July 2015 July 2015 July 2015 July 2015
- Slides: 33
July 2015…. .
July 2015…. .
July 2015…. .
July 2015…. .
July 2015…. .
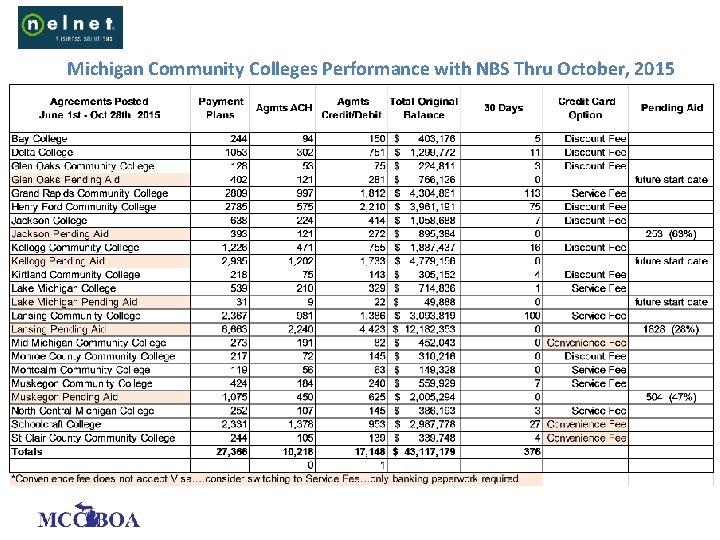
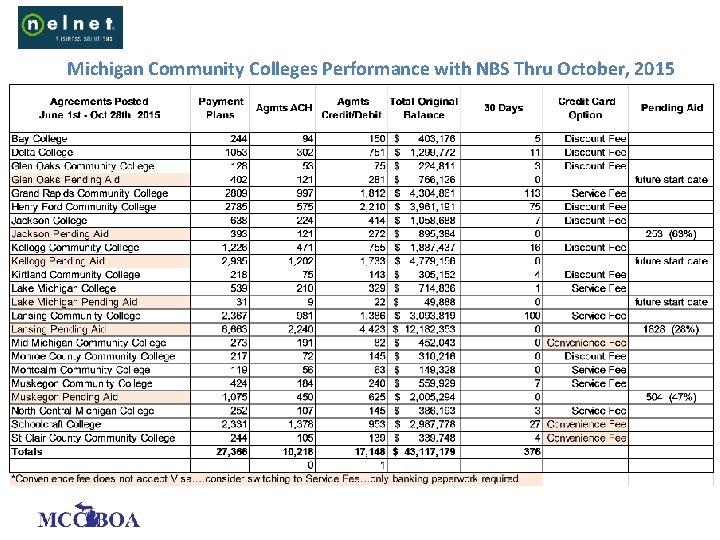
Michigan Community Colleges Performance with NBS Thru October, 2015
Protecting PII Compliance Management
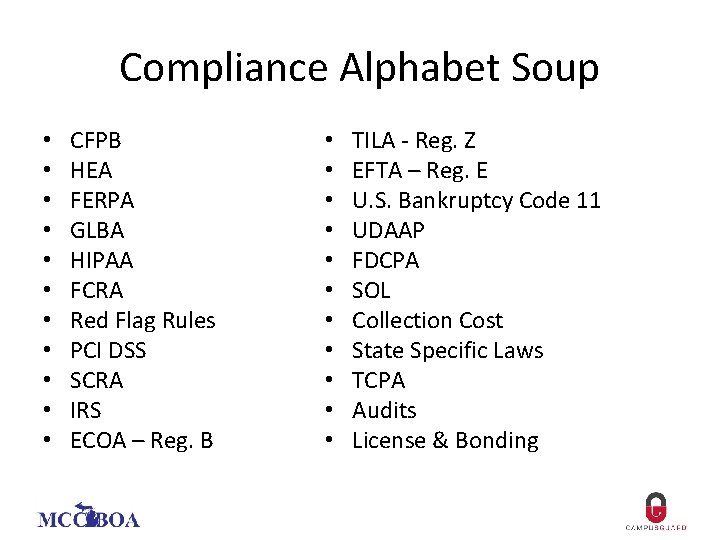
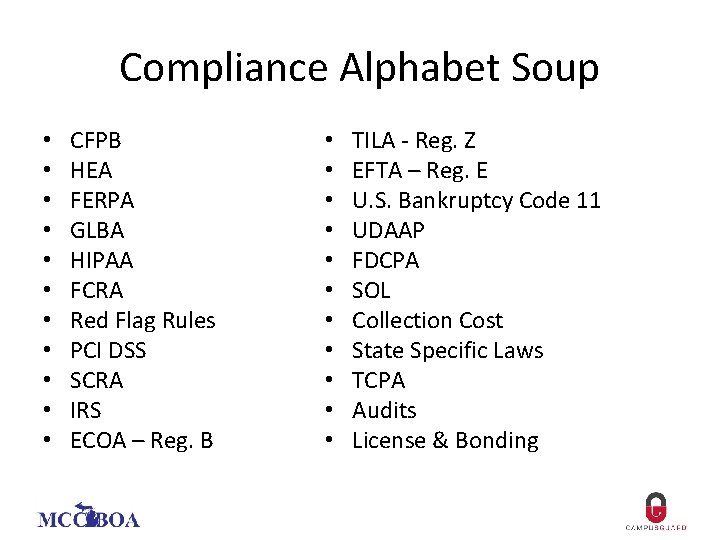
Compliance Alphabet Soup • • • CFPB HEA FERPA GLBA HIPAA FCRA Red Flag Rules PCI DSS SCRA IRS ECOA – Reg. B • • • TILA - Reg. Z EFTA – Reg. E U. S. Bankruptcy Code 11 UDAAP FDCPA SOL Collection Cost State Specific Laws TCPA Audits License & Bonding
PCI DSS: What Every Business Officer Needs to Know
5 Stages of PCI Grief q Denial: It doesn’t apply to me q Anger: It isn’t fair q Bargaining: I’ll do some of it q Depression: I’ll never get there q Acceptance: It will be OK
