LDAP Directory Services Security Directory Security Syllabus Brief
LDAP Directory Services: Security
Directory Security Syllabus · · · · Brief Review of Directories and LDAP Brief Review of Security Basic Security Concepts Security as Applied to Directories · Threats LDAP Protocol Security Features Typically Implemented Security Features Futures References
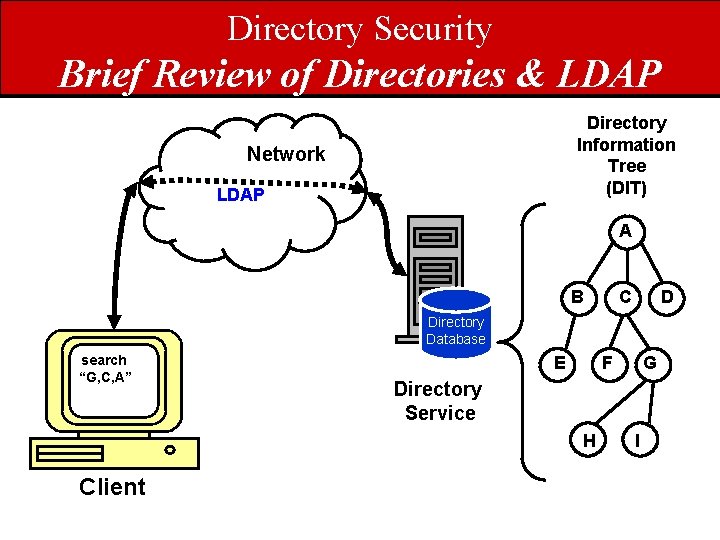
Directory Security Brief Review of Directories & LDAP Directory Information Tree (DIT) Network LDAP A B C D Directory Database search “G, C, A” E F Directory Service H Client G I
Directory Security Brief Review of Directories & LDAP • What directories are… – Object repositories – Typically read more than written – Have explicit access protocols – Support relatively complex queries • What directories are not… – RDBMSs – Lack notions of. . • Tabular views • JOIN operations • Stored Procedures
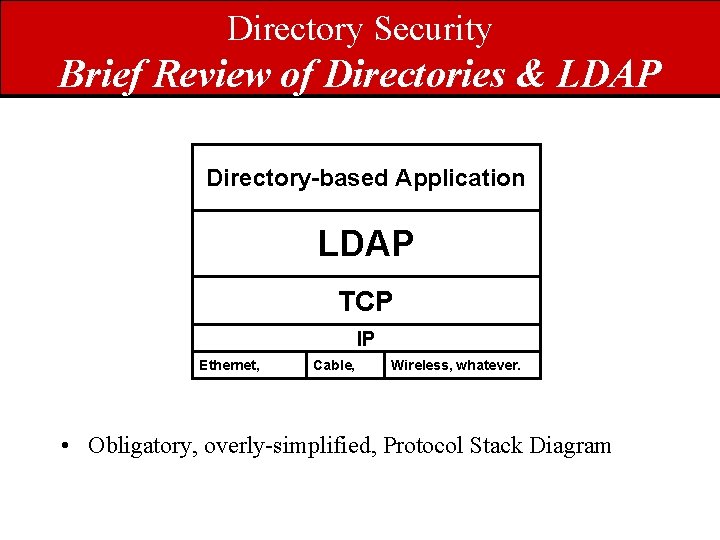
