Knapsack Cryptosystems Dinara Barshevich JASS 05 St Petersburg
Knapsack Cryptosystems Dinara Barshevich JASS’ 05 St. Petersburg 11/27/2020 Knapsack Cryptosystems 1
Brief historical background 1976, Diffie & Hellman – Public Key Cryptosystem n 1977 RSA – the first incarnation of such system n 1978 Merkle – Hellman Cryptosystem n 1980 s years: attacks to MH n 11/27/2020 Knapsack Cryptosystems 2
Agenda Idea of Public-Key Cryptosystems n Knapsack problem: setting, comlexity and basic analyses n Knapsack Public-Key Cryptosystems n Algorithm of Merkle – Hellman n Attacks to Merkle – Hellman Cryptosystem n What next? n 11/27/2020 Knapsack Cryptosystems 3
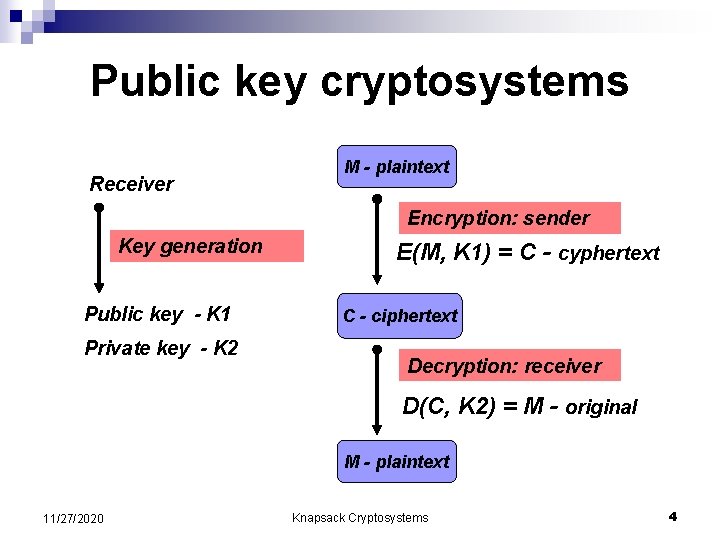
Public key cryptosystems Receiver M - plaintext Encryption: sender Key generation Public key - K 1 Private key - K 2 E(M, K 1) = C - cyphertext C - ciphertext Decryption: receiver D(C, K 2) = M - original M - plaintext 11/27/2020 Knapsack Cryptosystems 4
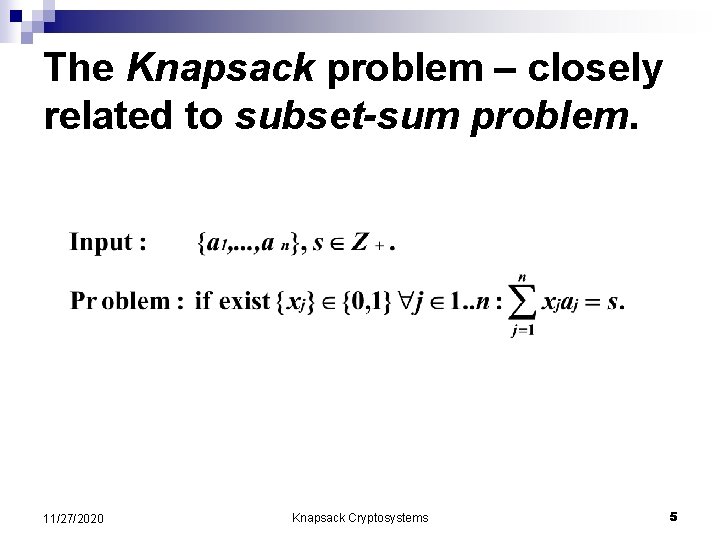
The Knapsack problem – closely related to subset-sum problem. 11/27/2020 Knapsack Cryptosystems 5
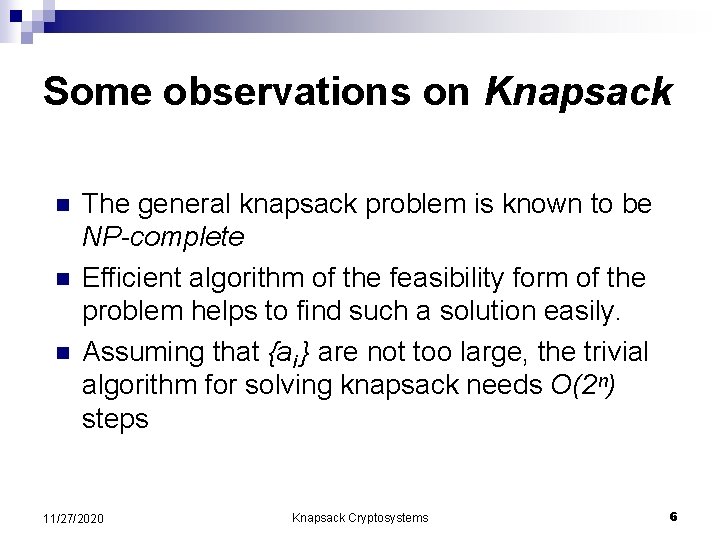
