Key Establishment Protocols 12 6 12 9 Seunggyu
Key Establishment Protocols - 12. 6 ~ 12. 9 - Seunggyu BYEON hrfeel@mobile. re. kr Intelligence Networking & Computing Lab. Dept. of Electrical & Computer Eng. Pusan National University 1
Contents 12. 6 Key agreement based on asymmetric techniques 12. 7 Secret sharing 12. 8 Conference keying 12. 9 Analysis of key establishment protocols Intelligence Networking and Computing Lab. 2
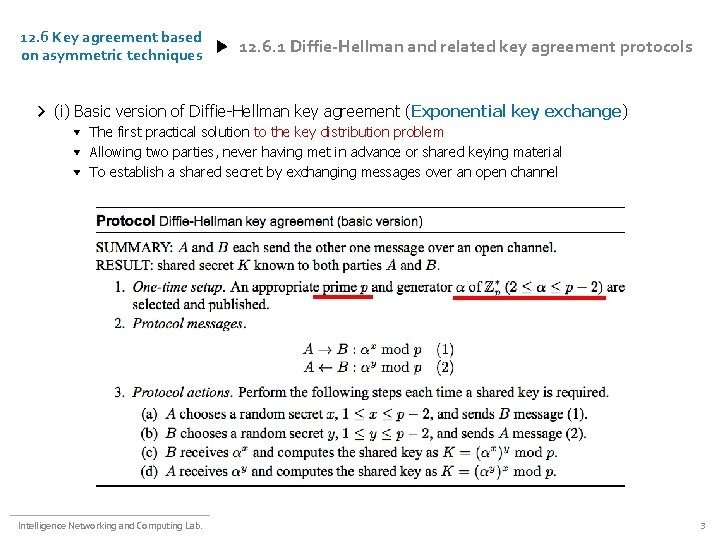
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (i) Basic version of Diffie-Hellman key agreement (Exponential key exchange) The first practical solution to the key distribution problem Allowing two parties, never having met in advance or shared keying material To establish a shared secret by exchanging messages over an open channel Intelligence Networking and Computing Lab. 3
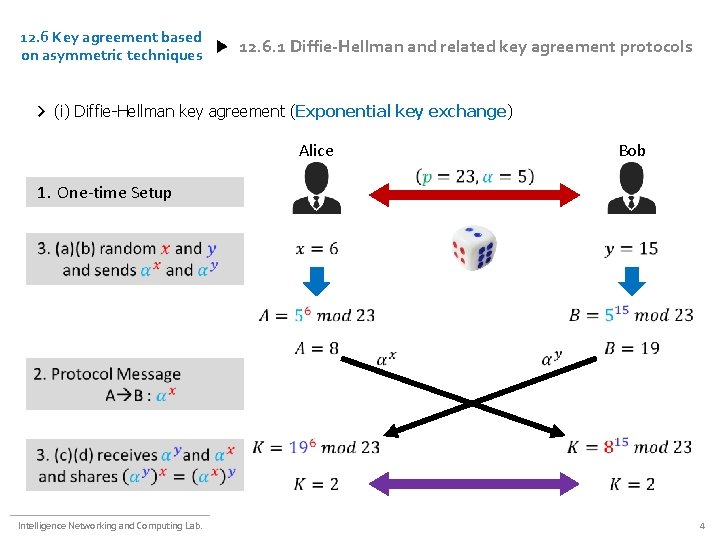
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (i) Diffie-Hellman key agreement (Exponential key exchange) Alice Bob 1. One-time Setup Intelligence Networking and Computing Lab. 4
