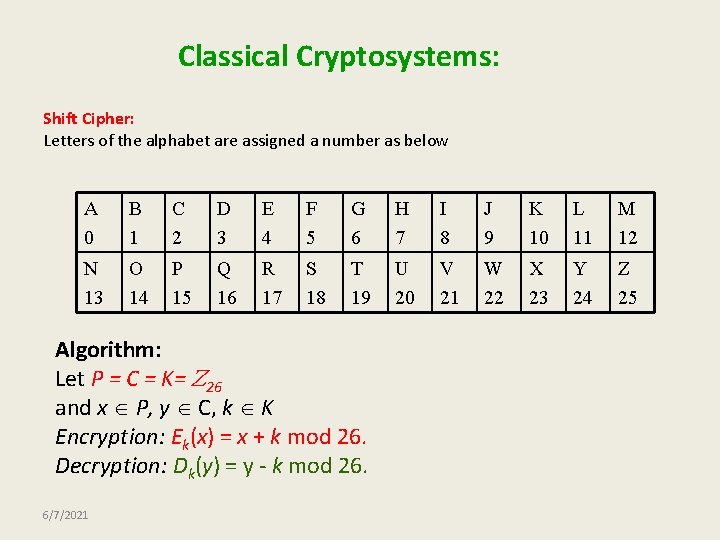
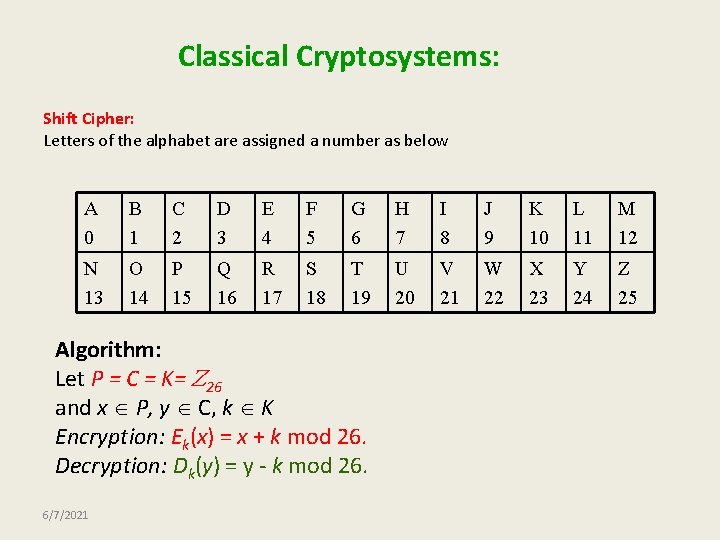
Classical Cryptosystems: Shift Cipher: Letters of the alphabet are assigned a number as below A 0 B 1 C 2 D 3 E 4 F 5 G 6 H 7 I 8 J 9 K 10 L 11 M 12 N 13 O 14 P 15 Q 16 R 17 S 18 T 19 U 20 V 21 W 22 X 23 Y 24 Z 25 Algorithm: Let P = C = K= 26 and x P, y C, k K Encryption: Ek(x) = x + k mod 26. Decryption: Dk(y) = y - k mod 26. 6/7/2021
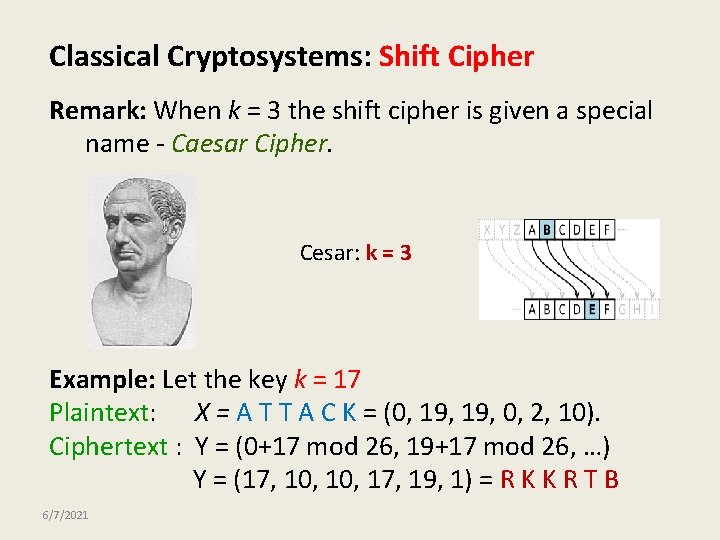
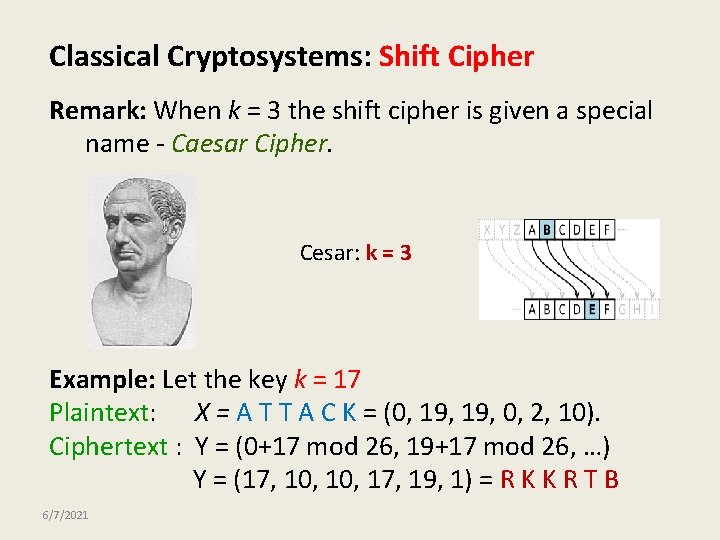
Classical Cryptosystems: Shift Cipher Remark: When k = 3 the shift cipher is given a special name - Caesar Cipher. Cesar: k = 3 Example: Let the key k = 17 Plaintext: X = A T T A C K = (0, 19, 0, 2, 10). Ciphertext : Y = (0+17 mod 26, 19+17 mod 26, …) Y = (17, 10, 17, 19, 1) = R K K R T B 6/7/2021
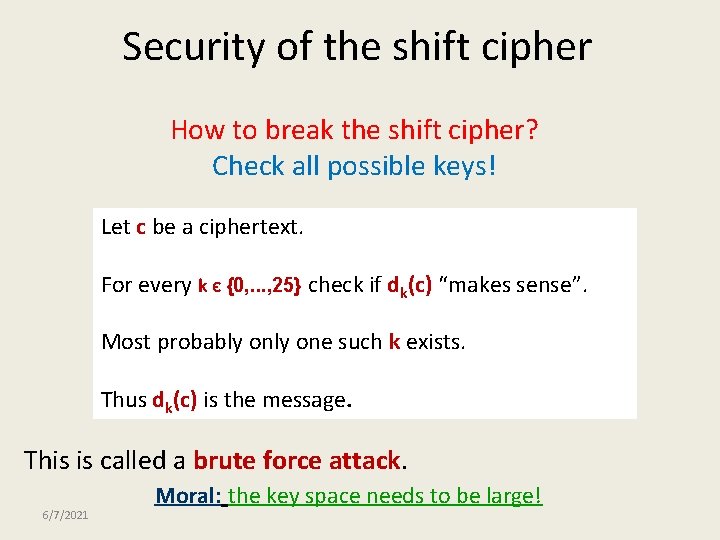
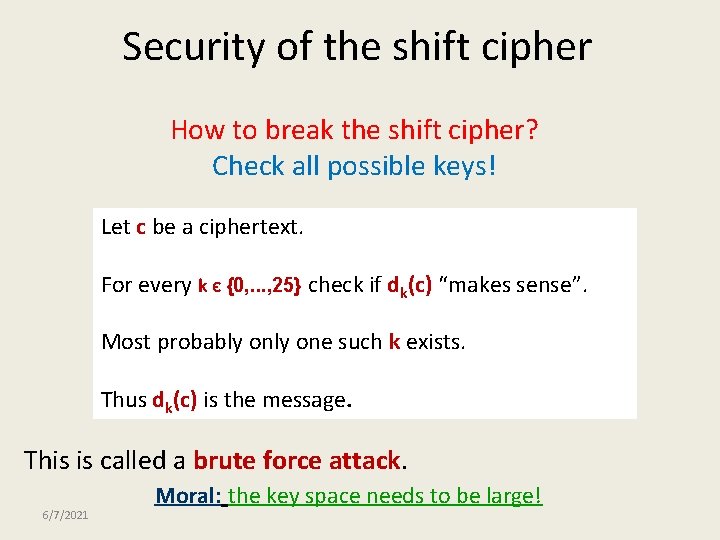
Security of the shift cipher How to break the shift cipher? Check all possible keys! Let c be a ciphertext. For every k Є {0, . . . , 25} check if dk(c) “makes sense”. Most probably one such k exists. Thus dk(c) is the message. This is called a brute force attack. 6/7/2021 Moral: the key space needs to be large!
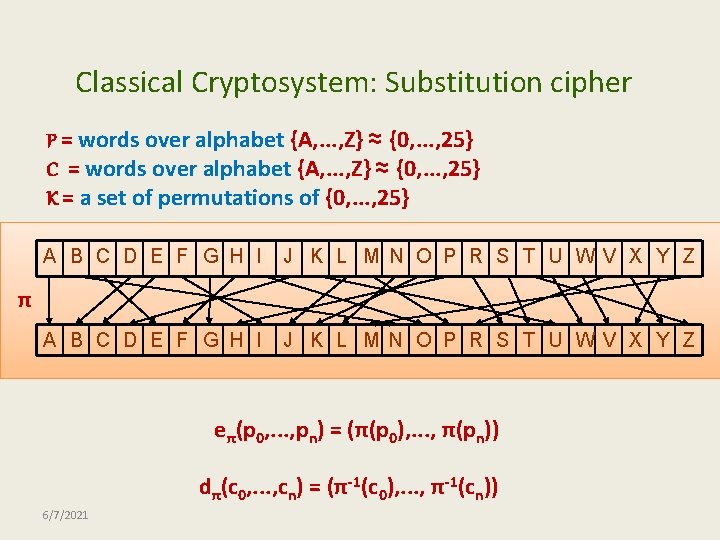
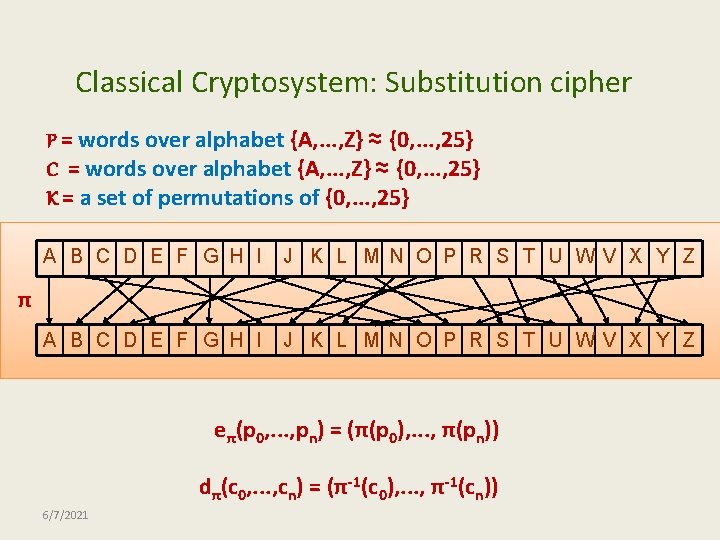
Classical Cryptosystem: Substitution cipher P = words over alphabet {A, . . . , Z} ≈ {0, . . . , 25} C = words over alphabet {A, . . . , Z} ≈ {0, . . . , 25} K = a set of permutations of {0, . . . , 25} A B C D E F G H I J K L M N O P R S T U WV X Y Z π eπ(p 0, . . . , pn) = (π(p 0), . . . , π(pn)) dπ(c 0, . . . , cn) = (π-1(c 0), . . . , π-1(cn)) 6/7/2021
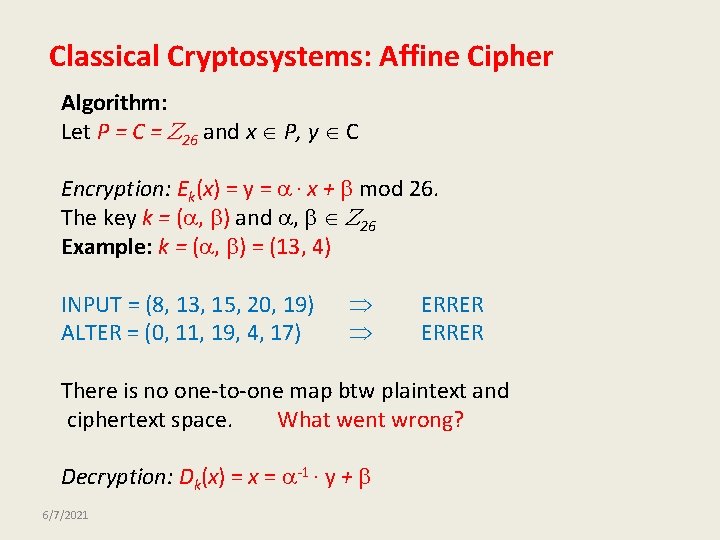
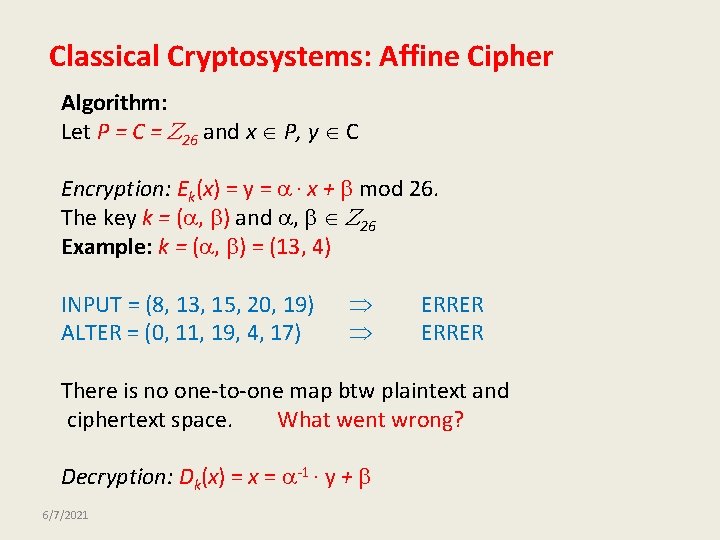
Classical Cryptosystems: Affine Cipher Algorithm: Let P = C = 26 and x P, y C Encryption: Ek(x) = y = · x + mod 26. The key k = ( , ) and , 26 Example: k = ( , ) = (13, 4) INPUT = (8, 13, 15, 20, 19) ALTER = (0, 11, 19, 4, 17) ERRER There is no one-to-one map btw plaintext and ciphertext space. What went wrong? Decryption: Dk(x) = x = -1 · y + 6/7/2021
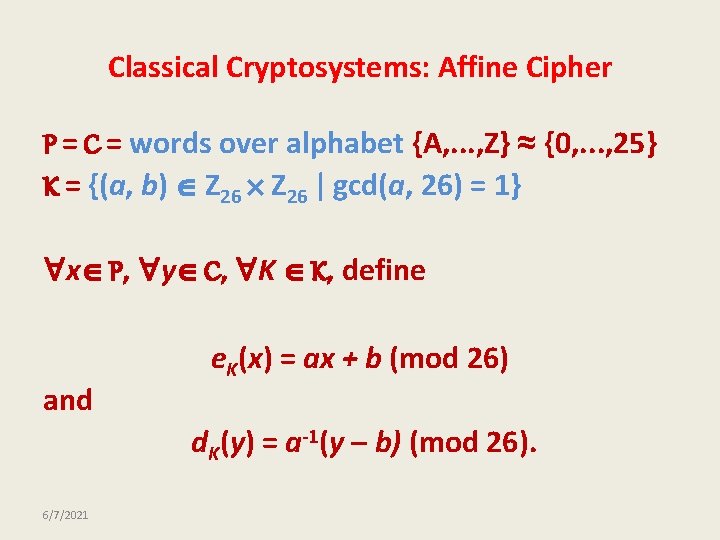
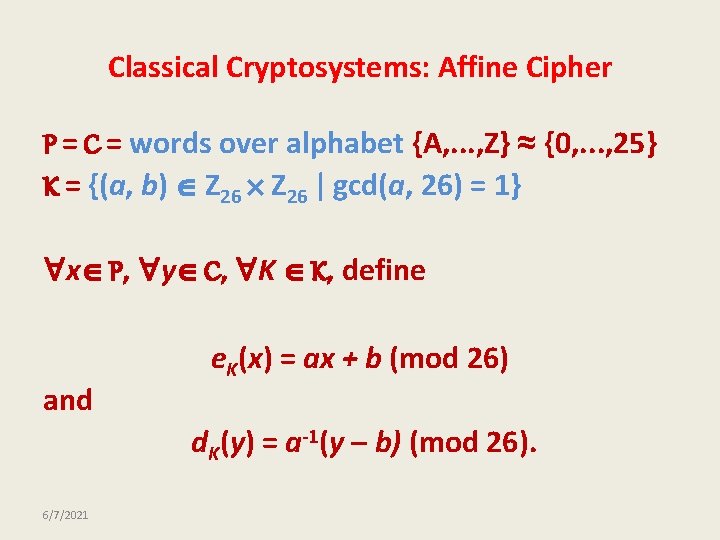
