KReach A Tool for Reachability in Petri Nets
KReach: A Tool for Reachability in Petri Nets Alex Dixon Ranko Lazić
![One Small Net p 0 p 1 Transitions: { [-1, 1], [2, -1] } One Small Net p 0 p 1 Transitions: { [-1, 1], [2, -1] }](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-2.jpg)
One Small Net p 0 p 1 Transitions: { [-1, 1], [2, -1] }
![The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1, The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1,](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-3.jpg)
The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1, 1], [2, -1] } RP: Can we get from the initial marking to the target marking only by applying transitions in any order?
![Complexity • Lower bound – Not Elementary [1] • Upper bound - Ackermannian [2] Complexity • Lower bound – Not Elementary [1] • Upper bound - Ackermannian [2]](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-4.jpg)
Complexity • Lower bound – Not Elementary [1] • Upper bound - Ackermannian [2] • Coverability is EXPSPACE-Complete [3] [1] Czerwinski et al. , STOC 2019 [2] Leroux & Schmitz, LICS 2019 [3] Rackoff, TCS 1978
![Kosaraju’s Algorithm[4] • Builds on the work of Mayr, Sacerdote, Tenney • Is a Kosaraju’s Algorithm[4] • Builds on the work of Mayr, Sacerdote, Tenney • Is a](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-5.jpg)
Kosaraju’s Algorithm[4] • Builds on the work of Mayr, Sacerdote, Tenney • Is a complete algorithm for deciding reachability • Can be implemented and tested (this work) [4] Kosaraju, STOC 1982
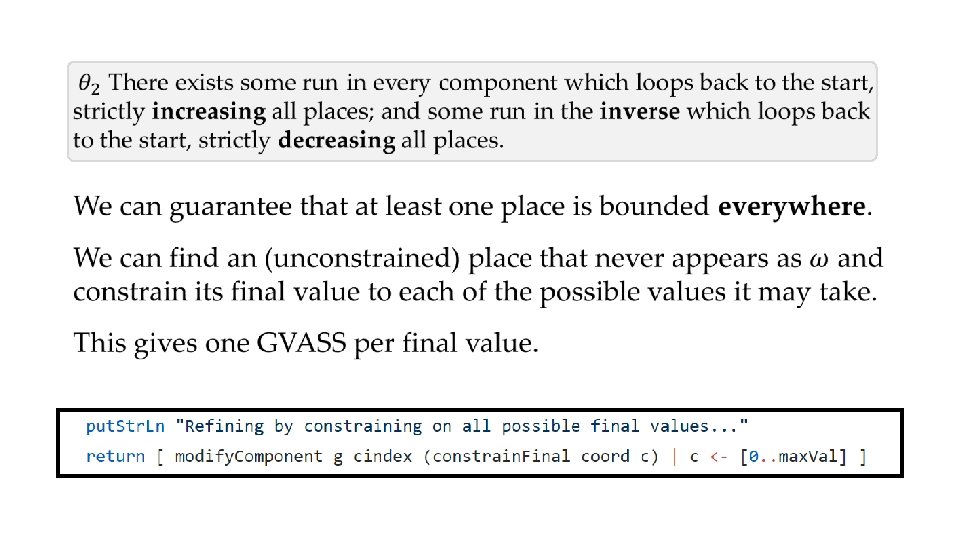
The algorithm, quickly • Search • Through the space of decompositions • Until: • One such decomposition fulfils our predicate (Reachable! ) • We exhaust the tree (Not reachable. ) As checking the predicate and decomposing the tree will terminate, and the tree is finite, the algorithm will halt.