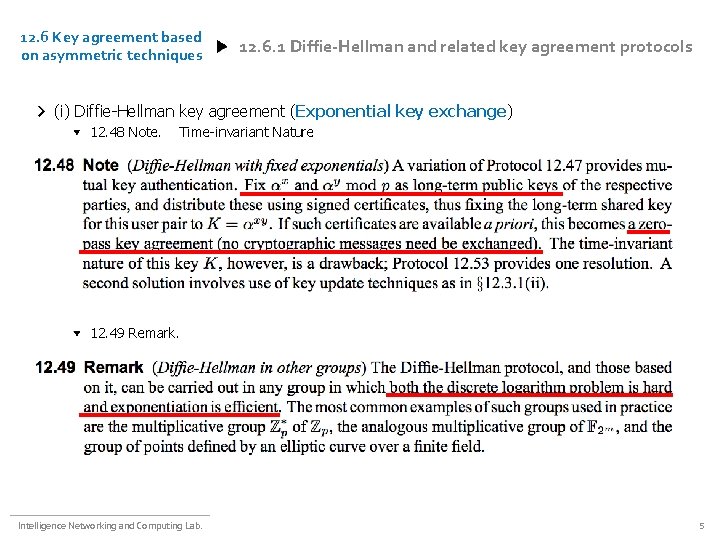
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (i) Diffie-Hellman key agreement (Exponential key exchange) 12. 48 Note. Time-invariant Nature 12. 49 Remark. Intelligence Networking and Computing Lab. 5
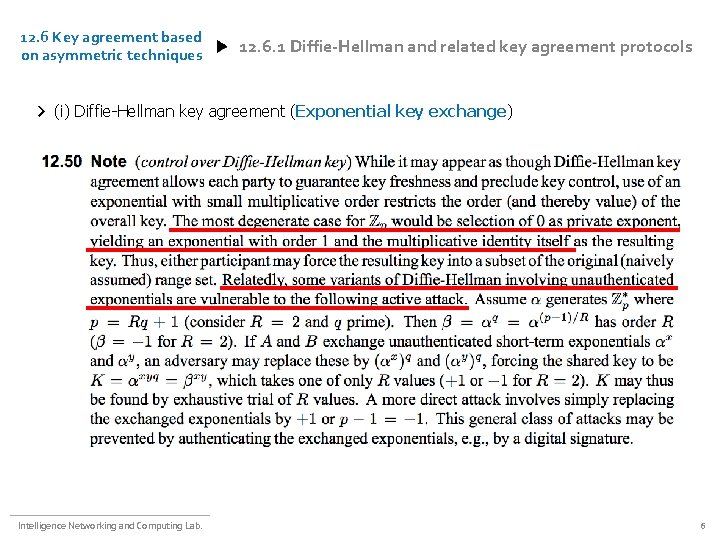
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (i) Diffie-Hellman key agreement (Exponential key exchange) Intelligence Networking and Computing Lab. 6
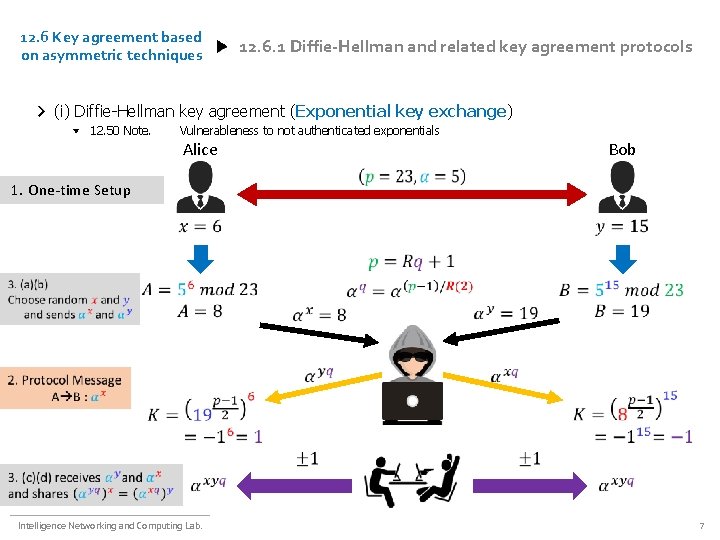
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (i) Diffie-Hellman key agreement (Exponential key exchange) 12. 50 Note. Vulnerableness to not authenticated exponentials Alice Bob 1. One-time Setup Intelligence Networking and Computing Lab. 7
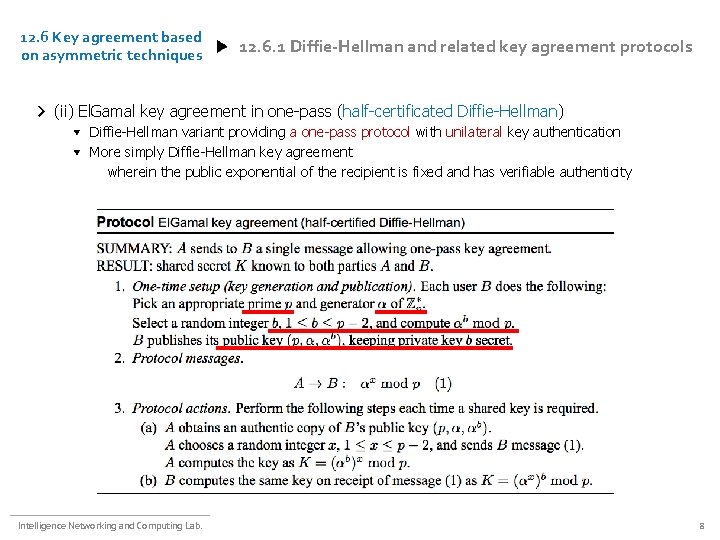