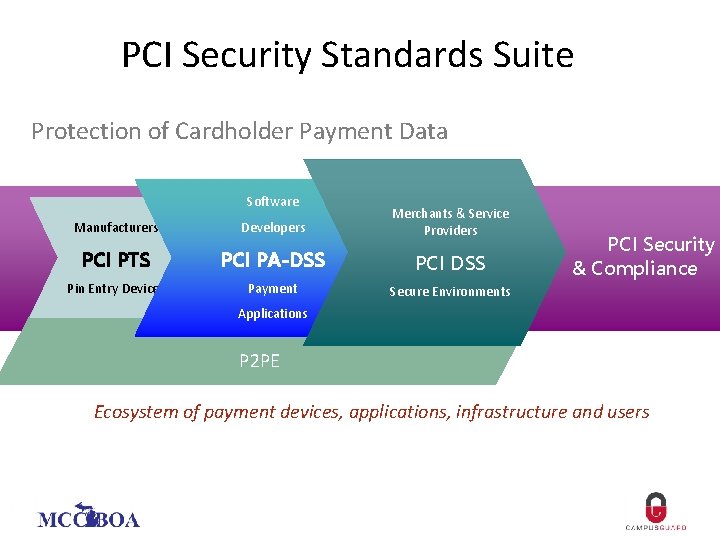
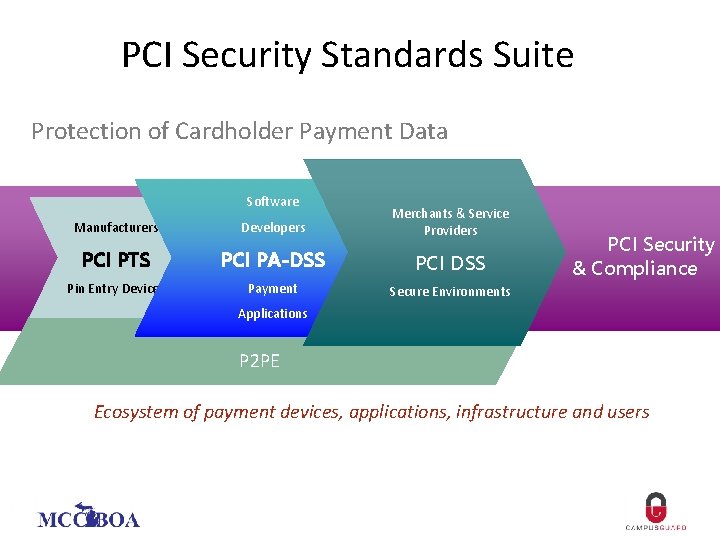
PCI Security Standards Suite Protection of Cardholder Payment Data Software Manufacturers Developers Merchants & Service Providers PCI PTS PCI PA-DSS PCI DSS Pin Entry Devices Payment Secure Environments PCI Security & Compliance Applications P 2 PE Ecosystem of payment devices, applications, infrastructure and users
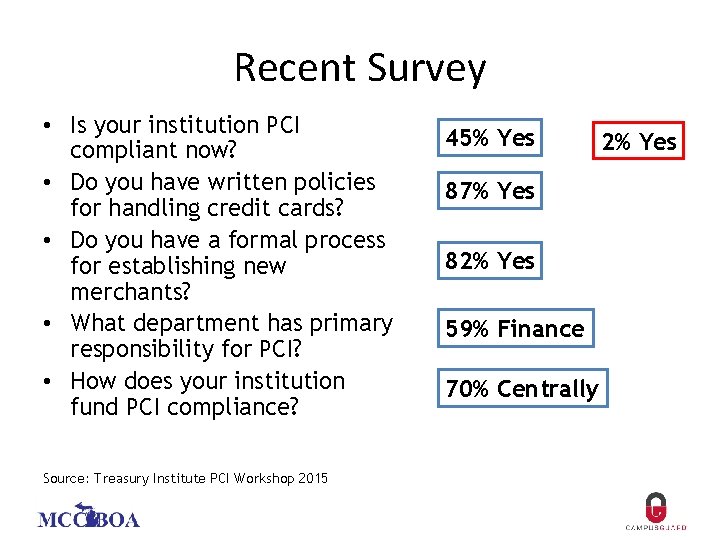
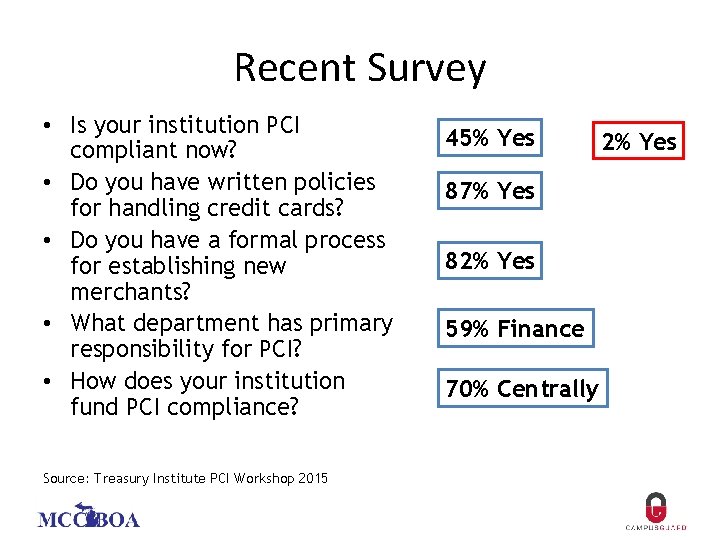
Recent Survey • Is your institution PCI compliant now? • Do you have written policies for handling credit cards? • Do you have a formal process for establishing new merchants? • What department has primary responsibility for PCI? • How does your institution fund PCI compliance? Source: Treasury Institute PCI Workshop 2015 45% Yes 87% Yes 82% Yes 59% Finance 70% Centrally 2% Yes
Why is PCI Compliance So Difficult?
