L12 CDNs 1 ACID vs BASE ACID Strong

L-12 CDNs 1
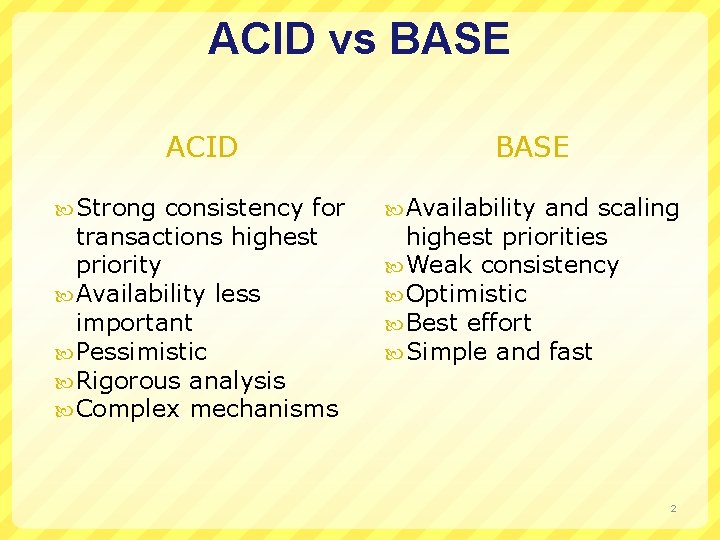
ACID vs BASE ACID Strong consistency for transactions highest priority Availability less important Pessimistic Rigorous analysis Complex mechanisms BASE Availability and scaling highest priorities Weak consistency Optimistic Best effort Simple and fast 2
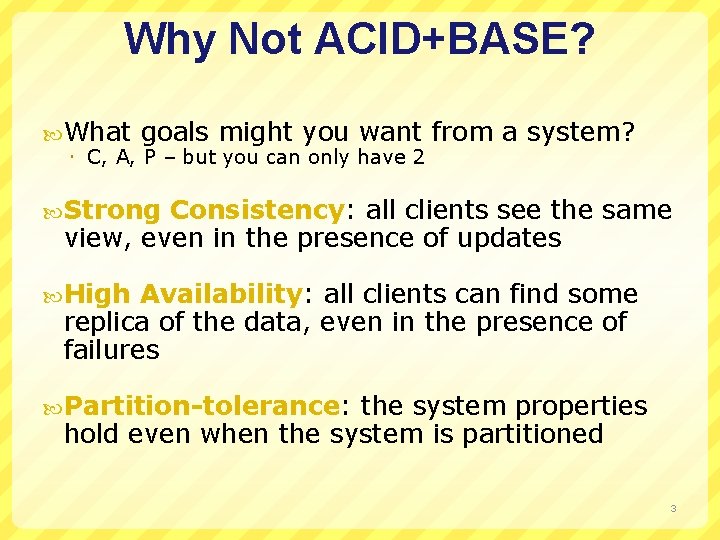
Why Not ACID+BASE? What goals might you want C, A, P – but you can only have 2 from a system? Strong Consistency: all clients see the same view, even in the presence of updates High Availability: all clients can find some replica of the data, even in the presence of failures Partition-tolerance: the system properties hold even when the system is partitioned 3
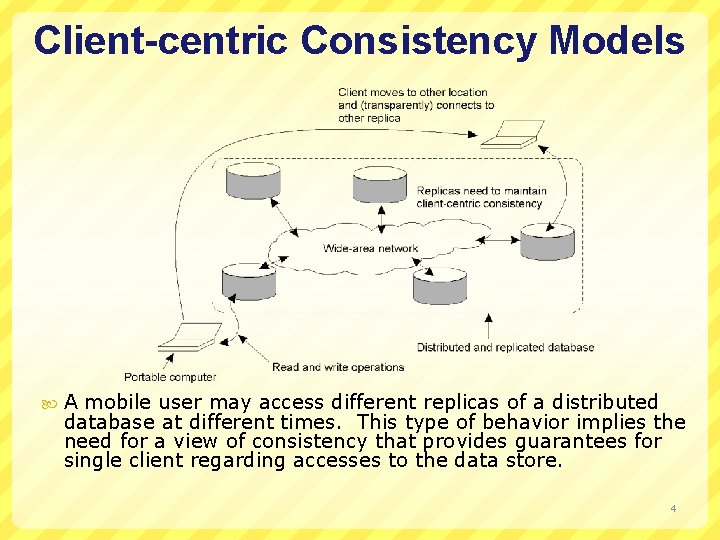
Client-centric Consistency Models A mobile user may access different replicas of a distributed database at different times. This type of behavior implies the need for a view of consistency that provides guarantees for single client regarding accesses to the data store. 4
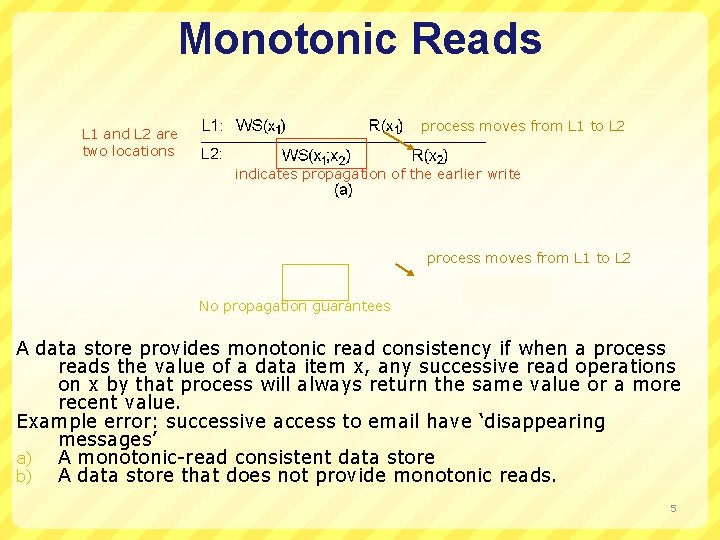
Monotonic Reads process moves from L 1 to L 2 L 1 and L 2 are two locations indicates propagation of the earlier write process moves from L 1 to L 2 No propagation guarantees A data store provides monotonic read consistency if when a process reads the value of a data item x, any successive read operations on x by that process will always return the same value or a more recent value. Example error: successive access to email have ‘disappearing messages’ a) A monotonic-read consistent data store b) A data store that does not provide monotonic reads. 5
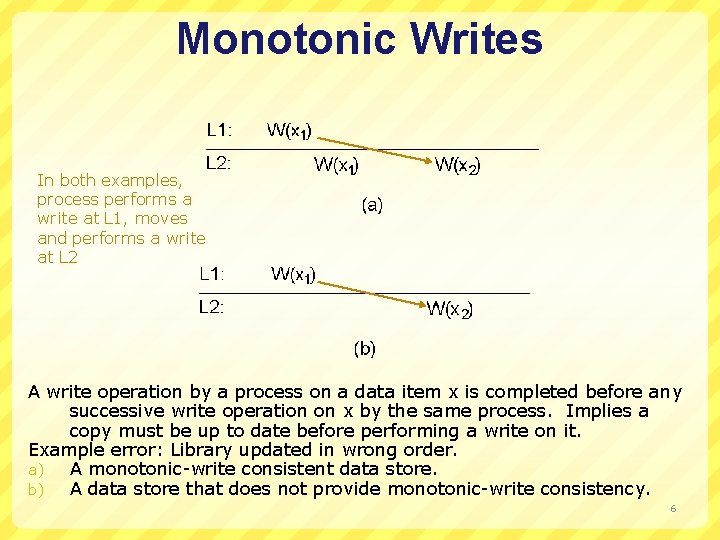
Monotonic Writes In both examples, process performs a write at L 1, moves and performs a write at L 2 A write operation by a process on a data item x is completed before any successive write operation on x by the same process. Implies a copy must be up to date before performing a write on it. Example error: Library updated in wrong order. a) A monotonic-write consistent data store. b) A data store that does not provide monotonic-write consistency. 6