![Resources for Kosaraju’s Algorithm: • C. Reutenauer, The mathematics of Petri nets[5] • S. Resources for Kosaraju’s Algorithm: • C. Reutenauer, The mathematics of Petri nets[5] • S.](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-7.jpg)
Resources for Kosaraju’s Algorithm: • C. Reutenauer, The mathematics of Petri nets[5] • S. Lasota, VASS reachability in three steps[6] [5] Translated into English by by Ian Craig [6] See Arxiv
This work provides 1. KReach - A complete implementation of Kosaraju’s algorithm (hence a general purpose reachability checker for Petri nets) 2. A readable implementation of the algorithm in code 3. A suite of VASS programming libraries for Haskell, including an implementation of Karp & Miller’s coverability checker
Implementation
![The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1, The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1,](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-10.jpg)
The Reachability Problem Initial marking [1, 0] Target marking [0, 4] Transitions: { [-1, 1], [2, -1] } Remark: A Petri Net is a VAS (aka a singleton VASS)
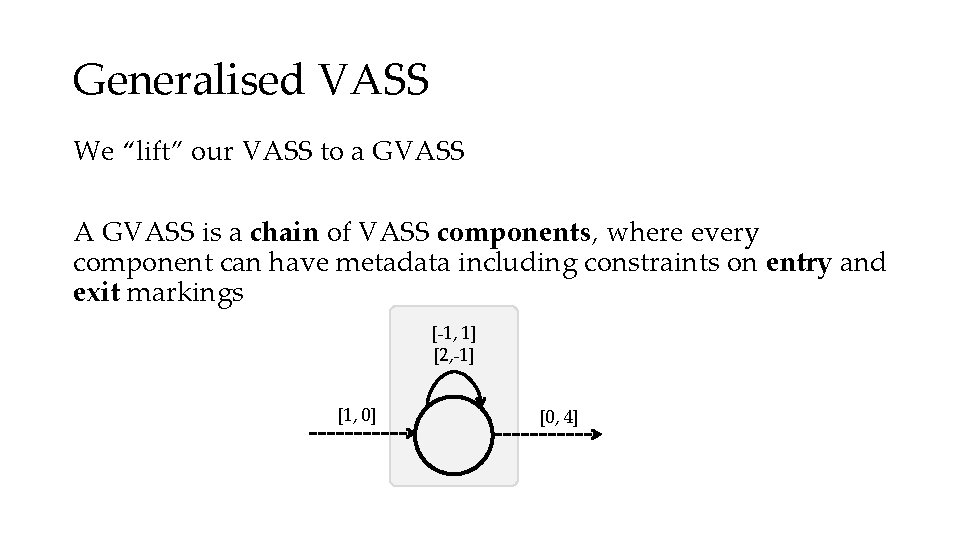
Generalised VASS We “lift” our VASS to a GVASS A GVASS is a chain of VASS components, where every component can have metadata including constraints on entry and exit markings [-1, 1] [2, -1] [1, 0] [0, 4]
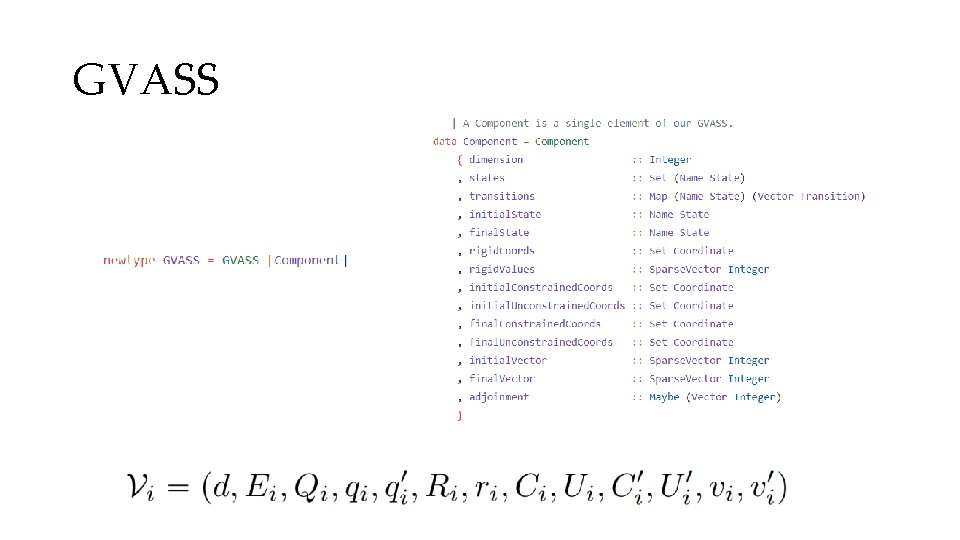
GVASS
![[Aside]: SCC If our VASS is multi-state, we will need to decompose it into [Aside]: SCC If our VASS is multi-state, we will need to decompose it into](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-13.jpg)
[Aside]: SCC If our VASS is multi-state, we will need to decompose it into strongly connected components. This will create one GVASS for each path through the SCCs (exponential!) We will do this at any time that non-strongly-connected components arise, and assume hereon that all components are strongly connected.
