Lawful Interception in 3 G IP Multimedia Subsystem
Lawful Interception in 3 G IP Multimedia Subsystem Author: Toni Mäki, Nokia Networks, toni. maki@nokia. com Supervisor: Prof. Raimo Kantola
Agenda • • • Network Architectures Lawful interception Goals of thesis Capturing the signalling Capturing the user data Correlating the signalling and user data
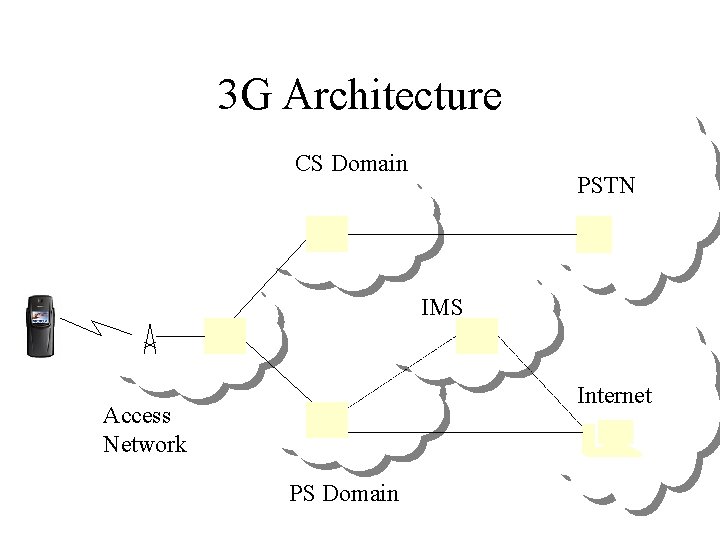
3 G Architecture CS Domain PSTN IMS Internet Access Network PS Domain
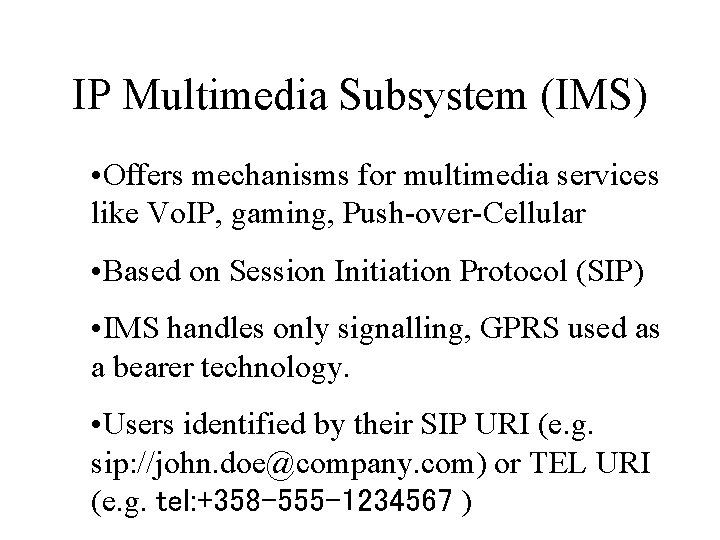
IP Multimedia Subsystem (IMS) • Offers mechanisms for multimedia services like Vo. IP, gaming, Push-over-Cellular • Based on Session Initiation Protocol (SIP) • IMS handles only signalling, GPRS used as a bearer technology. • Users identified by their SIP URI (e. g. sip: //john. doe@company. com) or TEL URI (e. g. tel: +358 -555 -1234567 )
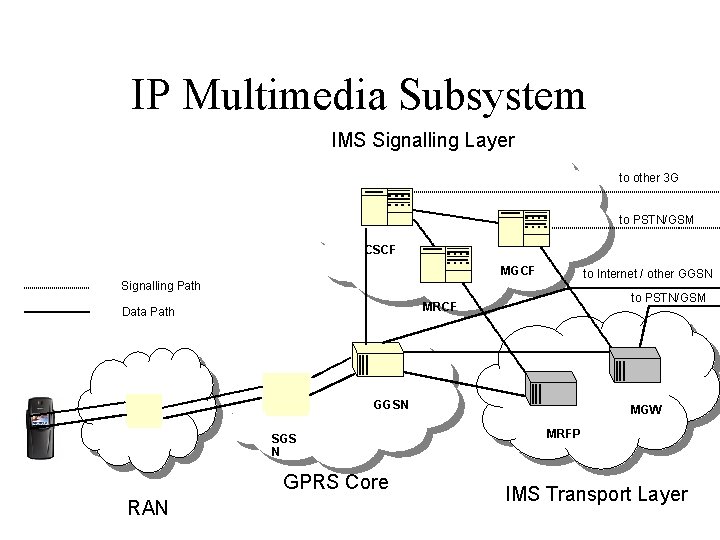
IP Multimedia Subsystem IMS Signalling Layer to other 3 G to PSTN/GSM CSCF MGCF to Internet / other GGSN Signalling Path to PSTN/GSM MRCF Data Path GGSN SGS N GPRS Core RAN MGW MRFP IMS Transport Layer
