l Palo Alto SSL VPN l Fortinet SSL

- Slides: 19
目錄 l. Palo Alto SSL VPN 漏洞 l. Fortinet SSL VPN 漏洞 l. Pulse Secure SSL VPN 漏洞 l資料來源 3
Palo Alto SSL VPN 漏洞 4
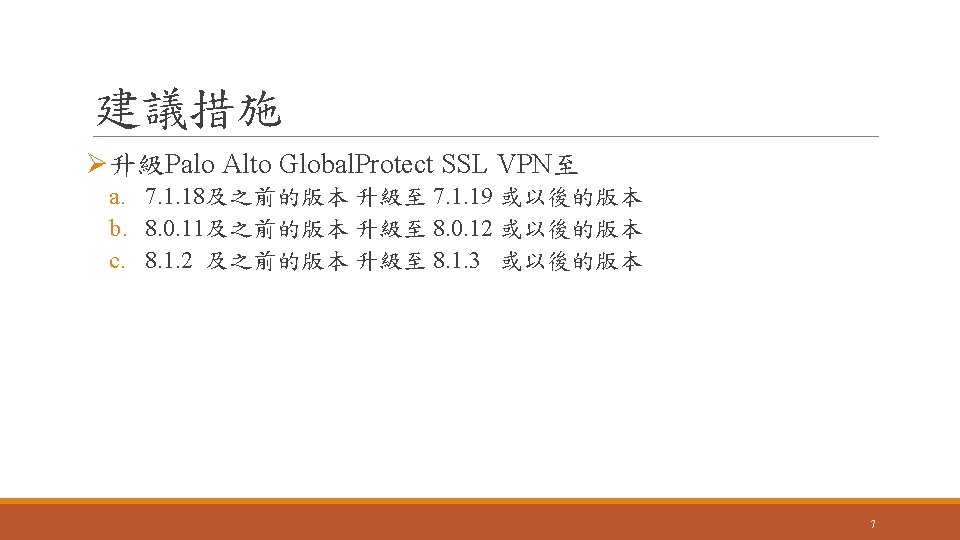
影響範圍 l存在漏洞的版本如下,建議用戶儘速更新至最新版以避免遭受攻擊: üPalo Alto Global. Protect SSL VPN 7. 1. 0 ~ 7. 1. 18 üPalo Alto Global. Protect SSL VPN 8. 0. 0 ~ 8. 0. 11 üPalo Alto Global. Protect SSL VPN 8. 1. 0 ~ 8. 1. 2 l 9. x 和 7. 0. x 並沒有存在此漏洞 6
Fortigate SSL VPN 漏洞 8

簡介 l. Fortigate SSL VPN是Fortinet旗下SSL VPN產品 l這些CVE漏洞是有先去通報原廠,等廠商修好漏洞後才公開 l研究團隊在black