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (ii) El. Gamal key agreement in one-pass (half-certificated Diffie-Hellman) Diffie-Hellman variant providing a one-pass protocol with unilateral key authentication More simply Diffie-Hellman key agreement wherein the public exponential of the recipient is fixed and has verifiable authenticity Intelligence Networking and Computing Lab. 8
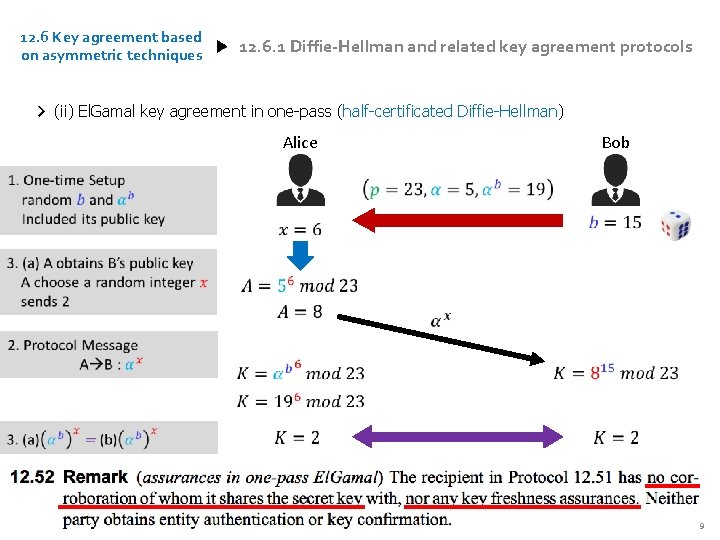
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (ii) El. Gamal key agreement in one-pass (half-certificated Diffie-Hellman) Alice Intelligence Networking and Computing Lab. Bob 9

12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols As in El. Gamal key agreement, A sends to B a single message, resulting in the shared key K B independently initiates an analogous protocol with A, resulting in the shared key K’ Each of A and B then computes k=KK’ mod p Intelligence Networking and Computing Lab. 10
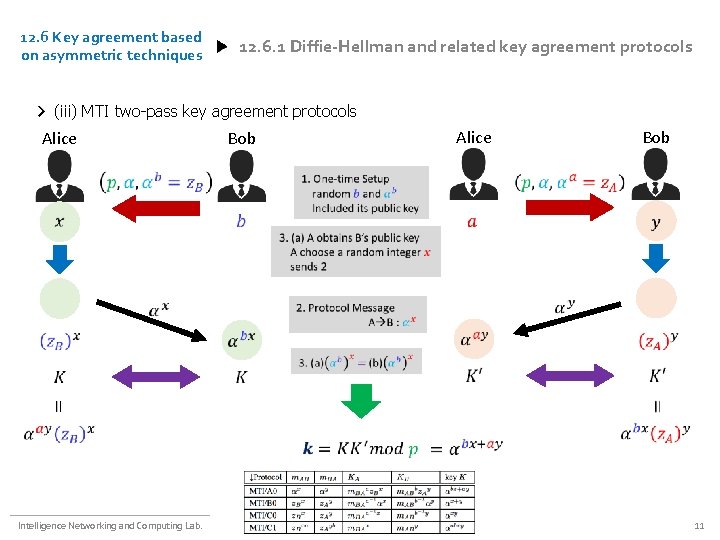
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols Alice Intelligence Networking and Computing Lab. Bob Alice Bob 11
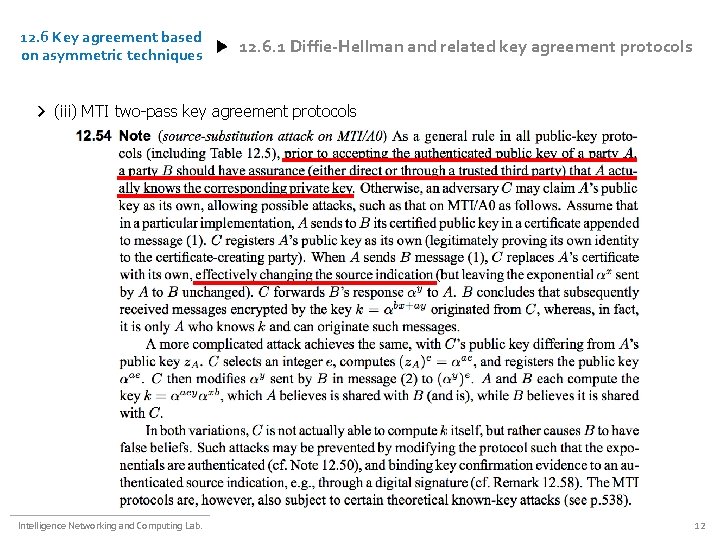