Classical Cryptosystems: Affine Cipher P = C = words over alphabet {A, . . . , Z} ≈ {0, . . . , 25} K = {(a, b) Z 26 | gcd(a, 26) = 1} x P, y C, K K, define and e. K(x) = ax + b (mod 26) d. K(y) = a-1(y – b) (mod 26). 6/7/2021
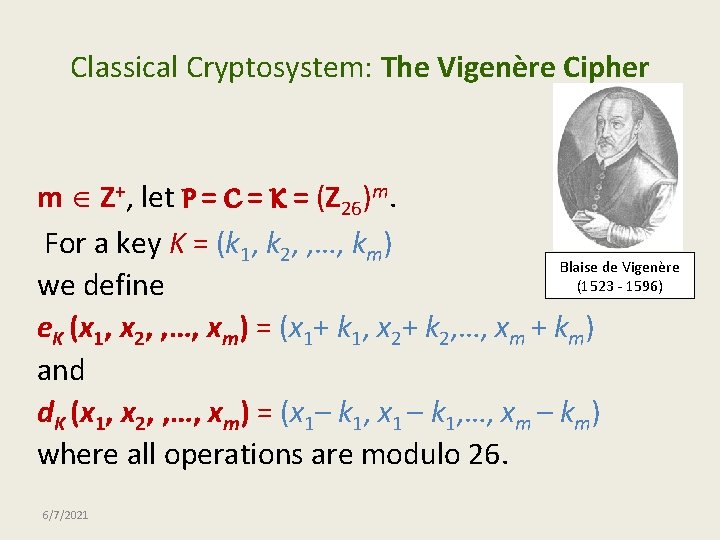
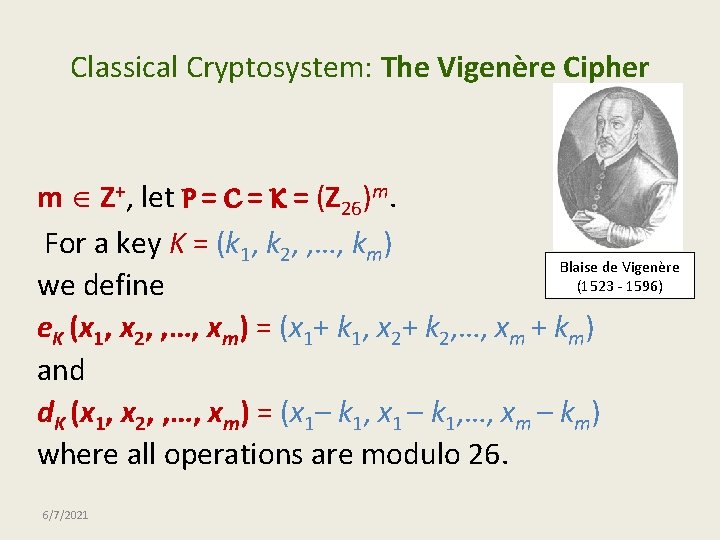
Classical Cryptosystem: The Vigenère Cipher m Z+, let P = C = K = (Z 26)m. For a key K = (k 1, k 2, , …, km) Blaise de Vigenère (1523 - 1596) we define e. K (x 1, x 2, , …, xm) = (x 1+ k 1, x 2+ k 2, …, xm + km) and d. K (x 1, x 2, , …, xm) = (x 1– k 1, x 1 – k 1, …, xm – km) where all operations are modulo 26. 6/7/2021
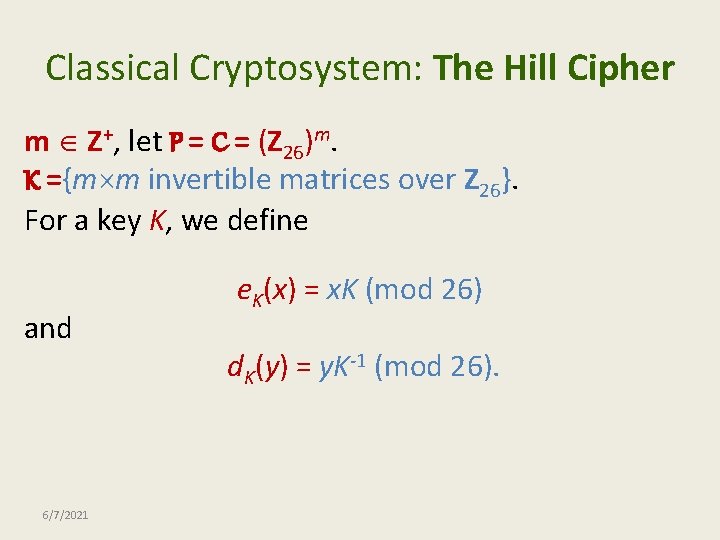
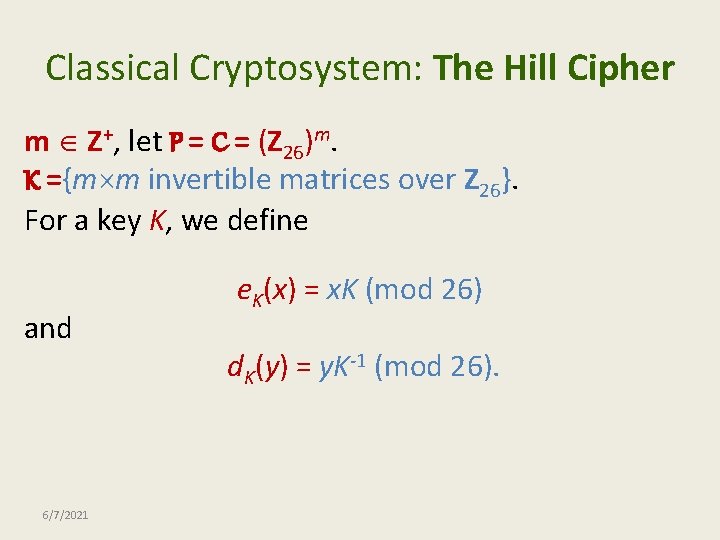
Classical Cryptosystem: The Hill Cipher m Z+, let P = C = (Z 26)m. K ={m m invertible matrices over Z 26}. For a key K, we define and 6/7/2021 e. K(x) = x. K (mod 26) d. K(y) = y. K-1 (mod 26).
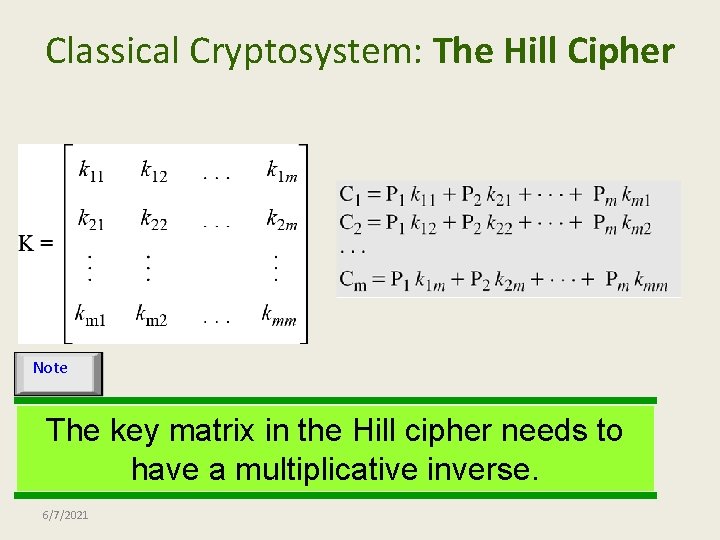
Classical Cryptosystem: The Hill Cipher Note The key matrix in the Hill cipher needs to have a multiplicative inverse. 6/7/2021
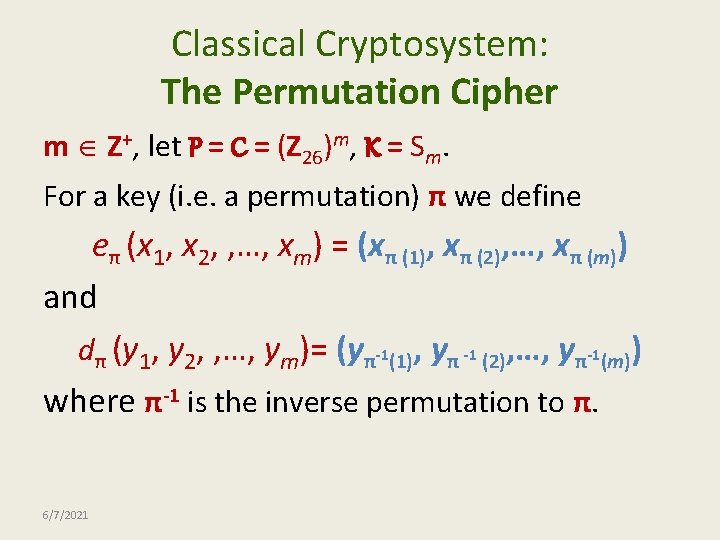
Classical Cryptosystem: The Permutation Cipher m Z+, let P = C = (Z 26)m, K = Sm. For a key (i. e. a permutation) π we define eπ (x 1, x 2, , …, xm) = (xπ (1), xπ (2), …, xπ (m)) and dπ (y 1, y 2, , …, ym)= (yπ-1(1), yπ -1 (2), …, yπ-1(m)) where π-1 is the inverse permutation to π. 6/7/2021
Plan 1. Introduction 2. Classical Cryptosystems 3. Cryptanalysis 6/7/2021
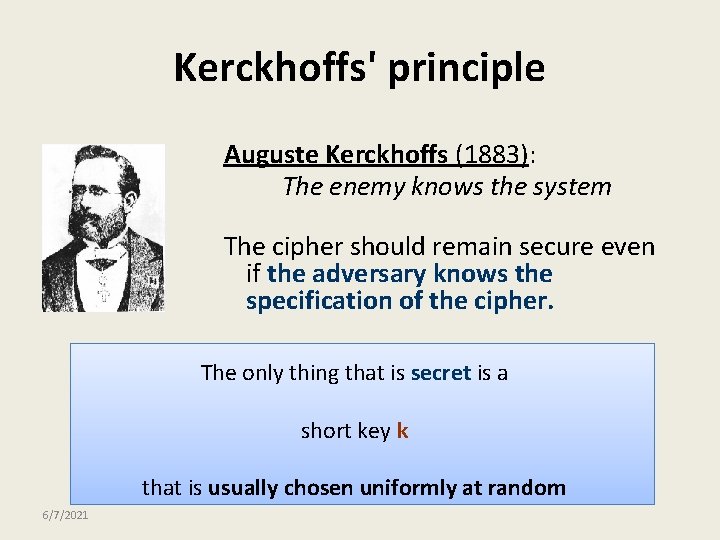
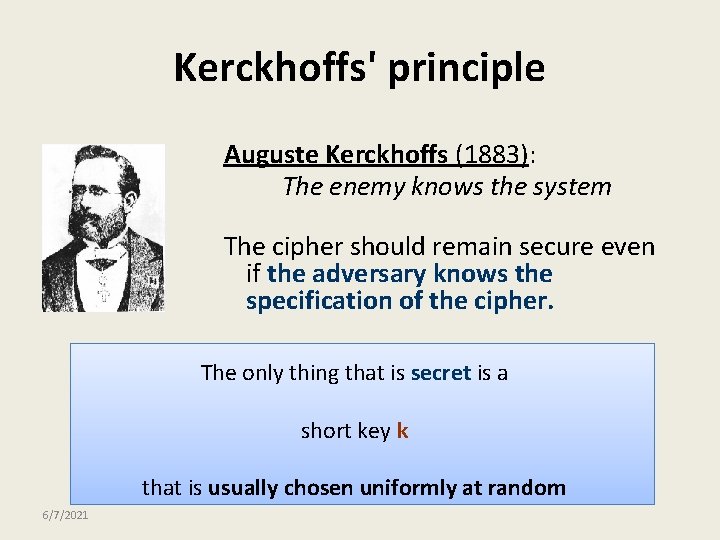
Kerckhoffs' principle Auguste Kerckhoffs (1883): The enemy knows the system The cipher should remain secure even if the adversary knows the specification of the cipher. The only thing that is secret is a short key k that is usually chosen uniformly at random 6/7/2021
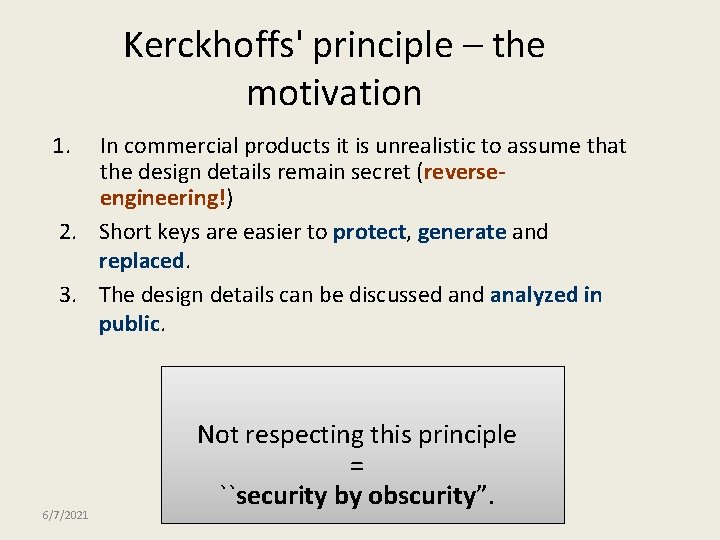
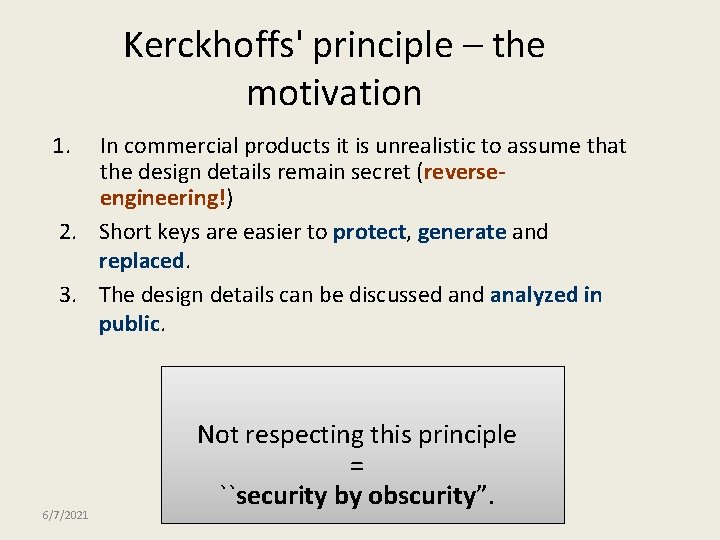
Kerckhoffs' principle – the motivation 1. In commercial products it is unrealistic to assume that the design details remain secret (reverseengineering!) 2. Short keys are easier to protect, generate and replaced. 3. The design details can be discussed analyzed in public. 6/7/2021 Not respecting this principle = ``security by obscurity”.