Directory Security Brief Review of Directories & LDAP Directory-based Application LDAP TCP IP Ethernet, Cable, Wireless, whatever. • Obligatory, overly-simplified, Protocol Stack Diagram
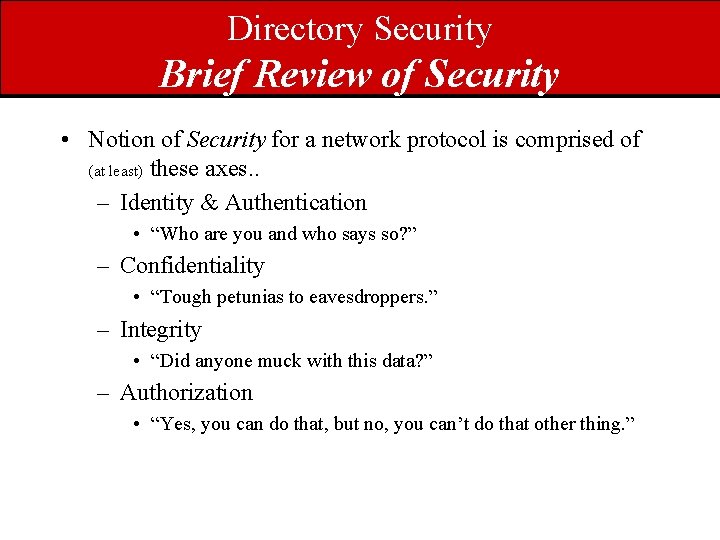
Directory Security Brief Review of Security • Notion of Security for a network protocol is comprised of (at least) these axes. . – Identity & Authentication • “Who are you and who says so? ” – Confidentiality • “Tough petunias to eavesdroppers. ” – Integrity • “Did anyone muck with this data? ” – Authorization • “Yes, you can do that, but no, you can’t do that other thing. ”
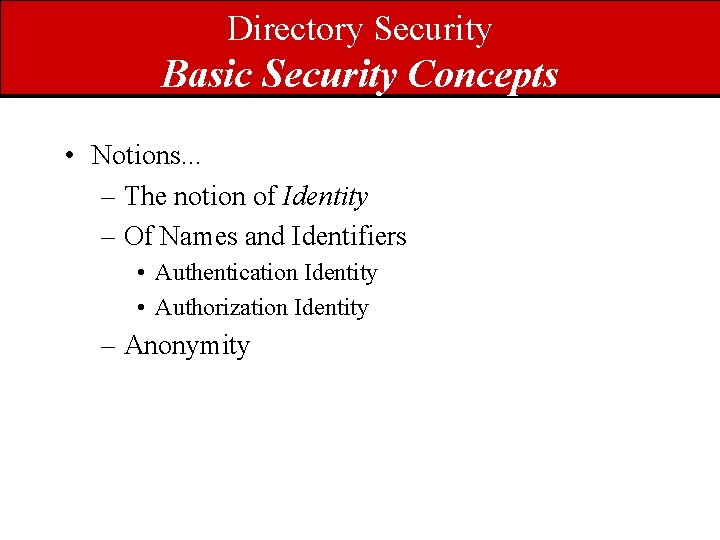
Directory Security Basic Security Concepts • Notions. . . – The notion of Identity – Of Names and Identifiers • Authentication Identity • Authorization Identity – Anonymity
Directory Security Basic Security Concepts Overall Namespace Names Identifiers
Directory Security Basic Security Concepts • The applicable “science & technology of implementation”. . . – Ciphers – Encryption – Integrity • AKA Cryptography [11]
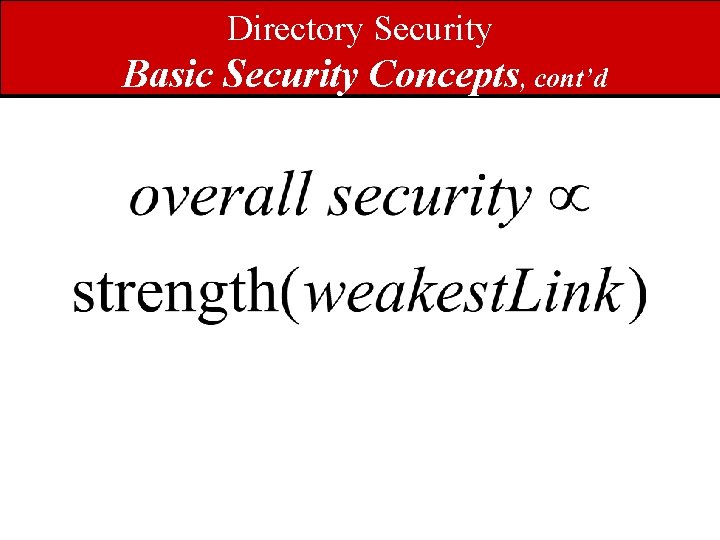