hat USA 2019公布了五個Fortigate SSL VPN漏洞 圖片來源:https: //www. fortinet. com/tw 9
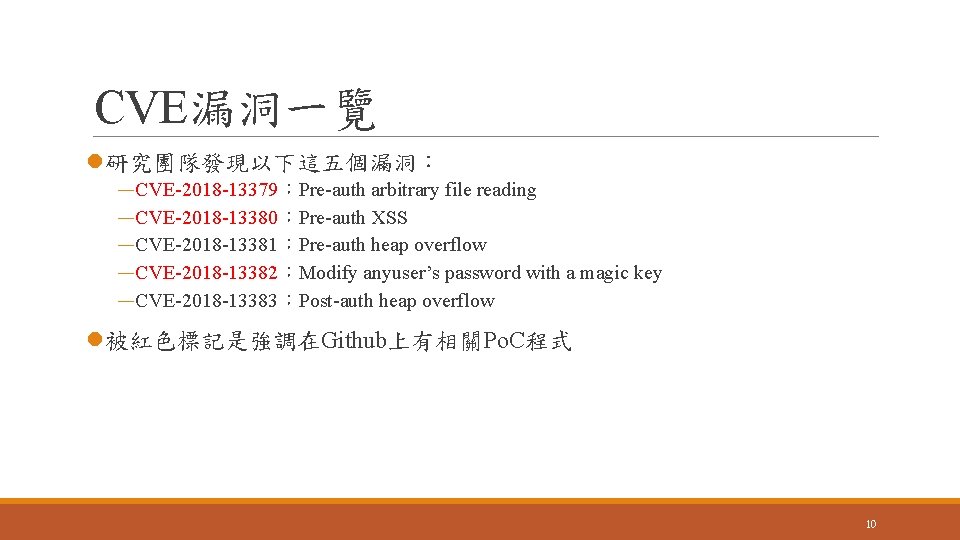
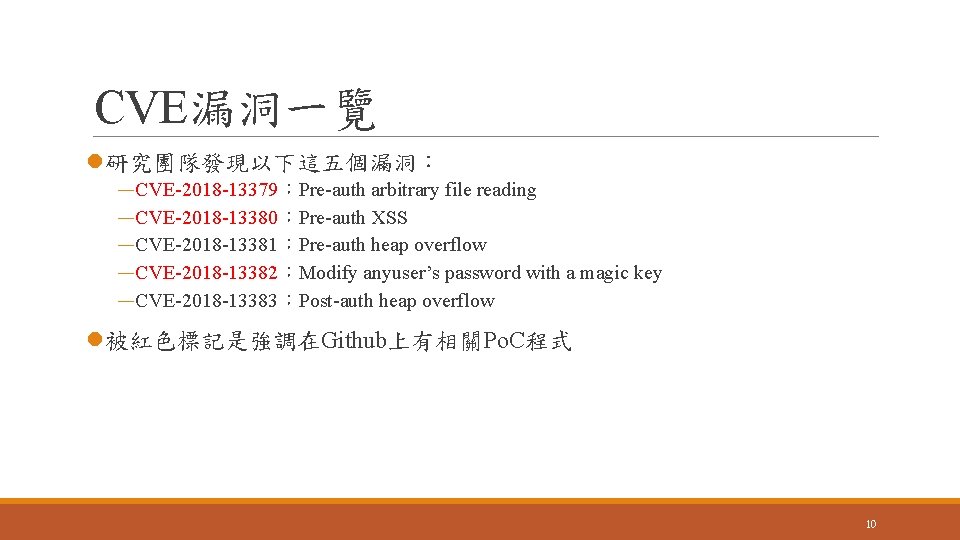
CVE漏洞一覽 l研究團隊發現以下這五個漏洞: —CVE-2018 -13379:Pre-auth arbitrary file reading —CVE-2018 -13380:Pre-auth XSS —CVE-2018 -13381:Pre-auth heap overflow —CVE-2018 -13382:Modify anyuser’s password with a magic key —CVE-2018 -13383:Post-auth heap overflow l被紅色標記是強調在Github上有相關Po. C程式 10
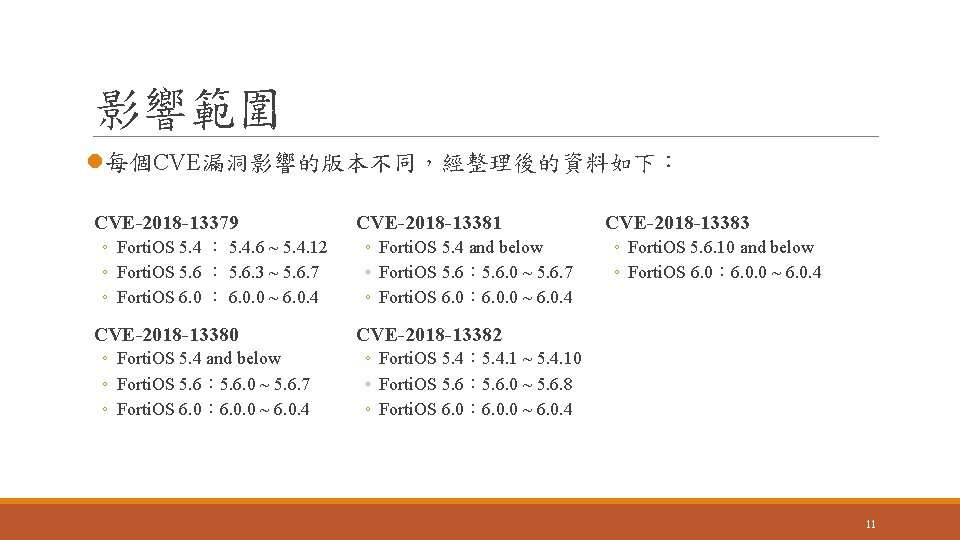
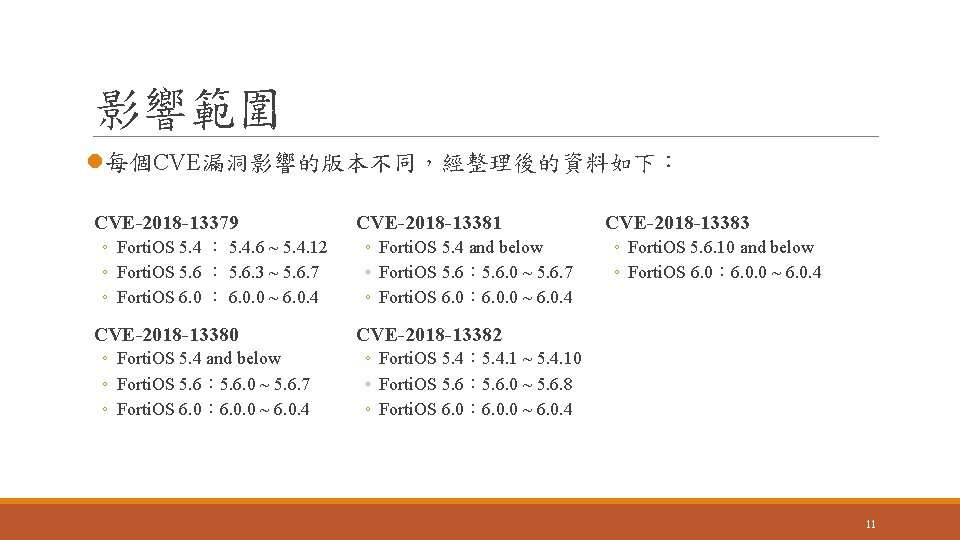
