Leakage Evaluation on Power Balance Countermeasure Against SideChannel
Leakage Evaluation on Power Balance Countermeasure Against Side-Channel Attack on FPGAs Xin Fang, Pei Luo, Yunsi Fei, and Miriam Leeser Electrical & Computer Engineering Department, Northeastern University, Boston
Outline 1. Introduction to Advanced Encryption Standard (AES) Algorithm 2. Introduction to Side Channel Attack (SCA) 3. Power Analysis on AES 4. Countermeasure using WDDL 5. Cons of Wave Dynamic Differential Logic (WDDL) 6. Implementation Improvement by Register Placement 7. Dual Rail Precharge Logic without Early Evaluation (DPL-no. EE) 8. Four Experiments Comparison and Conclusion 2
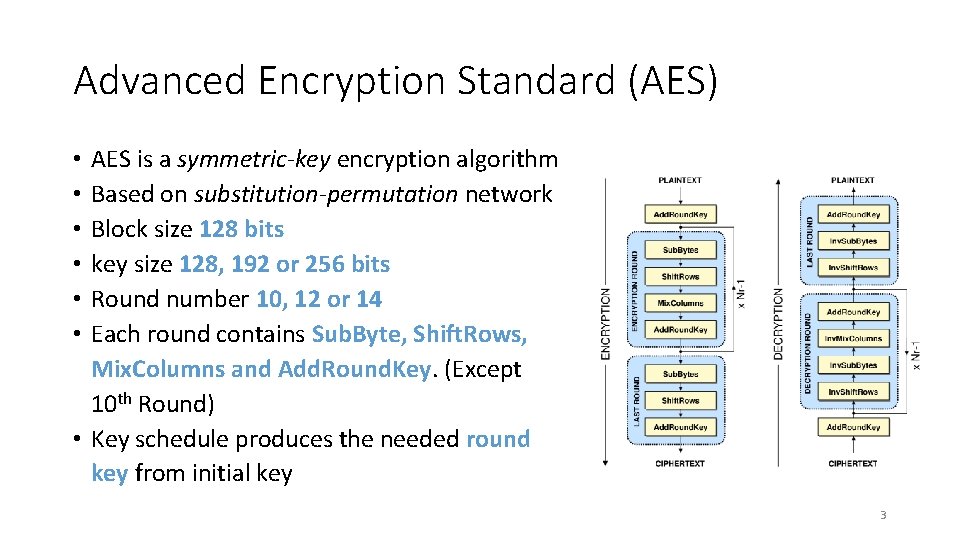
Advanced Encryption Standard (AES) AES is a symmetric-key encryption algorithm Based on substitution-permutation network Block size 128 bits key size 128, 192 or 256 bits Round number 10, 12 or 14 Each round contains