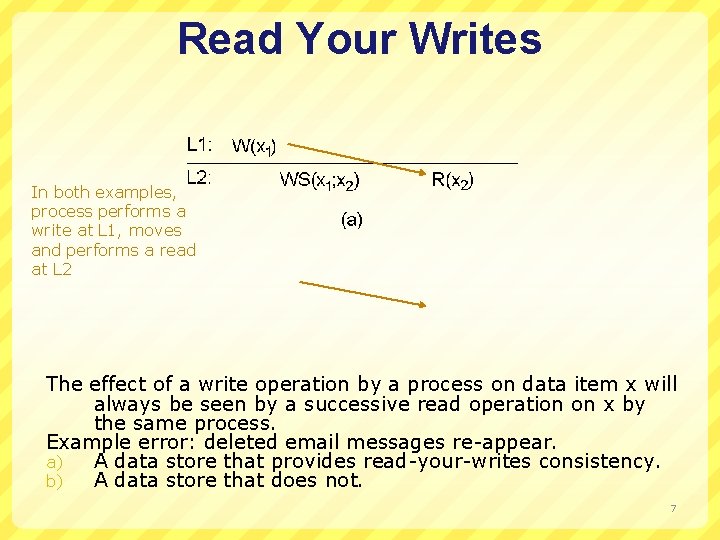
Read Your Writes In both examples, process performs a write at L 1, moves and performs a read at L 2 The effect of a write operation by a process on data item x will always be seen by a successive read operation on x by the same process. Example error: deleted email messages re-appear. a) A data store that provides read-your-writes consistency. b) A data store that does not. 7
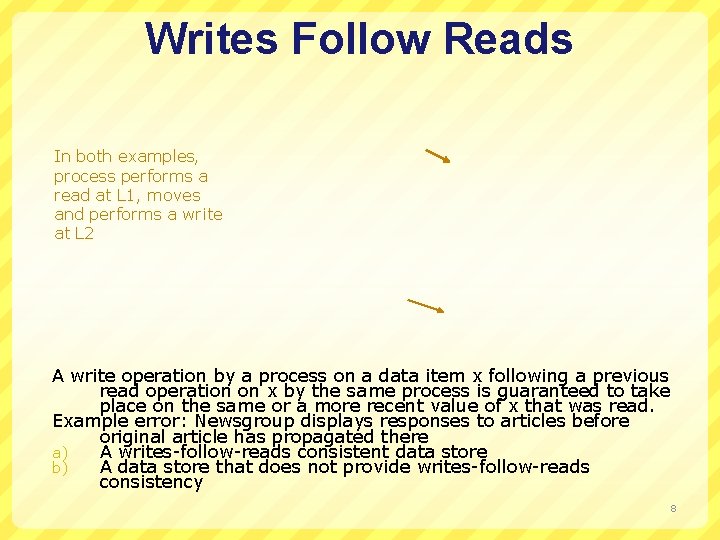
Writes Follow Reads In both examples, process performs a read at L 1, moves and performs a write at L 2 A write operation by a process on a data item x following a previous read operation on x by the same process is guaranteed to take place on the same or a more recent value of x that was read. Example error: Newsgroup displays responses to articles before original article has propagated there a) A writes-follow-reads consistent data store b) A data store that does not provide writes-follow-reads consistency 8
9
Motivating Scenario: Shared Calendar updates made by several people e. g. , meeting room scheduling, or exec+admin Want to allow Mobile users But updates offline conflicts can’t be prevented Two possibilities: Disallow offline updates? Conflict resolution? 10
Conflict Resolution Replication not transparent to application Only the application knows how to resolve conflicts Application can do record-level conflict detection, not just file-level conflict detection Calendar example: record-level, and easy resolution Split of responsibility: Replication system: propagates updates Application: resolves conflict Optimistic application of writes requires that writes be “undo-able” 11
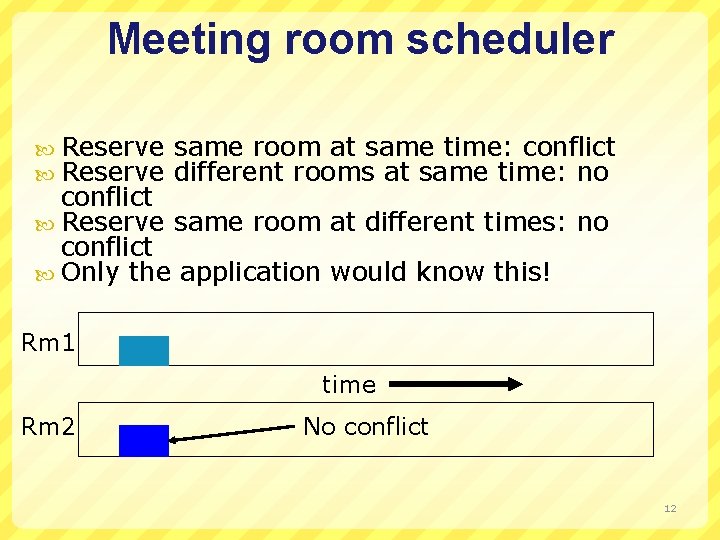
