KEEP YOUR BUSINESS SAFE ONLINE With Web Hawk

KEEP YOUR BUSINESS SAFE ONLINE With Web. Hawk (Cyber Threat Security) ®
Introduction Web. Hawk® secures your business network from malicious hackers and other internal and external internet threats, better, faster, cheaper and easier, than any other solution. • Business Owners Love Us • • Increased Productivity and Quick ROI More Features and Lower Cost Reduced Bandwidth Expense Reduced Liability • Phishing losses • Corporate Data losses • Intellectual Property losses • Network Administrators Love Us • Fast, Quick Setup • Ease of Use • Intuitive Reporting
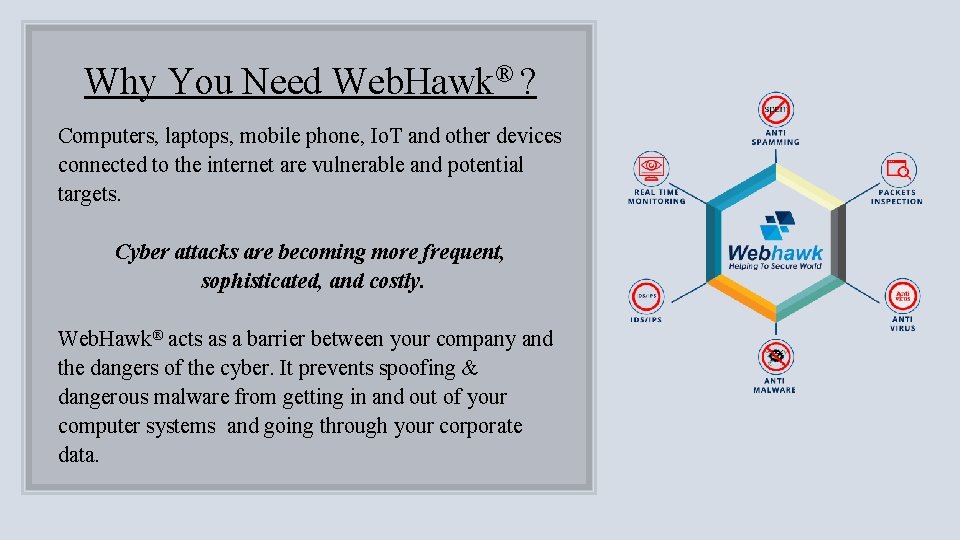
Why You Need Web. Hawk® ? Computers, laptops, mobile phone, Io. T and other devices connected to the internet are vulnerable and potential targets. Cyber attacks are becoming more frequent, sophisticated, and costly. Web. Hawk® acts as a barrier between your company and the dangers of the cyber. It prevents spoofing & dangerous malware from getting in and out of your computer systems and going through your corporate data.
Features Web. Hawk® is a simple, elegant, integrated solution for all your cyber security needs. It includes: • • • Anti-Virus Anti-Spyware Ransomware Protection Anti-Spam Network Firewall Intrusion Detection & Prevention User/Group Management VPN ISP load balancing Content Filtering Data Leak Prevention etc.
Some Unique (and really cool) Features of ® Web. Hawk
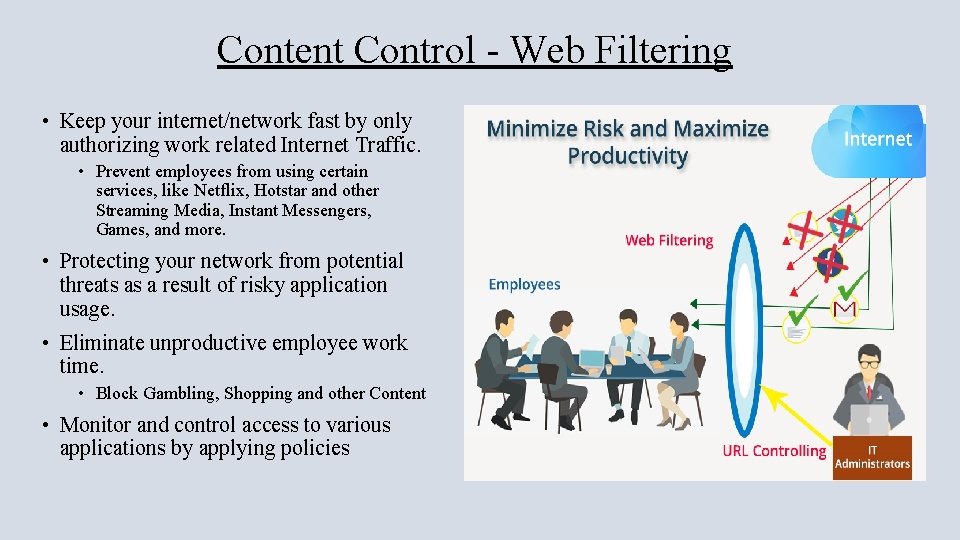
Content Control - Web Filtering • Keep your internet/network fast by only authorizing work related Internet Traffic. • Prevent employees from using certain services, like Netflix, Hotstar and other Streaming Media, Instant Messengers, Games, and more. • Protecting your network from potential threats as a result of risky application usage. • Eliminate unproductive employee work time. • Block Gambling, Shopping and other Content • Monitor and control access to various applications by applying policies
Bandwidth Optimization Guarantee Bandwidth for Business Critical Applications Applying content filtering policies that blocks websites & activities such as streaming videos, media players, sites like You. Tube, Video and AD’S increases bandwidth and Internet browsing speed. USB Internet Support Web. Hawk® also provides internet support through USB. Internet speeds are determined by your plan and your Internet service provider. Web. Hawk® ensures you are maximizing your Internet network speed.