Sub. Byte, Shift. Rows, Mix. Columns and Add. Round. Key. (Except 10 th Round) • Key schedule produces the needed round key from initial key • • • 3
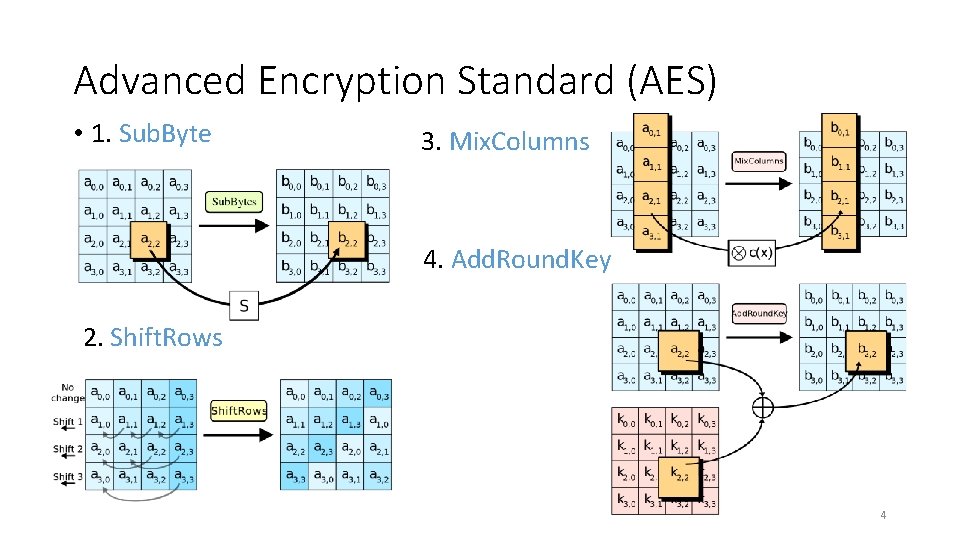
Advanced Encryption Standard (AES) • 1. Sub. Byte 3. Mix. Columns 4. Add. Round. Key 2. Shift. Rows 4
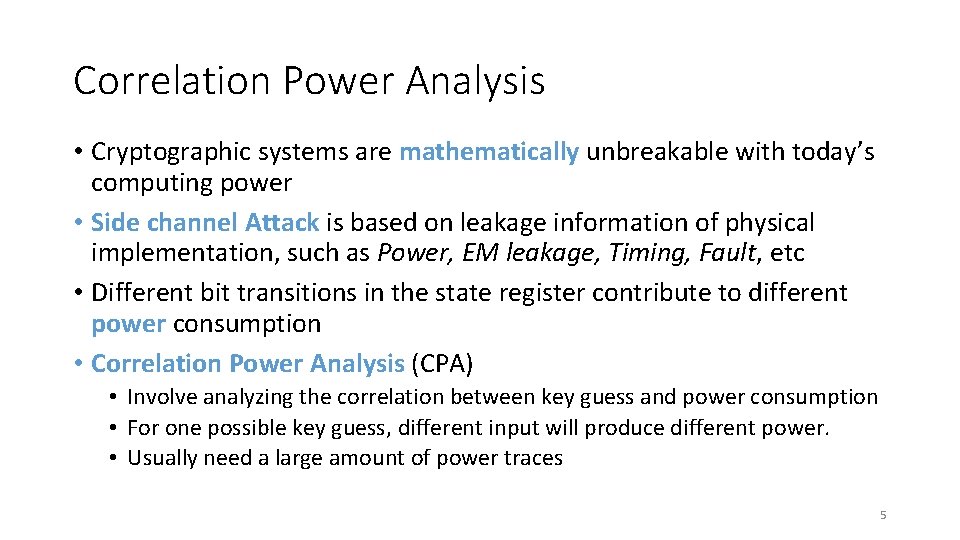
Correlation Power Analysis • Cryptographic systems are mathematically unbreakable with today’s computing power • Side channel Attack is based on leakage information of physical implementation, such as Power, EM leakage, Timing, Fault, etc • Different bit transitions in the state register contribute to different power consumption • Correlation Power Analysis (CPA) • Involve analyzing the correlation between key guess and power consumption • For one possible key guess, different input will produce different power. • Usually need a large amount of power traces 5