Lawful Interception • Authorities capture the communications of certain users in order to tackle criminal activity • Ability to perform lawful interception may be a precondition for a licence to operate telecommunications network • Lawful interception is a very delicate issue. • IRI (Interception Related Information) contains signalling, interception activation statuses, etc… • CC (Content of Communications) contains the actual communications transmitted or received
Lawful Interception in GPRS • The packet traffic of a user is tunnelled over the GPRS network to the Internet. • These tunnels are recognised and captured in lawful interception for GPRS. All the tunnels of targeted user are delivered to authorities. • All the GPRS signalling related to monitored user is captured (e. g. network attach, tunnel creation etc…) • Lawful interception in GPRS is based on traditional GSM user identifiers (IMSI, MSISDN, IMEI)
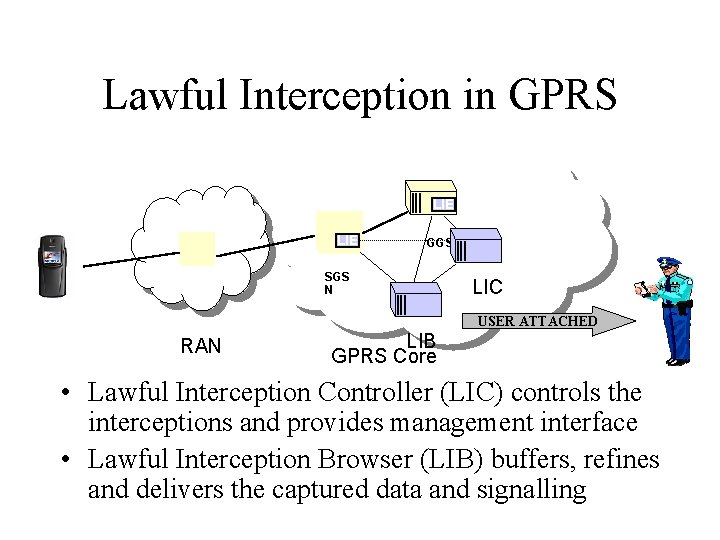
Lawful Interception in GPRS LIE GGSN SGS N LIC USER ATTACHED RAN LIB GPRS Core • Lawful Interception Controller (LIC) controls the interceptions and provides management interface • Lawful Interception Browser (LIB) buffers, refines and delivers the captured data and signalling