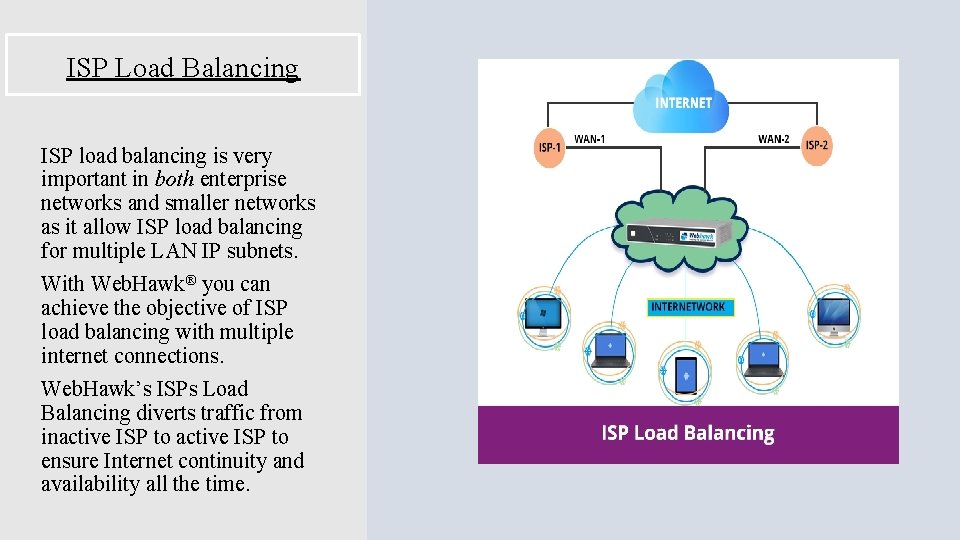
ISP Load Balancing ISP load balancing is very important in both enterprise networks and smaller networks as it allow ISP load balancing for multiple LAN IP subnets. With Web. Hawk® you can achieve the objective of ISP load balancing with multiple internet connections. Web. Hawk’s ISPs Load Balancing diverts traffic from inactive ISP to ensure Internet continuity and availability all the time.
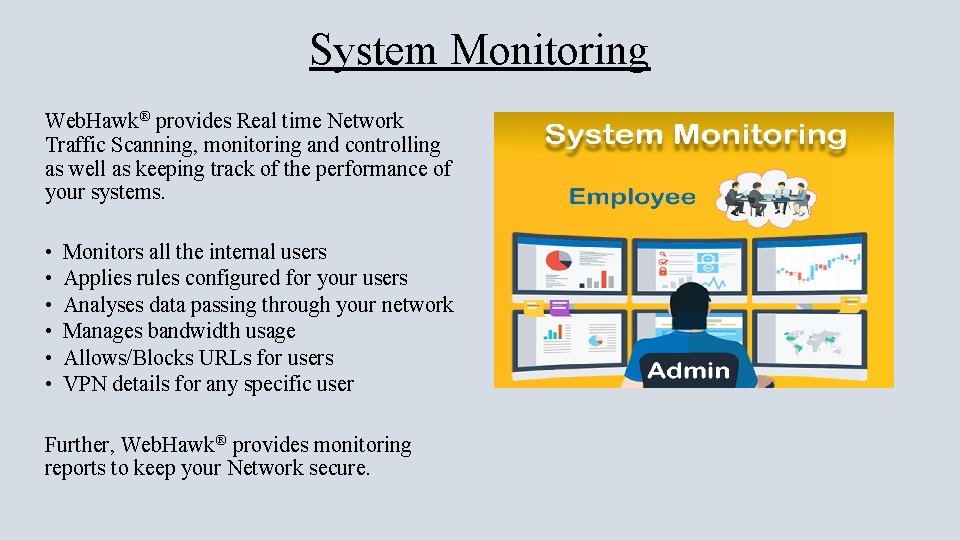
System Monitoring Web. Hawk® provides Real time Network Traffic Scanning, monitoring and controlling as well as keeping track of the performance of your systems. • • • Monitors all the internal users Applies rules configured for your users Analyses data passing through your network Manages bandwidth usage Allows/Blocks URLs for users VPN details for any specific user Further, Web. Hawk® provides monitoring reports to keep your Network secure.