Some observations on Knapsack n n n The general knapsack problem is known to be NP-complete Efficient algorithm of the feasibility form of the problem helps to find such a solution easily. Assuming that {ai } are not too large, the trivial algorithm for solving knapsack needs O(2ⁿ) steps 11/27/2020 Knapsack Cryptosystems 6
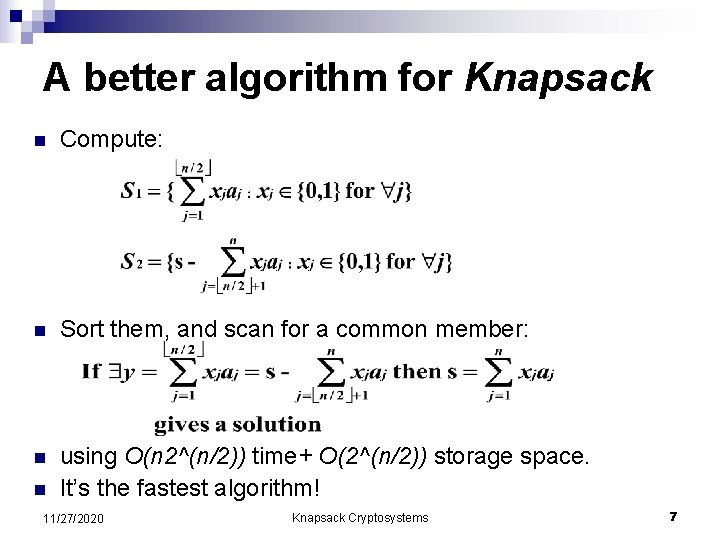
A better algorithm for Knapsack n Compute: n Sort them, and scan for a common member: n using O(n 2^(n/2)) time+ O(2^(n/2)) storage space. It’s the fastest algorithm! n 11/27/2020 Knapsack Cryptosystems 7
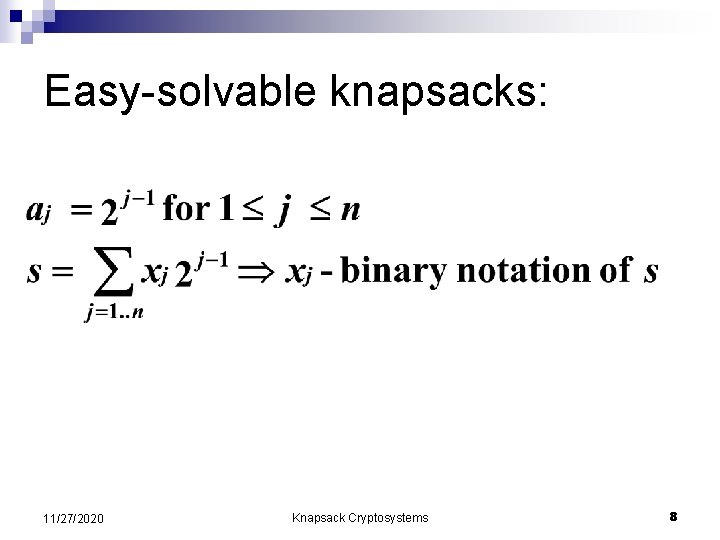
Easy-solvable knapsacks: 11/27/2020 Knapsack Cryptosystems 8
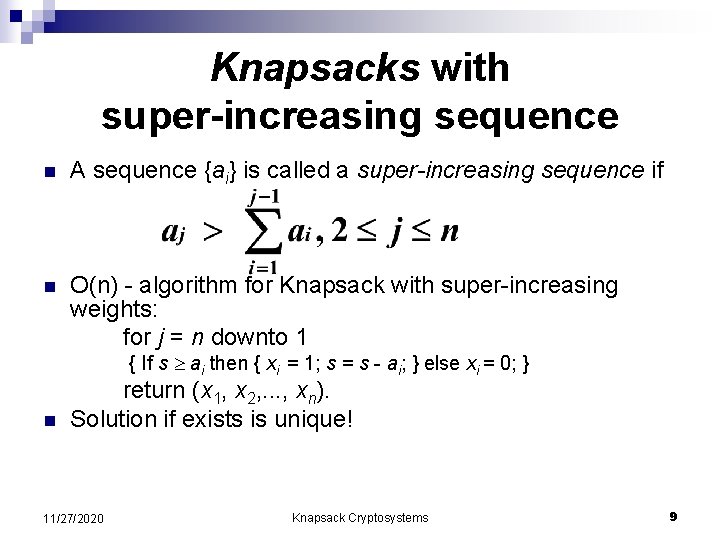
Knapsacks with super-increasing sequence n A sequence {ai} is called a super-increasing sequence if n O(n) - algorithm for Knapsack with super-increasing weights: for j = n downto 1 { If s ai then { xi = 1; s = s - ai; } else xi = 0; } n return (x 1, x 2, . . . , xn). Solution if exists is unique! 11/27/2020 Knapsack Cryptosystems 9
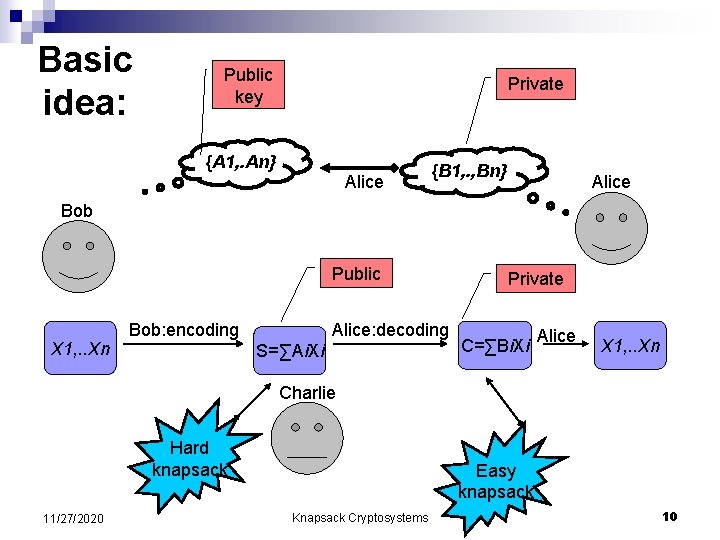
Basic idea: Public key Private {A 1, . An} Alice {B 1, . , Bn} Alice Bob Public X 1, . . Xn Bob: encoding Alice: decoding S=∑Ai. Xi Private C=∑Bi. Xi Alice X 1, . . Xn Charlie Hard knapsack 11/27/2020 Easy knapsack Knapsack Cryptosystems 10
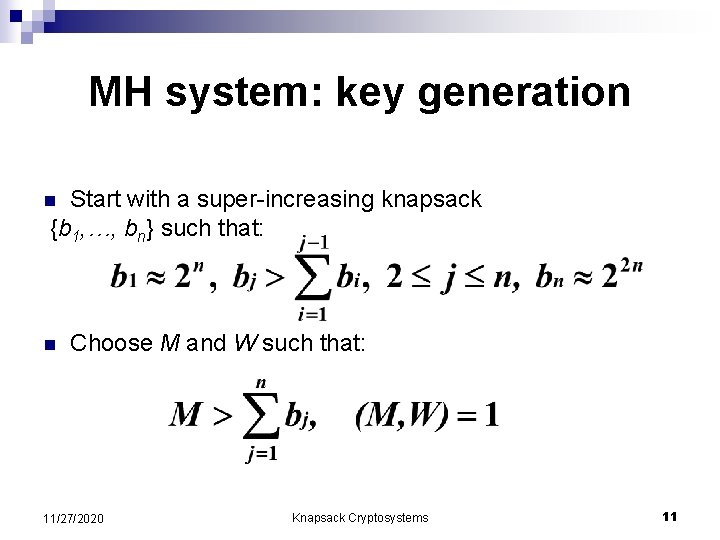