Directory Security Basic Security Concepts, cont’d

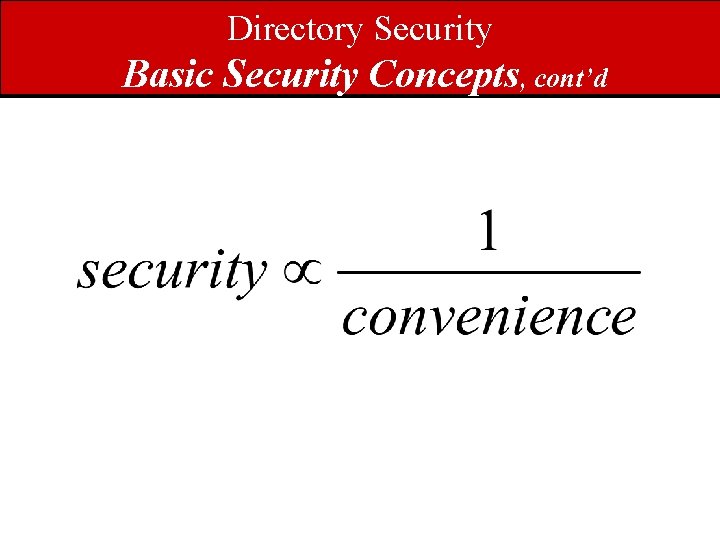
Directory Security Basic Security Concepts, cont’d
Directory Security Basic Security Concepts, cont’d
Directory Security as Applied to Directories • One needs to separately consider each of the four security axes in the context of anticipated threats. • Also need to consider security from the perspectives of. . – the info stored in the directory, and. . – attributes of the requesters. • E. g. how much you trust them. • Note that. . – data security != access security
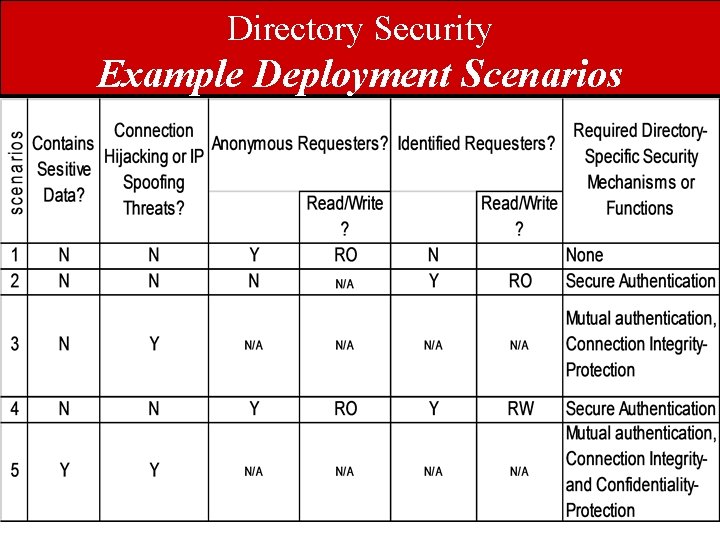
Directory Security Example Deployment Scenarios
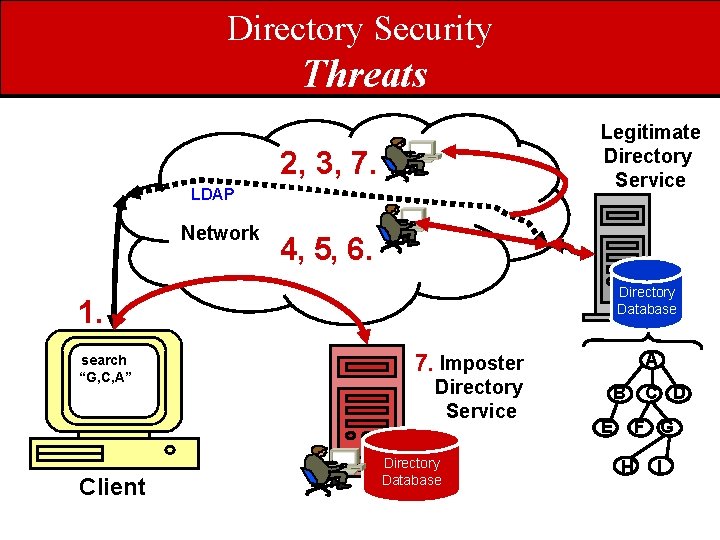
Directory Security Threats Legitimate Directory Service 2, 3, 7. LDAP Network 4, 5, 6. Directory Database 1. search “G, C, A” Client 7. Imposter Directory Service Directory Database A B E C D F G H I
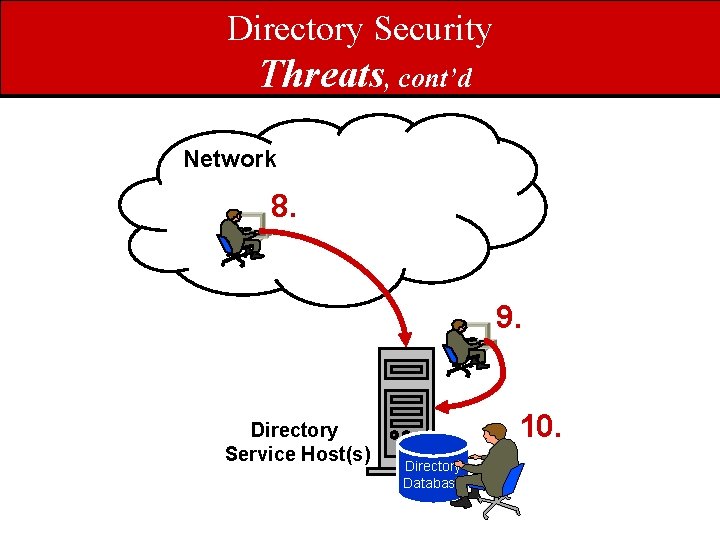
Directory Security Threats, cont’d Network 8. 9. Directory Service Host(s) 10. Directory Database