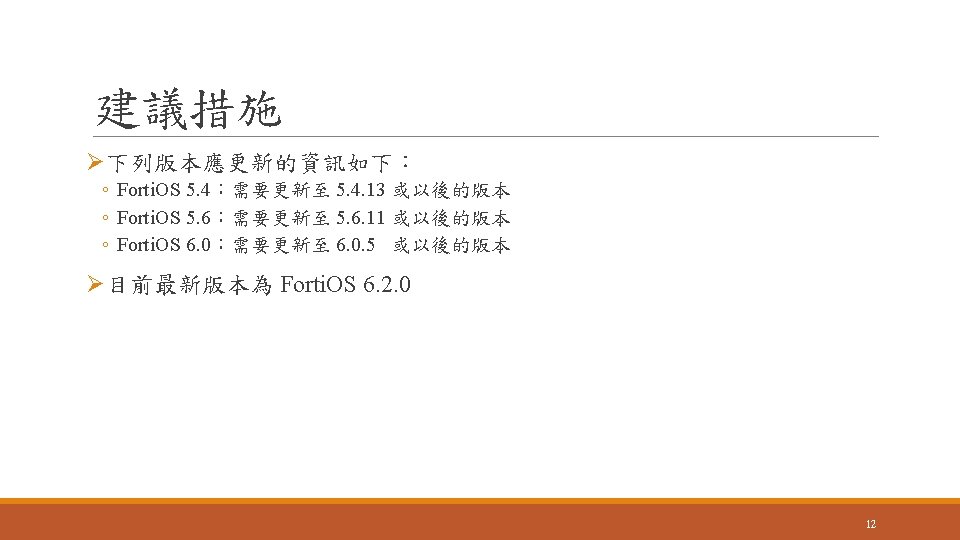
影響範圍 l每個CVE漏洞影響的版本不同,經整理後的資料如下: CVE-2018 -13379 ◦ Forti. OS 5. 4 : 5. 4. 6 ~ 5. 4. 12 ◦ Forti. OS 5. 6 : 5. 6. 3 ~ 5. 6. 7 ◦ Forti. OS 6. 0 : 6. 0. 0 ~ 6. 0. 4 CVE-2018 -13380 ◦ Forti. OS 5. 4 and below ◦ Forti. OS 5. 6: 5. 6. 0 ~ 5. 6. 7 ◦ Forti. OS 6. 0: 6. 0. 0 ~ 6. 0. 4 CVE-2018 -13381 ◦ Forti. OS 5. 4 and below ◦ Forti. OS 5. 6: 5. 6. 0 ~ 5. 6. 7 ◦ Forti. OS 6. 0: 6. 0. 0 ~ 6. 0. 4 CVE-2018 -13383 ◦ Forti. OS 5. 6. 10 and below ◦ Forti. OS 6. 0: 6. 0. 0 ~ 6. 0. 4 CVE-2018 -13382 ◦ Forti. OS 5. 