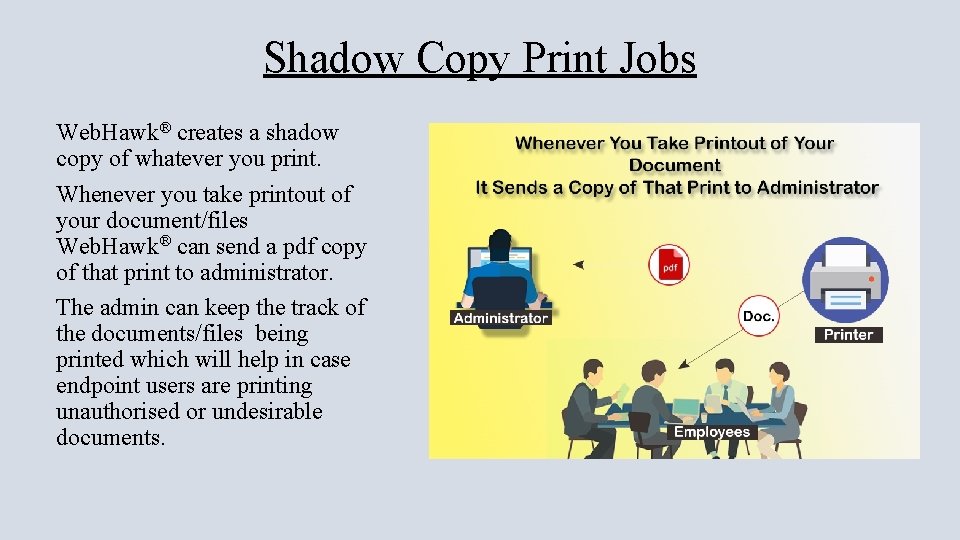
Shadow Copy Print Jobs Web. Hawk® creates a shadow copy of whatever you print. Whenever you take printout of your document/files Web. Hawk® can send a pdf copy of that print to administrator. The admin can keep the track of the documents/files being printed which will help in case endpoint users are printing unauthorised or undesirable documents.
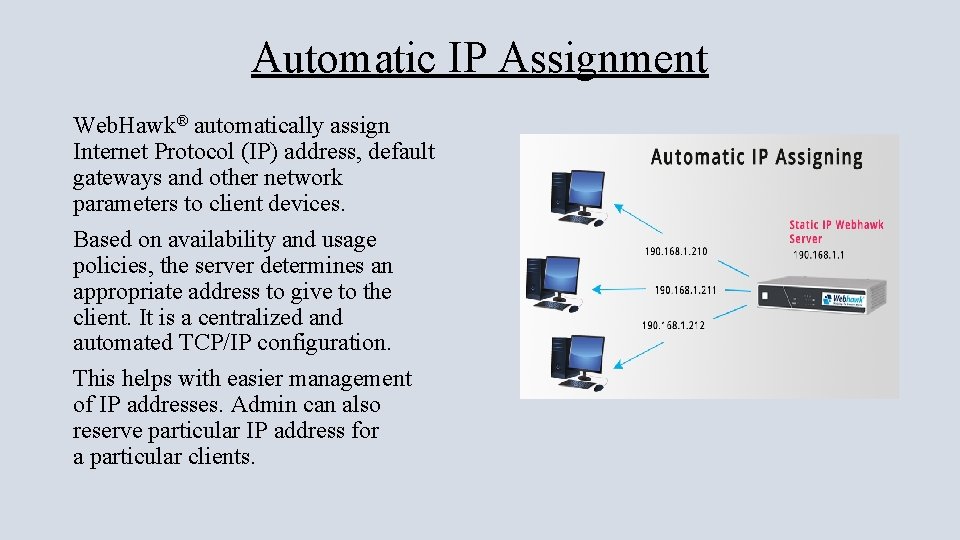
Automatic IP Assignment Web. Hawk® automatically assign Internet Protocol (IP) address, default gateways and other network parameters to client devices. Based on availability and usage policies, the server determines an appropriate address to give to the client. It is a centralized and automated TCP/IP configuration. This helps with easier management of IP addresses. Admin can also reserve particular IP address for a particular clients.
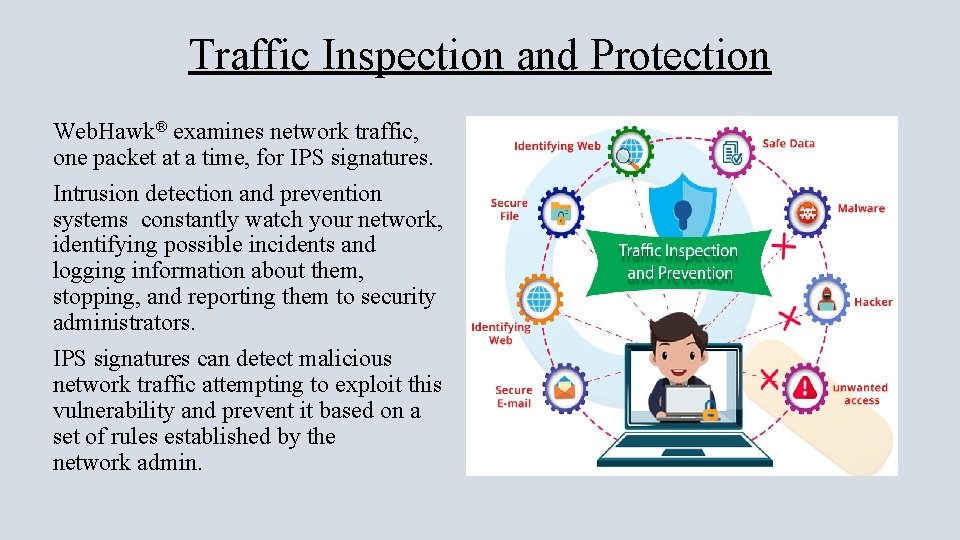
Traffic Inspection and Protection Web. Hawk® examines network traffic, one packet at a time, for IPS signatures. Intrusion detection and prevention systems constantly watch your network, identifying possible incidents and logging information about them, stopping, and reporting them to security administrators. IPS signatures can detect malicious network traffic attempting to exploit this vulnerability and prevent it based on a set of rules established by the network admin.