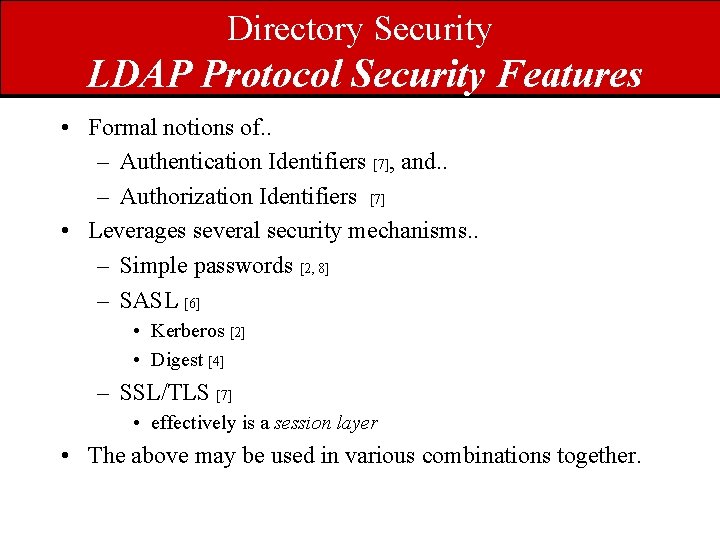
Directory Security LDAP Protocol Security Features • Formal notions of. . – Authentication Identifiers [7], and. . – Authorization Identifiers [7] • Leverages several security mechanisms. . – Simple passwords [2, 8] – SASL [6] • Kerberos [2] • Digest [4] – SSL/TLS [7] • effectively is a session layer • The above may be used in various combinations together.
Directory Security LDAP Protocol Security Features • Integral-to-the-protocol data integrity and attribution are works-in-progress.
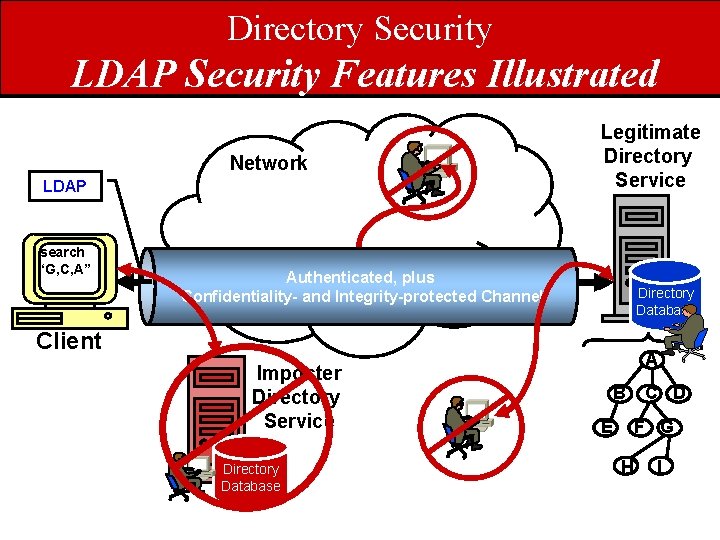
Directory Security LDAP Security Features Illustrated Network LDAP search “G, C, A” Legitimate Directory Service Authenticated, plus Confidentiality- and LDAP Integrity-protected Channel Directory Database Client Imposter Directory Service Directory Database A B E C D F G H I
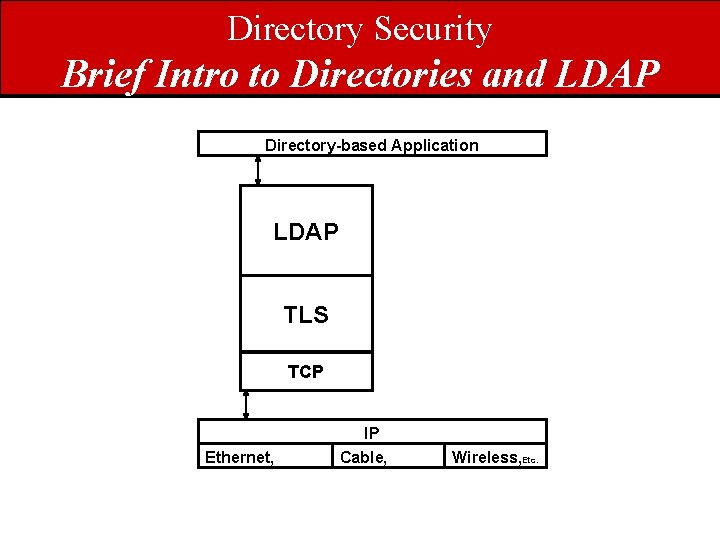
Directory Security Brief Intro to Directories and LDAP Directory-based Application LDAP TLS TCP IP Ethernet, Cable, Wireless, Etc.