4: 5. 4. 1 ~ 5. 4. 10 ◦ Forti. OS 5. 6: 5. 6. 0 ~ 5. 6. 8 ◦ Forti. OS 6. 0: 6. 0. 0 ~ 6. 0. 4 11
Pulse Secure SSL VPN 漏洞 13
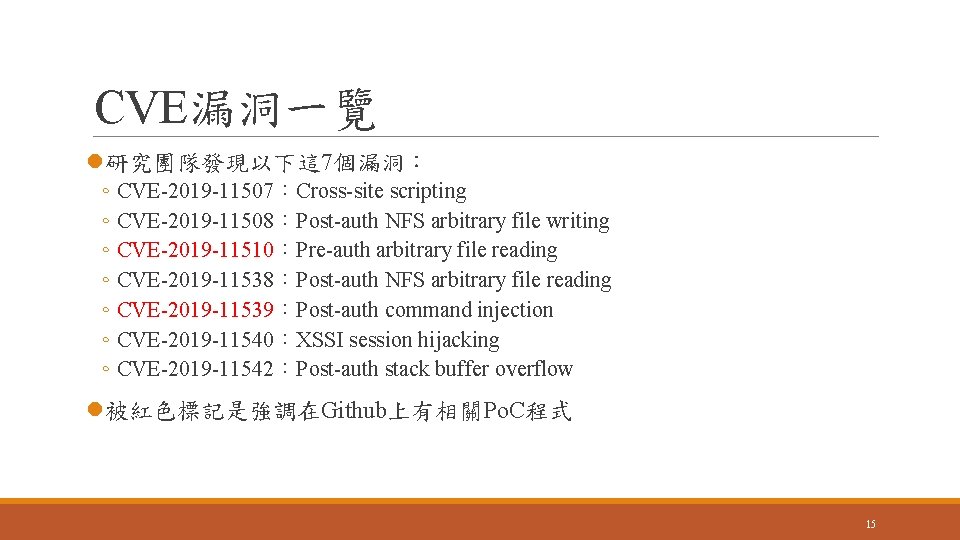
CVE漏洞一覽 l研究團隊發現以下這 7個漏洞: ◦ CVE-2019 -11507:Cross-site scripting ◦ CVE-2019 -11508:Post-auth NFS arbitrary file writing ◦ CVE-2019 -11510:Pre-auth arbitrary file reading ◦ CVE-2019 -11538:Post-auth NFS arbitrary file reading ◦ CVE-2019 -11539:Post-auth command injection ◦ CVE-2019 -11540:XSSI session hijacking ◦ CVE-2019 -11542:Post-auth stack buffer overflow l被紅色標記是強調在Github上有相關Po. C程式 15