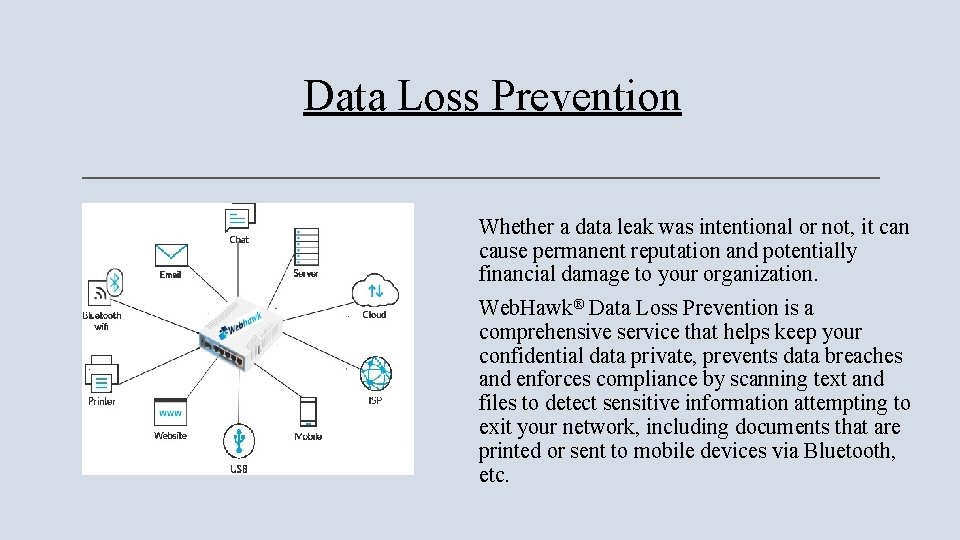
Data Loss Prevention Whether a data leak was intentional or not, it can cause permanent reputation and potentially financial damage to your organization. Web. Hawk® Data Loss Prevention is a comprehensive service that helps keep your confidential data private, prevents data breaches and enforces compliance by scanning text and files to detect sensitive information attempting to exit your network, including documents that are printed or sent to mobile devices via Bluetooth, etc.
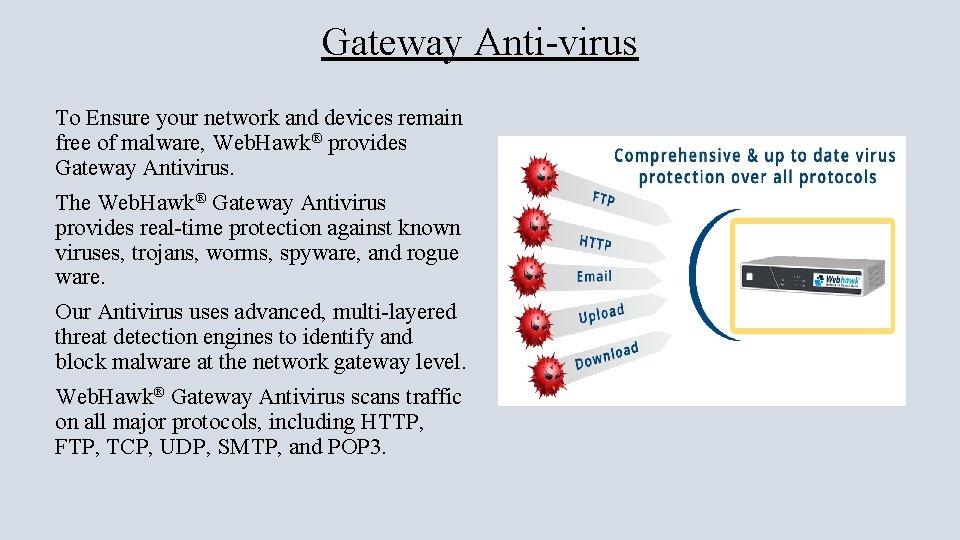
Gateway Anti-virus To Ensure your network and devices remain free of malware, Web. Hawk® provides Gateway Antivirus. The Web. Hawk® Gateway Antivirus provides real-time protection against known viruses, trojans, worms, spyware, and rogue ware. Our Antivirus uses advanced, multi-layered threat detection engines to identify and block malware at the network gateway level. Web. Hawk® Gateway Antivirus scans traffic on all major protocols, including HTTP, FTP, TCP, UDP, SMTP, and POP 3.
Real-time Visibility, Logging and Reporting Web. Hawk® Gateway Antivirus seamlessly integrates with Web. Hawk® Dimension for complete visibility into the top blocked malware as well as the source and destination of the attack. You also have instant views with dashboards and charts that show the total number of files scanned and number of viruses detected over a set period of time i. e Web. Hawk® provides real-time logging and reporting capabilities.
