Kernel Address Sanitizer A fast memory error detector
- Slides: 14
Kernel Address. Sanitizer A fast memory error detector for Linux kernel Dmitry Vyukov, dvyukov@ Nov 14, 2014, Zero. Nights Google Confidential and Proprietary
Address/Thread/Memory. Sanitizer Address. Sanitizer (ASan): use-after-free, use-after-return, out-ofbounds on heap, stack, globals. Thread. Sanitizer (TSan): data races, deadlocks, mallocs in signal handlers. Memory. Sanitizer (MSan): uses of uninitialized memory [Valgrind is sloooooow] Google Confidential and Proprietary
User-space usage ● ● ● Continuous testing of Chromium and server-side codebase. We use "asanified" Chrome as default browser. Cluster. Fuzz: massive Chromium fuzzing. End-to-end system tests and live traffic serving. Lots of internal fuzzing. Thousands of bugs found. Also found bugs in: Firefox, Opera, vlc, ffmpeg, Free. Type, Web. RTC, My. SQL, Postgre. SQL, perl, PHP, clang, gcc, glibc. Google Confidential and Proprietary
Linux Kernel CONFIG_DEBUG_SLAB: does not detect OOB reads, best-effort UAF detection. CONFIG_DEBUG_PAGEALLOC: Detects UAF only when the whole page is unused. CONFIG_KMEMCHECK: Slow. Google Confidential and Proprietary