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols Intelligence Networking and Computing Lab. 12
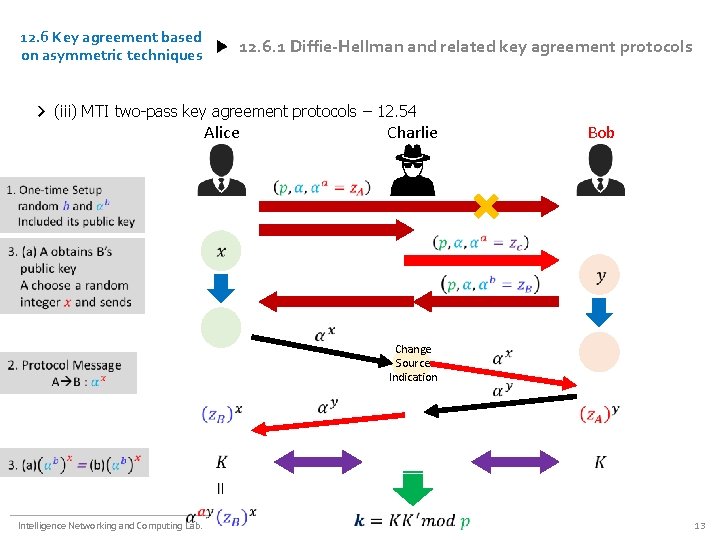
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols – 12. 54 Alice Charlie Bob Change Source Indication Intelligence Networking and Computing Lab. 13
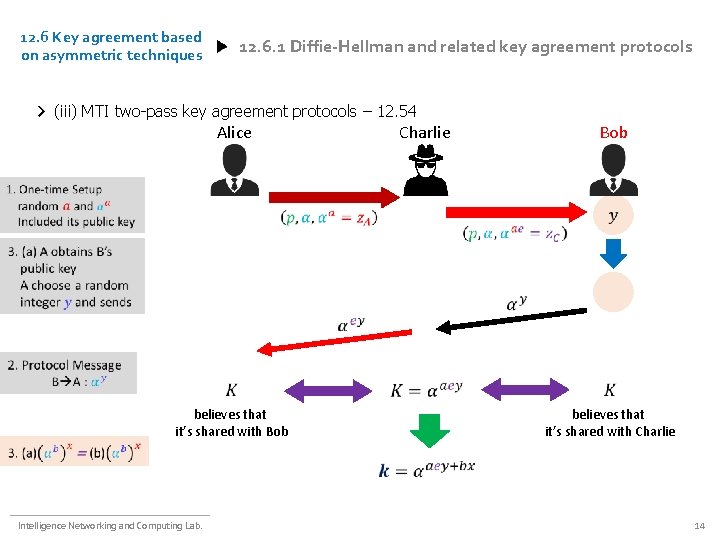
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols – 12. 54 Alice believes that it’s shared with Bob Intelligence Networking and Computing Lab. Charlie Bob believes that it’s shared with Charlie 14
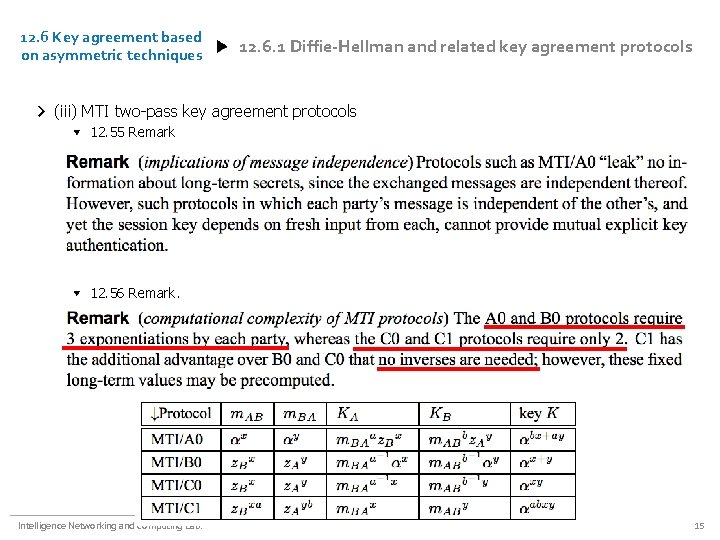
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iii) MTI two-pass key agreement protocols 12. 55 Remark 12. 56 Remark. Intelligence Networking and Computing Lab. 15
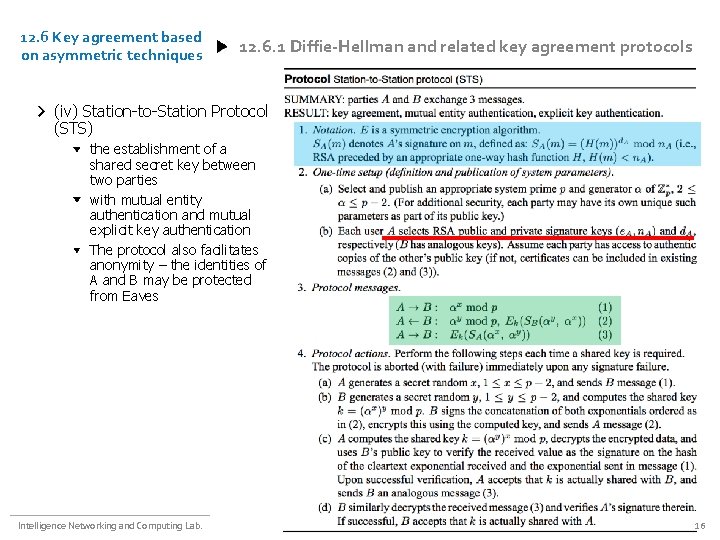
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iv) Station-to-Station Protocol (STS) the establishment of a shared secret key between two parties with mutual entity authentication