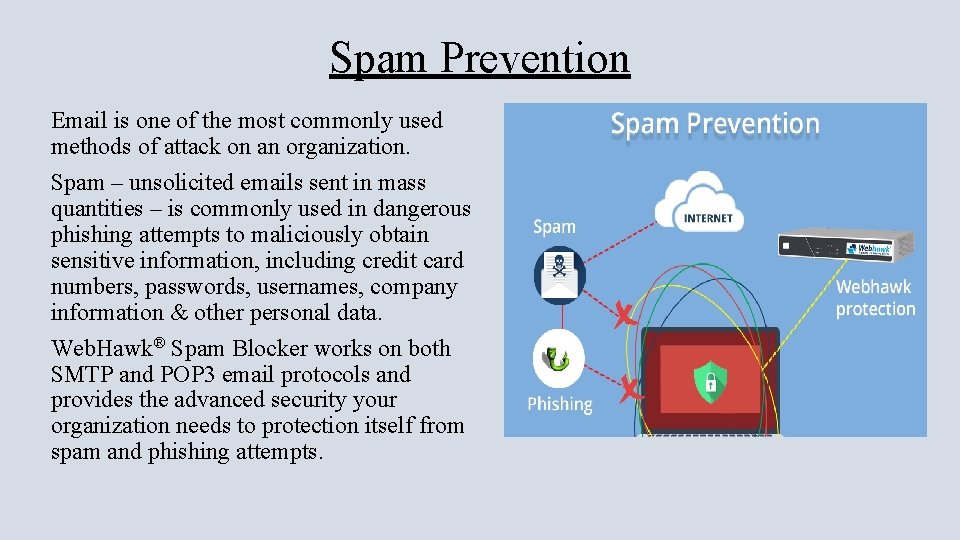
Spam Prevention Email is one of the most commonly used methods of attack on an organization. Spam – unsolicited emails sent in mass quantities – is commonly used in dangerous phishing attempts to maliciously obtain sensitive information, including credit card numbers, passwords, usernames, company information & other personal data. Web. Hawk® Spam Blocker works on both SMTP and POP 3 email protocols and provides the advanced security your organization needs to protection itself from spam and phishing attempts.
Tunnelling Web. Hawk® provides VPN services allowing users to create secure connections to other networks over the Internet. It creates a safe and encrypted connection over a less secure network, such as the public internet. • IPsec VPN: IPsec VPN uses tunnelling to establish a private connection through which all your data is passed through. IPsec operates at network layer and this allows it to encrypt the entire packet. • P 2 P VPN: PPTP doesn't do encryption, it simply tunnels and encapsulates the data packet. • SSL VPN: SSL VPN allow users to establish secure remote-access sessions from virtually any Internet-connected web browser. Delivering the ability for people to access e -mail, critical information systems, files, and other network resources from virtually anywhere is not a trivial task. SSL and TLS are used extensively in the security of online retailers and service providers.
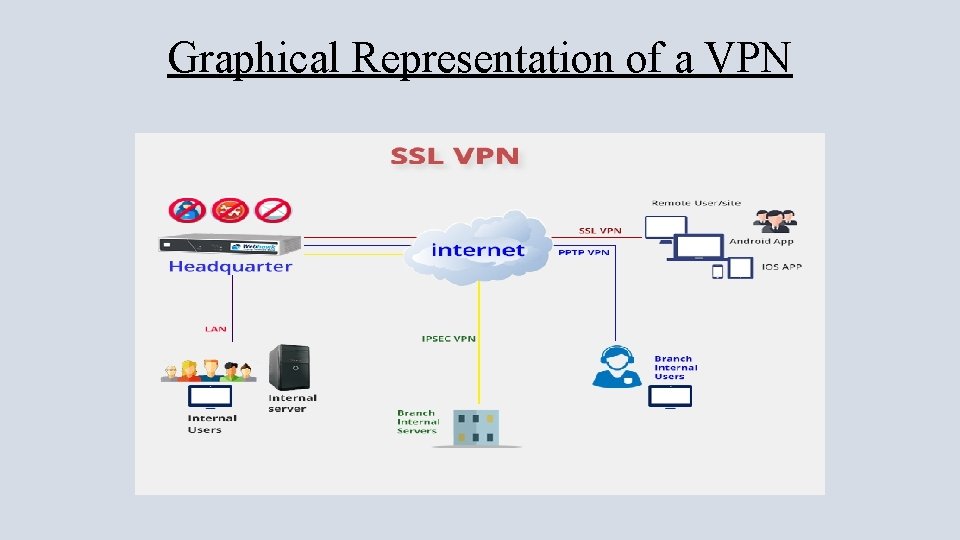
Graphical Representation of a VPN