Meeting room scheduler Reserve same room at same time: conflict different rooms at same time: no conflict Reserve same room at different times: no conflict Only the application would know this! Rm 1 time Rm 2 No conflict 12
Meeting Room Scheduler Rm 1 No conflict time Rm 2 13
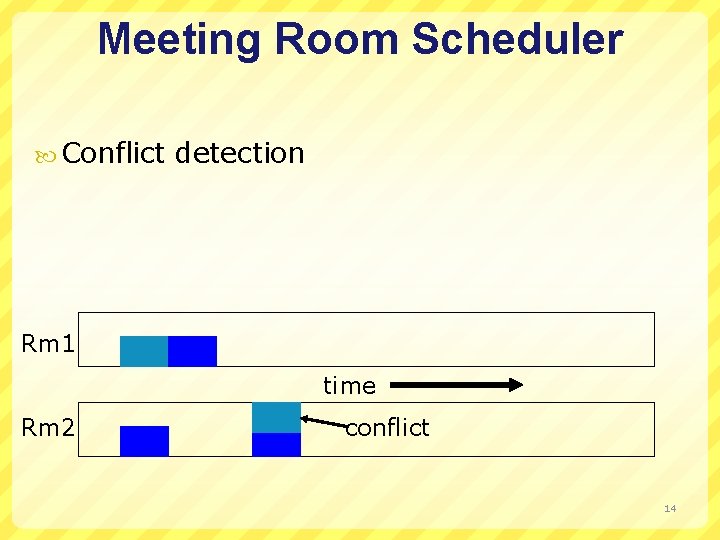
Meeting Room Scheduler Conflict detection Rm 1 time Rm 2 conflict 14
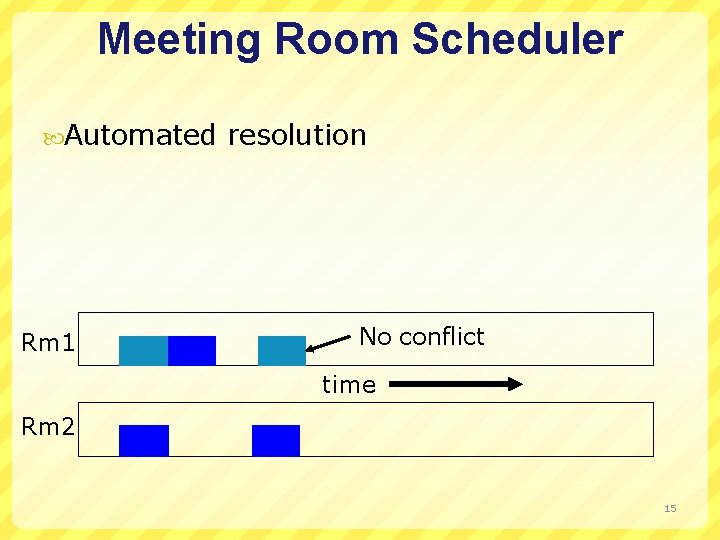
Meeting Room Scheduler Automated Rm 1 resolution No conflict time Rm 2 15
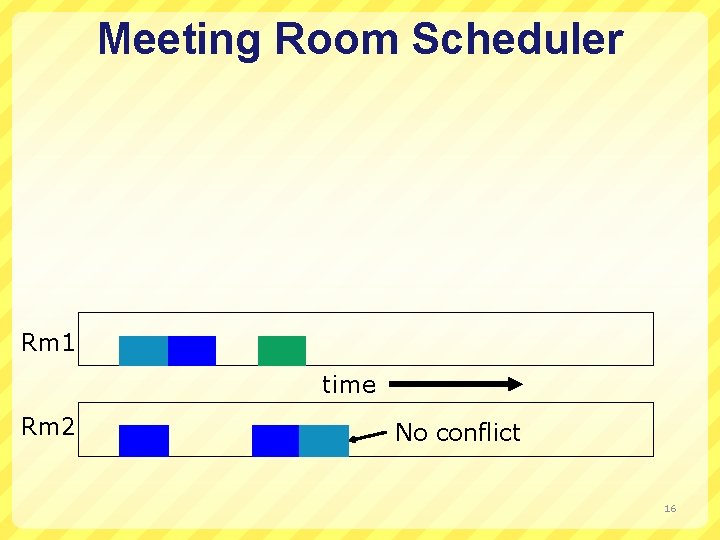
Meeting Room Scheduler Rm 1 time Rm 2 No conflict 16
Other Resolution Strategies Classes take priority over meetings Faculty reservations are bumped by admin reservations Move meetings to bigger room, if available Point: Conflicts are detected at very fine granularity Resolution can be policy-driven 17
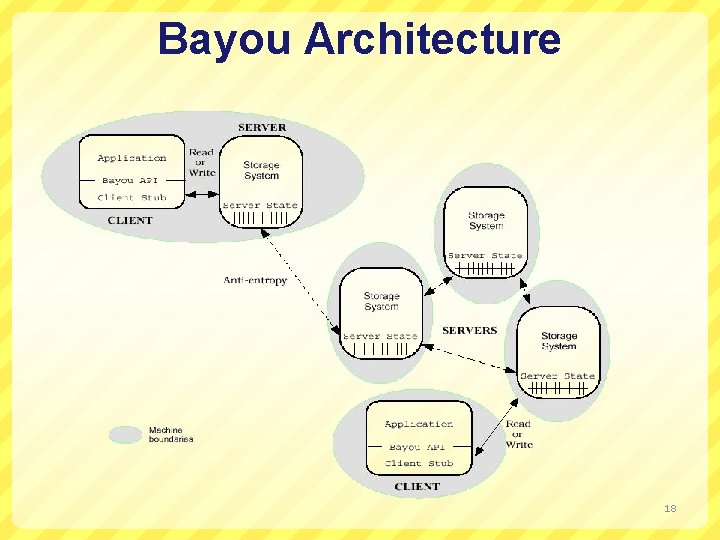
Bayou Architecture 18
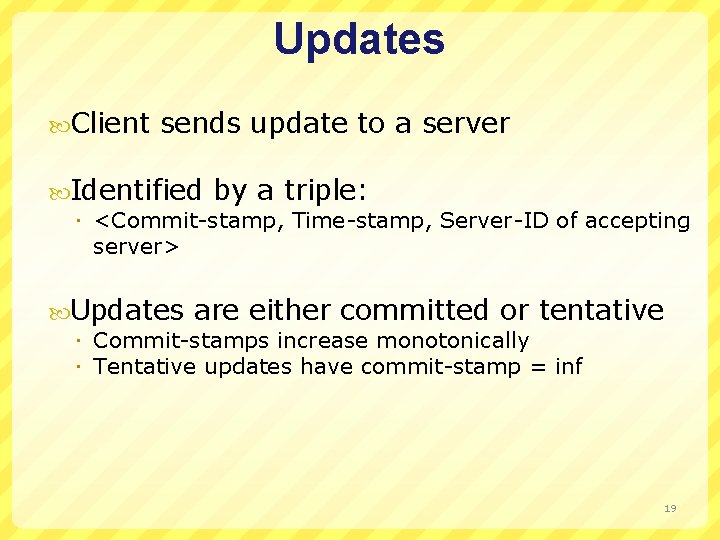
Updates Client sends update to a server Identified by a triple: <Commit-stamp, Time-stamp, Server-ID of accepting server> Updates are either committed or tentative Commit-stamps increase monotonically Tentative updates have commit-stamp = inf 19
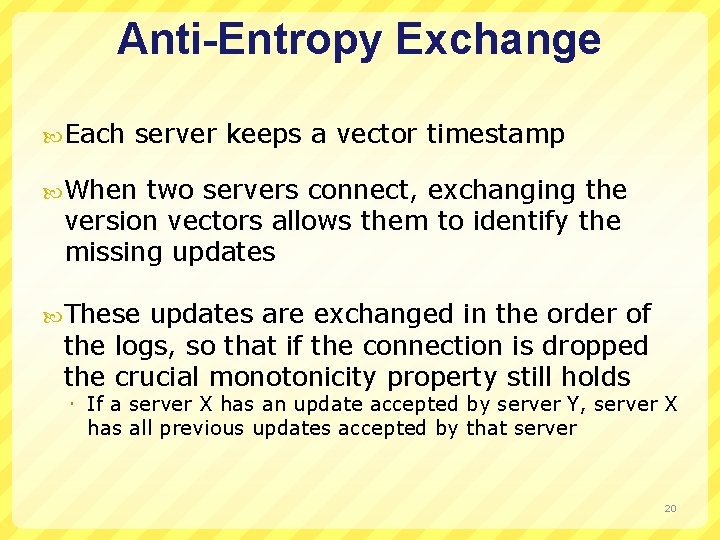
Anti-Entropy Exchange Each server keeps a vector timestamp When two servers connect, exchanging the version vectors allows them to identify the missing updates These updates are exchanged in the order of the logs, so that if the connection is dropped the crucial monotonicity property still holds If a server X has an update accepted by server Y, server X has all previous updates accepted by that server 20
![Example with Three Servers P A B [0, 0, 0] Version Vectors 21 Example with Three Servers P A B [0, 0, 0] Version Vectors 21](http://slidetodoc.com/presentation_image/00fd3276afc19a10b566e94cc48be3cd/image-21.jpg)
Example with Three Servers P A B [0, 0, 0] Version Vectors 21
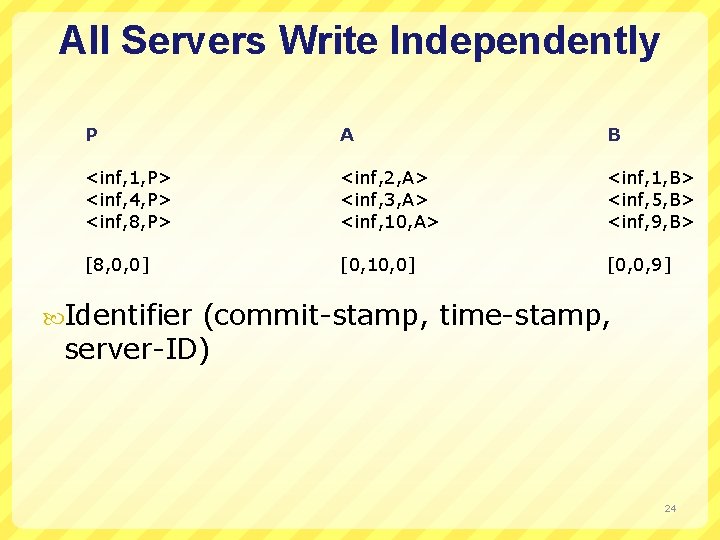