MH system: key generation Start with a super-increasing knapsack {b 1, …, bn} such that: n n Choose M and W such that: 11/27/2020 Knapsack Cryptosystems 11
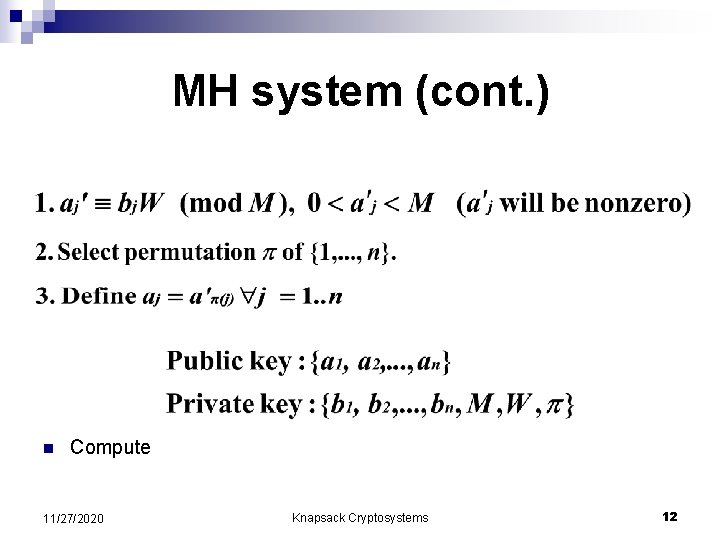
MH system (cont. ) n Compute 11/27/2020 Knapsack Cryptosystems 12
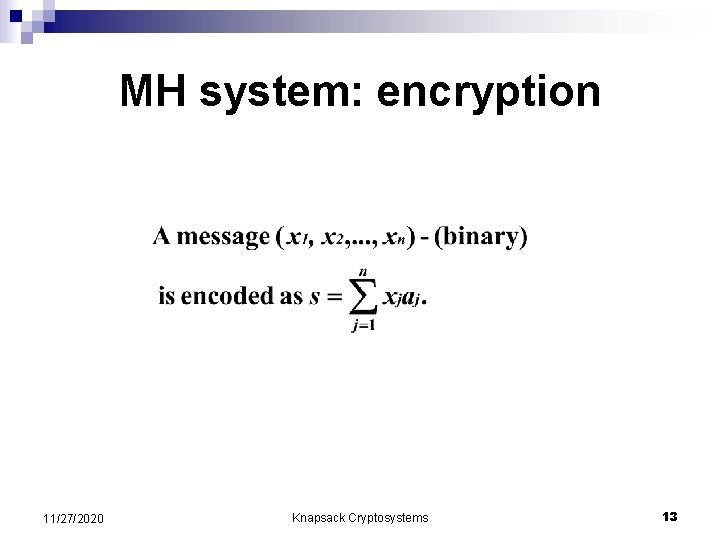
MH system: encryption 11/27/2020 Knapsack Cryptosystems 13
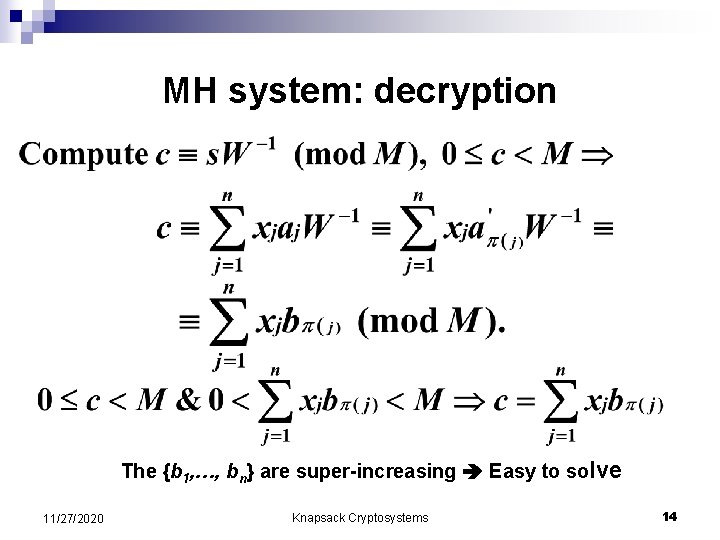
MH system: decryption The {b 1, …, bn} are super-increasing Easy to solve 11/27/2020 Knapsack Cryptosystems 14
Two variants of Merkle. Hellman cryptosystem singly-iterated Merkle-Hellman cryptosystem n multiply-iterated Merkle-Hellman cryptosystem n 11/27/2020 Knapsack Cryptosystems 15
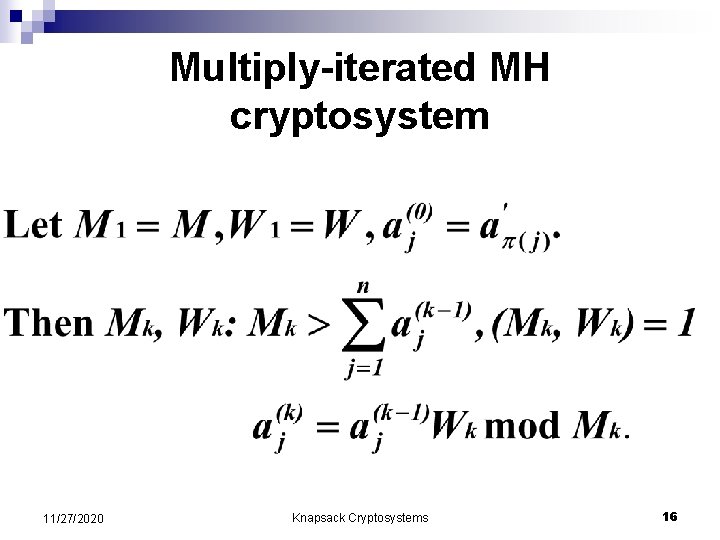
Multiply-iterated MH cryptosystem 11/27/2020 Knapsack Cryptosystems 16
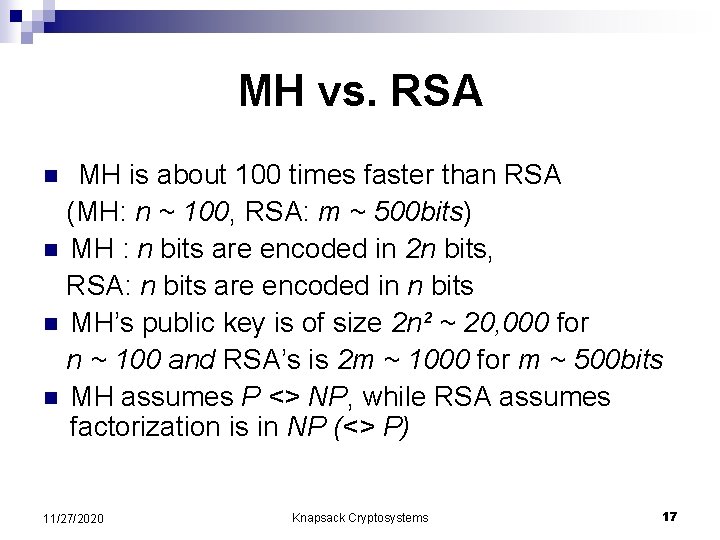
MH vs. RSA MH is about 100 times faster than RSA (MH: n ~ 100, RSA: m ~ 500 bits) n MH : n bits are encoded in 2 n bits, RSA: n bits are encoded in n bits n MH’s public key is of size 2 n² ~ 20, 000 for n ~ 100 and RSA’s is 2 m ~ 1000 for m ~ 500 bits n MH assumes P <> NP, while RSA assumes factorization is in NP (<> P) n 11/27/2020 Knapsack Cryptosystems 17
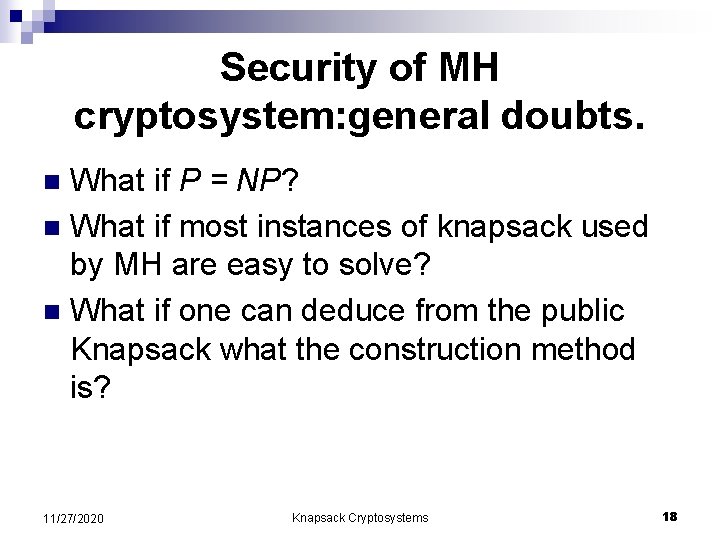