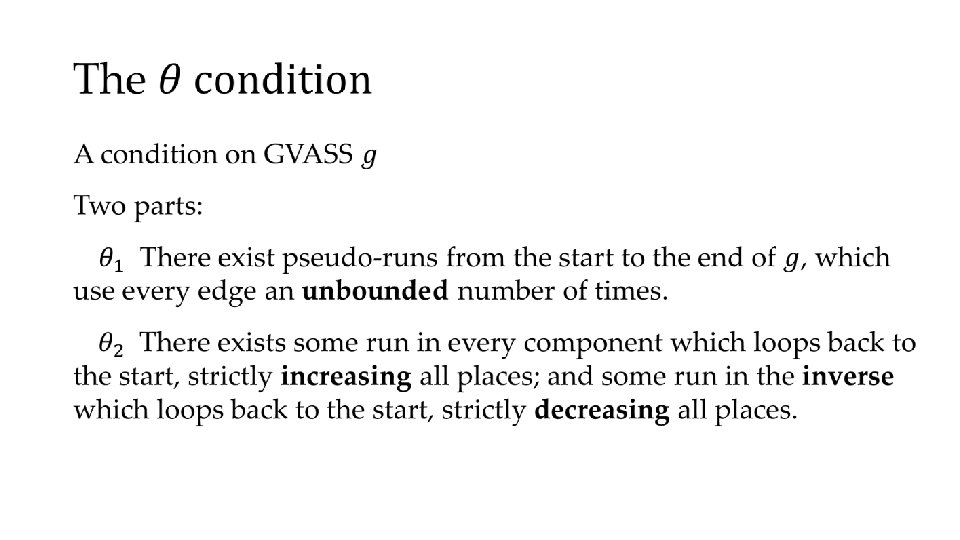
This is an Integer Linear Programming problem Variables: Edges (transitions) Coefficients: Edge weightings Equations for: • Parikh image • Constrained values • Kirchoff’s laws [-1, 1] [2, -1] [1, 0] [0, 4]
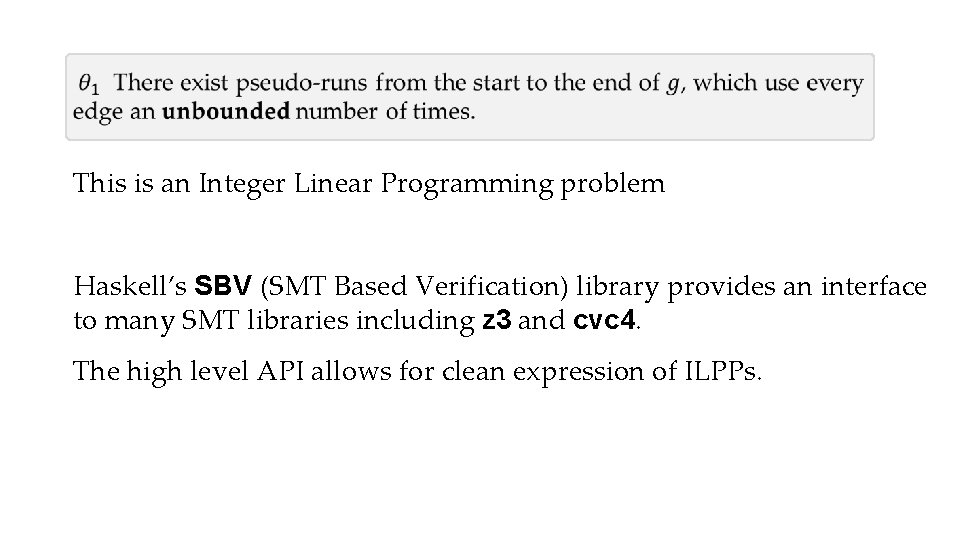
This is an Integer Linear Programming problem Haskell’s SBV (SMT Based Verification) library provides an interface to many SMT libraries including z 3 and cvc 4. The high level API allows for clean expression of ILPPs.