All Servers Write Independently P A B <inf, 1, P> <inf, 4, P> <inf, 8, P> <inf, 2, A> <inf, 3, A> <inf, 10, A> <inf, 1, B> <inf, 5, B> <inf, 9, B> [8, 0, 0] [0, 10, 0] [0, 0, 9] Identifier (commit-stamp, time-stamp, server-ID) 24
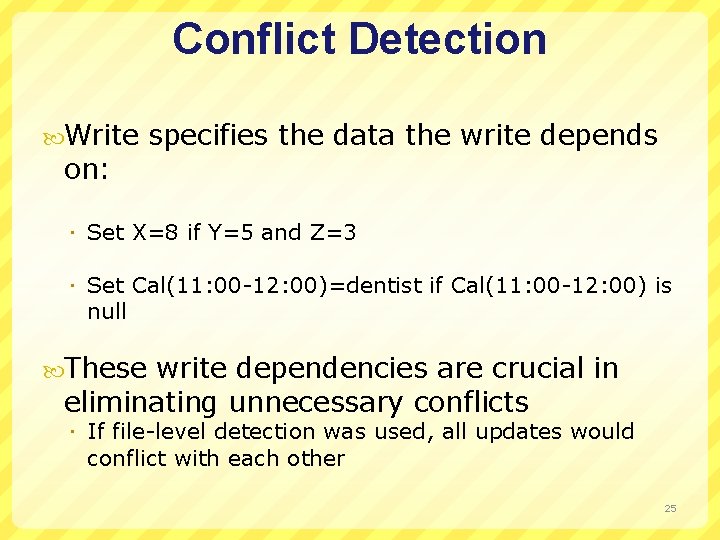
Conflict Detection Write on: specifies the data the write depends Set X=8 if Y=5 and Z=3 Set Cal(11: 00 -12: 00)=dentist if Cal(11: 00 -12: 00) is null These write dependencies are crucial in eliminating unnecessary conflicts If file-level detection was used, all updates would conflict with each other 25
Conflict Resolution Specified When called by merge procedure (mergeproc) conflict is detected, mergeproc is Move appointments to open spot on calendar Move meetings to open room 26
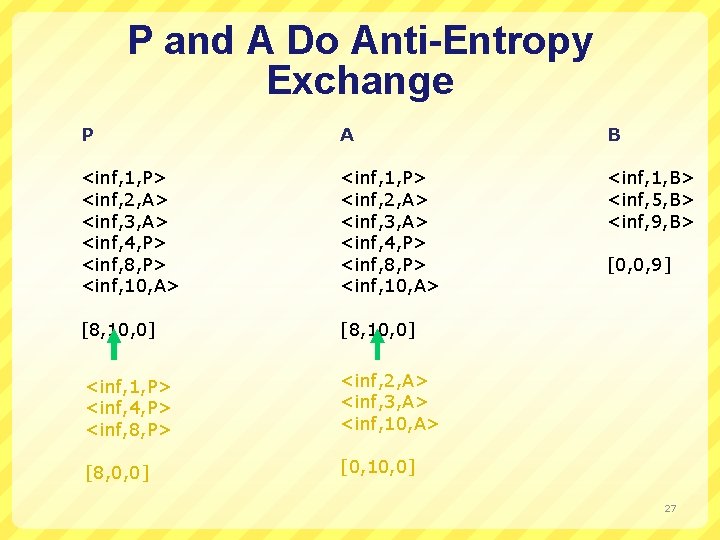
P and A Do Anti-Entropy Exchange P A B <inf, 1, P> <inf, 2, A> <inf, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> <inf, 1, B> <inf, 5, B> <inf, 9, B> [8, 10, 0] <inf, 1, P> <inf, 4, P> <inf, 8, P> <inf, 2, A> <inf, 3, A> <inf, 10, A> [8, 0, 0] [0, 10, 0] [0, 0, 9] 27
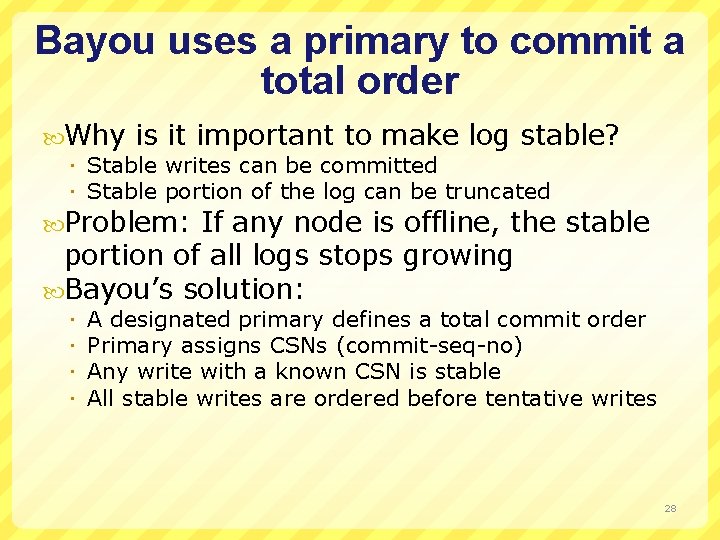
Bayou uses a primary to commit a total order Why is it important to make log stable? Stable writes can be committed Stable portion of the log can be truncated Problem: If any node is offline, the stable portion of all logs stops growing Bayou’s solution: A designated primary defines a total commit order Primary assigns CSNs (commit-seq-no) Any write with a known CSN is stable All stable writes are ordered before tentative writes 28
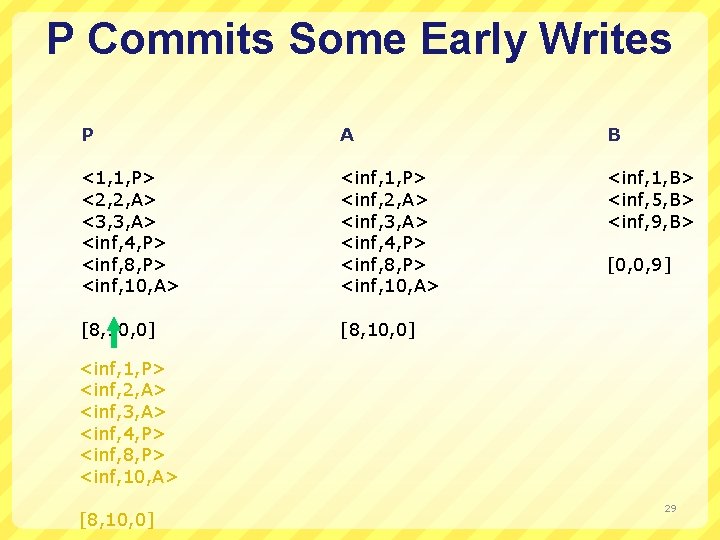
P Commits Some Early Writes P A B <1, 1, P> <2, 2, A> <3, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> <inf, 1, P> <inf, 2, A> <inf, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> <inf, 1, B> <inf, 5, B> <inf, 9, B> [8, 10, 0] [0, 0, 9] <inf, 1, P> <inf, 2, A> <inf, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> [8, 10, 0] 29
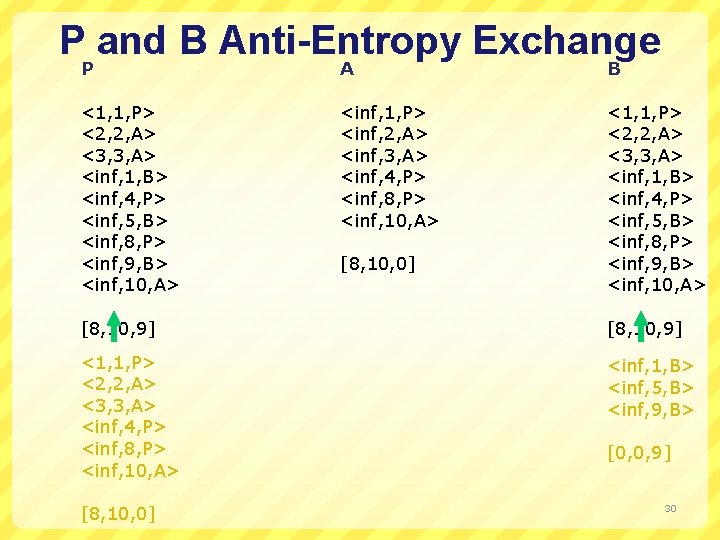