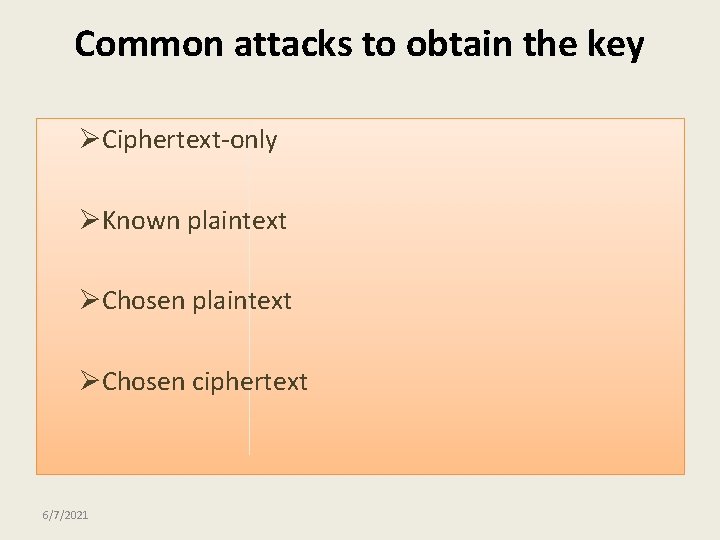
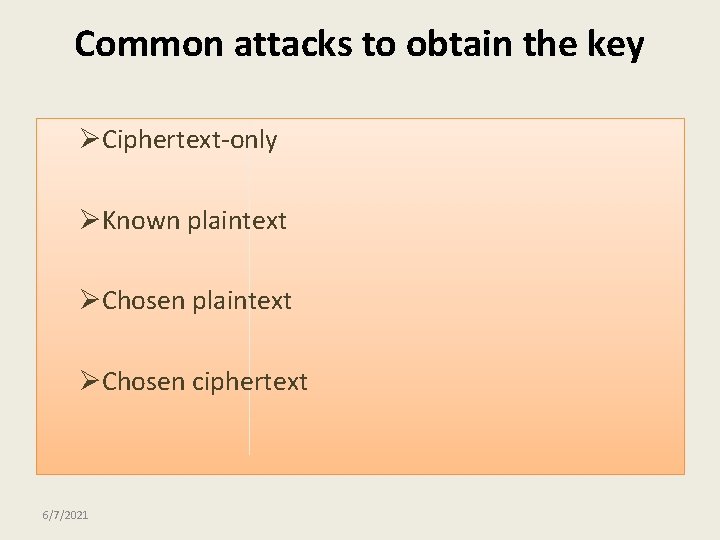
Common attacks to obtain the key ØCiphertext-only ØKnown plaintext ØChosen ciphertext 6/7/2021
Attack on a Shift Cipher • Ciphertext-only • Exhaustive search • 26 cases • Very insecure cipher 6/7/2021
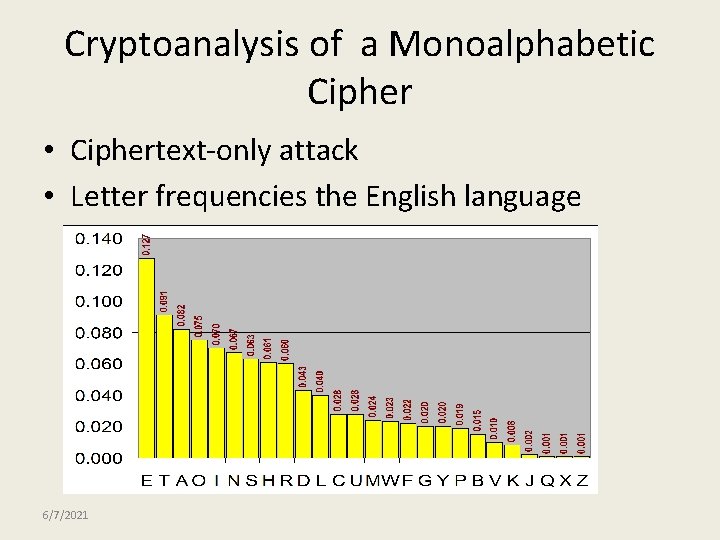
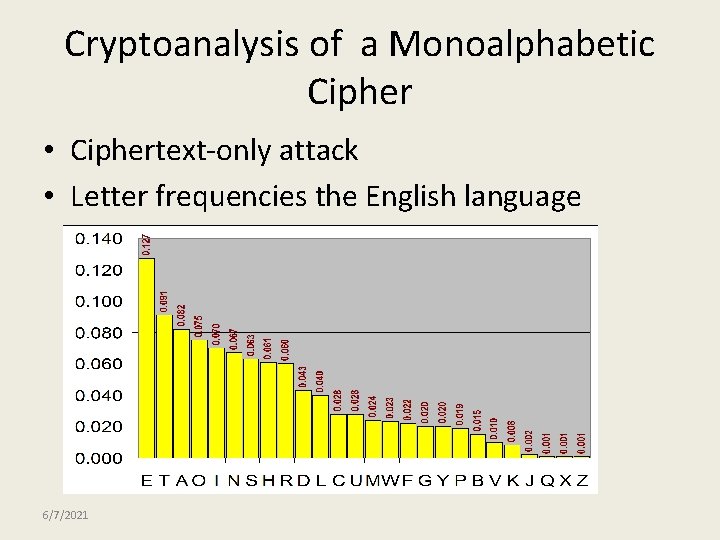
Cryptoanalysis of a Monoalphabetic Cipher • Ciphertext-only attack • Letter frequencies the English language 6/7/2021
Attack on a Substitution Cipher • Insecure cipher, even though the number of possible keys is 26! = 403291461126605635584000000 (approximately 4. 0329· 1026) • Letter frequencies calculator 6/7/2021
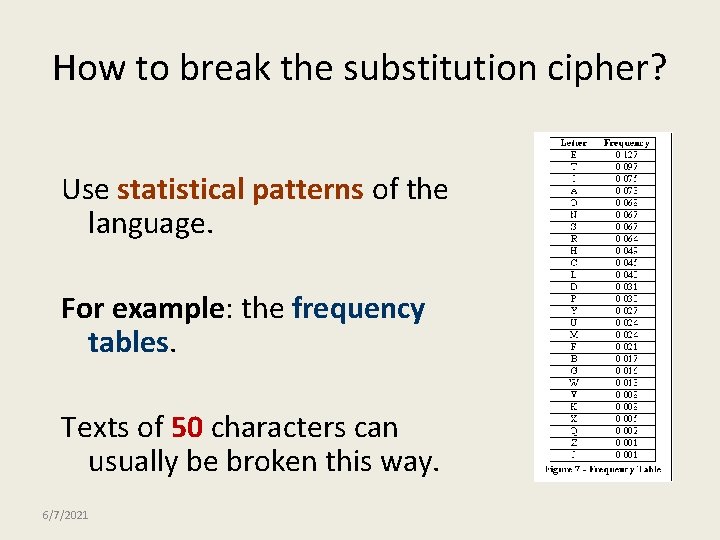
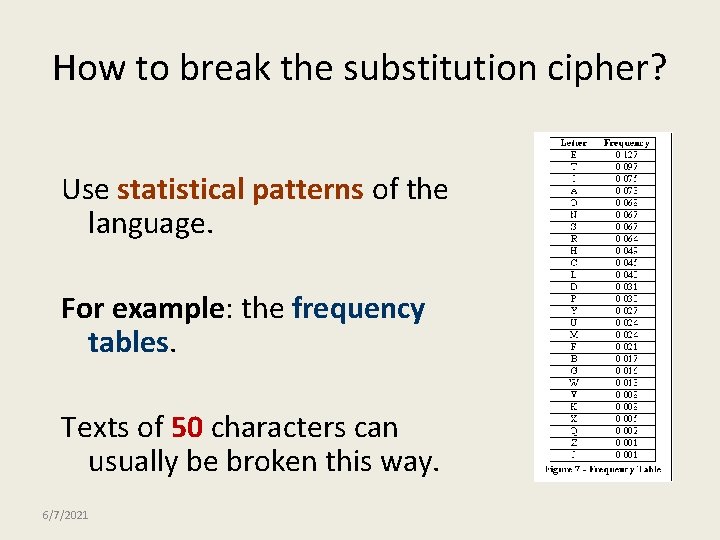
How to break the substitution cipher? Use statistical patterns of the language. For example: the frequency tables. Texts of 50 characters can usually be broken this way. 6/7/2021
Breaking an Affine Cipher • How would you break the affine cipher? – Check all 312 (a, b) combinations – or, take advantage of the mathematical relationship c = a*p + b (mod 26) • Given this ciphertext from an affine cipher find the key and plaintext by using frequency analysis to guess two (a, b) pairs. FMXVE DKAPH FERBN DKRXR SREFM ORUDS DKDVS HVUFE DKAPR KDLYE VLRHH RH 6/7/2021
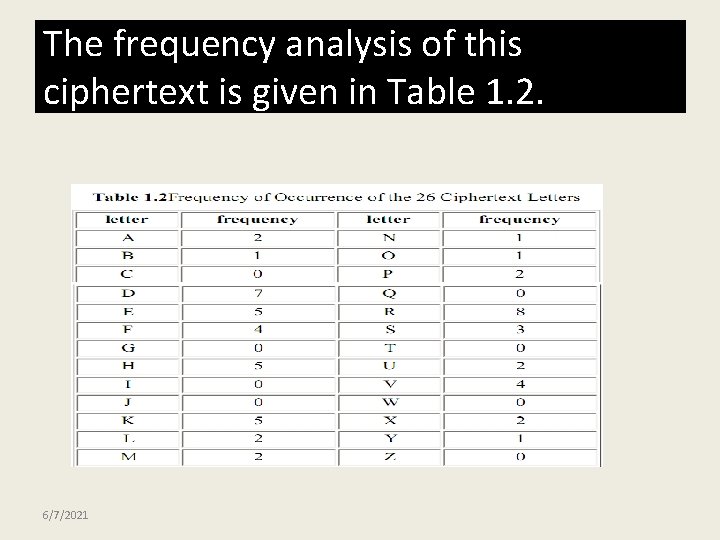
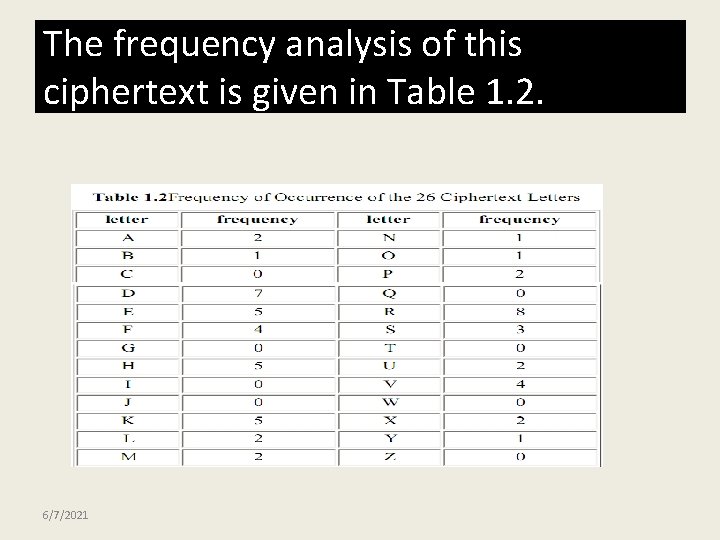
The frequency analysis of this ciphertext is given in Table 1. 2. 6/7/2021
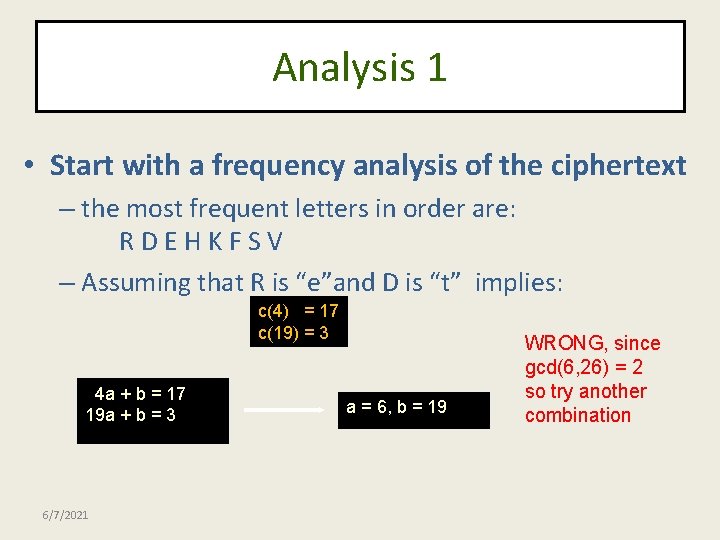
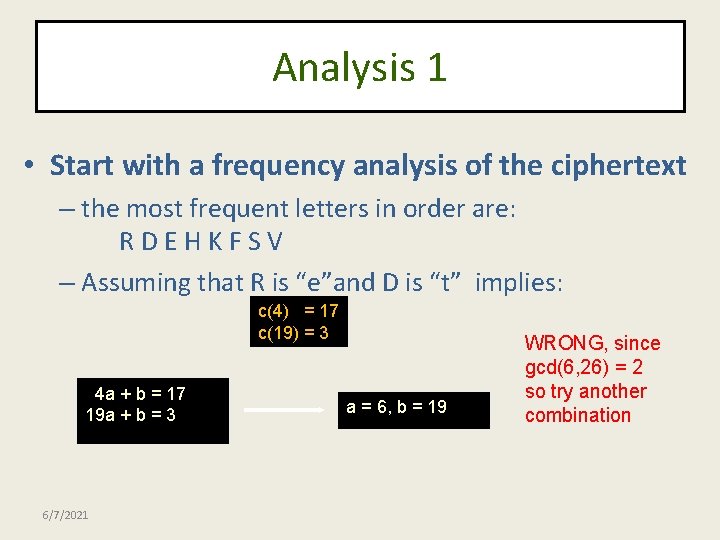
Analysis 1 • Start with a frequency analysis of the ciphertext – the most frequent letters in order are: RDEHKFSV – Assuming that R is “e”and D is “t” implies: c(4) = 17 c(19) = 3 4 a + b = 17 19 a + b = 3 6/7/2021 a = 6, b = 19 WRONG, since gcd(6, 26) = 2 so try another combination
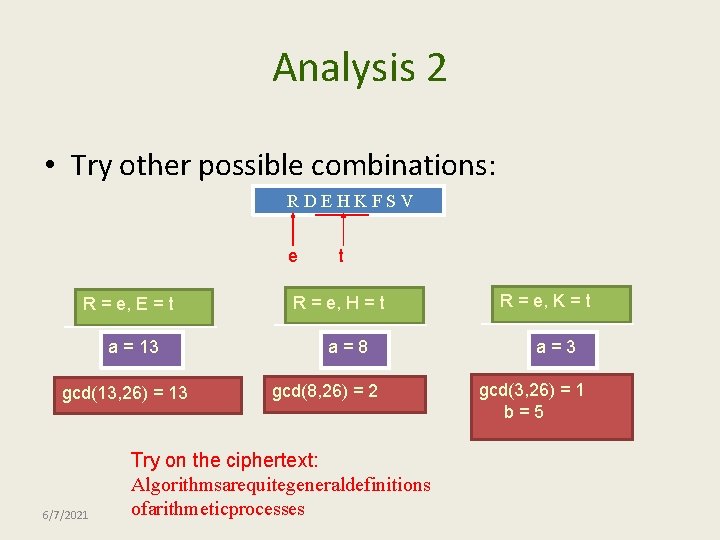
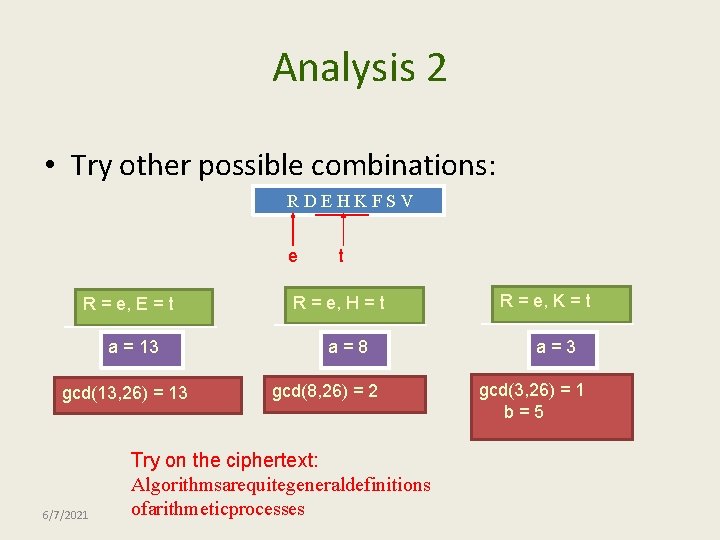
