Lecture 1 Data Network Security Communication Communicationistheexchangeof Informationfromoneentitytothe

- Slides: 20
Lecture 1 Data & Network Security
Communication • “Communicationistheexchangeof. Informationfromoneentitytothe rusinga. Transmission. Medium” • Asyoucanclearlynotice, thedefinitionof. Data. Communicationalthough. Si mpleleavesmanyquestionsunanswered: • Exchange? ? • Information? ? • Entities? ? • Medium? ? • Transmission? ?
Communication • When we communicate , we share information • Information can be LOCAL or REMOTE • LOCAL communication occurs face to face • REMOTE communication occurs over a long distance • When we refer to COMPUTER SYSTEMS, Data is represented in the form of Binary Units (Bits) in the form of Zeros (0’s) and One’s (1’s) • Also the entities can most of the times be considered to be COMPUTERS!
Computer Communication • Computer Communication is the exchange of data (in the form of 0’s and 1’s) between two devices (computers) via some form of the transmission medium. ” • Computer communication is considered to be Local if the communicating devices are present in the same building or a similarly restricted geographical area. • Computer Communication is considered Remote, if the devices are farther apart.
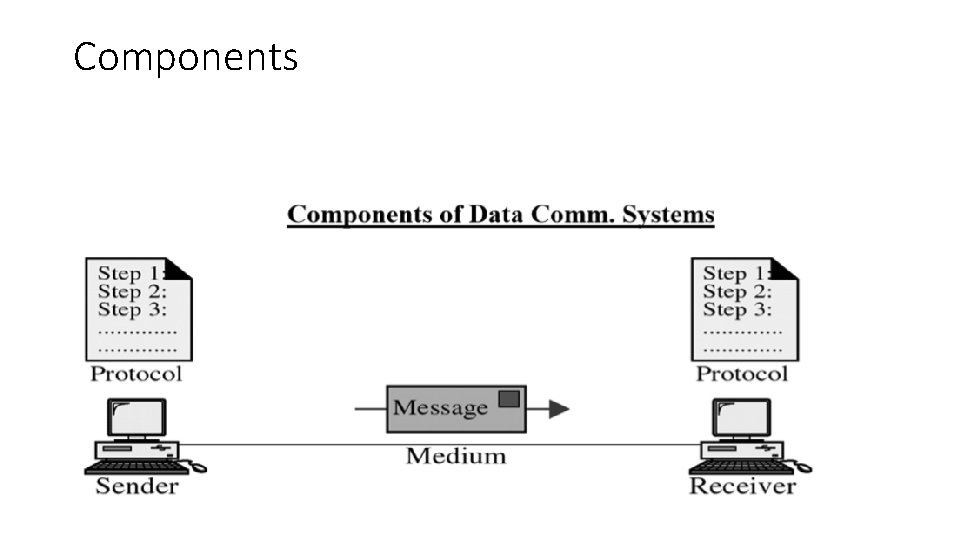
• Any system is made up of more than one component. Similarly, a data communication system is made up of 5 components as shown in the upcoming figure: 1) Message 2) Sender 3) Receiver 4) Transmission Medium 5) Protocol