Correlation Power Analysis • Example of standard AES power trace • Attack module example: Hamming Distance of the 9 th and 10 th round Step 1: make the assumption for potential 1 byte key guess Step 2: Based on the ciphertext and partial key guess, calculate the output of 9 th round 6
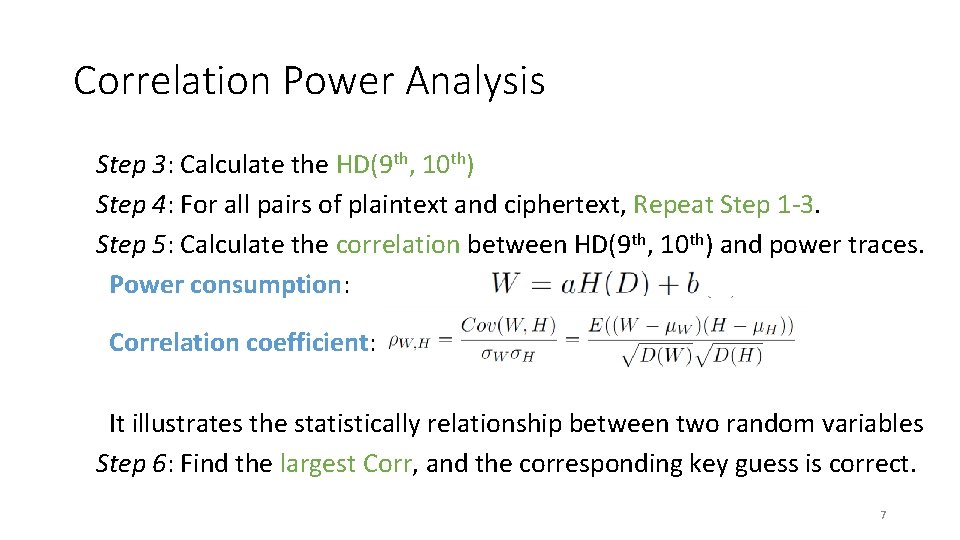
Correlation Power Analysis Step 3: Calculate the HD(9 th, 10 th) Step 4: For all pairs of plaintext and ciphertext, Repeat Step 1 -3. Step 5: Calculate the correlation between HD(9 th, 10 th) and power traces. Power consumption: Correlation coefficient: It illustrates the statistically relationship between two random variables Step 6: Find the largest Corr, and the corresponding key guess is correct. 7
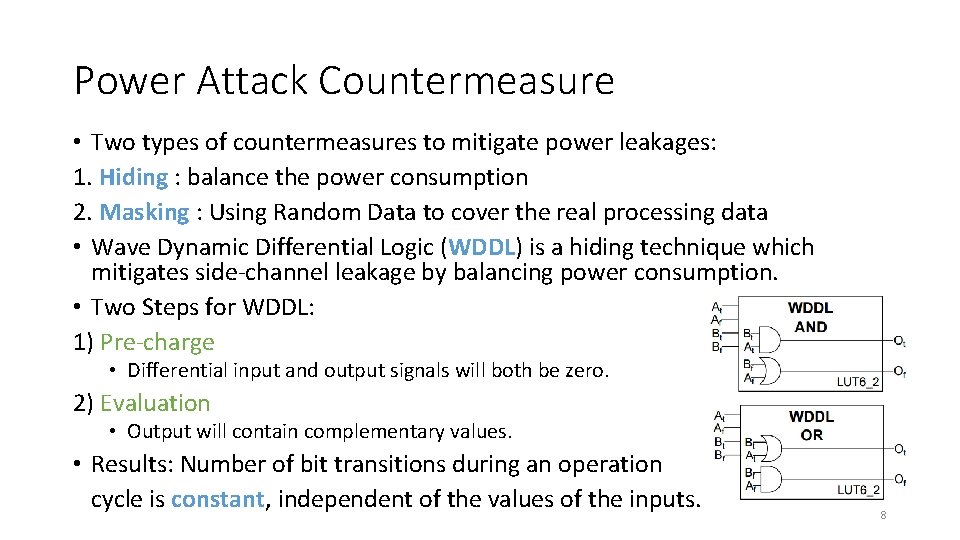
Power Attack Countermeasure • Two types of countermeasures to mitigate power leakages: 1. Hiding : balance the power consumption 2. Masking : Using Random Data to cover the real processing