Analysis 2 • Try other possible combinations: RDEHKFSV e R = e, E = t a = 13 gcd(13, 26) = 13 6/7/2021 t R = e, H = t a=8 gcd(8, 26) = 2 Try on the ciphertext: Algorithmsarequitegeneraldefinitions ofarithmeticprocesses R = e, K = t a=3 gcd(3, 26) = 1 b=5
Security of Vigenere Cipher • Vigenere masks the frequency with which a character appears in a language: one letter in the ciphertext corresponds to multiple letters in the plaintext. Makes the use of frequency analysis more difficult. • Any message encrypted by a Vigenere cipher is a collection of as many shift ciphers as there are letters in the key. 6/7/2021
Vigenere Cipher: Cryptanalysis • Find the length of the key. • Divide the message into that many shift cipher encryptions. • Use frequency analysis to solve the resulting shift ciphers. – how? 6/7/2021
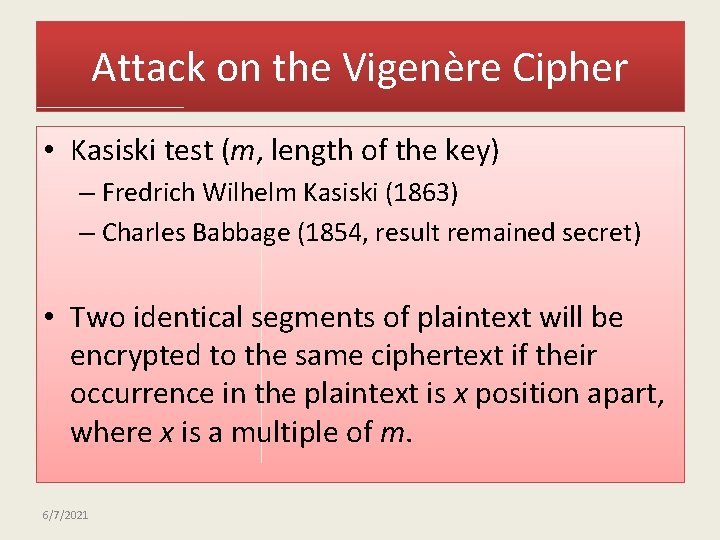
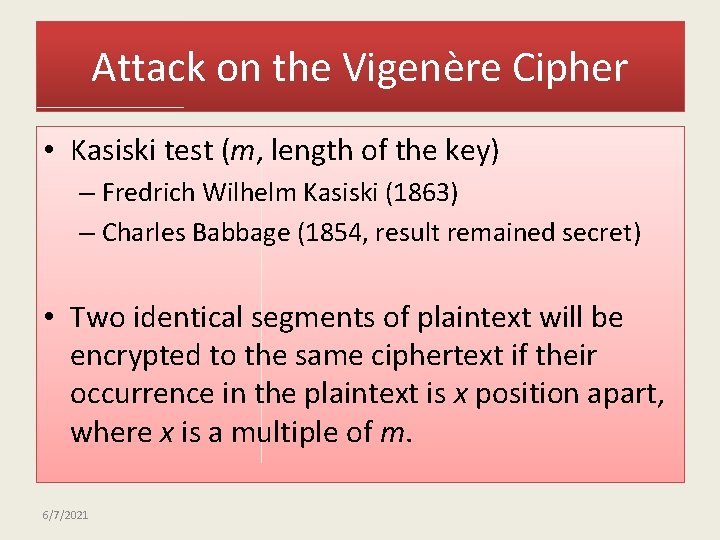
Attack on the Vigenère Cipher • Kasiski test (m, length of the key) – Fredrich Wilhelm Kasiski (1863) – Charles Babbage (1854, result remained secret) • Two identical segments of plaintext will be encrypted to the same ciphertext if their occurrence in the plaintext is x position apart, where x is a multiple of m. 6/7/2021
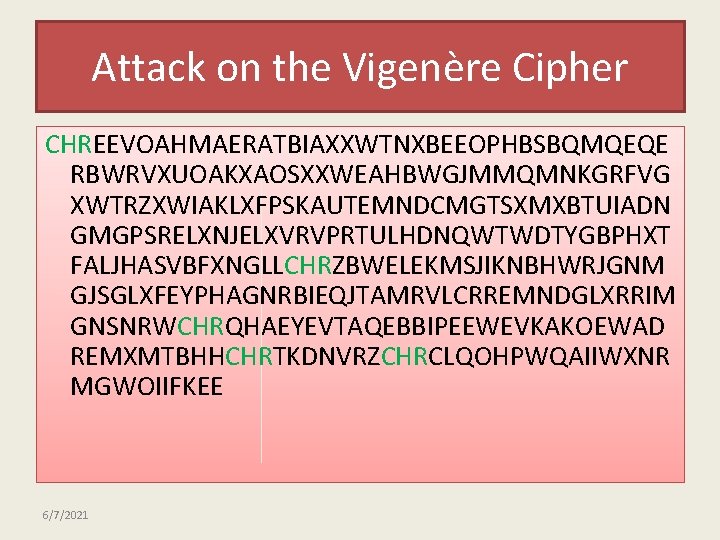
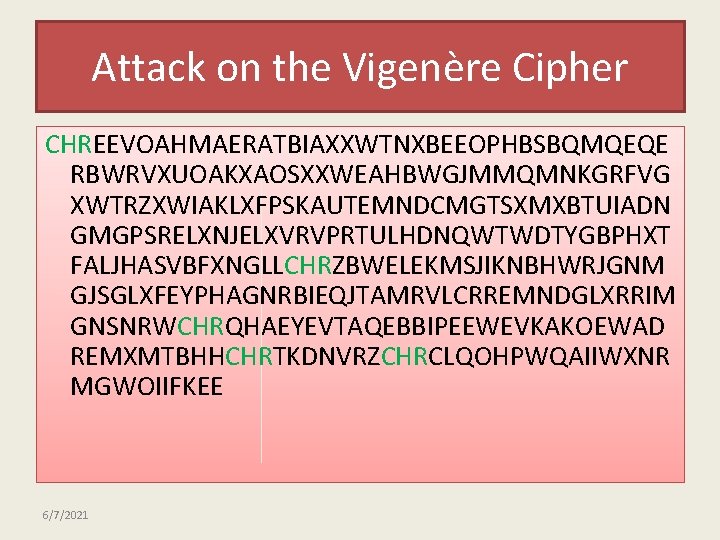
Attack on the Vigenère Cipher CHREEVOAHMAERATBIAXXWTNXBEEOPHBSBQMQEQE RBWRVXUOAKXAOSXXWEAHBWGJMMQMNKGRFVG XWTRZXWIAKLXFPSKAUTEMNDCMGTSXMXBTUIADN GMGPSRELXNJELXVRVPRTULHDNQWTWDTYGBPHXT FALJHASVBFXNGLLCHRZBWELEKMSJIKNBHWRJGNM GJSGLXFEYPHAGNRBIEQJTAMRVLCRREMNDGLXRRIM GNSNRWCHRQHAEYEVTAQEBBIPEEWEVKAKOEWAD REMXMTBHHCHRTKDNVRZCHRCLQOHPWQAIIWXNR MGWOIIFKEE 6/7/2021
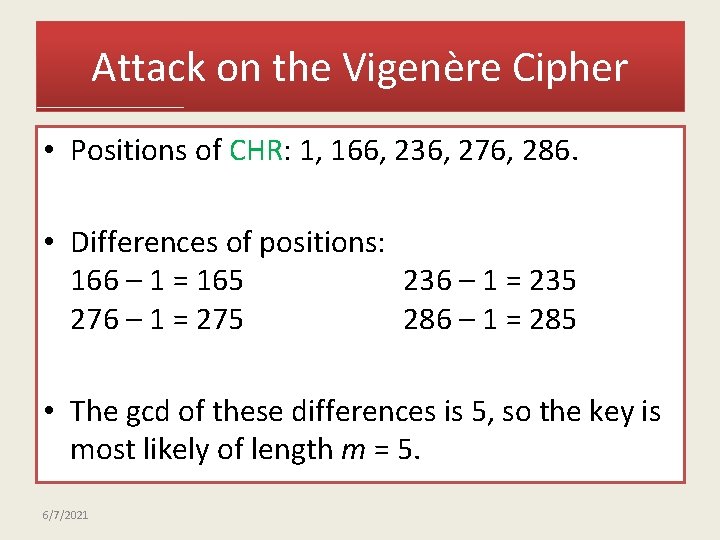
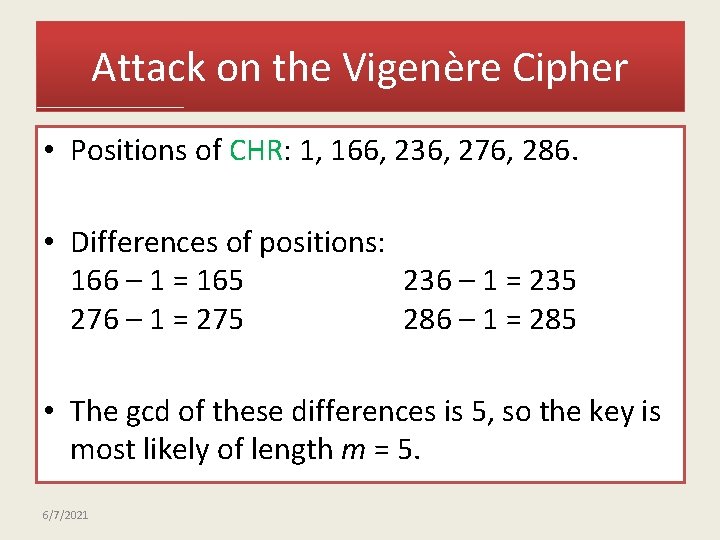
Attack on the Vigenère Cipher • Positions of CHR: 1, 166, 236, 276, 286. • Differences of positions: 166 – 1 = 165 236 – 1 = 235 276 – 1 = 275 286 – 1 = 285 • The gcd of these differences is 5, so the key is most likely of length m = 5. 6/7/2021