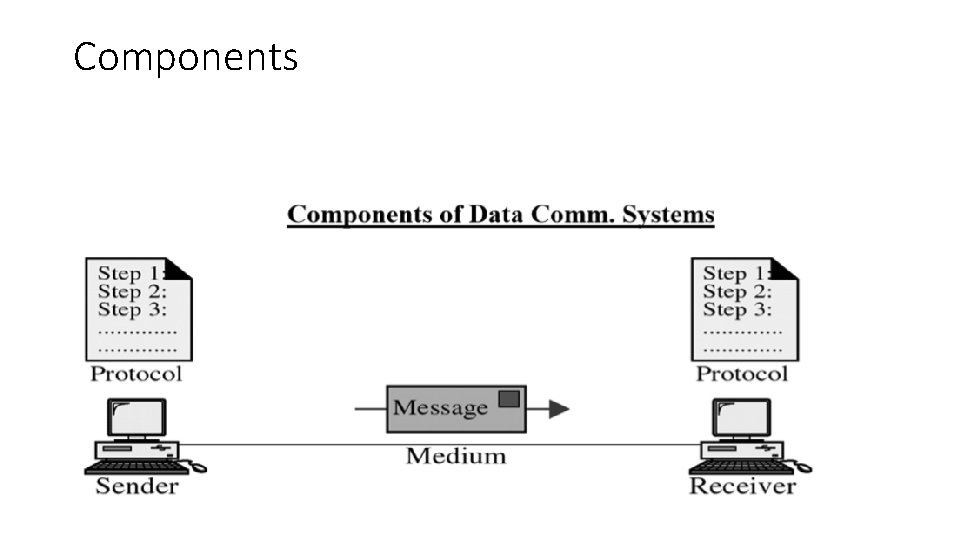
Components
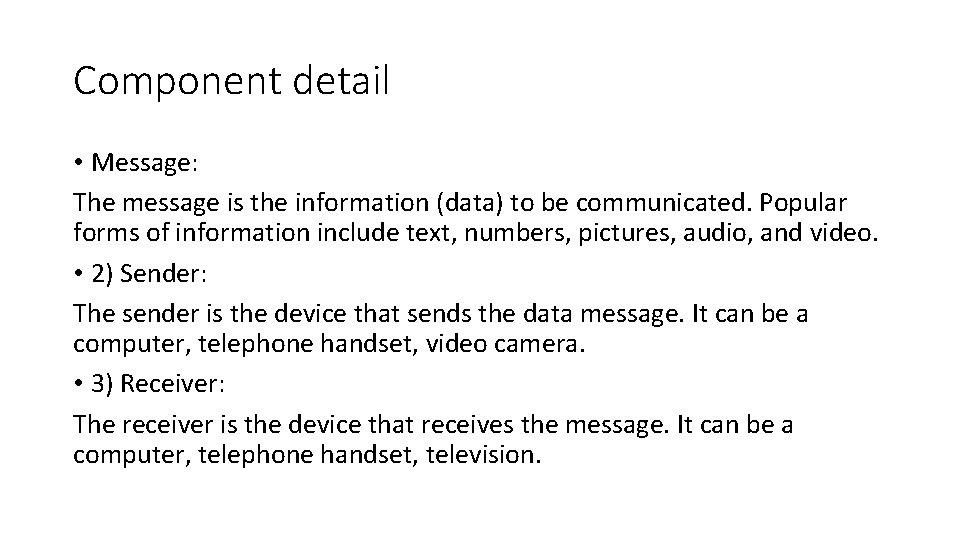
Component detail • Message: The message is the information (data) to be communicated. Popular forms of information include text, numbers, pictures, audio, and video. • 2) Sender: The sender is the device that sends the data message. It can be a computer, telephone handset, video camera. • 3) Receiver: The receiver is the device that receives the message. It can be a computer, telephone handset, television.
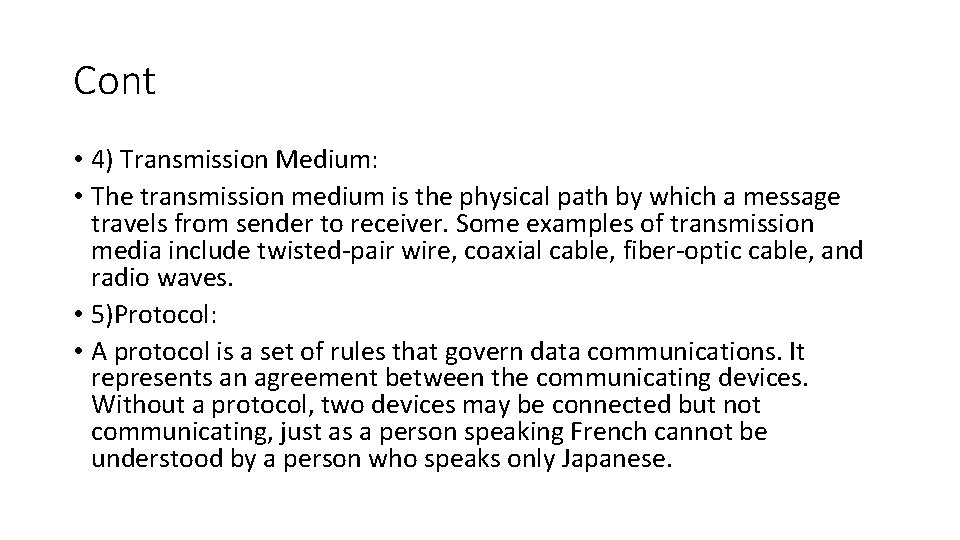
Cont • 4) Transmission Medium: • The transmission medium is the physical path by which a message travels from sender to receiver. Some examples of transmission media include twisted-pair wire, coaxial cable, fiber-optic cable, and radio waves. • 5)Protocol: • A protocol is a set of rules that govern data communications. It represents an agreement between the communicating devices. Without a protocol, two devices may be connected but not communicating, just as a person speaking French cannot be understood by a person who speaks only Japanese.
Networks • Anetworkisasetofdevices/nodetwoormorethantwoconnectedtogethe rbycommunicationlinks. Adevices/nodecanbeacomputer, printer, orany otherdevicecapableofsendingand/orreceivingdatageneratedbyothern odesonthenetwork. • Bothdevicesmustfollowtheagreeduponrules“Standard”toshareinform ationbetweenthem.