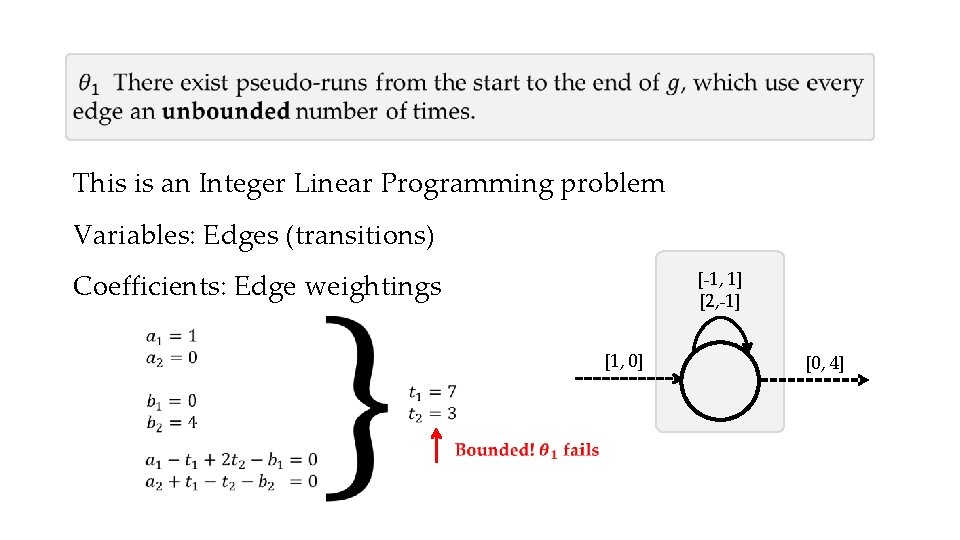
This is an Integer Linear Programming problem Variables: Edges (transitions) Coefficients: Edge weightings [-1, 1] [2, -1] [1, 0] [0, 4]
![• [-1, 1] [1, 0] [+2, -1] [-1, 1] [+2, -1] [0, 4] • [-1, 1] [1, 0] [+2, -1] [-1, 1] [+2, -1] [0, 4]](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-18.jpg)
• [-1, 1] [1, 0] [+2, -1] [-1, 1] [+2, -1] [0, 4] We get a new GVASS for every possible assignment of values!
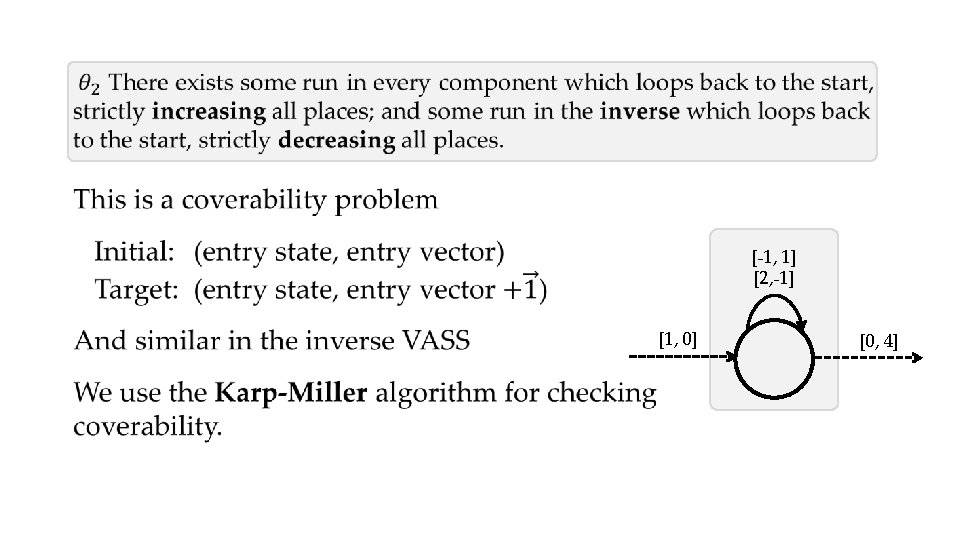
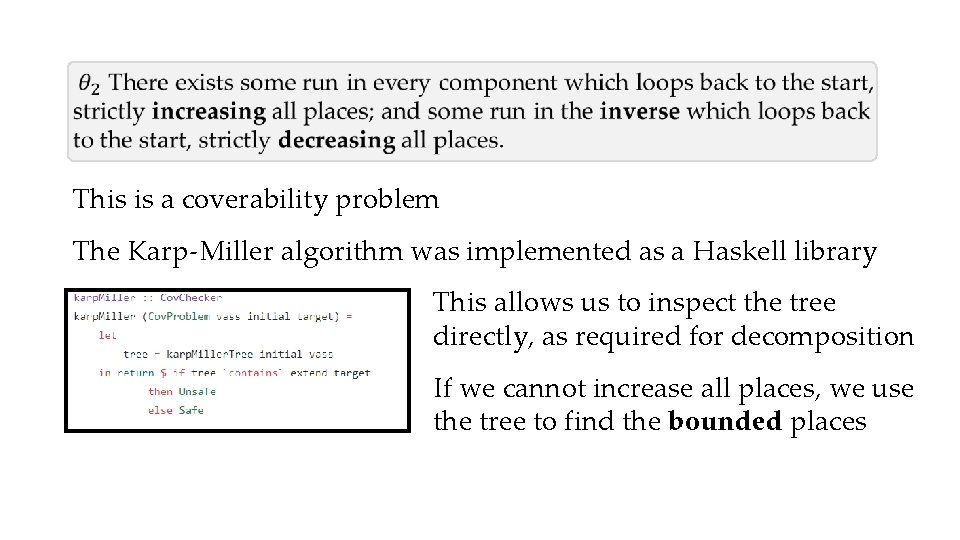