Attack on the Vigenère Cipher • Divide the ciphertext into 5 substrings (positions 5 k, 5 k+1, 5 k+2, 5 k+3, 5 k+4) • Analyze each substring as a monoalphabetic cipher. • Also an insecure cipher 6/7/2021
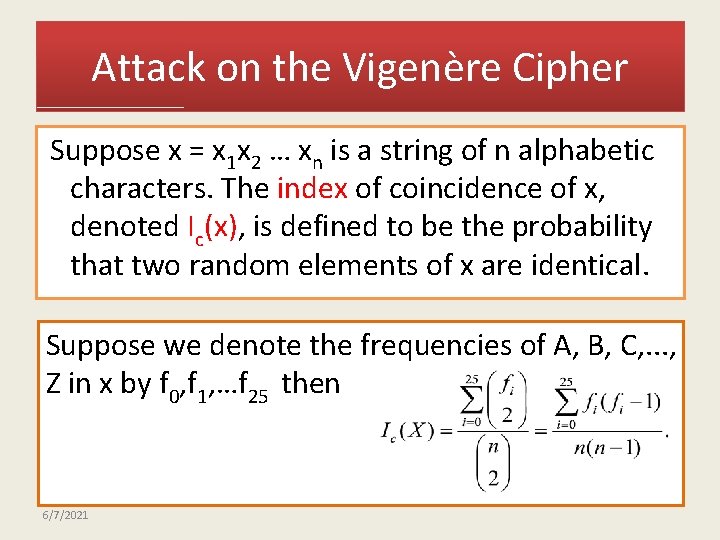
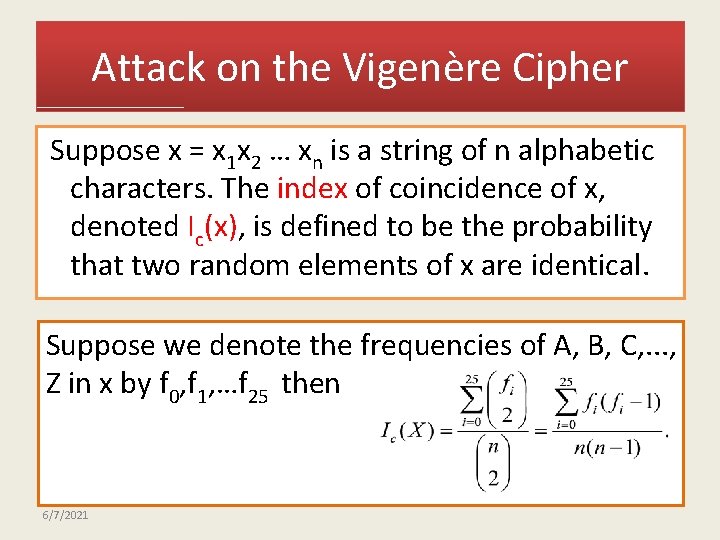
Attack on the Vigenère Cipher Suppose x = x 1 x 2 … xn is a string of n alphabetic characters. The index of coincidence of x, denoted Ic(x), is defined to be the probability that two random elements of x are identical. Suppose we denote the frequencies of A, B, C, . . . , Z in x by f 0, f 1, …f 25 then 6/7/2021
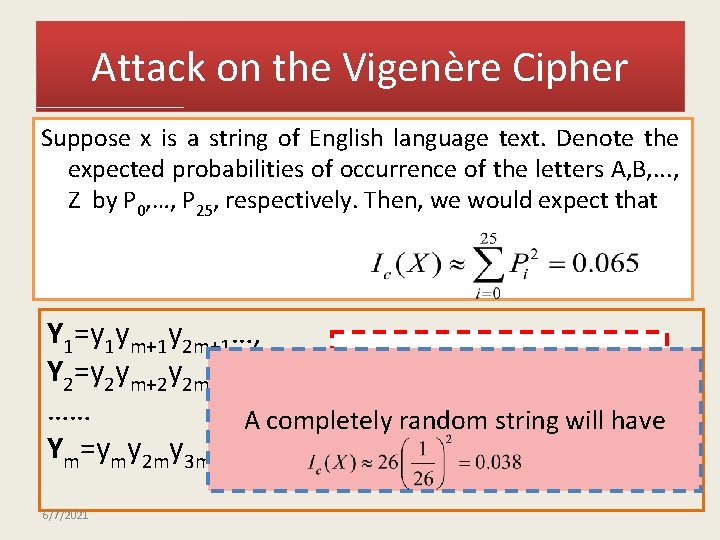
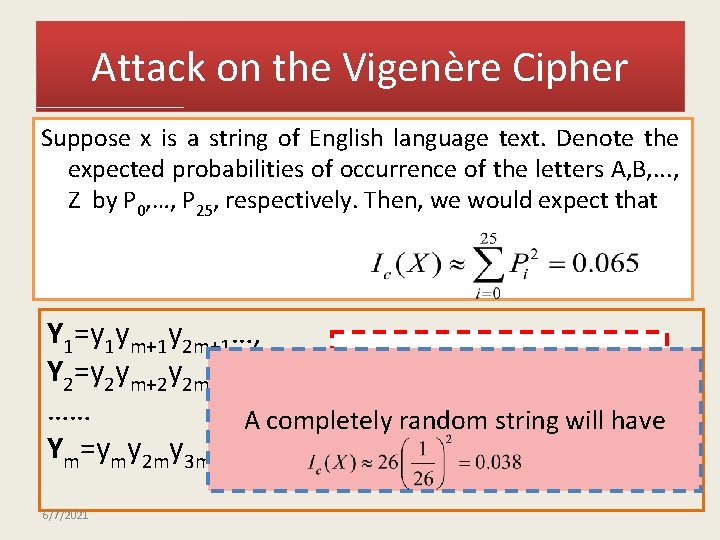
Attack on the Vigenère Cipher Suppose x is a string of English language text. Denote the expected probabilities of occurrence of the letters A, B, . . . , Z by P 0, …, P 25, respectively. Then, we would expect that Y 1=y 1 ym+1 y 2 m+1…, If m is the key word length Y 2=y 2 ym+2 y 2 m+2…, …… A completely random string have Then each value Ic(yiwill ) should Ym=ymy 2 my 3 m…, be roughly equal to 0. 065 6/7/2021
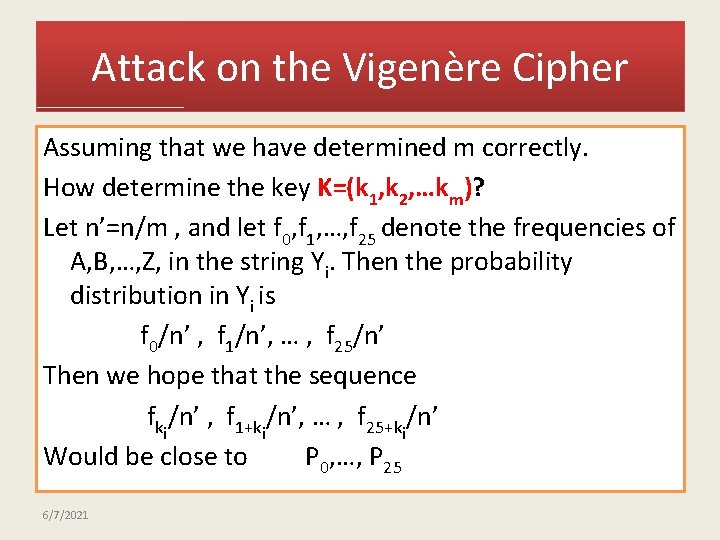
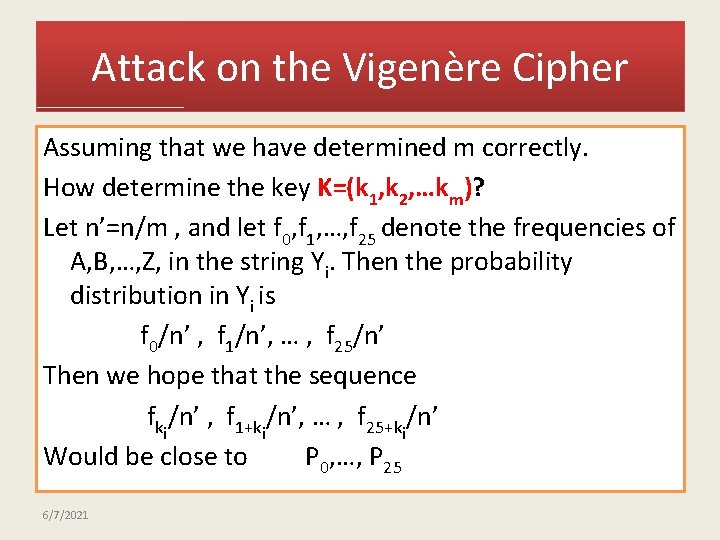
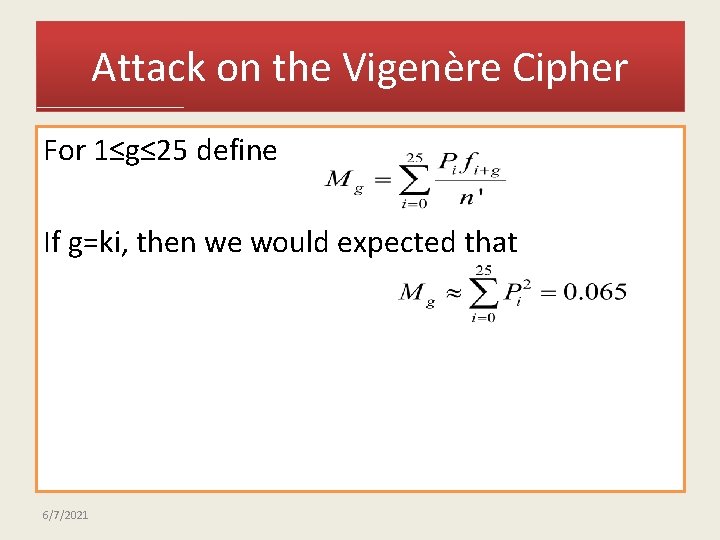
Attack on the Vigenère Cipher Assuming that we have determined m correctly. How determine the key K=(k 1, k 2, …km)? Let n’=n/m , and let f 0, f 1, …, f 25 denote the frequencies of A, B, …, Z, in the string Yi. Then the probability distribution in Yi is nf 0/n’ , f 1/n’, … , f 25/n’ Then we hope that the sequence n fki/n’ , f 1+ki/n’, … , f 25+ki/n’ Would be close to P 0, …, P 25 6/7/2021
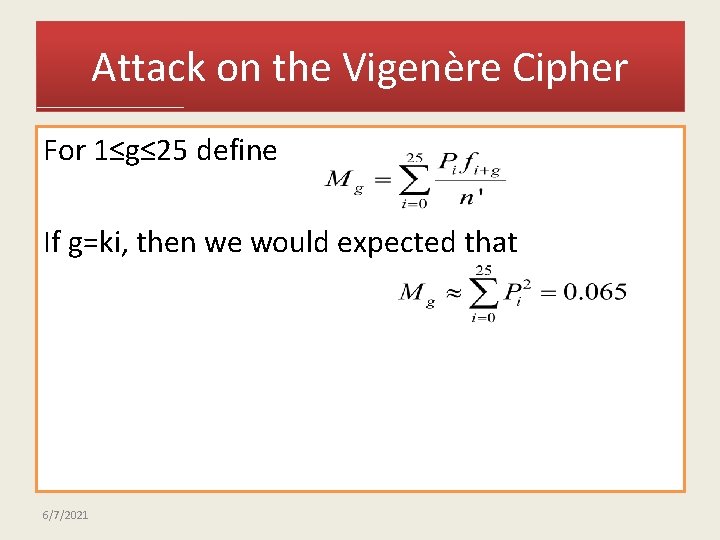
Attack on the Vigenère Cipher For 1≤g≤ 25 define If g=ki, then we would expected that 6/7/2021
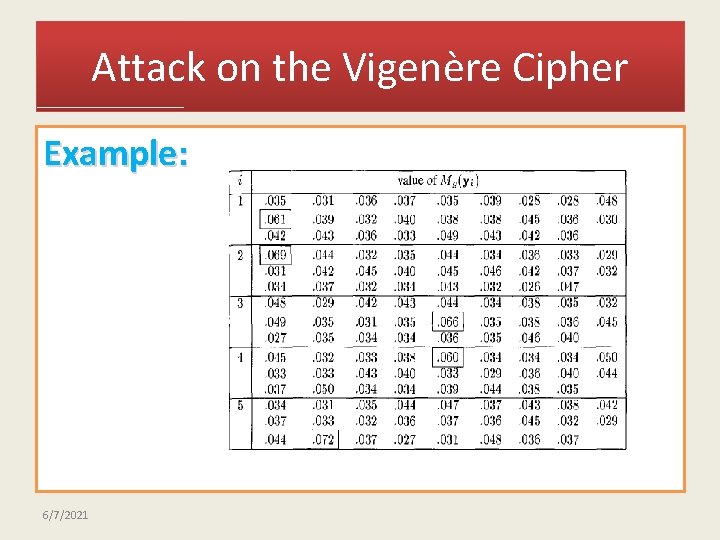
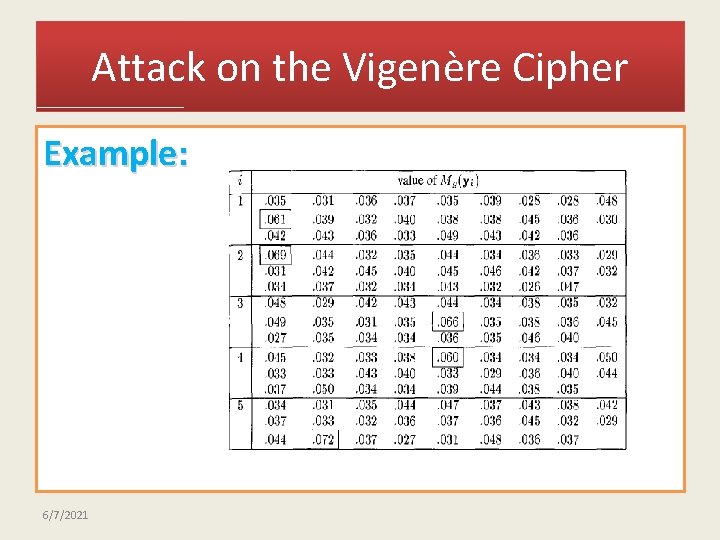
Attack on the Vigenère Cipher Example: 6/7/2021
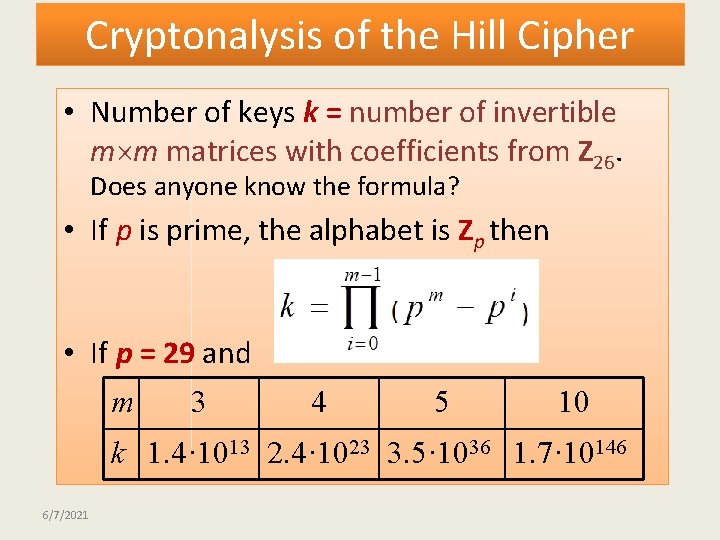
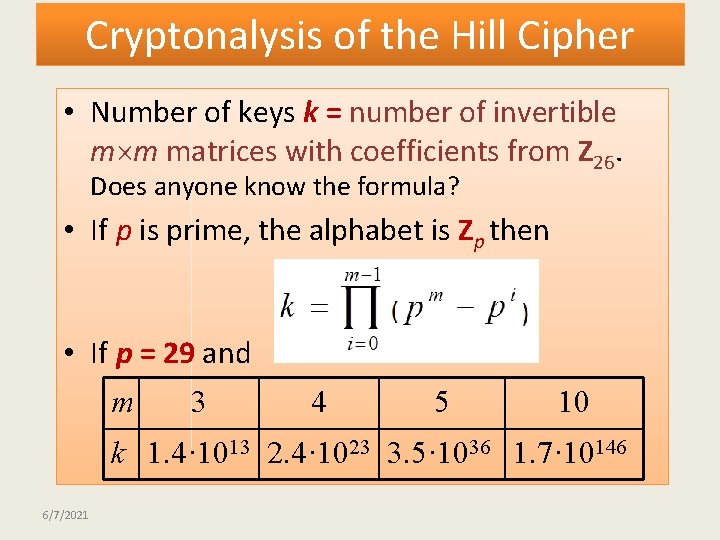
