LEADERS EDGE Cyber Intelligence Fighting Cyber Crime Insert

LEADERS EDGE Cyber Intelligence Fighting Cyber Crime Insert Event Date © Copyright 2013 EMC Corporation. All rights reserved. 2
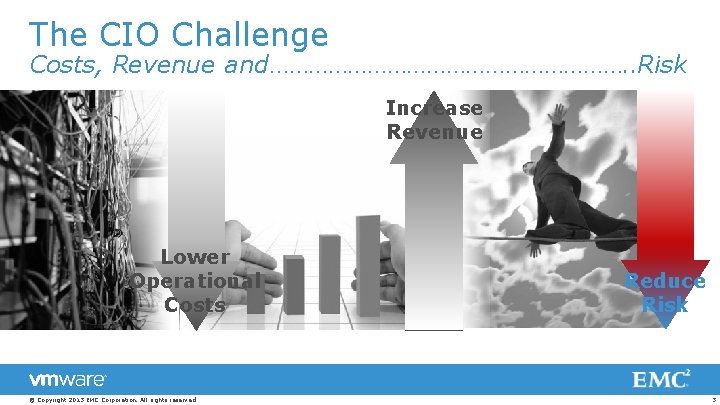
The CIO Challenge Costs, Revenue and………………………. . Risk Increase Revenue Lower Operational Costs © Copyright 2013 EMC Corporation. All rights reserved. Reduce Risk 3
The CIO Challenge Risk Align with Business Assess and Manage Threats Build Trusted Infrastructure © Copyright 2013 EMC Corporation. All rights reserved. 4

Threats Used to Be Simple TRADITIONAL ATTACKS FOCUS ON INTRUSION © Copyright 2013 EMC Corporation. All rights reserved. TRADITIONAL DEFENSES FOCUS ON PREVENTION 5
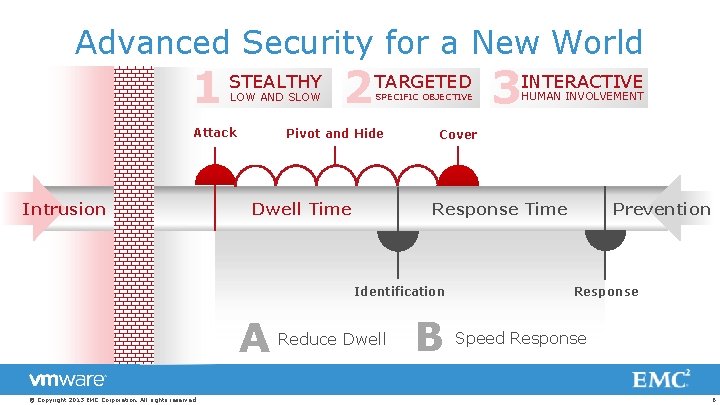
Advanced Security for a New World 1 STEALTHY 2 TARGETED 3 INTERACTIVE LOW AND SLOW Attack Intrusion SPECIFIC OBJECTIVE Pivot and Hide Dwell Time Cover Response Time Identification A © Copyright 2013 EMC Corporation. All rights reserved. HUMAN INVOLVEMENT Reduce Dwell B Prevention Response Speed Response 6
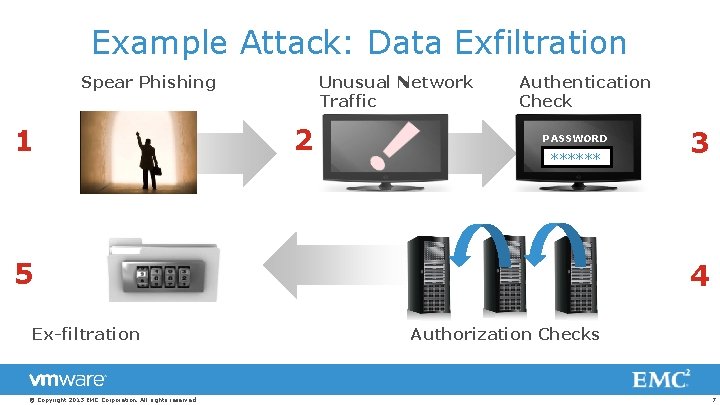
Example Attack: Data Exfiltration Spear Phishing 1 Unusual Network Traffic 2 Authentication Check PASSWORD ****** 5 Ex-filtration © Copyright 2013 EMC Corporation. All rights reserved. 3 4 Authorization Checks 7
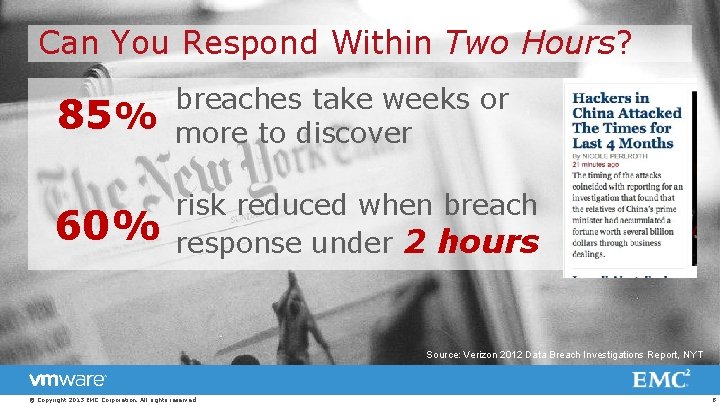
Can You Respond Within Two Hours? 85% breaches take weeks or more to discover 60% risk reduced when breach response under 2 hours Source: Verizon 2012 Data Breach Investigations Report, NYT © Copyright 2013 EMC Corporation. All rights reserved. 8