Network Criteria: • A network must be able to meet a certain number of criteria. The most important of these are: 1)Performance: 2) Reliability: In addition to accuracy of delivery, network reliability is measured by the frequency of failure, the time it takes a link to recover from a failure

• Security:
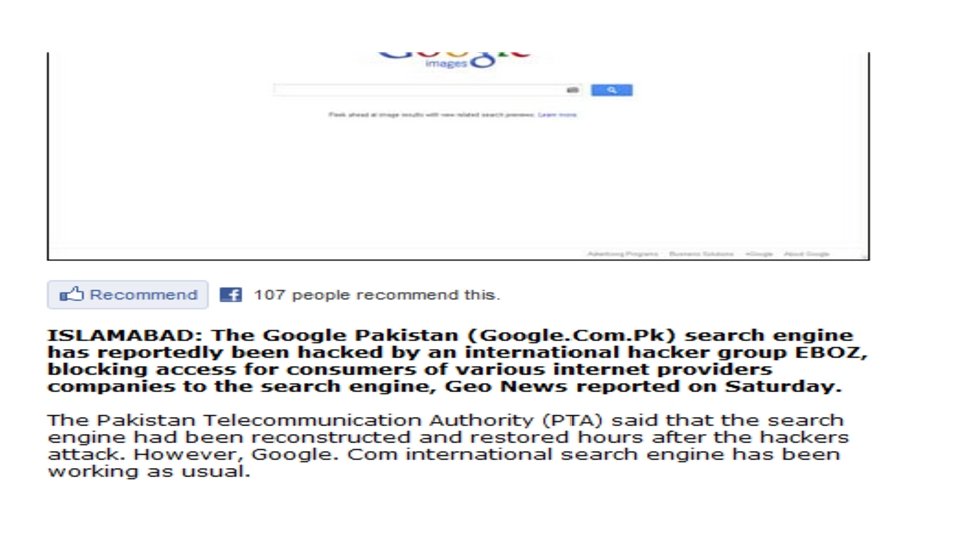
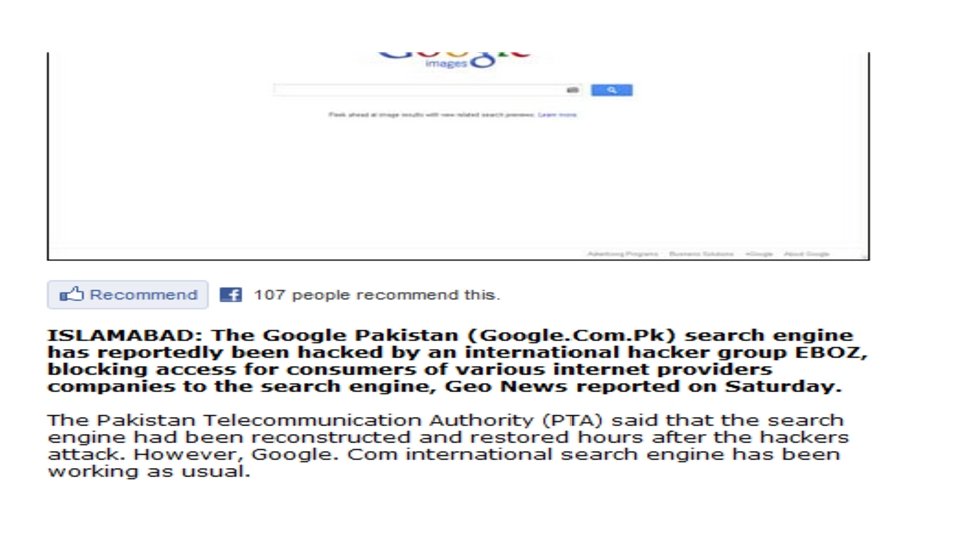
Introduction to network security. • 1996 Indian hackers attack Pakistan government sites. • Vladimir Levin stole US $ 10 million from Citibank. • 2006 Muslim hackers attack 598 Danish websites. • Yahoo, Google, FBI, CIA, several other well known government websites fall victim. • China hacker; 50+ Chinese Gov. websites/day
For Fun (31. 4%) No reason Specified (14. 7%) Political Reasons (11. 8%) Patriotism (10. 9%) As a challenge (10. 8%) Revenge (3. 3%)
Types of hackers • White Hat Hacker: • Good guys, ethical hackers who use their hacking skills for defensive purpose • Black Hat Hacker: • Bad guys, the malicious hackers or crackers who use their skills for illegal or malicious purposes • Grey Hat Hacker: • May work offensively or defensively depending on the situation
Hacker based on skill levels • Script Kiddies Computer novices using tools • Intermediate Hackers Halfway from script kiddies into elite hackers • Elite Hackers Highly skilled experts
Cryptology • Cryptology is a Greek word meaning “hidden, secret writing” • Cryptology consists on two concepts: 1. Cryptography 2. Cryptanalysis
Cryptography • It is the practice and study of techniques for secure communication in the presence of third parties (called adversaries or intruders) • More generally, it is about constructing and analyzing protocols that block adversaries • Various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography
Cont. . • Applications of cryptography include ATM cards, computer passwords, VPN and Secure Shell • Secure Shell (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. The best known example application is for remote login to computer systems by users.
Cryptanalysis: • Cryptanalysis (from the Greek kryptós, "hidden", and analýein, "to loosen" or "to untie") • Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.