Cryptonalysis of the Hill Cipher • Number of keys k = number of invertible m m matrices with coefficients from Z 26. Does anyone know the formula? • If p is prime, the alphabet is Zp then • If p = 29 and m 3 4 5 10 k 1. 4· 1013 2. 4· 1023 3. 5· 1036 1. 7· 10146 6/7/2021
Cryptanalysis of the Hill Cipher • Easily broken with known plaintext attack. • Permutation Cipher = Hill Cipher, where the key is a permutation matrix. • Both ciphers are insecure. 6/7/2021
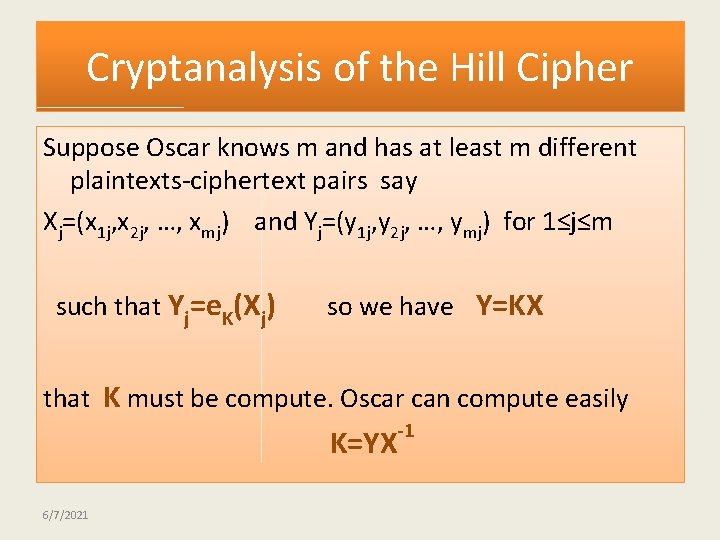
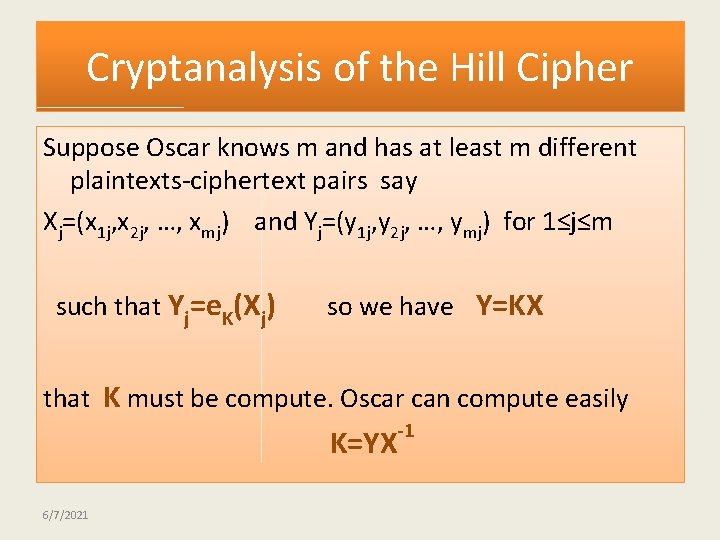
Cryptanalysis of the Hill Cipher Suppose Oscar knows m and has at least m different plaintexts-ciphertext pairs say Xj=(x 1 j, x 2 j, …, xmj) and Yj=(y 1 j, y 2 j, …, ymj) for 1≤j≤m such that Yj=e. K(Xj) so we have Y=KX that K must be compute. Oscar can compute easily K=YX 6/7/2021 -1
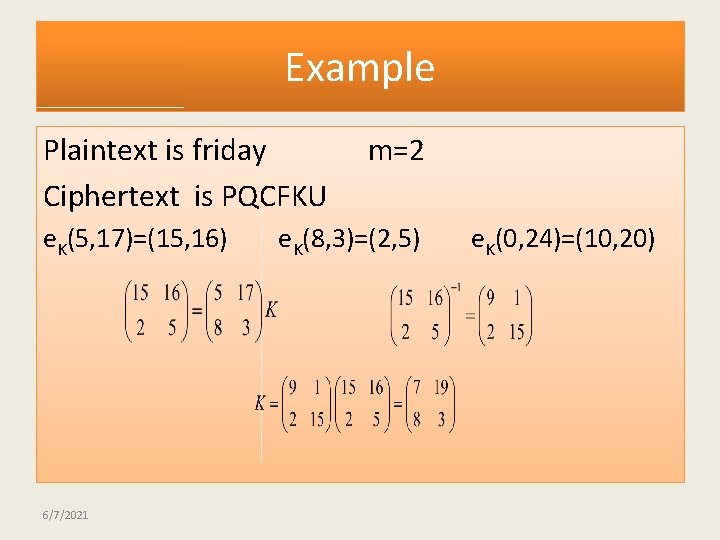
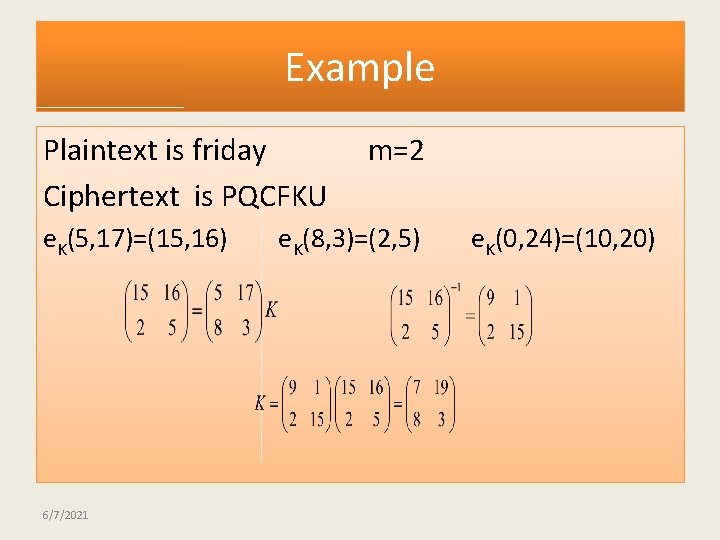
Example Plaintext is friday Ciphertext is PQCFKU e. K(5, 17)=(15, 16) 6/7/2021 m=2 e. K(8, 3)=(2, 5) e. K(0, 24)=(10, 20)
One-time Pads • By Gilbert Vernam and Joseph Mauborgne around 1918 • The key is a random sequence of 0’s and 1’s of the same length as the message. Once a key is used, it is discarded and never used again. • 00101001⊕ 10101100=10000101 • Used in “hot line” between USSR and US 6/7/2021
One-time Pads • E. g. , Plaintext: HELLO Key: KTBXZ -------Ciphertext : RXMIN (using addition mod 26) Key: KTBXZ -------Plaintext: HELLO (using subtraction mod 26) 6/7/2021
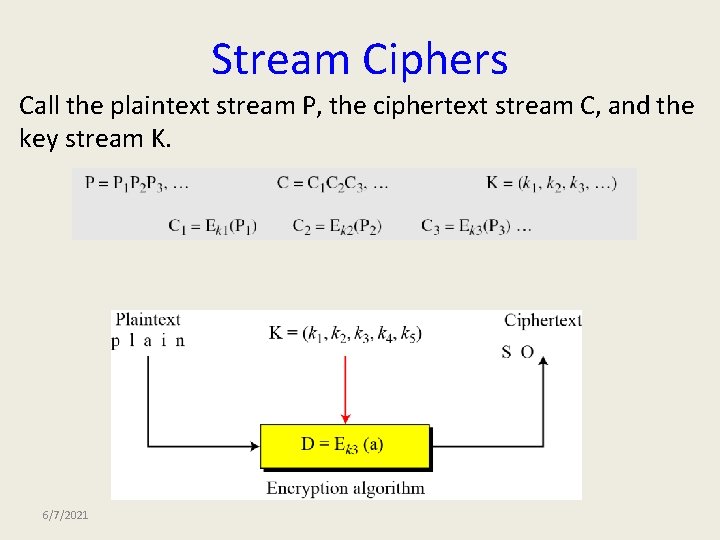
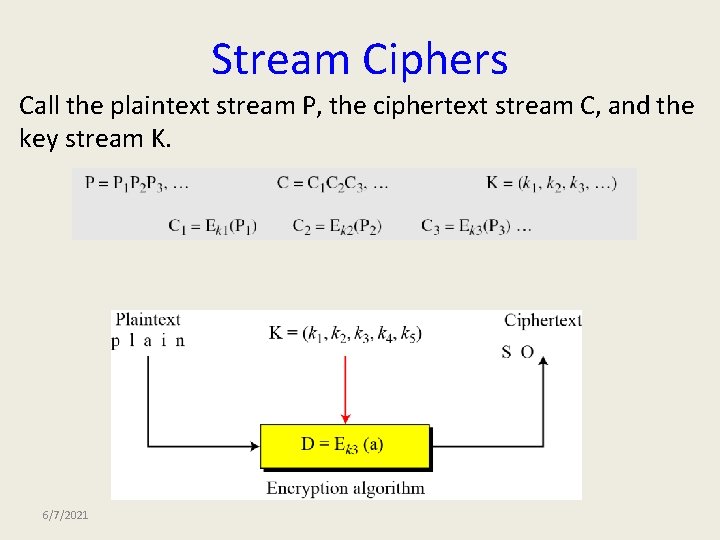
Stream Ciphers Call the plaintext stream P, the ciphertext stream C, and the key stream K. 6/7/2021
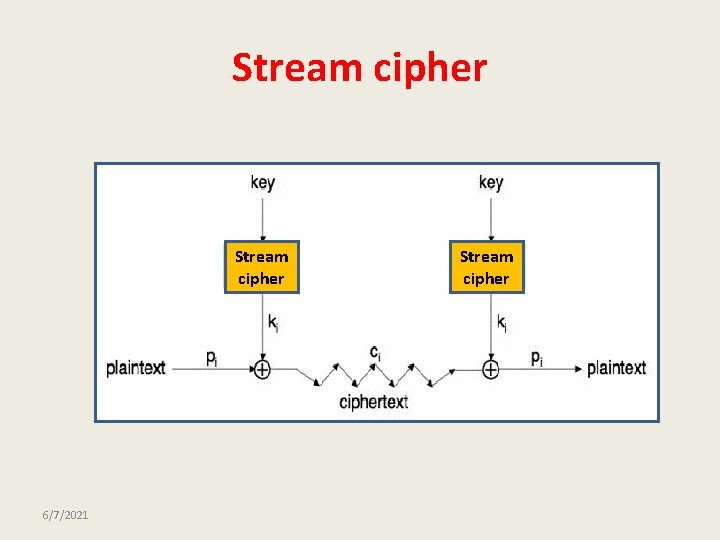
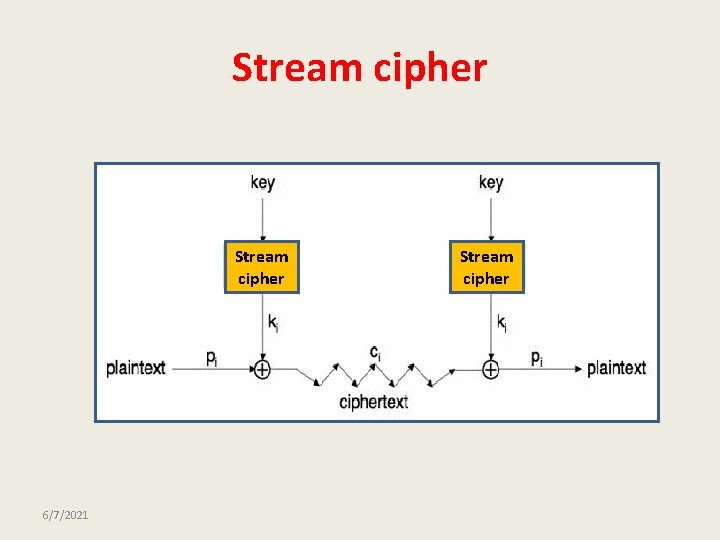
Stream cipher 6/7/2021 Stream cipher
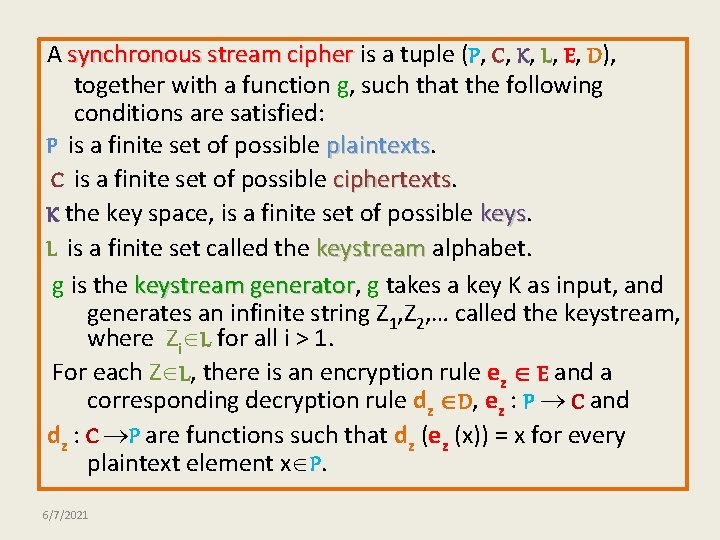
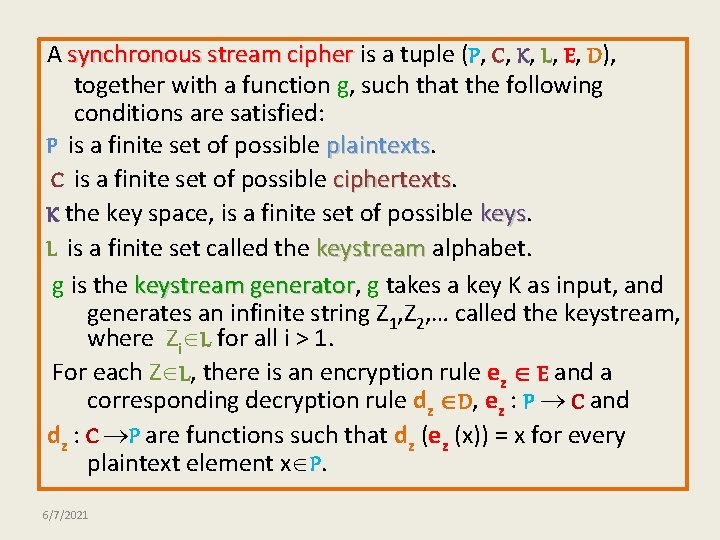