This is a coverability problem The Karp-Miller algorithm was implemented as a Haskell library This allows us to inspect the tree directly, as required for decomposition If we cannot increase all places, we use the tree to find the bounded places
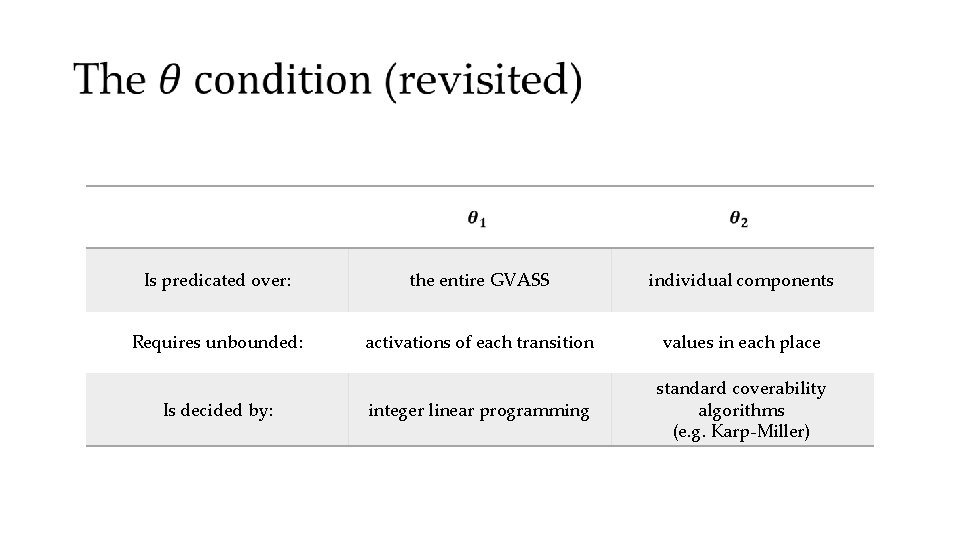
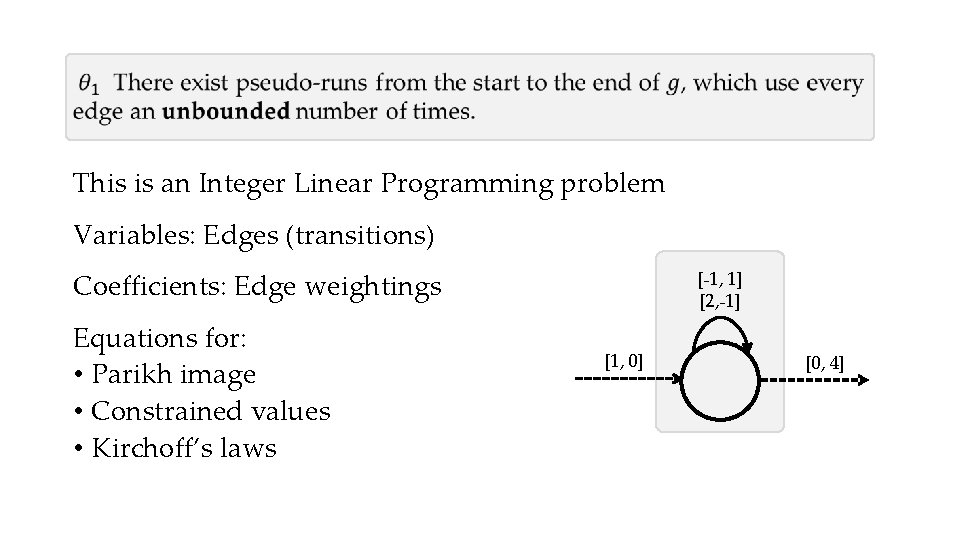
Is predicated over: the entire GVASS individual components Requires unbounded: activations of each transition values in each place integer linear programming standard coverability algorithms (e. g. Karp-Miller) Is decided by:
Usage
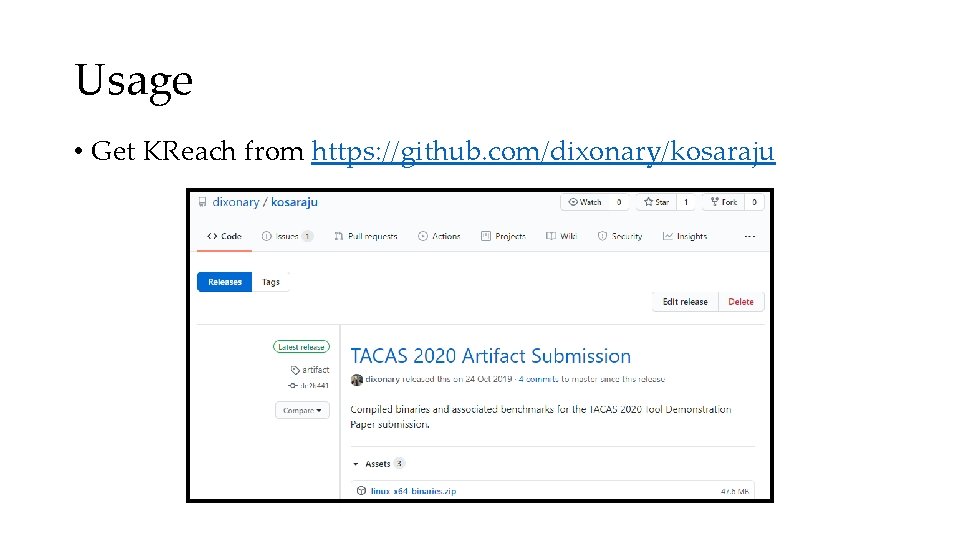