Threats Today Require a New Approach Proprietary and Confidential To Silver Tail Systems © Copyright 2013 EMC Corporation. All rights reserved. 9
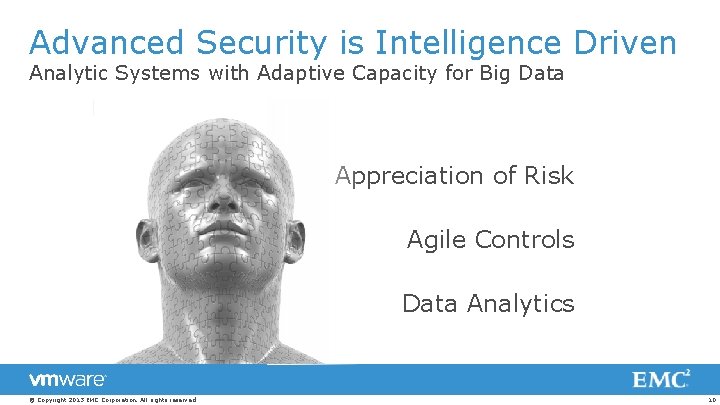
Advanced Security is Intelligence Driven Analytic Systems with Adaptive Capacity for Big Data Appreciation of Risk Agile Controls Data Analytics © Copyright 2013 EMC Corporation. All rights reserved. 10
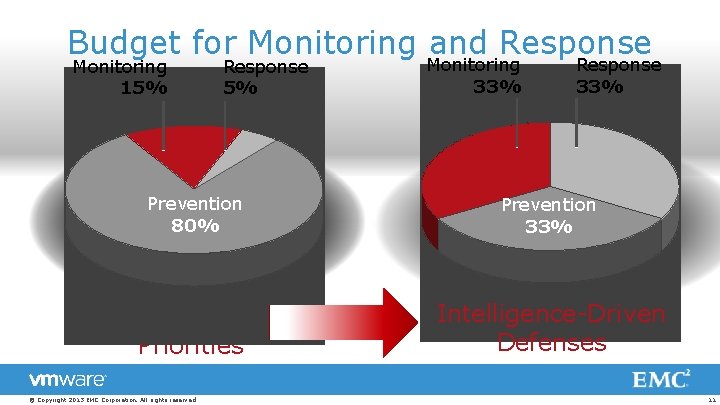
Budget for Monitoring and Response Monitoring 15% Response 5% Monitoring 33% Response 33% Prevention 80% Prevention 33% Today’s Priorities Intelligence-Driven Defenses © Copyright 2013 EMC Corporation. All rights reserved. 11
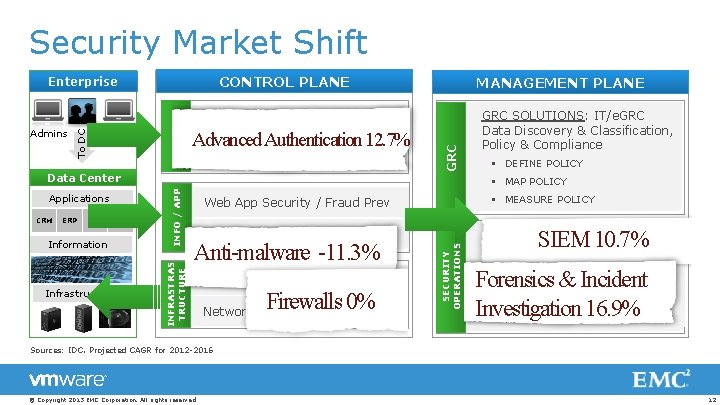
Security Market Shift CONTROL PLANE Advanced Authentication 12. 7% Authentication & Access Mgmt *** Information Infrastructure INFO / APP BI GRC SOLUTIONS: IT/e. GRC Data Discovery & Classification, Policy & Compliance § DEFINE POLICY § MAP POLICY INFRASTRAS TRUCTURE ERP ITaa. S Management CRM GRC Identity Mgmt & Governance Data Center Applications MANAGEMENT PLANE § MEASURE POLICY Web App Security / Fraud Prev Encryption/DLP/IRM Anti-malware -11. 3% Endpoint Controls Firewalls 0% Network / Messaging Controls SECURITY OPERATIONS Users To DC Admins IDENTITY Enterprise SIEM 10. 7% SIEM, Network and Endpoint Forensics & Incident Invest. , Advanced Analytics Forensics & Incident § DETECT Potential Threats § INVESTIGATE Attacks Investigation 16. 9% § RESPOND To Attacks Sources: IDC. Projected CAGR for 2012 -2016 © Copyright 2013 EMC Corporation. All rights reserved. 12