Colleges Campuses Are Like Cities…
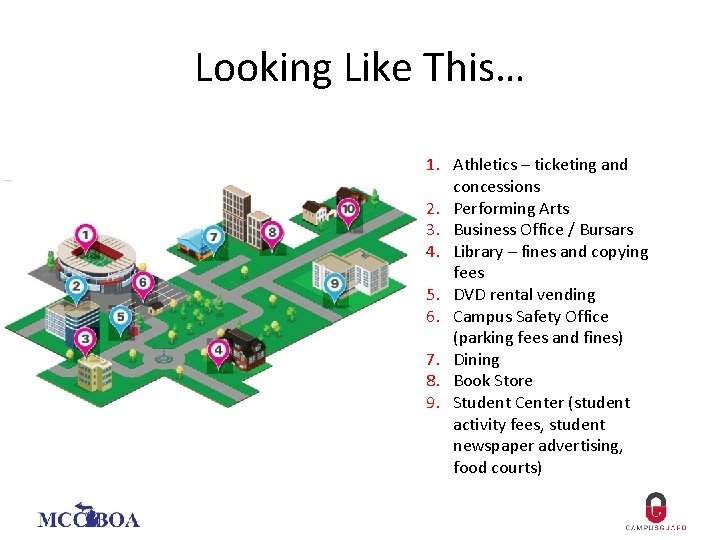
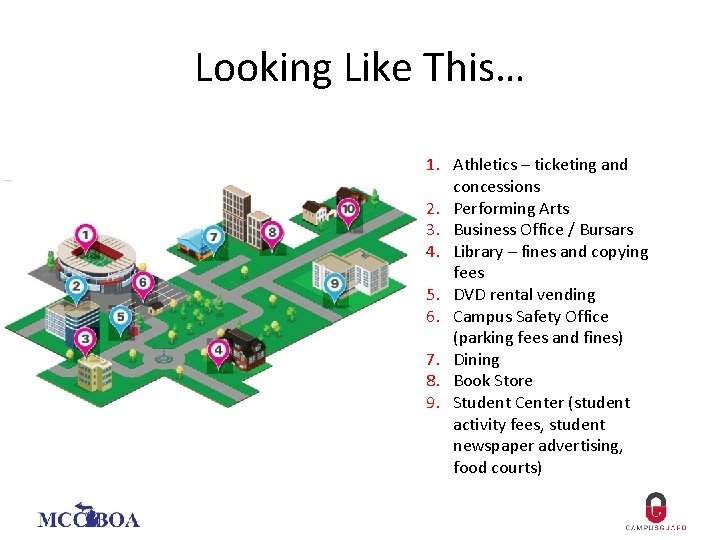
Looking Like This… 1. Athletics – ticketing and concessions 2. Performing Arts 3. Business Office / Bursars 4. Library – fines and copying fees 5. DVD rental vending 6. Campus Safety Office (parking fees and fines) 7. Dining 8. Book Store 9. Student Center (student activity fees, student newspaper advertising, food courts)
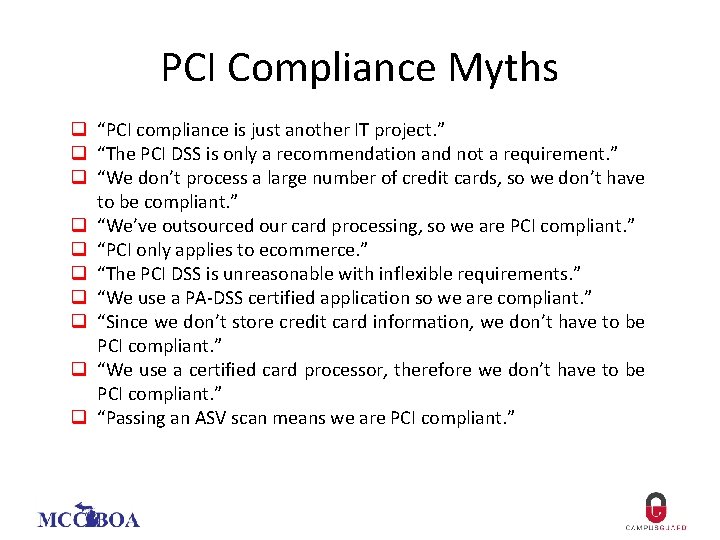
PCI Compliance Myths q “PCI compliance is just another IT project. ” q “The PCI DSS is only a recommendation and not a requirement. ” q “We don’t process a large number of credit cards, so we don’t have to be compliant. ” q “We’ve outsourced our card processing, so we are PCI compliant. ” q “PCI only applies to ecommerce. ” q “The PCI DSS is unreasonable with inflexible requirements. ” q “We use a PA-DSS certified application so we are compliant. ” q “Since we don’t store credit card information, we don’t have to be PCI compliant. ” q “We use a certified card processor, therefore we don’t have to be PCI compliant. ” q “Passing an ASV scan means we are PCI compliant. ”
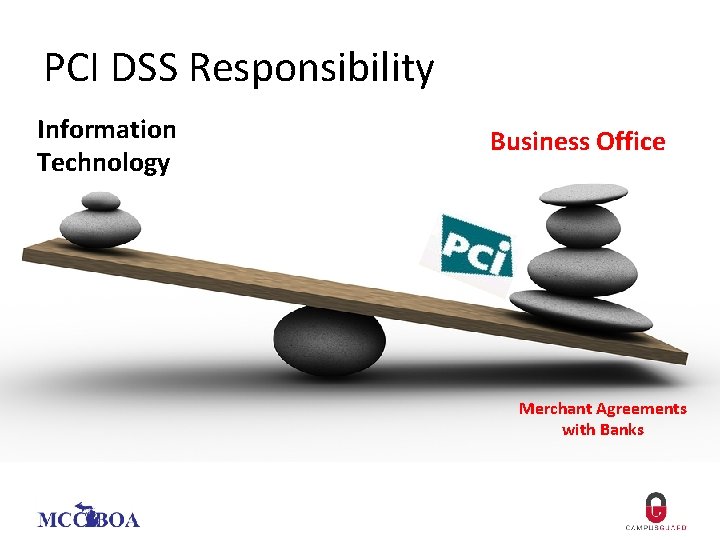
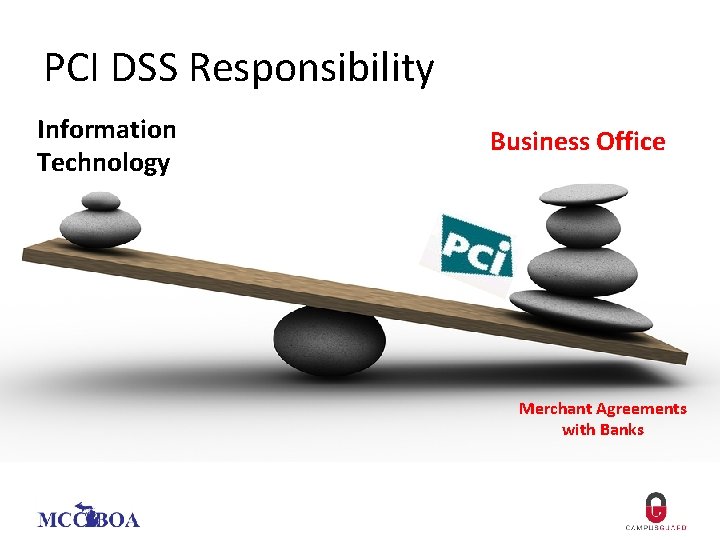
PCI DSS Responsibility Information Technology Business Office Merchant Agreements with Banks
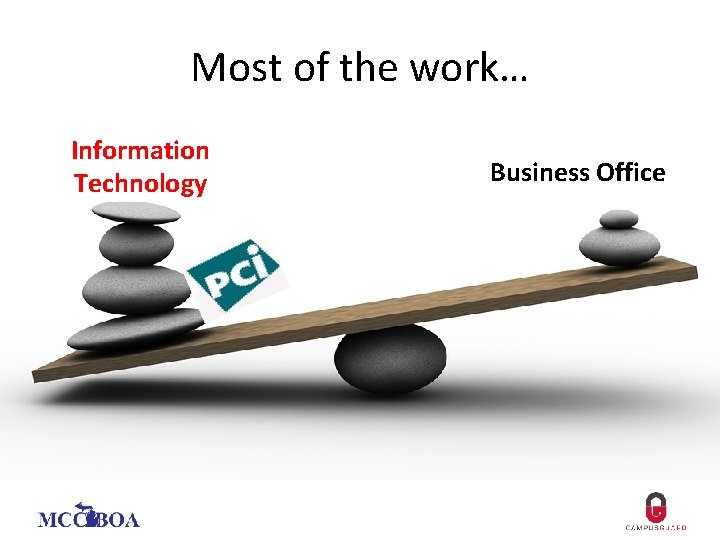
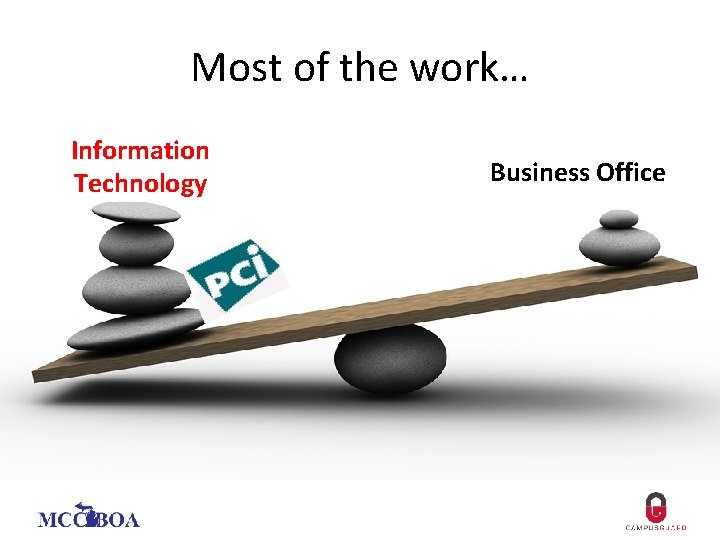
Most of the work… Information Technology Business Office
Preparation for Assessment q Is your campus compliant today? q Who owns “overall responsibility” for the PCI compliance program? q How is ongoing oversight accomplished? q Who has ownership of high level policies and procedures? q How is required training accomplished? q Who controls the technical functionality of your credit card environment? q Who are your third-party service providers?