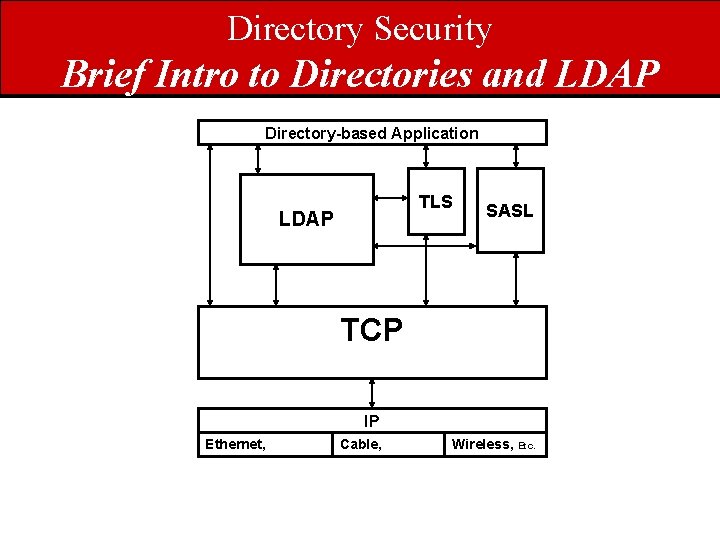
Directory Security Brief Intro to Directories and LDAP Directory-based Application TLS LDAP SASL TCP IP Ethernet, Cable, Wireless, Etc.
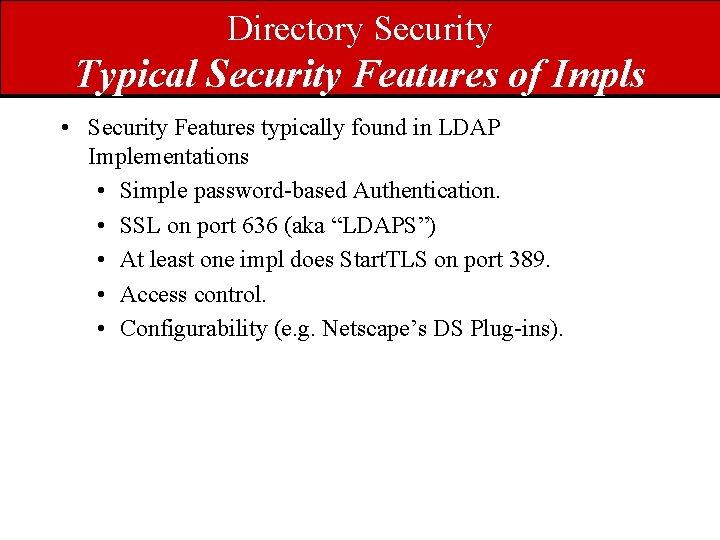
Directory Security Typical Security Features of Impls • Security Features typically found in LDAP Implementations • Simple password-based Authentication. • SSL on port 636 (aka “LDAPS”) • At least one impl does Start. TLS on port 389. • Access control. • Configurability (e. g. Netscape’s DS Plug-ins).