Security of MH cryptosystem: general doubts. What if P = NP? n What if most instances of knapsack used by MH are easy to solve? n What if one can deduce from the public Knapsack what the construction method is? n 11/27/2020 Knapsack Cryptosystems 18
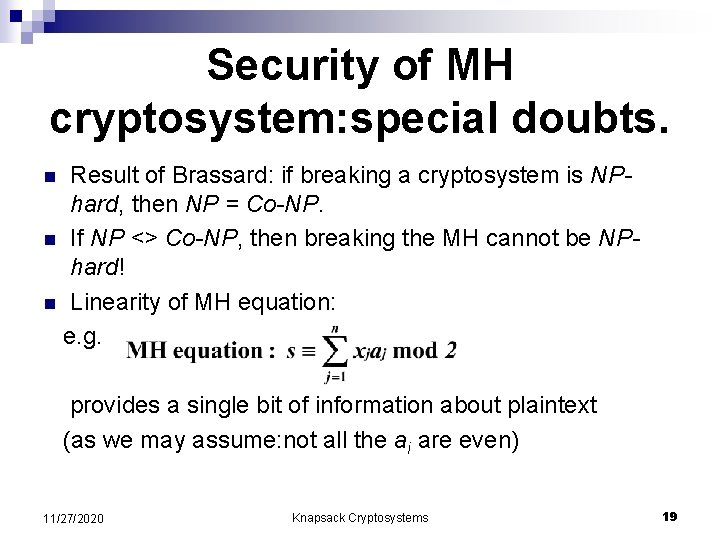
Security of MH cryptosystem: special doubts. Result of Brassard: if breaking a cryptosystem is NPhard, then NP = Co-NP. n If NP <> Co-NP, then breaking the MH cannot be NPhard! n Linearity of MH equation: e. g. n provides a single bit of information about plaintext (as we may assume: not all the ai are even) 11/27/2020 Knapsack Cryptosystems 19
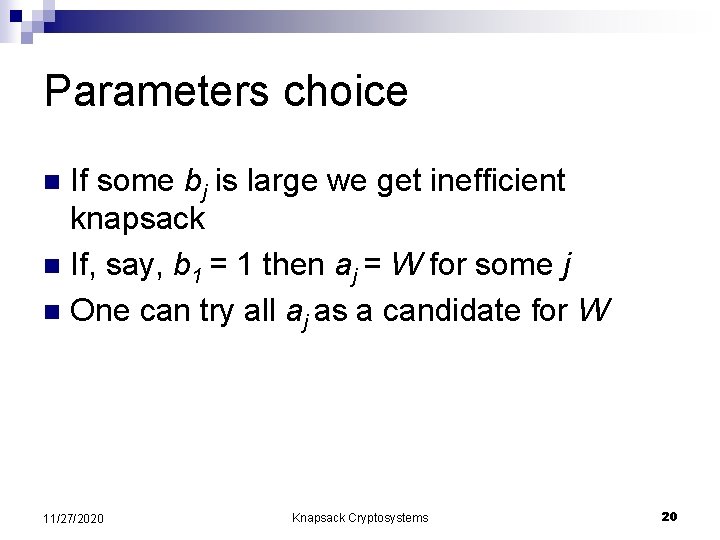
Parameters choice If some bj is large we get inefficient knapsack n If, say, b 1 = 1 then aj = W for some j n One can try all aj as a candidate for W n 11/27/2020 Knapsack Cryptosystems 20
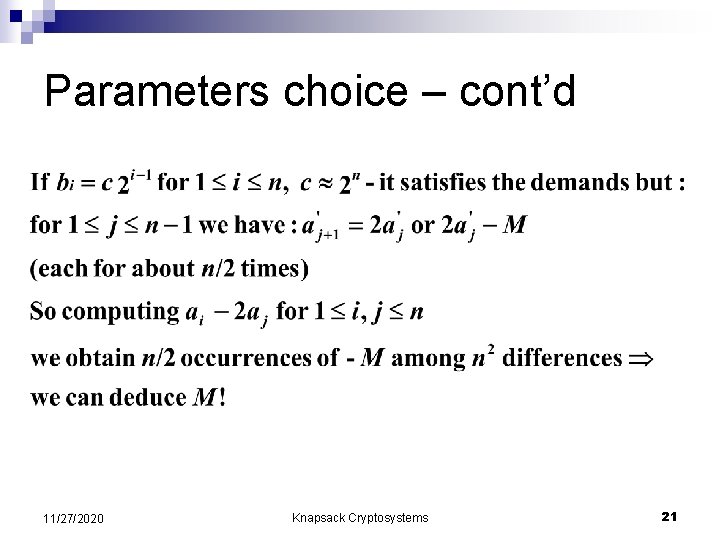
Parameters choice – cont’d 11/27/2020 Knapsack Cryptosystems 21
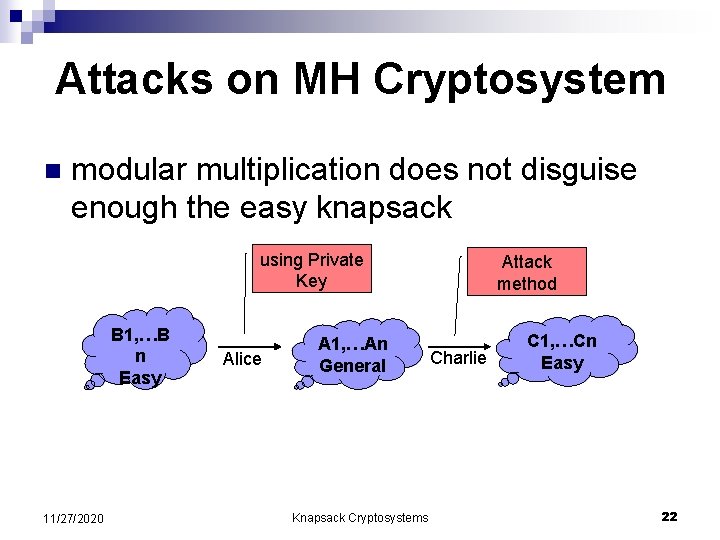
Attacks on MH Cryptosystem n modular multiplication does not disguise enough the easy knapsack using Private Key B 1, …B n Easy 11/27/2020 Alice A 1, …An General Knapsack Cryptosystems Attack method Charlie C 1, …Cn Easy 22
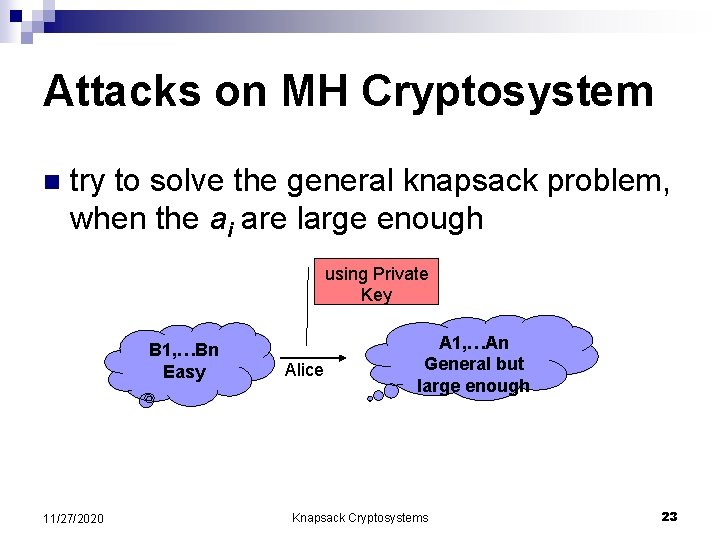