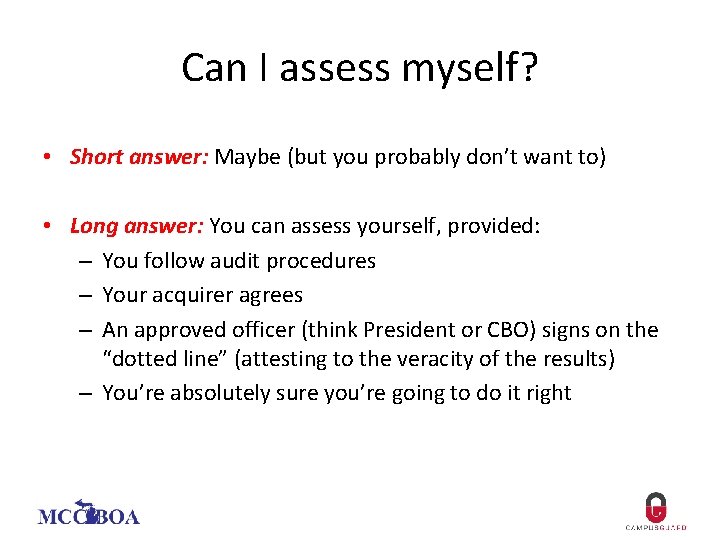
Can I assess myself? • Short answer: Maybe (but you probably don’t want to) • Long answer: You can assess yourself, provided: – You follow audit procedures – Your acquirer agrees – An approved officer (think President or CBO) signs on the “dotted line” (attesting to the veracity of the results) – You’re absolutely sure you’re going to do it right
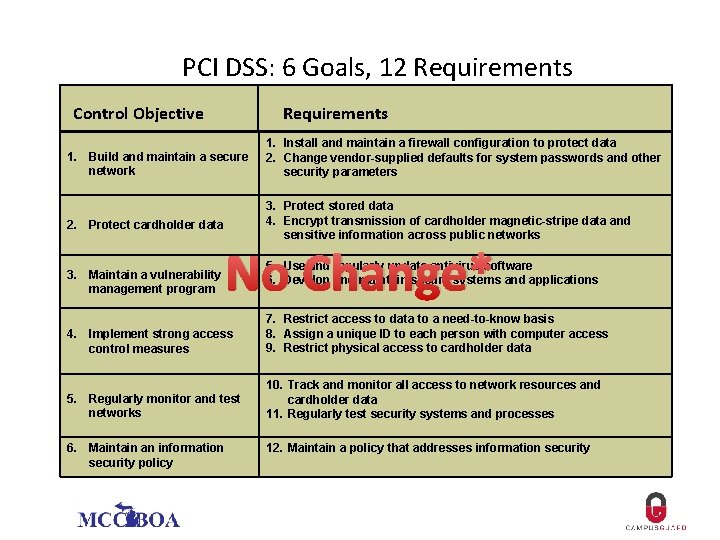
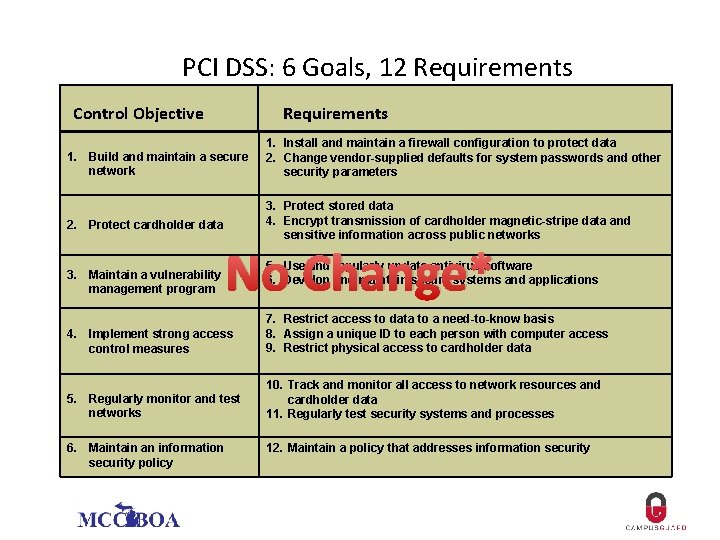
PCI DSS: 6 Goals, 12 Requirements Control Objective Requirements 1. Build and maintain a secure network 2. Protect cardholder data 3. Maintain a vulnerability management program 1. Install and maintain a firewall configuration to protect data 2. Change vendor-supplied defaults for system passwords and other security parameters 3. Protect stored data 4. Encrypt transmission of cardholder magnetic-stripe data and sensitive information across public networks No Change* 5. Use and regularly update antivirus software 6. Develop and maintain secure systems and applications 4. Implement strong access control measures 7. Restrict access to data to a need-to-know basis 8. Assign a unique ID to each person with computer access 9. Restrict physical access to cardholder data 5. Regularly monitor and test networks 10. Track and monitor all access to network resources and cardholder data 11. Regularly test security systems and processes 6. Maintain an information security policy 12. Maintain a policy that addresses information security
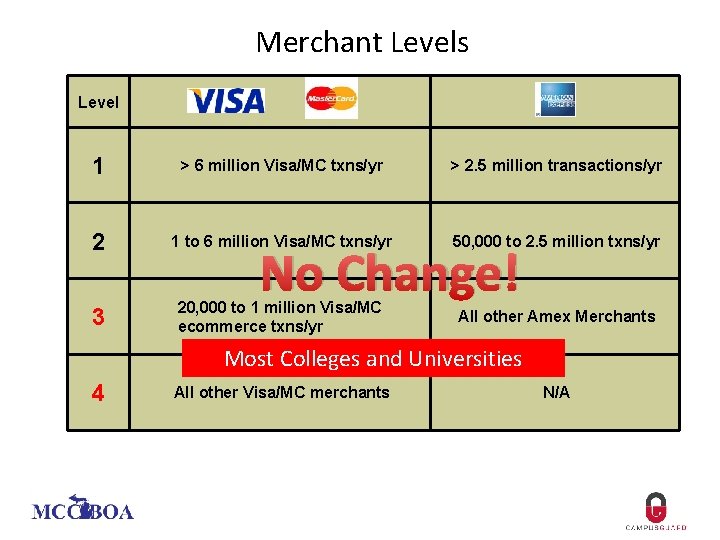
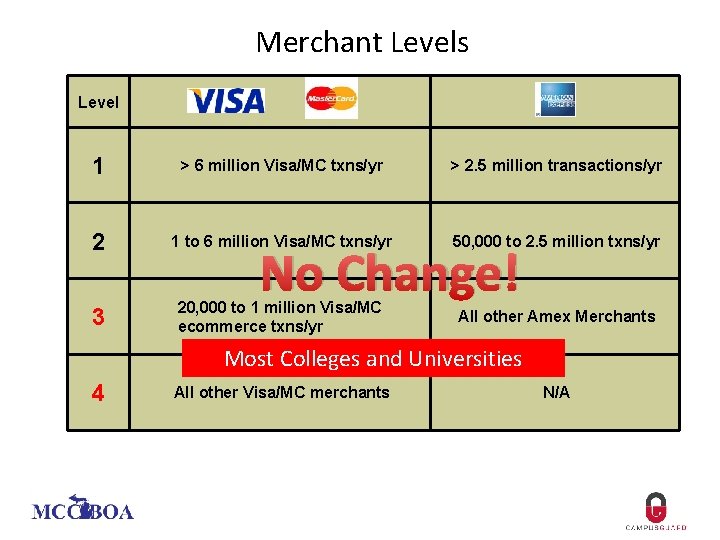