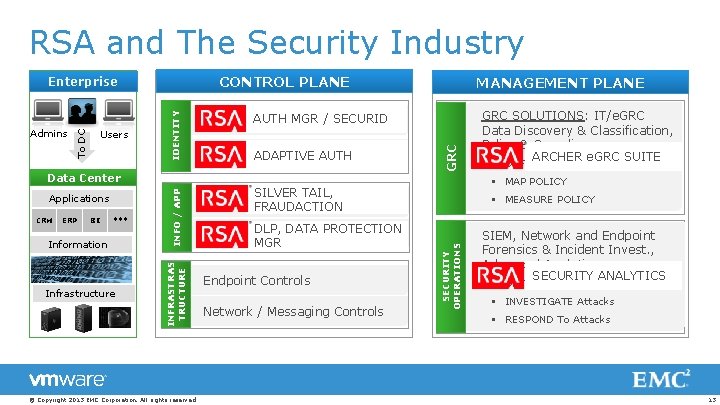
RSA and The Security Industry CONTROL PLANE CRM ERP ITaa. S Management Applications BI *** Information Infrastructure INFRASTRAS TRUCTURE Data Center © Copyright 2013 EMC Corporation. All rights reserved. DLP, DATA PROTECTION Encryption/DLP/IRM MGR Endpoint Controls Network / Messaging Controls GRC SILVER TAIL, Web App. FRAUDACTION Security / Fraud Prev Authentication & Access ADAPTIVE AUTHMgmt MANAGEMENT PLANE GRC SOLUTIONS: IT/e. GRC Data Discovery & Classification, Policy & Compliance ARCHER e. GRC SUITE § DEFINE POLICY § MAP POLICY § MEASURE POLICY SECURITY OPERATIONS IDENTITY Users To DC Admins / SECURID Identity AUTH Mgmt MGR & Governance INFO / APP Enterprise SIEM, Network and Endpoint Forensics & Incident Invest. , Advanced Analytics SECURITY ANALYTICS § DETECT Potential Threats § INVESTIGATE Attacks § RESPOND To Attacks 13
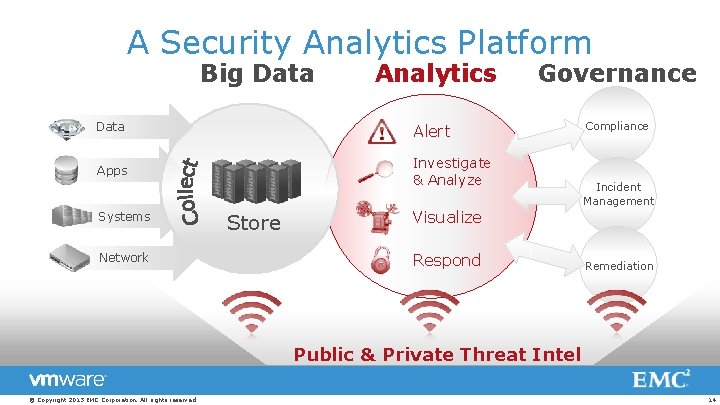
A Security Analytics Platform Big Data Analytics Data Alert Apps Investigate & Analyze Systems Network Store Governance Visualize Respond Compliance Incident Management Remediation Public & Private Threat Intel © Copyright 2013 EMC Corporation. All rights reserved. 14

Discussion Topic Are Security Analytics within your team’s current capabilities? What is your approach? © Copyright 2013 EMC Corporation. All rights reserved. 15
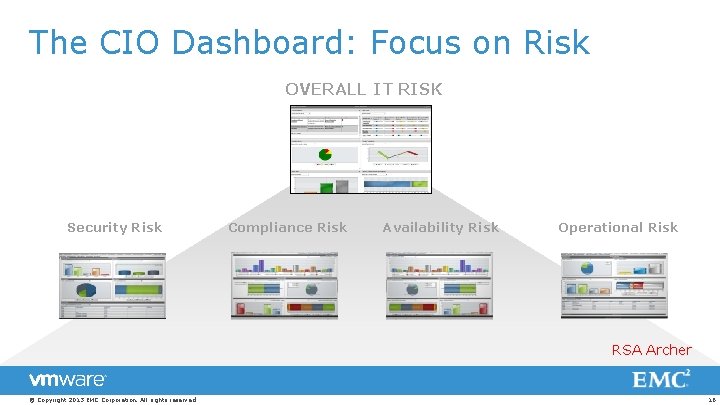
