King Hezekiah 4 Security in a Fearful World
- Slides: 22
King Hezekiah 4. Security in a Fearful World
Security: Greatest Driver of our Decisions? • • • To secure Food and shelter To secure Safety To secure what we’ve attained To secure Loyalty, and Love To secure Health, Future Success
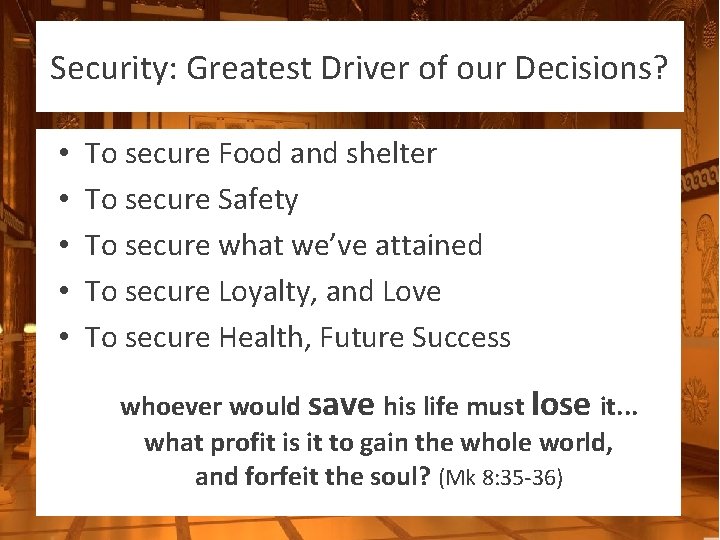
Security: Greatest Driver of our Decisions? • • • To secure Food and shelter To secure Safety To secure what we’ve attained To secure Loyalty, and Love To secure Health, Future Success whoever would save his life must lose it. . . what profit is it to gain the whole world, and forfeit the soul? (Mk 8: 35 -36)
Spot the Difference?
2 Chronicles 32
2 Chronicles 32 Apparent Success! • The Assyrians repelled (2 -8) • The Assyrians threaten (9 -19) • The Assyrians miraculously defeated (20 -23)
2 Chronicles 32 Apparent Success! • The Assyrians repelled (2 -8) • The Assyrians threaten (9 -19) • The Assyrians miraculously defeated (20 -23) 25 “But Hezekiah did not make return. . . His heart was proud” cf 2 Kings 18, Isaiah 36
2 Chronicles 32 “After these acts of faithfulness, Sennacherib came. . . ” (1). . . “. . . wrath came upon him, and Judah and Jerusalem” (26 b)
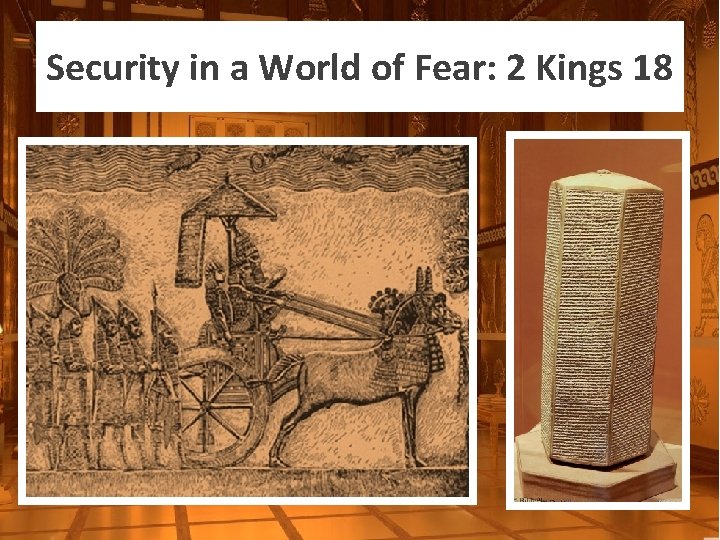
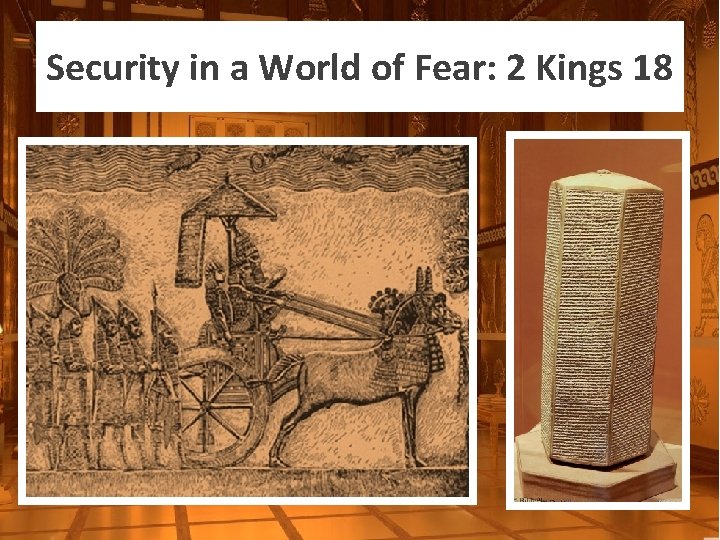
Security in a World of Fear: 2 Kings 18
Security in a World of Fear 2 failed efforts at security:
Security in a World of Fear 2 failed efforts at security: 1. Trust the enemy (18: 14 -16)
Security in a World of Fear 2 failed efforts at security: 1. Trust the enemy (18: 14 -16) 2. Trust the enemy’s enemy (18: 17 -19: 37)
Security in a World of Fear 2 failed efforts at security: 1. Trust the enemy (18: 14 -16) 2. Trust the enemy’s enemy (18: 17 -19: 37) God alone is Jerusalem’s security (19: 6, 32 -37) “I will defend this city to save it, for my own sake and for the sake of my servant David”
Security in a World of Fear 2 failed efforts at security. 1 cause of both:
Security in a World of Fear 2 failed efforts at security. 1 cause of both: (19) “he thought…. :
Security in a World of Fear 2 failed efforts at security. 1 cause of both: (19) “he thought…. : Why not, if there will be peace and security in my days”
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9)
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9) – Place no confidence in your past spiritual experience. Place it solely in the Gospel of Jesus
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9) – Place no confidence in your past spiritual experience. Place it solely in the Gospel of Jesus 2. Ease of Living can mask what we really trust
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9) – Place no confidence in your past spiritual experience. Place it solely in the Gospel of Jesus 2. Ease of Living can mask what we really trust – Review your fears now, Resolve future decisions now
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9) – Place no confidence in your past spiritual experience. Place it solely in the Gospel of Jesus 2. Ease of Living can mask what we really trust – Review your fears now, Resolve future decisions now 3. The LORD alone is Trust-worthy (2 Ki 20: 5)
Lessons to take home 1. How-we-Begin is no guarantee of How-we-End (Jer 19: 7, 9) – Place no confidence in your past spiritual experience. Place it solely in the Gospel of Jesus 2. Ease of Living can mask what we really trust – Review your fears now, Resolve future decisions now 3. The LORD alone is Trust-worthy (2 Ki 20: 5) – Take Christ’s words to heart, Live for Him