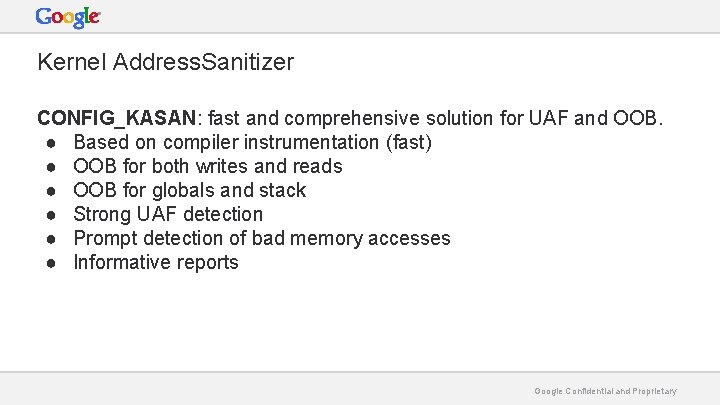
Kernel Address. Sanitizer CONFIG_KASAN: fast and comprehensive solution for UAF and OOB. ● Based on compiler instrumentation (fast) ● OOB for both writes and reads ● OOB for globals and stack ● Strong UAF detection ● Prompt detection of bad memory accesses ● Informative reports Google Confidential and Proprietary
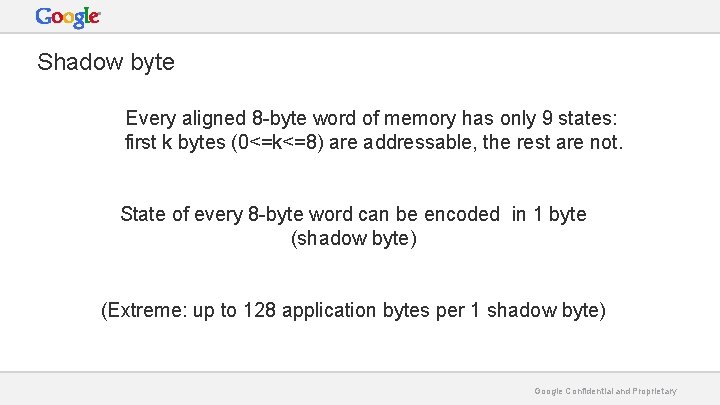
Shadow byte Every aligned 8 -byte word of memory has only 9 states: first k bytes (0<=k<=8) are addressable, the rest are not. State of every 8 -byte word can be encoded in 1 byte (shadow byte) (Extreme: up to 128 application bytes per 1 shadow byte) Google Confidential and Proprietary
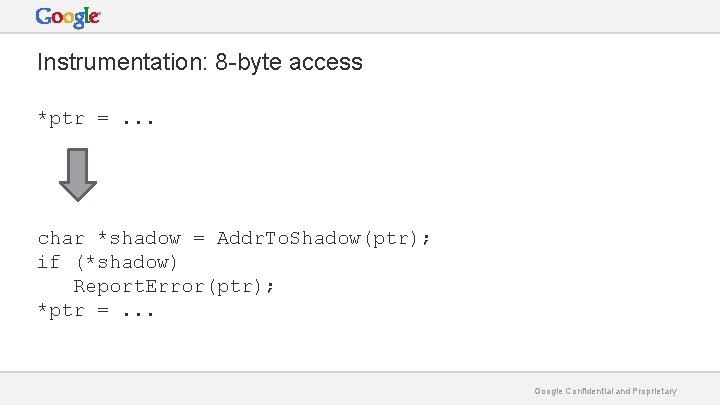
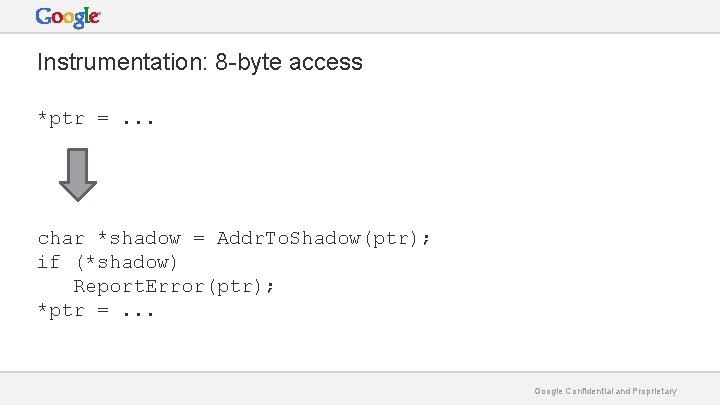
Instrumentation: 8 -byte access *ptr =. . . char *shadow = Addr. To. Shadow(ptr); if (*shadow) Report. Error(ptr); *ptr =. . . Google Confidential and Proprietary
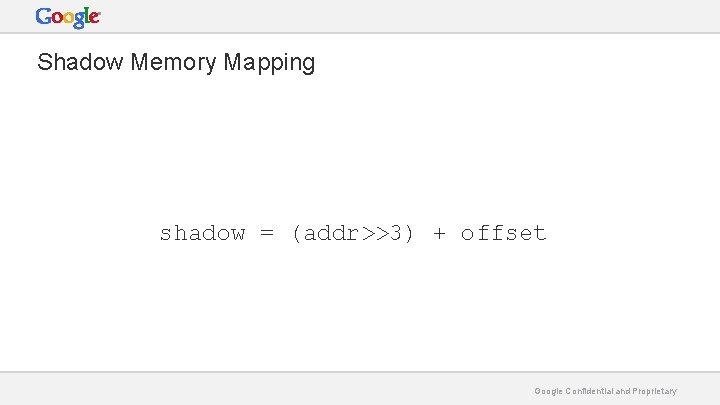
