Kaspersky Security for Enterprise of our employees are








- Slides: 46

Kaspersky Security for Enterprise

of our employees are R&D specialists new malicious files are detected by Kaspersky every day Threat Research and Global Research and Analysis Teams are strategically located all around the globe, providing unparalleled depth of analysis and understanding of all kinds of threats. world-leading security researchers
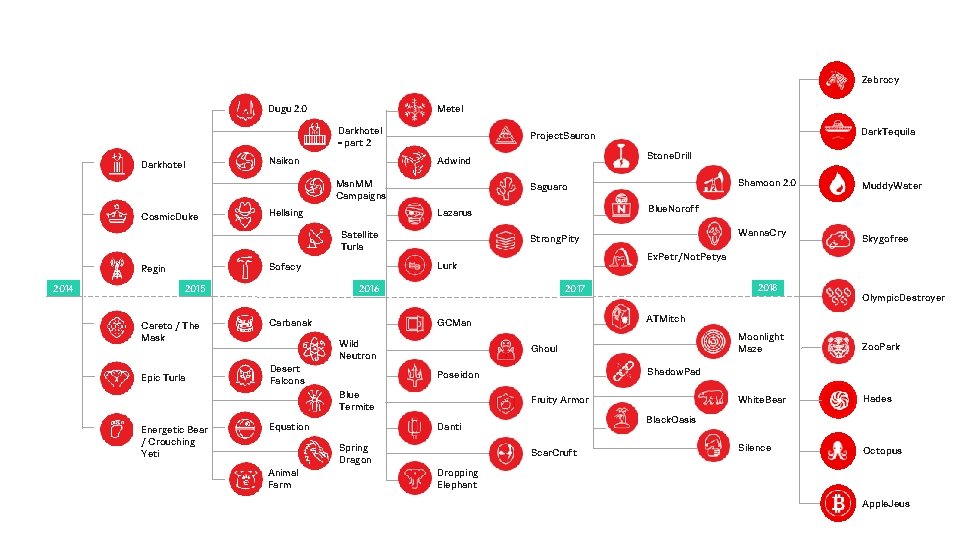
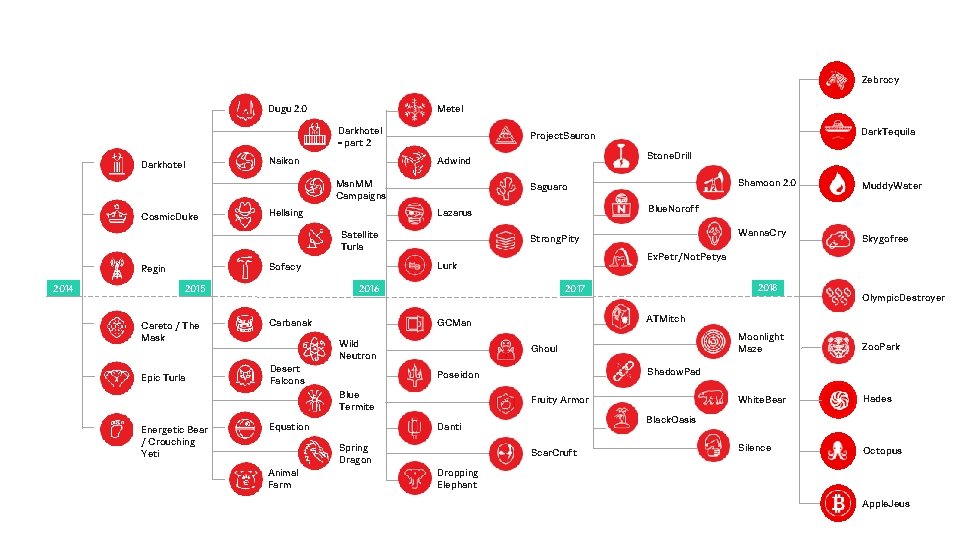
Zebrocy Metel Dugu 2. 0 Darkhotel - part 2 Darkhotel Msn. MM Campaigns Cosmic. Duke 2014 Careto / The Mask Epic Turla Wild Neutron Desert Falcons Fruity Armor Animal Farm Zoo. Park White. Bear Hades Silence Octopus Black. Oasis Danti Spring Dragon Moonlight Maze Shadow. Pad Poseidon Equation Olympic. Destroyer ATMitch Ghoul Blue Termite Energetic Bear / Crouching Yeti 2018 2017 GCMan Carbanak Skygofree Ex. Petr/Not. Petya 2016 2015 Wanna. Cry Strong. Pity Lurk Sofacy Muddy. Water Blue. Noroff Lazarus Hellsing Shamoon 2. 0 Saguaro Satellite Turla Regin Stone. Drill Adwind Naikon Dark. Tequila Project. Sauron Scar. Cruft Dropping Elephant Apple. Jeus

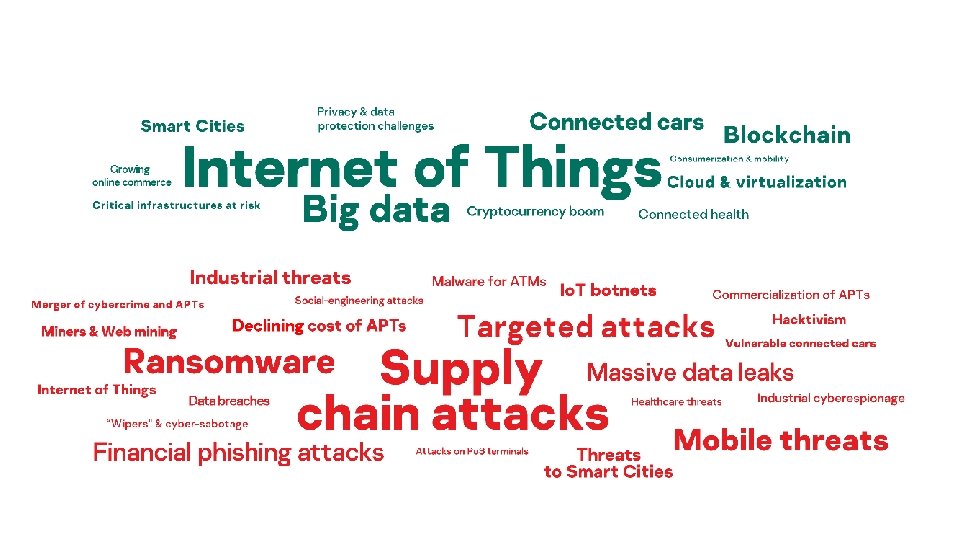
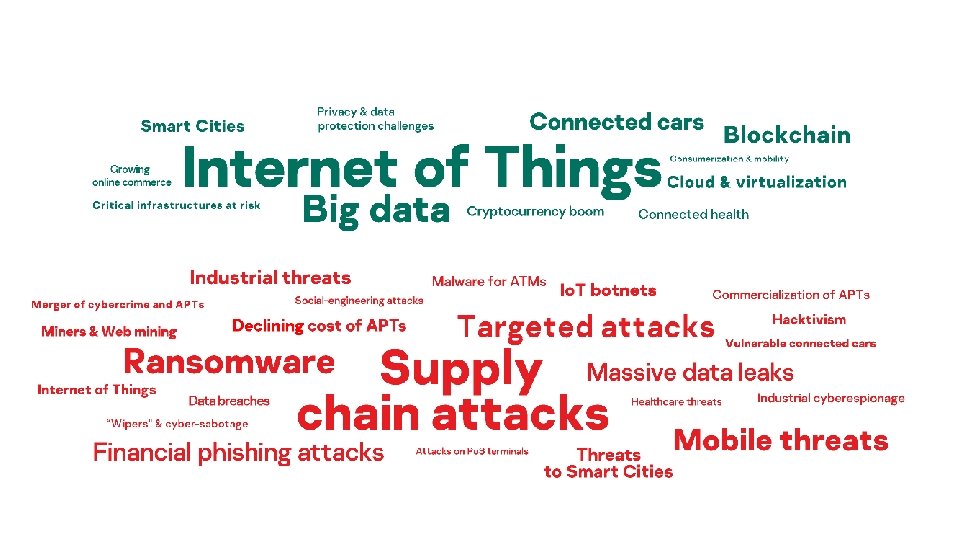
Industry trends and challenges
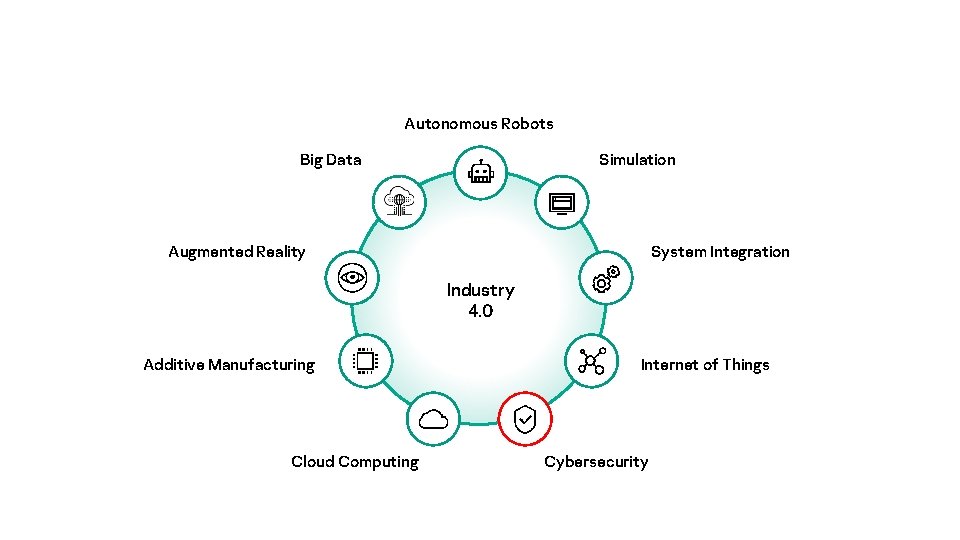
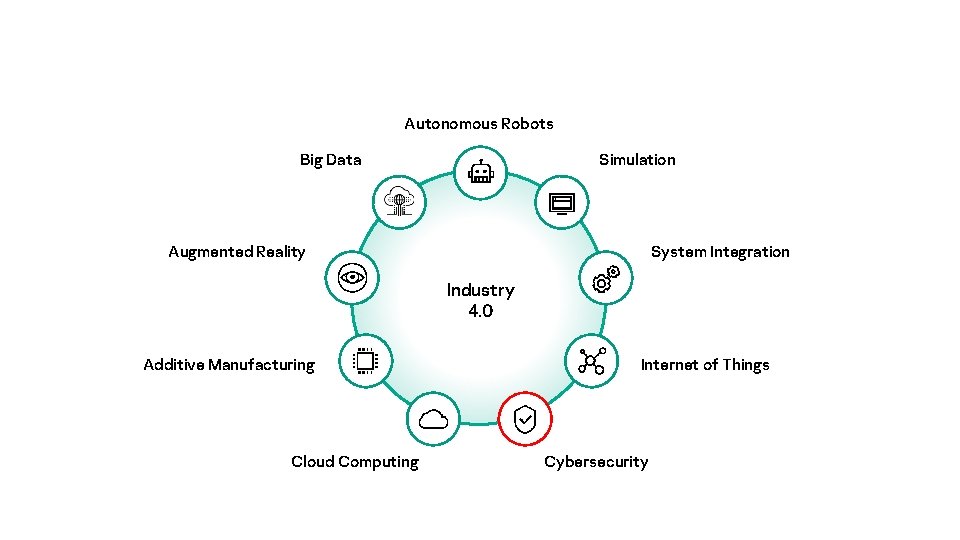
Autonomous Robots Big Data Simulation Augmented Reality System Integration Industry 4. 0 Additive Manufacturing Cloud Computing Internet of Things Cybersecurity
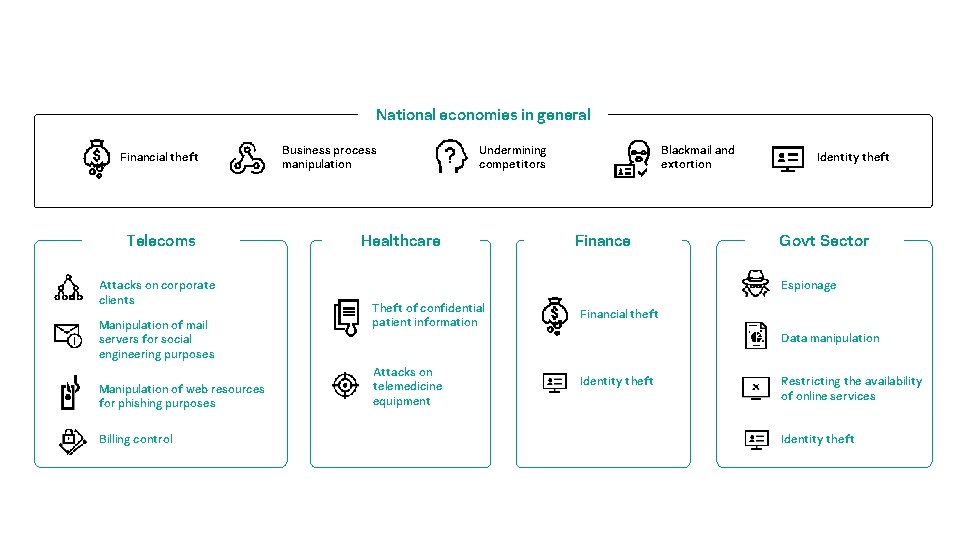
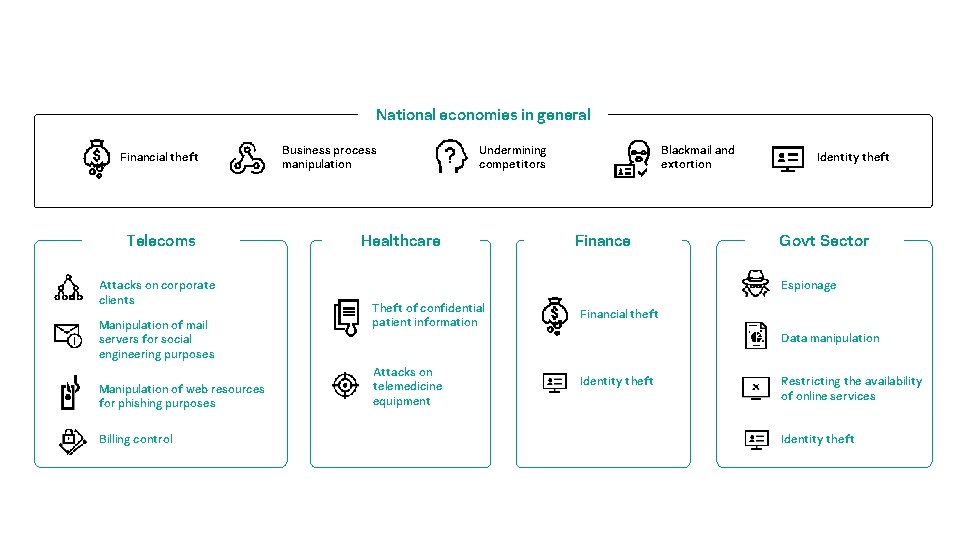
National economies in general Financial theft Telecoms Attacks on corporate clients Manipulation of mail servers for social engineering purposes Manipulation of web resources for phishing purposes Billing control Business process manipulation Undermining competitors Healthcare Blackmail and extortion Finance Identity theft Govt Sector Espionage Theft of confidential patient information Financial theft Data manipulation Attacks on telemedicine equipment Identity theft Restricting the availability of online services Identity theft
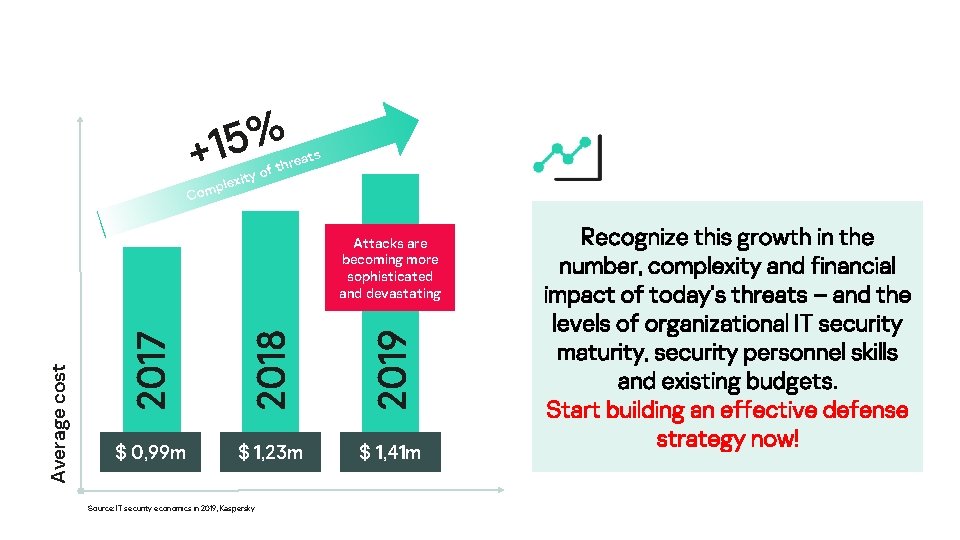
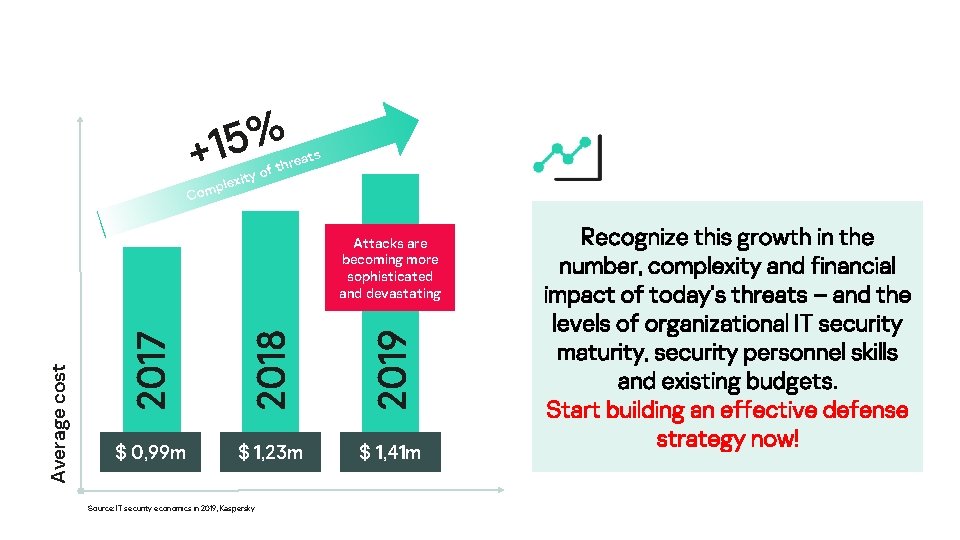
% 5 1 + ity o lex omp s reat f th C 2017 2018 2019 Average cost Attacks are becoming more sophisticated and devastating $ 0, 99 m $ 1, 23 m $ 1, 41 m Source: IT security economics in 2019, Kaspersky Recognize this growth in the number, complexity and financial impact of today’s threats – and the levels of organizational IT security maturity, security personnel skills and existing budgets. Start building an effective defense strategy now!