data • Wave Dynamic Differential Logic (WDDL) is a hiding technique which mitigates side-channel leakage by balancing power consumption. • Two Steps for WDDL: 1) Pre-charge • Differential input and output signals will both be zero. 2) Evaluation • Output will contain complementary values. • Results: Number of bit transitions during an operation cycle is constant, independent of the values of the inputs. 8
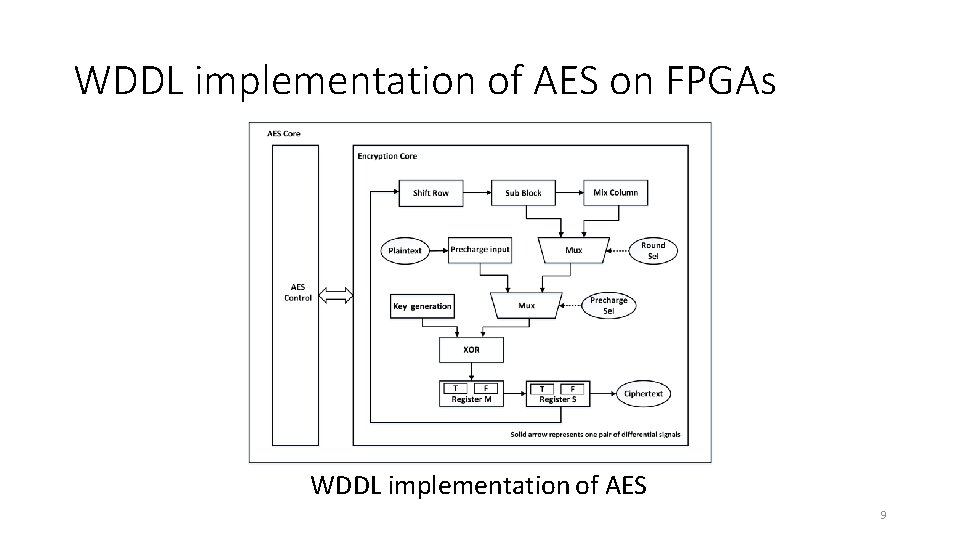
WDDL implementation of AES on FPGAs WDDL implementation of AES 9
Cons of WDDL • WDDL can still leak information • Difference in loading capacitance between two complementary wires can cause unbalanced power leakage • Early evaluation effect • To mitigate the leakage • We propose the placement constraints for registers 10
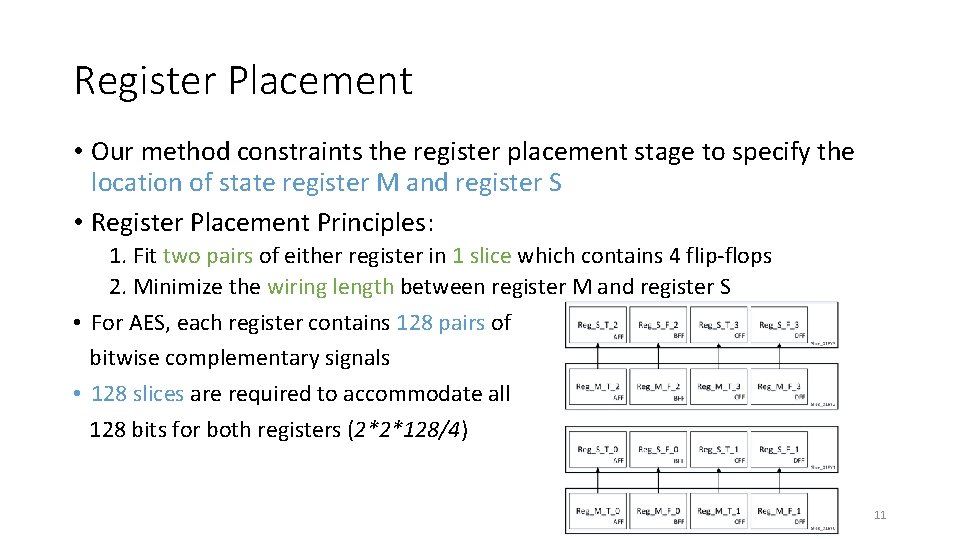