Attacks on MH Cryptosystem n try to solve the general knapsack problem, when the ai are large enough using Private Key B 1, …Bn Easy 11/27/2020 Alice A 1, …An General but large enough Knapsack Cryptosystems 23
Attacks on MH knapsack cryptosystem Rely on the fact that the modular multiplication does not disguise enough the easy knapsack: 1. Shamir’s polynomial algorithm for the singly-iterated Merkle-Hellman, 1982 2. Brickell’s attack on the multiply-iterated Merkle-Hellman, 1985 n 11/27/2020 Knapsack Cryptosystems 24
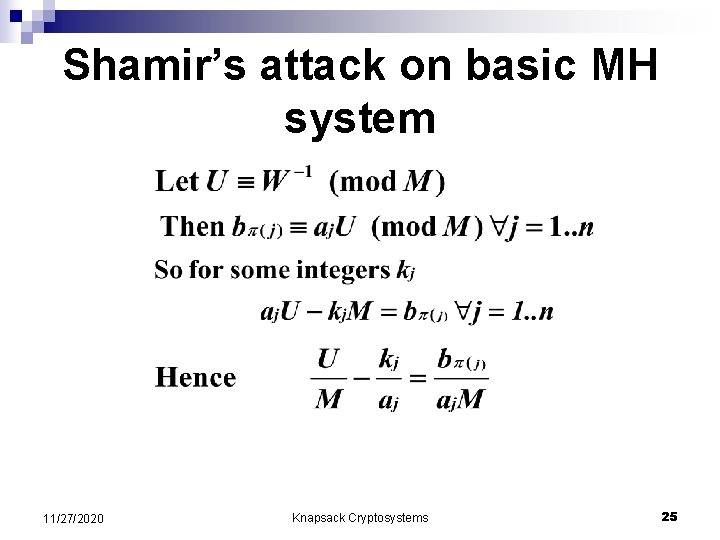
Shamir’s attack on basic MH system 11/27/2020 Knapsack Cryptosystems 25
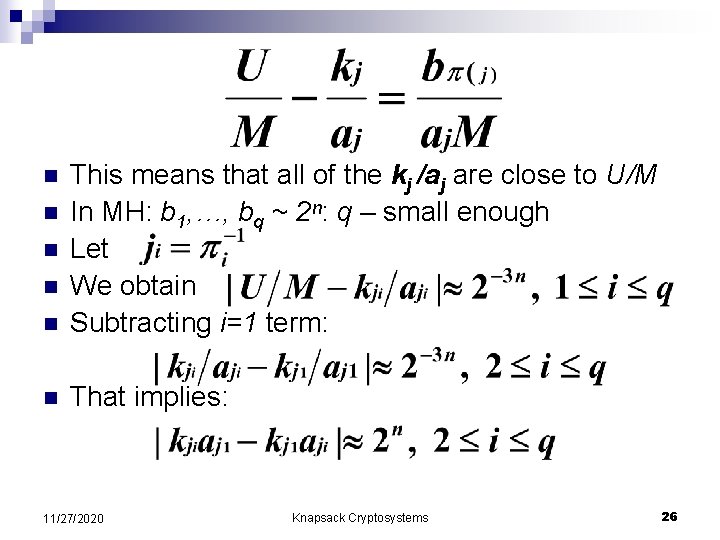
n This means that all of the kj /aj are close to U/M In MH: b 1, …, bq ~ 2ⁿ: q – small enough Let We obtain Subtracting i=1 term: n That implies: n n 11/27/2020 Knapsack Cryptosystems 26
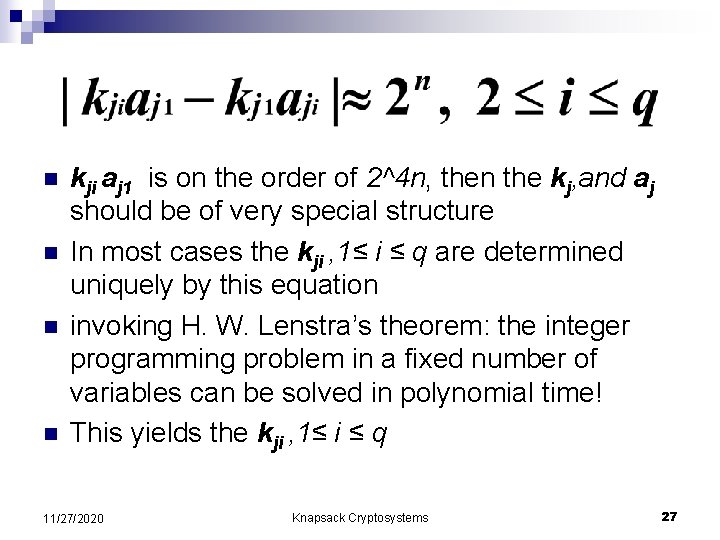
n n kji aj 1 is on the order of 2^4 n, then the kj, and aj should be of very special structure In most cases the kji , 1≤ i ≤ q are determined uniquely by this equation invoking H. W. Lenstra’s theorem: the integer programming problem in a fixed number of variables can be solved in polynomial time! This yields the kji , 1≤ i ≤ q 11/27/2020 Knapsack Cryptosystems 27
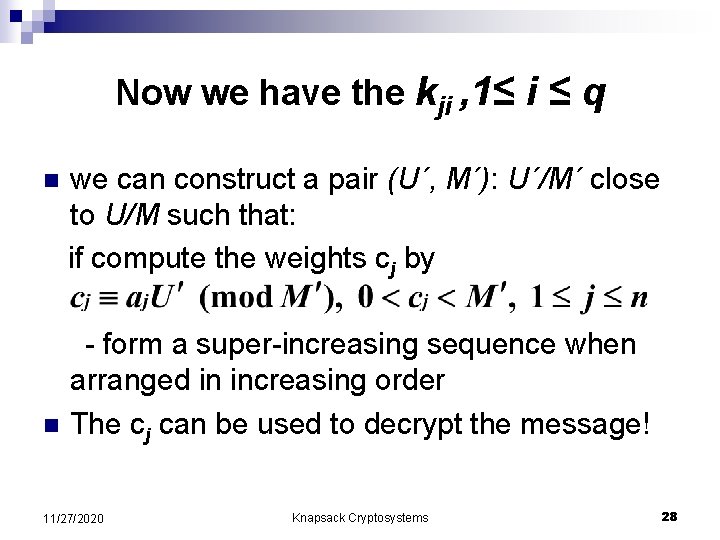