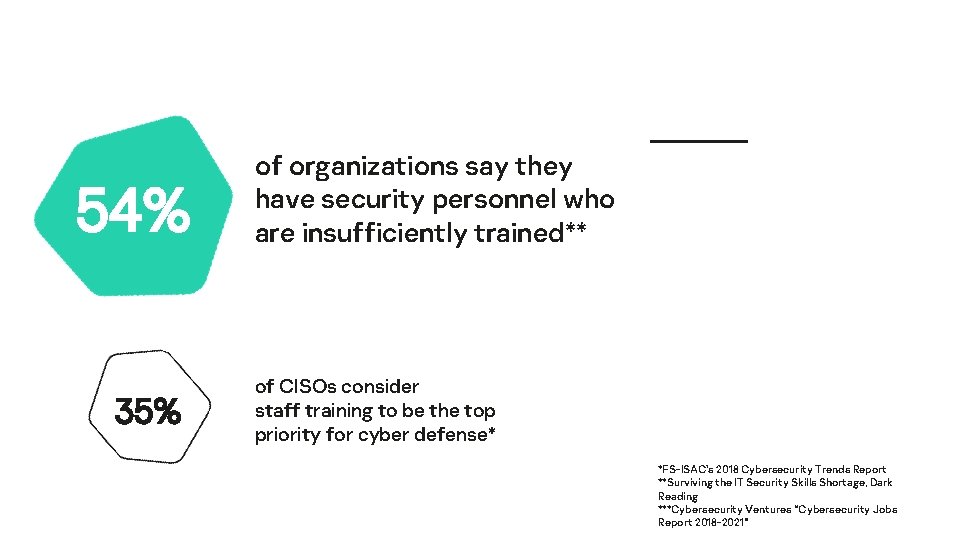
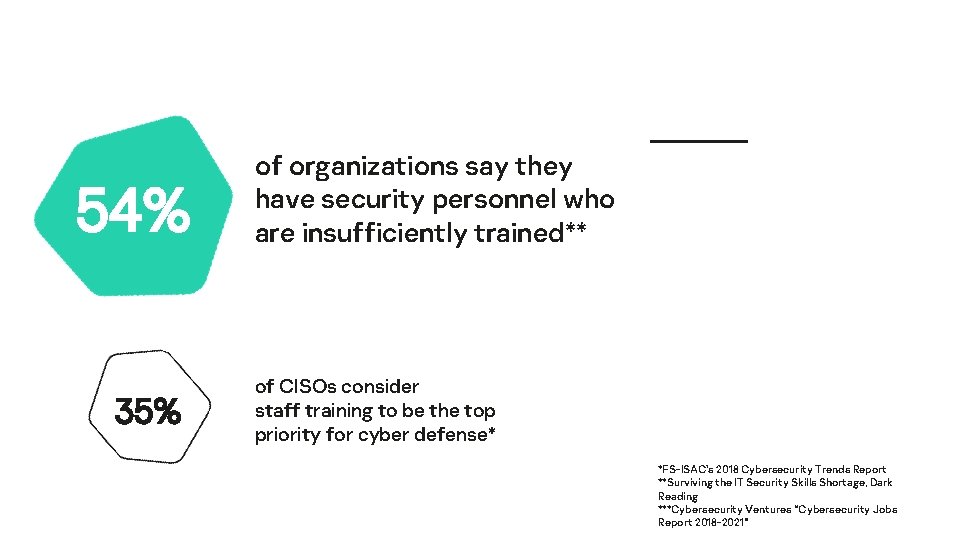
54% 35% of organizations say they have security personnel who are insufficiently trained** of CISOs consider staff training to be the top priority for cyber defense* *FS-ISAC's 2018 Cybersecurity Trends Report **Surviving the IT Security Skills Shortage, Dark Reading ***Cybersecurity Ventures “Cybersecurity Jobs Report 2018 -2021”
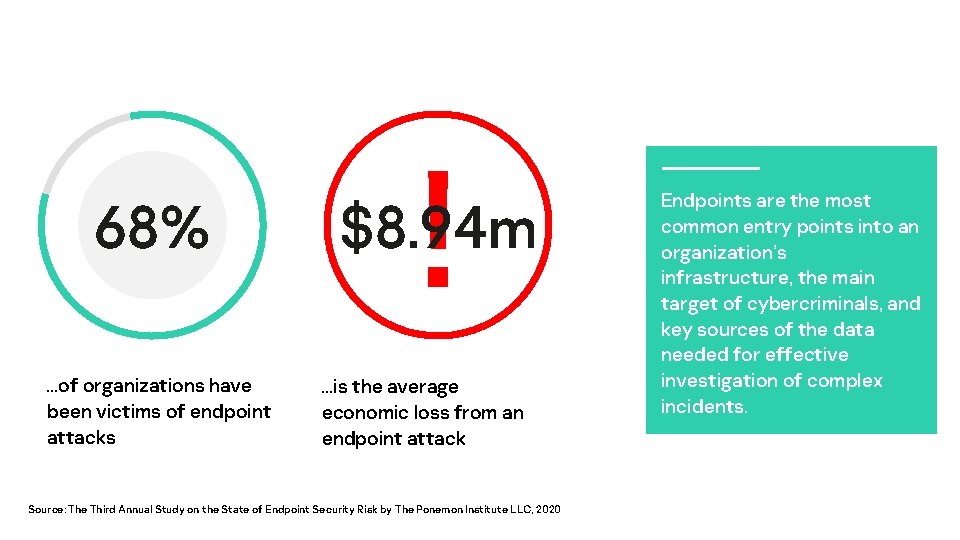
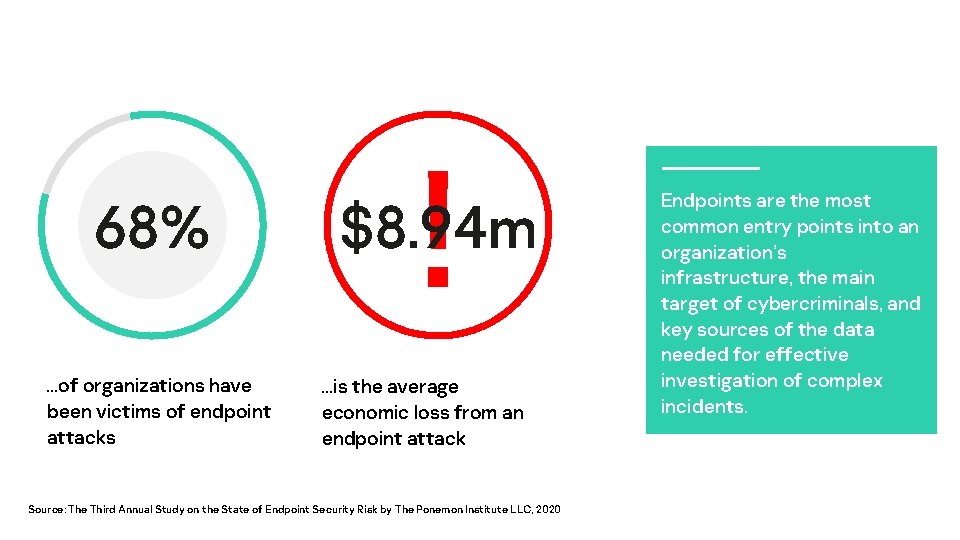
68% v …of organizations have been victims of endpoint attacks ! $8. 94 m …is the average economic loss from an endpoint attack Source: The Third Annual Study on the State of Endpoint Security Risk by The Ponemon Institute LLC, 2020 Endpoints are the most common entry points into an organization’s infrastructure, the main target of cybercriminals, and key sources of the data needed for effective investigation of complex incidents.
A stage-by-stage, endpoint-centric cybersecurity strategy

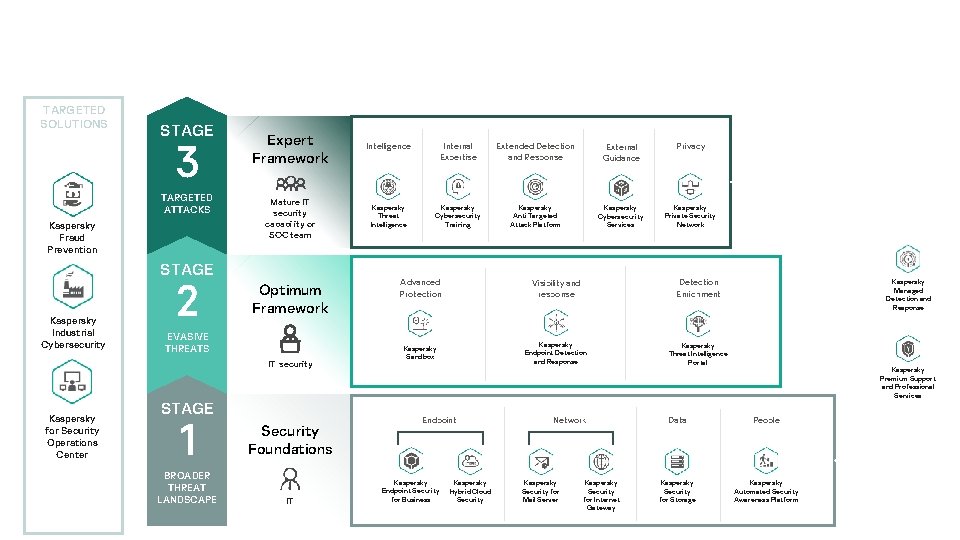
Targeted attacks Sophistication of attacks Mature IT security capability or SOC team Evasive threats IT security Commodity threats IT Expertise required
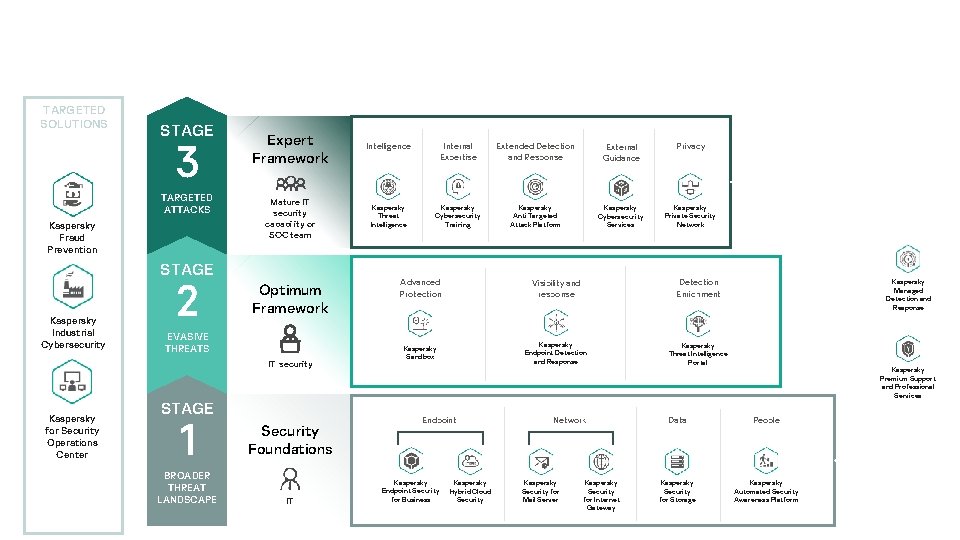
TARGETED SOLUTIONS STAGE 3 TARGETED ATTACKS Kaspersky Fraud Prevention Expert Framework Intelligence Internal Expertise Extended Detection and Response External Guidance Privacy Mature IT security capability or SOC team Kaspersky Threat Intelligence Kaspersky Cybersecurity Training Kaspersky Anti Targeted Attack Platform Kaspersky Cybersecurity Services Kaspersky Private Security Network STAGE Kaspersky Industrial Cybersecurity 2 Optimum Framework EVASIVE THREATS IT security Kaspersky for Security Operations Center STAGE 1 BROADER THREAT LANDSCAPE Security Foundations IT Advanced Protection Visibility and response Detection Enrichment Kaspersky Sandbox Kaspersky Endpoint Detection and Response Kaspersky Threat Intelligence Portal Endpoint Kaspersky Endpoint Security for Business Kaspersky Hybrid Cloud Security Network Kaspersky Security for Mail Server Kaspersky Security for Internet Gateway Kaspersky Managed Detection and Response Kaspersky Premium Support and Professional Services Data People Kaspersky Security for Storage Kaspersky Automated Security Awareness Platform
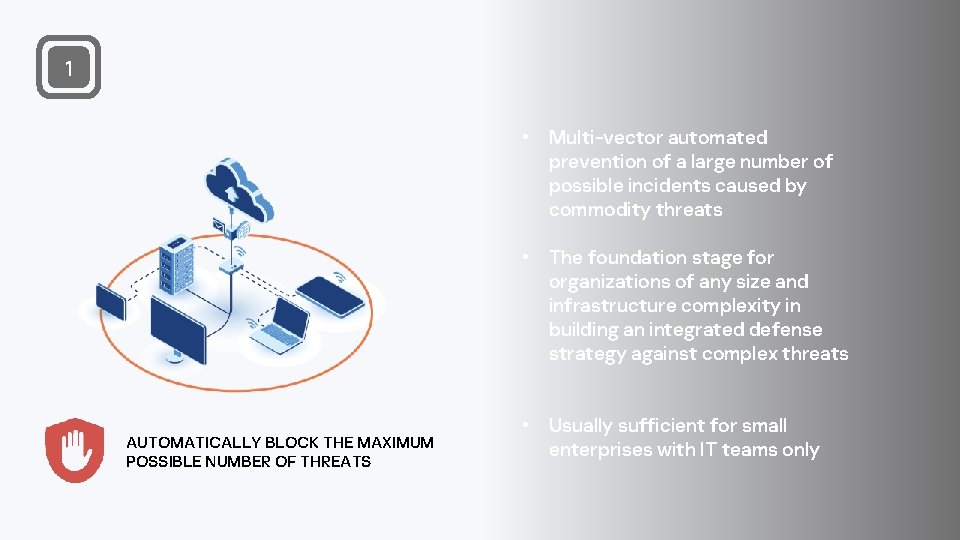
1 • Multi-vector automated prevention of a large number of possible incidents caused by commodity threats • The foundation stage for organizations of any size and infrastructure complexity in building an integrated defense strategy against complex threats AUTOMATICALLY BLOCK THE MAXIMUM POSSIBLE NUMBER OF THREATS • Usually sufficient for small enterprises with IT teams only
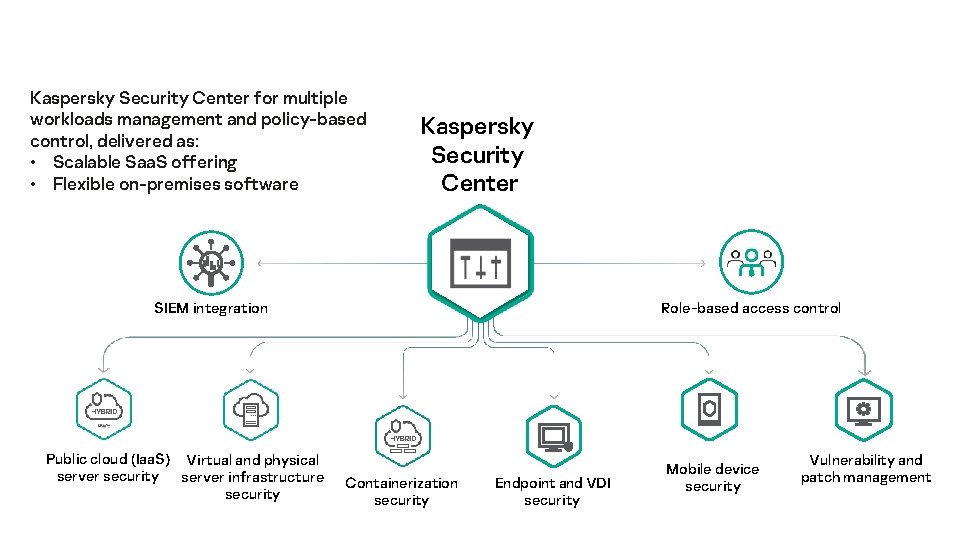
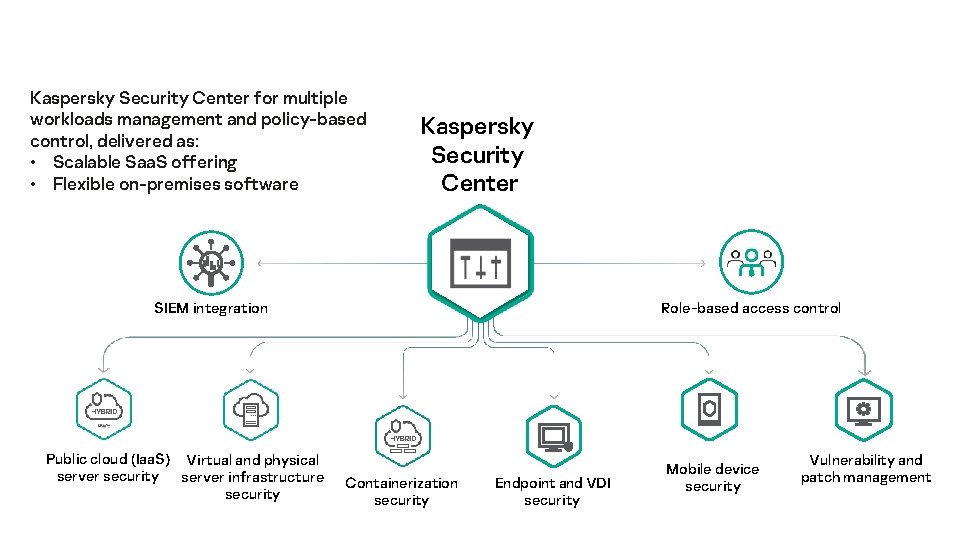