The CIO Dashboard: Focus on Risk OVERALL IT RISK Security Risk Compliance Risk Availability Risk Operational Risk RSA Archer © Copyright 2013 EMC Corporation. All rights reserved. 16
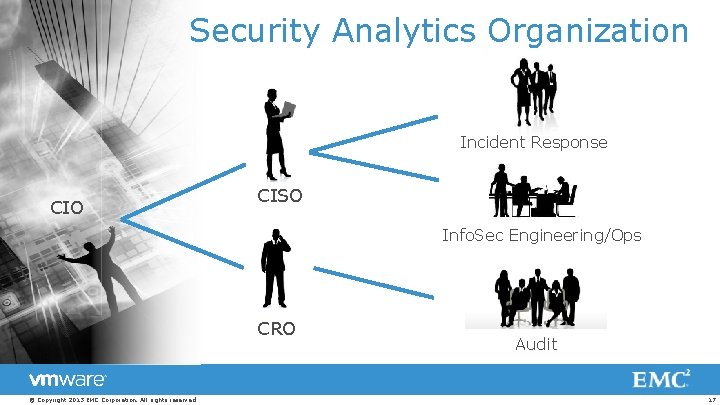
Security Analytics Organization Incident Response CIO CISO Info. Sec Engineering/Ops CRO © Copyright 2013 EMC Corporation. All rights reserved. Audit 17
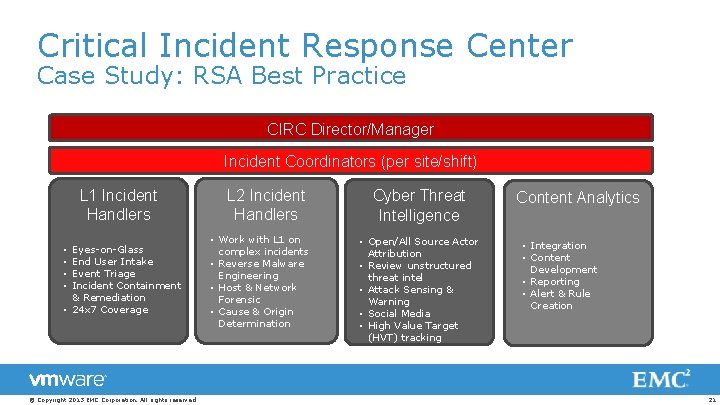
Critical Incident Response Center Case Study: RSA Best Practice CIRC Director/Manager Incident Coordinators (per site/shift) L 1 Incident Handlers Eyes-on-Glass End User Intake Event Triage Incident Containment & Remediation • 24 x 7 Coverage • • © Copyright 2013 EMC Corporation. All rights reserved. L 2 Incident Handlers • Work with L 1 on complex incidents • Reverse Malware Engineering • Host & Network Forensic • Cause & Origin Determination Cyber Threat Intelligence • Open/All Source Actor Attribution • Review unstructured threat intel • Attack Sensing & Warning • Social Media • High Value Target (HVT) tracking Content Analytics • Integration • Content Development • Reporting • Alert & Rule Creation 21

Discussion Topic How does your Security and GRC organization compare to this model? What do you expect from your CSO/CISO? © Copyright 2013 EMC Corporation. All rights reserved. 22
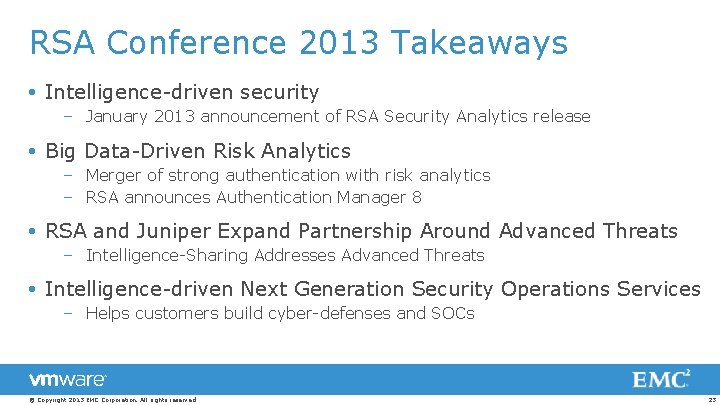