Now we have the kji , 1≤ i ≤ q n n we can construct a pair (U´, M´): U´/M´ close to U/M such that: if compute the weights cj by - form a super-increasing sequence when arranged in increasing order The cj can be used to decrypt the message! 11/27/2020 Knapsack Cryptosystems 28
But how to find j 1, …, jq ? As permutation π is secret, we do not have j 1, …, jq n The solution is easy: the cryptanalyst considers all possible choices of them, and still remains in polynomial time! n 11/27/2020 Knapsack Cryptosystems 29
Difficulties of Shamir’s method n n n The crucial tool in the attack was Lenstra’s result on integer programming in a fixed number of variables Lenstra’s algorithm running time is given by a high degree polynomial – never implemented! Continued fraction can be used instead of Lenstra’s result, but when the bj are large enough, it fails 11/27/2020 Knapsack Cryptosystems 30
Attacks to low-density general knapsack problems try to solve the general knapsack problem, when the ai are large enough n 2 famous attacks: - Lagarias and Odlyzko, 1983 - Brickell low-density attack, 1984 n 11/27/2020 Knapsack Cryptosystems 31
On integer lattices n n n An integer lattice is an additive subgroup of Zⁿ that contains n linearly independent vectors over Rⁿ A basis (v 1 , …, vn ) of L is a set of elements of L such that L = {z 1 v 1 +…+ zn vn : zi – integer} Input: (v 1 , …, vn ) – basis of L - lattice SVL: Find the shortest non-zero vector of L quite hard problem – yet not proved! 11/27/2020 Knapsack Cryptosystems 32
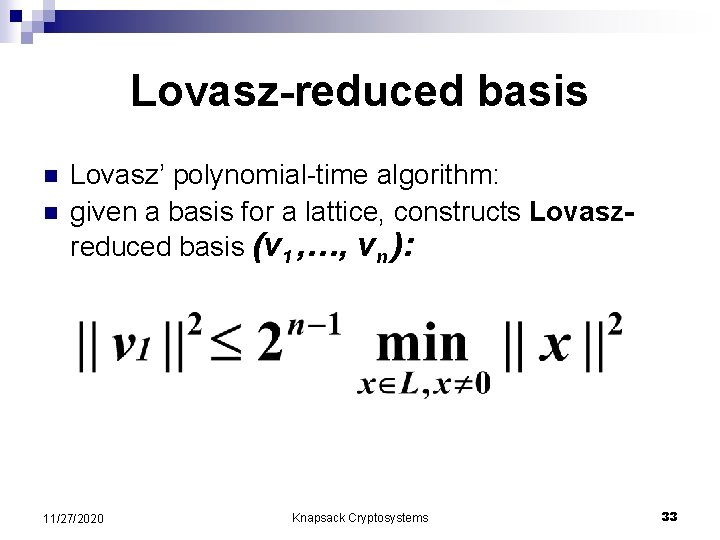
Lovasz-reduced basis n n Lovasz’ polynomial-time algorithm: given a basis for a lattice, constructs Lovaszreduced basis (v 1 , …, vn ): 11/27/2020 Knapsack Cryptosystems 33
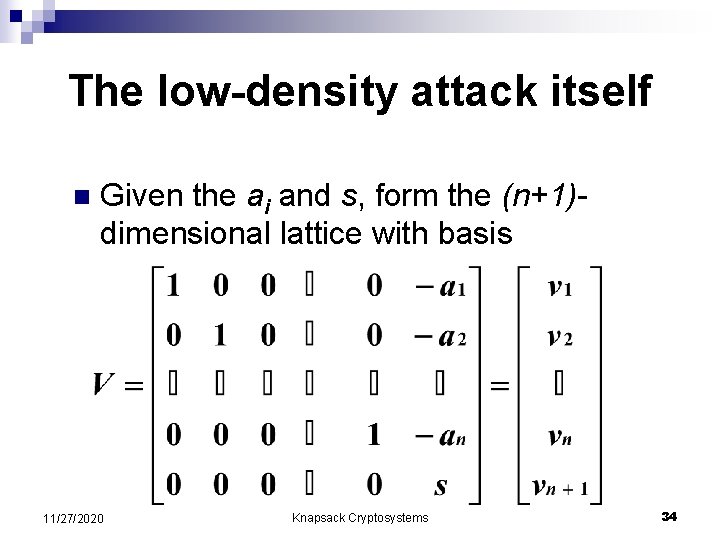
The low-density attack itself n Given the ai and s, form the (n+1)dimensional lattice with basis 11/27/2020 Knapsack Cryptosystems 34
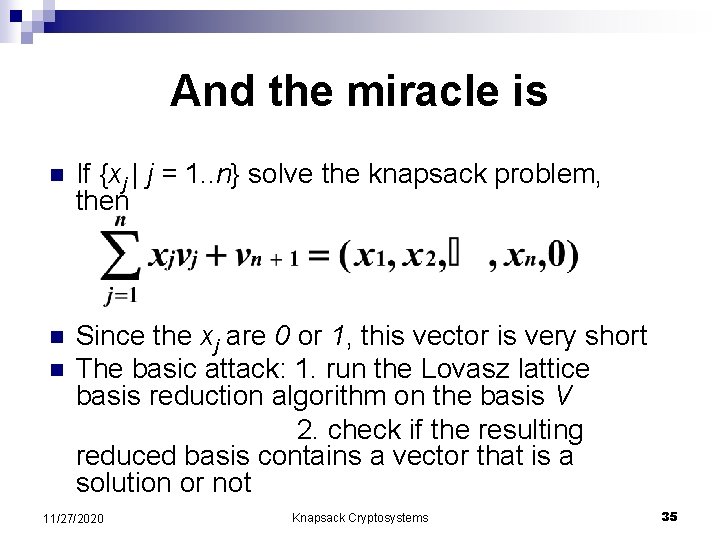
And the miracle is n If {xj | j = 1. . n} solve the knapsack problem, then n Since the xj are 0 or 1, this vector is very short The basic attack: 1. run the Lovasz lattice basis reduction algorithm on the basis V 2. check if the resulting reduced basis contains a vector that is a solution or not n 11/27/2020 Knapsack Cryptosystems 35
How it works: If {aj} are large: most vectors in the lattice are large. So the vector X corresponding to our solution might be the shortest: n If aj ~ 2^(βn) where β>1. 54725 then X is the shortest in most lattices n So: if we could efficiently solve SVL – we can solve most low-density knapsacks n 11/27/2020 Knapsack Cryptosystems 36
