Lby V and Lby R Henning Schulzrinne Definition
Lby. V and Lby. R Henning Schulzrinne
Definition • Lby. R – Consumers (recipients) of location information resolves URL and obtains location value • Lby. V – Target (or proxy) inserts & delivers location value to all or some consumers in signaling path • Lby. V-plain: as-is – accessibility the same as carrying protocol (say, SIP) • Lby. V-SMIME: encapsulated in S/MIME – Targeted to one (logical) receiver
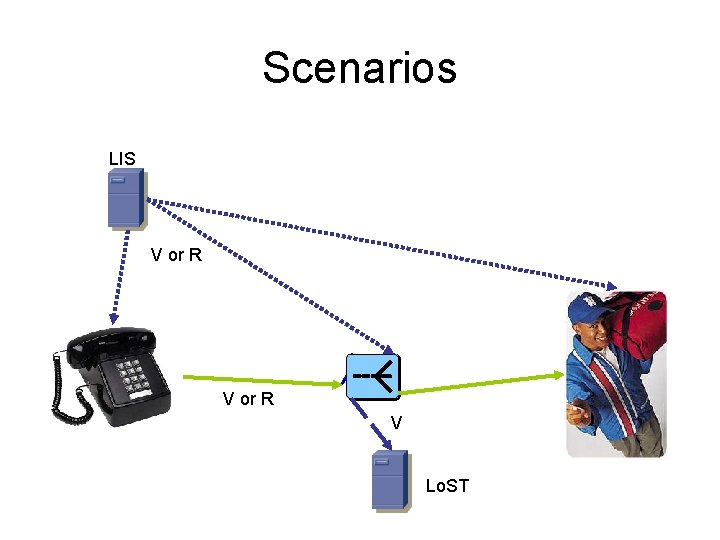
Scenarios LIS V or R V Lo. ST
Issues • • Insertion Updates if target moving Size/overhead Mid-stream insertion Privacy policies Reliability Security – Encryption – Integrity
Insertion • Lby. V – Can be inserted by end system – Can be inserted by proxy • Via data: URL in header • Lby. R – Same • Via header addition • Same issues for privacy policies
Privacy policies • Whenever LO is generated by third party, unclear how in-band privacy policies are configured – generator may not know intended use (pizza delivery vs. emergency call) • Issue for Lby. R or Lby. V proxy-insertion – may be solvable by configuration mechanism
Updates for moving targets • Lby. V – Target has to push (UPDATE, re-INVITE) • But it knows when location has changed significantly • May be difficult if inserted by proxy • Lby. R – Receiver polls LIS or subscribes to LIS or target • Polling: may not know when location is changing
Reliability • Lby. R – Recipient needs protocol transaction to get LO – Thus, two points of failure • Impact on reliability depends on relative failure probabilities of the two parts • Lby. V – “fate sharing”: no signaling without location – Thus, one point of failure
Overhead • LIS likely close to target • Details depend on assumptions – Cost of one hop is constant or distance-dependent • Lby. R: Each retrieval one additional protocol exchange – With headers, TCP setup, TLS, as applicable • Lby. V: – Additional LO in message
Access control • Lby. R – Anybody who has access to reference – Unless • desired recipient has a security relationship with LIS AND • rule maker can access authorization upload policies to LIS • Lby. V – Anybody who has access to value – Unless • Target can encrypt value for recipient – Single target: S/MIME, encrypted with recipient’s public key
- Slides: 10