Register Placement • Our method constraints the register placement stage to specify the location of state register M and register S • Register Placement Principles: 1. Fit two pairs of either register in 1 slice which contains 4 flip-flops 2. Minimize the wiring length between register M and register S • For AES, each register contains 128 pairs of bitwise complementary signals • 128 slices are required to accommodate all 128 bits for both registers (2*2*128/4) 11
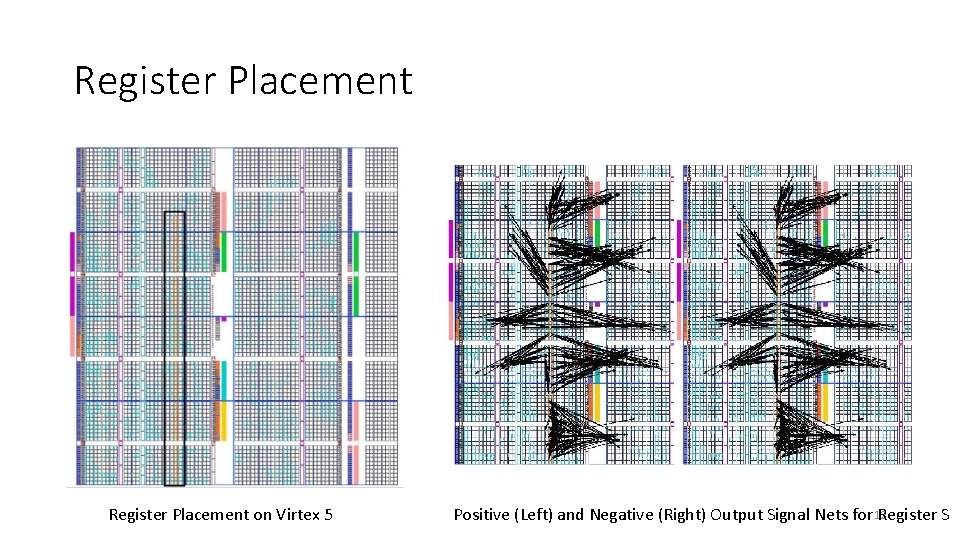
Register Placement on Virtex 5 Positive (Left) and Negative (Right) Output Signal Nets for 12 Register S
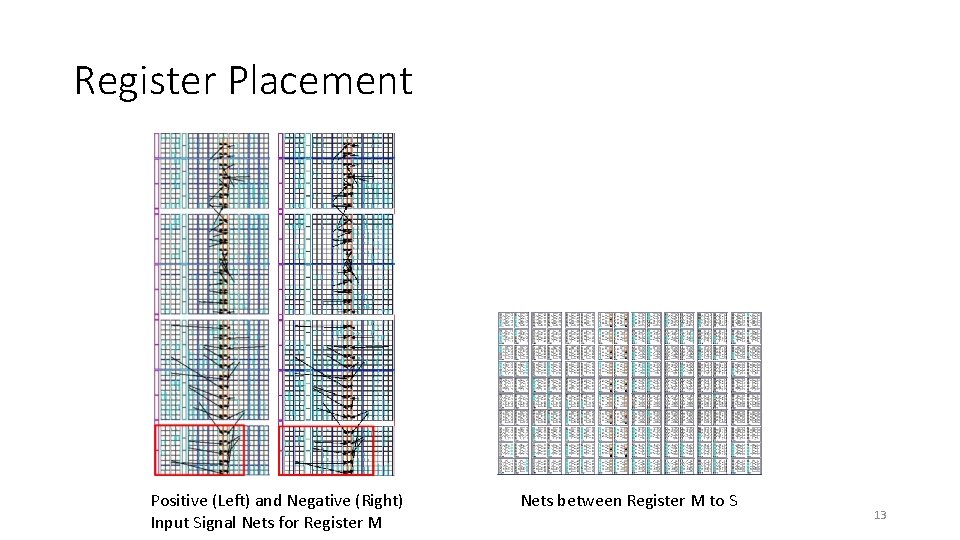
Register Placement Positive (Left) and Negative (Right) Input Signal Nets for Register M Nets between Register M to S 13
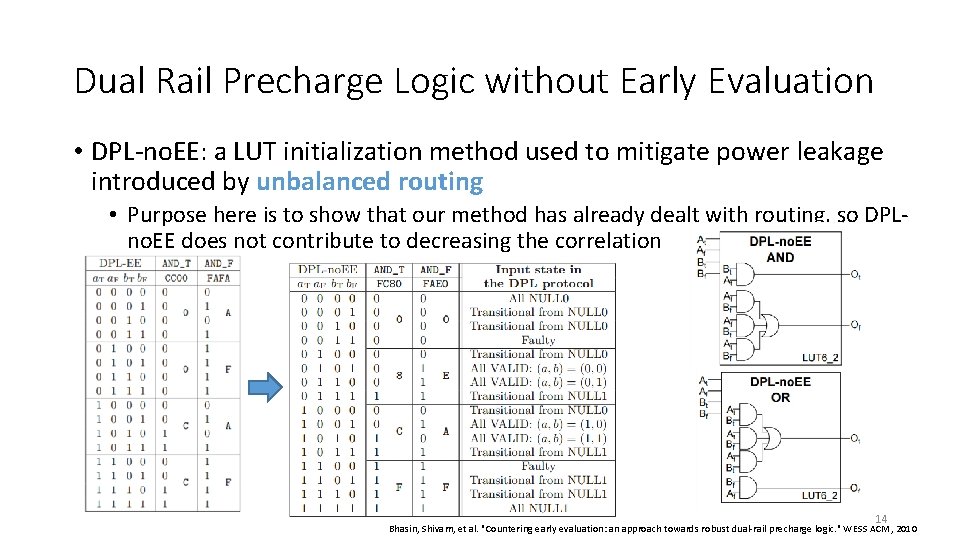
Dual Rail Precharge Logic without Early Evaluation • DPL-no. EE: a LUT initialization method used to mitigate power leakage introduced by unbalanced routing • Purpose here is to show that our method has already dealt with