Merchant Levels Level 1 > 6 million Visa/MC txns/yr > 2. 5 million transactions/yr 2 1 to 6 million Visa/MC txns/yr 50, 000 to 2. 5 million txns/yr 3 20, 000 to 1 million Visa/MC ecommerce txns/yr All other Amex Merchants No Change! Most Colleges and Universities 4 All other Visa/MC merchants N/A
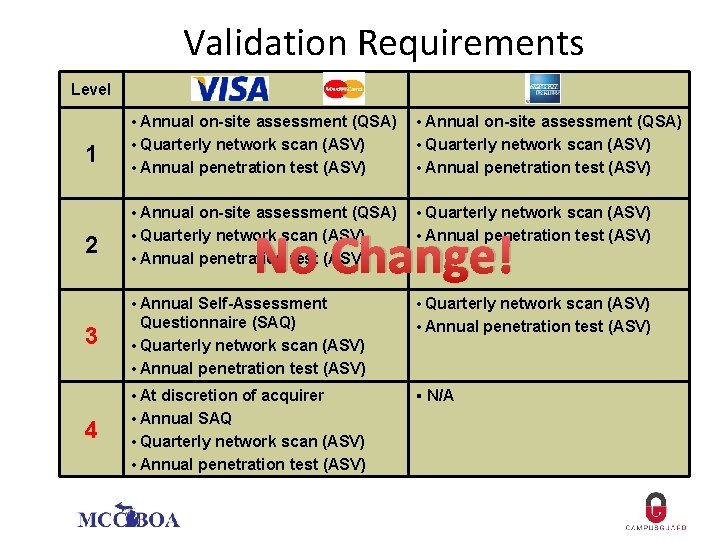
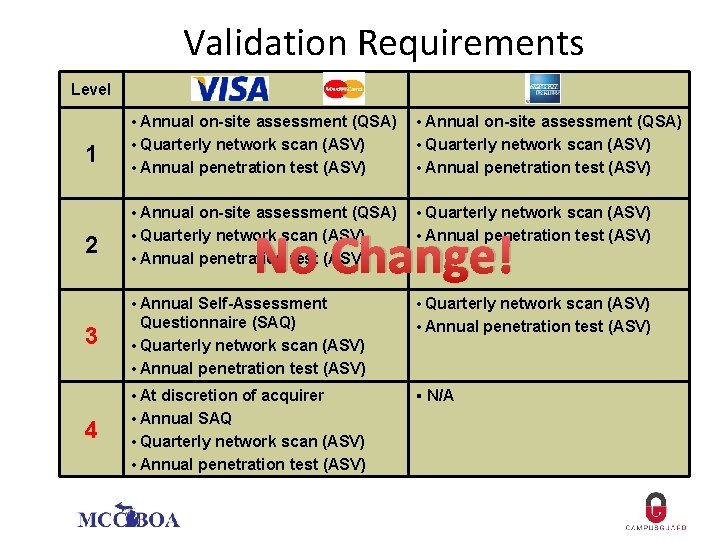
Validation Requirements Level 1 2 3 4 • Annual on-site assessment (QSA) • Quarterly network scan (ASV) • Annual penetration test (ASV) No Change! • Annual penetration test (ASV) • Annual Self-Assessment • Quarterly network scan (ASV) Questionnaire (SAQ) • Quarterly network scan (ASV) • Annual penetration test (ASV) • At discretion of acquirer § N/A • Annual SAQ • Quarterly network scan (ASV) • Annual penetration test (ASV)
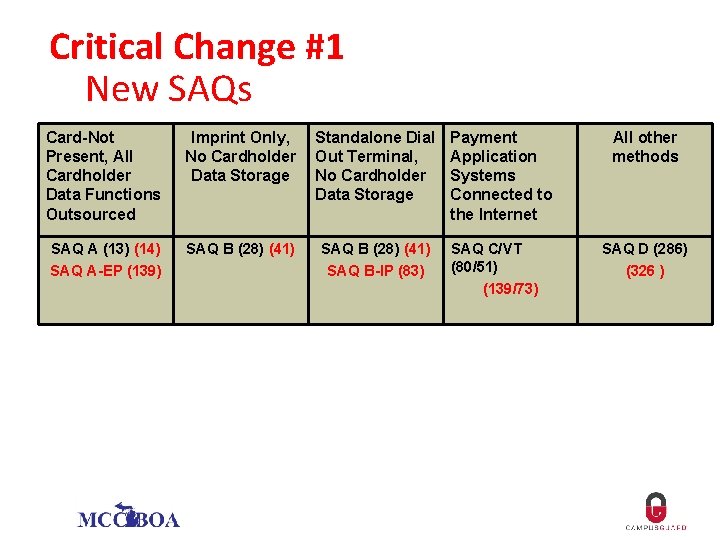
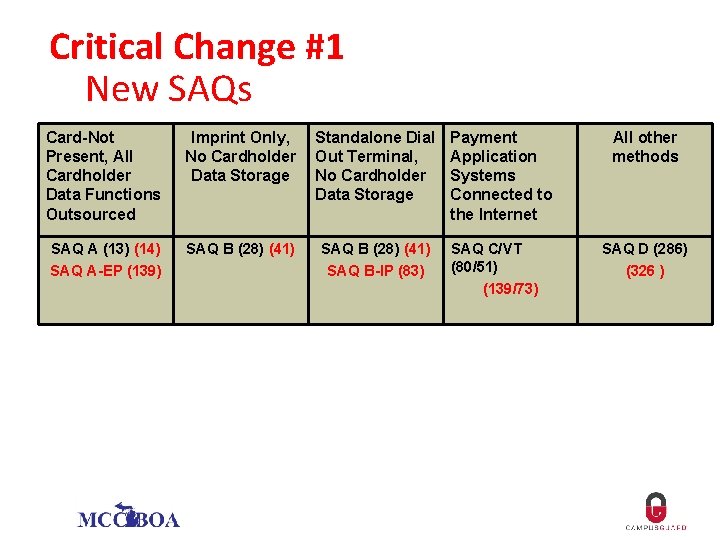
Critical Change #1 New SAQs Card-Not Present, All Cardholder Data Functions Outsourced Imprint Only, No Cardholder Data Storage Standalone Dial Out Terminal, No Cardholder Data Storage SAQ A (13) (14) SAQ A-EP (139) SAQ B (28) (41) SAQ B-IP (83) Payment Application Systems Connected to the Internet SAQ C/VT (80/51) (139/73) All other methods SAQ D (286) (326 )
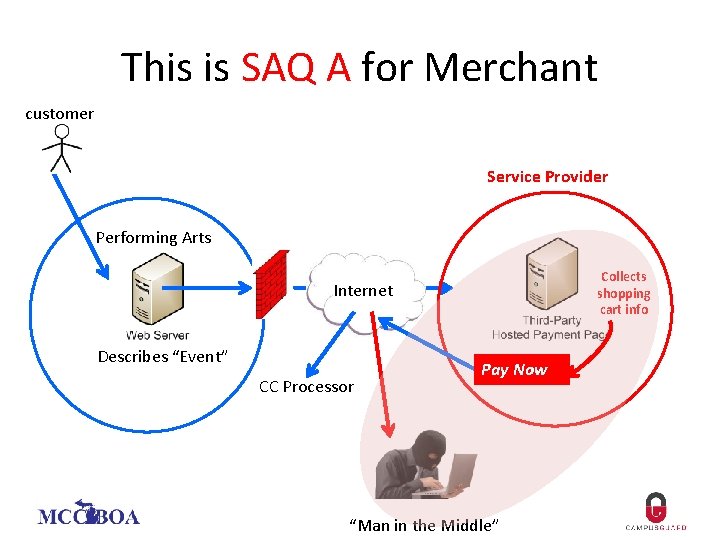
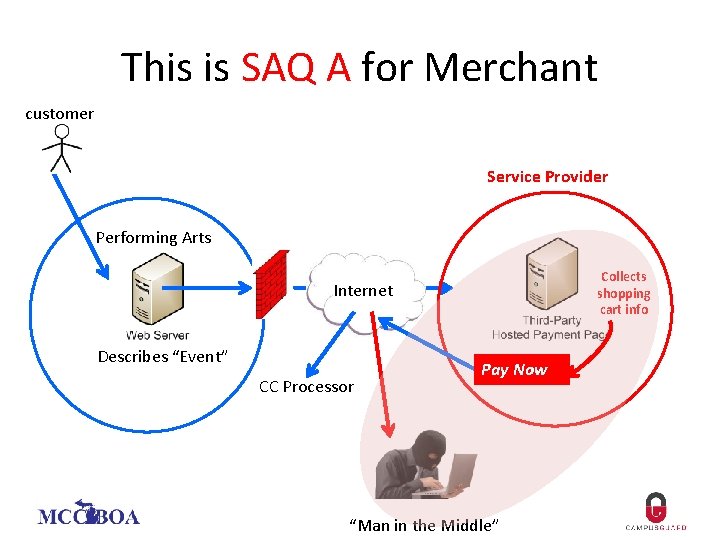
This is SAQ A for Merchant customer Service Provider Performing Arts Collects shopping cart info Internet Describes “Event” CC Processor Pay Now “Man in the Middle”
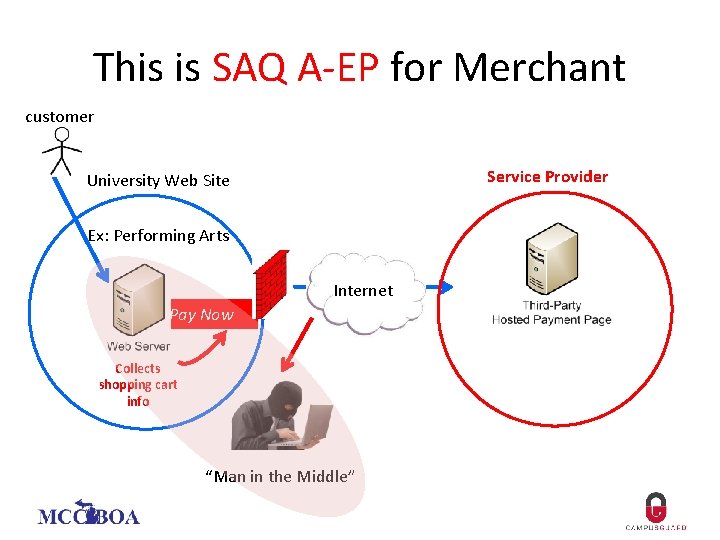
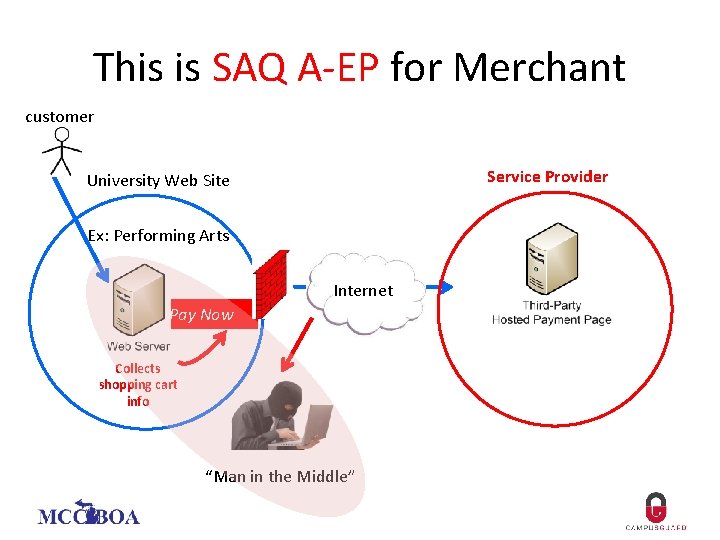
This is SAQ A-EP for Merchant customer Service Provider University Web Site Ex: Performing Arts Internet Pay Now Collects shopping cart info “Man in the Middle”
Critical Change #2 Shared Responsibilities