Goals of Thesis • Design/refine the interception of IMS related IRI • Design the interception of IMS related CC • Very wide problem definition – One task was to find out the problems
Methodology • The messaging was analysed using signalling flows • Standards were thoroughly studied
LI in IMS (IRI) • All the SIP messages transmitted, received or executed on behalf of the user must be delivered to the authorities • Interception is activated based on SIP URI or TEL URI • CSCF recognises the SIP messages to be captured by looking into the ’To’ and ’From’ fields in the SIP message header. • CSCF also checks for the implicit registrations
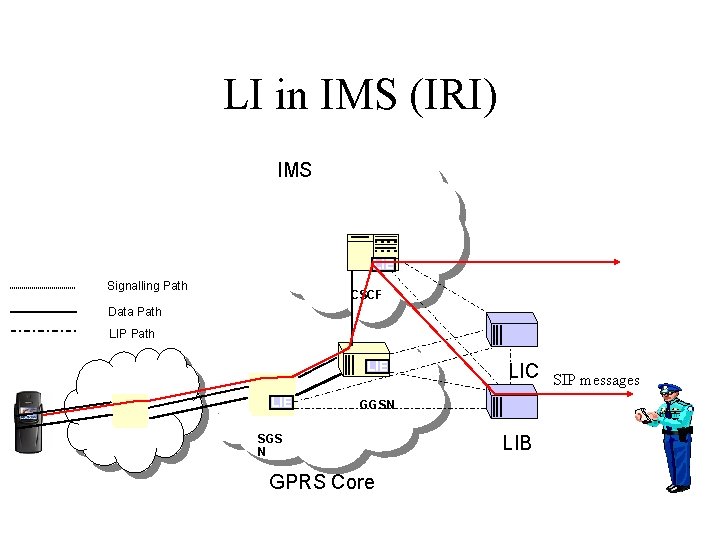
LI in IMS (IRI) IMS LIE Signalling Path CSCF Data Path LIP Path LIE LIC GGSN SGS N GPRS Core LIB SIP messages
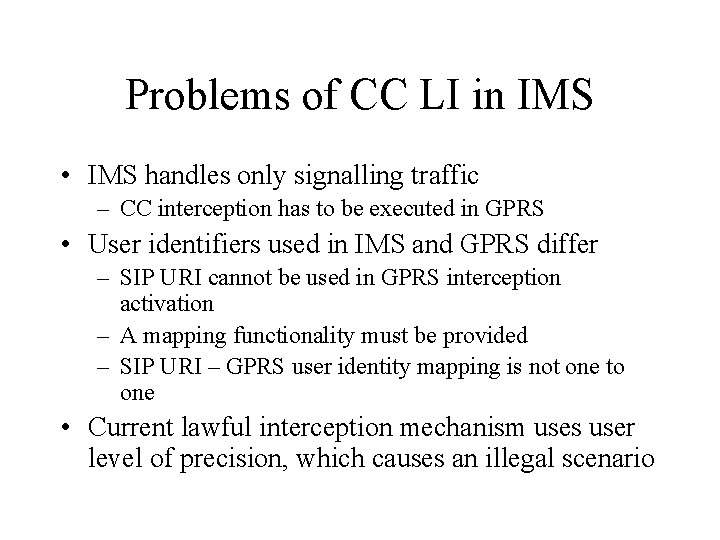
Problems of CC LI in IMS • IMS handles only signalling traffic – CC interception has to be executed in GPRS • User identifiers used in IMS and GPRS differ – SIP URI cannot be used in GPRS interception activation – A mapping functionality must be provided – SIP URI – GPRS user identity mapping is not one to one • Current lawful interception mechanism uses user level of precision, which causes an illegal scenario