P and B Anti-Entropy Exchange P A B <1, 1, P> <2, 2, A> <3, 3, A> <inf, 1, B> <inf, 4, P> <inf, 5, B> <inf, 8, P> <inf, 9, B> <inf, 10, A> <inf, 1, P> <inf, 2, A> <inf, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> <1, 1, P> <2, 2, A> <3, 3, A> <inf, 1, B> <inf, 4, P> <inf, 5, B> <inf, 8, P> <inf, 9, B> <inf, 10, A> [8, 10, 0] [8, 10, 9] <1, 1, P> <2, 2, A> <3, 3, A> <inf, 4, P> <inf, 8, P> <inf, 10, A> <inf, 1, B> <inf, 5, B> <inf, 9, B> [8, 10, 0] [0, 0, 9] 30
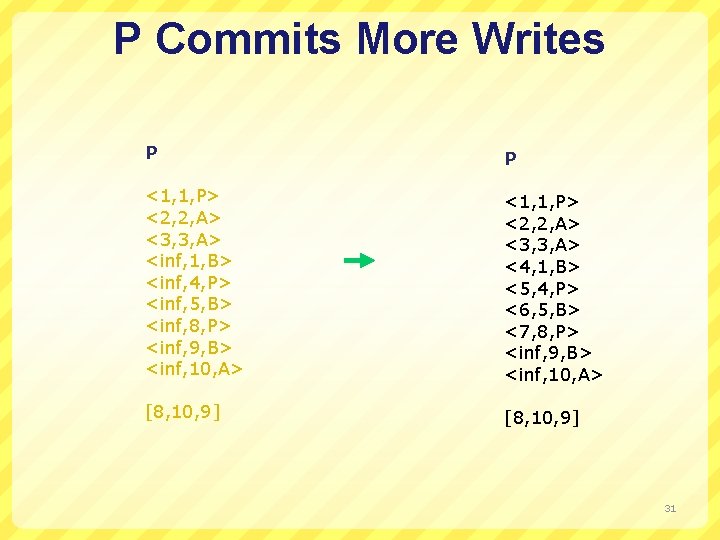
P Commits More Writes P P <1, 1, P> <2, 2, A> <3, 3, A> <inf, 1, B> <inf, 4, P> <inf, 5, B> <inf, 8, P> <inf, 9, B> <inf, 10, A> <1, 1, P> <2, 2, A> <3, 3, A> <4, 1, B> <5, 4, P> <6, 5, B> <7, 8, P> <inf, 9, B> <inf, 10, A> [8, 10, 9] 31
Bayou Summary Simple gossip based design Key difference exploits knowledge of application semantics To identify conflicts To handle merges Greater complexity for the programmer Might be useful in ubicomp context 32
Important Lessons ACID vs. BASE Understand the tradeoffs you are making ACID makes things better for programmer/system designed BASE often preferred by users Client-centric consistency Different guarantees than data-centric Eventual consistency BASE-like design better performance/availability Must design system to tolerate Bayou a good example of making tolerance explicit 33
Today's Lecture CDNs 34
HTTP Caching Clients often cache documents Challenge: update of documents If-Modified-Since requests to check HTTP 0. 9/1. 0 used just date HTTP 1. 1 has an opaque “entity tag” (could be a file signature, etc. ) as well When/how often should the original be checked for changes? Check every time? Check each session? Day? Etc? Use Expires header If no Expires, often use Last-Modified as estimate 35
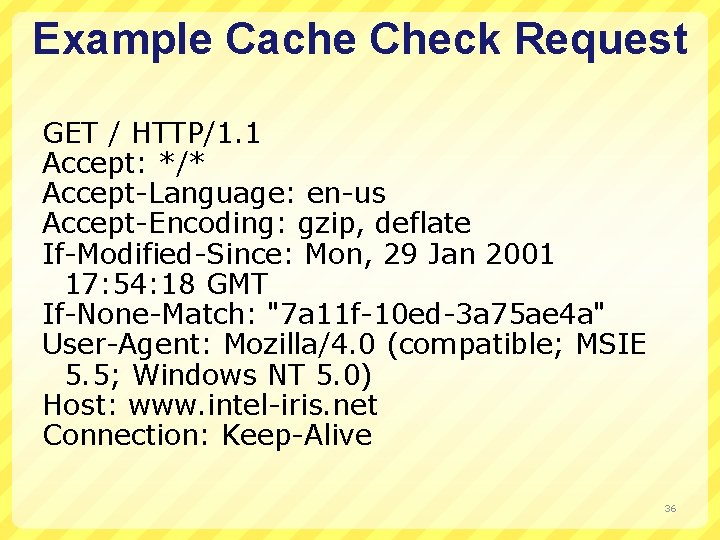