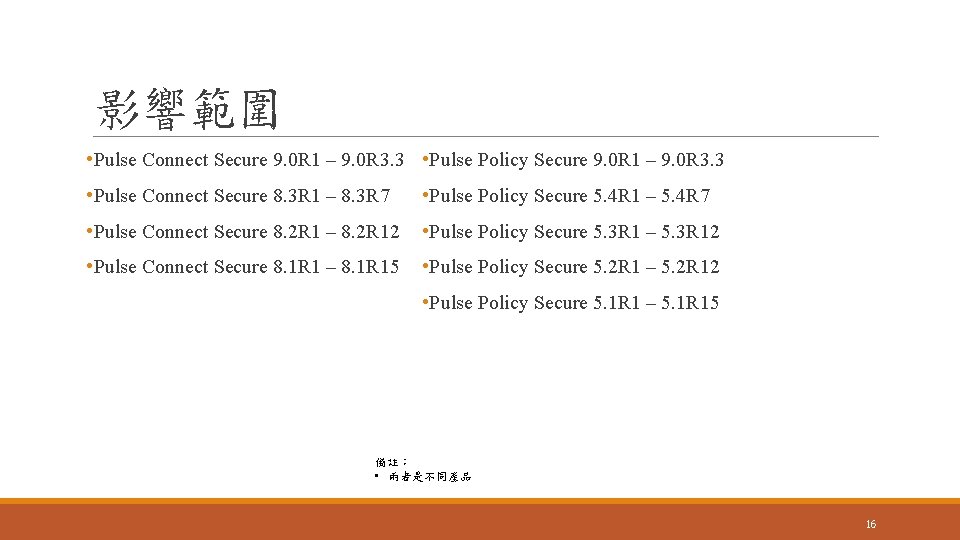
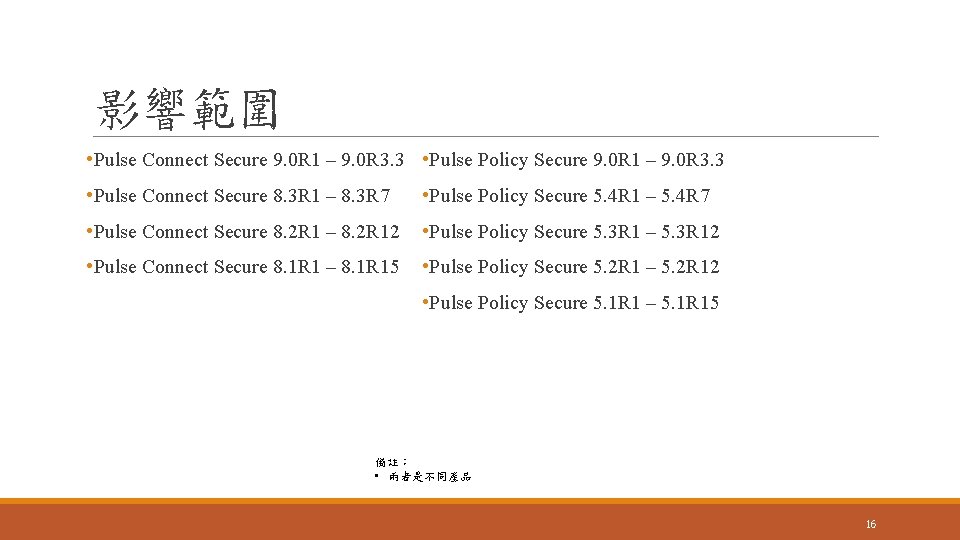
影響範圍 • Pulse Connect Secure 9. 0 R 1 – 9. 0 R 3. 3 • Pulse Policy Secure 9. 0 R 1 – 9. 0 R 3. 3 • Pulse Connect Secure 8. 3 R 1 – 8. 3 R 7 • Pulse Policy Secure 5. 4 R 1 – 5. 4 R 7 • Pulse Connect Secure 8. 2 R 1 – 8. 2 R 12 • Pulse Policy Secure 5. 3 R 1 – 5. 3 R 12 • Pulse Connect Secure 8. 1 R 1 – 8. 1 R 15 • Pulse Policy Secure 5. 2 R 1 – 5. 2 R 12 • Pulse Policy Secure 5. 1 R 1 – 5. 1 R 15 備註: • 兩者是不同產品 16