Usage • Get KReach from https: //github. com/dixonary/kosaraju
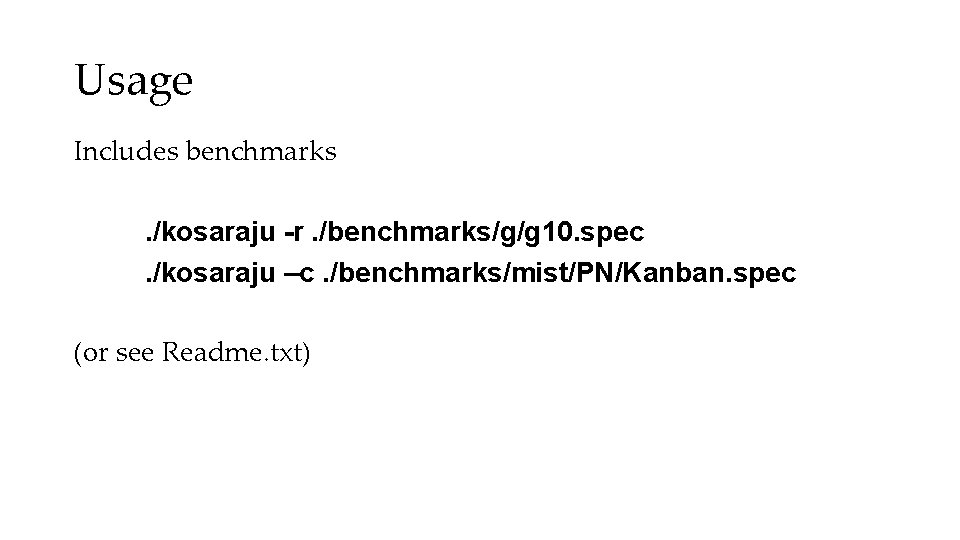
Usage Includes benchmarks. /kosaraju -r. /benchmarks/g/g 10. spec. /kosaraju –c. /benchmarks/mist/PN/Kanban. spec (or see Readme. txt)

Results
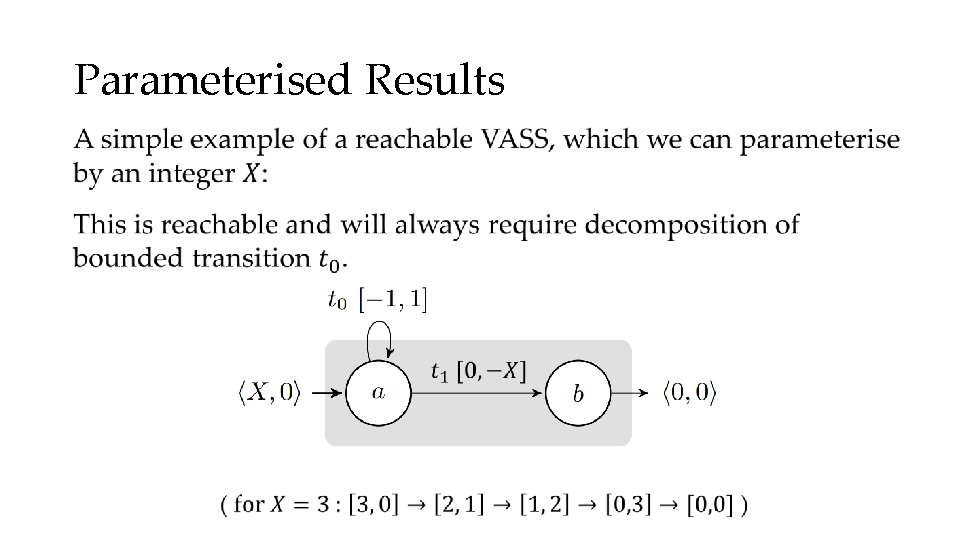
Parameterised Results •
Early Outs •
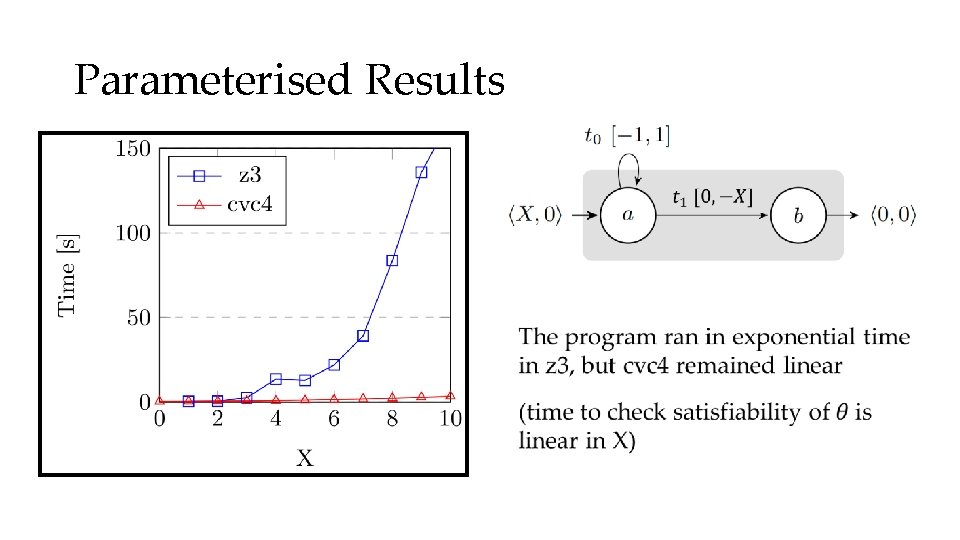
Parameterised Results •
The fast and the curious The dataset used includes samples from MIST, SOTER, BUG_TRACKING and others. Non-synthetic problems with reachable answers (“unsafe” coverability