Example Cache Check Request GET / HTTP/1. 1 Accept: */* Accept-Language: en-us Accept-Encoding: gzip, deflate If-Modified-Since: Mon, 29 Jan 2001 17: 54: 18 GMT If-None-Match: "7 a 11 f-10 ed-3 a 75 ae 4 a" User-Agent: Mozilla/4. 0 (compatible; MSIE 5. 5; Windows NT 5. 0) Host: www. intel-iris. net Connection: Keep-Alive 36
Example Cache Check Response HTTP/1. 1 304 Not Modified Date: Tue, 27 Mar 2001 03: 50: 51 GMT Server: Apache/1. 3. 14 (Unix) (Red. Hat/Linux) mod_ssl/2. 7. 1 Open. SSL/0. 9. 5 a DAV/1. 0. 2 PHP/4. 0. 1 pl 2 mod_perl/1. 24 Connection: Keep-Alive: timeout=15, max=100 ETag: "7 a 11 f-10 ed-3 a 75 ae 4 a" 37
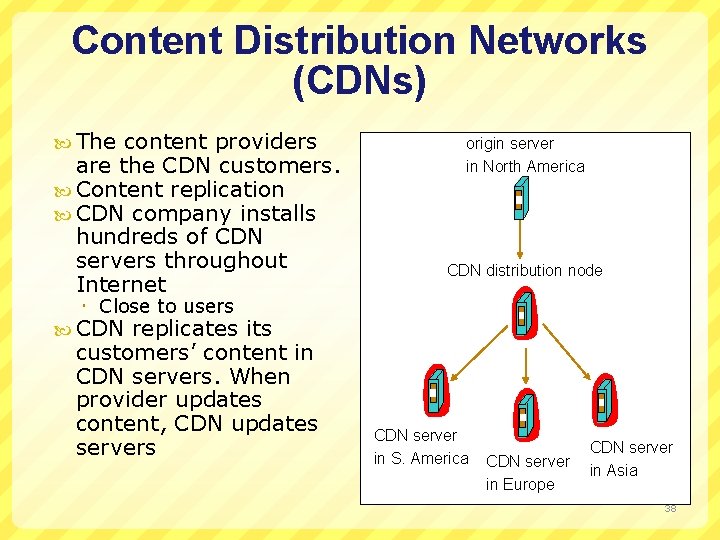
Content Distribution Networks (CDNs) The content providers are the CDN customers. Content replication CDN company installs hundreds of CDN servers throughout Internet origin server in North America CDN distribution node Close to users CDN replicates its customers’ content in CDN servers. When provider updates content, CDN updates servers CDN server in S. America CDN server in Europe CDN server in Asia 38
Server Selection Service is replicated in many places in network How do direct clients to a particular server? As part of routing anycast, cluster load balancing As part of application HTTP redirect As part of naming DNS Which server? Lowest load to balance load on servers Best performance to improve client performance Based on Geography? RTT? Throughput? Load? Any alive node to provide fault tolerance 39
Routing Based Anycast Give service a single IP address Each node implementing service advertises route to address Packets get routed from client to “closest” service node Closest is defined by routing metrics May not mirror performance/application needs What about the stability of routes? 40
Application Based HTTP support simple way to indicate that Web page has moved Server gets Get request from client Decides which server is best suited for particular client and object Returns HTTP redirect to that server Can May make informed application specific decision introduce additional overhead multiple connection setup, name lookups, etc. While good solution in general HTTP Redirect has some design flaws – especially with current browsers 41