Kaspersky Security Center for multiple workloads management and policy-based control, delivered as: • Scalable Saa. S offering • Flexible on-premises software Kaspersky Security Center SIEM integration Public cloud (Iaa. S) Virtual and physical server security server infrastructure security Role-based access control Containerization security Endpoint and VDI security Mobile device security Vulnerability and patch management
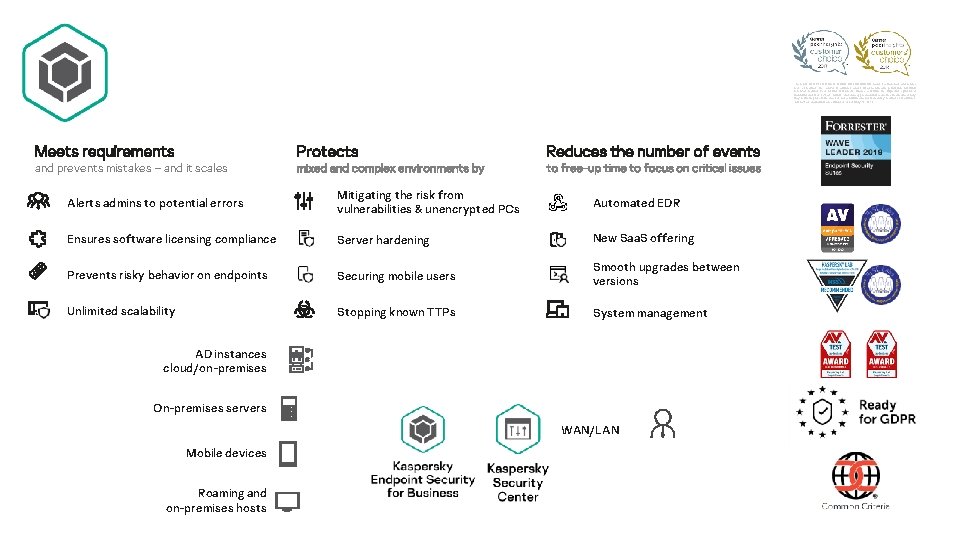
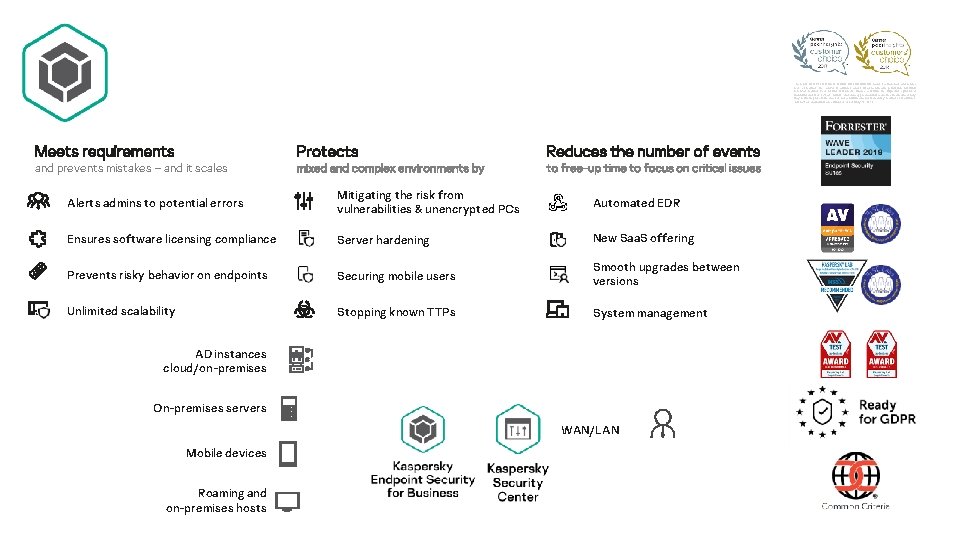
The GARTNER PEER INSIGHTS CUSTOMERS’ CHOICE badge is a trademark and service mark of Gartner, Inc. , and/or its affiliates, and is used herein with permission. All rights reserved. Gartner Peer Insights Customers’ Choice constitute the subjective opinions of individual end-user reviews, ratings, and data applied against a documented methodology; they neither represent the views of, nor constitute an endorsement by, Gartner or its affiliates. *All reviews and ratings are current as of February 12, 2019. Meets requirements and prevents mistakes – and it scales Protects mixed and complex environments by Reduces the number of events to free-up time to focus on critical issues Alerts admins to potential errors Mitigating the risk from vulnerabilities & unencrypted PCs Automated EDR Ensures software licensing compliance Server hardening New Saa. S offering Prevents risky behavior on endpoints Securing mobile users Smooth upgrades between versions Unlimited scalability Stopping known TTPs System management AD instances cloud/on-premises On-premises servers WAN/LAN Mobile devices Roaming and on-premises hosts
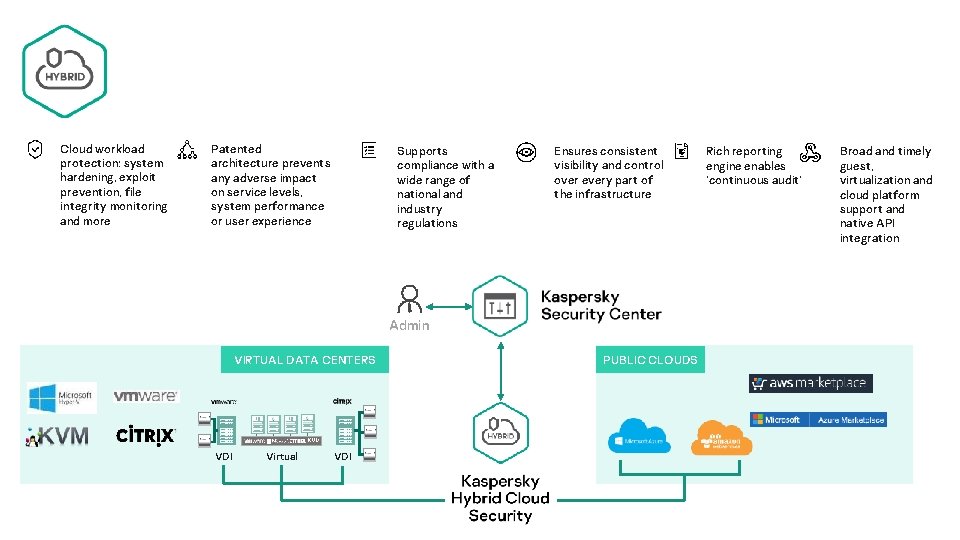
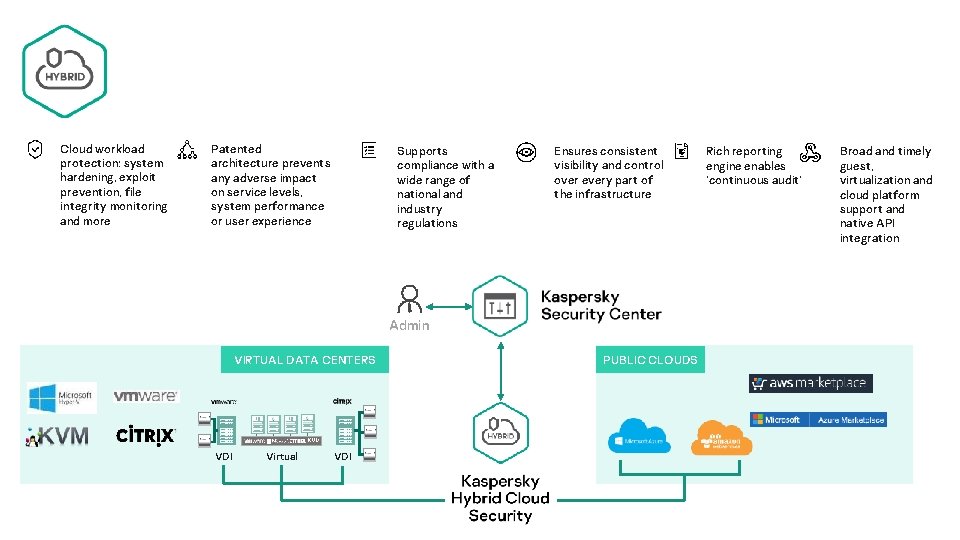
Cloud workload protection: system hardening, exploit prevention, file integrity monitoring and more Patented architecture prevents any adverse impact on service levels, system performance or user experience Supports compliance with a wide range of national and industry regulations Ensures consistent visibility and control over every part of the infrastructure Admin VIRTUAL DATA CENTERS VDI Virtual VDI PUBLIC CLOUDS Rich reporting engine enables ‘continuous audit’ Broad and timely guest, virtualization and cloud platform support and native API integration
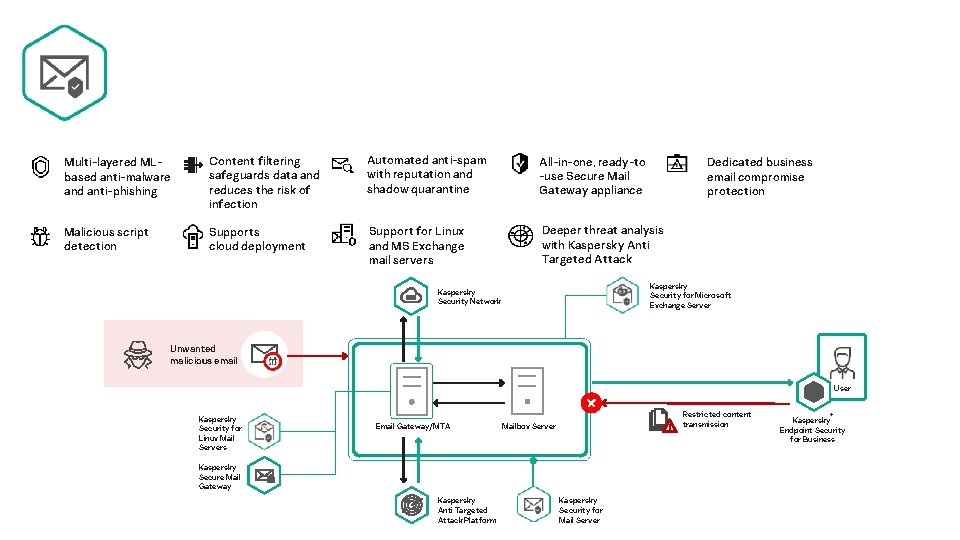
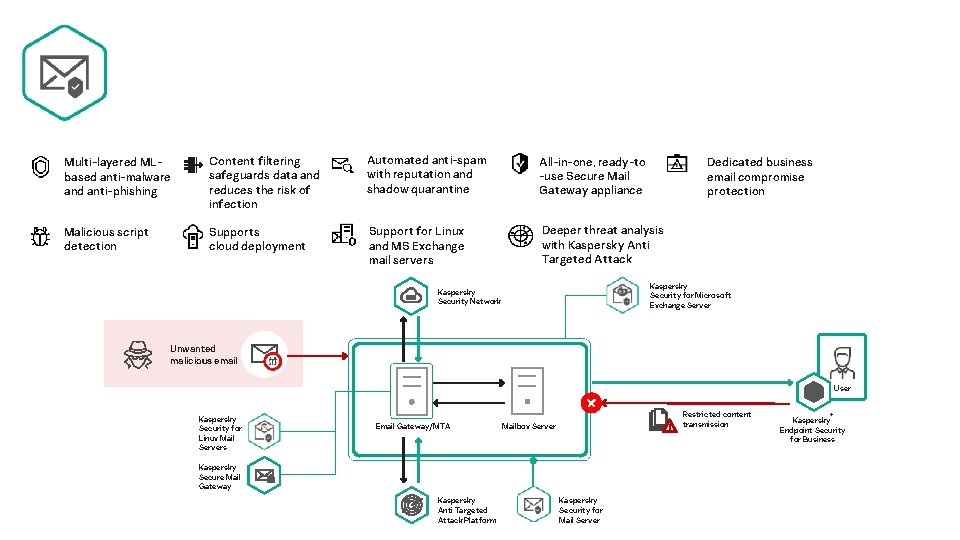
Multi-layered MLbased anti-malware and anti-phishing Content filtering safeguards data and reduces the risk of infection Automated anti-spam with reputation and shadow quarantine All-in-one, ready-to -use Secure Mail Gateway appliance Malicious script detection Supports cloud deployment Support for Linux and MS Exchange mail servers Deeper threat analysis with Kaspersky Anti Targeted Attack Dedicated business email compromise protection Kaspersky Security for Microsoft Exchange Server Kaspersky Security Network Unwanted malicious email User Kaspersky Security for Linux Mail Servers Email Gateway/MTA Restricted content transmission Mailbox Server Kaspersky Secure Mail Gateway Kaspersky Anti Targeted Attack Platform Kaspersky Security for Mail Server ® Kaspersky Endpoint Security for Business