Active Directory Domain Control • • • Central domain and directory management. Users, Security groups, Distribution lists, Contacts. Multiple Organization Units (OUs), Group Policy Objects (GPOs) Single Sign-On authentication Users and Groups access and modification permissions Management of user profile pictures User's and group’s Quota management USB Blocking for Users and groups Control over all the activities done by users
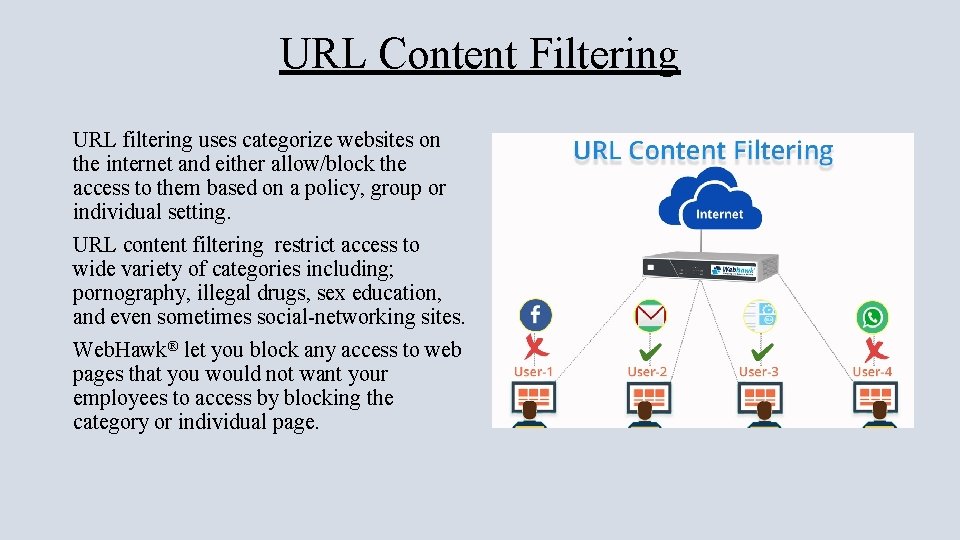
URL Content Filtering URL filtering uses categorize websites on the internet and either allow/block the access to them based on a policy, group or individual setting. URL content filtering restrict access to wide variety of categories including; pornography, illegal drugs, sex education, and even sometimes social-networking sites. Web. Hawk® let you block any access to web pages that you would not want your employees to access by blocking the category or individual page.
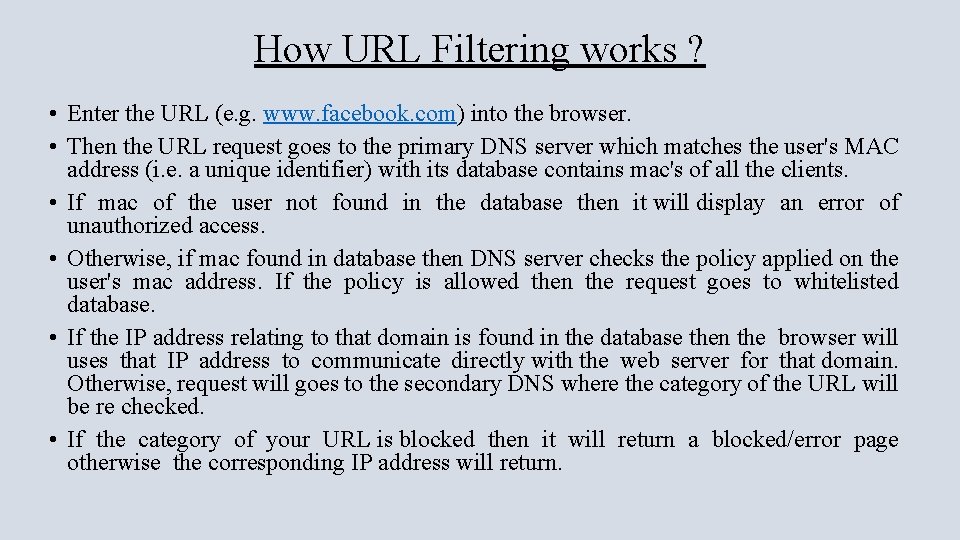
How URL Filtering works ? • Enter the URL (e. g. www. facebook. com) into the browser. • Then the URL request goes to the primary DNS server which matches the user's MAC address (i. e. a unique identifier) with its database contains mac's of all the clients. • If mac of the user not found in the database then it will display an error of unauthorized access. • Otherwise, if mac found in database then DNS server checks the policy applied on the user's mac address. If the policy is allowed then the request goes to whitelisted database. • If the IP address relating to that domain is found in the database then the browser will uses that IP address to communicate directly with the web server for that domain. Otherwise, request will goes to the secondary DNS where the category of the URL will be re checked. • If the category of your URL is blocked then it will return a blocked/error page otherwise the corresponding IP address will return.