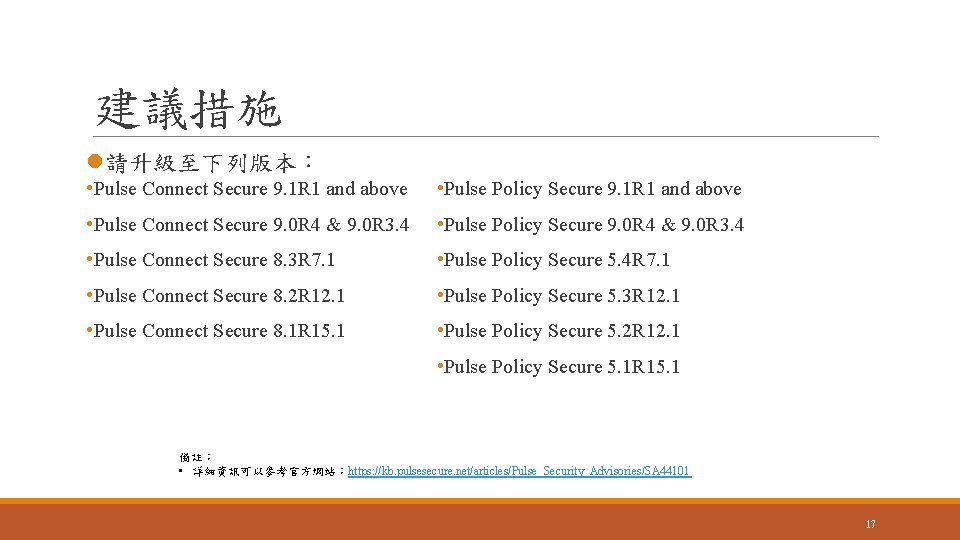
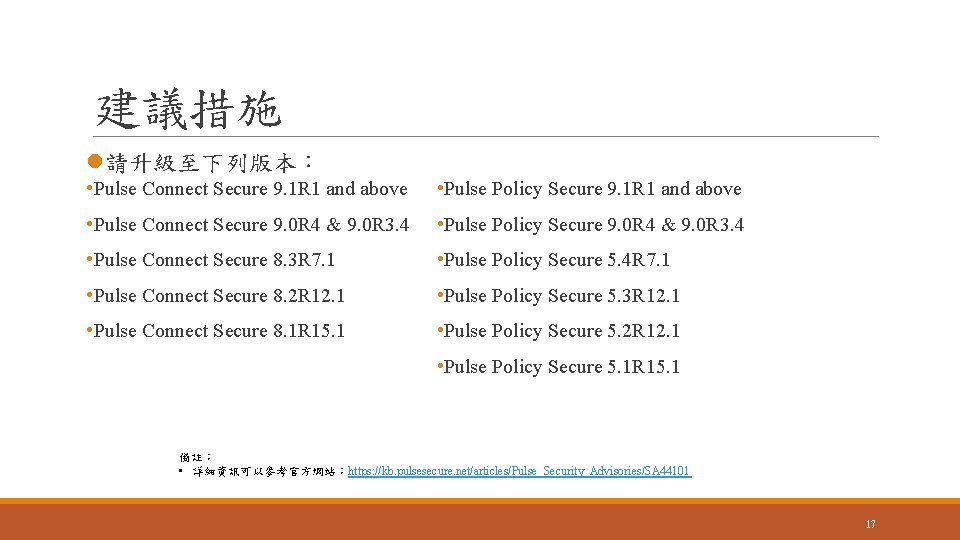
建議措施 l請升級至下列版本: • Pulse Connect Secure 9. 1 R 1 and above • Pulse Policy Secure 9. 1 R 1 and above • Pulse Connect Secure 9. 0 R 4 & 9. 0 R 3. 4 • Pulse Policy Secure 9. 0 R 4 & 9. 0 R 3. 4 • Pulse Connect Secure 8. 3 R 7. 1 • Pulse Policy Secure 5. 4 R 7. 1 • Pulse Connect Secure 8. 2 R 12. 1 • Pulse Policy Secure 5. 3 R 12. 1 • Pulse Connect Secure 8. 1 R 15. 1 • Pulse Policy Secure 5. 2 R 12. 1 • Pulse Policy Secure 5. 1 R 15. 