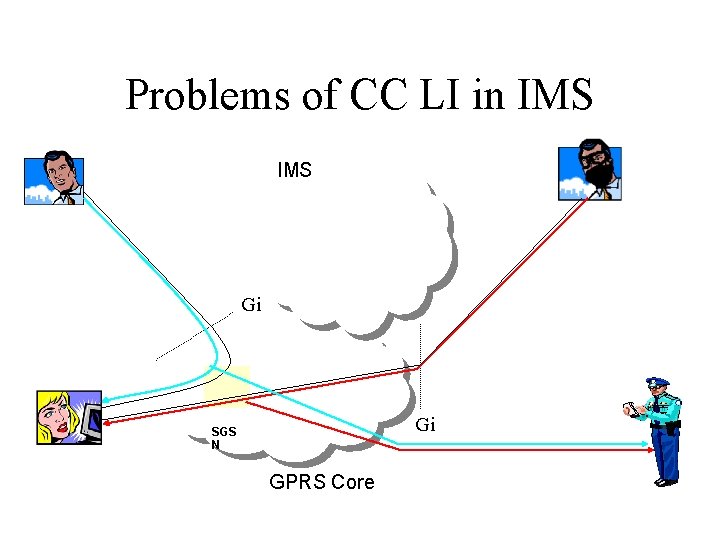
Problems of CC LI in IMS Gi Gi SGS N GPRS Core
LI in IMS (CC) • CPS notifies the LIC about the created sessions – LIC creates GPRS interceptions for CC collection • CPS notifies the LIC about released sessions – LIC releases the GPRS interception resources
LI in IMS (CC) Solution 1 • GPRS interception is activated using IMSI • Existing network elements may co-exist • The out-of-call packets need to be filtered out, before the data is forwarded to the authority
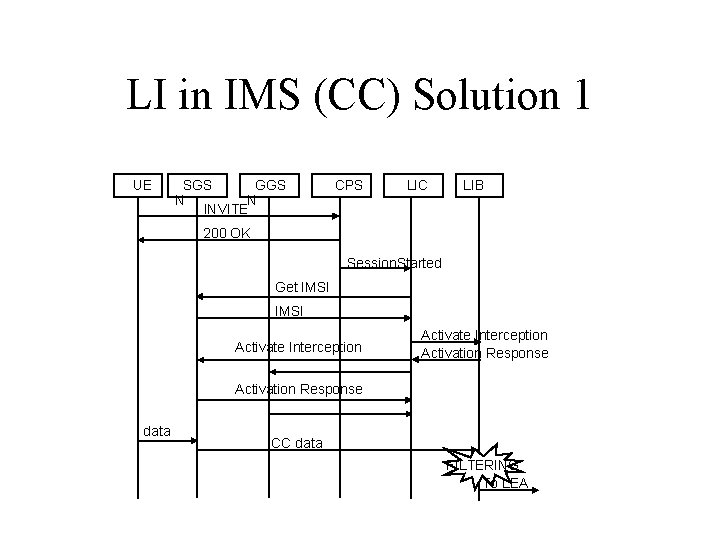
LI in IMS (CC) Solution 1 UE SGS GGS N N INVITE CPS LIC LIB 200 OK Session. Started Get IMSI Activate Interception Activation Response data CC data FILTERING To LEA
LI in IMS (CC) Solution 2 • GPRS interception is activate using the IP flow identifiers as target identifier • Quicker activation and less burden to the network • The CC interception is done only at the IMS entry point, GGSN
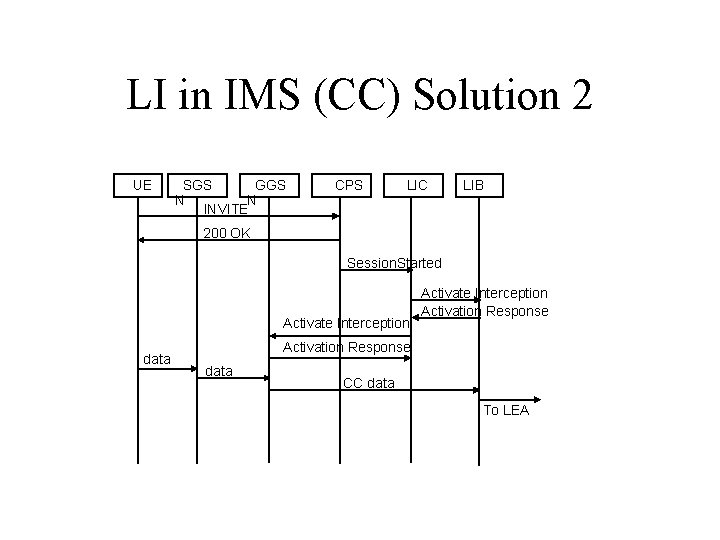