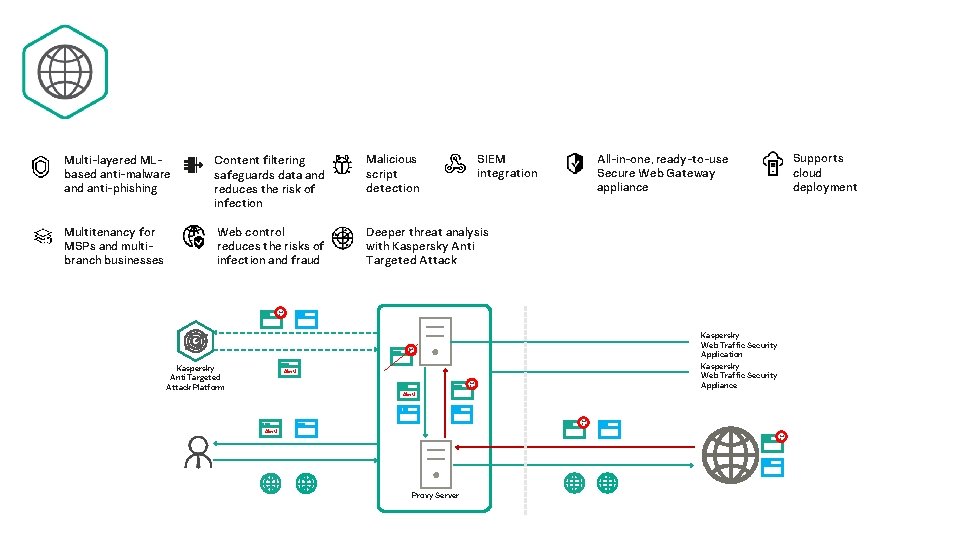
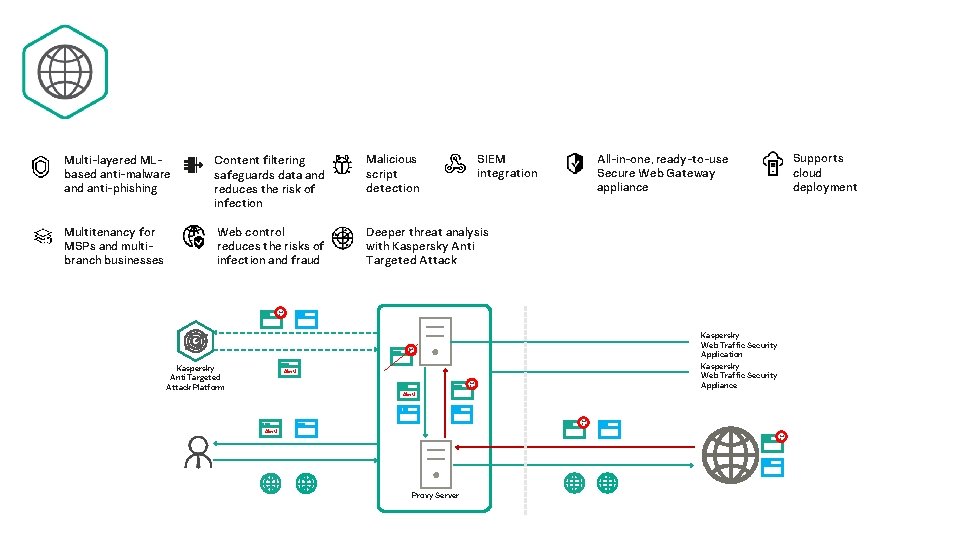
SIEM integration Multi-layered MLbased anti-malware and anti-phishing Content filtering safeguards data and reduces the risk of infection Malicious script detection Multitenancy for MSPs and multibranch businesses Web control reduces the risks of infection and fraud Deeper threat analysis with Kaspersky Anti Targeted Attack Platform All-in-one, ready-to-use Secure Web Gateway appliance Kaspersky Web Traffic Security Application Kaspersky Web Traffic Security Appliance Alert! Proxy Server Supports cloud deployment
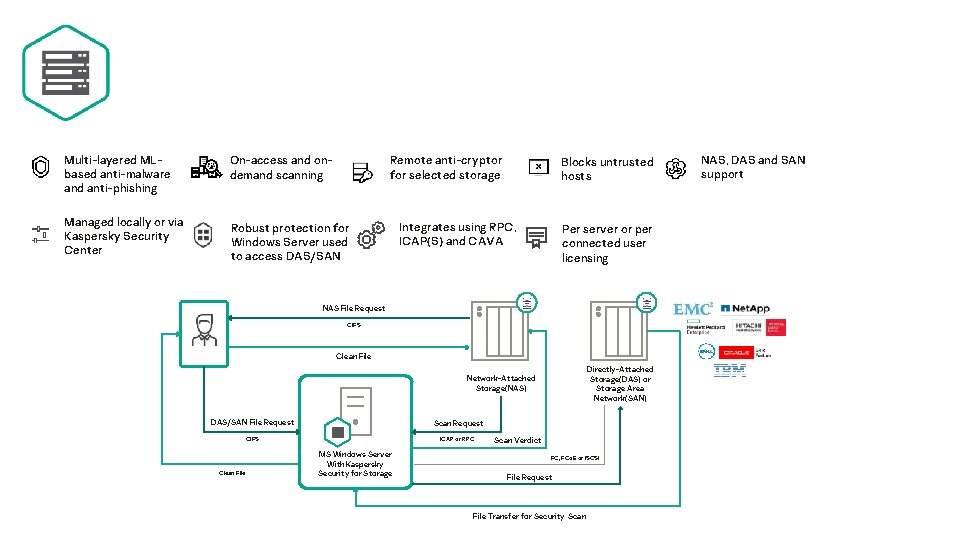
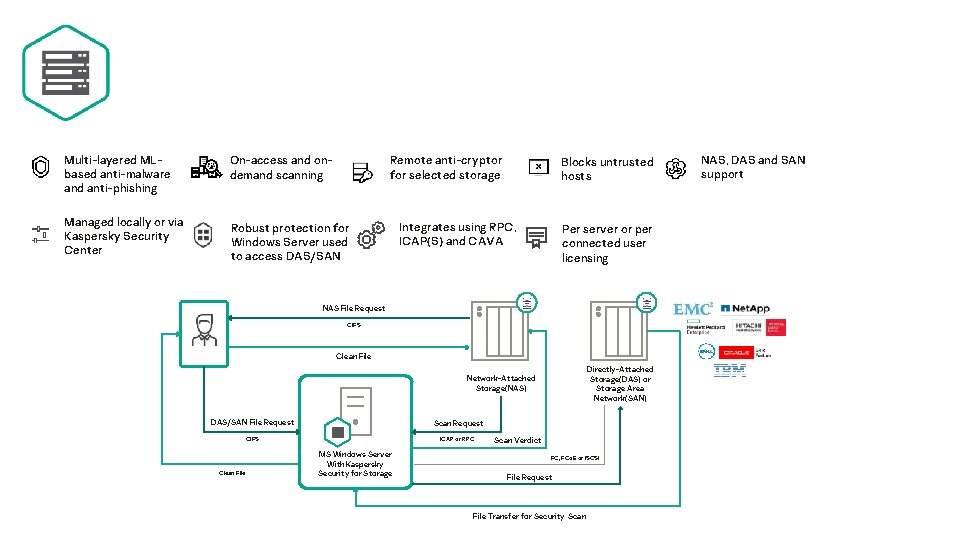
Multi-layered MLbased anti-malware and anti-phishing On-access and ondemand scanning Managed locally or via Kaspersky Security Center Robust protection for Windows Server used to access DAS/SAN Remote anti-cryptor for selected storage Blocks untrusted hosts Integrates using RPC, ICAP(S) and CAVA Per server or per connected user licensing NAS File Request CIFS Clean File Directly-Attached Storage(DAS) or Storage Area Network(SAN) Network-Attached Storage(NAS) DAS/SAN File Request Scan Request CIFS ICAP or RPC Clean File MS Windows Server With Kaspersky Security for Storage Scan Verdict FC, FCo. E or ISCSI File Request File Transfer for Security Scan NAS, DAS and SAN support
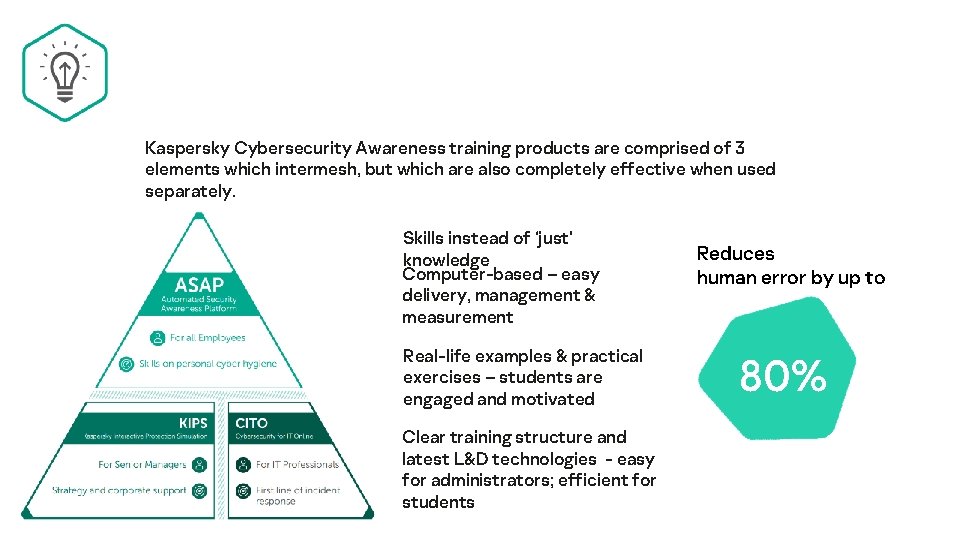
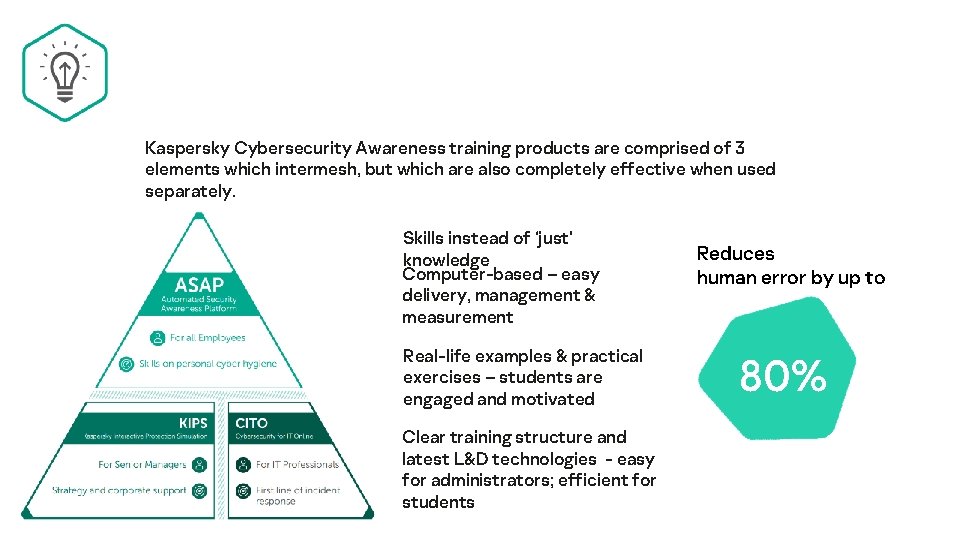
Kaspersky Cybersecurity Awareness training products are comprised of 3 elements which intermesh, but which are also completely effective when used separately. Skills instead of ‘just’ knowledge Computer-based – easy delivery, management & measurement Real-life examples & practical exercises – students are engaged and motivated Clear training structure and latest L&D technologies - easy for administrators; efficient for students Reduces human error by up to 80%
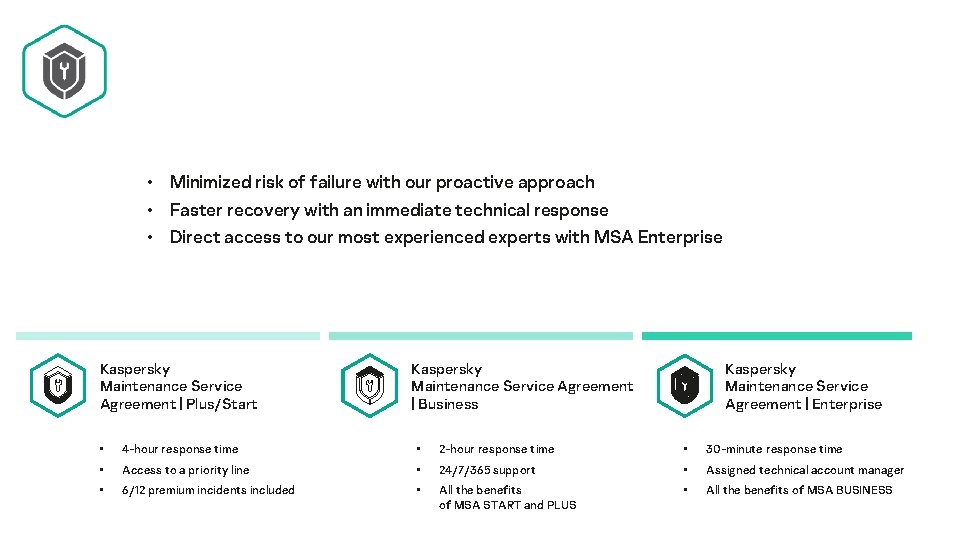
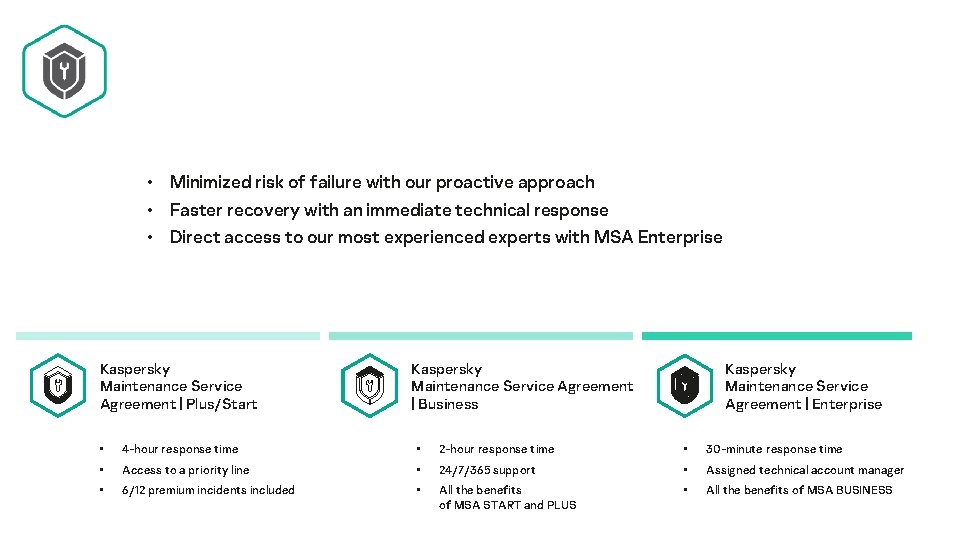
• Minimized risk of failure with our proactive approach • Faster recovery with an immediate technical response • Direct access to our most experienced experts with MSA Enterprise Kaspersky Maintenance Service Agreement | Plus/Start Kaspersky Maintenance Service Agreement | Business Kaspersky Maintenance Service Agreement | Enterprise • 4 -hour response time • 2 -hour response time • 30 -minute response time • Access to a priority line • 24/7/365 support • Assigned technical account manager • 6/12 premium incidents included • All the benefits of MSA START and PLUS • All the benefits of MSA BUSINESS
Access to globally renowned security experts Risk protection assurance Maximize ROI Ultimate product experience