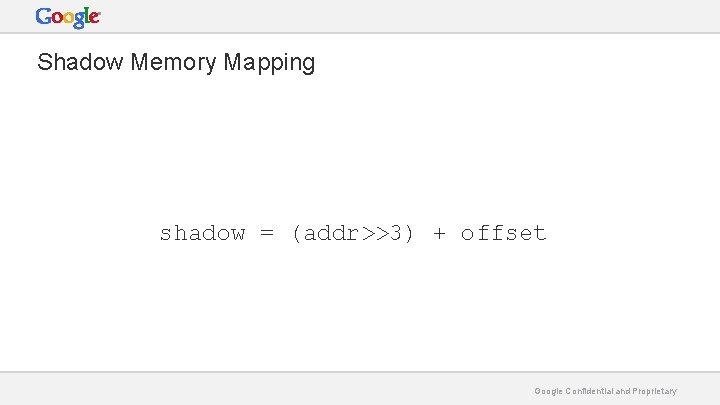
Shadow Memory Mapping shadow = (addr>>3) + offset Google Confidential and Proprietary
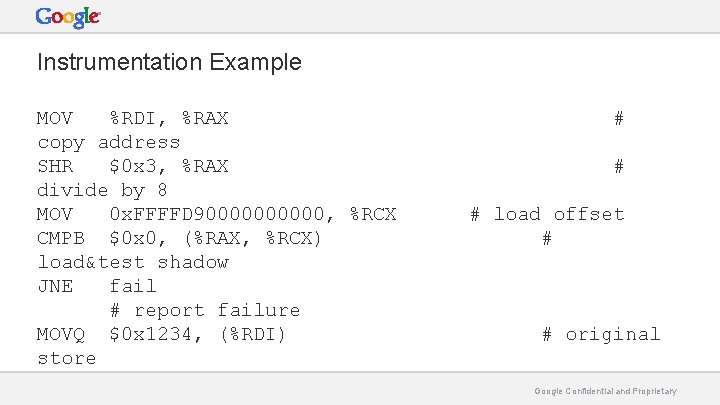
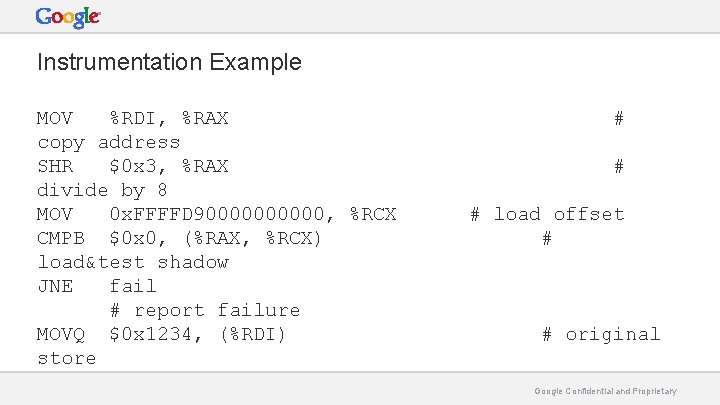
Instrumentation Example MOV %RDI, %RAX copy address SHR $0 x 3, %RAX divide by 8 MOV 0 x. FFFFD 900000, %RCX CMPB $0 x 0, (%RAX, %RCX) load&test shadow JNE fail # report failure MOVQ $0 x 1234, (%RDI) store # # # load offset # # original Google Confidential and Proprietary
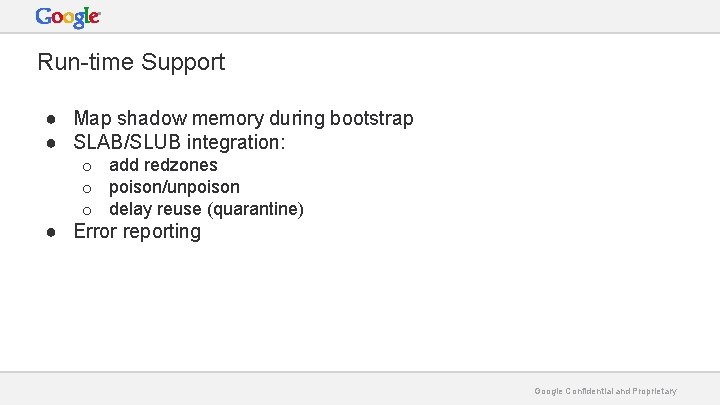
Run-time Support ● Map shadow memory during bootstrap ● SLAB/SLUB integration: o o o add redzones poison/unpoison delay reuse (quarantine) ● Error reporting Google Confidential and Proprietary
Trophies ● ~20 bugs in upstream kernel ● ~20 in our internal kernel ● X bugs found by Samsung and Oracle Google Confidential and Proprietary
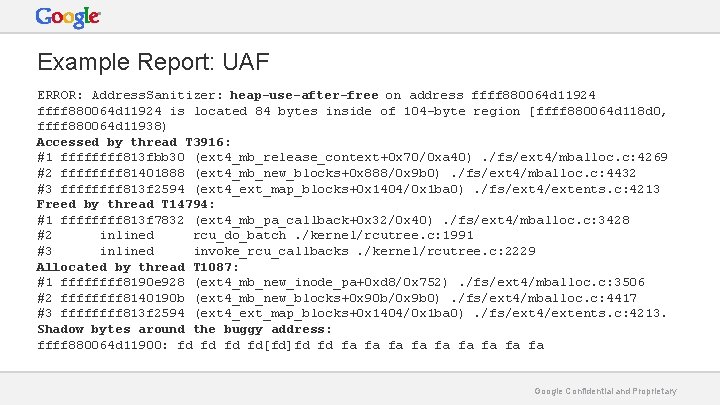
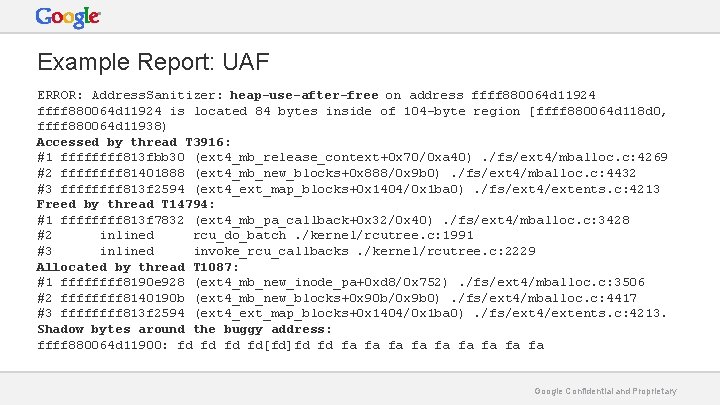
Example Report: UAF ERROR: Address. Sanitizer: heap-use-after-free on address ffff 880064 d 11924 is located 84 bytes inside of 104 -byte region [ffff 880064 d 118 d 