LI in IMS (CC) Solution 2 UE SGS GGS N N INVITE CPS LIC LIB 200 OK Session. Started Activate Interception data Activate Interception Activation Response data CC data To LEA
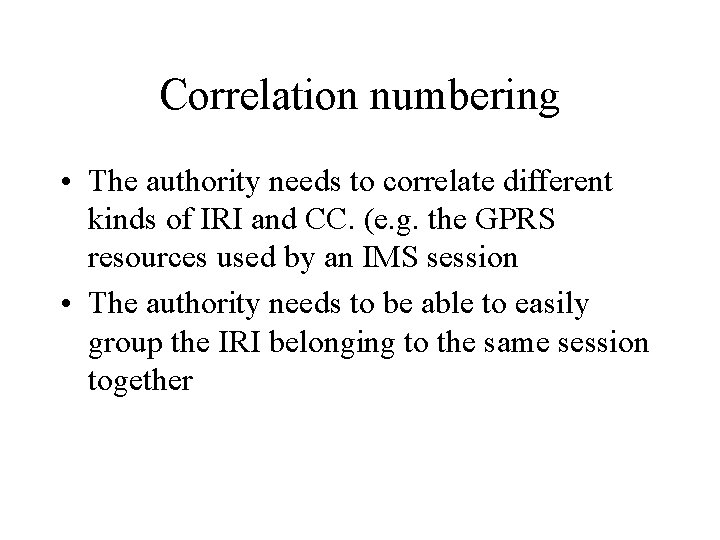
Correlation numbering • The authority needs to correlate different kinds of IRI and CC. (e. g. the GPRS resources used by an IMS session • The authority needs to be able to easily group the IRI belonging to the same session together
Correlation Numbering • IMS IRI carries Session Correlation Number, List of GPRS Correlation Numbers • GPRS IRI carries only GPRS Correlation Number • IMS CC carries GPRS Correlation Number, Session Correlation Number, and Media component identifier
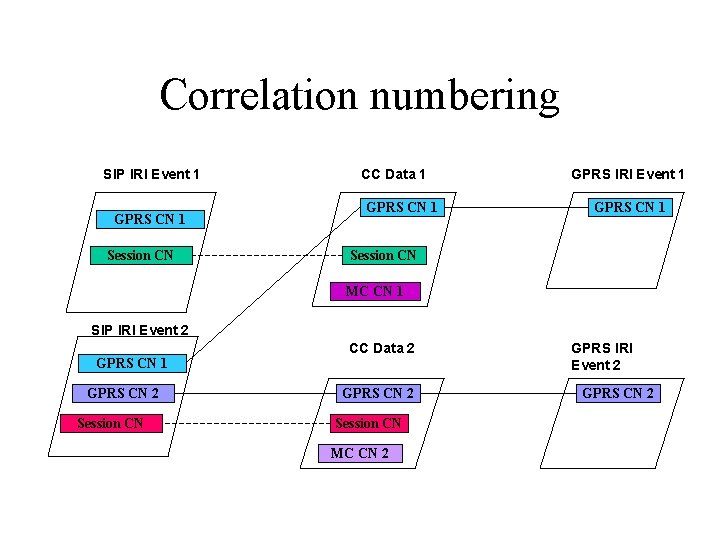
Correlation numbering SIP IRI Event 1 GPRS CN 1 Session CN CC Data 1 GPRS CN 1 GPRS IRI Event 1 GPRS CN 1 Session CN MC CN 1 SIP IRI Event 2 GPRS CN 1 GPRS CN 2 Session CN CC Data 2 GPRS CN 2 Session CN MC CN 2 GPRS IRI Event 2 GPRS CN 2
Conclusions • IRI monitoring including the implicit registration • Capturing of content of communications in GPRS • Correlation numbering scheme
QUESTIONS? Thank you for listening!
- Slides: 24