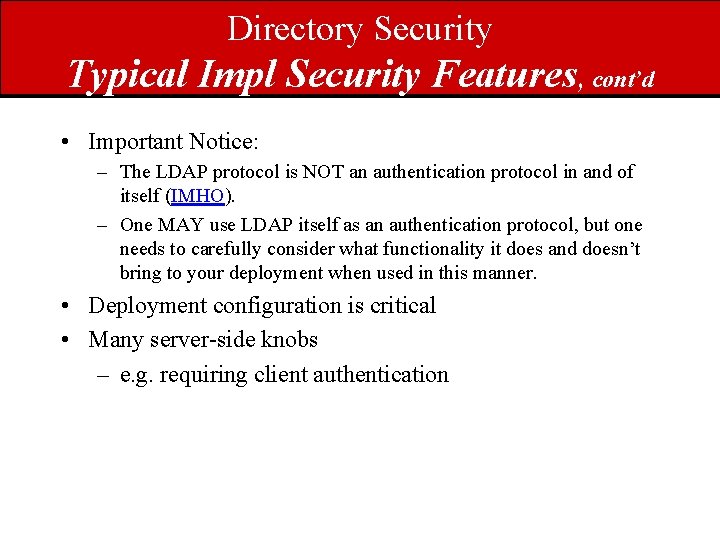
Directory Security Typical Impl Security Features, cont’d • Important Notice: – The LDAP protocol is NOT an authentication protocol in and of itself (IMHO). – One MAY use LDAP itself as an authentication protocol, but one needs to carefully consider what functionality it does and doesn’t bring to your deployment when used in this manner. • Deployment configuration is critical • Many server-side knobs – e. g. requiring client authentication
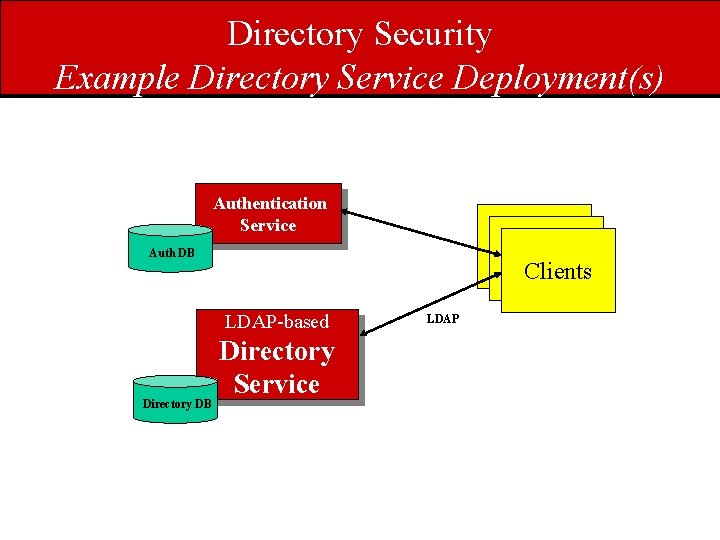
Directory Security Example Directory Service Deployment(s) Authentication Service Desktop Clients Auth DB LDAP-based Directory DB Directory Service LDAP
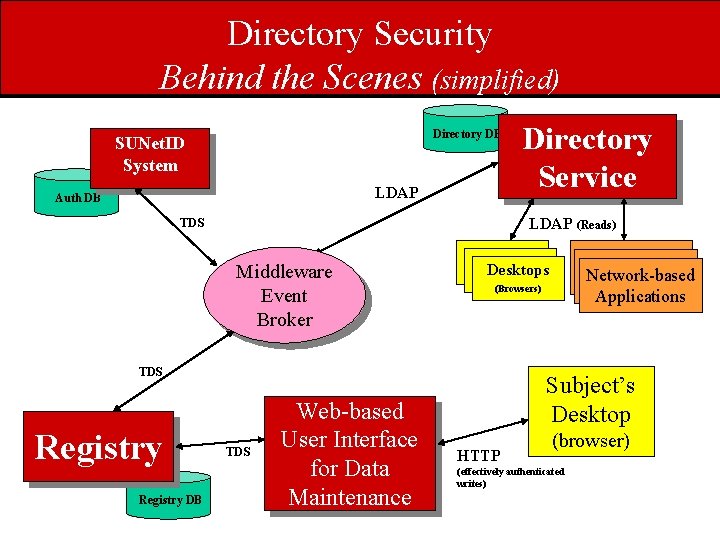
Directory Security Behind the Scenes (simplified) Directory DB SUNet. ID System LDAP Auth DB LDAP (Reads) TDS Middleware Event Broker Registry DB TDS Web-based User Interface for Data Maintenance Network-based Applications Desktops (Browsers) TDS Registry Directory Service Subject’s Desktop HTTP (browser) (effectively authenticated writes)
- Slides: 25