“Shared Responsibility” Requirement 12: Maintain an Information Security Policy For Your College: 12. 8 Managing relationships with service providers 12. 8. 2 Written agreements with service providers 12. 8. 3 Established process for engaging service providers 12. 8. 4 Monitor service provider compliance 12. 8. 5 (NEW) Is information maintained about which PCI DSS requirements are maintained by each service provider and which are maintained by the entity? For Service Providers 12. 9 (NEW) Do service providers acknowledge in writing to customers that they are responsible for the security of cardholder data the service provider possesses or otherwise stores, processes on behalf of the customer, or to the extent that they could impact the security of the customer’s cardholder data environment?
Example Contract Language PCI DSS COMPLIANCE: (College) requires that the contractor shall at all times maintain compliance with the most current Payment Card Industry Data Security Standards (PCI DSS). The contractor will be required to provide written confirmation of compliance. Contractor acknowledges responsibility for the security of cardholder data as defined within the PCI DSS. Contractor acknowledges and agrees that cardholder data may only be used for completing the contracted services as described in the full text of this document, or as required by the PCI DSS, or as required by applicable law. In the event of a breach or intrusion or otherwise unauthorized access to cardholder data stored at or for the contractor, contractor shall immediately notify (College) to allow the proper PCI DSS compliant breach notification process to commence. The contractor shall provide appropriate payment card companies, acquiring financial institutions and their respective