KennedyKassebaum Bill Health Insurance Portability and Accountability Act
Kennedy-Kassebaum Bill Health Insurance Portability and Accountability Act (HIPAA) o. What Is HIPAA? o. HIPAA Standards o. Access Control o. Encryption o. Risk Assessment o. Conclusion
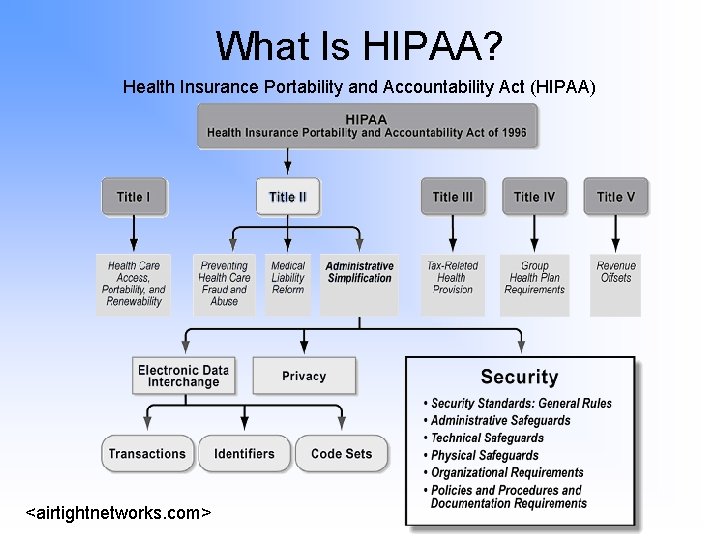
What Is HIPAA? Health Insurance Portability and Accountability Act (HIPAA) <airtightnetworks. com>
HIPAA Health Insurance Portability and Accountability Act (HIPAA) http: //www. asksam. com/ebooks/releases. asp? file=HIPAA
Standards To Consider Health Insurance Portability and Accountability Act (HIPAA) 164. 312(e)(1): “Implement technical security policies and procedures measures to guard against unauthorized access to electronic protected health information (EPHI) that is being transmitted over an electronic communications 164. 312(c)(1): “Implement policies and procedures to protect electronic protected health information from improper alteration or destruction. ” 164. 310(d)(1): “Implement policies and procedures to address the final disposition of EPHI, and/or the hardware or electronic media on which it is stored. ”
Access Control Health Insurance Portability and Accountability Act (HIPAA) o. What It Is o Limitation or permission granted to a certain entity to use some resource o. HIPAA Standard o§ 164. 312, Technical safeguards. “Access control: Implement technical policies and procedures for electronic information systems that maintain electronic protected health information to allow access only to those persons or software programs that have been granted access rights as specified in Sec. 164. 308(a)(4)” o. Log-In Systems o. Emergency Use o. Encryption
Encryption Health Insurance Portability and Accountability Act (HIPAA) o. What It Is o. Simply put, encryption is the encoding of plain text into an unreadable cipher text that can only be decrypted back into the original plain text with a key HIPAA Standards o. Addressable o. The Indian Health Service o “the final HIPAA Security Rule will require encryption only when individually identifiable health information is sent over a public network, such as the Internet. Encryption will not be required for other network connections, such as dial-up lines and Intranets. ” Conclusion
Risk Assessment Health Insurance Portability and Accountability Act (HIPAA) o. What It Is o. Assessing plausible risks that could blemish the purpose of the act, where as risks refer to any threat or vulnerability to a network or its data
Questions?
Works Cited Health Insurance Portability and Accountability Act (HIPAA) Air. Tight Networks, “HIPAA Security” http: //www. airtightnetworks. com/home/solutions/industry-solutions/healthcare/hipaa-security. html Essential Security http: //www. essentialsecurity. com/HIPAA-compliance-encrypted-email-whitepaper. pdf United States Department Of Health And Human Services http: //aspe. hhs. gov/admnsimp/ Security Focus http: //www. securityfocus. com/infocus/1764
- Slides: 9