How we solve SVL n Proved: we can solve knapsacks with aj ~ 2^(n^2) – extremely large! In practice: much better 11/27/2020 Knapsack Cryptosystems 37
Summary: MH algorithm itself n Attack using revealing an easy knapsack from public n Attack using solvability of low-density knapsacks n 11/27/2020 Knapsack Cryptosystems 38
In conclusion: n n n Both of two main fears were borne out. A few knapsack-based Cryptosystems still remain unbroken: e. g. Chor – Rivest 1988 Since 1) high speed 2) factorization and logarithm procedures can turn out efficiently solvable someday 3) elegance of the algorithm search is going on… 11/27/2020 Knapsack Cryptosystems 39
Example - exercise Make a private key: with n = 6 n (2, 3, 6, 13, 27, 52) n M = 105, W = 31 n aj : (62, 93, 81, 88, 102, 37) n 11/27/2020 Knapsack Cryptosystems 40
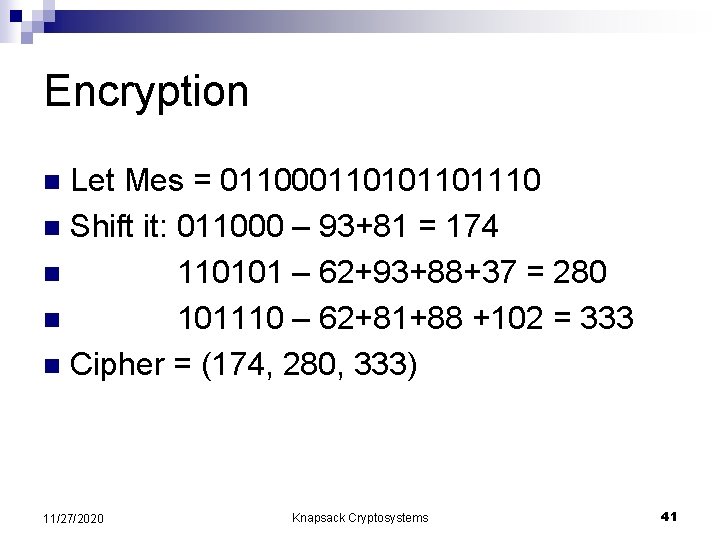
Encryption Let Mes = 0110001101110 n Shift it: 011000 – 93+81 = 174 n 110101 – 62+93+88+37 = 280 n 101110 – 62+81+88 +102 = 333 n Cipher = (174, 280, 333) n 11/27/2020 Knapsack Cryptosystems 41
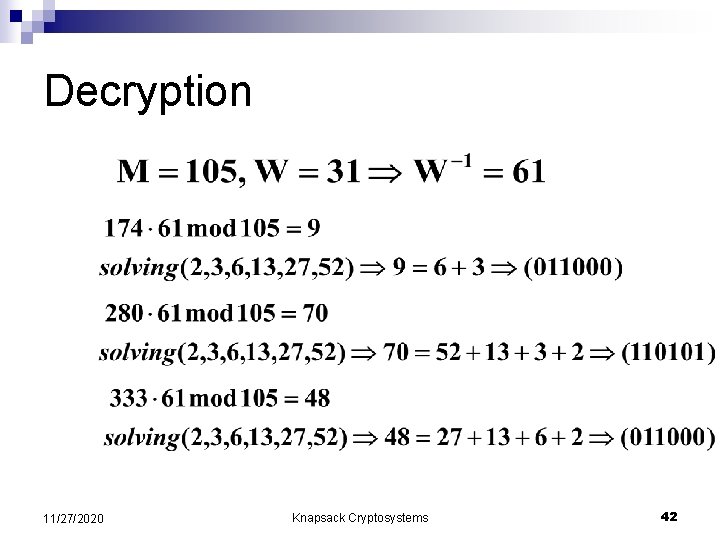
Decryption 11/27/2020 Knapsack Cryptosystems 42
- Slides: 42