designees access to the contractor’s facilities and all pertinent records to conduct a review of the contractor’s compliance with the PCI DSS requirements. In the event of a breach or intrusion the contractor acknowledges any/all costs related to breach or intrusion or unauthorized access to cardholder data entrusted to the contractor deemed to be the fault of the contractor shall be the liability of the contractor. Vendor agrees to assume responsibility for informing all such individuals in accordance with applicable law and to indemnify and hold harmless (College) and its officers and employees from and against any claims, damages or other harm related to such breach. (USE: Include in any solicitation / contract that may involve online credit card payments). IMPORTANT: Insert the following statement into the Scope of Work (potentially in the IT section dealing with credit cards and PCI compliance): “Provide documentation of your most current PCI system scan and the signature page from your Record of Compliance (ROC) or Attestation of Compliance (AOC). ”
Critical Change #3 Protecting POS Terminals 9. 9 Are devices that capture payment card via direct physical interaction with the card protected against tampering and substitution? • Maintain a list • Periodic inspection • Train personnel
MOBILE PAYMENTS? Card Readers: Smart Phone/Tablets • “Square” and others • “Category 3” device • None are certified compliant! Mobile Card Terminals n n Few are certified compliant Check with the PCI SSC
Resources www. pcisecuritystandards. org • • SAQs FAQs White Papers Certified QSAs and ASVs www. treasuryinstitute. org • Annual PCI Workshop • Listserv
Questions? Ron King rking@campusguard. com 972. 964. 8884