A synchronous stream cipher is a tuple (P, C, K, L, E, D), together with a function g, such that the following conditions are satisfied: P is a finite set of possible plaintexts C is a finite set of possible ciphertexts K the key space, is a finite set of possible keys L is a finite set called the keystream alphabet. g is the keystream generator, generator g takes a key K as input, and generates an infinite string Z 1, Z 2, … called the keystream, where Zi L for all i > 1. For each Z L, there is an encryption rule ez E and a corresponding decryption rule dz D, ez : P C and dz : C P are functions such that dz (ez (x)) = x for every plaintext element x P. 6/7/2021
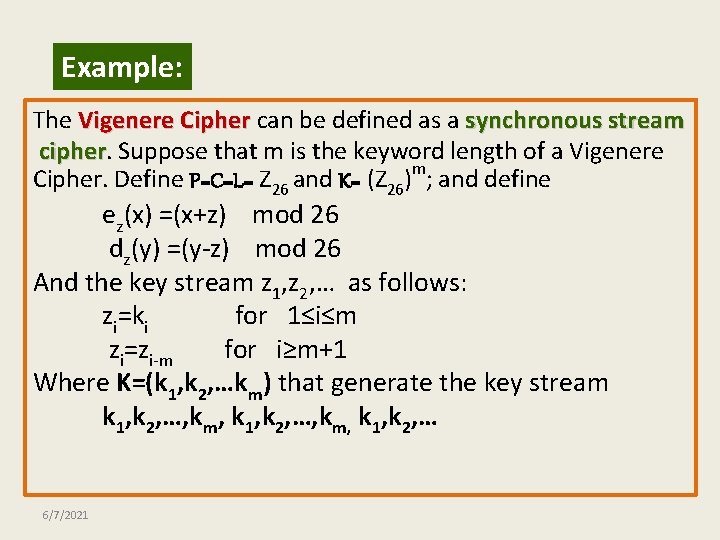
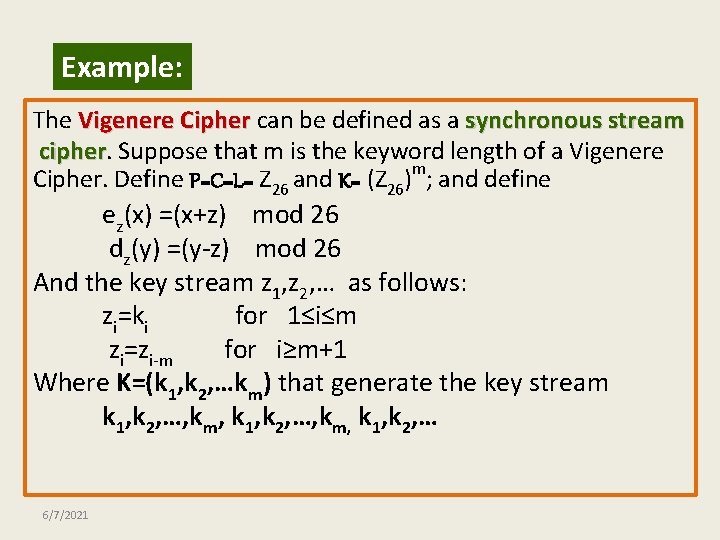
Example: The Vigenere Cipher can be defined as a synchronous stream cipher Suppose that m is the keyword length of a Vigenere Cipher. Define P=C=L= Z 26 and K= (Z 26)m; and define ez(x) =(x+z) mod 26 dz(y) =(y-z) mod 26 And the key stream z 1, z 2, … as follows: zi=ki for 1≤i≤m zi=zi-m for i≥m+1 Where K=(k 1, k 2, …km) that generate the key stream k 1, k 2, …, km, k 1, k 2, … 6/7/2021
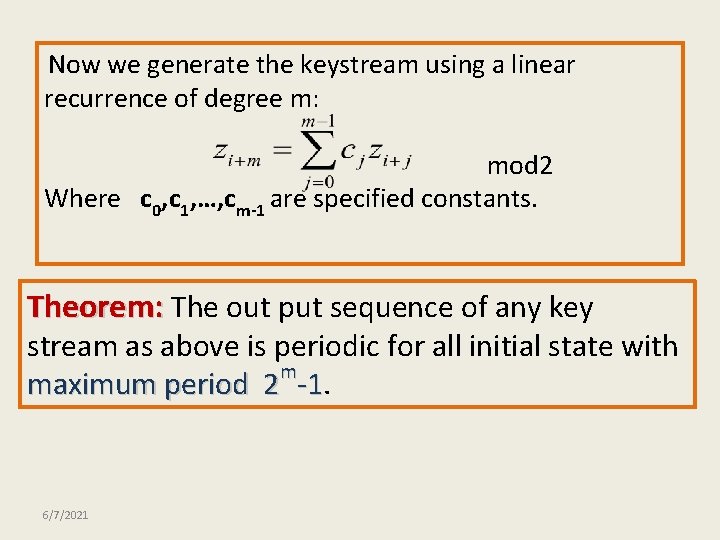
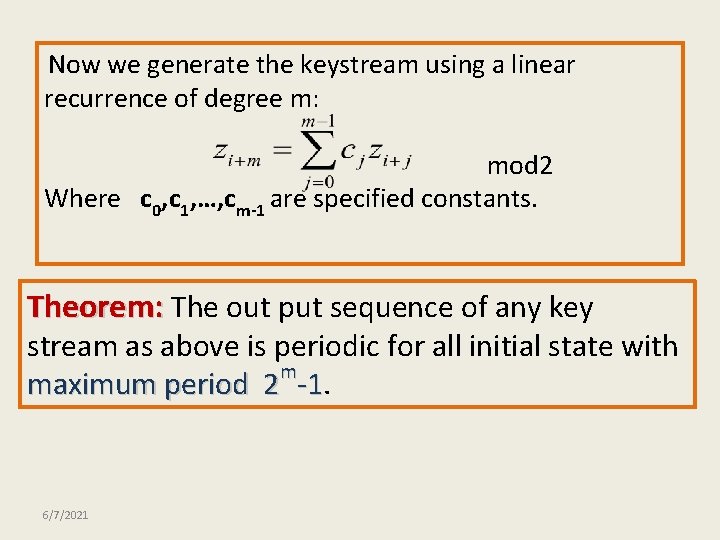
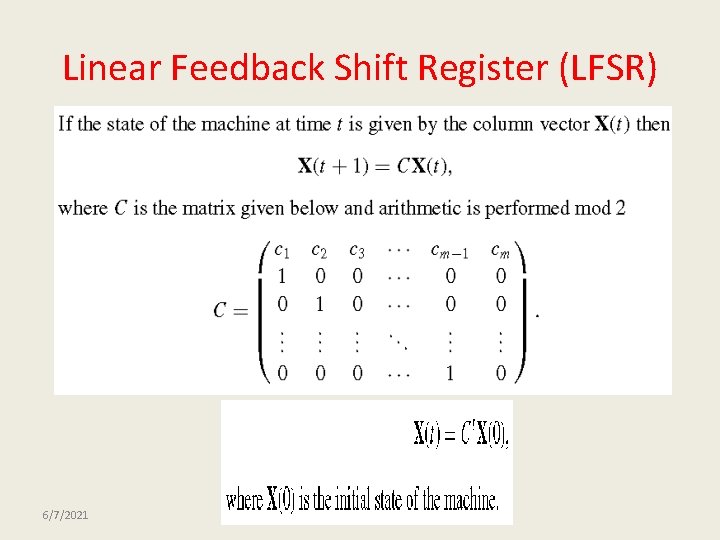
Now we generate the keystream using a linear recurrence of degree m: mod 2 Where c 0, c 1, …, cm-1 are specified constants. Theorem: The out put sequence of any key stream as above is periodic for all initial state with m maximum period 2 -1. -1 6/7/2021
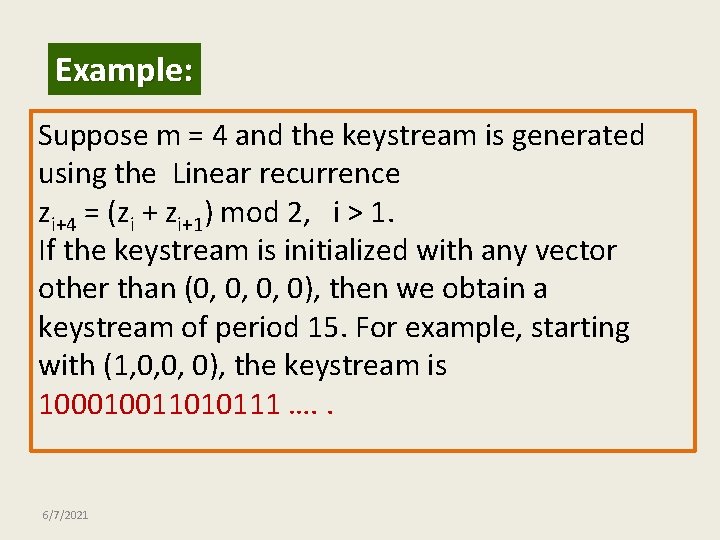
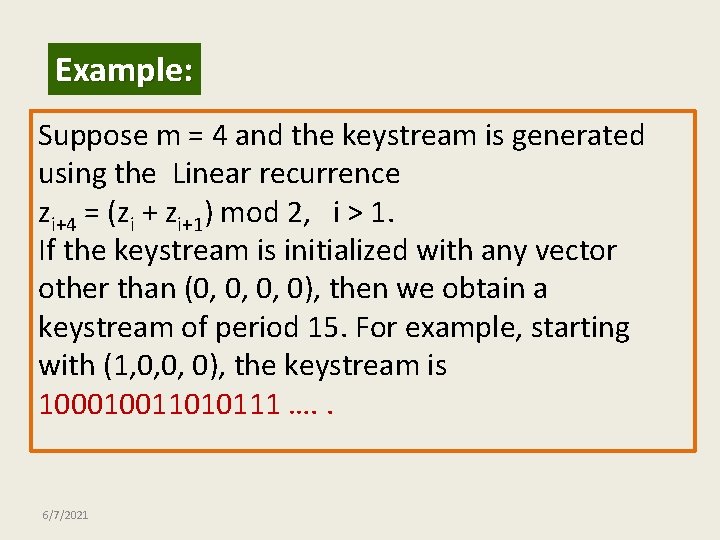
Example: Suppose m = 4 and the keystream is generated using the Linear recurrence zi+4 = (zi + zi+1) mod 2, i > 1. If the keystream is initialized with any vector other than (0, 0, 0, 0), then we obtain a keystream of period 15. For example, starting with (1, 0, 0, 0), the keystream is 100010011010111 …. . 6/7/2021
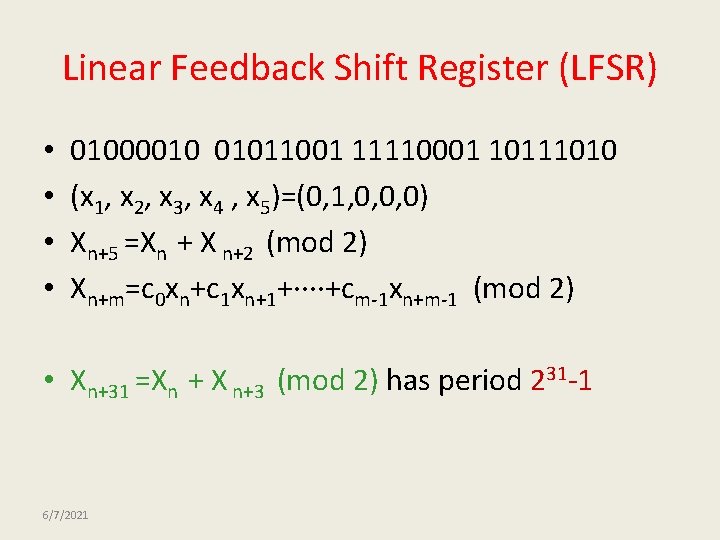
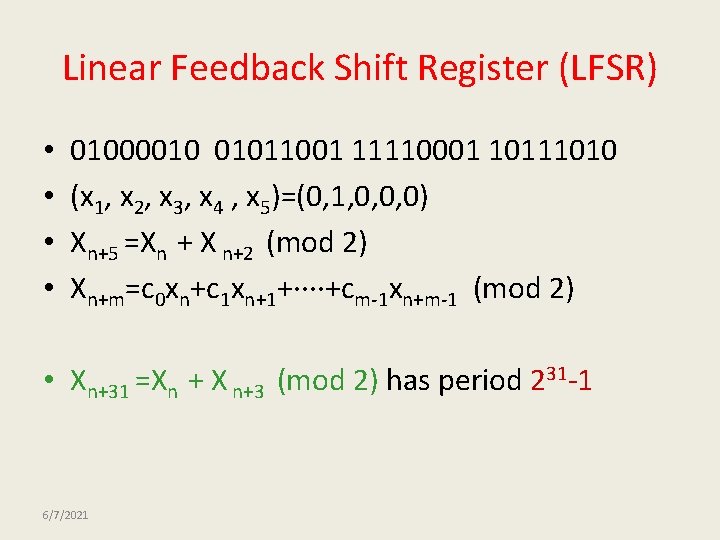
Linear Feedback Shift Register (LFSR) • • 01000010 01011001 11110001 10111010 (x 1, x 2, x 3, x 4 , x 5)=(0, 1, 0, 0, 0) Xn+5 =Xn + X n+2 (mod 2) Xn+m=c 0 xn+c 1 xn+1+····+cm-1 xn+m-1 (mod 2) • Xn+31 =Xn + X n+3 (mod 2) has period 231 -1 6/7/2021
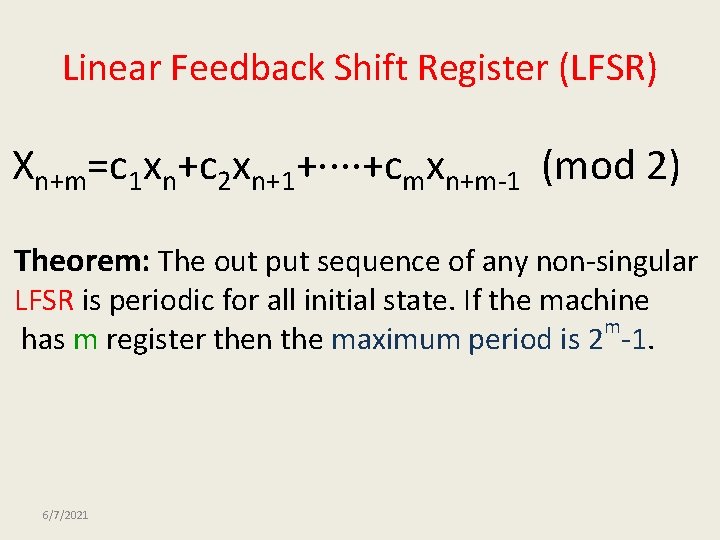