problems) often require the tree to be expanded. Some non-reachable answers (“safe” coverability problems) still require the tree to be unfolded some number of steps. KReach is unable* to solve any problems which induce large decomposition trees. * Within the given time and memory constraints [4 GB, 1 hr]
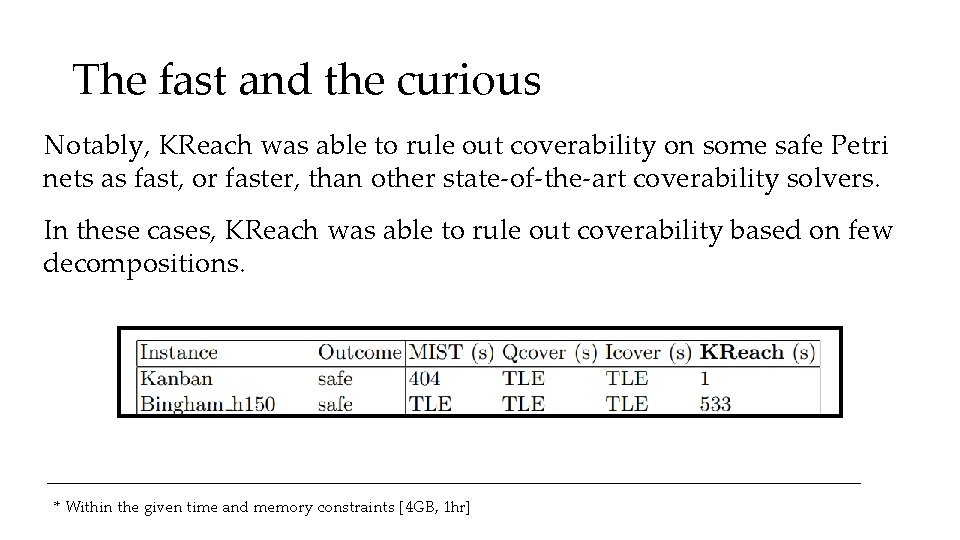
The fast and the curious Notably, KReach was able to rule out coverability on some safe Petri nets as fast, or faster, than other state-of-the-art coverability solvers. In these cases, KReach was able to rule out coverability based on few decompositions. * Within the given time and memory constraints [4 GB, 1 hr]
Further Work Build additional parsers for Petri Net interchange formats (. pnml) Investigate the feasibility of coverability tools which make use of invariants that arise from the ILP construction Introduce optimisations based on developments from the Ackermannian upper bound proof of Leroux & Schmitz (2019)
![[Aside]: Petri Puzzle [Aside]: Petri Puzzle](http://slidetodoc.com/presentation_image_h/7d62f0aab80d489e3222951c2fb5323e/image-34.jpg)
[Aside]: Petri Puzzle
- Slides: 34