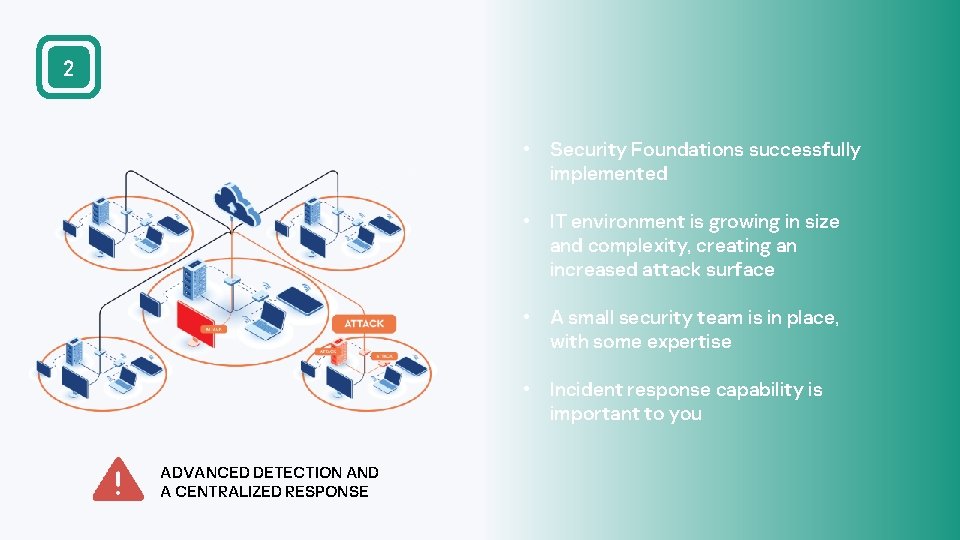
2 • Security Foundations successfully implemented • IT environment is growing in size and complexity, creating an increased attack surface • A small security team is in place, with some expertise • Incident response capability is important to you ADVANCED DETECTION AND A CENTRALIZED RESPONSE

In 2020, organizations everywhere have been forced to evolve their IT infrastructures almost overnight, blurring the boundaries of office walls. Today it’s time to combine all these 3 steps into one, to protect business continuity. 1 – Endpoint Protection Platform; 2 – Endpoint Detection and Response
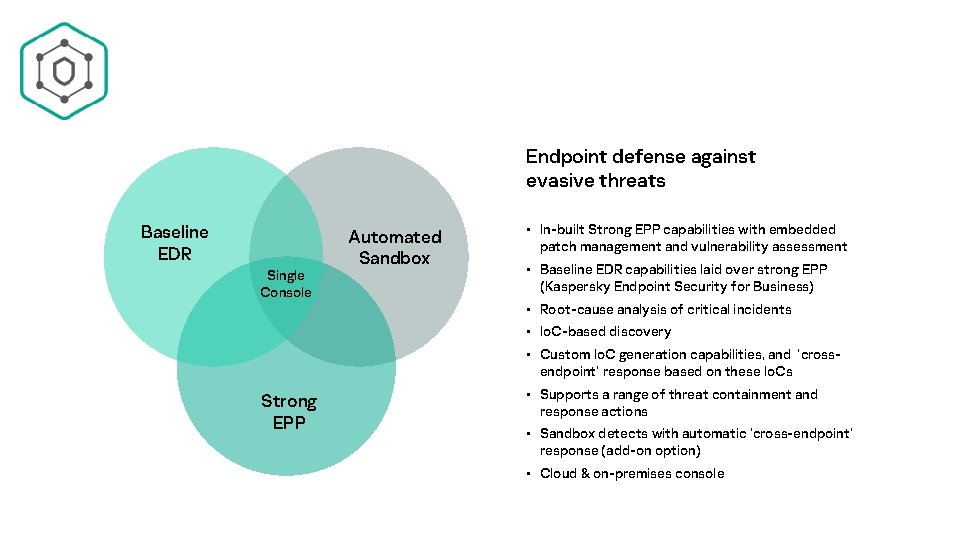
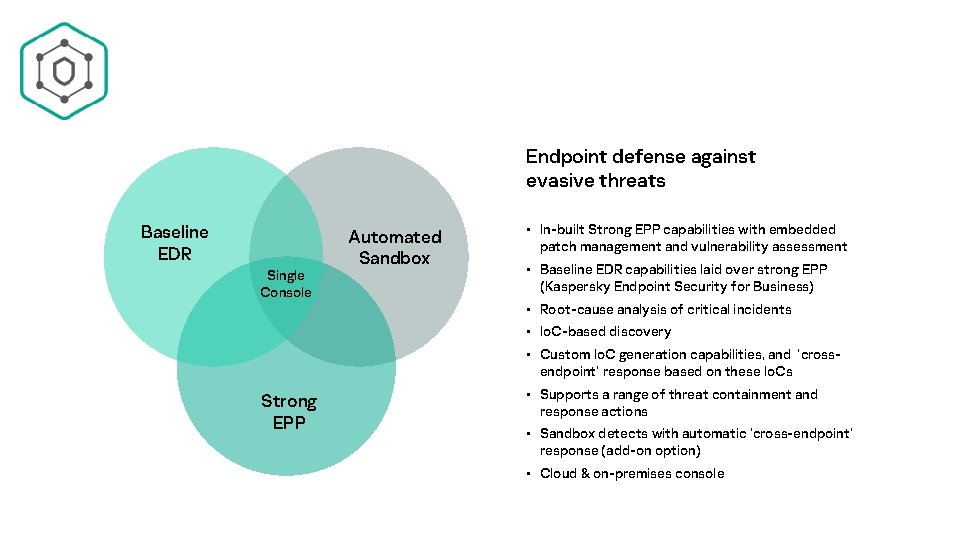
Endpoint defense against evasive threats Baseline EDR Single Console Automated Sandbox • In-built Strong EPP capabilities with embedded patch management and vulnerability assessment • Baseline EDR capabilities laid over strong EPP (Kaspersky Endpoint Security for Business) • Root-cause analysis of critical incidents • Io. C-based discovery • Custom Io. C generation capabilities, and ‘crossendpoint’ response based on these Io. Cs Strong EPP • Supports a range of threat containment and response actions • Sandbox detects with automatic ‘cross-endpoint’ response (add-on option) • Cloud & on-premises console
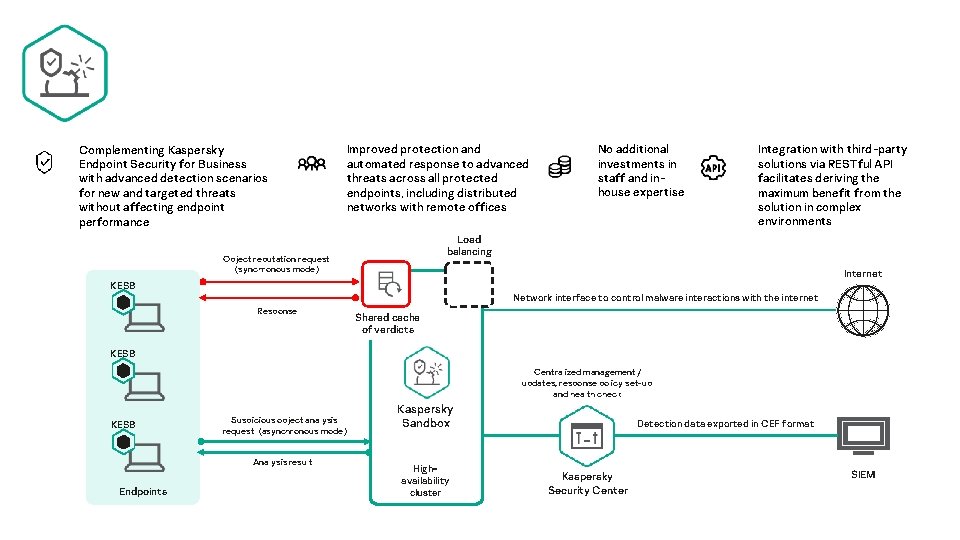
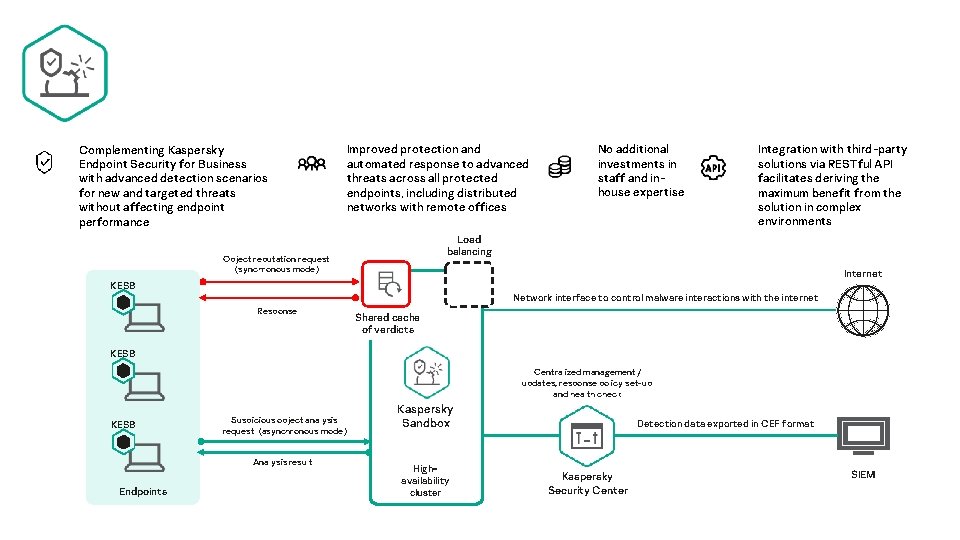
Complementing Kaspersky Endpoint Security for Business with advanced detection scenarios for new and targeted threats without affecting endpoint performance Improved protection and automated response to advanced threats across all protected endpoints, including distributed networks with remote offices No additional investments in staff and inhouse expertise Integration with third-party solutions via RESTful API facilitates deriving the maximum benefit from the solution in complex environments Load balancing Object reputation request (synchronous mode) Internet KESB Network interface to control malware interactions with the internet Response Shared cache of verdicts KESB Centralized management/ updates, response policy set-up and health check KESB Suspicious object analysis request (asynchronous mode) Analysis result Endpoints Kaspersky Sandbox Highavailability cluster Detection data exported in CEF format Kaspersky Security Center SIEM
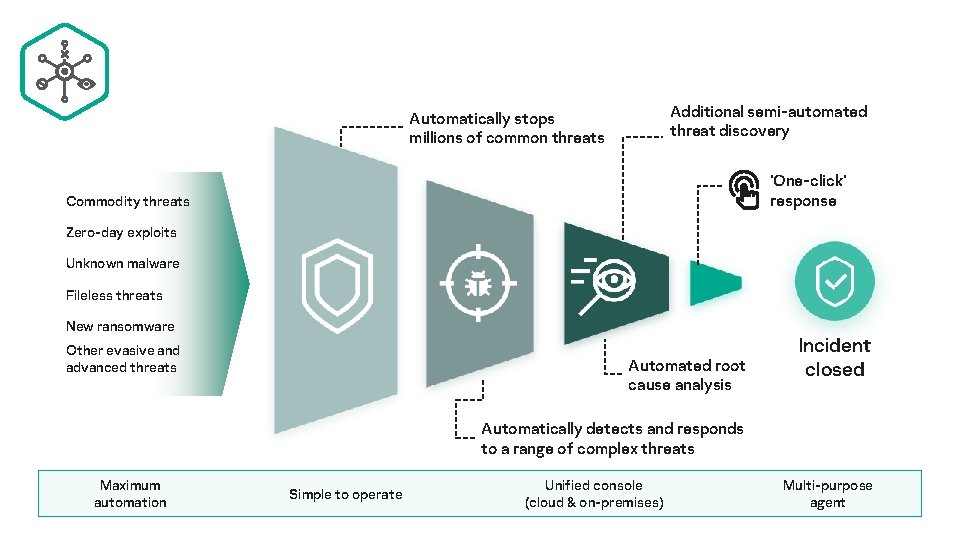
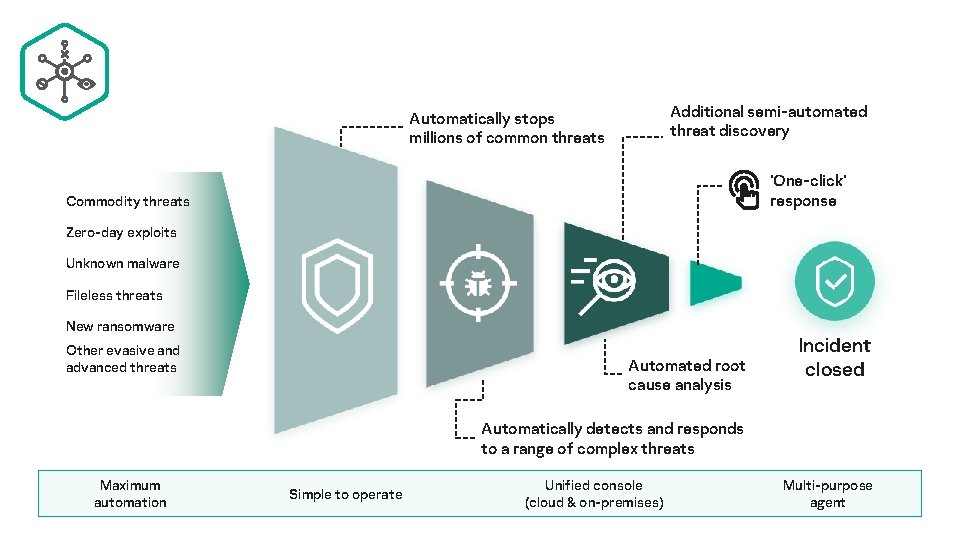
Additional semi-automated threat discovery Automatically stops millions of common threats ‘One-click’ response Commodity threats Zero-day exploits Unknown malware Fileless threats New ransomware Other evasive and advanced threats Automated root cause analysis Incident closed Automatically detects and responds to a range of complex threats Maximum automation Simple to operate Unified console (cloud & on-premises) Multi-purpose agent