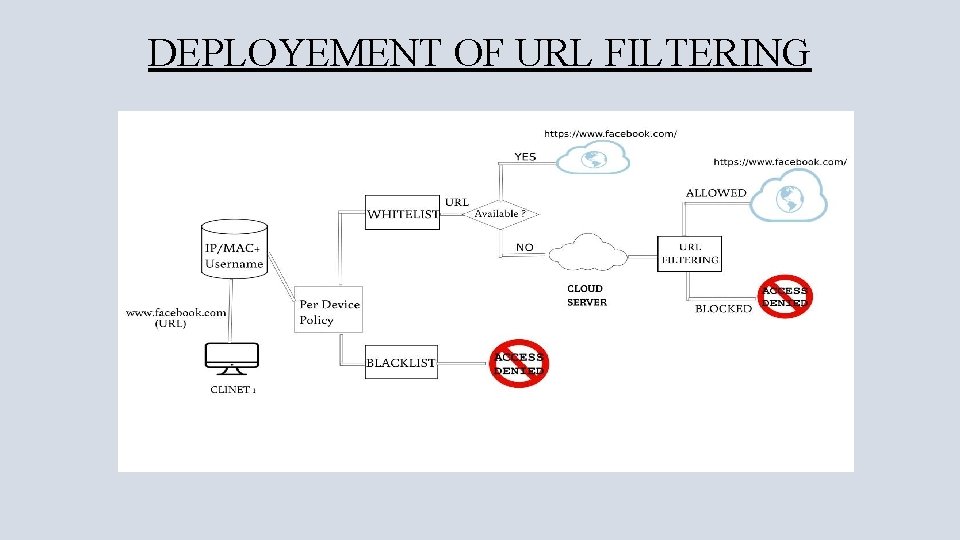
DEPLOYEMENT OF URL FILTERING
Cyber Attack Prevension
Benefits of Using Web. Hawk® • Easy to Deploy and maintain. • More Reliable and it runs in a single appliance it will involve less hardware replacement costs. • Cheaper, more effective, more flexible consume less power. • Less security staff required because there is only one system to maintain, update, upgrade, and monitor. • Software upgrades or updates are on any time will not affect the other services or the other components. Security logs are also available. • Backup and Restore point that saves your systems previous state allows you to revert Web. Hawk® to its previous point in time, which can be used to recover from system malfunctions or other problems.
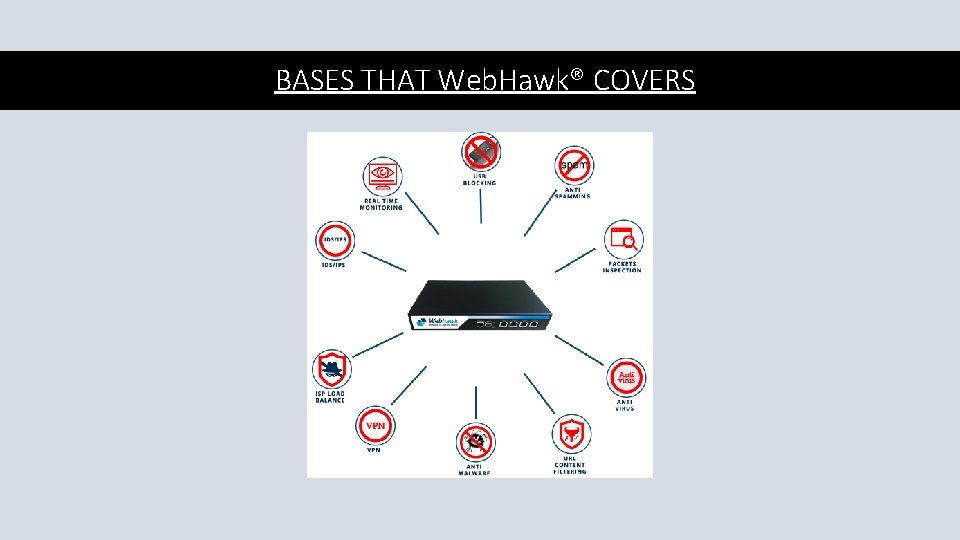
BASES THAT Web. Hawk® COVERS
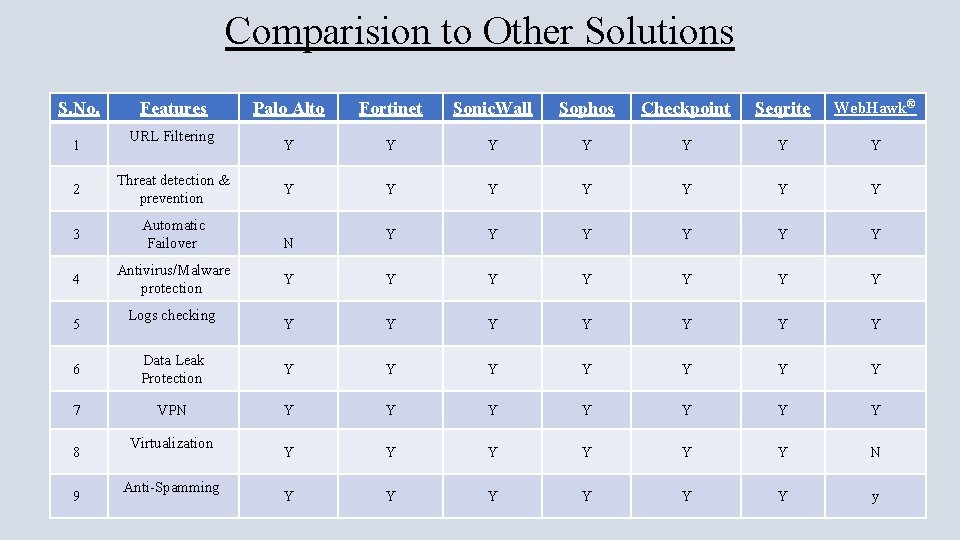
Comparision to Other Solutions S. No. 1 Features URL Filtering 2 Threat detection & prevention 3 Automatic Failover 4 Antivirus/Malware protection 5 Logs checking Palo Alto Fortinet Sonic. Wall Sophos Checkpoint Seqrite Web. Hawk® Y Y Y Y Y Y Y Y Y N 6 Data Leak Protection Y Y Y Y 7 VPN Y Y Y Y N Y Y Y y 8 9 Virtualization Anti-Spamming