routing, so DPLno. EE does not contribute to decreasing the correlation 14 Bhasin, Shivam, et al. "Countering early evaluation: an approach towards robust dual-rail precharge logic. " WESS ACM, 2010
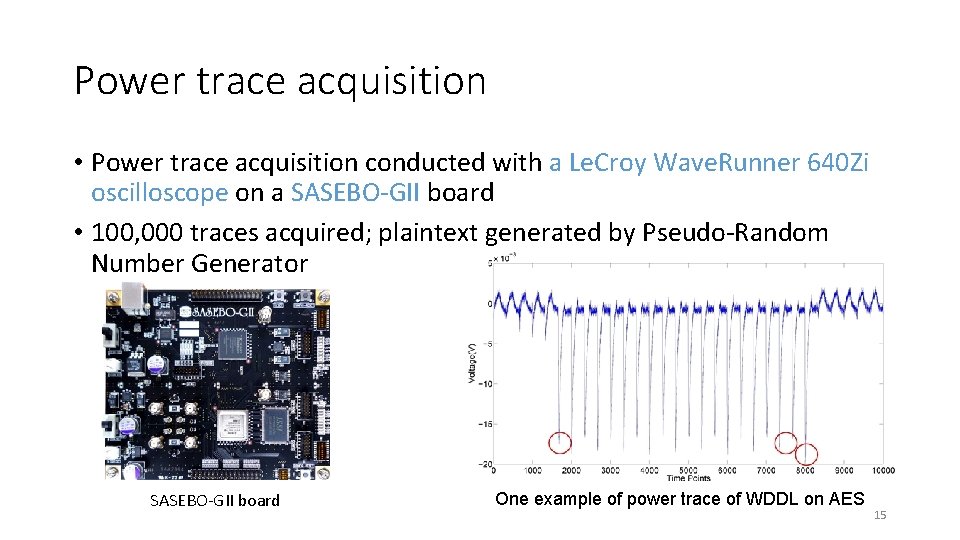
Power trace acquisition • Power trace acquisition conducted with a Le. Croy Wave. Runner 640 Zi oscilloscope on a SASEBO-GII board • 100, 000 traces acquired; plaintext generated by Pseudo-Random Number Generator SASEBO-GII board One example of power trace of WDDL on AES 15
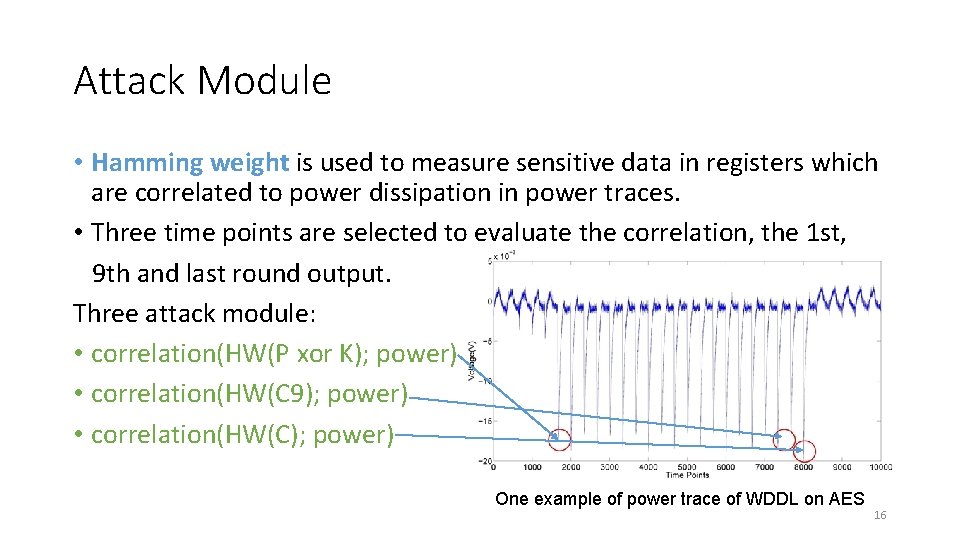
Attack Module • Hamming weight is used to measure sensitive data in registers which are correlated to power dissipation in power traces. • Three time points are selected to evaluate the correlation, the 1 st, 9 th and last round output. Three attack module: • correlation(HW(P xor K); power) • correlation(HW(C 9); power) • correlation(HW(C); power) One example of power trace of WDDL on AES 16