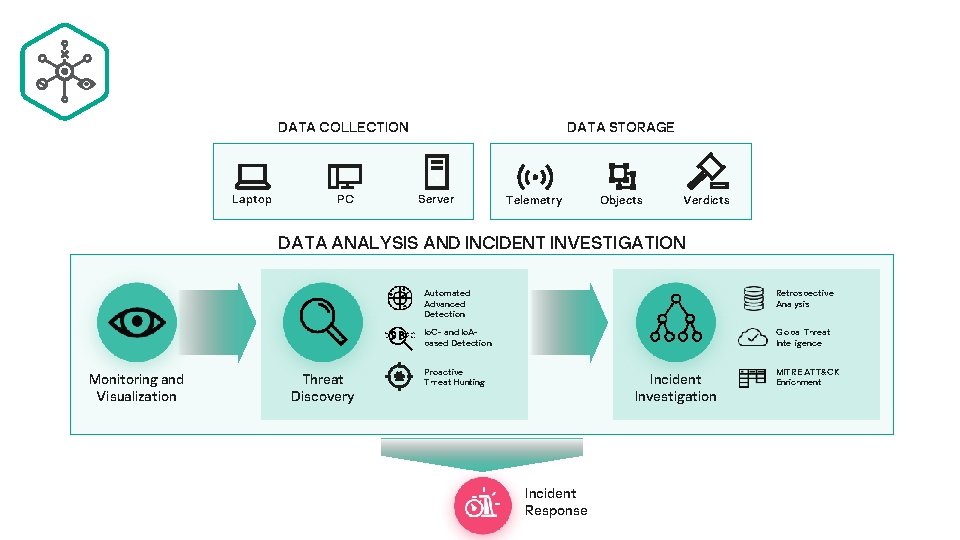
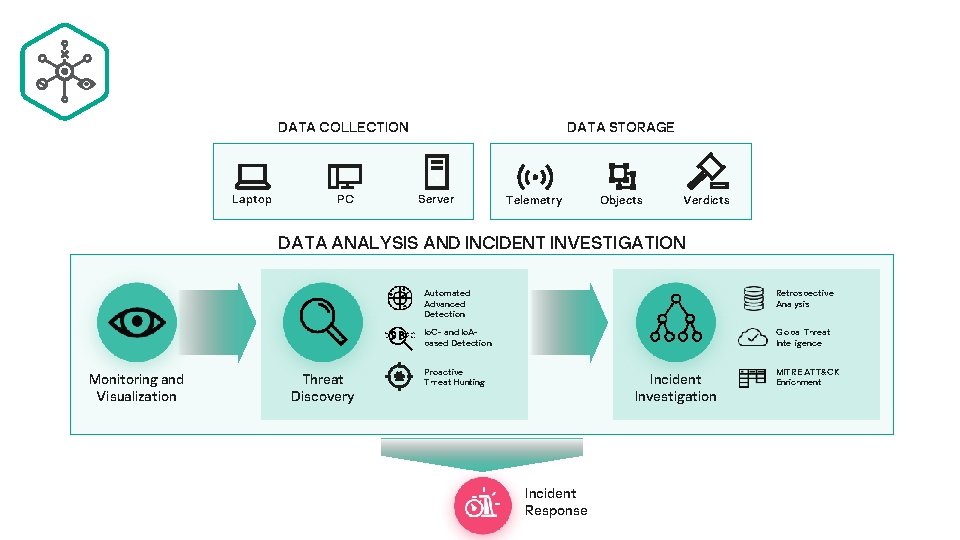
DATA STORAGE DATA COLLECTION Laptop PC Server Telemetry Objects Verdicts DATA ANALYSIS AND INCIDENT INVESTIGATION Monitoring and Visualization Threat Discovery Automated Advanced Detection Retrospective Analysis Io. C- and Io. Abased Detection Global Threat Intelligence Proactive Threat Hunting Incident Investigation Incident Response MITRE ATT&CK Enrichment
Fast, scalable turnkey deployment Completely managed or guided incident response Superior protection against even the most innovative non-malware threats Real-time situational awareness through various communication channels
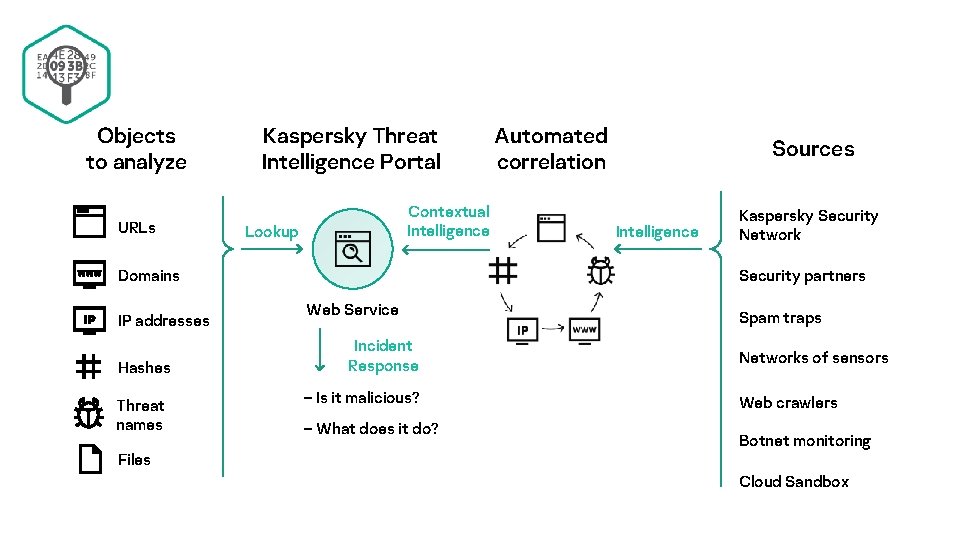
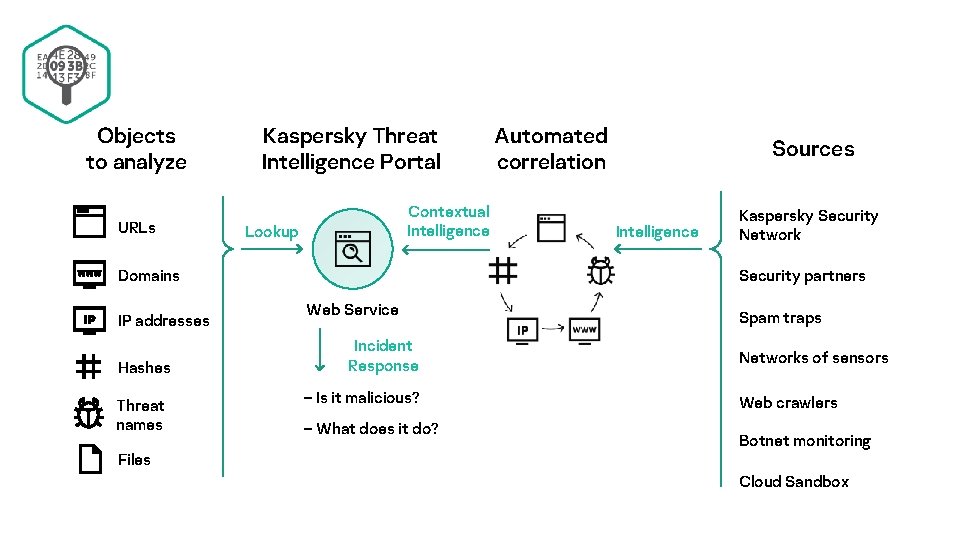
Objects to analyze URLs Kaspersky Threat Intelligence Portal Contextual Intelligence Lookup Domains IP addresses Hashes Threat names Automated correlation Sources Intelligence Kaspersky Security Network Security partners Web Service Incident Response – Is it malicious? – What does it do? Spam traps Networks of sensors Web crawlers Botnet monitoring Files Cloud Sandbox

3 • IT environments are becoming complex and distributed • IT security team is mature or a Security Operations Center is established • Risk appetite is low due to higher costs of security incidents and data breaches • Regulatory compliance is a concern READINESS FOR TARGETED AND APT-LIKE ATTACKS
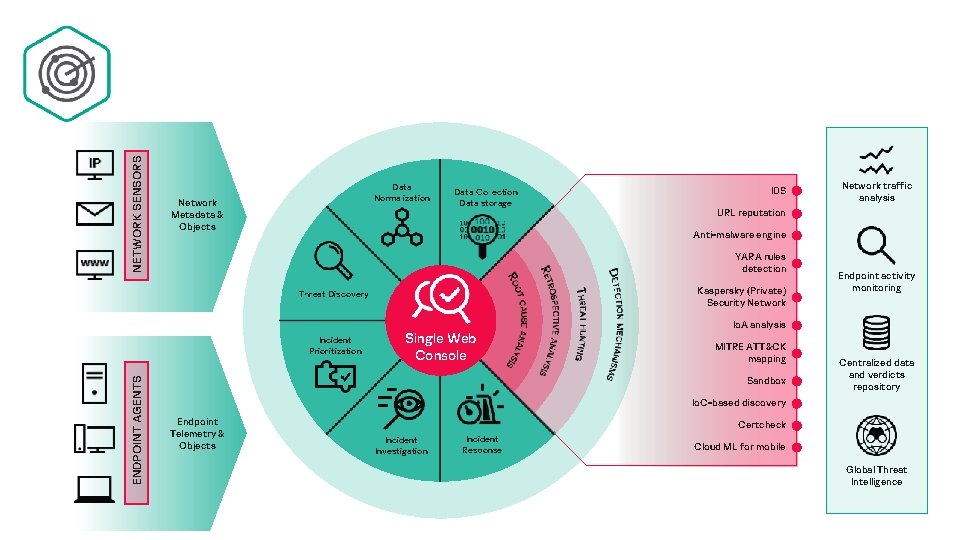
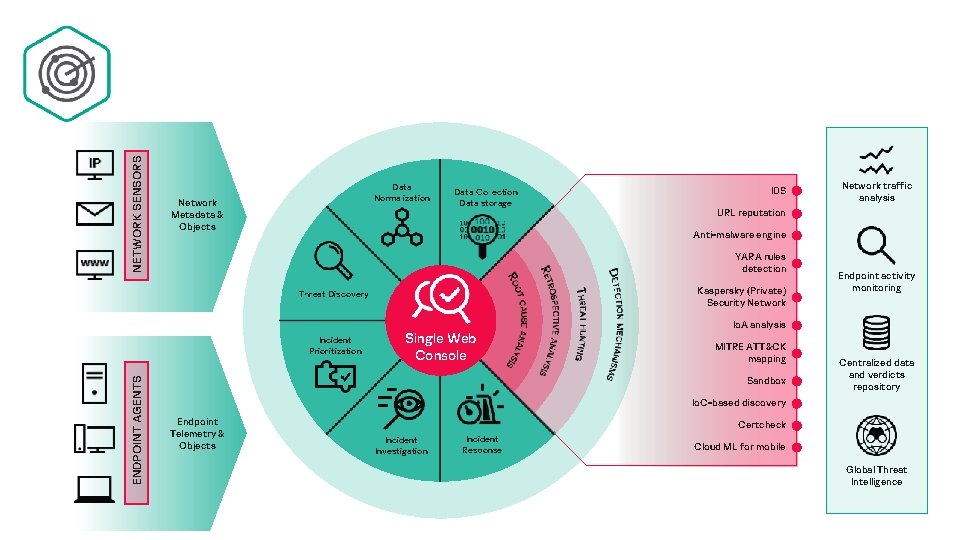
NETWORK SENSORS Data Normalization Network Metadata & Objects Data Collection Data storage Network traffic analysis URL reputation Anti-malware engine YARA rules detection Kaspersky (Private) Security Network Threat Discovery Incident Prioritization ENDPOINT AGENTS IDS Single Web Console Endpoint activity monitoring Io. A analysis MITRE ATT&CK mapping Sandbox Centralized data and verdicts repository Io. C-based discovery Endpoint Telemetry & Objects Certcheck Incident Investigation Incident Response Cloud ML for mobile Global Threat Intelligence
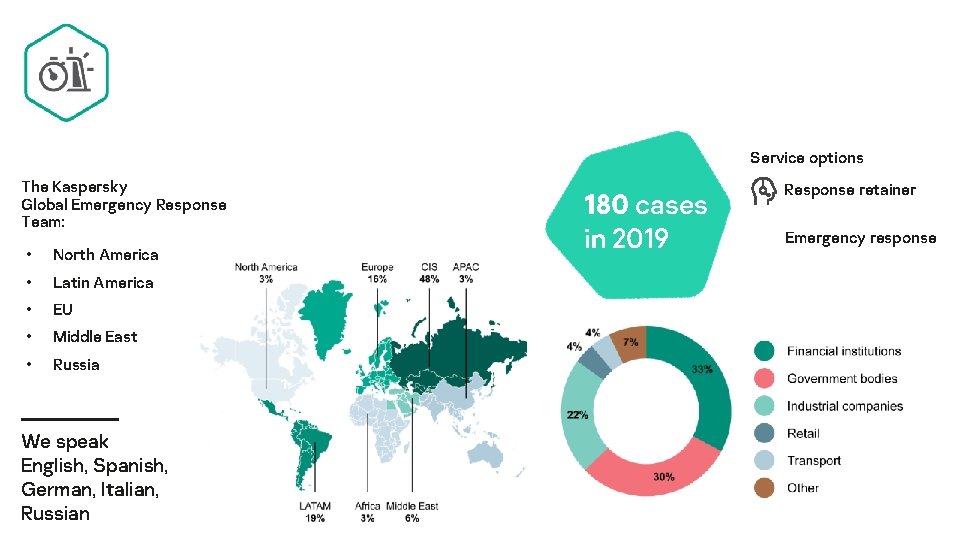
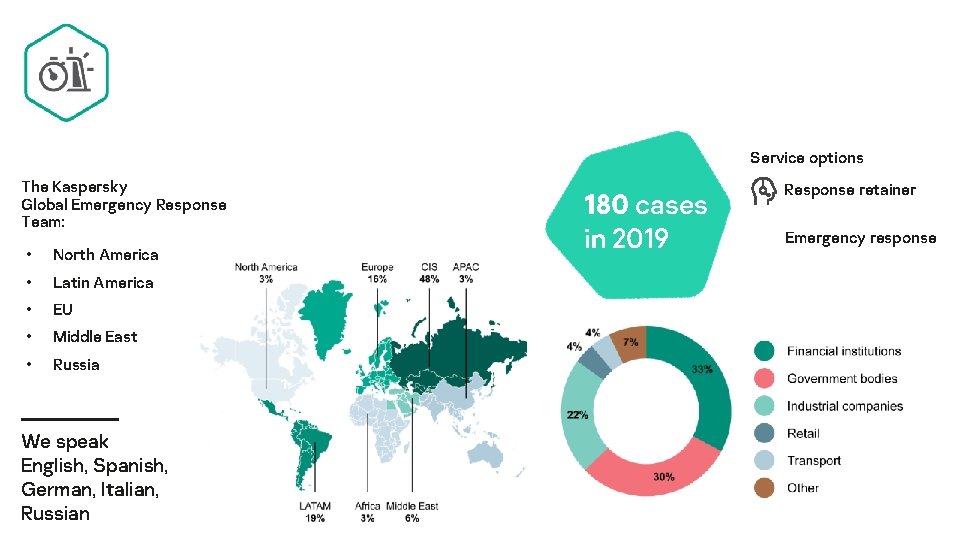
Service options The Kaspersky Global Emergency Response Team: • North America • Latin America • EU • Middle East • Russia We speak English, Spanish, German, Italian, Russian 180 cases in 2019 Response retainer Emergency response
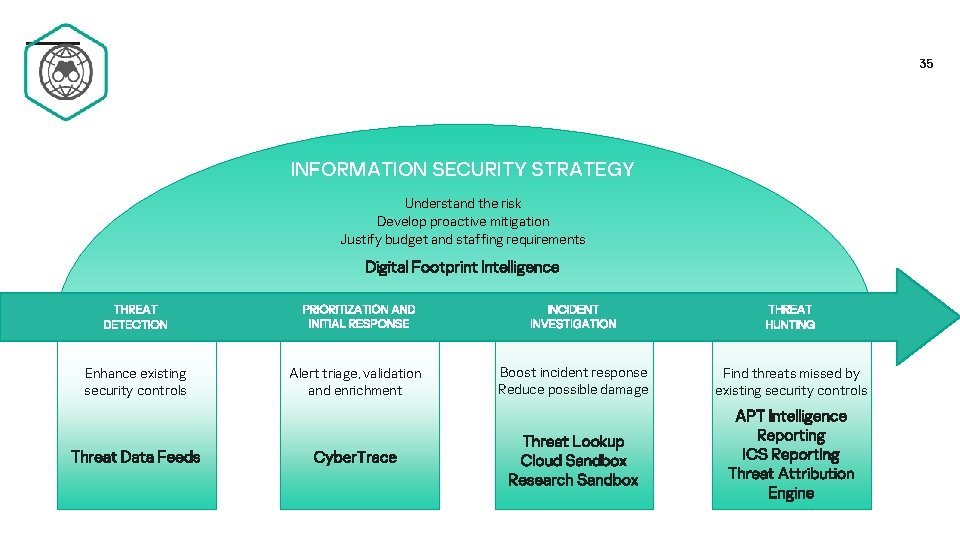
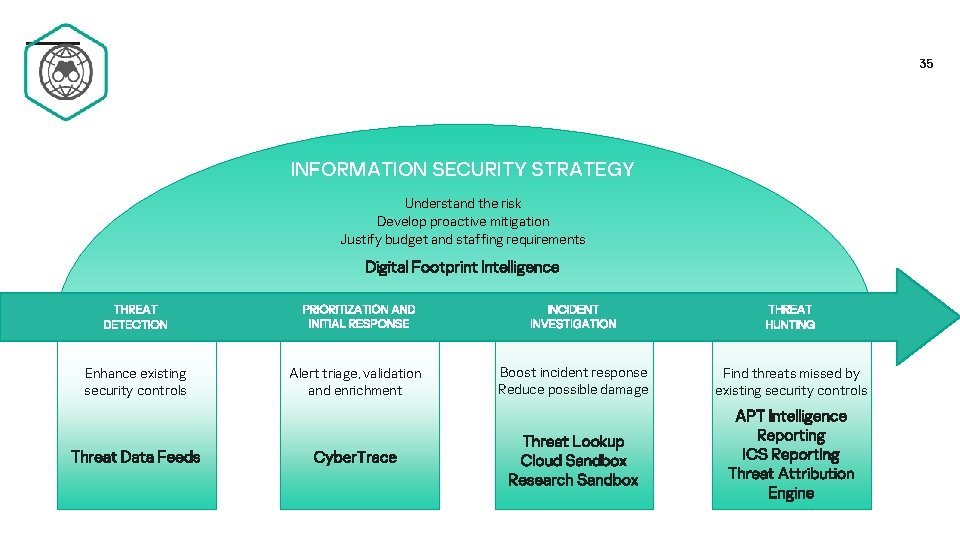
35 INFORMATION SECURITY STRATEGY Understand the risk Develop proactive mitigation Justify budget and staffing requirements Digital Footprint Intelligence THREAT DETECTION Enhance existing security controls Threat Data Feeds PRIORITIZATION AND INITIAL RESPONSE Alert triage, validation and enrichment Cyber. Trace INCIDENT INVESTIGATION THREAT HUNTING Boost incident response Reduce possible damage Find threats missed by existing security controls Threat Lookup Cloud Sandbox Research Sandbox APT Intelligence Reporting ICS Reporting Threat Attribution Engine