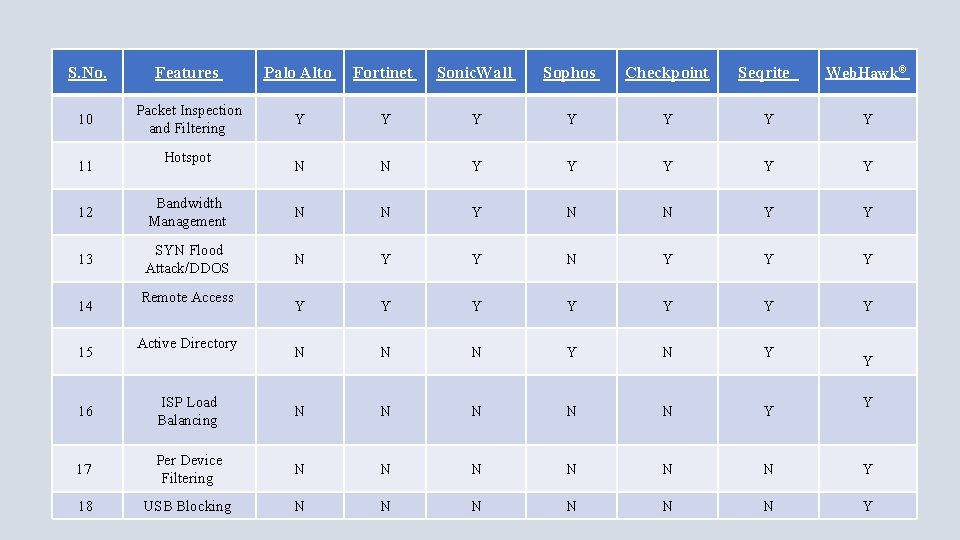
S. No. Features Palo Alto Fortinet Sonic. Wall Sophos Checkpoint Seqrite Web. Hawk® 10 Packet Inspection and Filtering Y Y Y Y N N Y Y Y 11 Hotspot 12 Bandwidth Management N N Y Y 13 SYN Flood Attack/DDOS N Y Y Y N N N Y 14 15 Remote Access Active Directory Y 16 ISP Load Balancing N N N Y Y 17 Per Device Filtering N N N Y 18 USB Blocking N N N Y
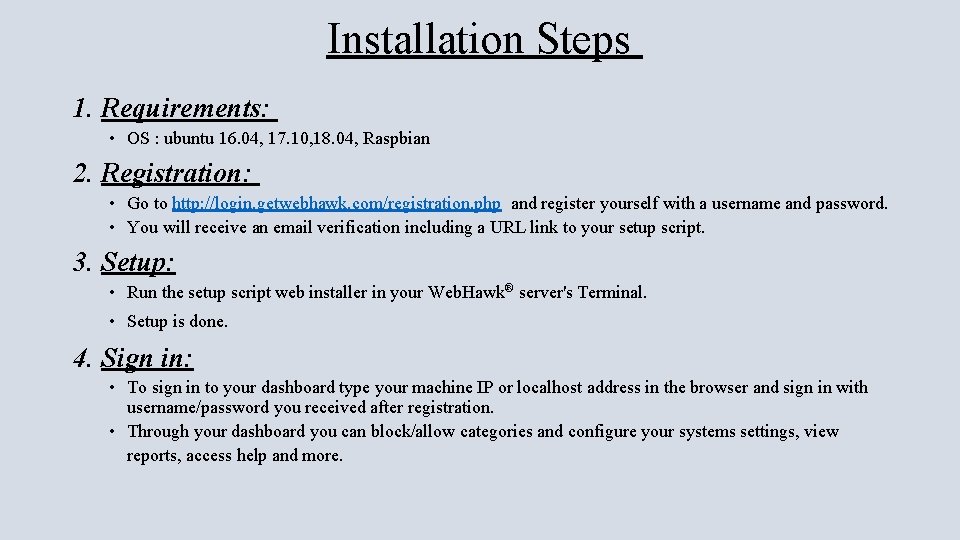
Installation Steps 1. Requirements: • OS : ubuntu 16. 04, 17. 10, 18. 04, Raspbian 2. Registration: • Go to http: //login. getwebhawk. com/registration. php and register yourself with a username and password. • You will receive an email verification including a URL link to your setup script. 3. Setup: • Run the setup script web installer in your Web. Hawk® server's Terminal. • Setup is done. 4. Sign in: • To sign in to your dashboard type your machine IP or localhost address in the browser and sign in with username/password you received after registration. • Through your dashboard you can block/allow categories and configure your systems settings, view reports, access help and more.

Thank you Please contact us with any questions: sales@getwebhawk. com +91 -788 -849 -1800
- Slides: 29