RSA Conference 2013 Takeaways Intelligence-driven security – January 2013 announcement of RSA Security Analytics release Big Data-Driven Risk Analytics – Merger of strong authentication with risk analytics – RSA announces Authentication Manager 8 RSA and Juniper Expand Partnership Around Advanced Threats – Intelligence-Sharing Addresses Advanced Threats Intelligence-driven Next Generation Security Operations Services – Helps customers build cyber-defenses and SOCs © Copyright 2013 EMC Corporation. All rights reserved. 23
RSA and EMC Resources RSA Blog EMC CIO Connect © Copyright 2013 EMC Corporation. All rights reserved. RSA Security Briefs RSA Features EMC Product Security 24

Industry Resources 2012 Data Breach Investigations Report (DBIR) http: //www. verizonenterprise. com/resources/reports/rp_data-breachinvestigations-report-2012 -ebk_en_xg. pdf 2013 Global Security Report https: //www 2. trustwave. com/2013 GSR. html Security Intel Analysis/Internet Threat Research http: //www. trendmicro. com/us/security-intelligence/index. html 2013 Security Threat Report http: //www. sophos. com/en-us/security-news-trends/reports/securitythreat-report. aspx Security Bulletin 2012 http: //www. securelist. com/en/analysis/204792254/Kaspersky_S ecurity_Bulletin_2012_Malware_Evolution Threat Report 2012 http: //www. fsecure. com/static/doc/labs_global/Research/Threat_Report_H 2_2012. pdf © Copyright 2013 EMC Corporation. All rights reserved. 25

IS WHERE SECURITY MEETS BIG DATA Intelligence-Driven Security SOC | GRC | Identity | Anti-Fraud © Copyright 2013 EMC Corporation. All rights reserved. 26

Thank You © Copyright 2013 EMC Corporation. All rights reserved. 27

- Slides: 25