Key Management Shared Key Exchange Problem How do
Key Management
Shared Key Exchange Problem • • How do Alice and Bob exchange a shared secret? Offline – • • • Doesn’t scale Using public key cryptography (possible) Using specially crafted messages (Diffie-Hellman) Using a trusted third party (KDC) – – – Secrets should never be sent in clear We should prevent replay attacks We should prevent reuse of old keys
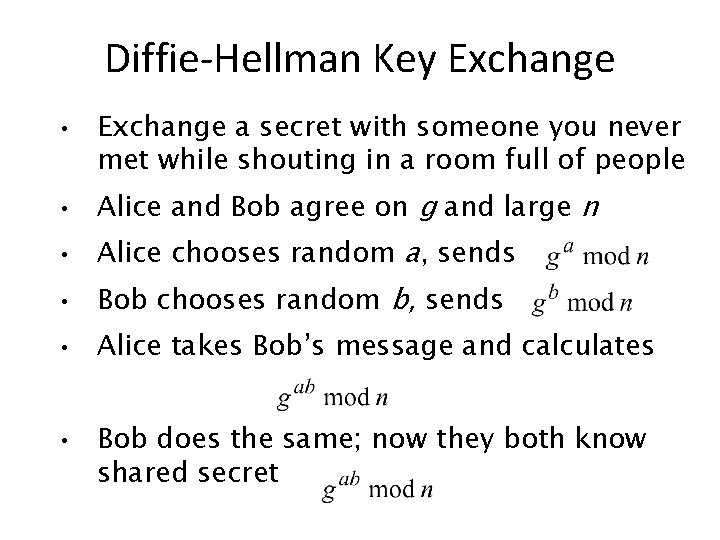
Diffie-Hellman Key Exchange • Exchange a secret with someone you never met while shouting in a room full of people • Alice and Bob agree on g and large n • Alice chooses random a, sends • Bob chooses random b, sends • Alice takes Bob’s message and calculates • Bob does the same; now they both know shared secret
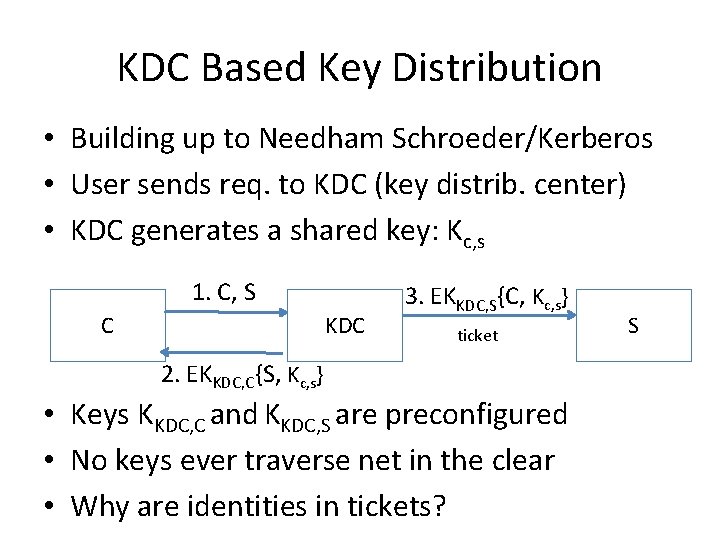
KDC Based Key Distribution • Building up to Needham Schroeder/Kerberos • User sends req. to KDC (key distrib. center) • KDC generates a shared key: Kc, s 1. C, S C KDC 3. EKKDC, S{C, Kc, s} ticket 2. EKKDC, C{S, Kc, s} • Keys KKDC, C and KKDC, S are preconfigured • No keys ever traverse net in the clear • Why are identities in tickets? S
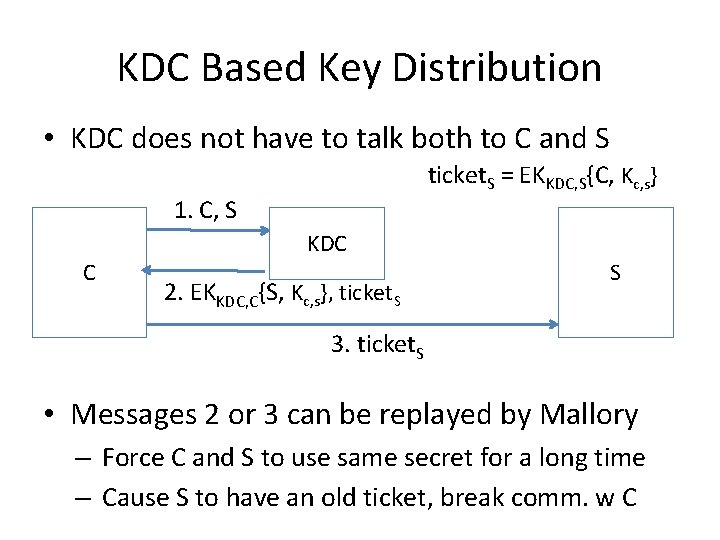
KDC Based Key Distribution • KDC does not have to talk both to C and S ticket. S = EKKDC, S{C, Kc, s} 1. C, S C KDC 2. EKKDC, C{S, Kc, s}, ticket. S S 3. ticket. S • Messages 2 or 3 can be replayed by Mallory – Force C and S to use same secret for a long time – Cause S to have an old ticket, break comm. w C
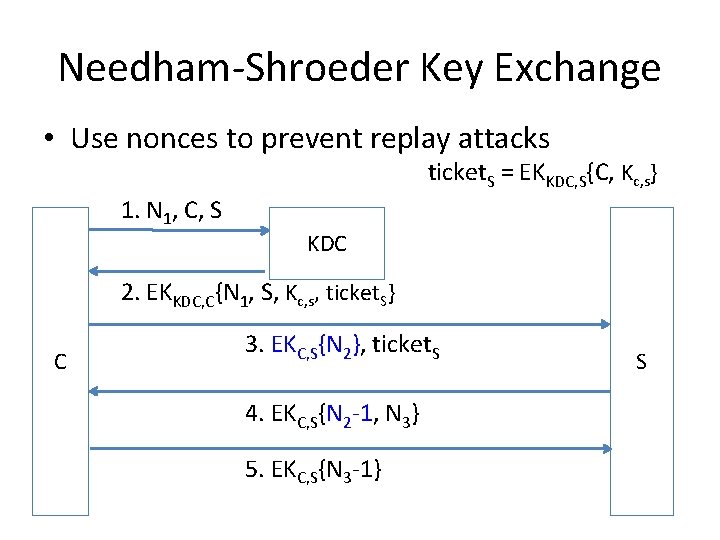
Needham-Shroeder Key Exchange • Use nonces to prevent replay attacks ticket. S = EKKDC, S{C, Kc, s} 1. N 1, C, S KDC 2. EKKDC, C{N 1, S, Kc, s, ticket. S} C 3. EKC, S{N 2}, ticket. S 4. EKC, S{N 2 -1, N 3} 5. EKC, S{N 3 -1} S
Problem • What happens if attacker gets session key? – Can reuse old session key to answer challengeresponse, generate new requests, etc – Need timestamps to ensure freshness = tickets expire after some time
Public Key Exchange Problem • How do we verify an identity: – – – Alice sends to Bob her public key Pub(A) Bob sends to Alice his public key Pub(B) How do we ensure that those keys really belong to Alice and Bob? Need a trusted third party
Man-in-the-Middle Attack On Key Exchange • • • Alice sends to Bob her public key Pub(A) Mallory captures this and sends to Bob Pub(M) Bob sends to Alice his public key Pub(B) Mallory captures this and sends to Alice Pub(M) Now Alice and Bob correspond through Mallory who can read/change all their messages
Public Key Exchange • Public key is public but … – How does either side know who and what the key is for? • Does this solve key distribution problem? – No – while confidentiality is not required, integrity is • Still need trusted third party – Digital certificates – certificate authority (CA) signs identity+public key tuple with its private key – Problem is finding a CA that both client and server trust