and mutual explicit key authentication The protocol also facilitates anonymity – the identities of A and B may be protected from Eaves Intelligence Networking and Computing Lab. 16
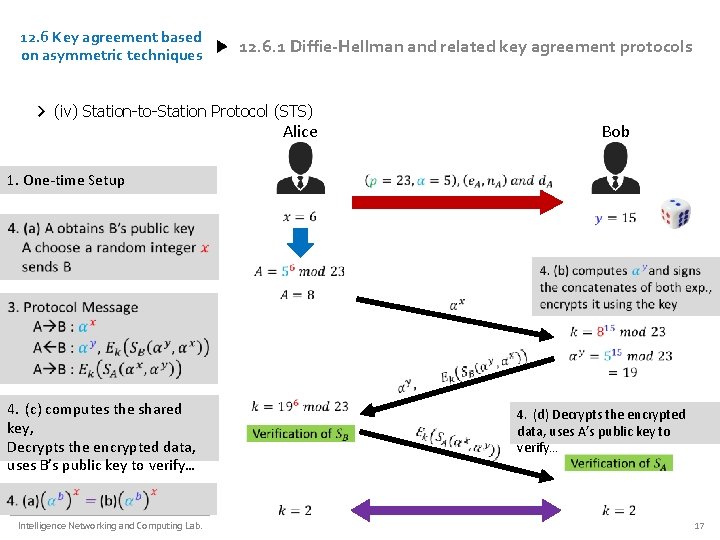
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iv) Station-to-Station Protocol (STS) Alice Bob 1. One-time Setup 4. (c) computes the shared key, Decrypts the encrypted data, uses B’s public key to verify… Intelligence Networking and Computing Lab. 4. (d) Decrypts the encrypted data, uses A’s public key to verify… 17
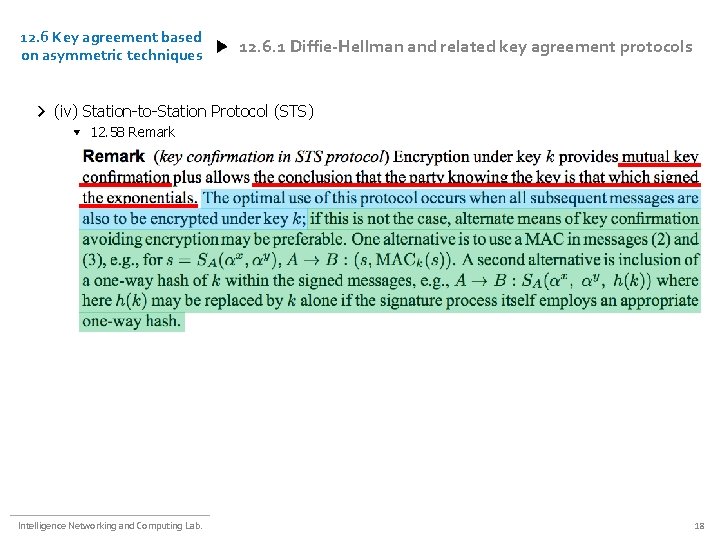
12. 6 Key agreement based on asymmetric techniques 12. 6. 1 Diffie-Hellman and related key agreement protocols (iv) Station-to-Station Protocol (STS) 12. 58 Remark Intelligence Networking and Computing Lab. 18
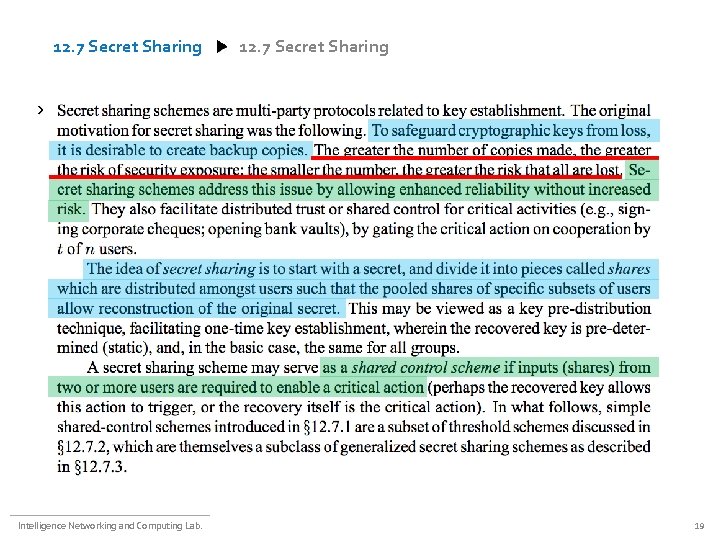
12. 7 Secret Sharing ㄴㄷㅊ Intelligence Networking and Computing Lab. 19
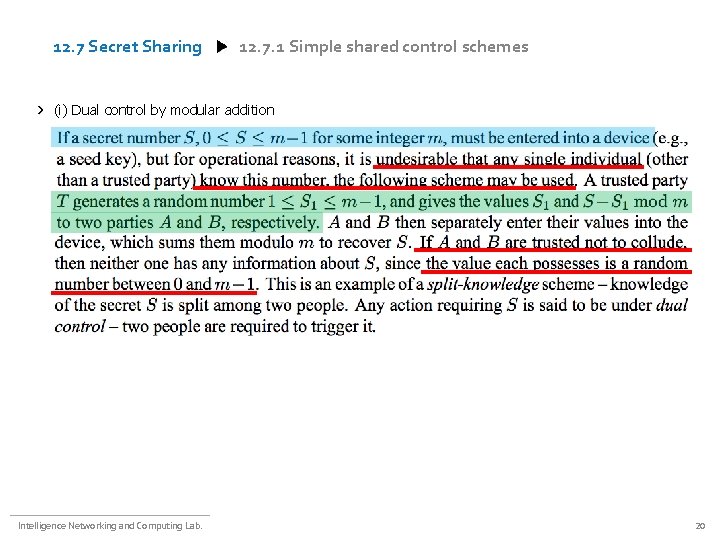