Naming Based Client Name does name lookup for service server chooses appropriate server address A-record returned is “best” one for the client What information can name server base decision on? Server load/location must be collected Information in the name lookup request Name service client typically the local name server for client 42
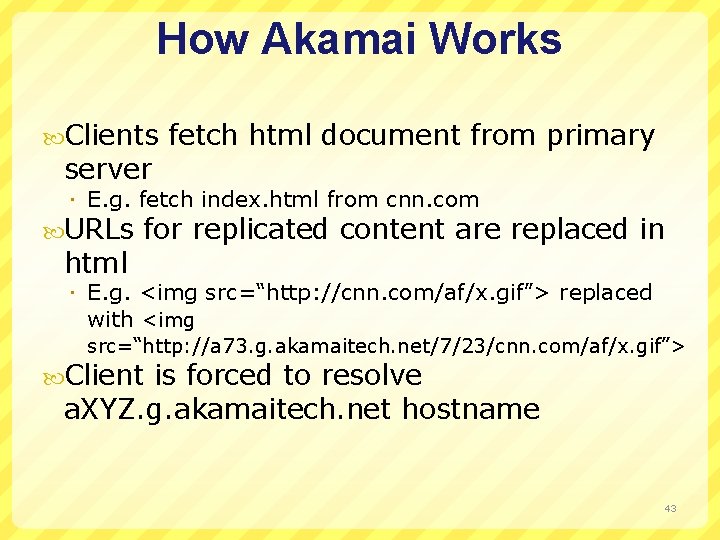
How Akamai Works Clients server fetch html document from primary E. g. fetch index. html from cnn. com URLs html for replicated content are replaced in E. g. <img src=“http: //cnn. com/af/x. gif”> replaced with <img src=“http: //a 73. g. akamaitech. net/7/23/cnn. com/af/x. gif”> Client is forced to resolve a. XYZ. g. akamaitech. net hostname 43
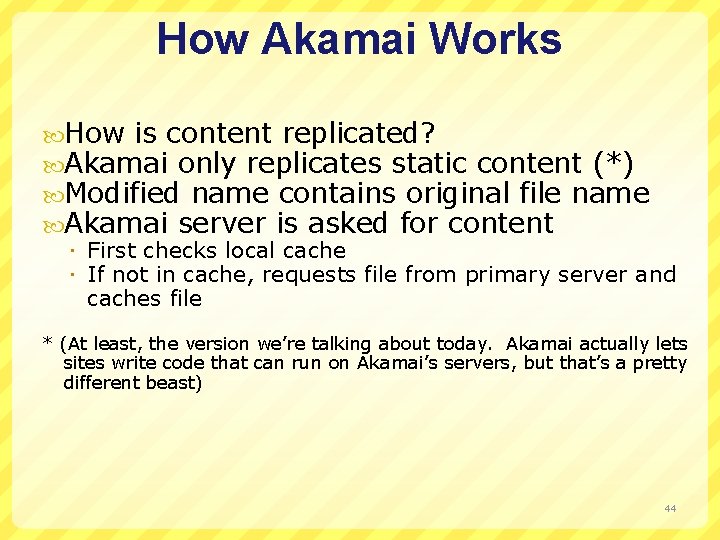
How Akamai Works How is content replicated? Akamai only replicates static content (*) Modified name contains original file name Akamai server is asked for content First checks local cache If not in cache, requests file from primary server and caches file * (At least, the version we’re talking about today. Akamai actually lets sites write code that can run on Akamai’s servers, but that’s a pretty different beast) 44
How Akamai Works Root server Akamai. net gives NS record for akamai. net name server returns NS record for g. akamaitech. net Name server chosen to be in region of client’s name server TTL is large G. akamaitech. net server in region nameserver chooses Should try to chose server that has file in cache - How to choose? Uses a. XYZ name and hash TTL is small why? 45
Simple Hashing Given document XYZ, we need to choose a server to use Suppose we use modulo Number servers from 1…n Place document XYZ on server (XYZ mod n) What happens when a servers fails? n n-1 Same if different people have different measures of n Why might this be bad? 46