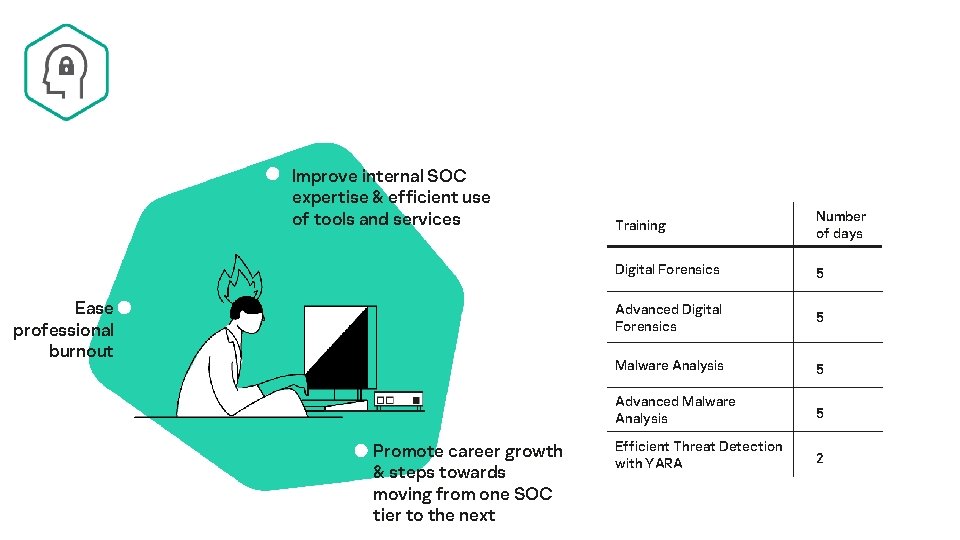
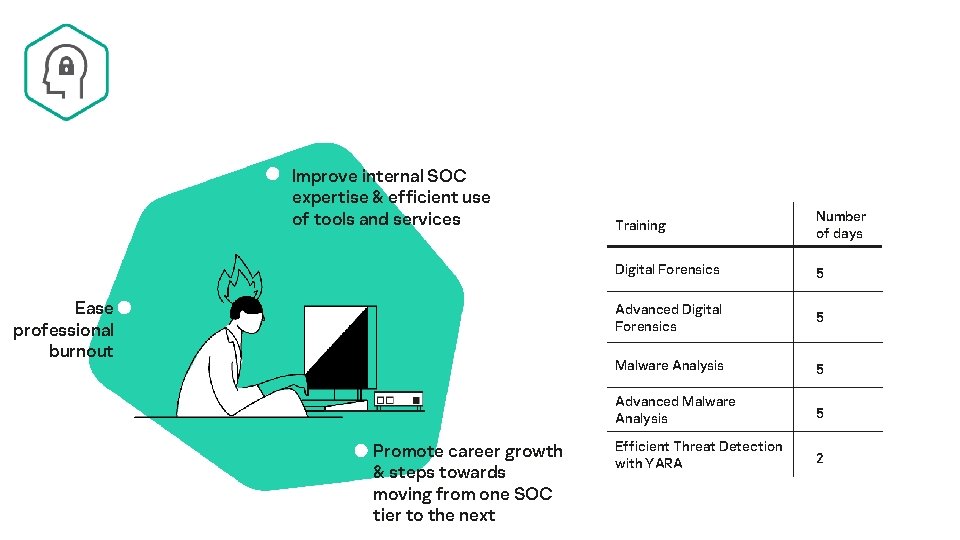
Improve internal SOC expertise & efficient use of tools and services Ease professional burnout Promote career growth & steps towards moving from one SOC tier to the next Training Number of days Digital Forensics 5 Advanced Digital Forensics 5 Malware Analysis 5 Advanced Malware Analysis 5 Efficient Threat Detection with YARA 2
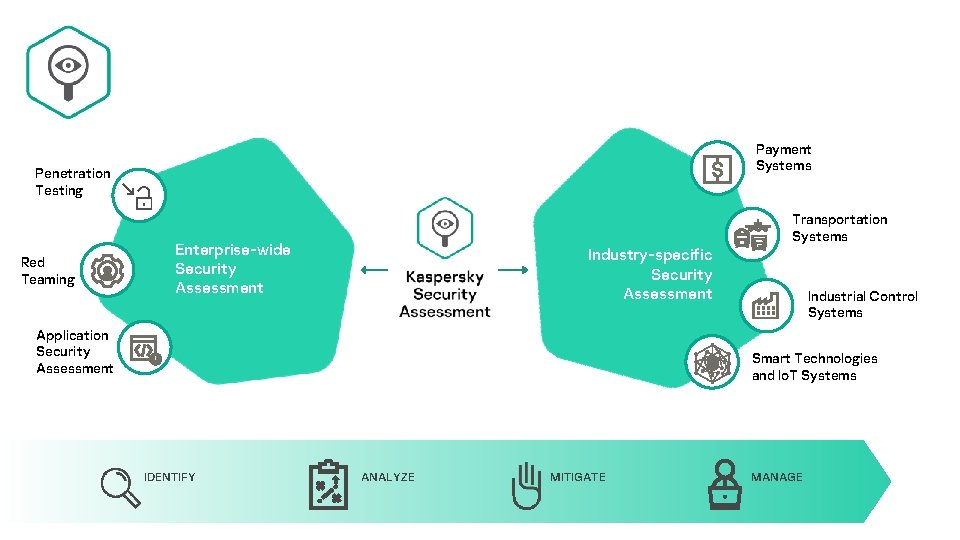
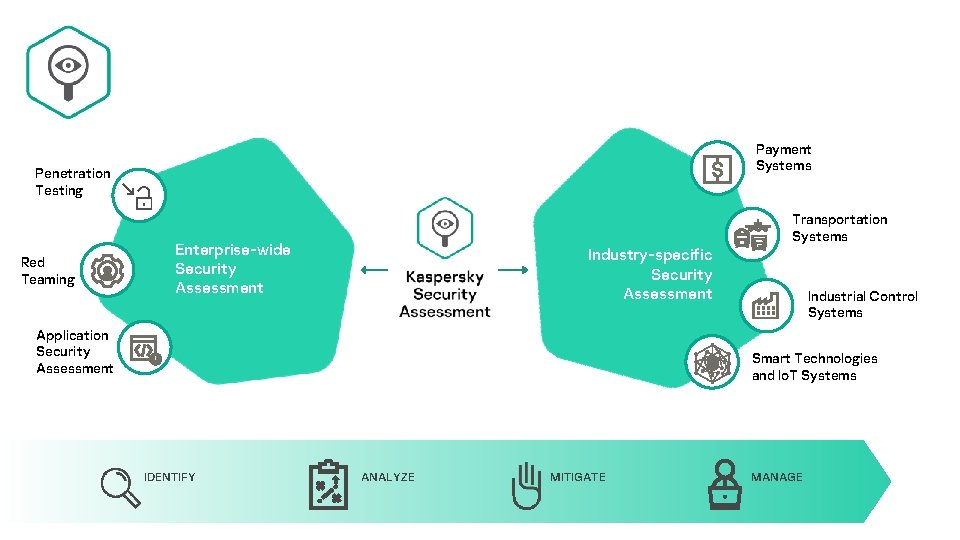
Payment Systems Penetration Testing Red Teaming Transportation Systems Enterprise-wide Security Assessment Industry-specific Security Assessment Application Security Assessment Industrial Control Systems Smart Technologies and Io. T Systems IDENTIFY ANALYZE MITIGATE MANAGE
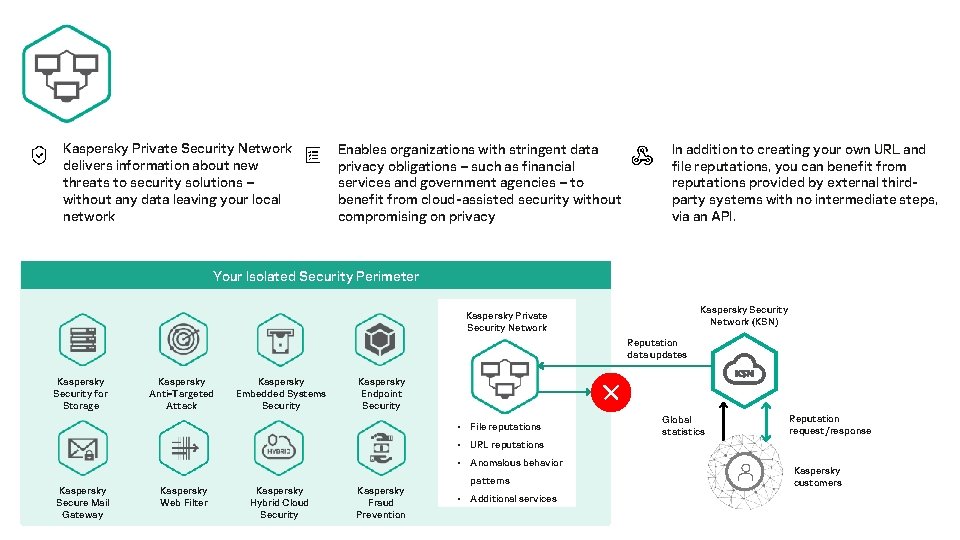
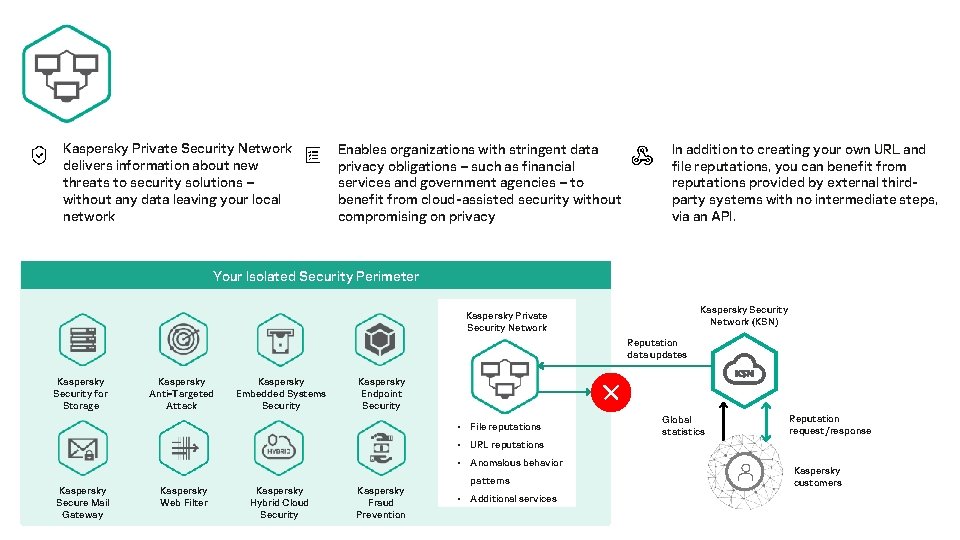
Kaspersky Private Security Network delivers information about new threats to security solutions – without any data leaving your local network Enables organizations with stringent data privacy obligations – such as financial services and government agencies – to benefit from cloud-assisted security without compromising on privacy In addition to creating your own URL and file reputations, you can benefit from reputations provided by external thirdparty systems with no intermediate steps, via an API. Your Isolated Security Perimeter Kaspersky Security Network (KSN) Kaspersky Private Security Network Reputation data updates Kaspersky Security for Storage Kaspersky Anti-Targeted Attack Kaspersky Embedded Systems Security Kaspersky Endpoint Security • File reputations Global statistics Reputation request/response • URL reputations • Anomalous behavior Kaspersky Secure Mail Gateway Kaspersky Web Filter Kaspersky Hybrid Cloud Security Kaspersky Fraud Prevention patterns • Additional services Kaspersky customers
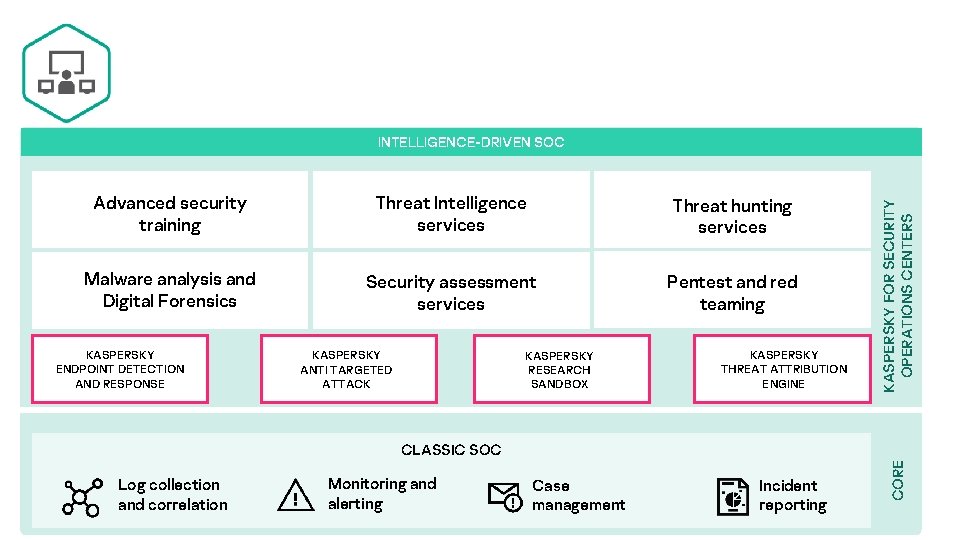
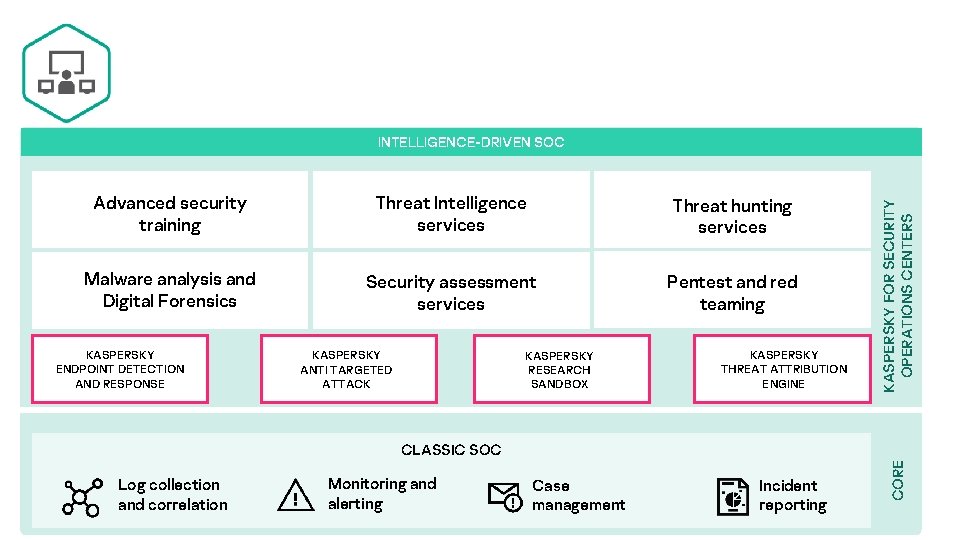
Advanced security training Threat Intelligence services Threat hunting services Malware analysis and Digital Forensics Security assessment services Pentest and red teaming KASPERSKY ENDPOINT DETECTION AND RESPONSE KASPERSKY ANTI TARGETED ATTACK KASPERSKY RESEARCH SANDBOX KASPERSKY THREAT ATTRIBUTION ENGINE KASPERSKY FOR SECURITY OPERATIONS CENTERS INTELLIGENCE-DRIVEN SOC Log collection and correlation Monitoring and alerting Case management Incident reporting CORE CLASSIC SOC
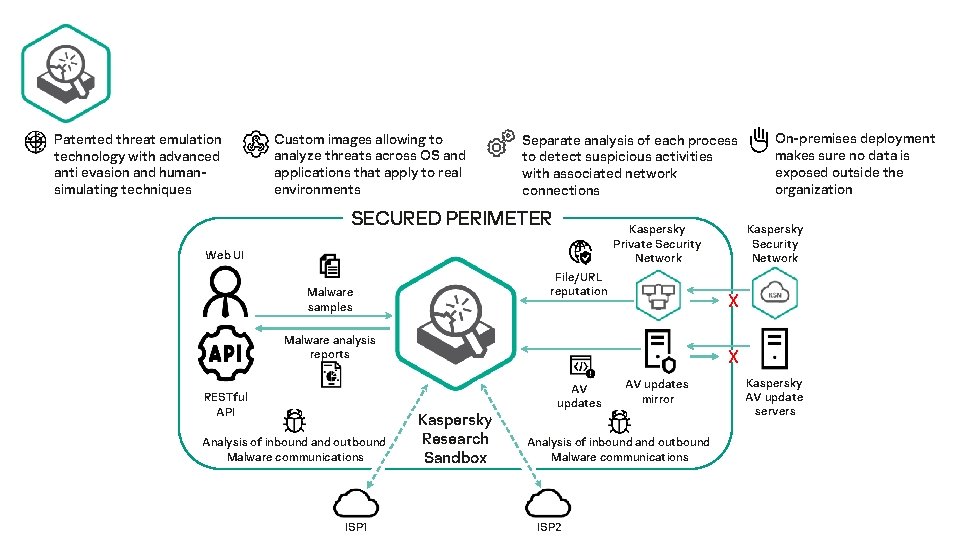
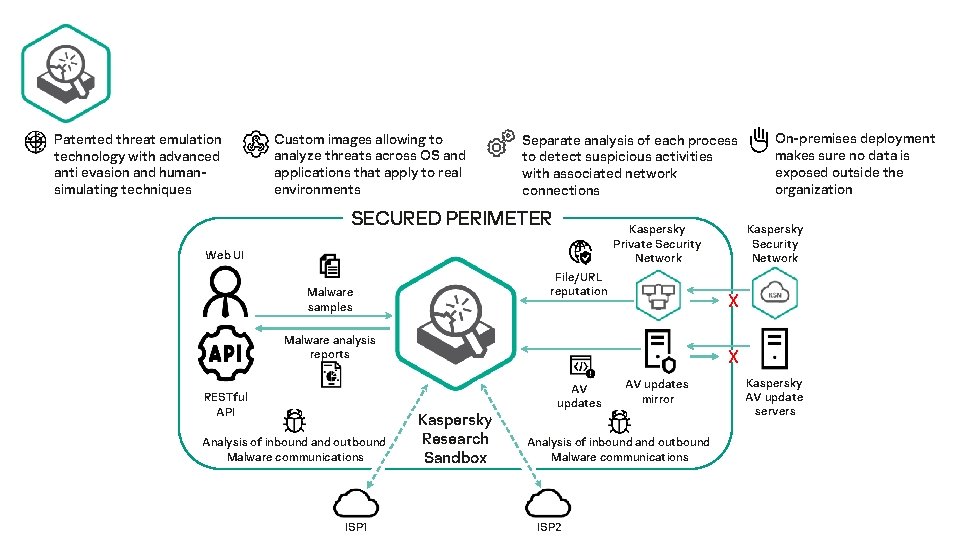