12. 7 Secret Sharing 12. 7. 1 Simple shared control schemes (i) Dual control by modular addition Intelligence Networking and Computing Lab. 20
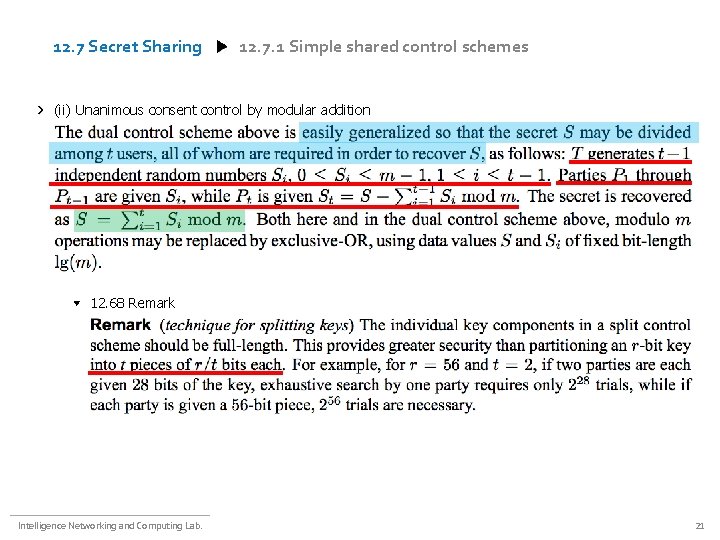
12. 7 Secret Sharing 12. 7. 1 Simple shared control schemes (ii) Unanimous consent control by modular addition 12. 68 Remark Intelligence Networking and Computing Lab. 21
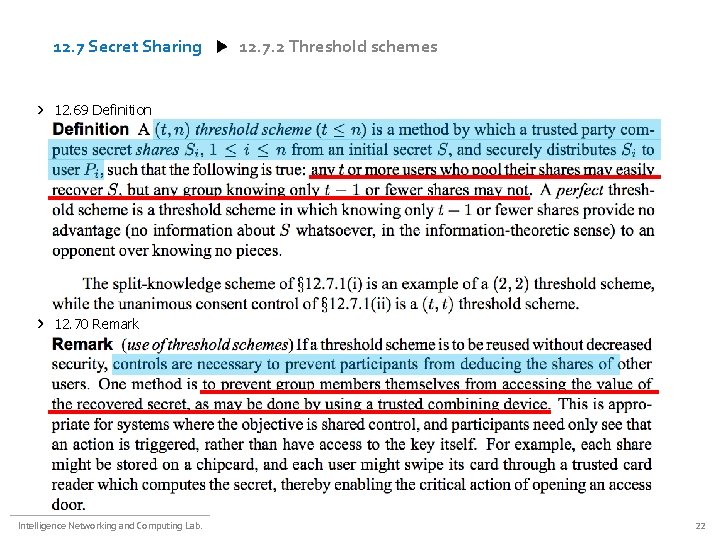
12. 7 Secret Sharing 12. 7. 2 Threshold schemes 12. 69 Definition 12. 70 Remark Intelligence Networking and Computing Lab. 22
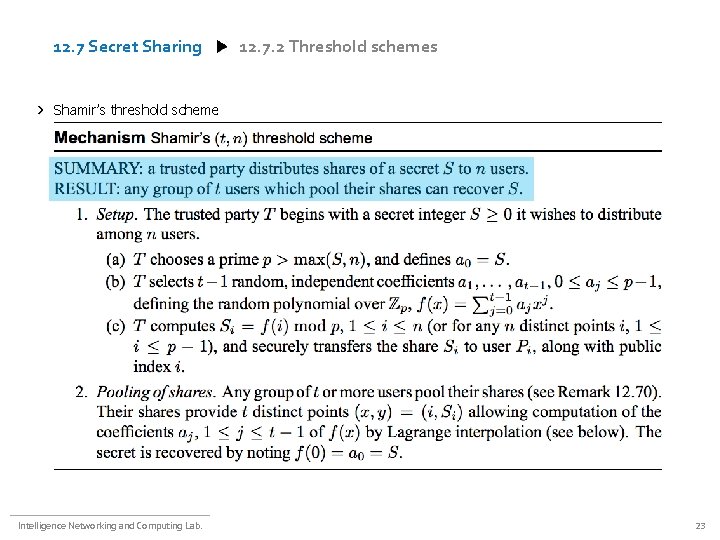
12. 7 Secret Sharing 12. 7. 2 Threshold schemes Shamir’s threshold scheme Intelligence Networking and Computing Lab. 23
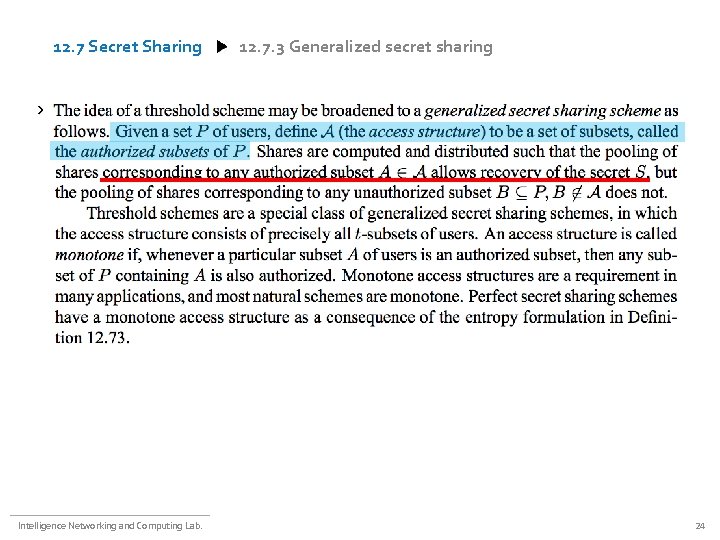
12. 7 Secret Sharing 12. 7. 3 Generalized secret sharing a Intelligence Networking and Computing Lab. 24
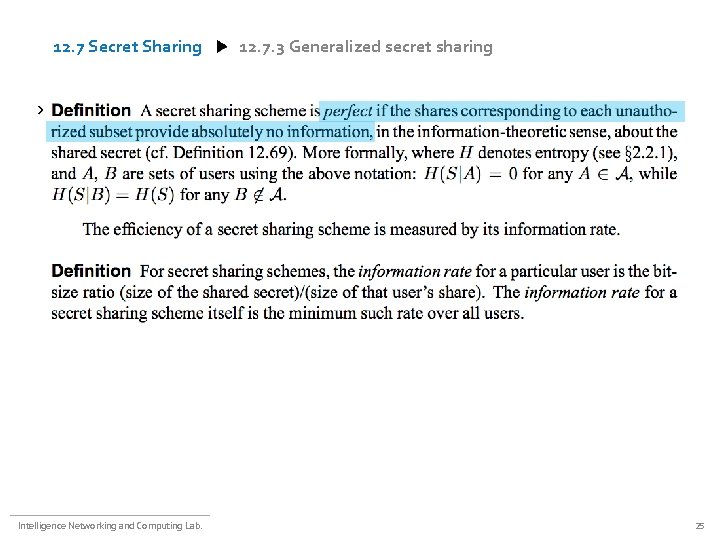
12. 7 Secret Sharing 12. 7. 3 Generalized secret sharing a Intelligence Networking and Computing Lab. 25
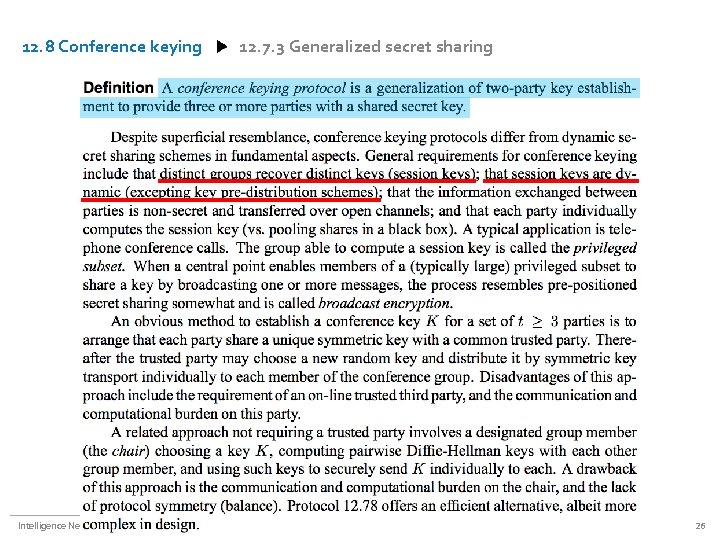