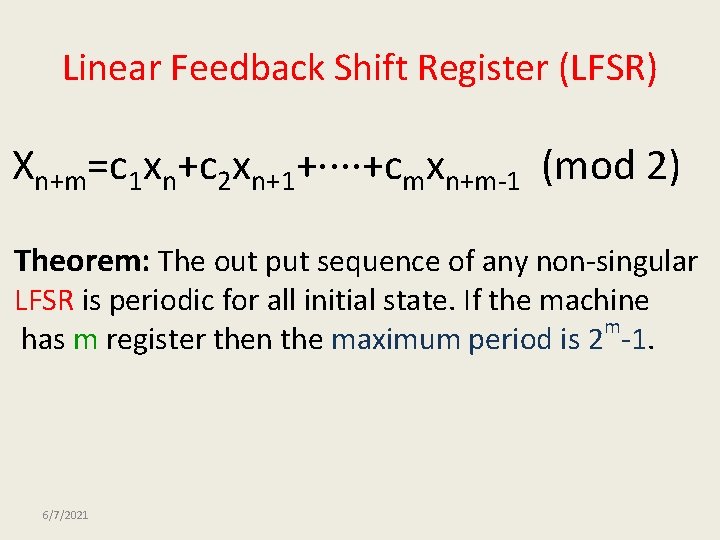
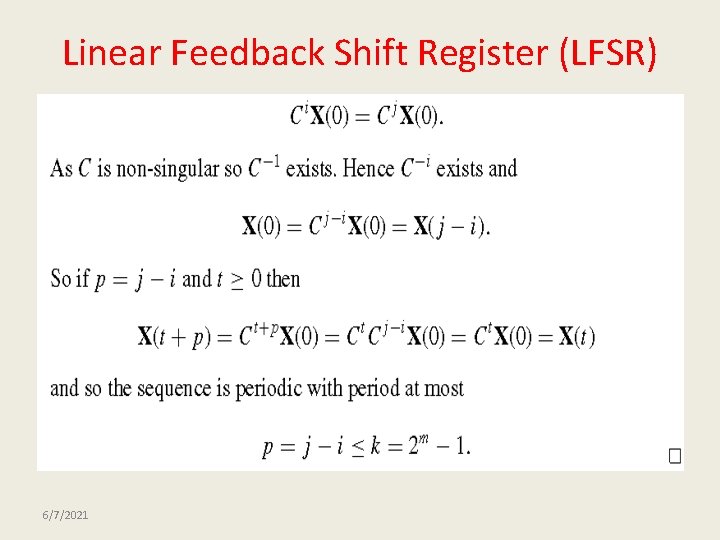
Linear Feedback Shift Register (LFSR) Xn+m=c 1 xn+c 2 xn+1+····+cmxn+m-1 (mod 2) Theorem: The out put sequence of any non-singular LFSR is periodic for all initial state. If the machine m has m register then the maximum period is 2 -1. 6/7/2021
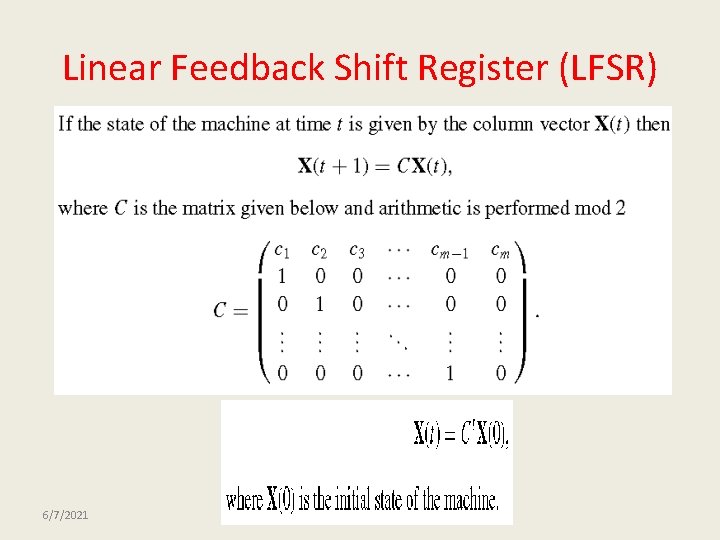
Linear Feedback Shift Register (LFSR) 6/7/2021
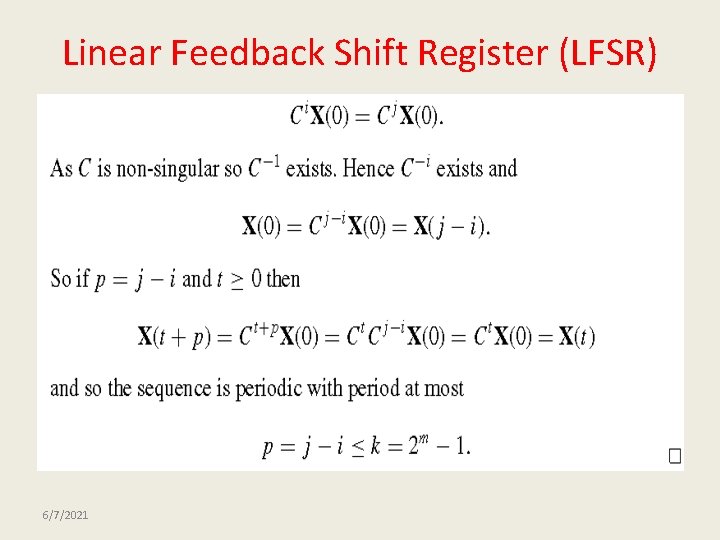
Linear Feedback Shift Register (LFSR) 6/7/2021
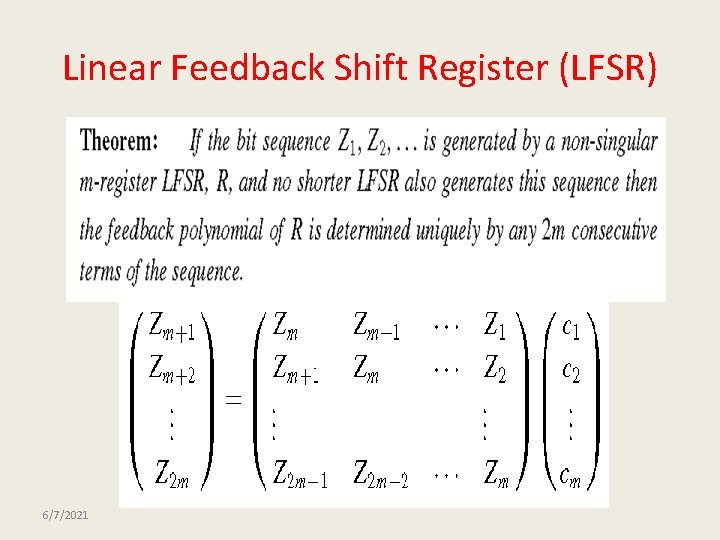
Linear Feedback Shift Register (LFSR) 6/7/2021
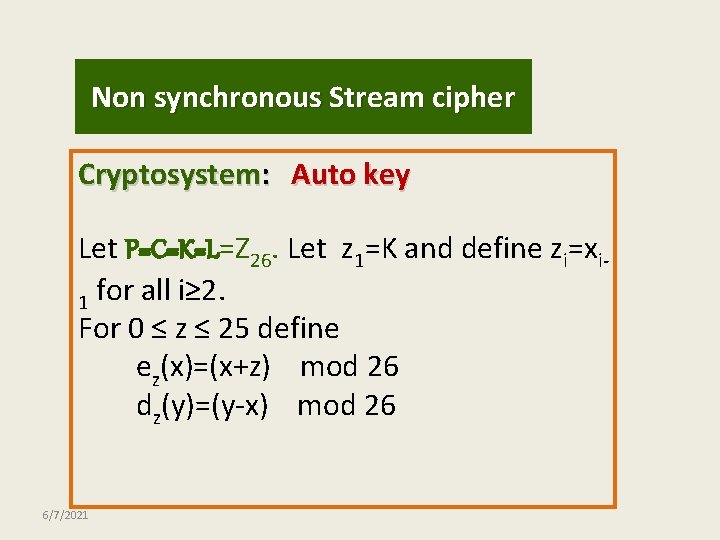
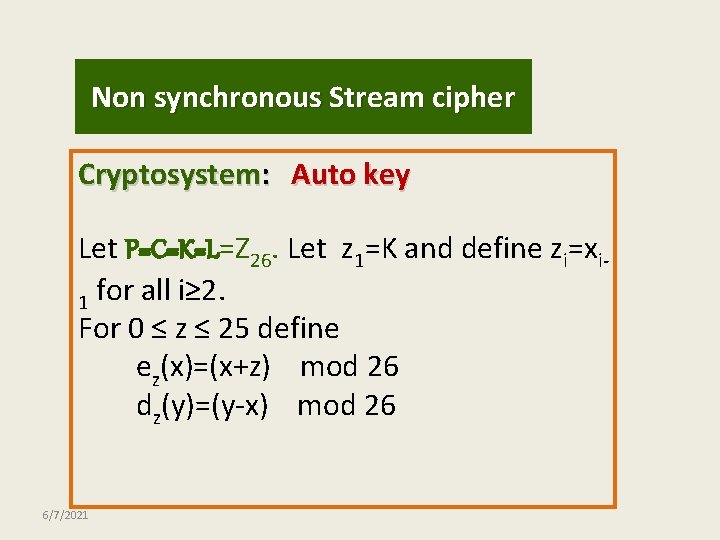
Non synchronous Stream cipher Cryptosystem: Auto key Let P=C=K=L=Z 26. Let z 1=K and define zi=xi 1 for all i≥ 2. For 0 ≤ z ≤ 25 define ez(x)=(x+z) mod 26 dz(y)=(y-x) mod 26 6/7/2021
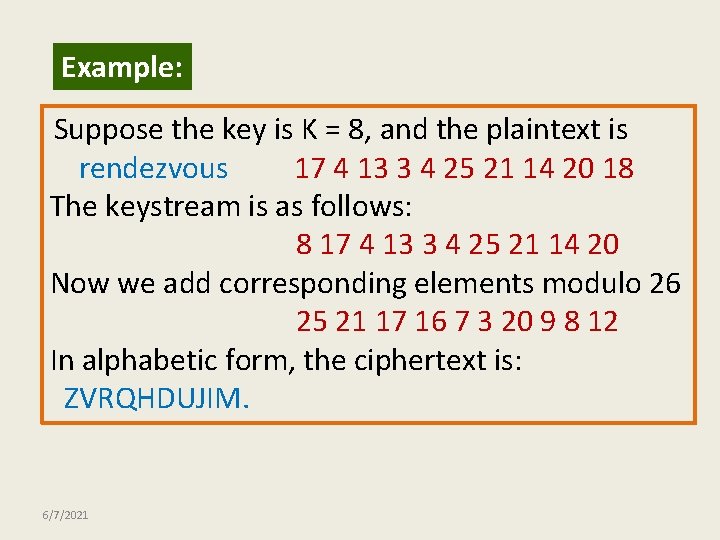
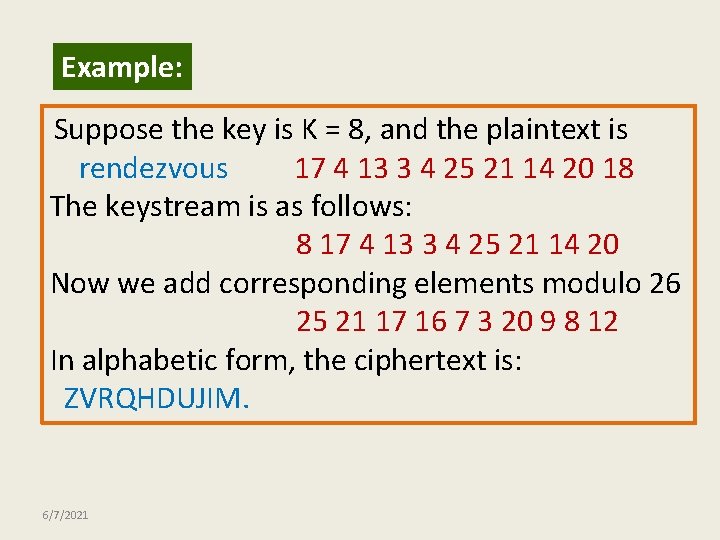
Example: Suppose the key is K = 8, and the plaintext is rendezvous 17 4 13 3 4 25 21 14 20 18 The keystream is as follows: 8 17 4 13 3 4 25 21 14 20 Now we add corresponding elements modulo 26 25 21 17 16 7 3 20 9 8 12 In alphabetic form, the ciphertext is: ZVRQHDUJIM. 6/7/2021
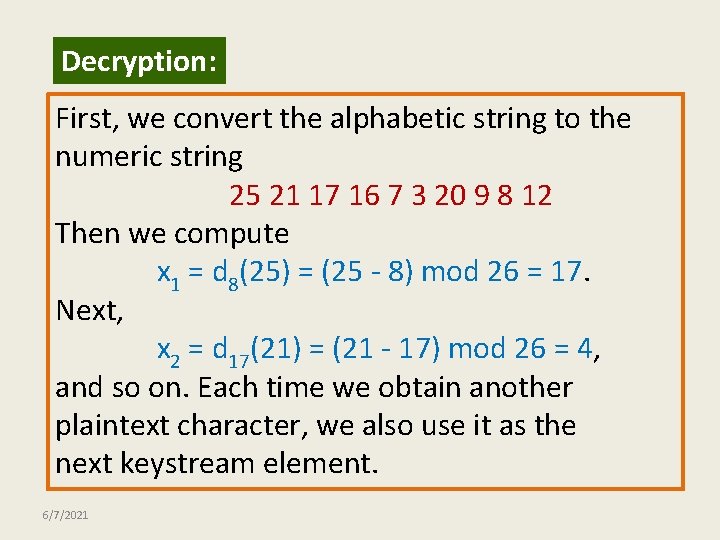
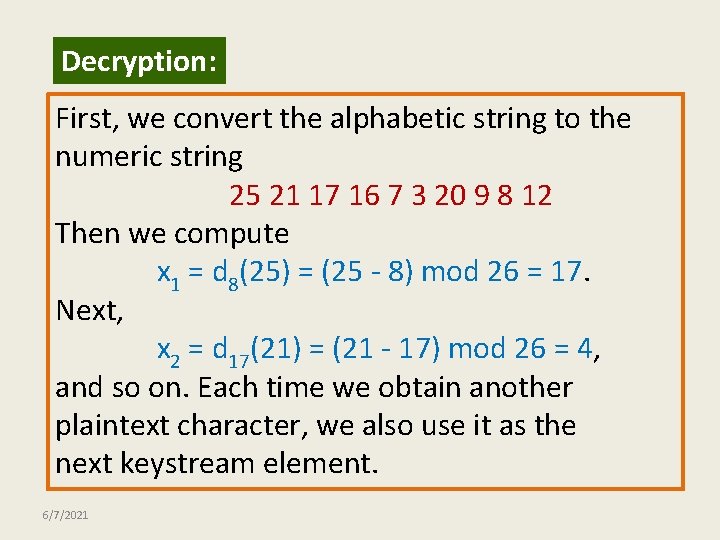
Decryption: First, we convert the alphabetic string to the numeric string 25 21 17 16 7 3 20 9 8 12 Then we compute x 1 = d 8(25) = (25 - 8) mod 26 = 17. Next, x 2 = d 17(21) = (21 - 17) mod 26 = 4, and so on. Each time we obtain another plaintext character, we also use it as the next keystream element. 6/7/2021
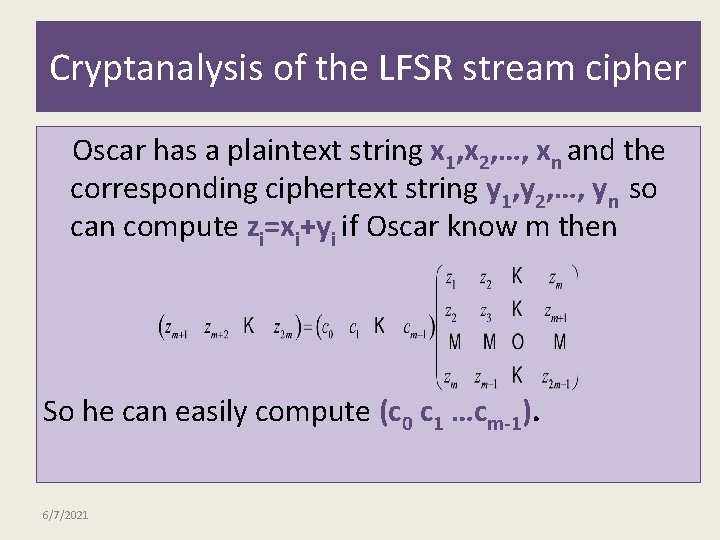
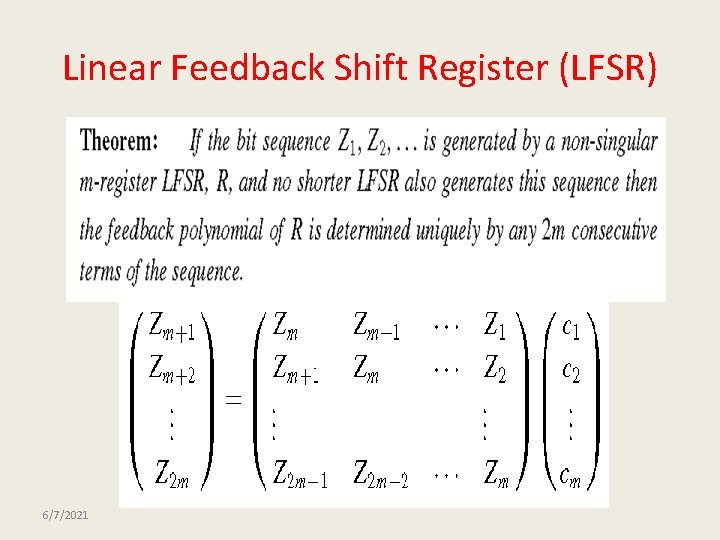
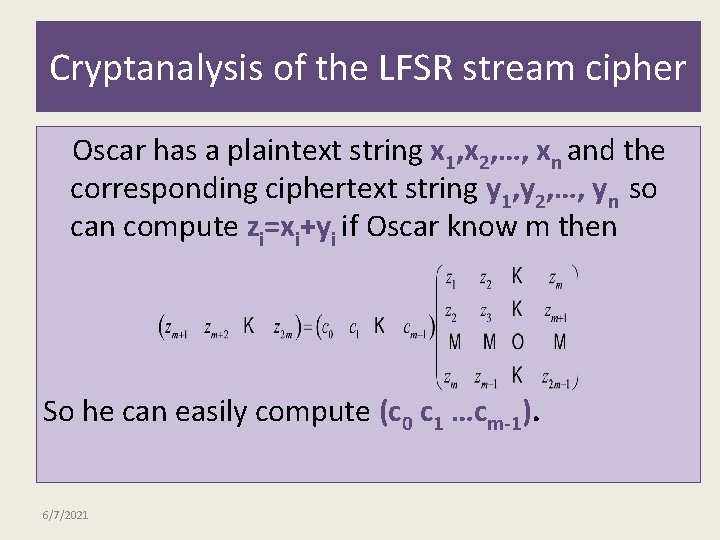
Cryptanalysis of the LFSR stream cipher Oscar has a plaintext string x 1, x 2, …, xn and the corresponding ciphertext string y 1, y 2, …, yn so can compute zi=xi+yi if Oscar know m then So he can easily compute (c 0 c 1 …cm-1). 6/7/2021
The End 6/7/2021