Patented threat emulation technology with advanced anti evasion and humansimulating techniques Custom images allowing to analyze threats across OS and applications that apply to real environments Separate analysis of each process to detect suspicious activities with associated network connections SECURED PERIMETER Kaspersky Private Security Network Web UI File/URL reputation Malware samples Analysis of inbound and outbound Malware communications ISP 1 Kaspersky Security Network X Malware analysis reports RESTful API On-premises deployment makes sure no data is exposed outside the organization X Kaspersky Research Sandbox AV updates mirror Analysis of inbound and outbound Malware communications ISP 2 Kaspersky AV update servers
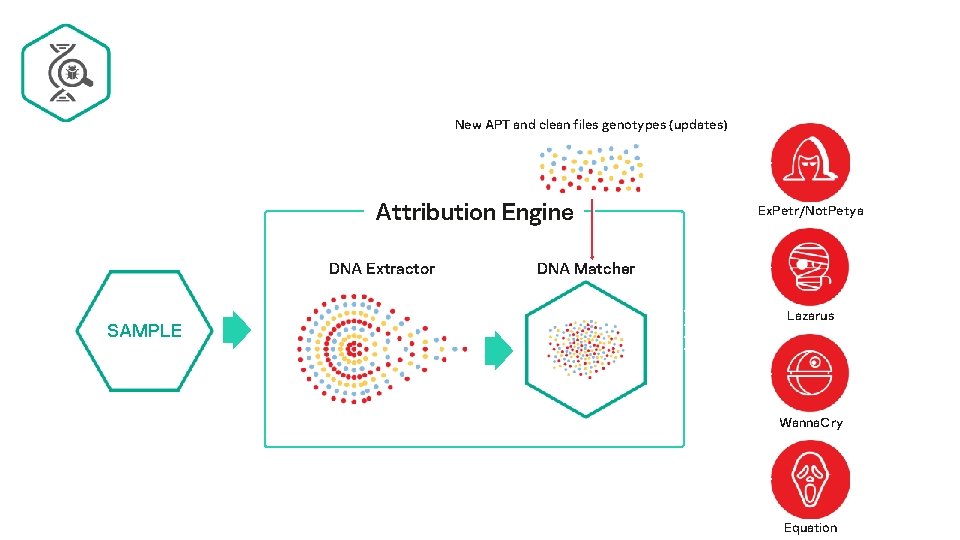
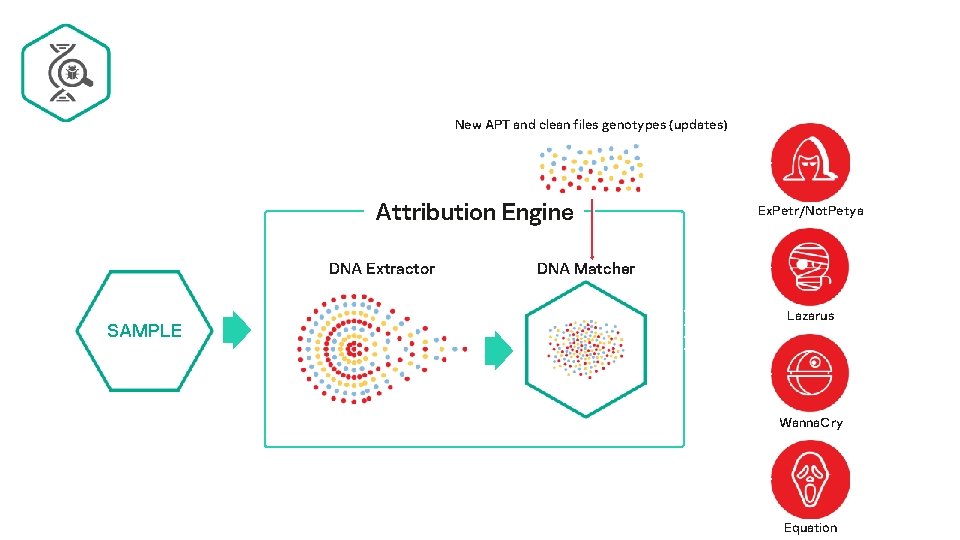
New APT and clean files genotypes (updates) Attribution Engine DNA Extractor SAMPLE Ex. Petr/Not. Petya DNA Matcher Lazarus Wanna. Cry Equation
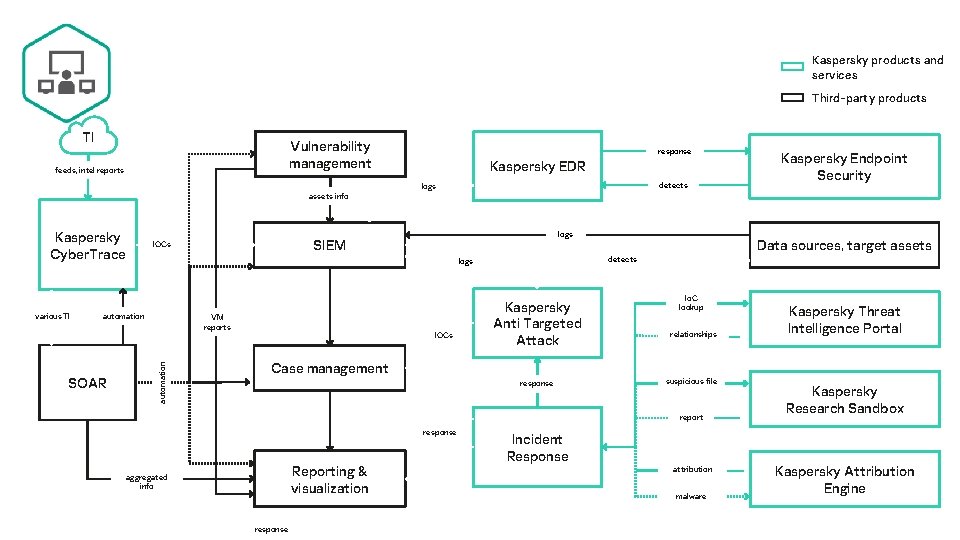
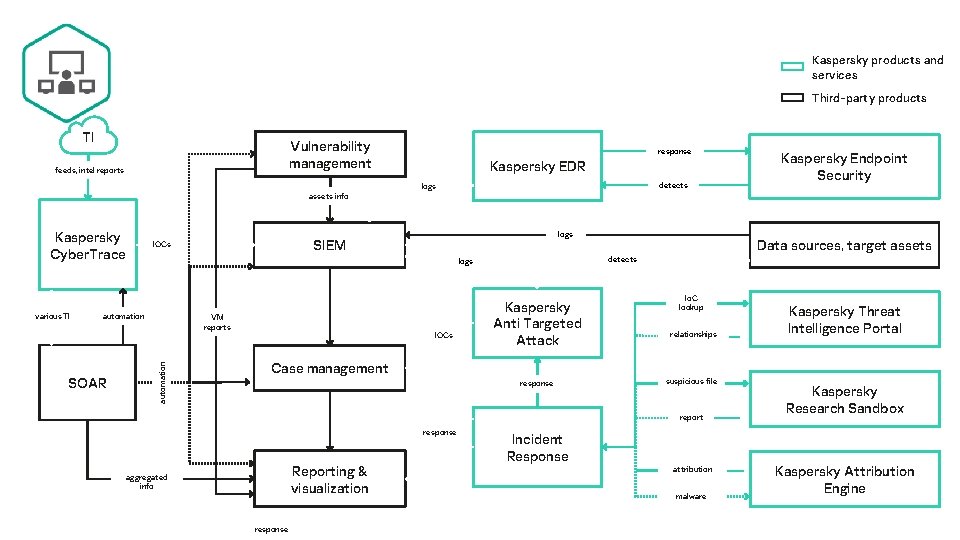
Kaspersky products and services Third-party products TI Vulnerability management feeds, intel reports response Kaspersky EDR detects logs Kaspersky Endpoint Security assets info Kaspersky Cyber. Trace automation SOAR VM reports IOCs Data sources, target assets detects logs automation various TI logs SIEM IOCs Kaspersky Anti Targeted Attack Case management response Io. C lookup relationships suspicious file report response Reporting & visualization aggregated info response Incident Response attribution malware Kaspersky Threat Intelligence Portal Kaspersky Research Sandbox Kaspersky Attribution Engine
The GARTNER PEER INSIGHTS CUSTOMERS’ CHOICE badge is a trademark and service mark of Gartner, Inc. , and/or its affiliates, and is used herein with permission. All rights reserved. Gartner Peer Insights Customers’ Choice constitute the subjective opinions of individual end-user reviews, ratings, and data applied against a documented methodology; they neither represent the views of, nor constitute an endorsement by, Gartner or its affiliates. Kaspersky has once again been named a Gartner Peer Insights Customers’ Choice for Endpoint Protection Platforms. Kaspersky is a Customers’ Choice in the April 2020 ‘Gartner Peer Insights ‘Voice of the Customer’: EDR Solutions’ report. Most Tested. Most Awarded Kaspersky has achieved more first places in independent tests than any other security vendor. And we do this year after year. www. kaspersky. com/top 3 Kaspersky quality confirmed by MITRE ATT&CK evaluation Most transparent With our first Transparency Center now active, and statistical processing based in Switzerland, the sovereignty of your data is guaranteed in ways no other vendor can match.
A siloed approach to cybersecurity puts businesses at risk Awareness, communication and cooperation are key to success in a world of rapidly changing cyberthreats Cybersecurity is not a destination – it’s an ongoing journey A proactive ‘detection and response’ mindset is the best way to counter today’s ever-evolving threats

Thank you! kaspersky. com