12. 8 Conference keying Intelligence Networking and Computing Lab. 12. 7. 3 Generalized secret sharing 26
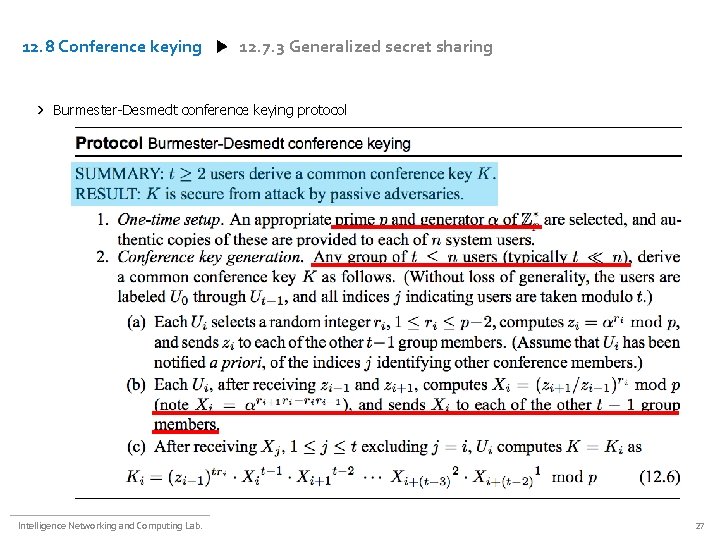
12. 8 Conference keying 12. 7. 3 Generalized secret sharing Burmester-Desmedt conference keying protocol Intelligence Networking and Computing Lab. 27
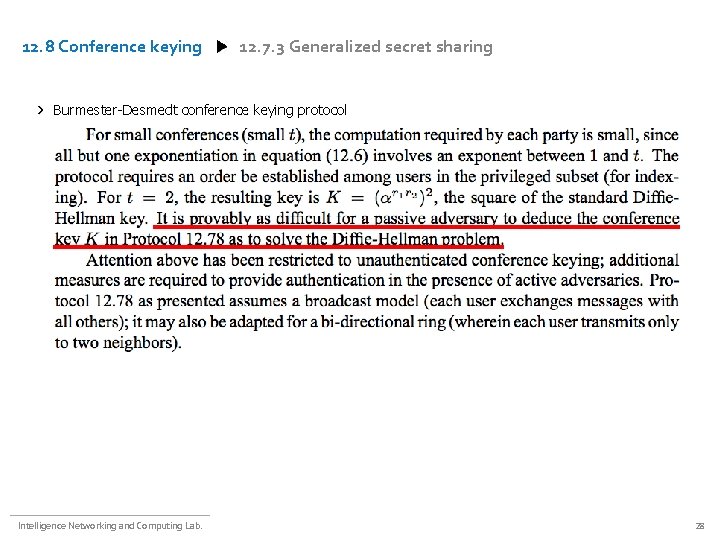
12. 8 Conference keying 12. 7. 3 Generalized secret sharing Burmester-Desmedt conference keying protocol Intelligence Networking and Computing Lab. 28
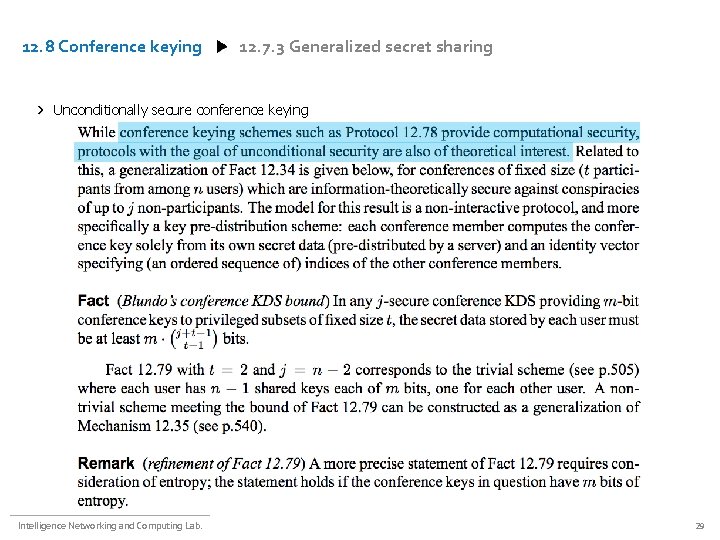
12. 8 Conference keying 12. 7. 3 Generalized secret sharing Unconditionally secure conference keying Intelligence Networking and Computing Lab. 29
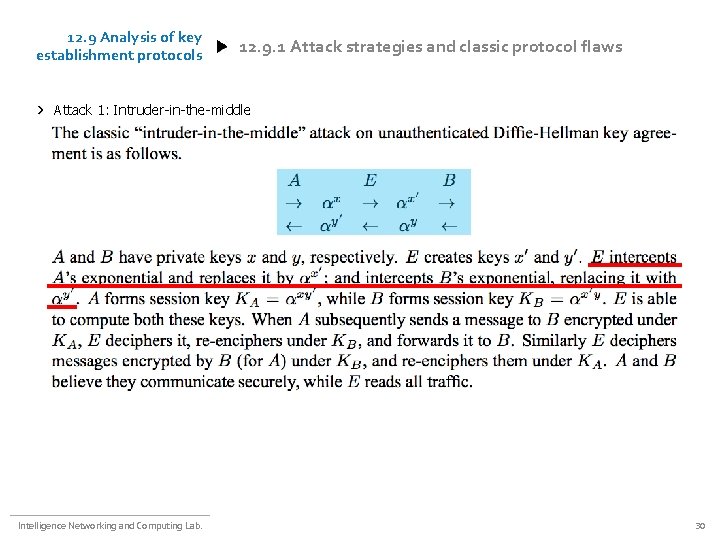
12. 9 Analysis of key establishment protocols 12. 9. 1 Attack strategies and classic protocol flaws Attack 1: Intruder-in-the-middle Intelligence Networking and Computing Lab. 30
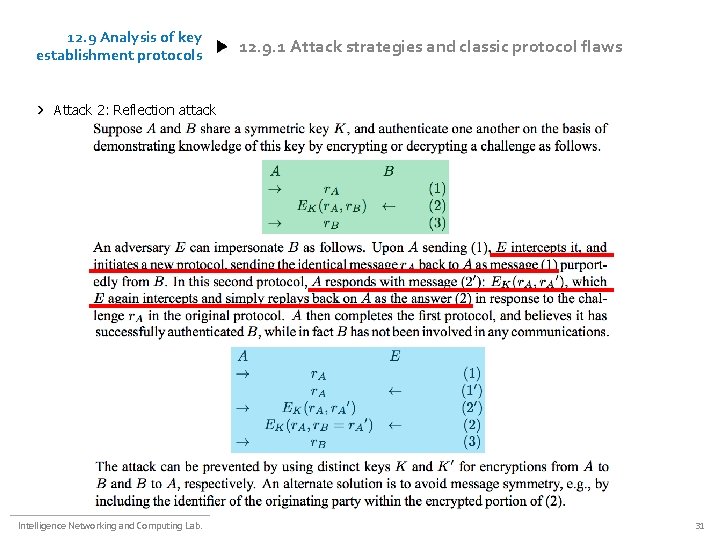
12. 9 Analysis of key establishment protocols 12. 9. 1 Attack strategies and classic protocol flaws Attack 2: Reflection attack Intelligence Networking and Computing Lab. 31