Simple Hashing Given document XYZ, we need to choose a server to use Suppose we use modulo Number servers from 1…n Place document XYZ on server (XYZ mod n) What happens when a servers fails? n n-1 Same if different people have different measures of n Why might this be bad? 47
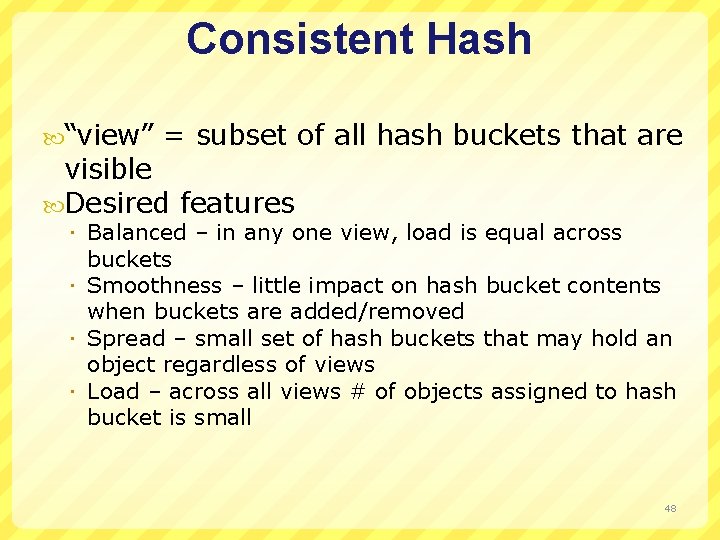
Consistent Hash “view” = subset of all hash buckets that are visible Desired features Balanced – in any one view, load is equal across buckets Smoothness – little impact on hash bucket contents when buckets are added/removed Spread – small set of hash buckets that may hold an object regardless of views Load – across all views # of objects assigned to hash bucket is small 48
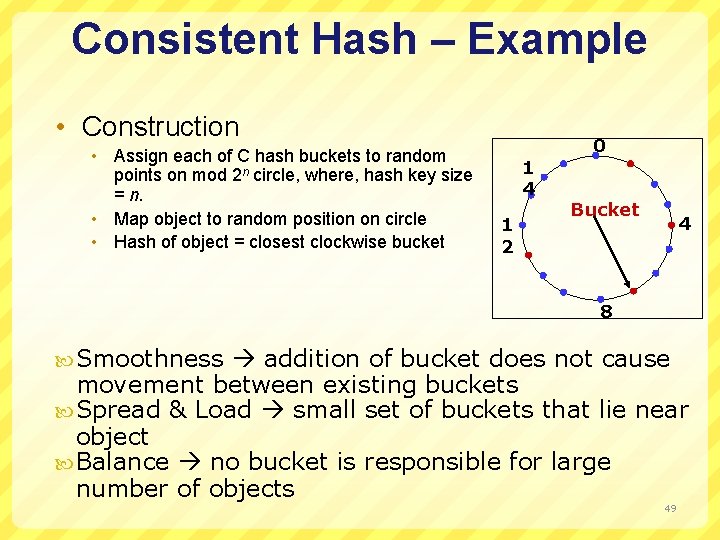
Consistent Hash – Example • Construction • Assign each of C hash buckets to random points on mod 2 n circle, where, hash key size = n. • Map object to random position on circle • Hash of object = closest clockwise bucket 1 4 1 2 0 Bucket 4 8 Smoothness addition of bucket does not cause movement between existing buckets Spread & Load small set of buckets that lie near object Balance no bucket is responsible for large number of objects 49
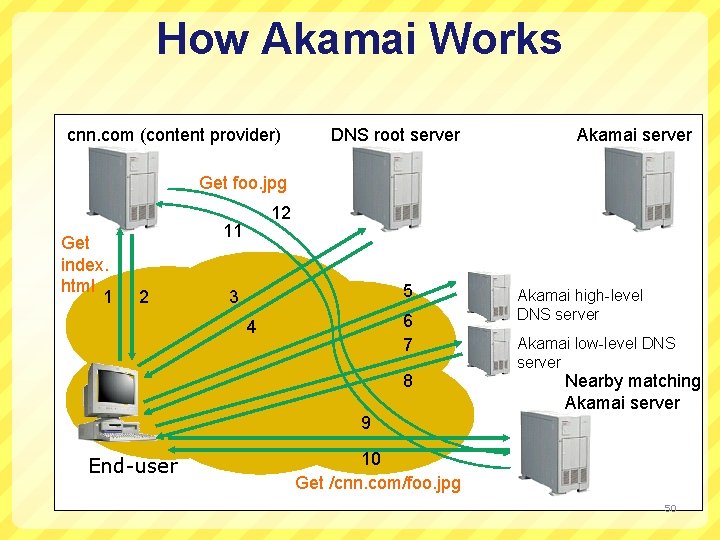
How Akamai Works cnn. com (content provider) DNS root server Akamai server Get foo. jpg Get index. html 1 12 11 2 5 3 6 7 4 8 Akamai high-level DNS server Akamai low-level DNS server Nearby matching Akamai server 9 End-user 10 Get /cnn. com/foo. jpg 50
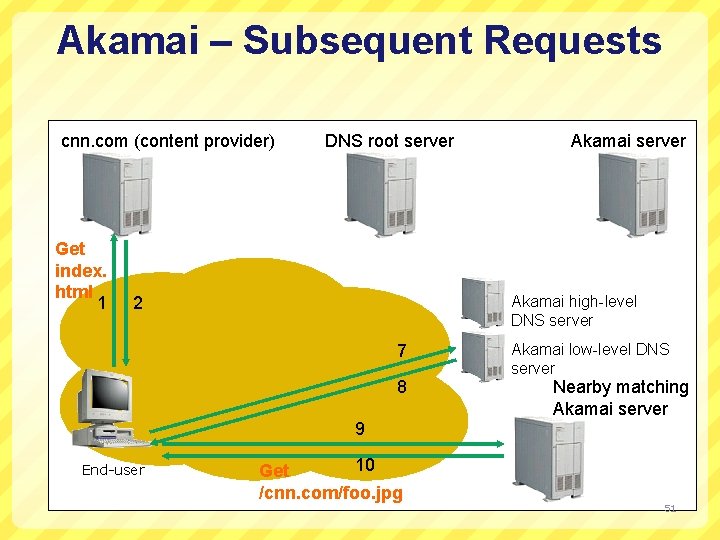
Akamai – Subsequent Requests cnn. com (content provider) Get index. html 1 DNS root server Akamai high-level DNS server 2 7 8 Akamai low-level DNS server Nearby matching Akamai server 9 End-user 10 Get /cnn. com/foo. jpg 51
Important Lessons Akamai CDN illustrate range of BASE (not ACID design) Weak consistency Naming of objects location translation Consistent hashing ideas Why are these the right design choices for this application? 52
- Slides: 50