1 備註: • 詳細資訊可以參考官方網站:https: //kb. pulsesecure. net/articles/Pulse_Security_Advisories/SA 44101 17
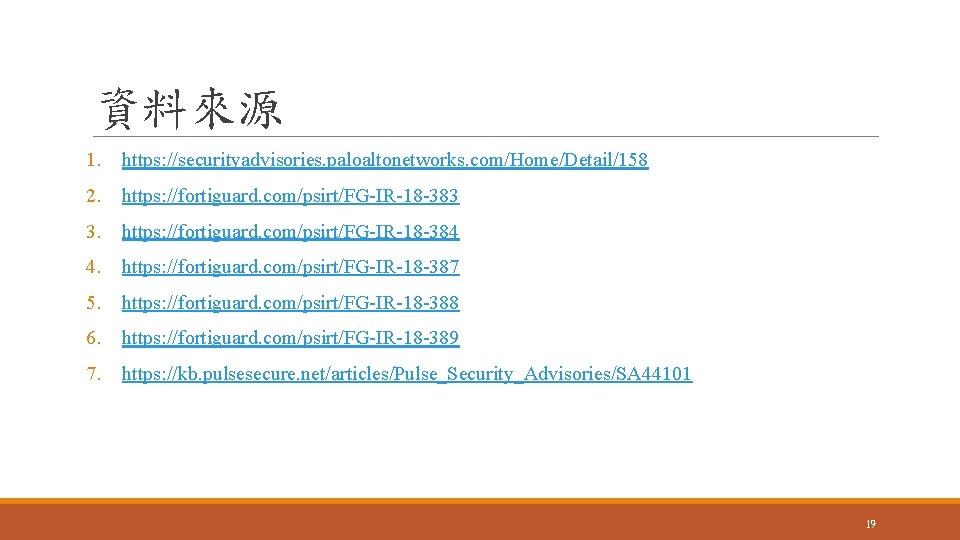
資料來源 1. https: //securityadvisories. paloaltonetworks. com/Home/Detail/158 2. https: //fortiguard. com/psirt/FG-IR-18 -383 3. https: //fortiguard. com/psirt/FG-IR-18 -384 4. https: //fortiguard. com/psirt/FG-IR-18 -387 5. https: //fortiguard. com/psirt/FG-IR-18 -388 6. https: //fortiguard. com/psirt/FG-IR-18 -389 7. https: //kb. pulsesecure. net/articles/Pulse_Security_Advisories/SA 44101 19