0, ffff 880064 d 11938) Accessed by thread T 3916: #1 ffff 813 fbb 30 (ext 4_mb_release_context+0 x 70/0 xa 40). /fs/ext 4/mballoc. c: 4269 #2 ffff 81401888 (ext 4_mb_new_blocks+0 x 888/0 x 9 b 0). /fs/ext 4/mballoc. c: 4432 #3 ffff 813 f 2594 (ext 4_ext_map_blocks+0 x 1404/0 x 1 ba 0). /fs/ext 4/extents. c: 4213 Freed by thread T 14794: #1 ffff 813 f 7832 (ext 4_mb_pa_callback+0 x 32/0 x 40). /fs/ext 4/mballoc. c: 3428 #2 inlined rcu_do_batch. /kernel/rcutree. c: 1991 #3 inlined invoke_rcu_callbacks. /kernel/rcutree. c: 2229 Allocated by thread T 1087: #1 ffff 8190 e 928 (ext 4_mb_new_inode_pa+0 xd 8/0 x 752). /fs/ext 4/mballoc. c: 3506 #2 ffff 8140190 b (ext 4_mb_new_blocks+0 x 90 b/0 x 9 b 0). /fs/ext 4/mballoc. c: 4417 #3 ffff 813 f 2594 (ext 4_ext_map_blocks+0 x 1404/0 x 1 ba 0). /fs/ext 4/extents. c: 4213. Shadow bytes around the buggy address: ffff 880064 d 11900: fd fd[fd]fd fd fa fa fa Google Confidential and Proprietary
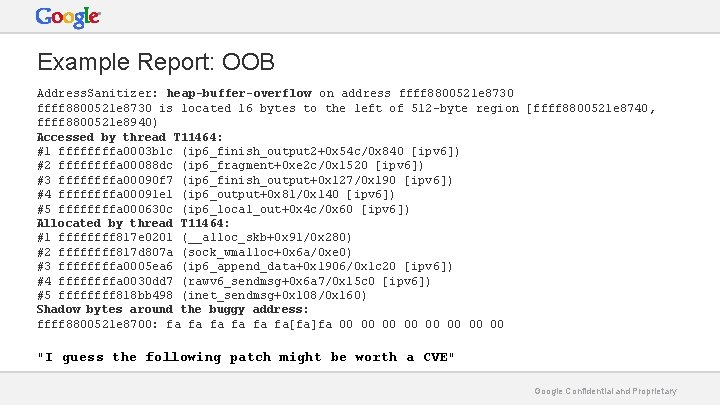
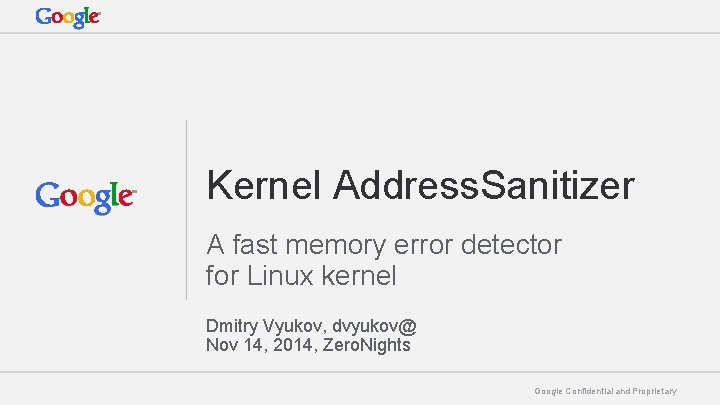