Digital Certificates • • • Everyone has Trent’s public key Trent signs both Alice’s and Bob’s public keys – he generates public-key certificate When they receive keys, verify the signature Mallory cannot impersonate Alice or Bob because her key is signed as Mallory’s Certificate usually contains more than the public key – Name, network address, organization • Trent is known as Certificate Authority (CA)
Certificate-Based Key Exchange • Authentication steps – Alice provides nonce, or a timestamp is used instead, along with her certificate. – Bob selects session key and sends it to Alice with nonce, encrypted with Alice’s public key, and signed with Bob’s private key. He sends his certificate too – Alice validates certificate – it is really Bob’s key inside – Alice checks signature and nonce – Bob really generated the message and it is fresh
PGP • Pretty Good Privacy – “Web of Trust” – Public key, identity association is signed by many entities – Receiver hopefully can locate several signatures that he can trust – Like an endorsement scheme
SSH • User keys installed on server out of band – User logs in with a password – Copies her public key onto server • Weak assurance of server keys – User machine remembers server keys on first contact – Checks if this is still the same host on subsequent contact – But no check on first contact
Recovery From Stolen Private Keys • Revocation lists (CRL’s) – Long lists – Hard to propagate • Lifetime / Expiration – Short life allows assurance of validity at time of issue • Real time validation – Receiver of a certificate asks the CA who signed it if corresponding private key was compromised – Can cache replies
Authentication and Identity Management
Basis for Authentication • Ideally – Who you are • Practically – Something you know (e. g. , password) – Something you have (e. g. , badge) – Something about you (e. g. , fingerprint)
Password Authentication • • Alice inputs her password, computer verifies this against list of passwords If computer is broken into, hackers can learn everybody’s passwords – Use one-way functions, store the result for every valid password – Perform one-way function on input, compare result against the list
Password Authentication • • Hackers can compile a list of frequently used passwords, apply one-way function to each and store them in a table – dictionary attack Host adds random salt to password, applies one-way function to that and stores result and salt value – Randomly generated, unique and long enough
Password Authentication • • Someone sniffing on the network can learn the password Lamport hash or S-KEY – time-varying password – To set-up the system, Alice enters random number R – Host calculates x 0=h(R), x 1=h(h(R)), x 2=h(h(h(R))), . . . , x 100 – Alice keeps this list, host sets her password to x 101 – Alice logs on with x 100, host verifies h(x 100)=x 101, resets password to x 100 – Next time Alice logs on with x 99
- Slides: 20