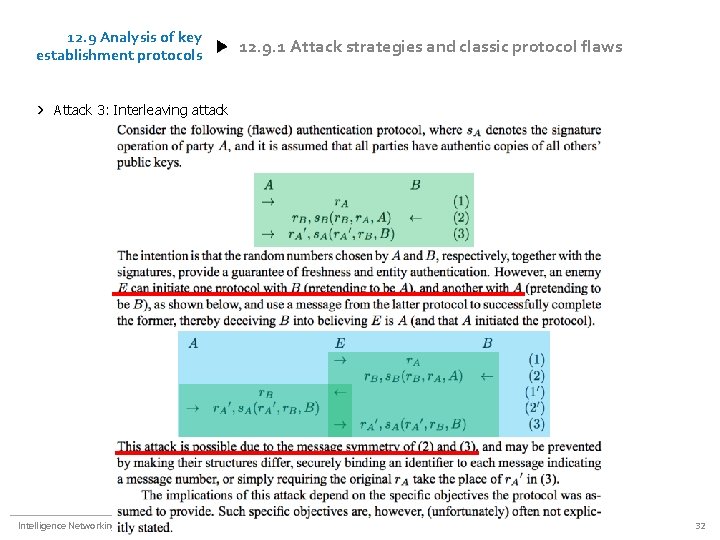
12. 9 Analysis of key establishment protocols 12. 9. 1 Attack strategies and classic protocol flaws Attack 3: Interleaving attack Intelligence Networking and Computing Lab. 32
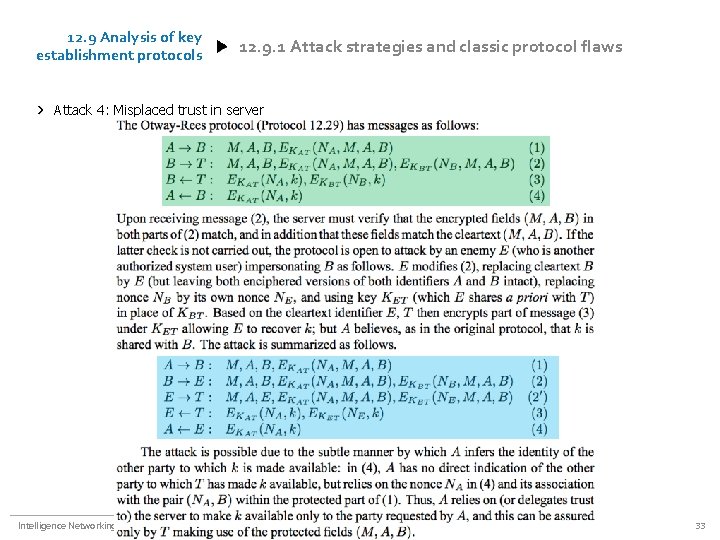
12. 9 Analysis of key establishment protocols 12. 9. 1 Attack strategies and classic protocol flaws Attack 4: Misplaced trust in server Intelligence Networking and Computing Lab. 33
12. 9 Analysis of key establishment protocols 12. 9. 2 Analysis objectives and methpds Definition Intelligence Networking and Computing Lab. 34
12. 9 Analysis of key establishment protocols 12. 9. 2 Analysis objectives and methpds Definition Intelligence Networking and Computing Lab. 35

I appreciate your deep interest Seunggyu BYEON hrfeel@mobile. re. kr Intelligence Networking & Computing Lab. Dept. of Electrical & Computer Eng. Pusan National University
- Slides: 36