Example Report: OOB Address. Sanitizer: heap-buffer-overflow on address ffff 8800521 e 8730 is located 16 bytes to the left of 512 -byte region [ffff 8800521 e 8740, ffff 8800521 e 8940) Accessed by thread T 11464: #1 ffffa 0003 b 1 c (ip 6_finish_output 2+0 x 54 c/0 x 840 [ipv 6]) #2 ffffa 00088 dc (ip 6_fragment+0 xe 2 c/0 x 1520 [ipv 6]) #3 ffffa 00090 f 7 (ip 6_finish_output+0 x 127/0 x 190 [ipv 6]) #4 ffffa 00091 e 1 (ip 6_output+0 x 81/0 x 140 [ipv 6]) #5 ffffa 000630 c (ip 6_local_out+0 x 4 c/0 x 60 [ipv 6]) Allocated by thread T 11464: #1 ffff 817 e 0201 (__alloc_skb+0 x 91/0 x 280) #2 ffff 817 d 807 a (sock_wmalloc+0 x 6 a/0 xe 0) #3 ffffa 0005 ea 6 (ip 6_append_data+0 x 1906/0 x 1 c 20 [ipv 6]) #4 ffffa 0030 dd 7 (rawv 6_sendmsg+0 x 6 a 7/0 x 15 c 0 [ipv 6]) #5 ffff 818 bb 498 (inet_sendmsg+0 x 108/0 x 160) Shadow bytes around the buggy address: ffff 8800521 e 8700: fa fa fa[fa]fa 00 00 "I guess the following patch might be worth a CVE" Google Confidential and Proprietary
Thanks! http: //address-sanitizer. googlecode. com http: //github. com/google/kasan Questions? Dmitry Vyukov, Google dvyukov@ Google Confidential and Proprietary