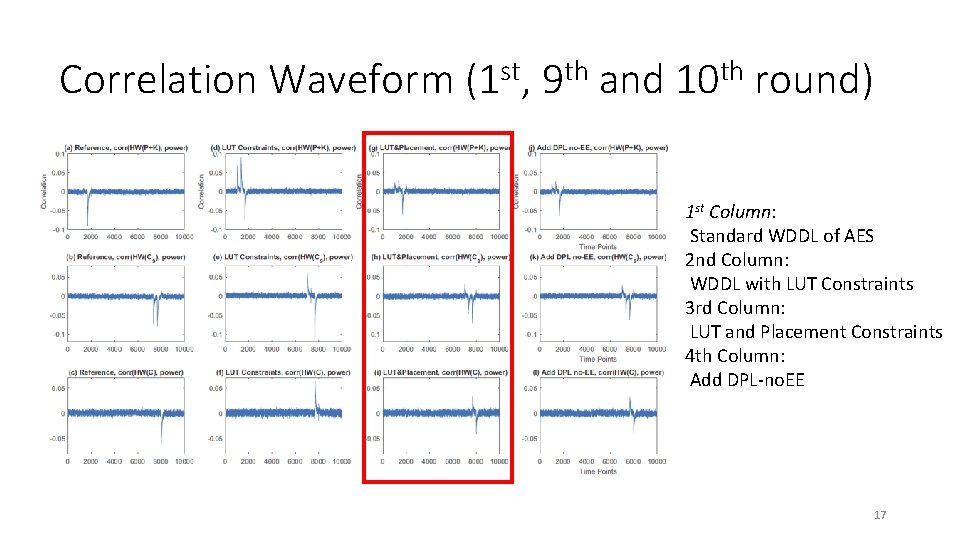
Correlation Waveform (1 st, 9 th and 10 th round) 1 st Column: Standard WDDL of AES 2 nd Column: WDDL with LUT Constraints 3 rd Column: LUT and Placement Constraints 4 th Column: Add DPL-no. EE 17
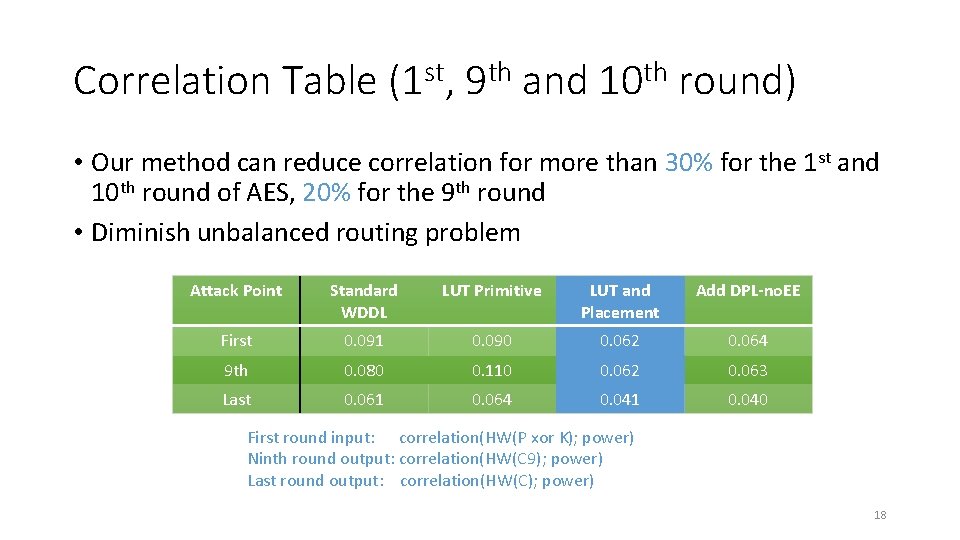
Correlation Table (1 st, 9 th and 10 th round) • Our method can reduce correlation for more than 30% for the 1 st and 10 th round of AES, 20% for the 9 th round • Diminish unbalanced routing problem Attack Point Standard WDDL LUT Primitive LUT and Placement Add DPL-no. EE First 0. 091 0. 090 0. 062 0. 064 9 th 0. 080 0. 110 0. 062 0. 063 Last 0. 061 0. 064 0. 041 0. 040 First round input: correlation(HW(P xor K); power) Ninth round output: correlation(HW(C 9); power) Last round output: correlation(HW(C); power) 18
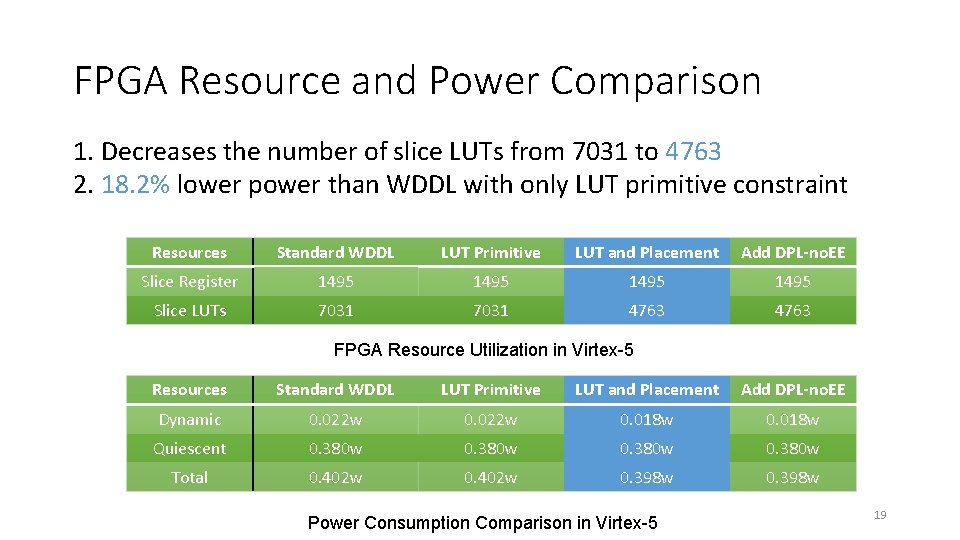
FPGA Resource and Power Comparison 1. Decreases the number of slice LUTs from 7031 to 4763 2. 18. 2% lower power than WDDL with only LUT primitive constraint Resources Standard WDDL LUT Primitive LUT and Placement Add DPL-no. EE Slice Register 1495 Slice LUTs 7031 4763 FPGA Resource Utilization in Virtex-5 Resources Standard WDDL LUT Primitive LUT and Placement Add DPL-no. EE Dynamic 0. 022 w 0. 018 w Quiescent 0. 380 w Total 0. 402 w 0. 398 w Power Consumption Comparison in Virtex-5 19
Conclusions • A methodology of generating register constraints to improve the WDDL implementation on a Virtex 5 FPGA • Evaluate it using the standard AES algorithm • Significantly reduce power leakage • Save FPGA resource and decrease power consumption 20
Thank you! • Acknowledgments: • This work is supported in part by NSF under MRI-1337854. • Thank you to Xilinx for their donations. • Xin Fang, fang. xi@husky. neu. edu • RCL website: http: //www. coe. neu. edu/Research/rcl/index. php 21
- Slides: 21